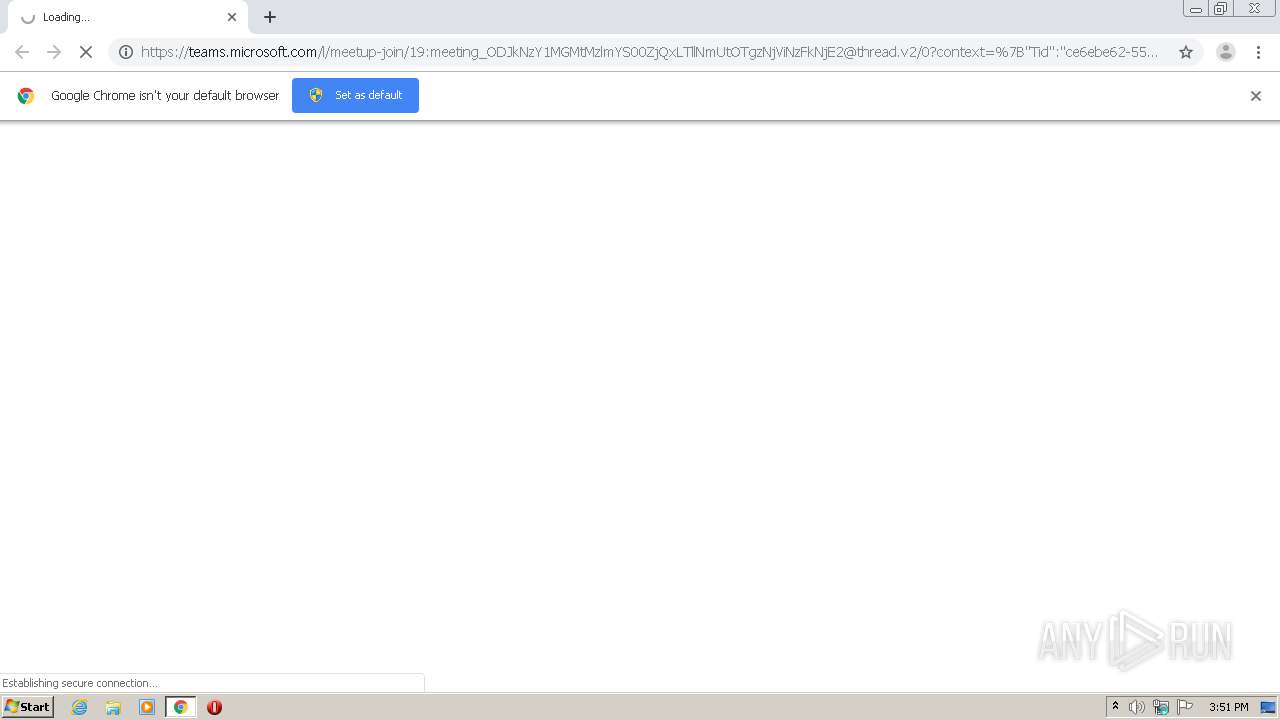
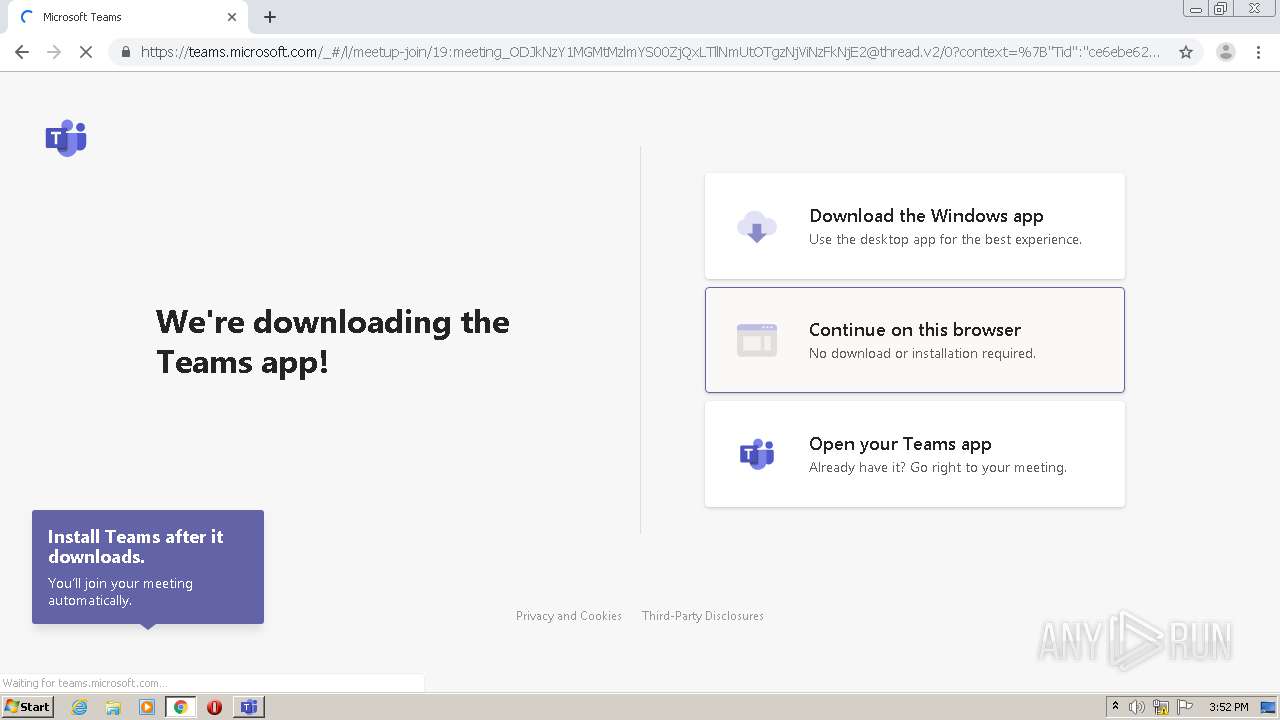
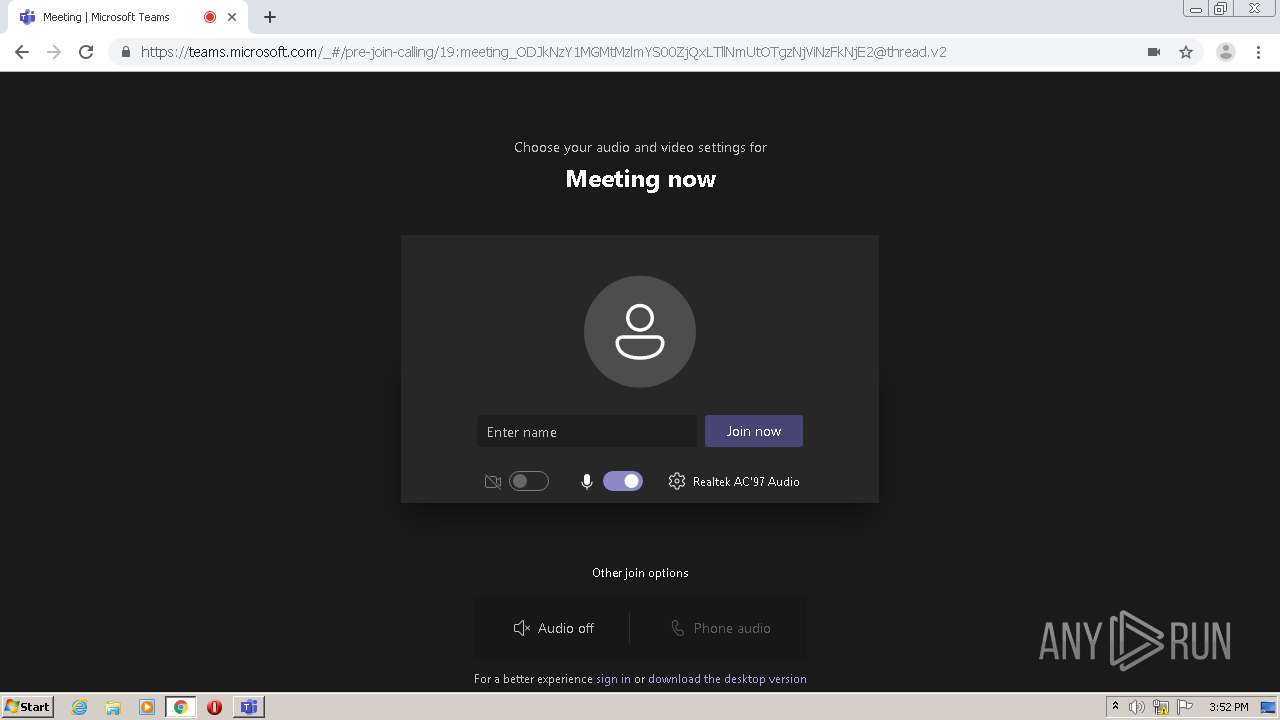
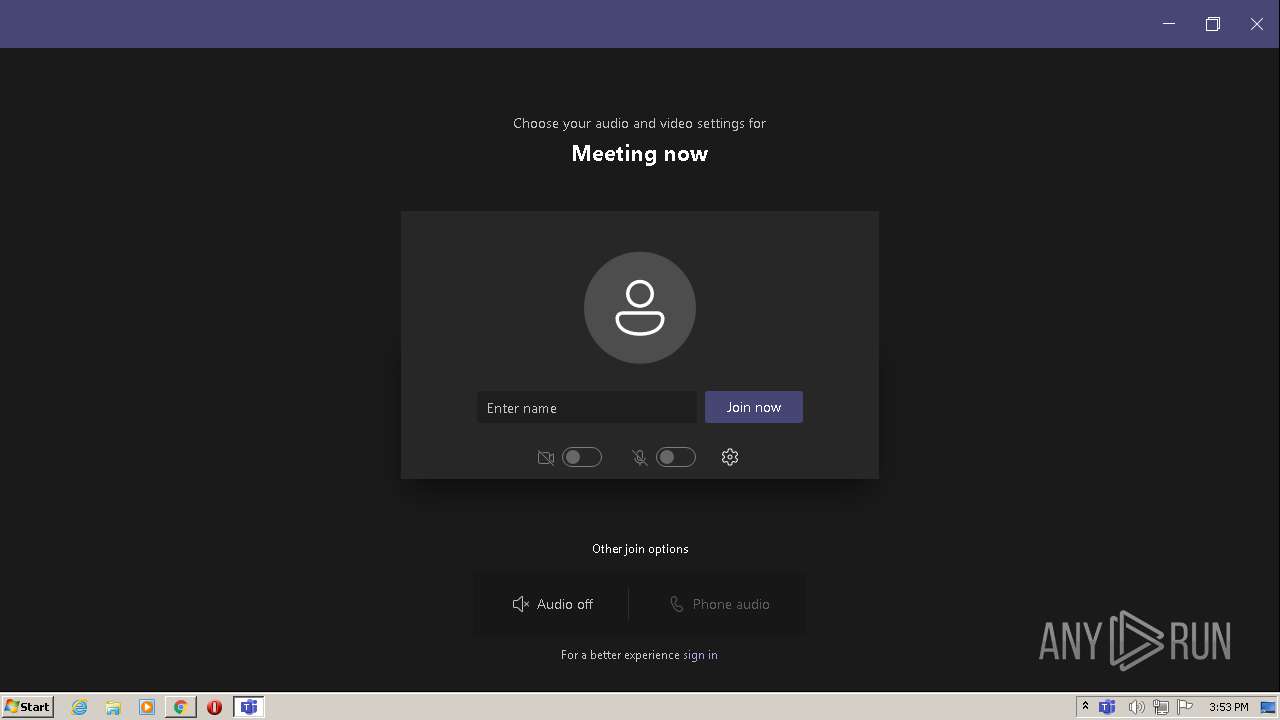
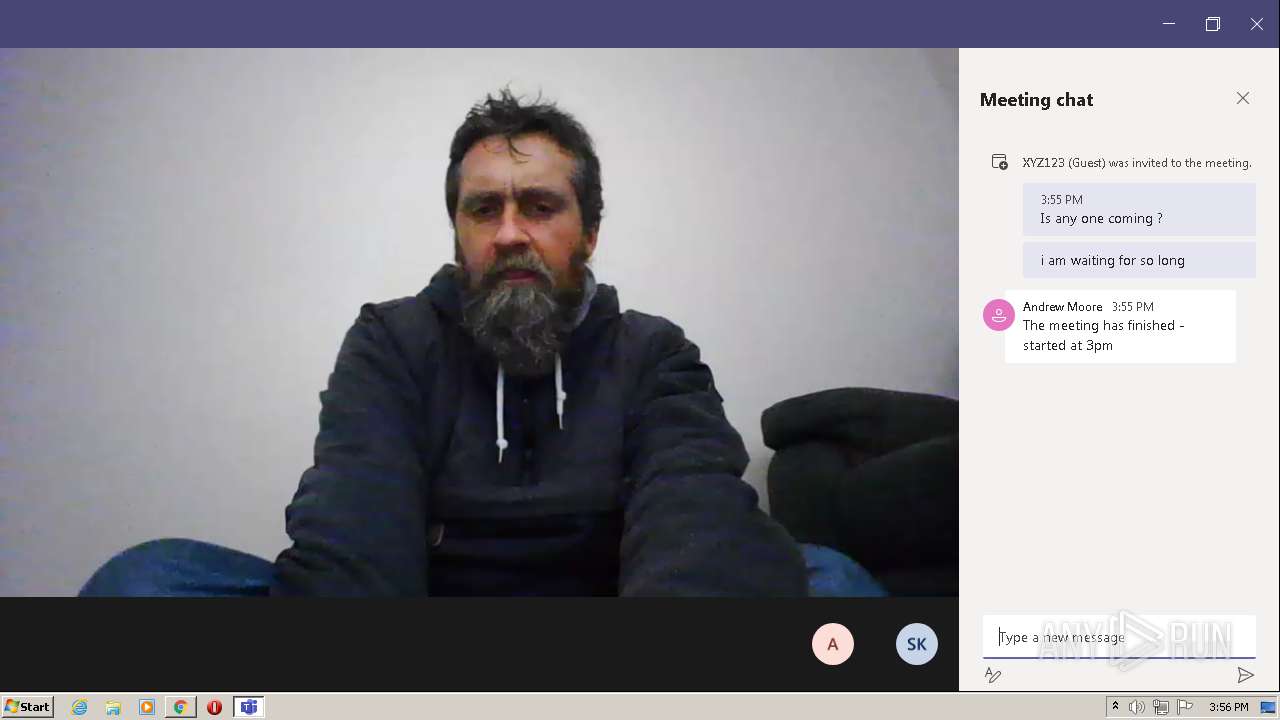
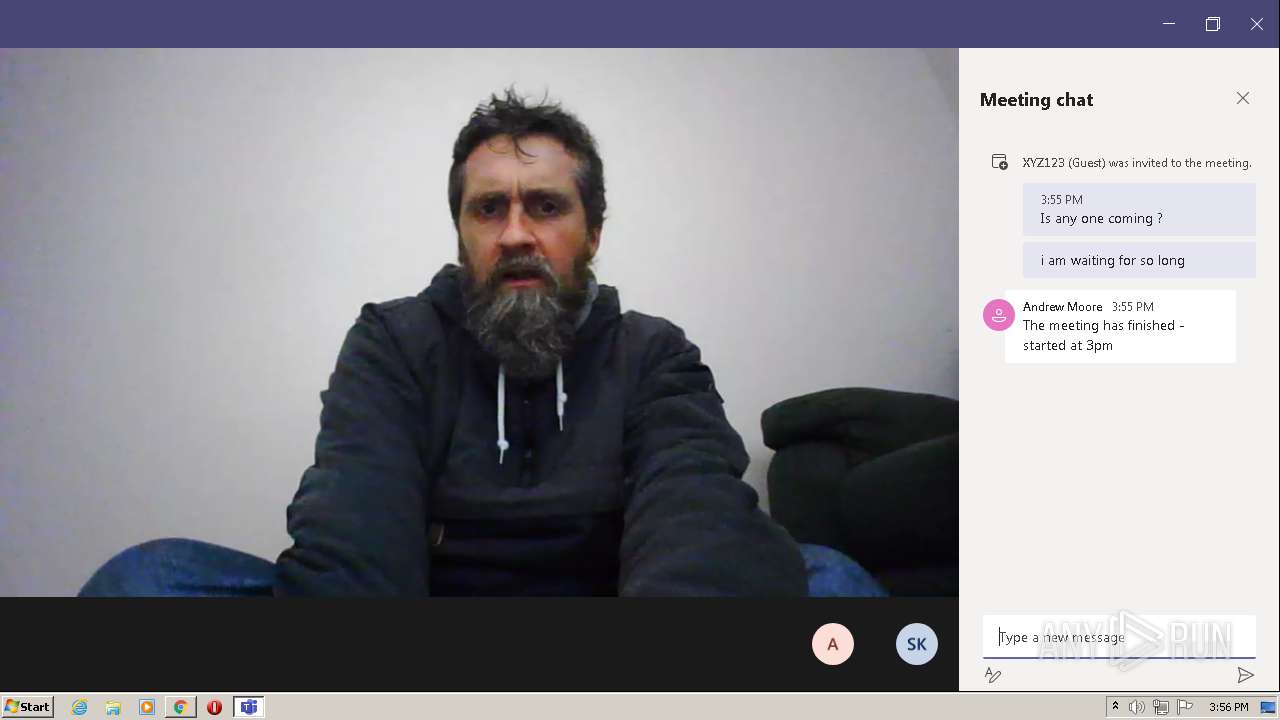
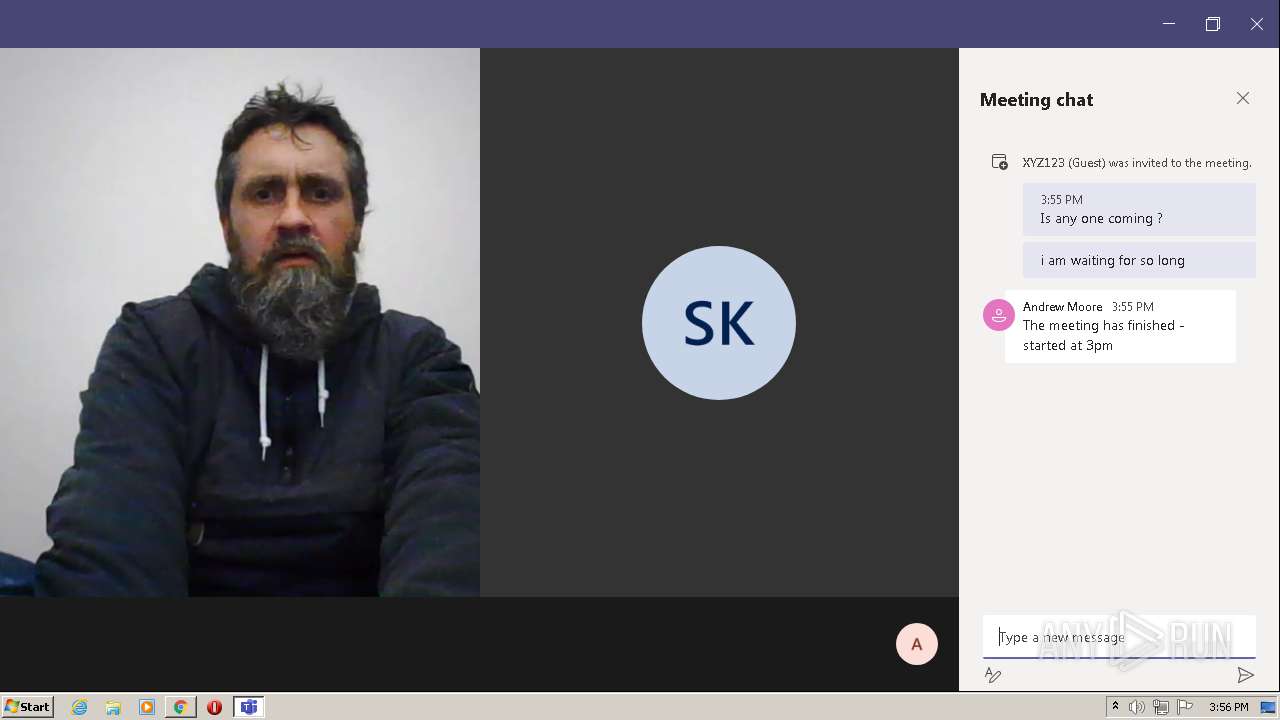
| URL: | https://teams.microsoft.com/l/meetup-join/19:meeting_ODJkNzY1MGMtMzlmYS00ZjQxLTllNmUtOTgzNjViNzFkNjE2@thread.v2/0?context=%7B%22Tid%22:%22ce6ebe62-557b-4436-a19c-767eca2cd451%22,%22Oid%22:%22892139bb-c14c-4f88-a5fb-b83ec59e3383%22%7D |
| Full analysis: | https://app.any.run/tasks/dbce03ce-cdbc-4c21-8608-83df780da73b |
| Verdict: | Malicious activity |
| Analysis date: | March 16, 2021, 15:50:40 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 793F0D61198FEB8158BFC2DE3D429CA9 |
| SHA1: | EFE92C0AD00CEBC3B8197B9302B598E2BD6E696C |
| SHA256: | 7EC8DA718AC0FE72DB0C92430448AF8F9E3A4E12F324CE80AE97A232F3BB5E5C |
| SSDEEP: | 6:2In+DEDrycfjCXMr+lRFAOyD0MoQUYSS57o9qNGU2+:2In+DEyuWXM2cOjMI87oOGU2+ |
MALICIOUS
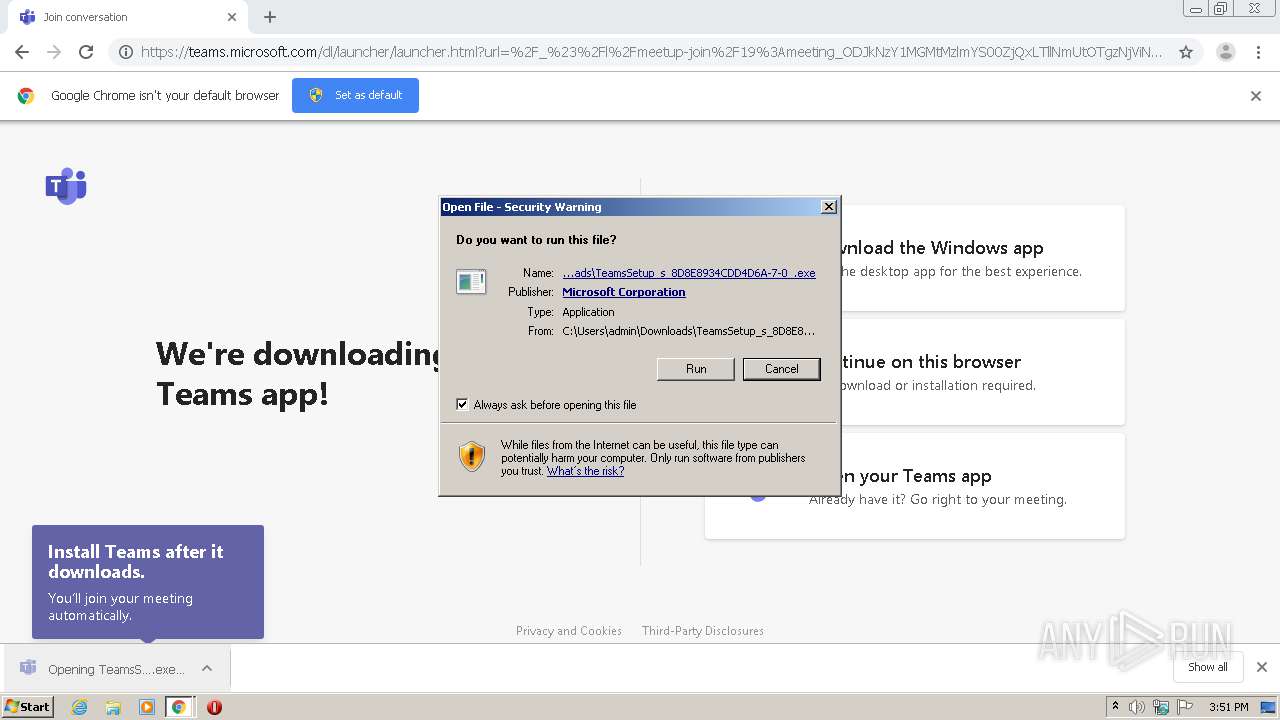
Application was dropped or rewritten from another process
- TeamsSetup_s_8D8E8934CDD4D6A-7-0_.exe (PID: 2564)
- Update.exe (PID: 2168)
- Squirrel.exe (PID: 1244)
- Update.exe (PID: 1832)
Loads dropped or rewritten executable
- Teams.exe (PID: 3204)
- Teams.exe (PID: 3148)
- Teams.exe (PID: 1796)
- Teams.exe (PID: 2976)
- Teams.exe (PID: 2744)
- Teams.exe (PID: 3924)
- Teams.exe (PID: 3136)
- Teams.exe (PID: 2144)
- regsvr32.exe (PID: 1452)
- Teams.exe (PID: 1328)
- Teams.exe (PID: 1964)
- Teams.exe (PID: 1628)
- Teams.exe (PID: 928)
- Teams.exe (PID: 2456)
- Teams.exe (PID: 1500)
- Teams.exe (PID: 3572)
- Teams.exe (PID: 3928)
Registers / Runs the DLL via REGSVR32.EXE
- Update.exe (PID: 2168)
Changes the autorun value in the registry
- Teams.exe (PID: 3924)
SUSPICIOUS
Executable content was dropped or overwritten
- chrome.exe (PID: 2344)
- TeamsSetup_s_8D8E8934CDD4D6A-7-0_.exe (PID: 2564)
- Update.exe (PID: 2168)
- Squirrel.exe (PID: 1244)
Drops a file that was compiled in debug mode
- chrome.exe (PID: 2344)
- Update.exe (PID: 2168)
Drops a file with a compile date too recent
- TeamsSetup_s_8D8E8934CDD4D6A-7-0_.exe (PID: 2564)
- chrome.exe (PID: 2344)
- Update.exe (PID: 2168)
- Squirrel.exe (PID: 1244)
Reads Environment values
- Update.exe (PID: 2168)
- Squirrel.exe (PID: 1244)
- Update.exe (PID: 1832)
- Teams.exe (PID: 3924)
Creates files in the user directory
- Update.exe (PID: 2168)
- Teams.exe (PID: 3204)
- Update.exe (PID: 1832)
- Teams.exe (PID: 3924)
- Teams.exe (PID: 3136)
- Teams.exe (PID: 1500)
- Teams.exe (PID: 3572)
Application launched itself
- Teams.exe (PID: 3204)
- Teams.exe (PID: 3924)
Reads CPU info
- Teams.exe (PID: 3204)
- Teams.exe (PID: 3924)
Drops a file with too old compile date
- Update.exe (PID: 2168)
Creates/Modifies COM task schedule object
- regsvr32.exe (PID: 1452)
Changes default file association
- Teams.exe (PID: 3924)
Creates a software uninstall entry
- Update.exe (PID: 2168)
INFO
Reads the hosts file
- chrome.exe (PID: 2668)
- chrome.exe (PID: 2344)
- Teams.exe (PID: 3204)
- Teams.exe (PID: 1796)
- Teams.exe (PID: 3924)
- Teams.exe (PID: 3136)
Application launched itself
- chrome.exe (PID: 2344)
Reads settings of System Certificates
- chrome.exe (PID: 2344)
- chrome.exe (PID: 2668)
- Teams.exe (PID: 3136)
- Squirrel.exe (PID: 1244)
- Teams.exe (PID: 1500)
Dropped object may contain Bitcoin addresses
- chrome.exe (PID: 2344)
Reads Microsoft Office registry keys
- Update.exe (PID: 2168)
- Update.exe (PID: 1832)
- Teams.exe (PID: 3924)
- Squirrel.exe (PID: 1244)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
75
Monitored processes
33
Malicious processes
13
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 928 | "C:\Users\admin\AppData\Local\Microsoft\Teams\current\Teams.exe" --type=renderer --no-sandbox --autoplay-policy=no-user-gesture-required --disable-background-timer-throttling --field-trial-handle=1092,15746368823688610453,6626166537806444277,131072 --enable-features=WebComponentsV0Enabled --disable-features=PictureInPicture,SpareRendererForSitePerProcess --lang=en-US --enable-wer --app-user-model-id=com.squirrel.Teams.Teams --app-path="C:\Users\admin\AppData\Local\Microsoft\Teams\current\resources\app.asar" --webview-tag --no-sandbox --no-zygote --native-window-open --preload="C:\Users\admin\AppData\Local\Microsoft\Teams\current\resources\app.asar\lib\renderer\preload.js" --background-color=#fff --enable-websql --electron-shared-settings=eyJjci5jb21wYW55IjoiRWxlY3Ryb24iLCJjci5kdW1wcyI6IiIsImNyLmVuYWJsZWQiOmZhbHNlLCJjci5wcm9kdWN0IjoiRWxlY3Ryb24iLCJjci5zZXNzaW9uIjoiIiwiY3IudXJsIjoiIiwiY3IudmVyc2lvbiI6IiJ9 --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=11 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2176 /prefetch:1 --msteams-process-type=mainWindow | C:\Users\admin\AppData\Local\Microsoft\Teams\current\Teams.exe | — | Teams.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Teams Exit code: 0 Version: 1.4.00.4167 Modules
| |||||||||||||||
| 972 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1040,10789544343577295578,11386743438726822229,131072 --enable-features=PasswordImport --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=10570954954188649975 --renderer-client-id=5 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2180 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1244 | "C:\Users\admin\AppData\Local\Microsoft\Teams\current\Squirrel.exe" --updateSelf=C:\Users\admin\AppData\Local\SquirrelTemp\Update.exe | C:\Users\admin\AppData\Local\Microsoft\Teams\current\Squirrel.exe | Update.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Teams Exit code: 0 Version: 1.10.56.0 Modules
| |||||||||||||||
| 1328 | "C:\Users\admin\AppData\Local\Microsoft\Teams\current\Teams.exe" --type=renderer --no-sandbox --autoplay-policy=no-user-gesture-required --disable-background-timer-throttling --field-trial-handle=1092,15746368823688610453,6626166537806444277,131072 --enable-features=WebComponentsV0Enabled --disable-features=PictureInPicture,SpareRendererForSitePerProcess --lang=en-US --enable-wer --app-user-model-id=com.squirrel.Teams.Teams --app-path="C:\Users\admin\AppData\Local\Microsoft\Teams\current\resources\app.asar" --no-sandbox --no-zygote --preload="C:\Users\admin\AppData\Local\Microsoft\Teams\current\resources\app.asar\lib\renderer\notifications\preload_notifications.js" --background-color=#fff --enable-websql --electron-shared-settings=eyJjci5jb21wYW55IjoiRWxlY3Ryb24iLCJjci5kdW1wcyI6IiIsImNyLmVuYWJsZWQiOmZhbHNlLCJjci5wcm9kdWN0IjoiRWxlY3Ryb24iLCJjci5zZXNzaW9uIjoiIiwiY3IudXJsIjoiIiwiY3IudmVyc2lvbiI6IiJ9 --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=9 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=1952 /prefetch:1 --msteams-process-type=notificationsManager | C:\Users\admin\AppData\Local\Microsoft\Teams\current\Teams.exe | — | Teams.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Teams Exit code: 0 Version: 1.4.00.4167 Modules
| |||||||||||||||
| 1452 | "C:\Windows\system32\regsvr32.exe" /s /n /i:user "C:\Users\admin\AppData\Local\Microsoft\TeamsMeetingAddin\1.0.20289.5\x86\Microsoft.Teams.AddinLoader.dll" | C:\Windows\system32\regsvr32.exe | — | Update.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft(C) Register Server Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1500 | "C:\Users\admin\AppData\Local\Microsoft\Teams\current\Teams.exe" --type=renderer --no-sandbox --autoplay-policy=no-user-gesture-required --disable-background-timer-throttling --field-trial-handle=1092,15746368823688610453,6626166537806444277,131072 --enable-features=WebComponentsV0Enabled --disable-features=PictureInPicture,SpareRendererForSitePerProcess --disable-gpu-compositing --lang=en-US --enable-wer --app-user-model-id=com.squirrel.Teams.Teams --app-path="C:\Users\admin\AppData\Local\Microsoft\Teams\current\resources\app.asar" --no-sandbox --no-zygote --preload="C:\Users\admin\AppData\Local\Microsoft\Teams\current\resources\app.asar\lib\pluginhost\preload.js" --background-color=#fff --enable-websql --electron-shared-settings=eyJjci5jb21wYW55IjoiRWxlY3Ryb24iLCJjci5kdW1wcyI6IiIsImNyLmVuYWJsZWQiOmZhbHNlLCJjci5wcm9kdWN0IjoiRWxlY3Ryb24iLCJjci5zZXNzaW9uIjoiIiwiY3IudXJsIjoiIiwiY3IudmVyc2lvbiI6IiJ9 --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=14 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2328 /prefetch:1 --msteams-process-type=pluginHost | C:\Users\admin\AppData\Local\Microsoft\Teams\current\Teams.exe | Teams.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Teams Exit code: 0 Version: 1.4.00.4167 Modules
| |||||||||||||||
| 1628 | "C:\Users\admin\AppData\Local\Microsoft\Teams\current\Teams.exe" --type=gpu-process --field-trial-handle=1092,15746368823688610453,6626166537806444277,131072 --enable-features=WebComponentsV0Enabled --disable-features=PictureInPicture,SpareRendererForSitePerProcess --no-sandbox --electron-shared-settings=eyJjci5jb21wYW55IjoiRWxlY3Ryb24iLCJjci5kdW1wcyI6IiIsImNyLmVuYWJsZWQiOmZhbHNlLCJjci5wcm9kdWN0IjoiRWxlY3Ryb24iLCJjci5zZXNzaW9uIjoiIiwiY3IudXJsIjoiIiwiY3IudmVyc2lvbiI6IiJ9 --gpu-preferences=KAAAAAAAAADgAAAwAAAAAAAAYAAAAAAAEAAAAAAAAAAAAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --mojo-platform-channel-handle=1132 /prefetch:2 | C:\Users\admin\AppData\Local\Microsoft\Teams\current\Teams.exe | — | Teams.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Teams Exit code: 0 Version: 1.4.00.4167 Modules
| |||||||||||||||
| 1796 | "C:\Users\admin\AppData\Local\Microsoft\Teams\current\Teams.exe" --type=utility --field-trial-handle=1156,1579168235630819793,6665784087651325488,131072 --enable-features=WebComponentsV0Enabled --disable-features=PictureInPicture,SpareRendererForSitePerProcess --lang=en-US --service-sandbox-type=network --electron-shared-settings=eyJjci5jb21wYW55IjoiRWxlY3Ryb24iLCJjci5kdW1wcyI6IiIsImNyLmVuYWJsZWQiOmZhbHNlLCJjci5wcm9kdWN0IjoiRWxlY3Ryb24iLCJjci5zZXNzaW9uIjoiIiwiY3IudXJsIjoiIiwiY3IudmVyc2lvbiI6IiJ9 --mojo-platform-channel-handle=1704 /prefetch:8 | C:\Users\admin\AppData\Local\Microsoft\Teams\current\Teams.exe | — | Teams.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Teams Exit code: 0 Version: 1.4.00.4167 Modules
| |||||||||||||||
| 1832 | C:\Users\admin\AppData\Local\Microsoft\Teams\Update.exe --createShortcut=Teams.exe -l=StartMenu,Desktop | C:\Users\admin\AppData\Local\Microsoft\Teams\Update.exe | Teams.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Teams Exit code: 0 Version: 1.10.56.0 Modules
| |||||||||||||||
| 1964 | "C:\Users\admin\AppData\Local\Microsoft\Teams\current\Teams.exe" --type=gpu-process --field-trial-handle=1092,15746368823688610453,6626166537806444277,131072 --enable-features=WebComponentsV0Enabled --disable-features=PictureInPicture,SpareRendererForSitePerProcess --no-sandbox --electron-shared-settings=eyJjci5jb21wYW55IjoiRWxlY3Ryb24iLCJjci5kdW1wcyI6IiIsImNyLmVuYWJsZWQiOmZhbHNlLCJjci5wcm9kdWN0IjoiRWxlY3Ryb24iLCJjci5zZXNzaW9uIjoiIiwiY3IudXJsIjoiIiwiY3IudmVyc2lvbiI6IiJ9 --gpu-preferences=KAAAAAAAAADgAAAwAAAAAAAAYAAAAAAAEAAAAAAAAAAAAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --mojo-platform-channel-handle=1132 /prefetch:2 | C:\Users\admin\AppData\Local\Microsoft\Teams\current\Teams.exe | — | Teams.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Teams Exit code: 0 Version: 1.4.00.4167 Modules
| |||||||||||||||
Total events
5 398
Read events
5 066
Write events
329
Delete events
3
Modification events
| (PID) Process: | (2344) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (2344) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (2344) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (2344) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (2852) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 2344-13260383466927625 |
Value: 259 | |||
| (PID) Process: | (2344) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (2344) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (2344) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (2344) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 3252-13245750958665039 |
Value: 0 | |||
| (PID) Process: | (2344) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
Executable files
493
Suspicious files
90
Text files
449
Unknown types
73
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2344 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\BrowserMetrics\BrowserMetrics-6050D3EB-928.pma | — | |
MD5:— | SHA256:— | |||
| 2344 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2344 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\92128fd6-251e-4aef-974f-4e3ae30d77a9.tmp | — | |
MD5:— | SHA256:— | |||
| 2344 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000048.dbtmp | — | |
MD5:— | SHA256:— | |||
| 2344 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Session Storage\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2344 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2344 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old~RF12d21d.TMP | text | |
MD5:— | SHA256:— | |||
| 2344 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old~RF12d23c.TMP | text | |
MD5:— | SHA256:— | |||
| 2344 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2344 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old~RF12d559.TMP | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
124
DNS requests
75
Threats
46
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2668 | chrome.exe | 52.113.194.132:443 | teams.microsoft.com | Microsoft Corporation | US | suspicious |
2668 | chrome.exe | 142.250.186.173:443 | accounts.google.com | Google Inc. | US | suspicious |
2668 | chrome.exe | 142.250.186.74:443 | safebrowsing.googleapis.com | Google Inc. | US | whitelisted |
2668 | chrome.exe | 152.199.19.160:443 | az725175.vo.msecnd.net | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
2668 | chrome.exe | 138.91.136.108:443 | browser.pipe.aria.microsoft.com | Microsoft Corporation | US | unknown |
2668 | chrome.exe | 2.20.143.23:443 | statics.teams.cdn.office.net | Akamai International B.V. | — | unknown |
2668 | chrome.exe | 40.77.226.250:443 | web.vortex.data.microsoft.com | Microsoft Corporation | IE | whitelisted |
2668 | chrome.exe | 216.58.212.131:443 | ssl.gstatic.com | Google Inc. | US | whitelisted |
2168 | Update.exe | 52.113.194.132:443 | teams.microsoft.com | Microsoft Corporation | US | suspicious |
2168 | Update.exe | 52.114.128.43:443 | mobile.pipe.aria.microsoft.com | Microsoft Corporation | US | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
teams.microsoft.com |
| whitelisted |
accounts.google.com |
| shared |
statics.teams.microsoft.com |
| whitelisted |
safebrowsing.googleapis.com |
| whitelisted |
statics.teams.cdn.office.net |
| whitelisted |
az725175.vo.msecnd.net |
| whitelisted |
browser.pipe.aria.microsoft.com |
| whitelisted |
web.vortex.data.microsoft.com |
| whitelisted |
ssl.gstatic.com |
| whitelisted |
mobile.pipe.aria.microsoft.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2668 | chrome.exe | Attempted User Privilege Gain | ET INFO Session Traversal Utilities for NAT (STUN Binding Request) |
2668 | chrome.exe | Attempted User Privilege Gain | ET INFO Session Traversal Utilities for NAT (STUN Binding Response) |
2668 | chrome.exe | Attempted User Privilege Gain | ET INFO Session Traversal Utilities for NAT (STUN Binding Request) |
2668 | chrome.exe | Attempted User Privilege Gain | ET INFO Session Traversal Utilities for NAT (STUN Binding Response) |
— | — | Attempted User Privilege Gain | ET INFO Session Traversal Utilities for NAT (STUN Binding Request) |
— | — | Attempted User Privilege Gain | ET INFO Session Traversal Utilities for NAT (STUN Binding Response) |
— | — | Attempted User Privilege Gain | ET INFO Session Traversal Utilities for NAT (STUN Binding Request) |
— | — | Attempted User Privilege Gain | ET INFO Session Traversal Utilities for NAT (STUN Binding Response) |
— | — | Attempted User Privilege Gain | ET INFO Session Traversal Utilities for NAT (STUN Binding Request) |
— | — | Attempted User Privilege Gain | ET INFO Session Traversal Utilities for NAT (STUN Binding Response) |
Process | Message |
|---|---|
Update.exe | Update.exe Information: 0 : |
Update.exe | Starting TelemetryManager constructor
|
Update.exe | Update.exe Information: 0 : |
Update.exe | TelemetryManagerImpl creation started
|
Update.exe | Update.exe Information: 0 : |
Update.exe | Performance counters are disabled. Skipping creation of counters category.
|
Update.exe | Update.exe Information: 0 : |
Update.exe | RecordBatcherTask with ID 4 started.
|
Update.exe | DataPackageSender with UserAgent name: AST-exe-C#, version: 1.10.56.0, [Ast_Default_Source]
|
Update.exe | DataPackageSender with UserAgent name: AST-exe-C#, version: 1.10.56.0, [Ast_Default_Source]
|