| File name: | 0aa8a03734867e84d33c72a2c0cc88d6 (1) |
| Full analysis: | https://app.any.run/tasks/571022f6-dea8-4052-892a-8aecbe6e05c1 |
| Verdict: | Malicious activity |
| Analysis date: | May 20, 2019, 15:36:08 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 0AA8A03734867E84D33C72A2C0CC88D6 |
| SHA1: | B52C7B4236C955FE8552EDA8325CFF93AB90DBE6 |
| SHA256: | 7ECAB4A1EB36D6494582097B4A361DFFFE7D6E1DECA3DB4AF86750BD9F237286 |
| SSDEEP: | 24576:iXhZgPlU9THIsRloUrvDuFtR7XVItaUMewrecHJvClv3b6hX/tNbXA5KLIrHiXxD:WIU9bII21zIVLwLHJvQ3ehaFI9VhnlT |
MALICIOUS
Application was dropped or rewritten from another process
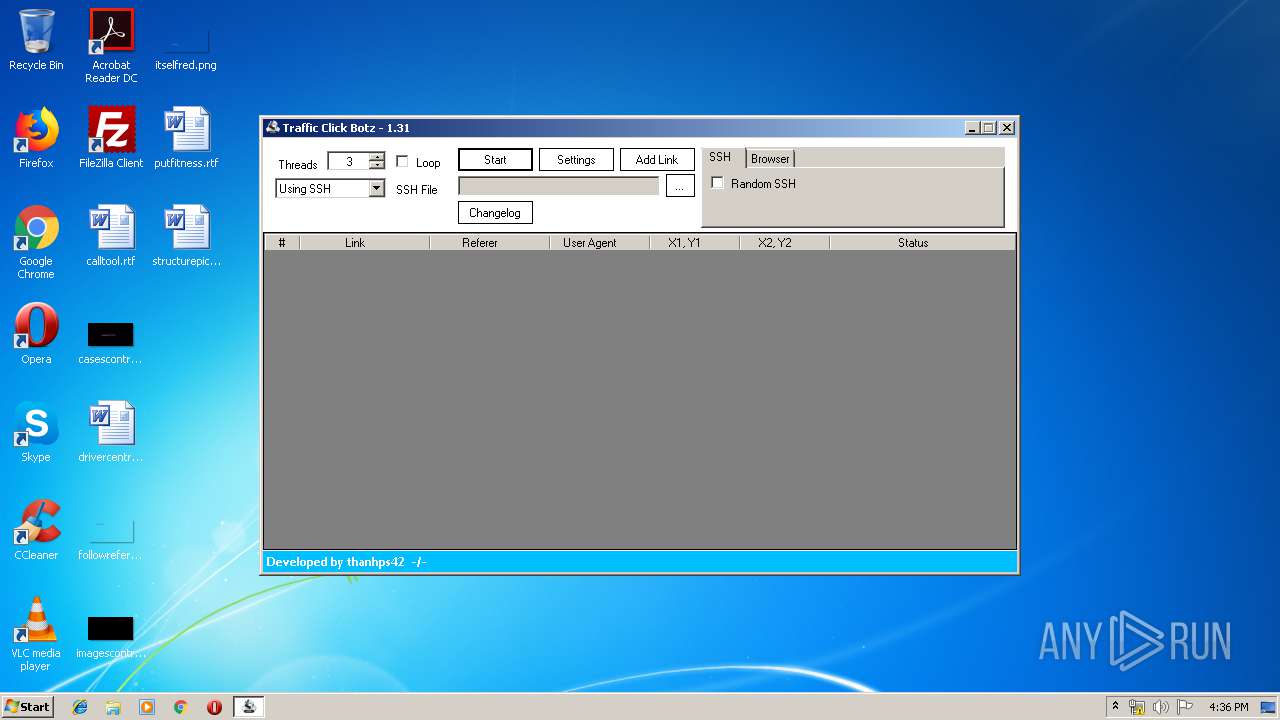
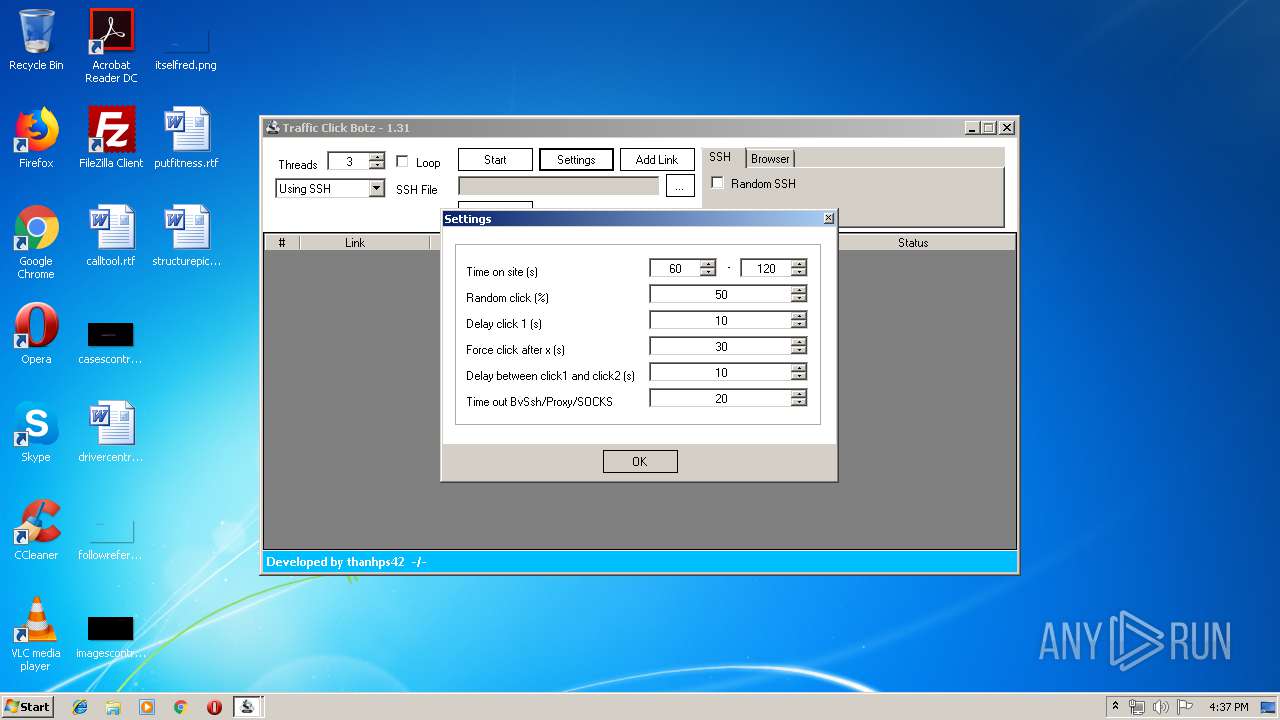
- Traffic Click Botz.exe (PID: 2792)
- net.exe (PID: 3200)
- AMDset.exe (PID: 1180)
- net.exe (PID: 2896)
Changes settings of System certificates
- AMDset.exe (PID: 1180)
SUSPICIOUS
Executable content was dropped or overwritten
- 0aa8a03734867e84d33c72a2c0cc88d6 (1).exe (PID: 3456)
- net.exe (PID: 3200)
Application launched itself
- net.exe (PID: 2896)
Creates files in the user directory
- net.exe (PID: 3200)
Reads Environment values
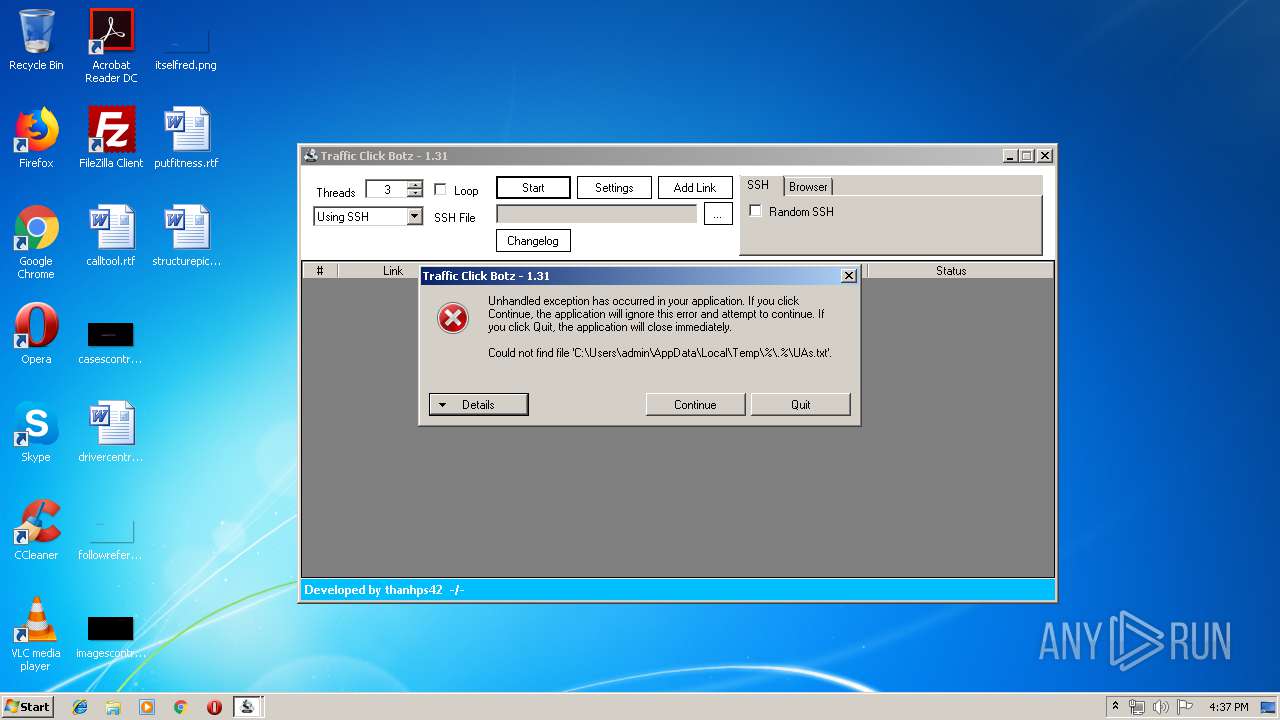
- Traffic Click Botz.exe (PID: 2792)
Adds / modifies Windows certificates
- AMDset.exe (PID: 1180)
INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win64 Executable (generic) (64.6) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (15.4) |
| .exe | | | Win32 Executable (generic) (10.5) |
| .exe | | | Generic Win/DOS Executable (4.6) |
| .exe | | | DOS Executable Generic (4.6) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2019:02:24 20:03:26+01:00 |
| PEType: | PE32 |
| LinkerVersion: | 14 |
| CodeSize: | 190976 |
| InitializedDataSize: | 230400 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x1d779 |
| OSVersion: | 5.1 |
| ImageVersion: | - |
| SubsystemVersion: | 5.1 |
| Subsystem: | Windows GUI |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 24-Feb-2019 19:03:26 |
| Detected languages: |
|
| Debug artifacts: |
|
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000110 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 6 |
| Time date stamp: | 24-Feb-2019 19:03:26 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x0002E864 | 0x0002EA00 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.69348 |
.rdata | 0x00030000 | 0x00009AAC | 0x00009C00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.13383 |
.data | 0x0003A000 | 0x000213D0 | 0x00000C00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 3.24289 |
.gfids | 0x0005C000 | 0x000000E8 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 2.09592 |
.rsrc | 0x0005D000 | 0x0002B95C | 0x0002BA00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 6.22784 |
.reloc | 0x00089000 | 0x00001FD0 | 0x00002000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 6.68736 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.25329 | 1875 | Latin 1 / Western European | English - United States | RT_MANIFEST |
2 | 4.44475 | 67624 | Latin 1 / Western European | Process Default Language | RT_ICON |
3 | 4.75897 | 16936 | Latin 1 / Western European | Process Default Language | RT_ICON |
4 | 4.76126 | 9640 | Latin 1 / Western European | Process Default Language | RT_ICON |
5 | 4.94268 | 4264 | Latin 1 / Western European | Process Default Language | RT_ICON |
6 | 5.24005 | 2440 | Latin 1 / Western European | Process Default Language | RT_ICON |
7 | 3.23498 | 564 | Latin 1 / Western European | German - Germany | RT_STRING |
8 | 3.21532 | 616 | Latin 1 / Western European | German - Germany | RT_STRING |
9 | 3.20126 | 604 | Latin 1 / Western European | German - Germany | RT_STRING |
10 | 3.20175 | 416 | Latin 1 / Western European | German - Germany | RT_STRING |
Imports
KERNEL32.dll |
USER32.dll (delay-loaded) |
gdiplus.dll |
Total processes
36
Monitored processes
5
Malicious processes
4
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1180 | C:\Users\admin\AppData\Roaming\AMDset\AMDset.exe | C:\Users\admin\AppData\Roaming\AMDset\AMDset.exe | net.exe | ||||||||||||
User: admin Company: Advanced Micro Devices, Inc. Integrity Level: MEDIUM Description: CLIStart Exit code: 0 Version: 3.5.0.0 Modules
| |||||||||||||||
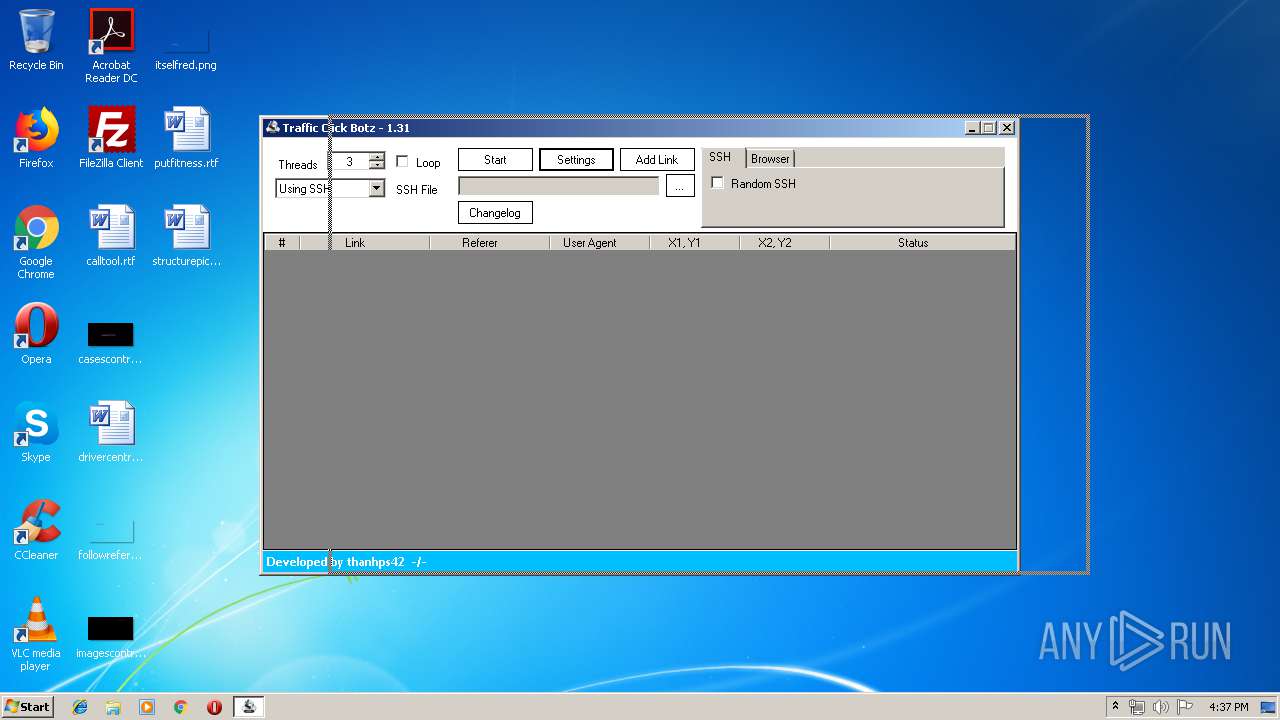
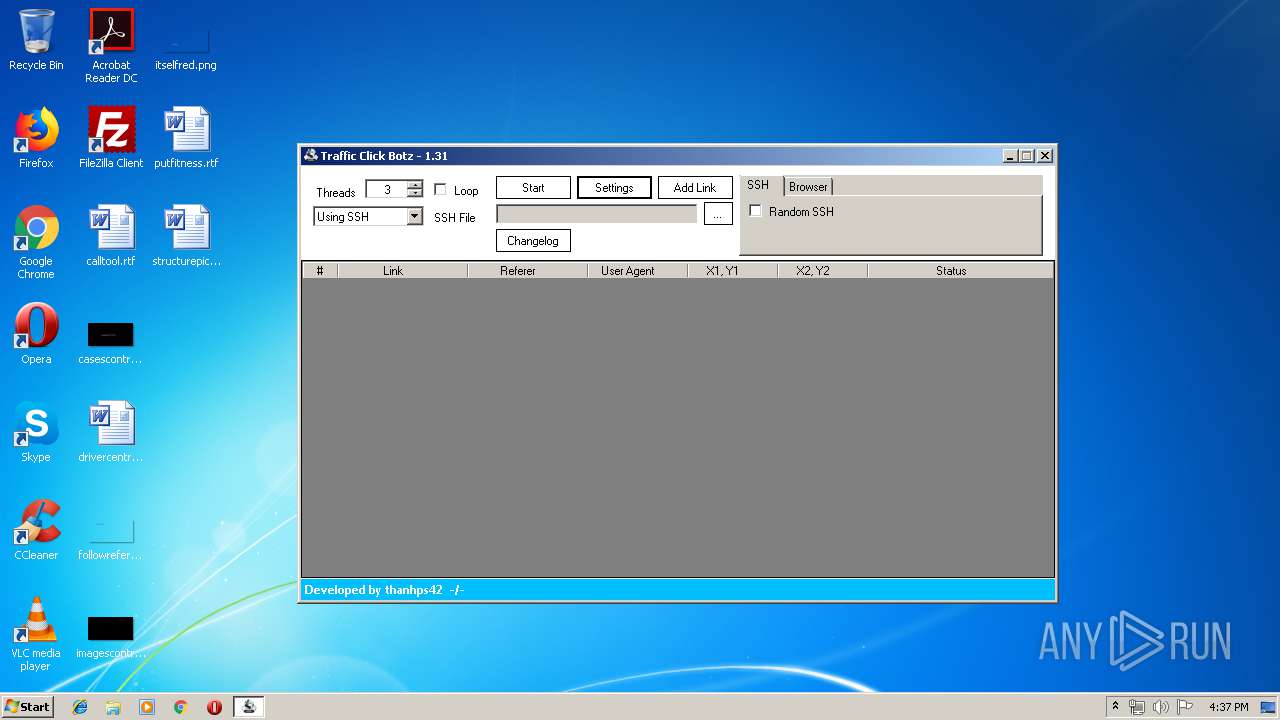
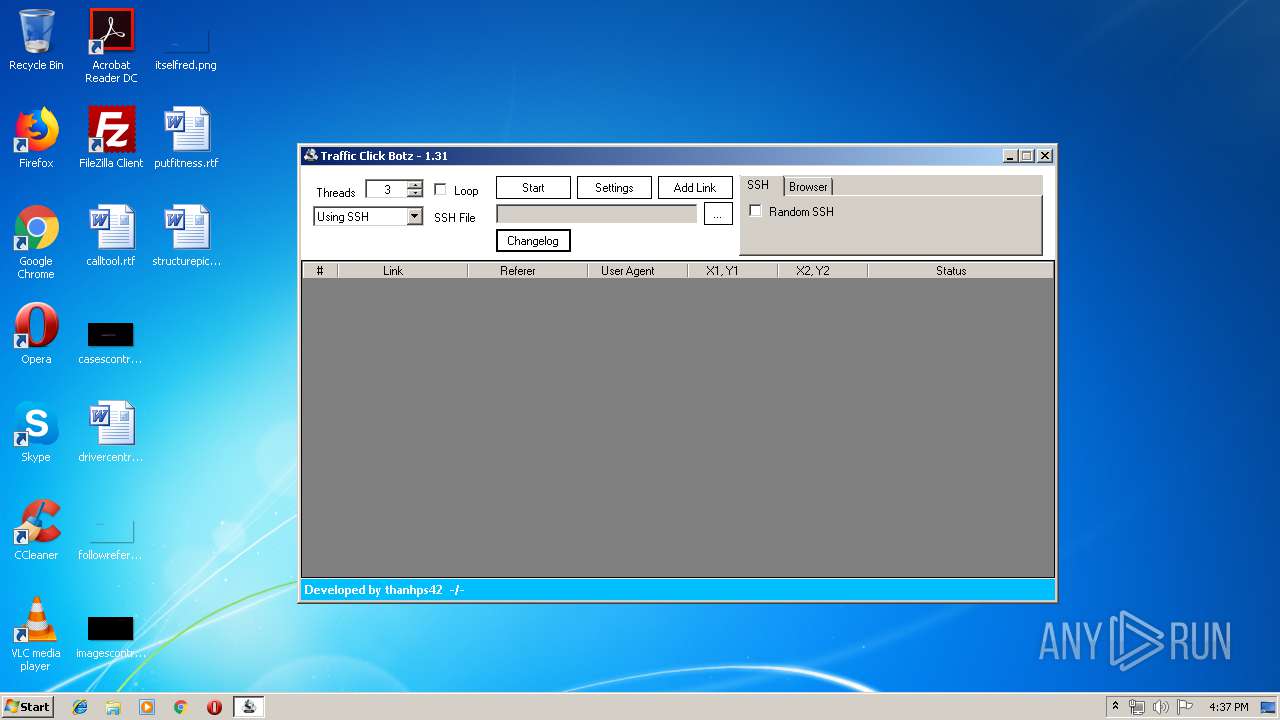
| 2792 | "C:\Users\admin\AppData\Local\Temp\%\.%\Traffic Click Botz.exe" | C:\Users\admin\AppData\Local\Temp\%\.%\Traffic Click Botz.exe | 0aa8a03734867e84d33c72a2c0cc88d6 (1).exe | ||||||||||||
User: admin Company: Microsoft Integrity Level: MEDIUM Description: Traffic Click Botz Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
| 2896 | "C:\Users\admin\AppData\Local\Temp\%\.%\net.exe" | C:\Users\admin\AppData\Local\Temp\%\.%\net.exe | — | 0aa8a03734867e84d33c72a2c0cc88d6 (1).exe | |||||||||||
User: admin Company: TechSmith Corporation Integrity Level: MEDIUM Description: CamtasiaStudio.exe Exit code: 0 Version: 0.0.31.0 Modules
| |||||||||||||||
| 3200 | "C:\Users\admin\AppData\Local\Temp\%\.%\net.exe" | C:\Users\admin\AppData\Local\Temp\%\.%\net.exe | net.exe | ||||||||||||
User: admin Company: TechSmith Corporation Integrity Level: MEDIUM Description: CamtasiaStudio.exe Exit code: 0 Version: 0.0.31.0 Modules
| |||||||||||||||
| 3456 | "C:\Users\admin\AppData\Local\Temp\0aa8a03734867e84d33c72a2c0cc88d6 (1).exe" | C:\Users\admin\AppData\Local\Temp\0aa8a03734867e84d33c72a2c0cc88d6 (1).exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
Total events
526
Read events
475
Write events
49
Delete events
2
Modification events
| (PID) Process: | (3456) 0aa8a03734867e84d33c72a2c0cc88d6 (1).exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (3456) 0aa8a03734867e84d33c72a2c0cc88d6 (1).exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (2792) Traffic Click Botz.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (2792) Traffic Click Botz.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (1180) AMDset.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\AMDset_RASAPI32 |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (1180) AMDset.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\AMDset_RASAPI32 |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
| (PID) Process: | (1180) AMDset.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\AMDset_RASAPI32 |
| Operation: | write | Name: | FileTracingMask |
Value: 4294901760 | |||
| (PID) Process: | (1180) AMDset.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\AMDset_RASAPI32 |
| Operation: | write | Name: | ConsoleTracingMask |
Value: 4294901760 | |||
| (PID) Process: | (1180) AMDset.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\AMDset_RASAPI32 |
| Operation: | write | Name: | MaxFileSize |
Value: 1048576 | |||
| (PID) Process: | (1180) AMDset.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\AMDset_RASAPI32 |
| Operation: | write | Name: | FileDirectory |
Value: %windir%\tracing | |||
Executable files
3
Suspicious files
0
Text files
1
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3200 | net.exe | C:\Users\admin\AppData\Local\Temp\autF5F6.tmp | — | |
MD5:— | SHA256:— | |||
| 2792 | Traffic Click Botz.exe | C:\Users\admin\AppData\Local\Temp\%\.%\Settings.xml | text | |
MD5:— | SHA256:— | |||
| 3456 | 0aa8a03734867e84d33c72a2c0cc88d6 (1).exe | C:\Users\admin\AppData\Local\Temp\%\.%\net.exe | executable | |
MD5:— | SHA256:— | |||
| 3456 | 0aa8a03734867e84d33c72a2c0cc88d6 (1).exe | C:\Users\admin\AppData\Local\Temp\%\.%\Traffic Click Botz.exe | executable | |
MD5:— | SHA256:— | |||
| 3200 | net.exe | C:\Users\admin\AppData\Roaming\AMDset\AMDset.exe | executable | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
177
DNS requests
3
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2792 | Traffic Click Botz.exe | 23.91.70.19:3306 | marten.arvixe.com | Colo4, LLC | US | suspicious |
1180 | AMDset.exe | 104.20.209.21:443 | pastebin.com | Cloudflare Inc | US | shared |
1180 | AMDset.exe | 185.163.45.48:5656 | — | MivoCloud SRL | MD | suspicious |
— | — | 23.91.70.19:3306 | marten.arvixe.com | Colo4, LLC | US | suspicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
marten.arvixe.com |
| suspicious |
pastebin.com |
| malicious |
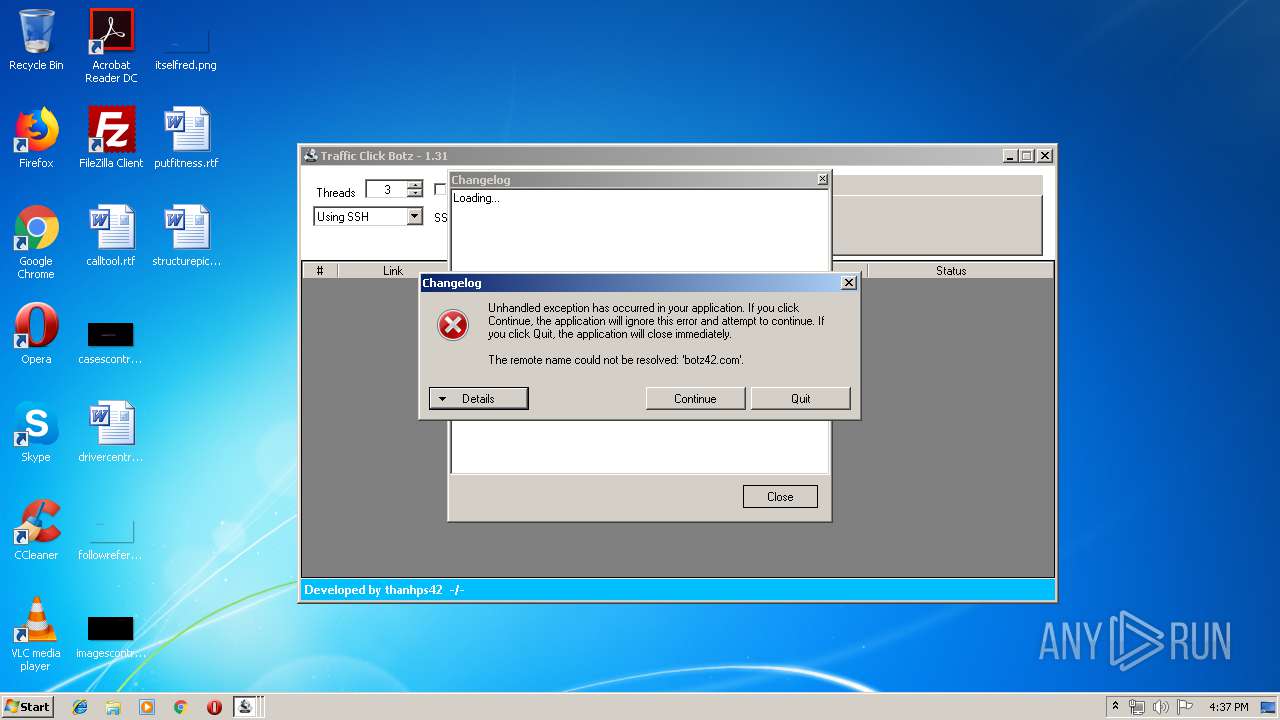
botz42.com |
| unknown |
Threats
Process | Message |
|---|---|
Traffic Click Botz.exe | Traffic Click Botz.exe Error: 0 : |
Traffic Click Botz.exe | Authentication to host 'marten.arvixe.com' for user 'thanhps_user' using method 'mysql_native_password' failed with message: Access denied for user 'thanhps_user'@'217.147.89.18' (using password: YES)
|
Traffic Click Botz.exe | Traffic Click Botz.exe Error: 0 : |
Traffic Click Botz.exe | Authentication to host 'marten.arvixe.com' for user 'thanhps_user' using method 'mysql_native_password' failed with message: Access denied for user 'thanhps_user'@'217.147.89.18' (using password: YES)
|
Traffic Click Botz.exe | Traffic Click Botz.exe Error: 0 : |
Traffic Click Botz.exe | Authentication to host 'marten.arvixe.com' for user 'thanhps_user' using method 'mysql_native_password' failed with message: Access denied for user 'thanhps_user'@'217.147.89.18' (using password: YES)
|
Traffic Click Botz.exe | Traffic Click Botz.exe Error: 0 : |
Traffic Click Botz.exe | Authentication to host 'marten.arvixe.com' for user 'thanhps_user' using method 'mysql_native_password' failed with message: Access denied for user 'thanhps_user'@'217.147.89.18' (using password: YES)
|
Traffic Click Botz.exe | Traffic Click Botz.exe Error: 0 : |
Traffic Click Botz.exe | Authentication to host 'marten.arvixe.com' for user 'thanhps_user' using method 'mysql_native_password' failed with message: Access denied for user 'thanhps_user'@'217.147.89.18' (using password: YES)
|