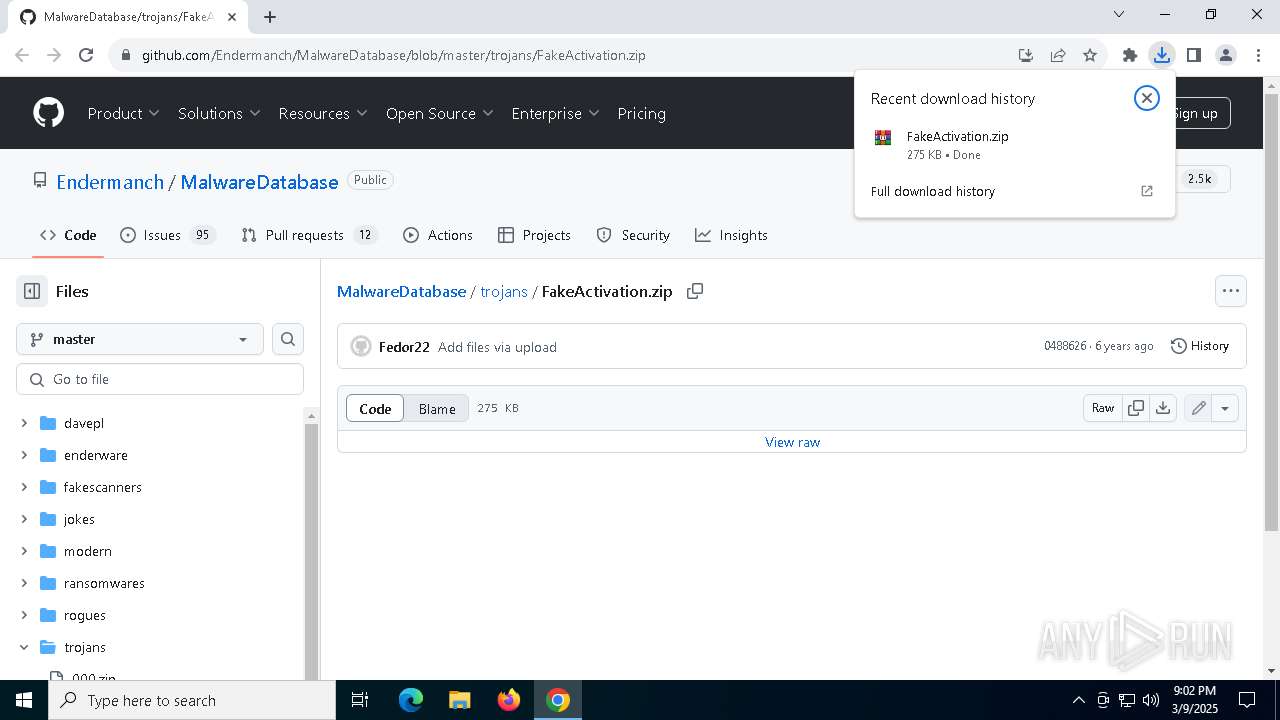
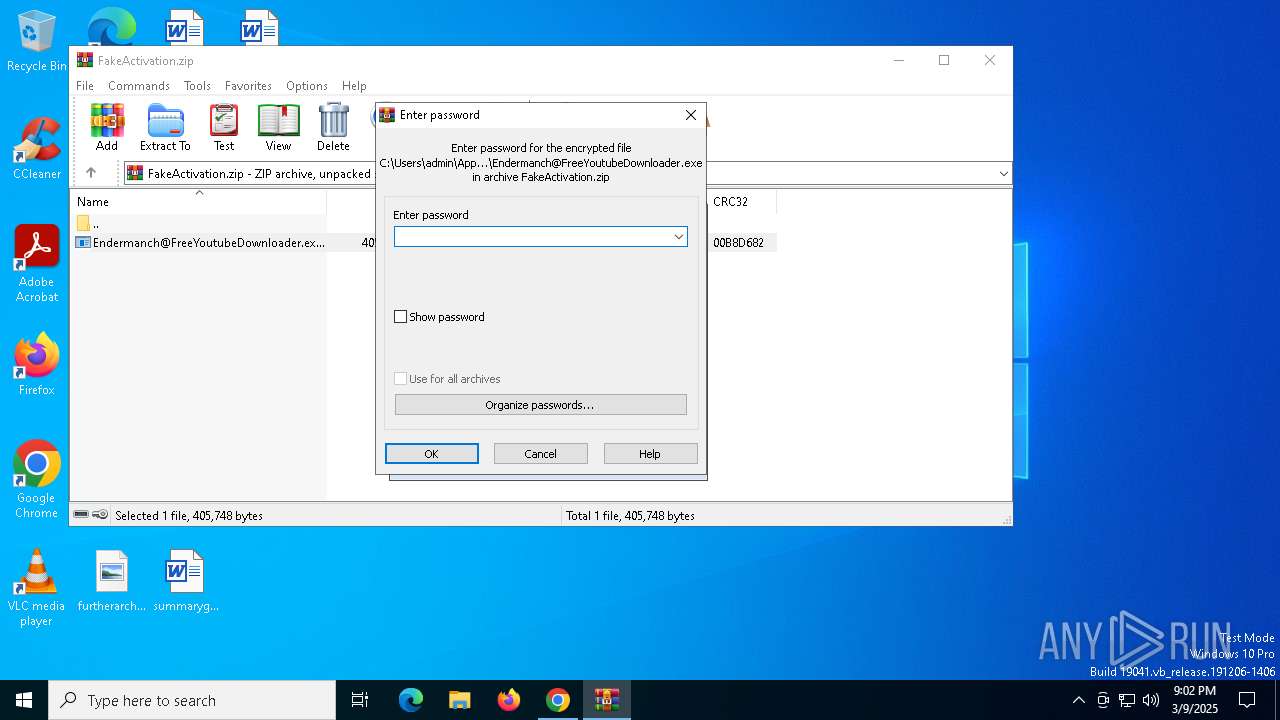
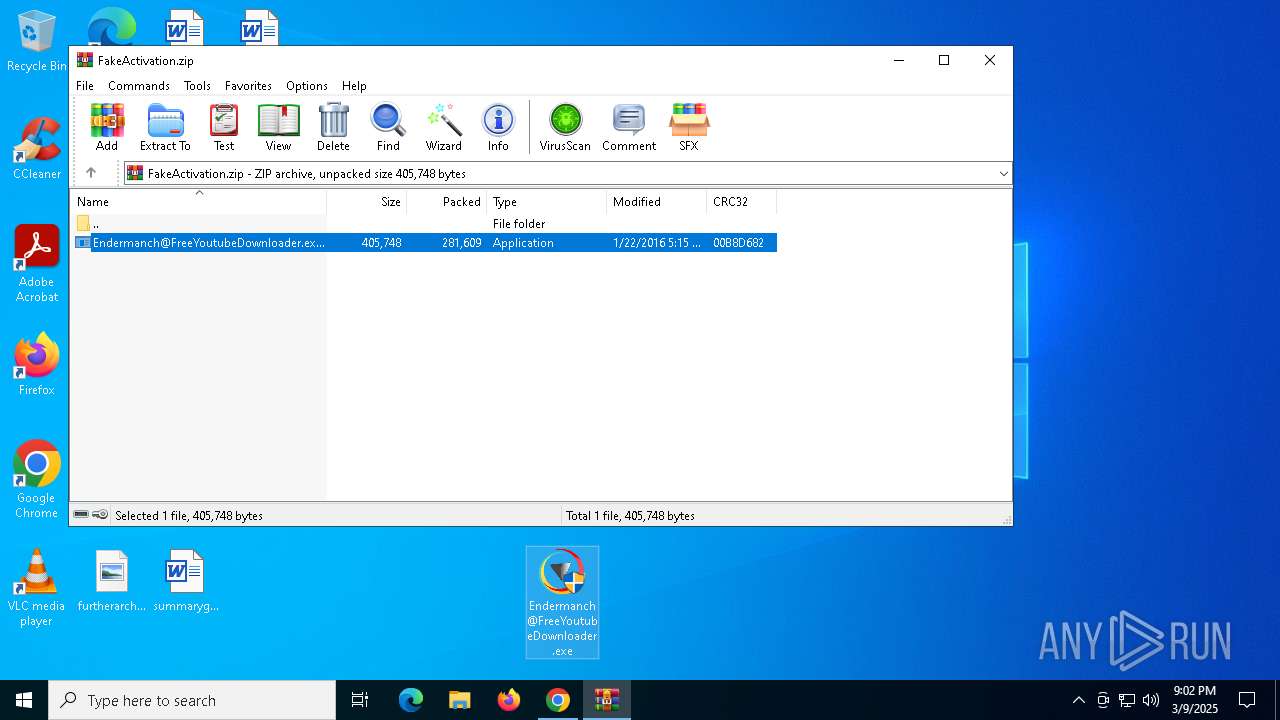
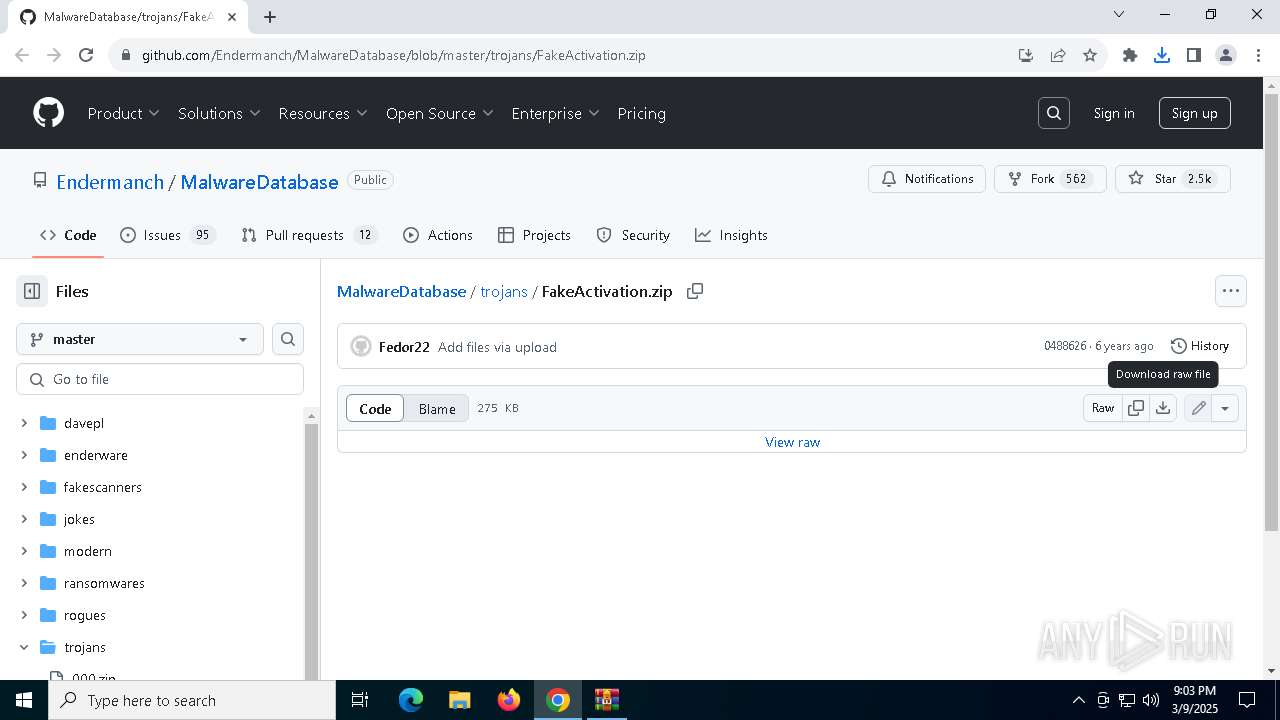
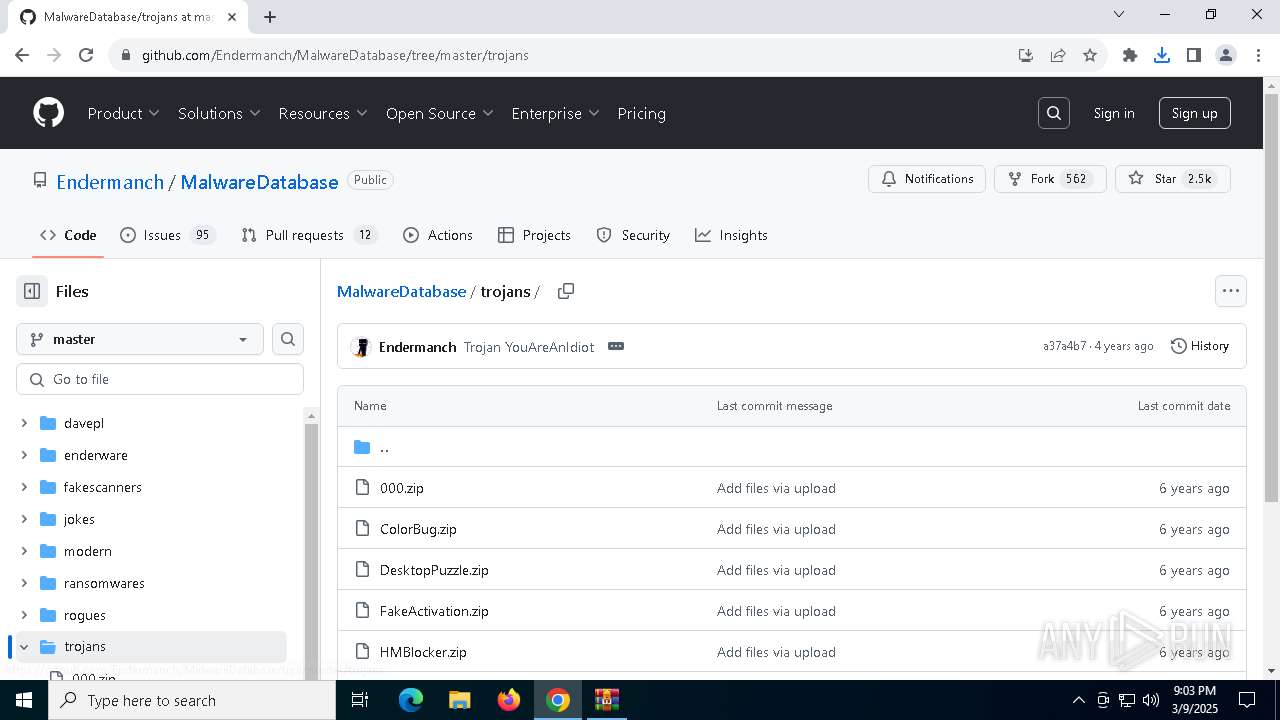
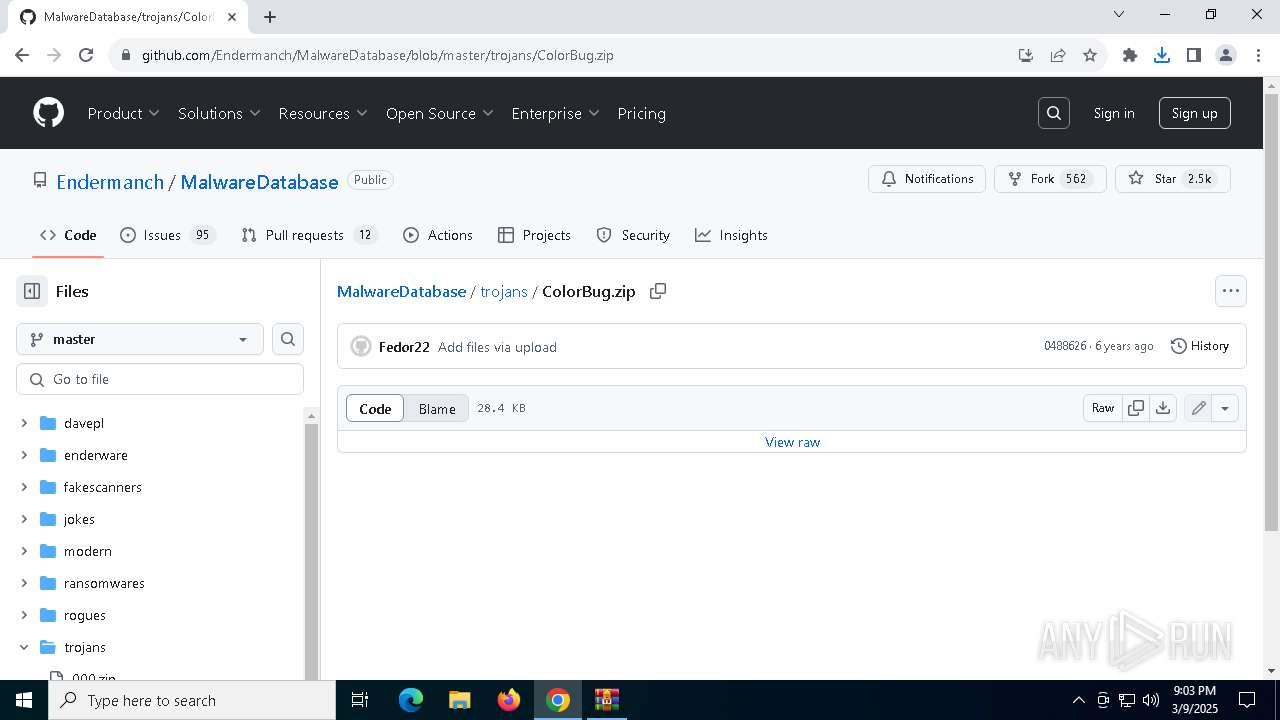
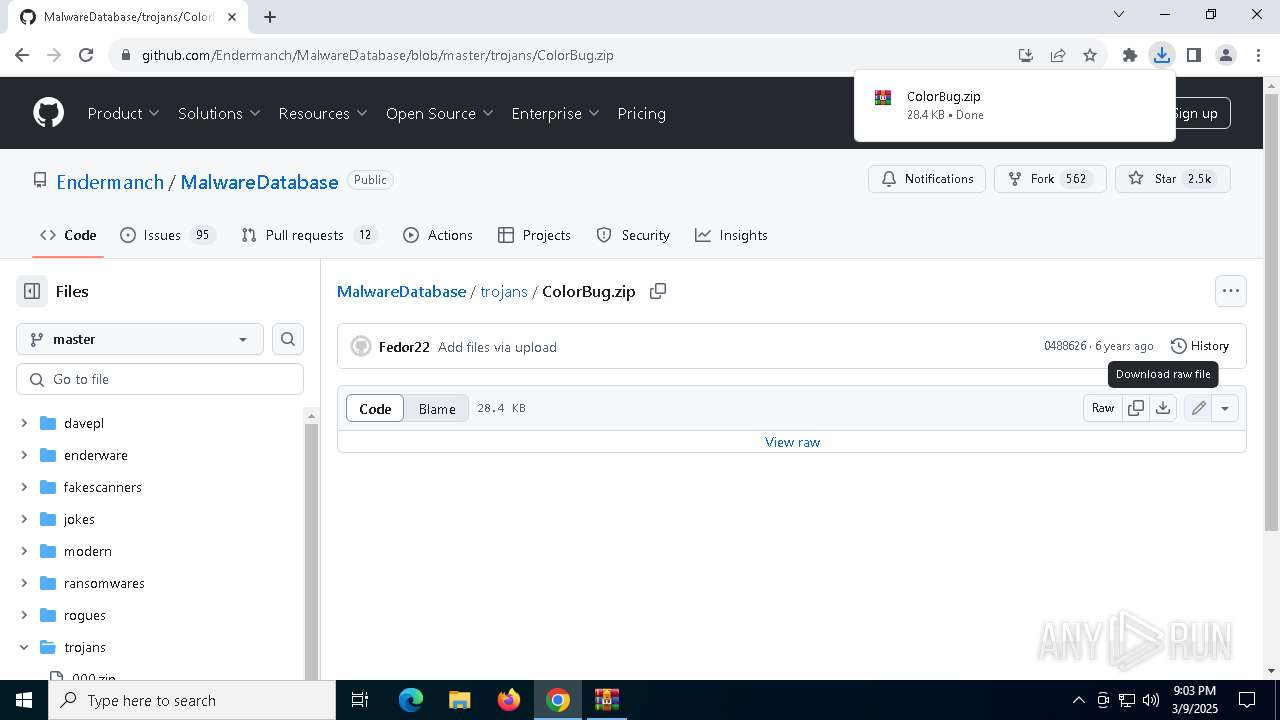
| URL: | https://github.com/Endermanch/MalwareDatabase/blob/master/trojans/FakeActivation.zip |
| Full analysis: | https://app.any.run/tasks/35f1ebb1-750d-4214-b184-2907264fdb2c |
| Verdict: | Malicious activity |
| Analysis date: | March 09, 2025, 21:02:08 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MD5: | A32389813750B1488F5AE786A56A9438 |
| SHA1: | 7A19FB9F260BC1D79B5AFA8CBD7E31C0529311BE |
| SHA256: | 7ECE13FBB127B099F1D0EBB1AABBE268D5927B5A83E5BD5538769C13AE5C588A |
| SSDEEP: | 3:N8tEdegLaKoEJ3PqkzEHaEADB34LL4n:2ufLtfnz+aECp4/4 |
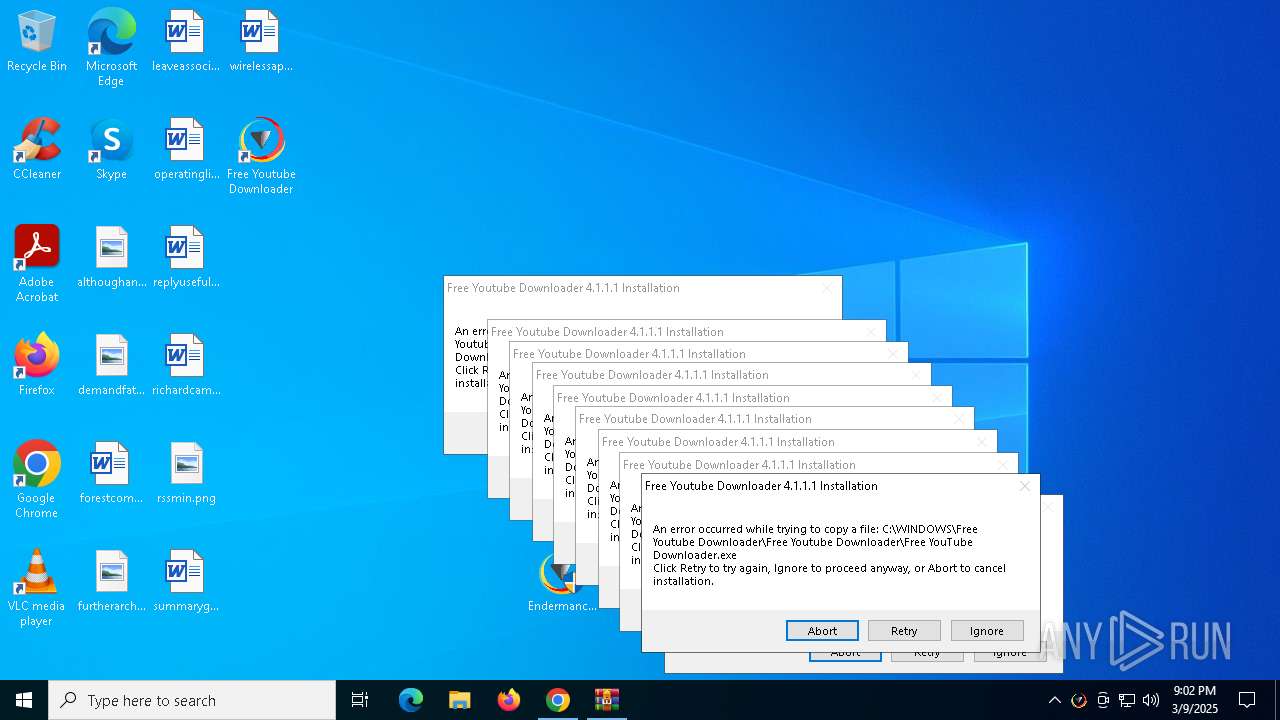
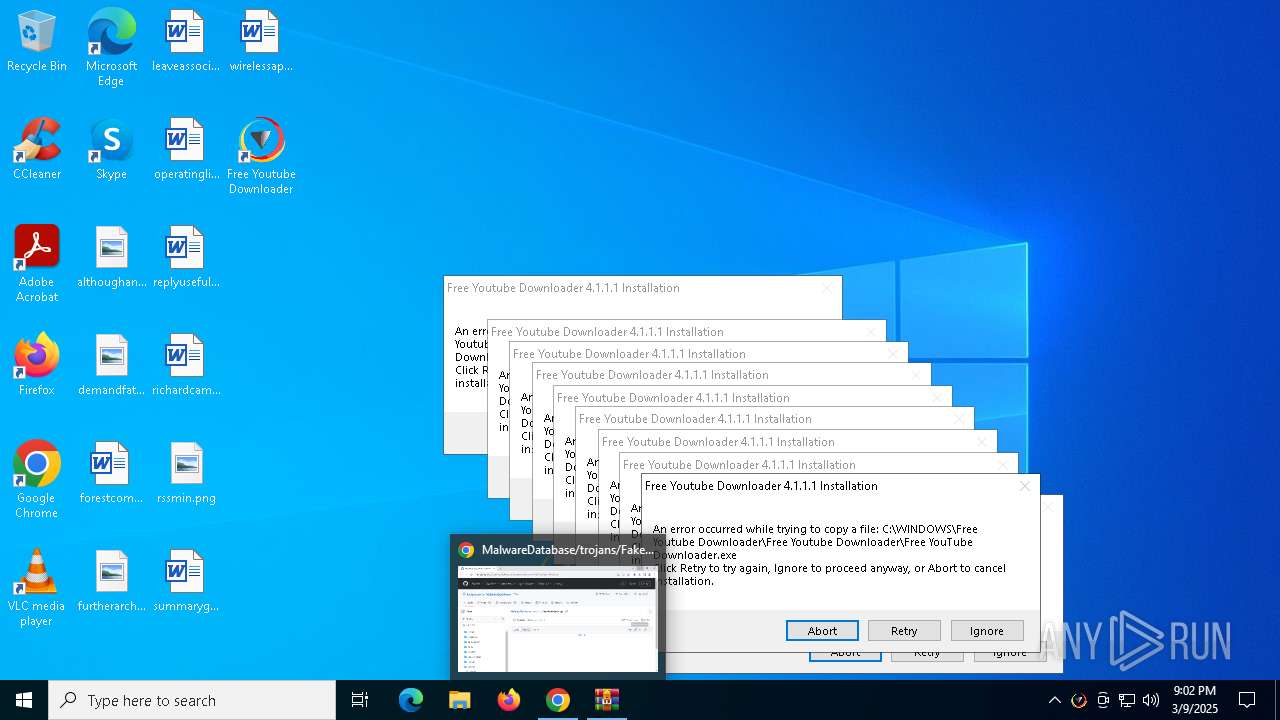
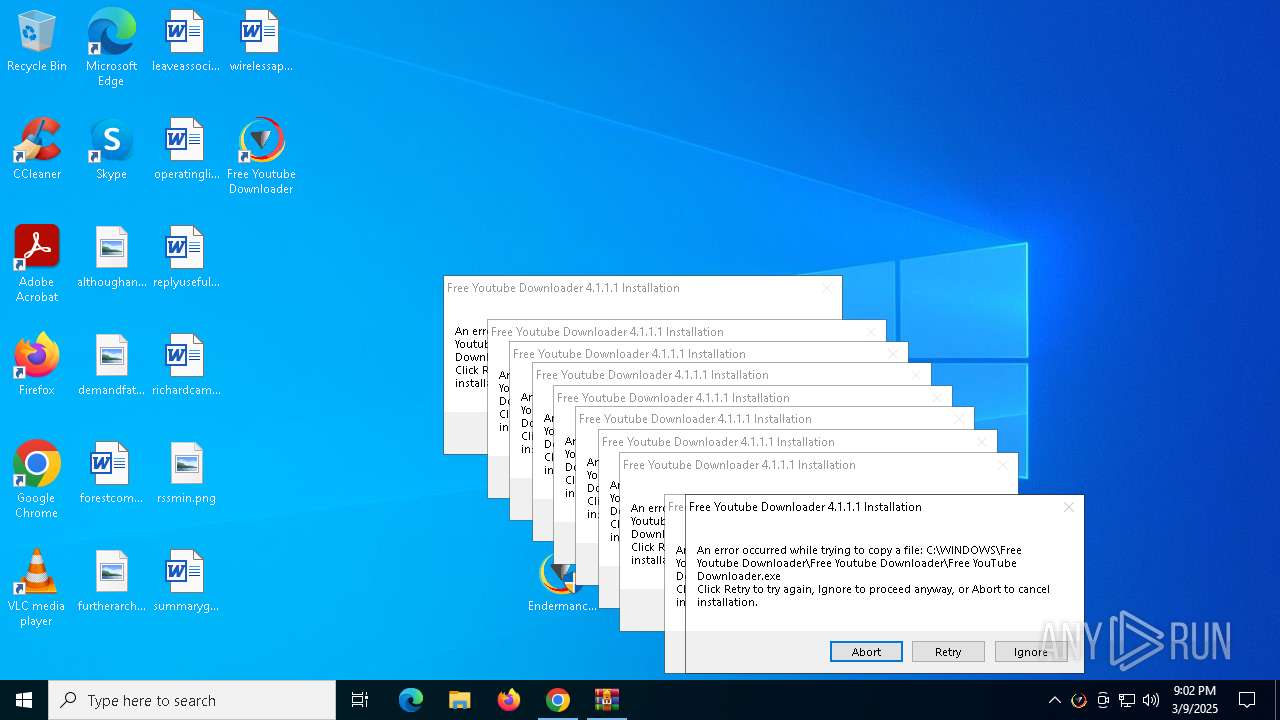
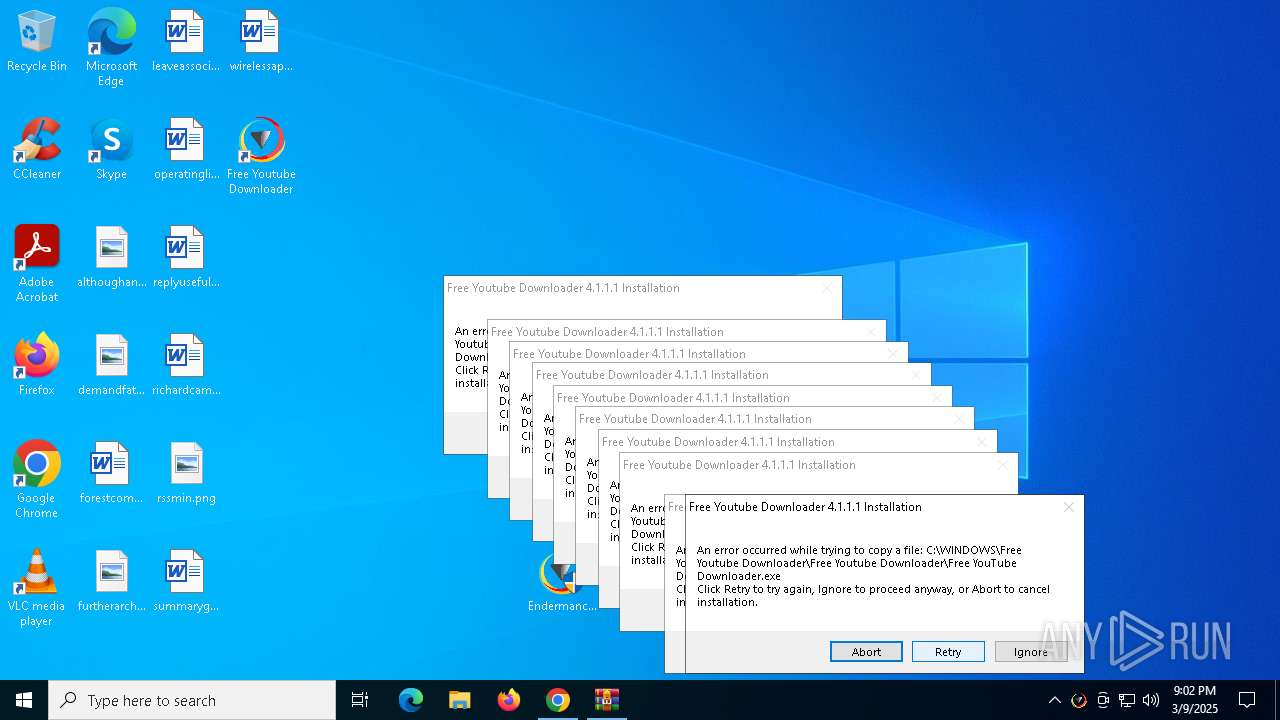
MALICIOUS
Changes the autorun value in the registry
- Endermanch@FreeYoutubeDownloader.exe (PID: 6988)
- Endermanch@FreeYoutubeDownloader.exe (PID: 8152)
SUSPICIOUS
Reads security settings of Internet Explorer
- Endermanch@FreeYoutubeDownloader.exe (PID: 6988)
- Endermanch@FreeYoutubeDownloader.exe (PID: 8152)
Creates a software uninstall entry
- Endermanch@FreeYoutubeDownloader.exe (PID: 6988)
- Endermanch@FreeYoutubeDownloader.exe (PID: 8152)
Executable content was dropped or overwritten
- Endermanch@FreeYoutubeDownloader.exe (PID: 8152)
- Endermanch@FreeYoutubeDownloader.exe (PID: 6988)
INFO
Reads security settings of Internet Explorer
- BackgroundTransferHost.exe (PID: 7612)
- BackgroundTransferHost.exe (PID: 2040)
- BackgroundTransferHost.exe (PID: 6476)
- BackgroundTransferHost.exe (PID: 1628)
- BackgroundTransferHost.exe (PID: 8036)
Creates files or folders in the user directory
- BackgroundTransferHost.exe (PID: 1628)
Checks proxy server information
- BackgroundTransferHost.exe (PID: 1628)
Application launched itself
- chrome.exe (PID: 6700)
Reads the software policy settings
- BackgroundTransferHost.exe (PID: 1628)
Reads Microsoft Office registry keys
- chrome.exe (PID: 6700)
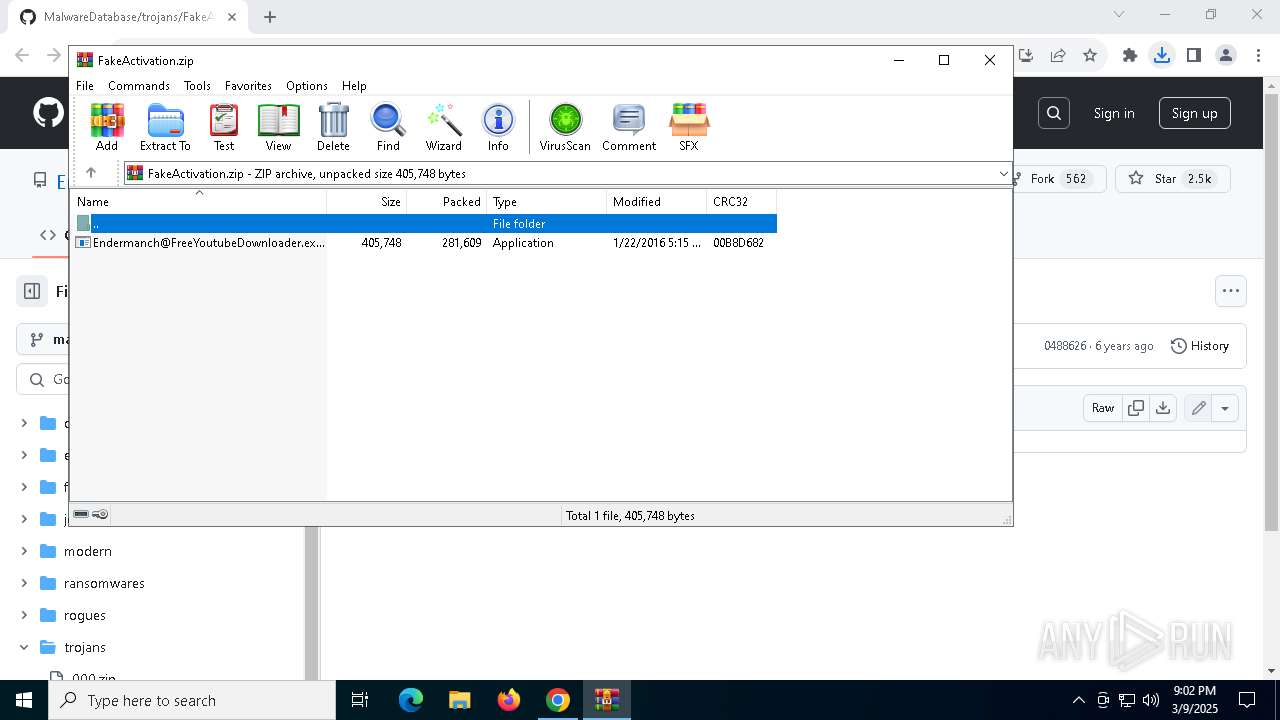
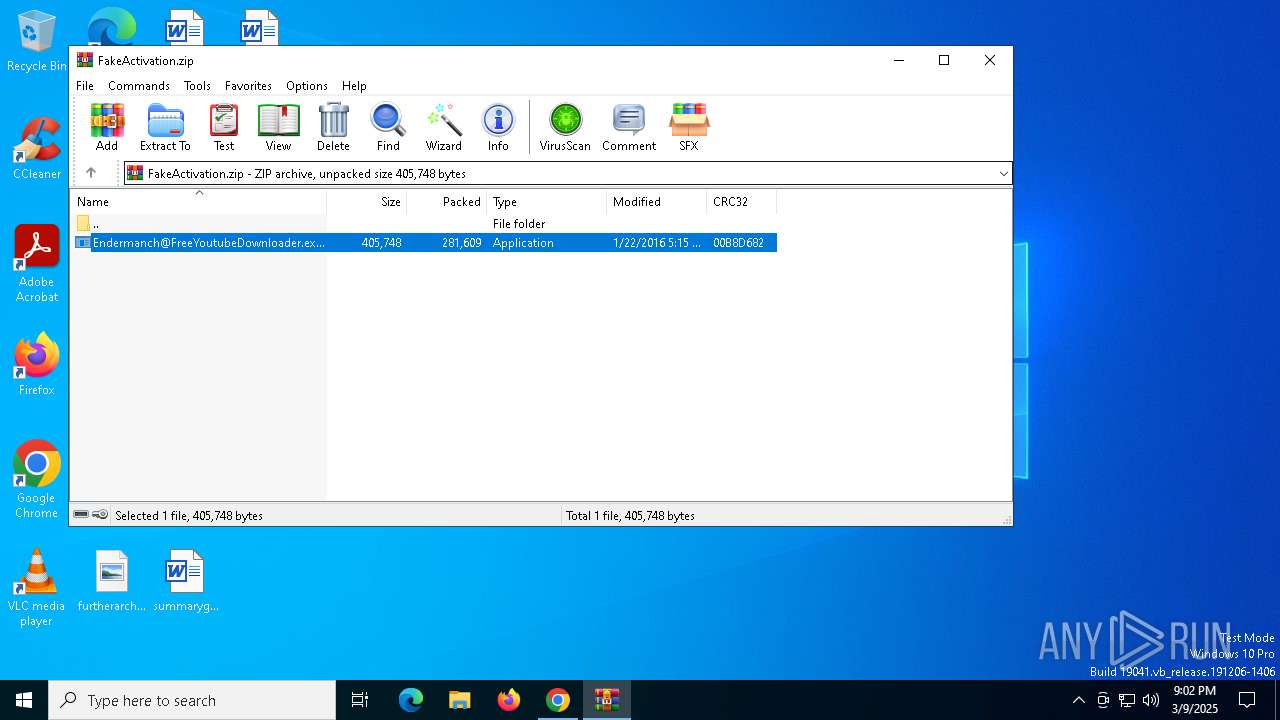
The sample compiled with english language support
- WinRAR.exe (PID: 4988)
Executable content was dropped or overwritten
- WinRAR.exe (PID: 4988)
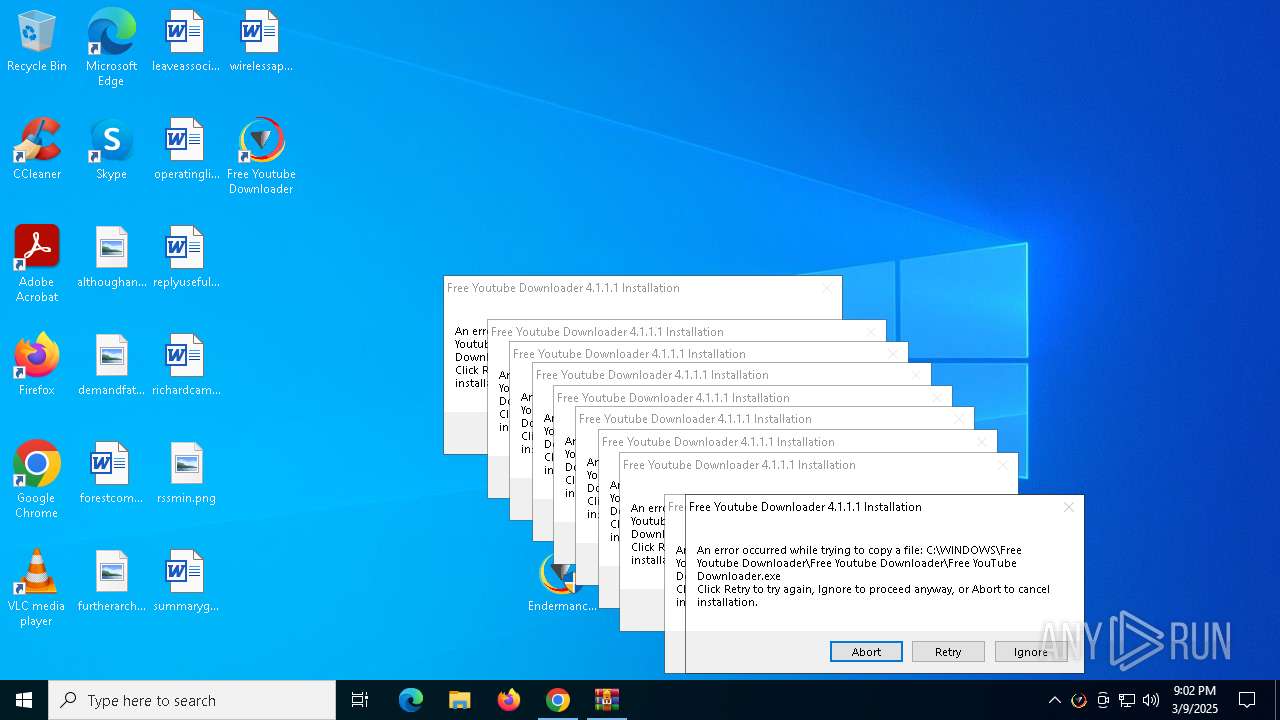
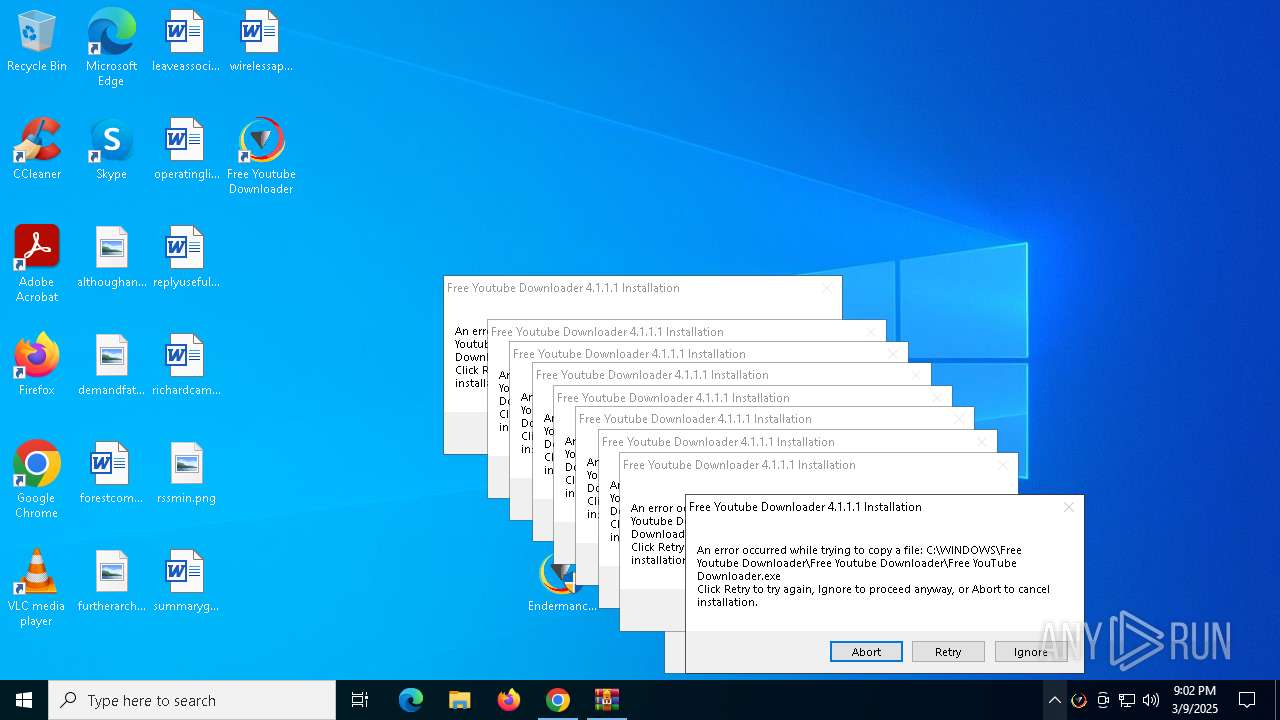
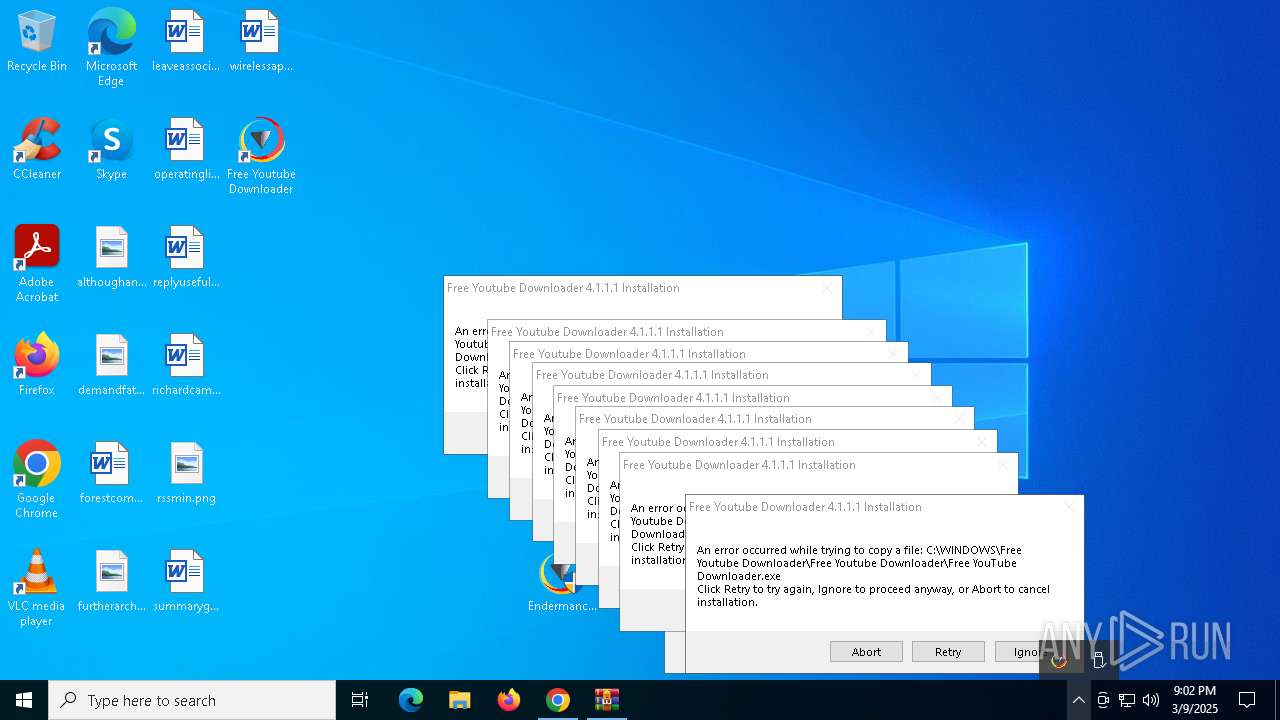
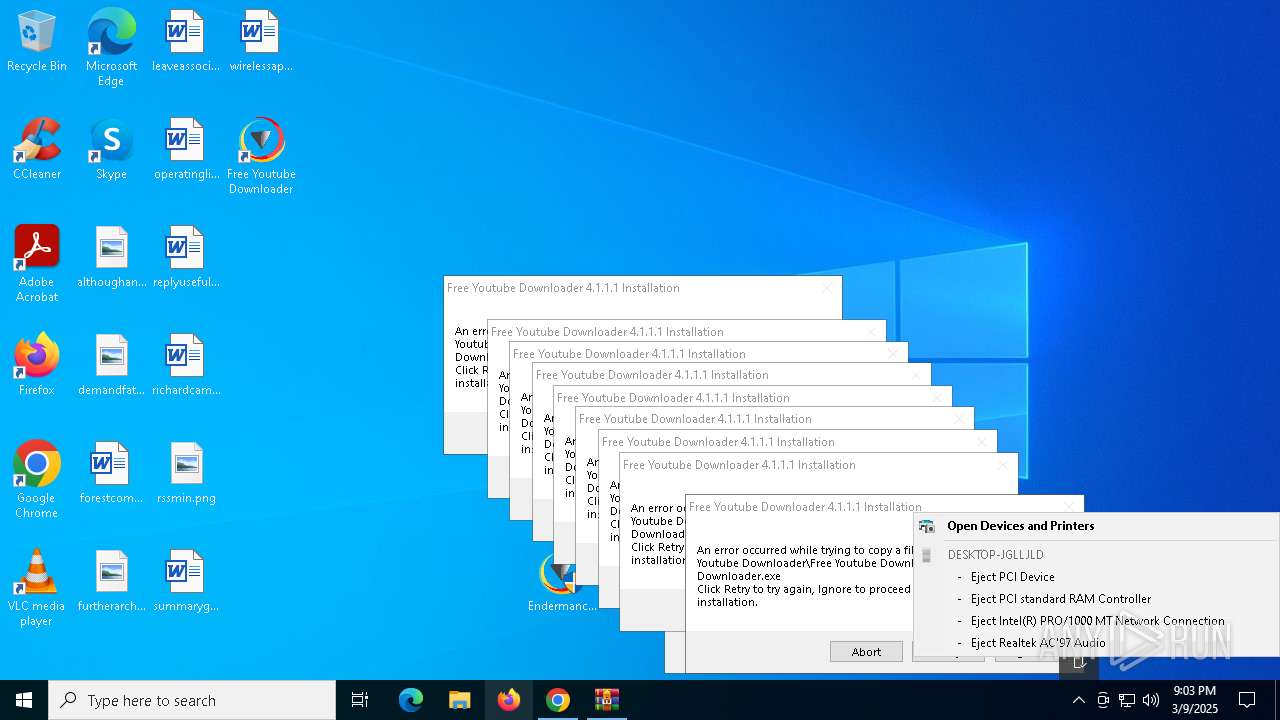
Manual execution by a user
- Endermanch@FreeYoutubeDownloader.exe (PID: 5720)
- Endermanch@FreeYoutubeDownloader.exe (PID: 6988)
- Endermanch@FreeYoutubeDownloader.exe (PID: 8152)
- Endermanch@FreeYoutubeDownloader.exe (PID: 5800)
- Endermanch@FreeYoutubeDownloader.exe (PID: 1040)
- Endermanch@FreeYoutubeDownloader.exe (PID: 1324)
- Endermanch@FreeYoutubeDownloader.exe (PID: 4224)
- Endermanch@FreeYoutubeDownloader.exe (PID: 4560)
- Endermanch@FreeYoutubeDownloader.exe (PID: 7916)
- Endermanch@FreeYoutubeDownloader.exe (PID: 8164)
- Endermanch@FreeYoutubeDownloader.exe (PID: 4112)
- Endermanch@FreeYoutubeDownloader.exe (PID: 2088)
- Endermanch@FreeYoutubeDownloader.exe (PID: 1348)
- Endermanch@FreeYoutubeDownloader.exe (PID: 6344)
- Endermanch@FreeYoutubeDownloader.exe (PID: 6476)
- Endermanch@FreeYoutubeDownloader.exe (PID: 4188)
- Endermanch@FreeYoutubeDownloader.exe (PID: 6644)
- Endermanch@FreeYoutubeDownloader.exe (PID: 7844)
- Endermanch@FreeYoutubeDownloader.exe (PID: 2504)
- Endermanch@FreeYoutubeDownloader.exe (PID: 8164)
- Endermanch@FreeYoutubeDownloader.exe (PID: 4428)
- Endermanch@FreeYoutubeDownloader.exe (PID: 5680)
- Endermanch@FreeYoutubeDownloader.exe (PID: 4628)
- Endermanch@FreeYoutubeDownloader.exe (PID: 7864)
- Endermanch@FreeYoutubeDownloader.exe (PID: 8088)
- Endermanch@FreeYoutubeDownloader.exe (PID: 6768)
- Endermanch@FreeYoutubeDownloader.exe (PID: 536)
- Endermanch@FreeYoutubeDownloader.exe (PID: 6476)
Checks supported languages
- Endermanch@FreeYoutubeDownloader.exe (PID: 6988)
- Endermanch@FreeYoutubeDownloader.exe (PID: 8152)
- Free YouTube Downloader.exe (PID: 4220)
- Free YouTube Downloader.exe (PID: 7828)
- Endermanch@FreeYoutubeDownloader.exe (PID: 1324)
- Endermanch@FreeYoutubeDownloader.exe (PID: 4560)
- Endermanch@FreeYoutubeDownloader.exe (PID: 4112)
- Endermanch@FreeYoutubeDownloader.exe (PID: 1348)
- Endermanch@FreeYoutubeDownloader.exe (PID: 5800)
- Endermanch@FreeYoutubeDownloader.exe (PID: 7844)
- Endermanch@FreeYoutubeDownloader.exe (PID: 8164)
- Endermanch@FreeYoutubeDownloader.exe (PID: 4188)
- Endermanch@FreeYoutubeDownloader.exe (PID: 6476)
- Endermanch@FreeYoutubeDownloader.exe (PID: 7864)
- Endermanch@FreeYoutubeDownloader.exe (PID: 8088)
- Endermanch@FreeYoutubeDownloader.exe (PID: 536)
Reads the computer name
- Endermanch@FreeYoutubeDownloader.exe (PID: 8152)
- Free YouTube Downloader.exe (PID: 4220)
- Free YouTube Downloader.exe (PID: 7828)
- Endermanch@FreeYoutubeDownloader.exe (PID: 5800)
- Endermanch@FreeYoutubeDownloader.exe (PID: 1324)
- Endermanch@FreeYoutubeDownloader.exe (PID: 4112)
- Endermanch@FreeYoutubeDownloader.exe (PID: 4560)
- Endermanch@FreeYoutubeDownloader.exe (PID: 1348)
- Endermanch@FreeYoutubeDownloader.exe (PID: 4188)
- Endermanch@FreeYoutubeDownloader.exe (PID: 6988)
- Endermanch@FreeYoutubeDownloader.exe (PID: 8164)
- Endermanch@FreeYoutubeDownloader.exe (PID: 6476)
- Endermanch@FreeYoutubeDownloader.exe (PID: 7864)
- Endermanch@FreeYoutubeDownloader.exe (PID: 8088)
- Endermanch@FreeYoutubeDownloader.exe (PID: 536)
- Endermanch@FreeYoutubeDownloader.exe (PID: 7844)
Create files in a temporary directory
- Endermanch@FreeYoutubeDownloader.exe (PID: 8152)
- Endermanch@FreeYoutubeDownloader.exe (PID: 1324)
- Endermanch@FreeYoutubeDownloader.exe (PID: 4560)
- Endermanch@FreeYoutubeDownloader.exe (PID: 4112)
- Endermanch@FreeYoutubeDownloader.exe (PID: 5800)
- Endermanch@FreeYoutubeDownloader.exe (PID: 1348)
- Endermanch@FreeYoutubeDownloader.exe (PID: 7844)
- Endermanch@FreeYoutubeDownloader.exe (PID: 4188)
- Endermanch@FreeYoutubeDownloader.exe (PID: 8164)
- Endermanch@FreeYoutubeDownloader.exe (PID: 6476)
- Endermanch@FreeYoutubeDownloader.exe (PID: 7864)
- Endermanch@FreeYoutubeDownloader.exe (PID: 6988)
- Endermanch@FreeYoutubeDownloader.exe (PID: 8088)
- Endermanch@FreeYoutubeDownloader.exe (PID: 536)
Process checks computer location settings
- Endermanch@FreeYoutubeDownloader.exe (PID: 8152)
- Endermanch@FreeYoutubeDownloader.exe (PID: 6988)
Reads the machine GUID from the registry
- Free YouTube Downloader.exe (PID: 7828)
- Free YouTube Downloader.exe (PID: 4220)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
202
Monitored processes
52
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 536 | "C:\Users\admin\Desktop\Endermanch@FreeYoutubeDownloader.exe" | C:\Users\admin\Desktop\Endermanch@FreeYoutubeDownloader.exe | explorer.exe | ||||||||||||
User: admin Company: Free Youtube Downloader Integrity Level: HIGH Description: Free Youtube Downloader 4.1.1.1 Installation Version: 4.1.1.1 Modules
| |||||||||||||||
| 920 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.FileUtilService --lang=en-US --service-sandbox-type=service --disable-quic --no-appcompat-clear --mojo-platform-channel-handle=4460 --field-trial-handle=1856,i,10601624117135383022,14855562016911067676,262144 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction --variations-seed-version /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 122.0.6261.70 Modules
| |||||||||||||||
| 1040 | "C:\Users\admin\Desktop\Endermanch@FreeYoutubeDownloader.exe" | C:\Users\admin\Desktop\Endermanch@FreeYoutubeDownloader.exe | — | explorer.exe | |||||||||||
User: admin Company: Free Youtube Downloader Integrity Level: MEDIUM Description: Free Youtube Downloader 4.1.1.1 Installation Exit code: 3221226540 Version: 4.1.1.1 Modules
| |||||||||||||||
| 1164 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=quarantine.mojom.Quarantine --lang=en-US --service-sandbox-type=none --disable-quic --no-appcompat-clear --mojo-platform-channel-handle=5700 --field-trial-handle=1856,i,10601624117135383022,14855562016911067676,262144 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction --variations-seed-version /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 122.0.6261.70 Modules
| |||||||||||||||
| 1324 | "C:\Users\admin\Desktop\Endermanch@FreeYoutubeDownloader.exe" | C:\Users\admin\Desktop\Endermanch@FreeYoutubeDownloader.exe | explorer.exe | ||||||||||||
User: admin Company: Free Youtube Downloader Integrity Level: HIGH Description: Free Youtube Downloader 4.1.1.1 Installation Version: 4.1.1.1 Modules
| |||||||||||||||
| 1348 | "C:\Users\admin\Desktop\Endermanch@FreeYoutubeDownloader.exe" | C:\Users\admin\Desktop\Endermanch@FreeYoutubeDownloader.exe | explorer.exe | ||||||||||||
User: admin Company: Free Youtube Downloader Integrity Level: HIGH Description: Free Youtube Downloader 4.1.1.1 Installation Version: 4.1.1.1 Modules
| |||||||||||||||
| 1628 | "BackgroundTransferHost.exe" -ServerName:BackgroundTransferHost.1 | C:\Windows\System32\BackgroundTransferHost.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Download/Upload Host Exit code: 1 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2040 | "BackgroundTransferHost.exe" -ServerName:BackgroundTransferHost.1 | C:\Windows\System32\BackgroundTransferHost.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Download/Upload Host Exit code: 1 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2088 | "C:\Users\admin\Desktop\Endermanch@FreeYoutubeDownloader.exe" | C:\Users\admin\Desktop\Endermanch@FreeYoutubeDownloader.exe | — | explorer.exe | |||||||||||
User: admin Company: Free Youtube Downloader Integrity Level: MEDIUM Description: Free Youtube Downloader 4.1.1.1 Installation Exit code: 3221226540 Version: 4.1.1.1 Modules
| |||||||||||||||
| 2504 | "C:\Users\admin\Desktop\Endermanch@FreeYoutubeDownloader.exe" | C:\Users\admin\Desktop\Endermanch@FreeYoutubeDownloader.exe | — | explorer.exe | |||||||||||
User: admin Company: Free Youtube Downloader Integrity Level: MEDIUM Description: Free Youtube Downloader 4.1.1.1 Installation Exit code: 3221226540 Version: 4.1.1.1 Modules
| |||||||||||||||
Total events
10 122
Read events
10 048
Write events
74
Delete events
0
Modification events
| (PID) Process: | (6700) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (6700) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (6700) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (6700) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (6700) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
| (PID) Process: | (7612) BackgroundTransferHost.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\CurrentVersion\AppContainer\Storage\microsoft.windows.contentdeliverymanager_cw5n1h2txyewy\Internet Settings\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (7612) BackgroundTransferHost.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\CurrentVersion\AppContainer\Storage\microsoft.windows.contentdeliverymanager_cw5n1h2txyewy\Internet Settings\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (7612) BackgroundTransferHost.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\CurrentVersion\AppContainer\Storage\microsoft.windows.contentdeliverymanager_cw5n1h2txyewy\Internet Settings\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (1628) BackgroundTransferHost.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\CurrentVersion\AppContainer\Storage\microsoft.windows.contentdeliverymanager_cw5n1h2txyewy\Internet Settings\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (1628) BackgroundTransferHost.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\CurrentVersion\AppContainer\Storage\microsoft.windows.contentdeliverymanager_cw5n1h2txyewy\Internet Settings\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
Executable files
8
Suspicious files
59
Text files
20
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6700 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\parcel_tracking_db\LOG.old~RF10c304.TMP | — | |
MD5:— | SHA256:— | |||
| 6700 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\discounts_db\LOG.old~RF10c304.TMP | — | |
MD5:— | SHA256:— | |||
| 6700 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\chrome_cart_db\LOG.old~RF10c304.TMP | — | |
MD5:— | SHA256:— | |||
| 6700 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6700 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\chrome_cart_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6700 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6700 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\commerce_subscription_db\LOG.old~RF10c313.TMP | — | |
MD5:— | SHA256:— | |||
| 6700 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6700 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\coupon_db\LOG.old~RF10c323.TMP | — | |
MD5:— | SHA256:— | |||
| 6700 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\coupon_db\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
5
TCP/UDP connections
56
DNS requests
39
Threats
2
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
7860 | SIHClient.exe | GET | 200 | 23.52.120.96:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
1628 | BackgroundTransferHost.exe | GET | 200 | 184.30.131.245:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
7860 | SIHClient.exe | GET | 200 | 23.52.120.96:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
7836 | backgroundTaskHost.exe | GET | 200 | 184.30.131.245:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAUZZSZEml49Gjh0j13P68w%3D | unknown | — | — | whitelisted |
6544 | svchost.exe | GET | 200 | 184.30.131.245:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
2104 | svchost.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
5496 | MoUsoCoreWorker.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
6700 | chrome.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
7316 | chrome.exe | 140.82.121.4:443 | github.com | GITHUB | US | whitelisted |
7316 | chrome.exe | 142.251.31.84:443 | accounts.google.com | GOOGLE | US | whitelisted |
3216 | svchost.exe | 40.115.3.253:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
7316 | chrome.exe | 185.199.111.154:443 | github.githubassets.com | FASTLY | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
github.com |
| whitelisted |
accounts.google.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
github.githubassets.com |
| whitelisted |
avatars.githubusercontent.com |
| whitelisted |
github-cloud.s3.amazonaws.com |
| whitelisted |
user-images.githubusercontent.com |
| whitelisted |
login.live.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
7316 | chrome.exe | Not Suspicious Traffic | INFO [ANY.RUN] Attempting to access raw user content on GitHub |
7316 | chrome.exe | Not Suspicious Traffic | INFO [ANY.RUN] Attempting to access raw user content on GitHub |