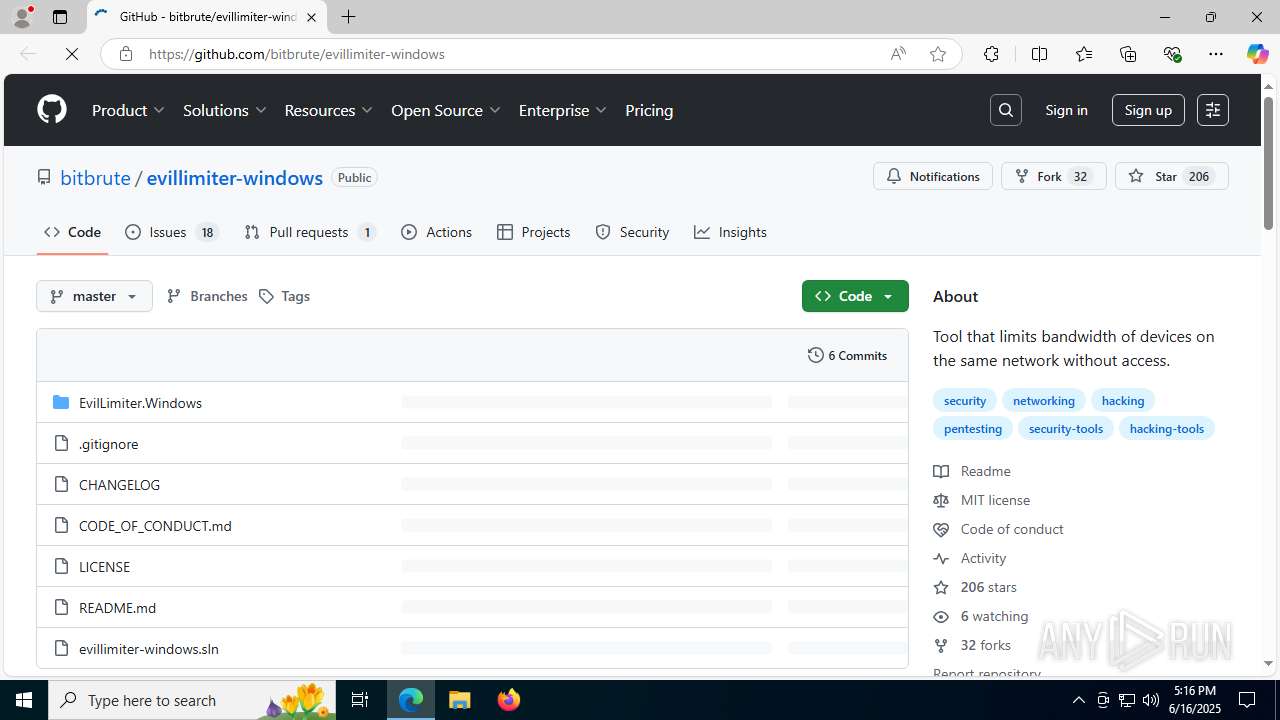
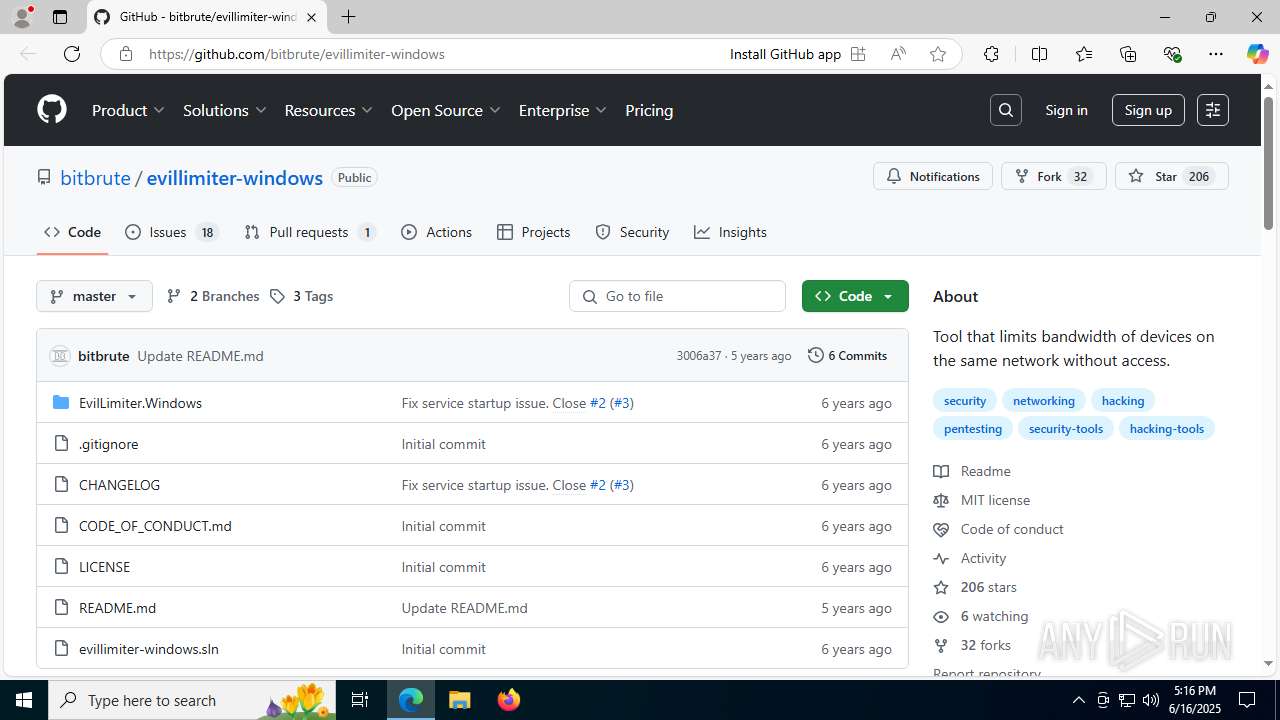
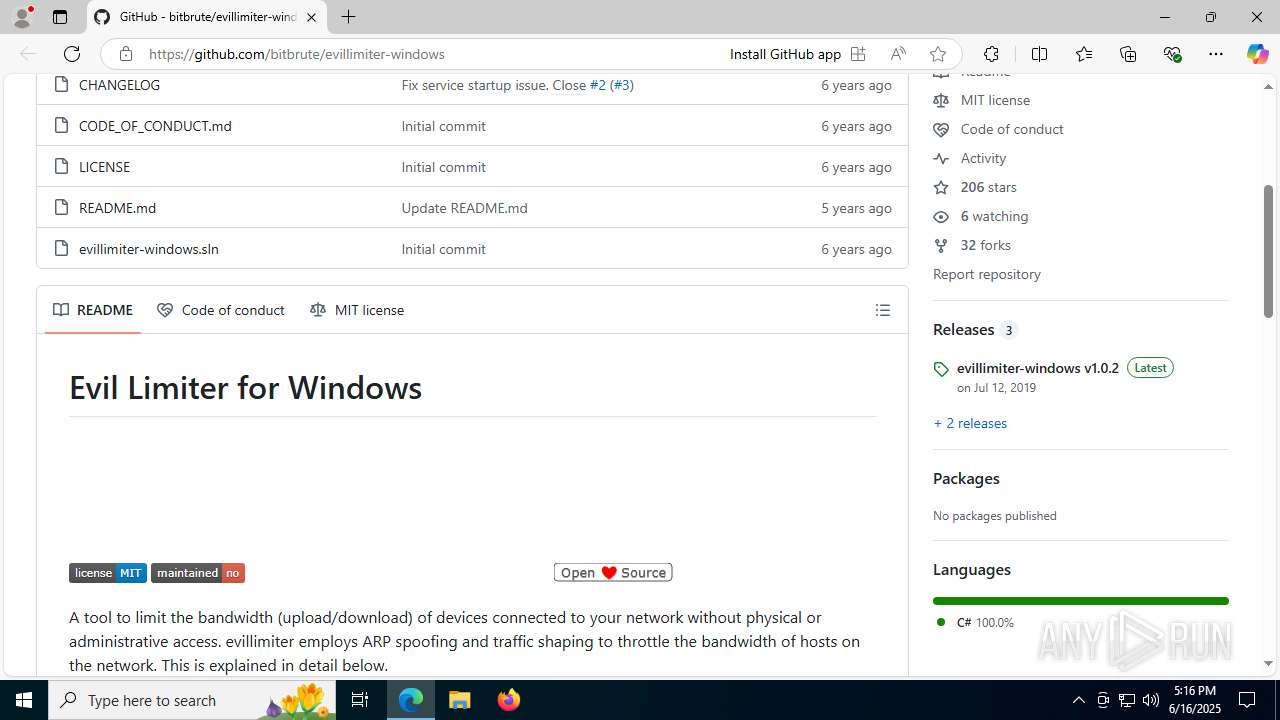
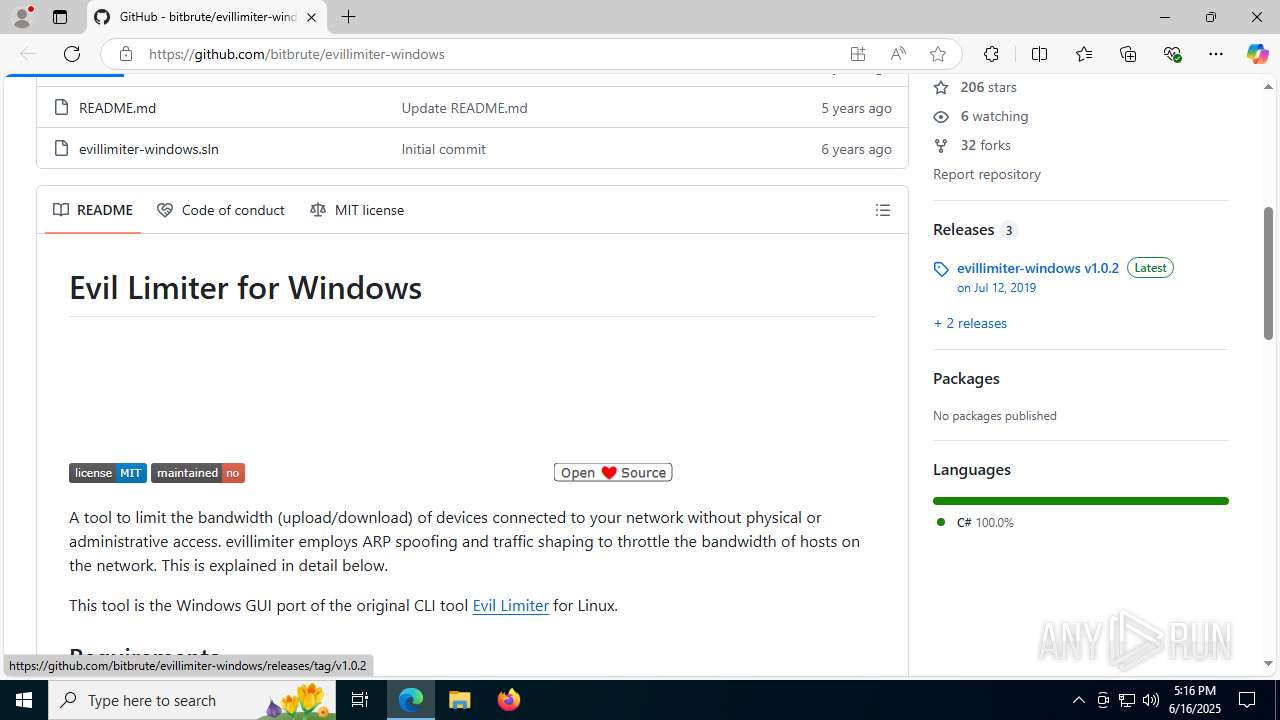
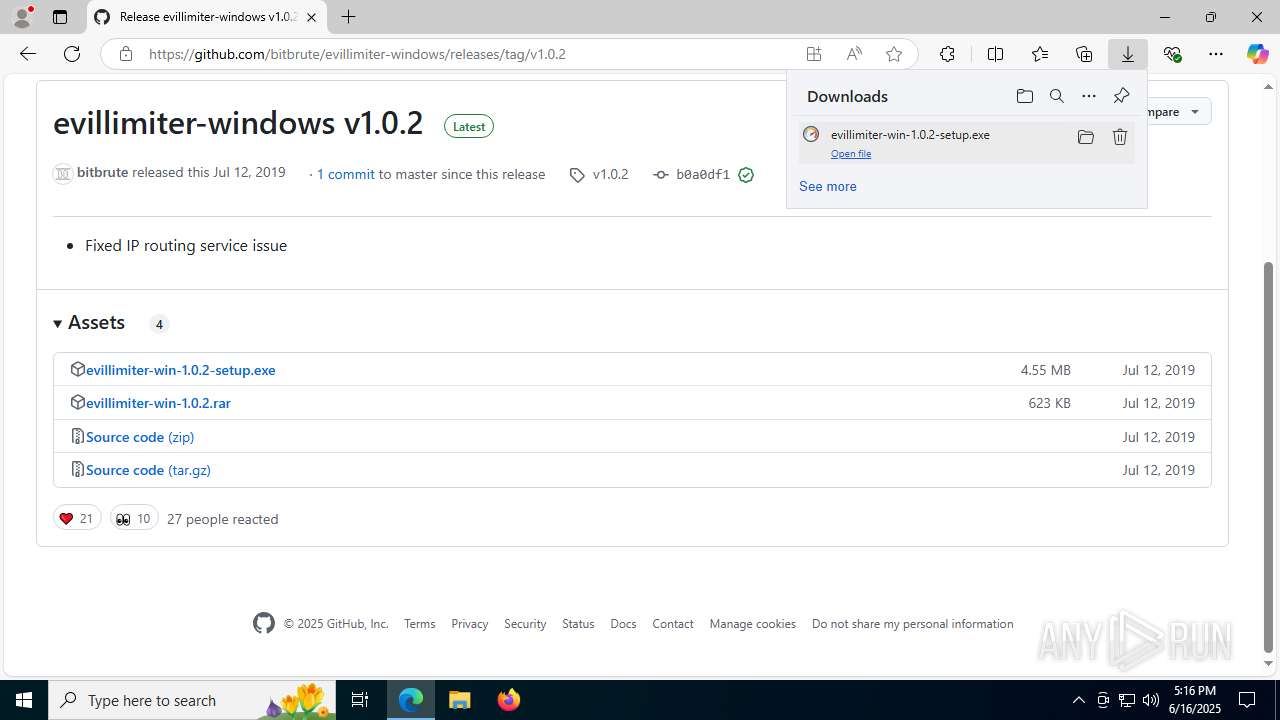
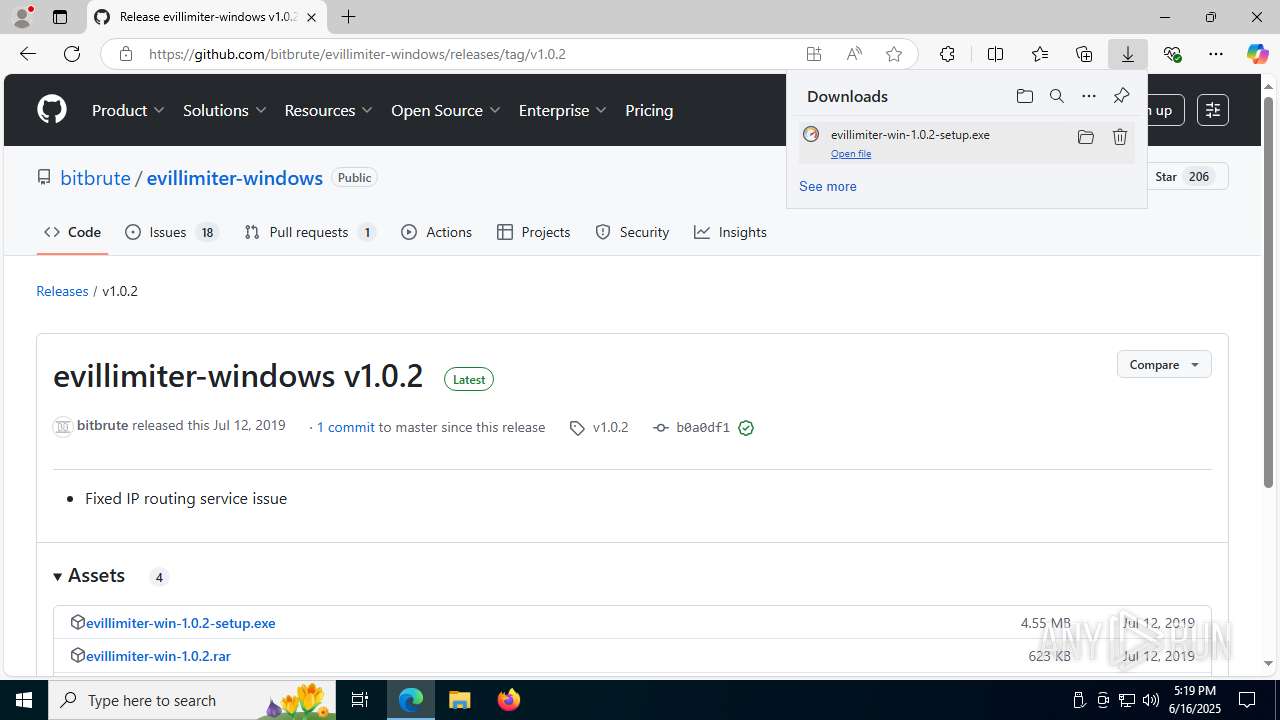
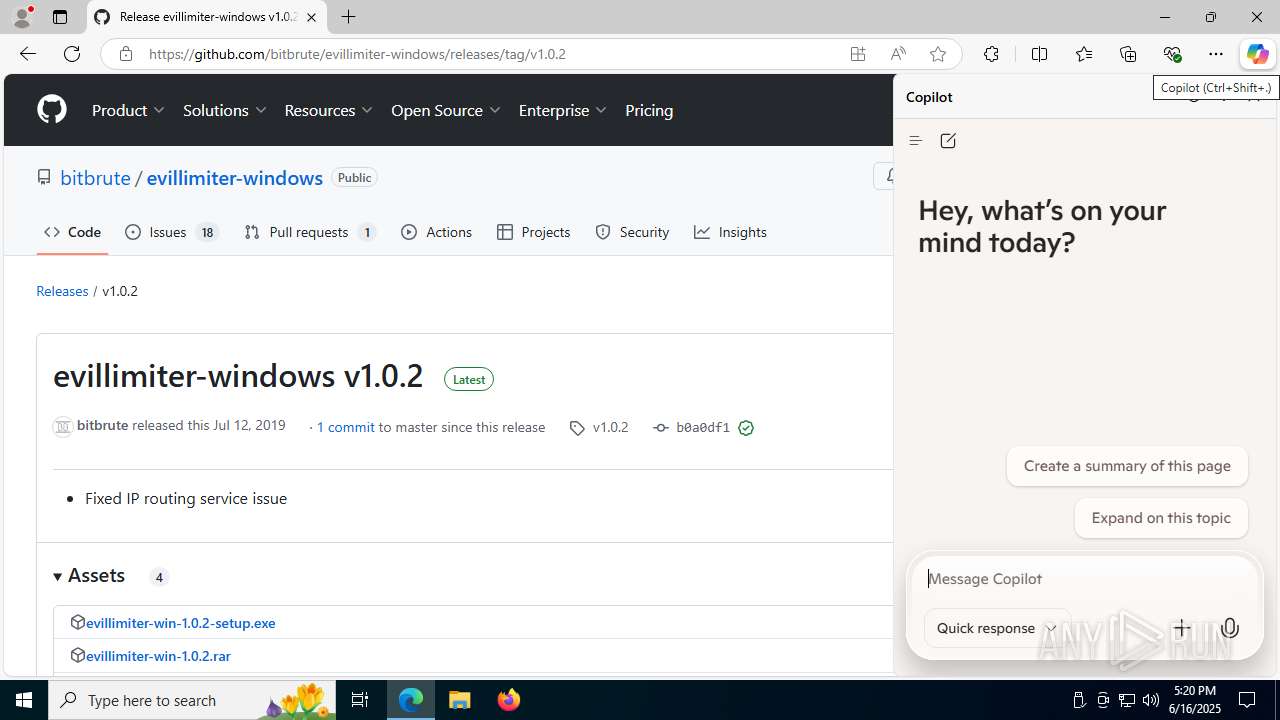
| URL: | https://github.com/bitbrute/evillimiter-windows |
| Full analysis: | https://app.any.run/tasks/9477db06-bc35-43f7-a1ff-fde1b0b62efc |
| Verdict: | Malicious activity |
| Analysis date: | June 16, 2025, 17:16:30 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MD5: | A7488E2BA22FA62D1D182FB3311ACE74 |
| SHA1: | 672A2E9EDA99AE8C11A4CC802897771C187AD166 |
| SHA256: | 7EC781E9D745E59213BF7D53AE633D631E920CED54C293F89400688CCF185734 |
| SSDEEP: | 3:N8tEd3QgmKrJ4RAXyKSW:2uagmKd4gyKSW |
MALICIOUS
Uses Task Scheduler to run other applications
- npcap-0.996.exe (PID: 7484)
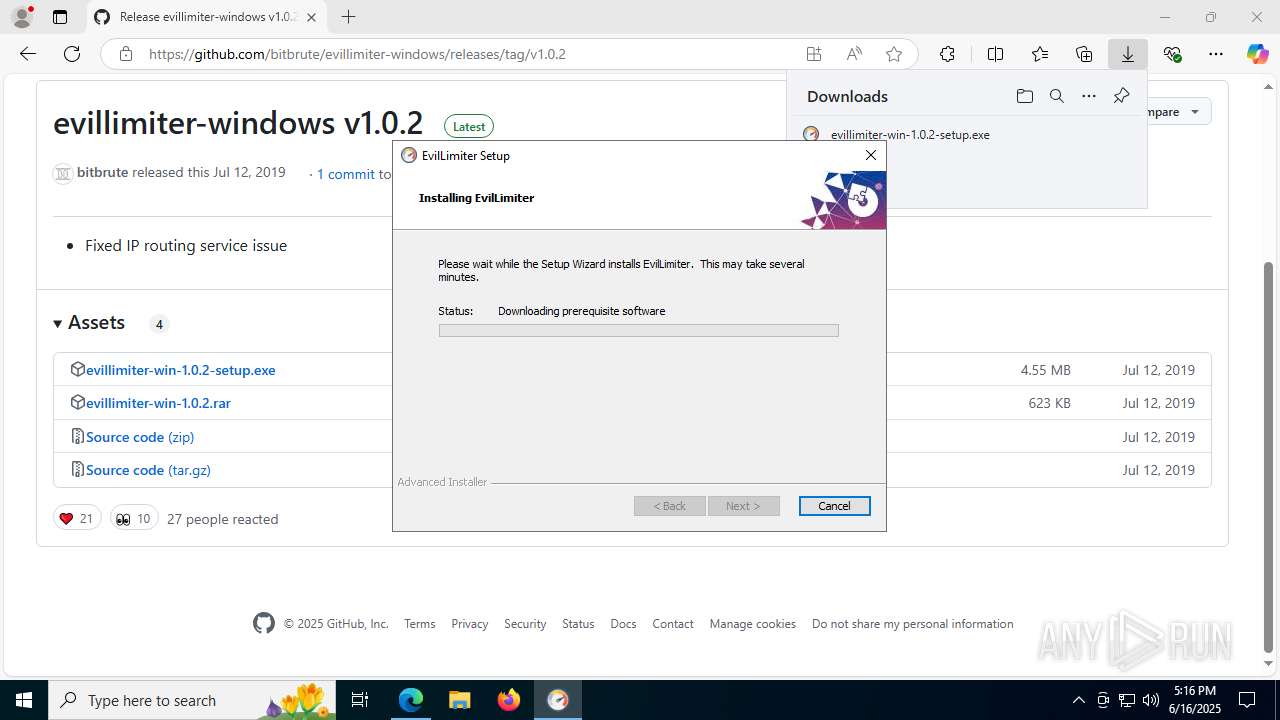
SUSPICIOUS
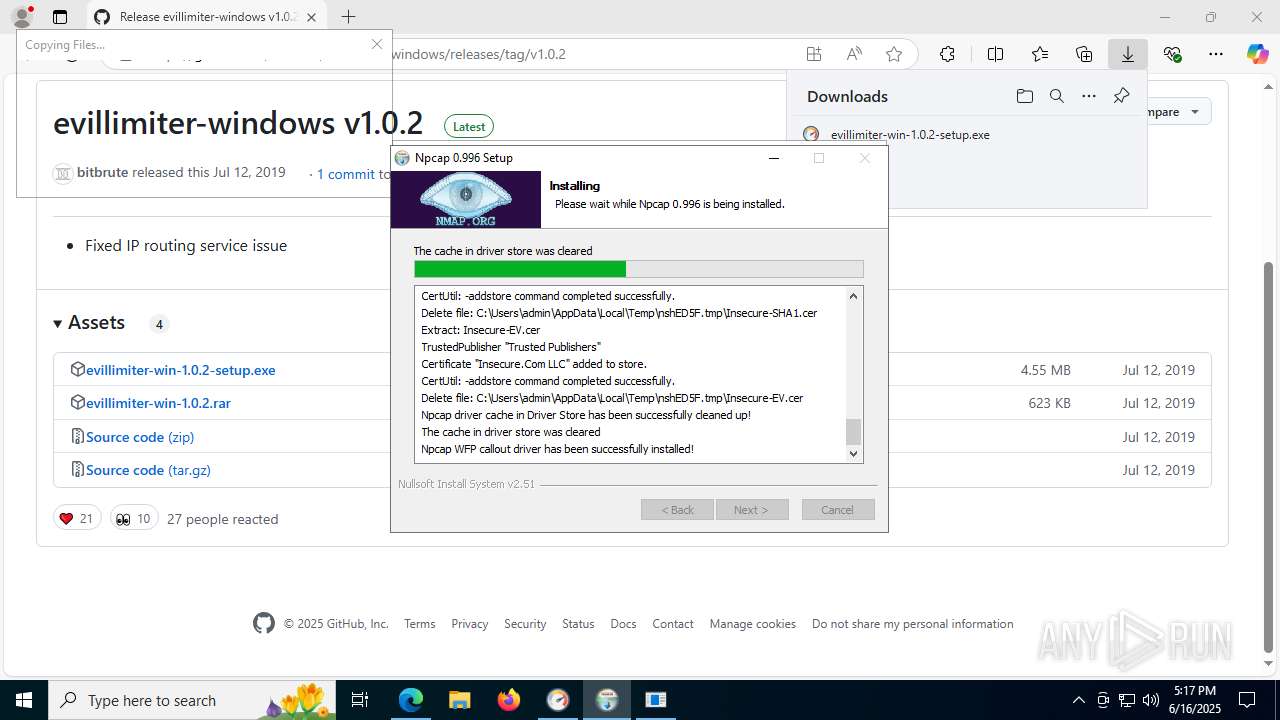
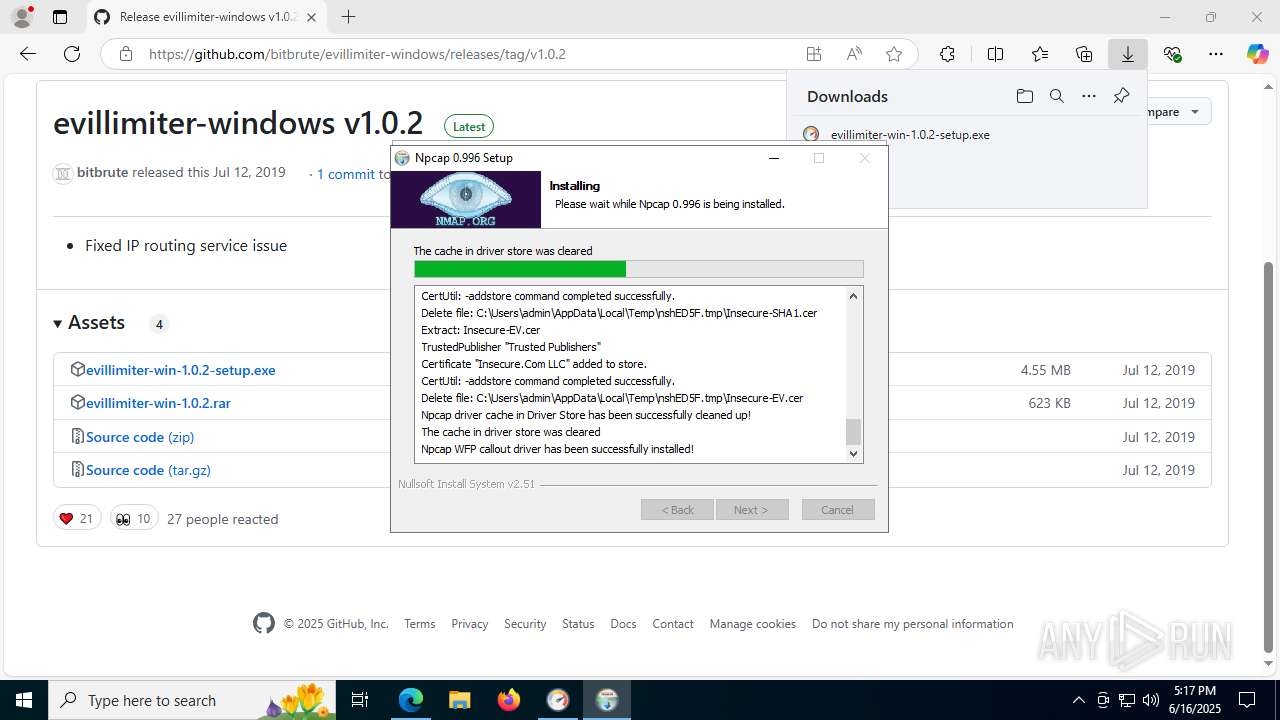
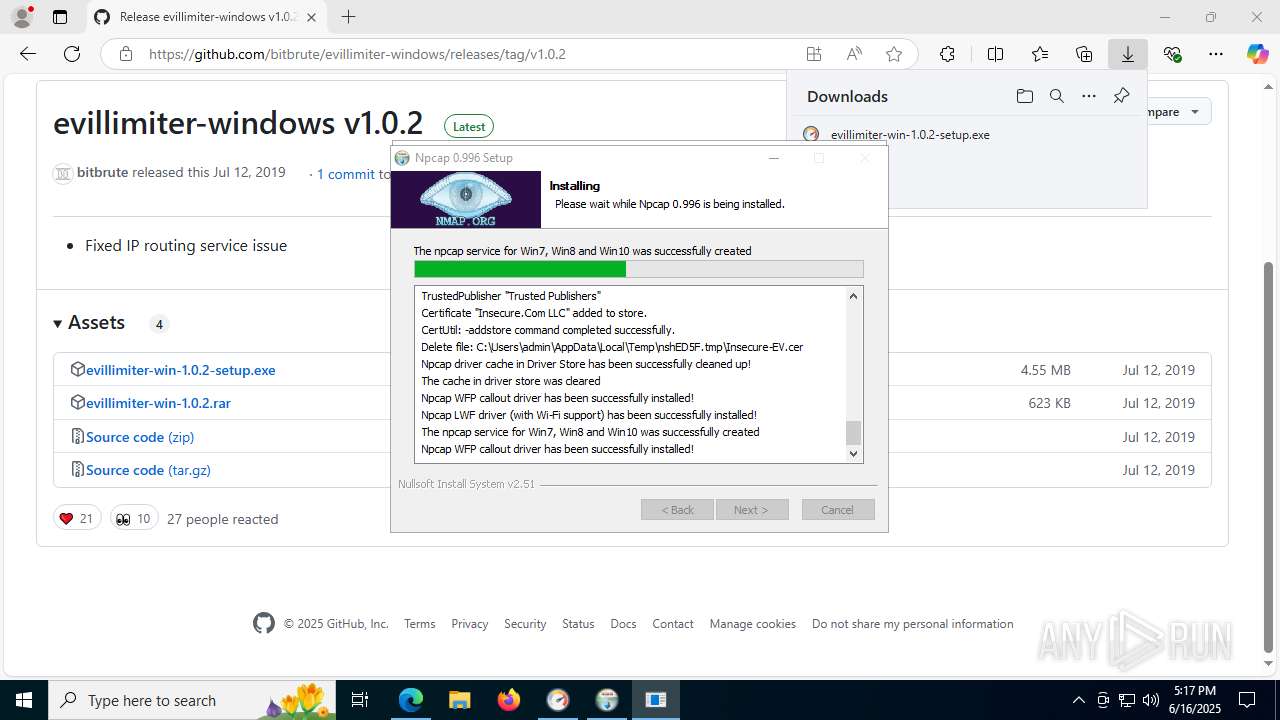
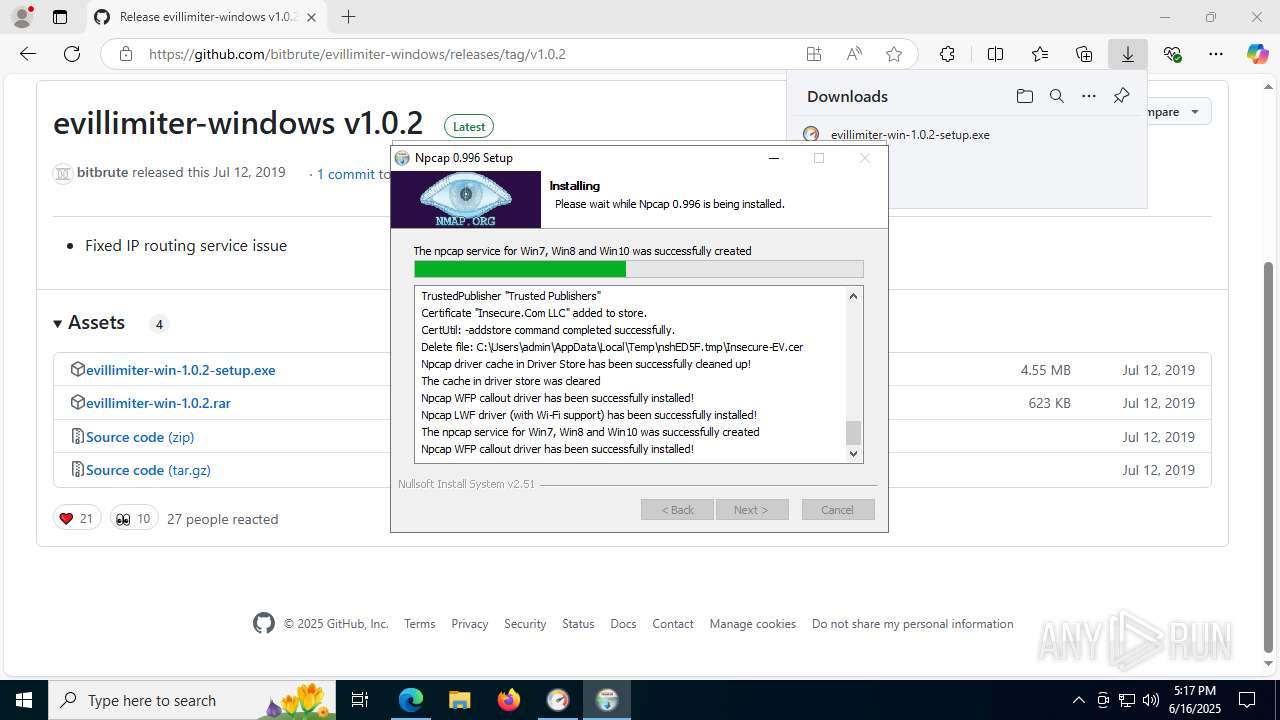
Executable content was dropped or overwritten
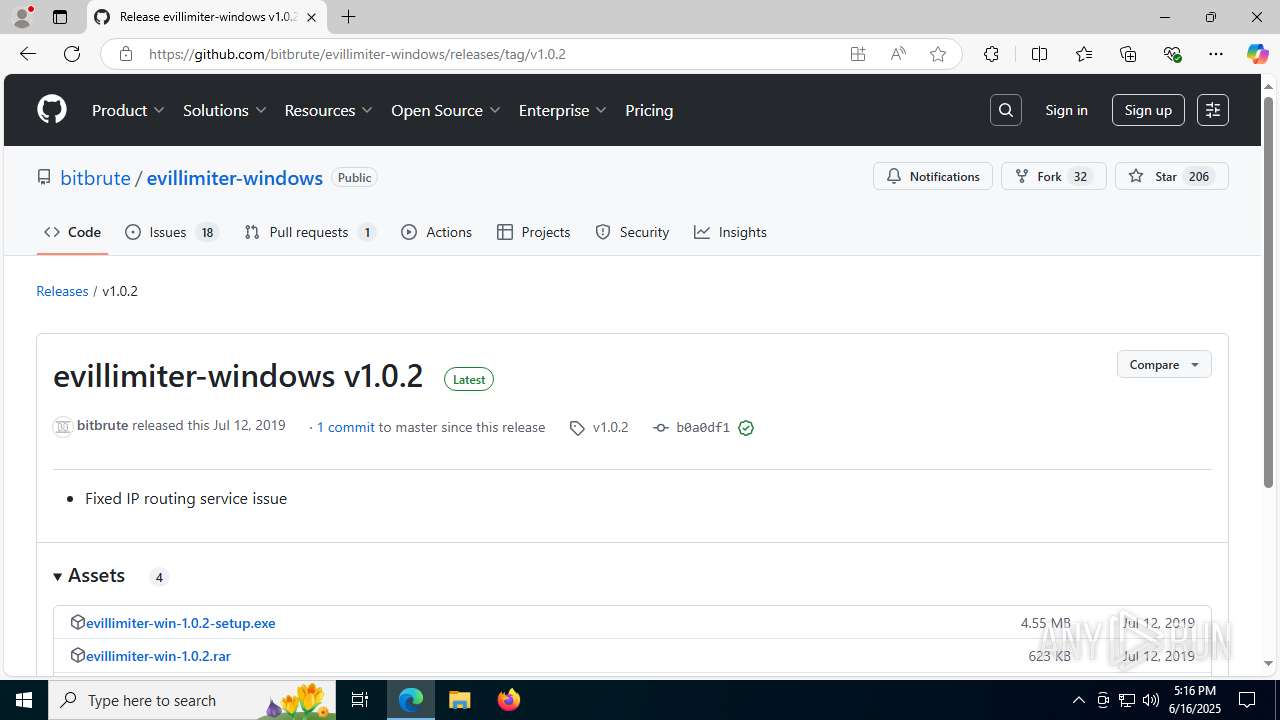
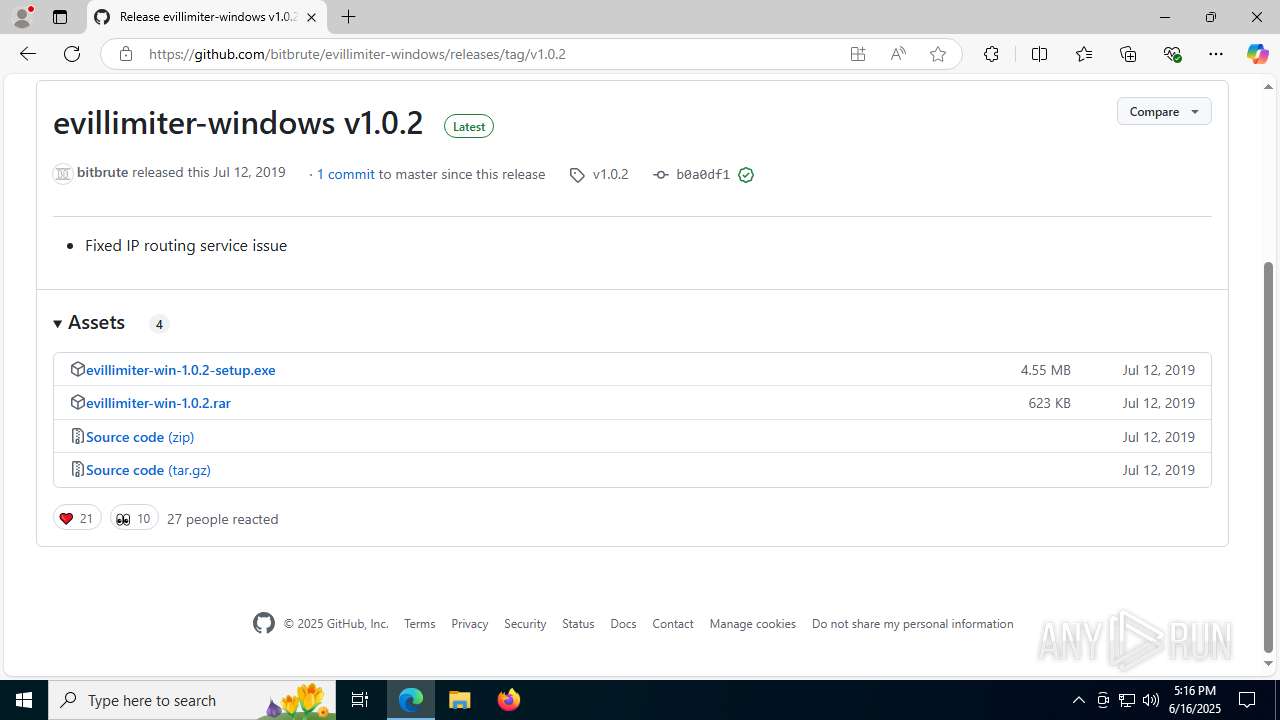
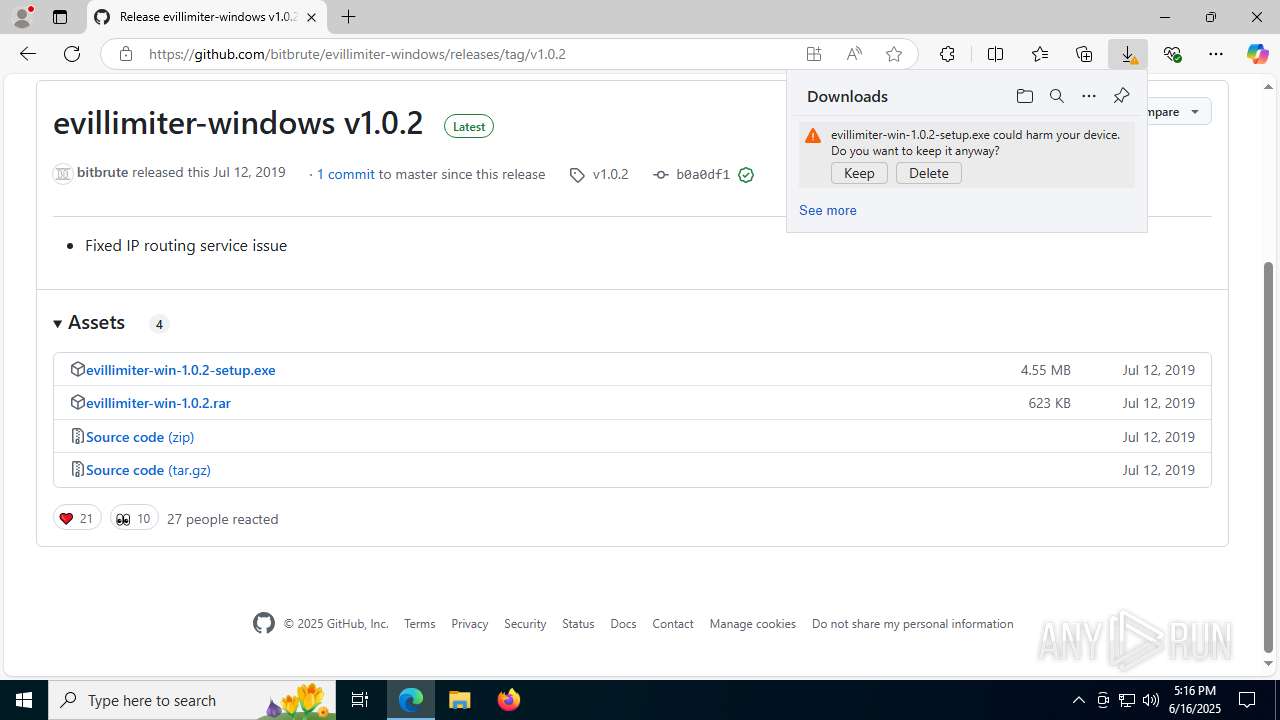
- evillimiter-win-1.0.2-setup.exe (PID: 8076)
- evillimiter-win-1.0.2-setup.exe (PID: 7988)
- npcap-0.996.exe (PID: 7484)
- NPFInstall.exe (PID: 7960)
- drvinst.exe (PID: 7236)
- NPFInstall2.exe (PID: 6528)
- drvinst.exe (PID: 7564)
Process drops legitimate windows executable
- evillimiter-win-1.0.2-setup.exe (PID: 8076)
- evillimiter-win-1.0.2-setup.exe (PID: 7988)
Reads the Windows owner or organization settings
- evillimiter-win-1.0.2-setup.exe (PID: 8076)
- evillimiter-win-1.0.2-setup.exe (PID: 7988)
Reads security settings of Internet Explorer
- msiexec.exe (PID: 8180)
- evillimiter-win-1.0.2-setup.exe (PID: 8076)
- evillimiter-win-1.0.2-setup.exe (PID: 7988)
Application launched itself
- evillimiter-win-1.0.2-setup.exe (PID: 8076)
- cmd.exe (PID: 7820)
- cmd.exe (PID: 7264)
Executes as Windows Service
- VSSVC.exe (PID: 7964)
There is functionality for taking screenshot (YARA)
- evillimiter-win-1.0.2-setup.exe (PID: 8076)
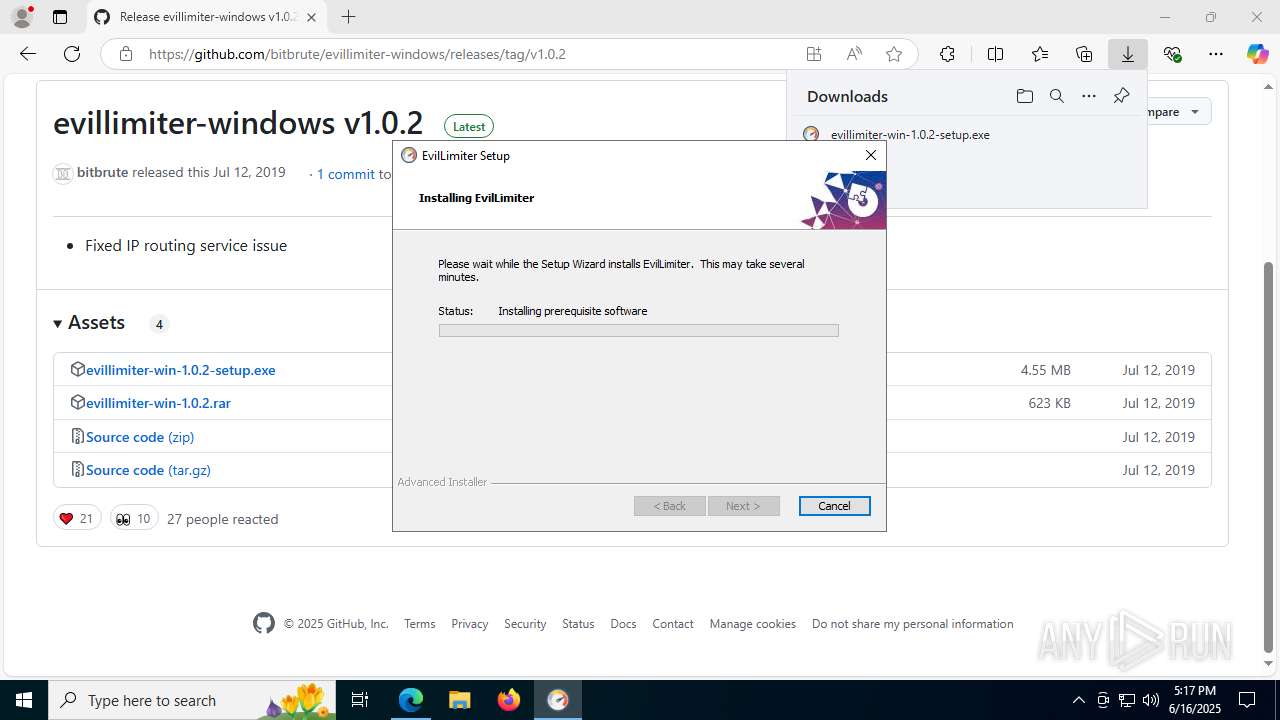
Detects AdvancedInstaller (YARA)
- evillimiter-win-1.0.2-setup.exe (PID: 8076)
- msiexec.exe (PID: 8140)
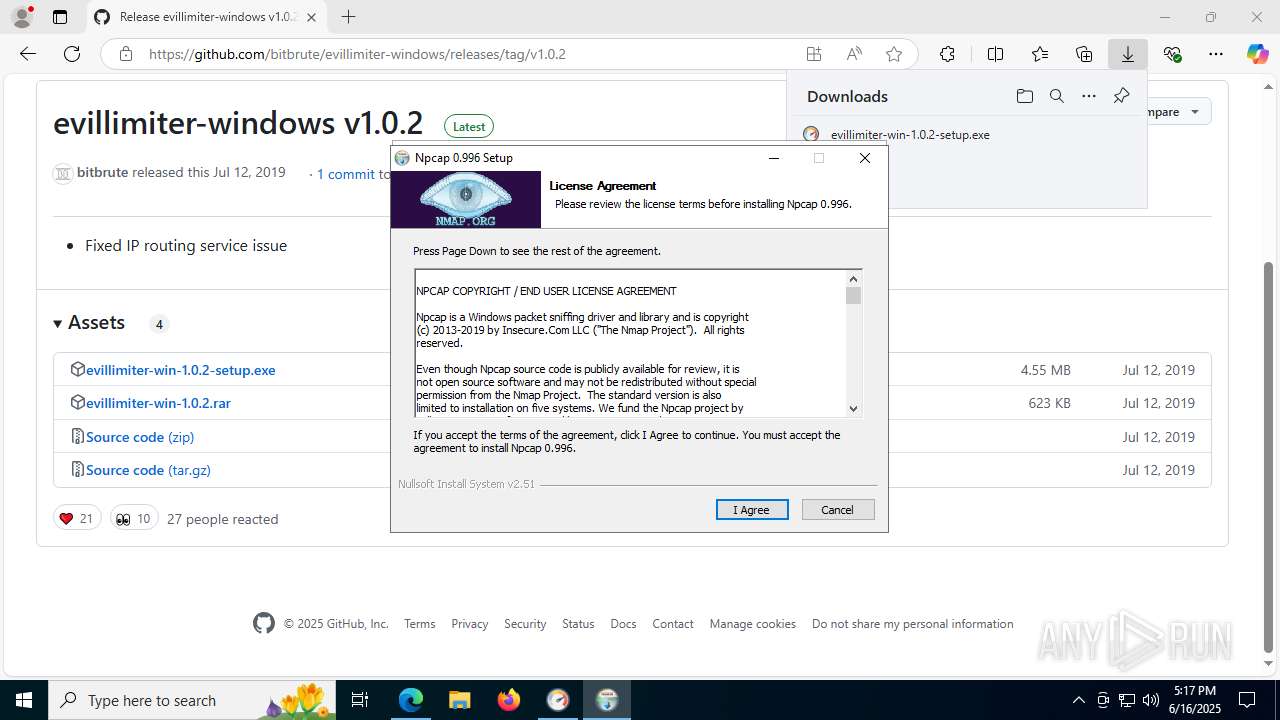
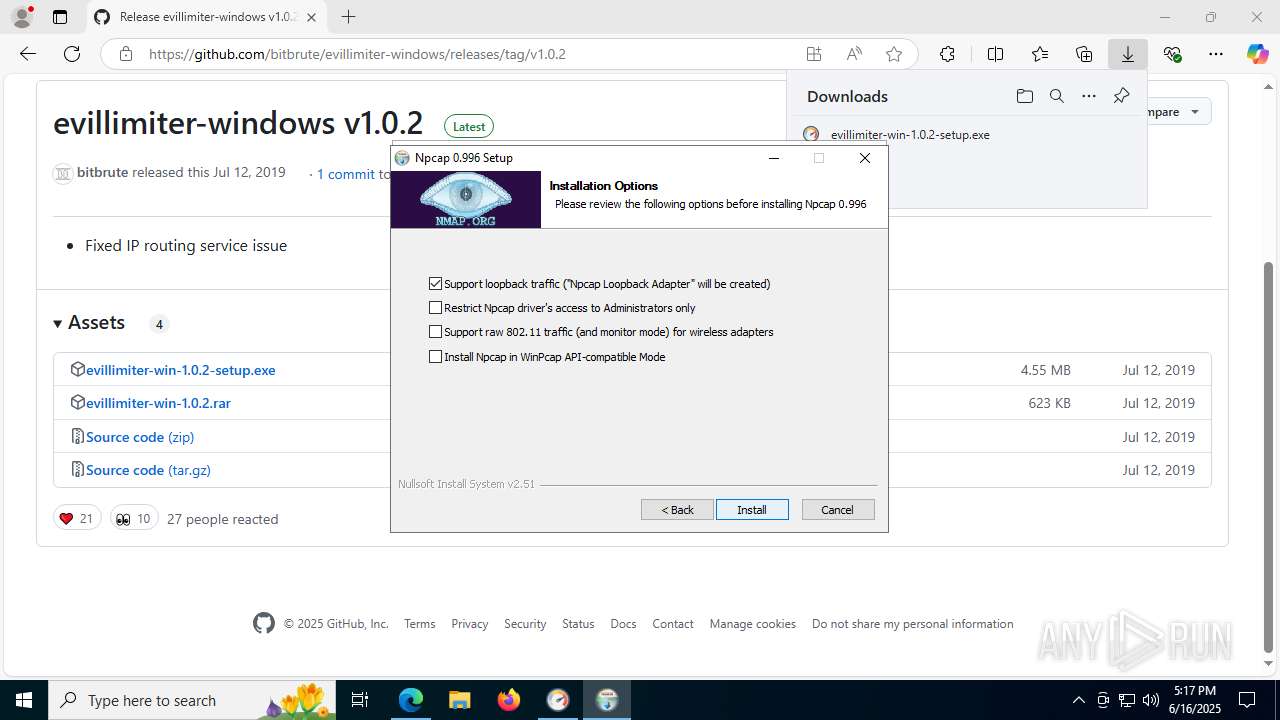
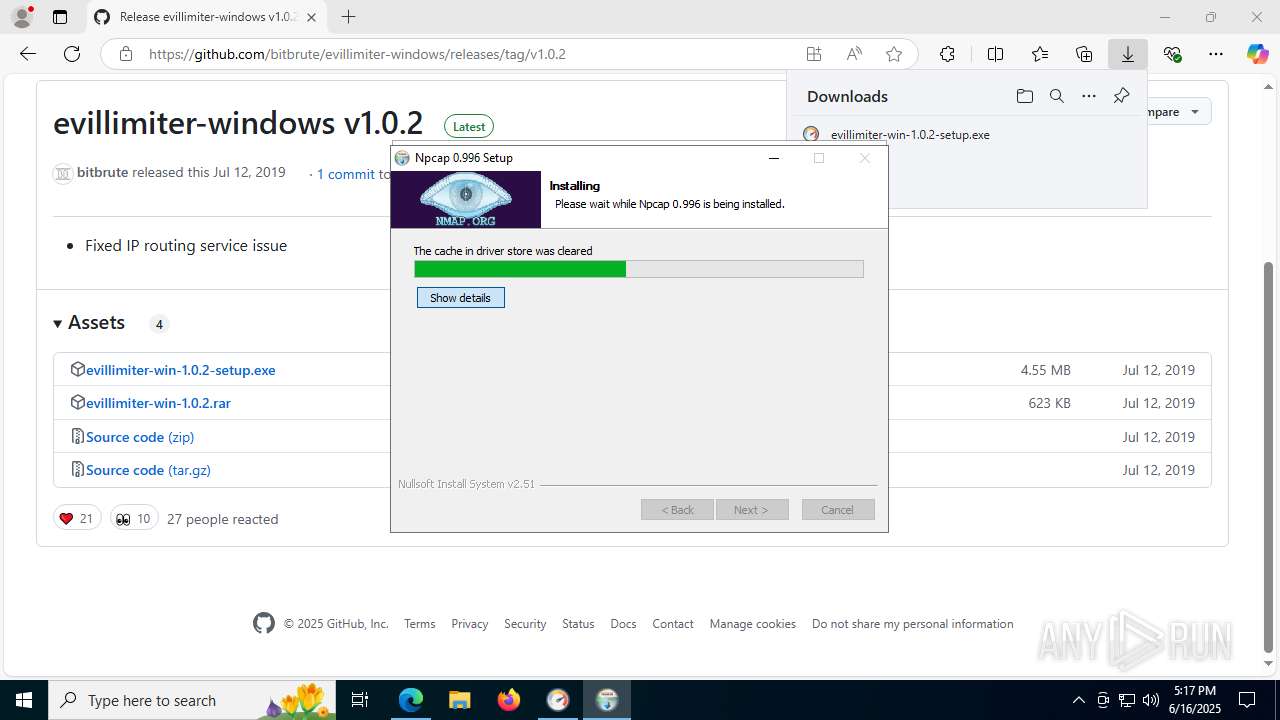
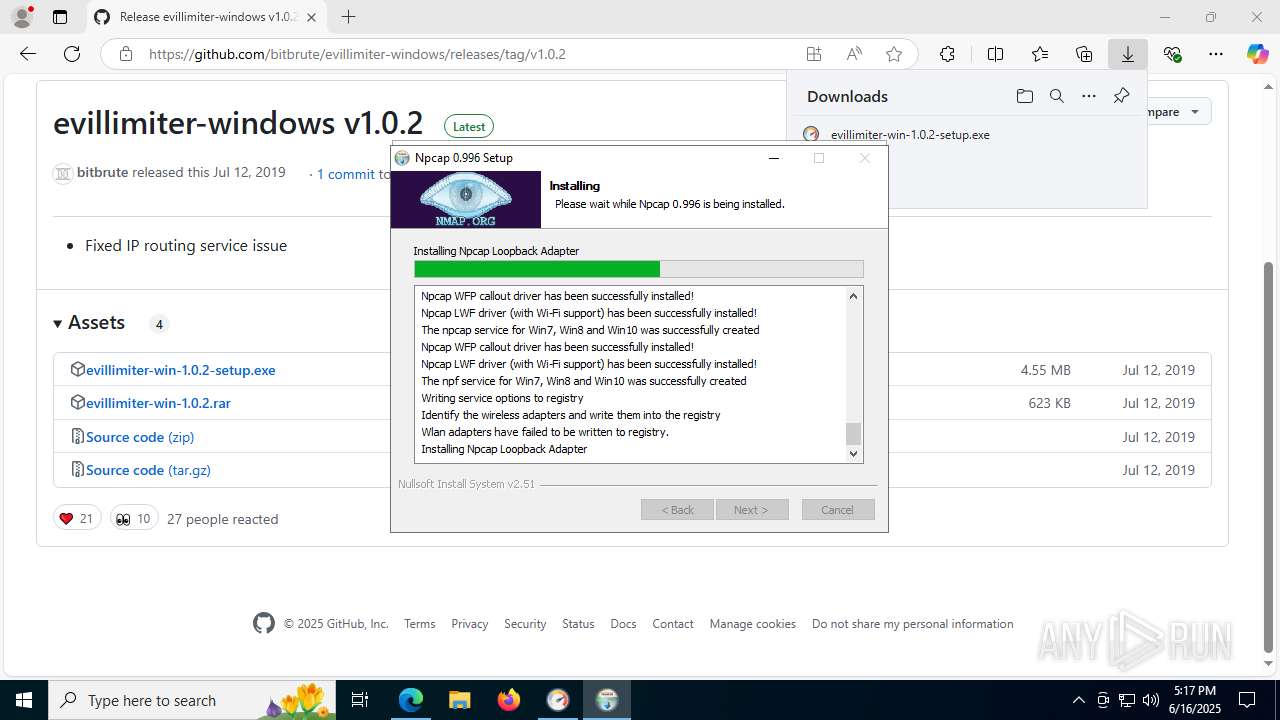
Malware-specific behavior (creating "System.dll" in Temp)
- npcap-0.996.exe (PID: 7484)
Drops a system driver (possible attempt to evade defenses)
- npcap-0.996.exe (PID: 7484)
- NPFInstall.exe (PID: 7960)
- drvinst.exe (PID: 7564)
- drvinst.exe (PID: 7236)
- msiexec.exe (PID: 8140)
- NPFInstall2.exe (PID: 6528)
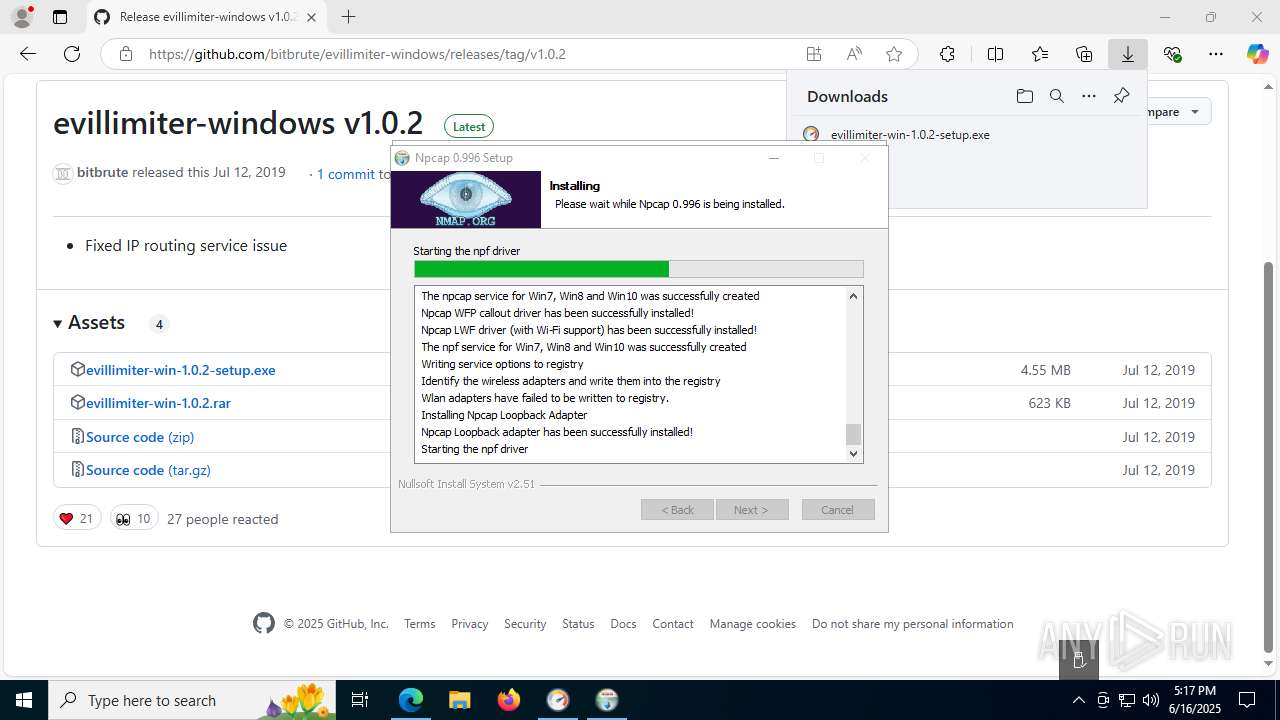
Suspicious use of NETSH.EXE
- NPFInstall.exe (PID: 3760)
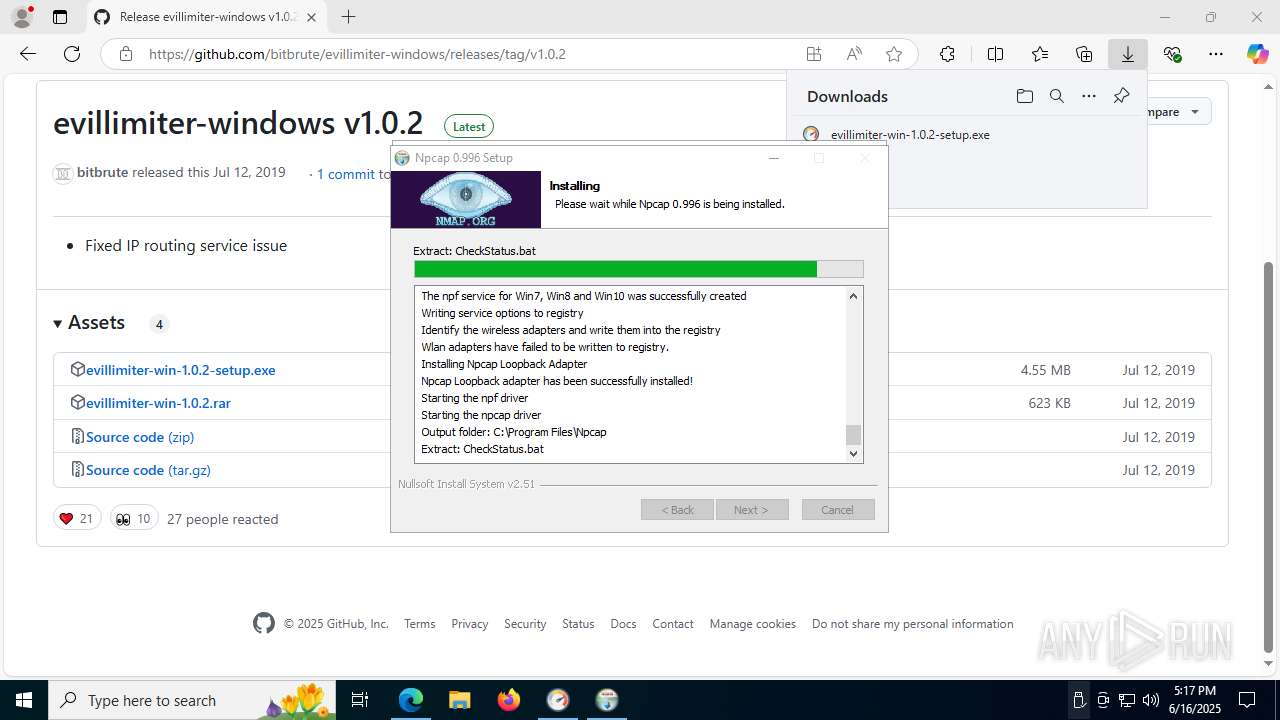
Executing commands from a ".bat" file
- evillimiter-win-1.0.2-setup.exe (PID: 8076)
- cmd.exe (PID: 7264)
- cmd.exe (PID: 7820)
Starts CMD.EXE for commands execution
- evillimiter-win-1.0.2-setup.exe (PID: 8076)
- cmd.exe (PID: 7264)
- cmd.exe (PID: 7820)
Uses ATTRIB.EXE to modify file attributes
- cmd.exe (PID: 7264)
- cmd.exe (PID: 7820)
ADVANCEDINSTALLER mutex has been found
- evillimiter-win-1.0.2-setup.exe (PID: 8076)
INFO
Application launched itself
- msedge.exe (PID: 2708)
Checks supported languages
- identity_helper.exe (PID: 7468)
- msiexec.exe (PID: 8180)
- msiexec.exe (PID: 8140)
- evillimiter-win-1.0.2-setup.exe (PID: 7988)
- evillimiter-win-1.0.2-setup.exe (PID: 8076)
Reads Environment values
- identity_helper.exe (PID: 7468)
- evillimiter-win-1.0.2-setup.exe (PID: 8076)
- msiexec.exe (PID: 8180)
- evillimiter-win-1.0.2-setup.exe (PID: 7988)
Reads the computer name
- identity_helper.exe (PID: 7468)
- evillimiter-win-1.0.2-setup.exe (PID: 8076)
- msiexec.exe (PID: 8140)
- msiexec.exe (PID: 8180)
- evillimiter-win-1.0.2-setup.exe (PID: 7988)
The sample compiled with english language support
- msedge.exe (PID: 3572)
- msiexec.exe (PID: 8180)
- evillimiter-win-1.0.2-setup.exe (PID: 8076)
- evillimiter-win-1.0.2-setup.exe (PID: 7988)
- msiexec.exe (PID: 8140)
- npcap-0.996.exe (PID: 7484)
- msedge.exe (PID: 2708)
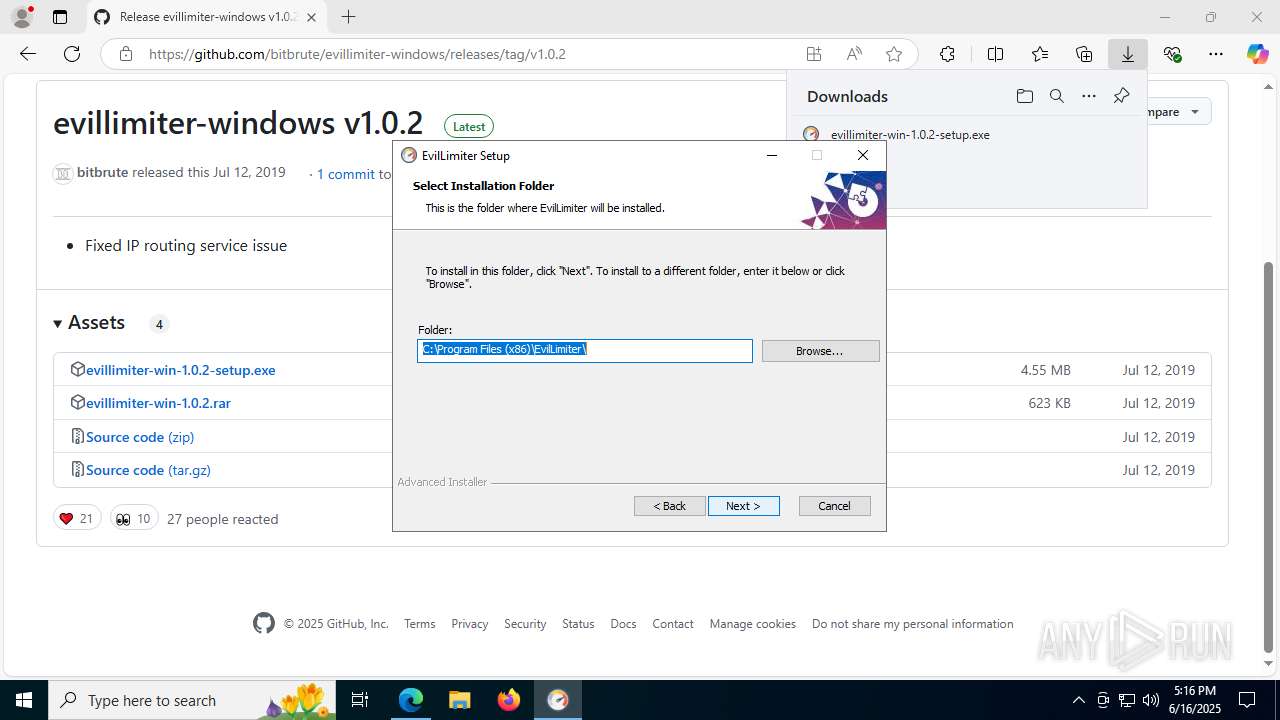
Creates files or folders in the user directory
- evillimiter-win-1.0.2-setup.exe (PID: 8076)
- msiexec.exe (PID: 8180)
Create files in a temporary directory
- evillimiter-win-1.0.2-setup.exe (PID: 8076)
- evillimiter-win-1.0.2-setup.exe (PID: 7988)
Checks proxy server information
- msiexec.exe (PID: 8180)
Reads the machine GUID from the registry
- msiexec.exe (PID: 8180)
- evillimiter-win-1.0.2-setup.exe (PID: 7988)
Executable content was dropped or overwritten
- msiexec.exe (PID: 8180)
- msiexec.exe (PID: 8140)
- msedge.exe (PID: 3572)
- msedge.exe (PID: 2708)
Reads the software policy settings
- msiexec.exe (PID: 8180)
Process checks computer location settings
- evillimiter-win-1.0.2-setup.exe (PID: 8076)
Manages system restore points
- SrTasks.exe (PID: 1700)
Launching a file from Task Scheduler
- npcap-0.996.exe (PID: 7484)
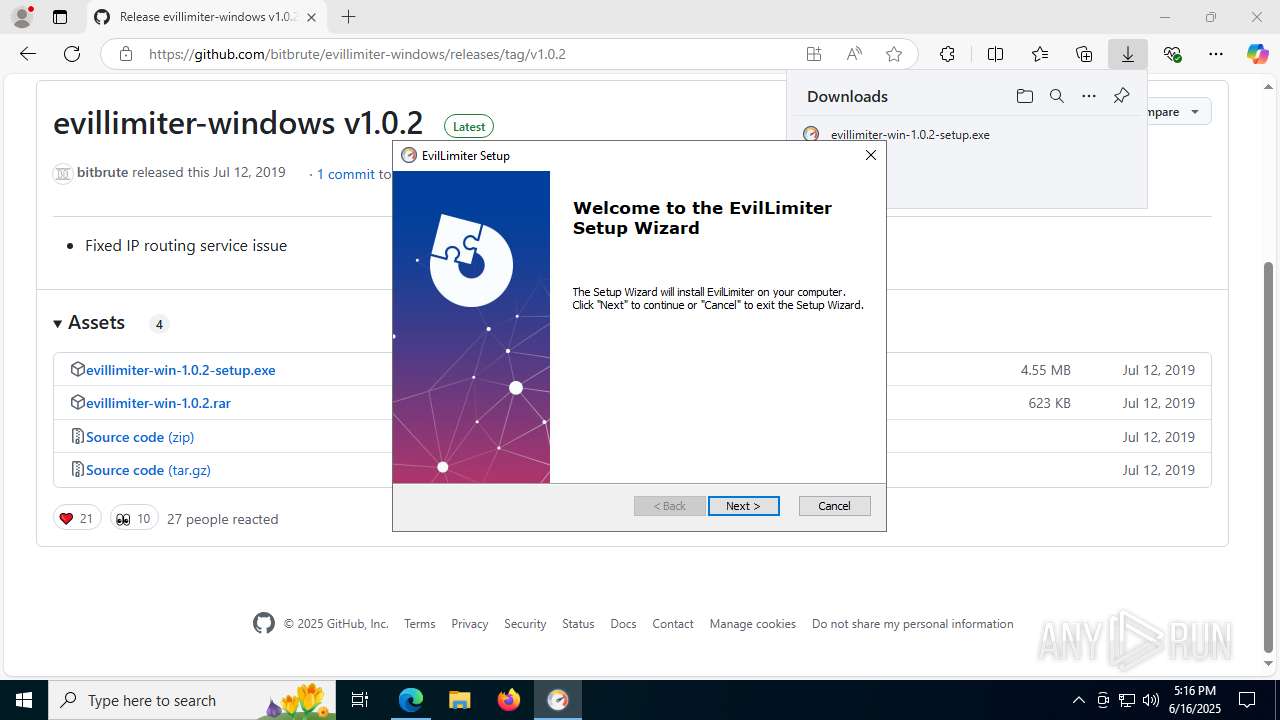
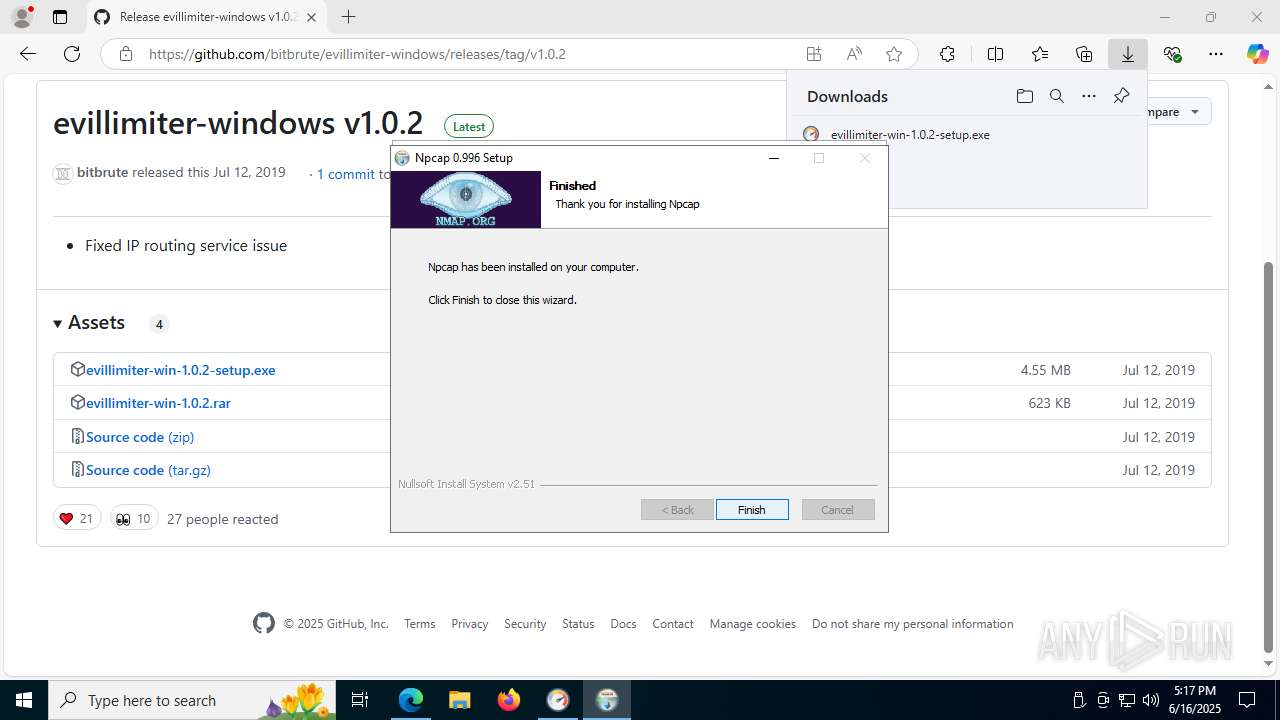
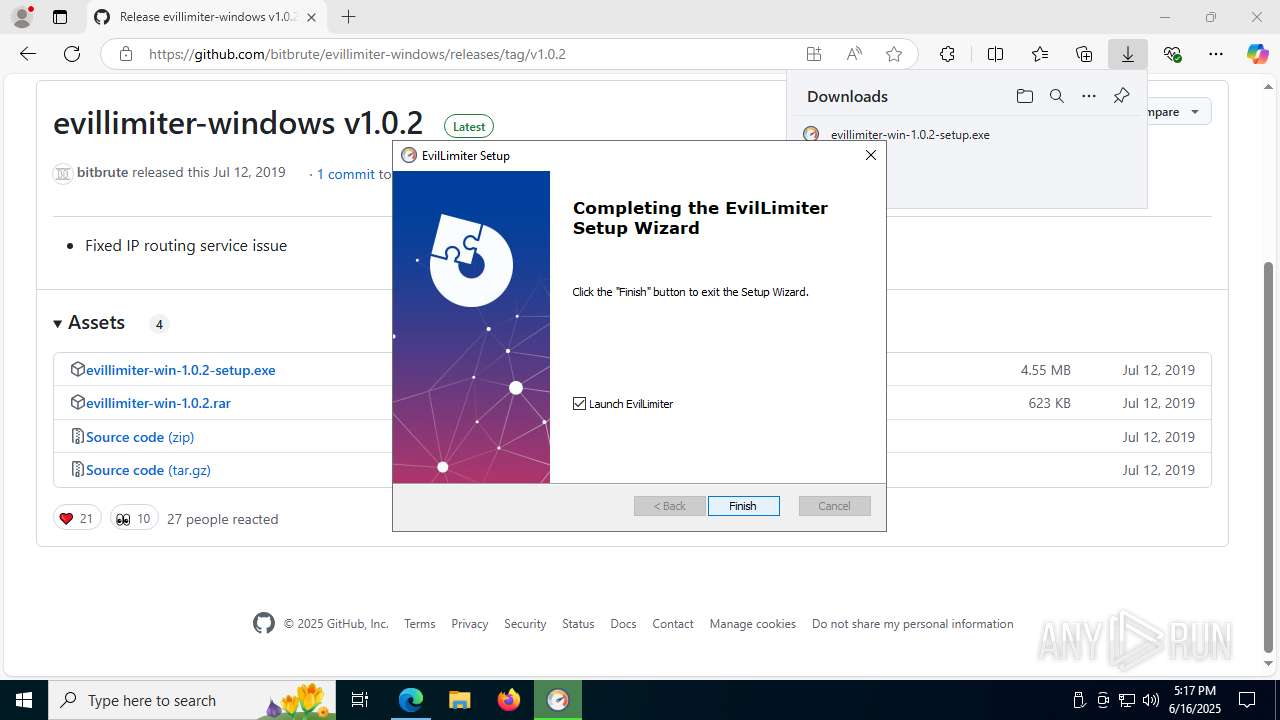
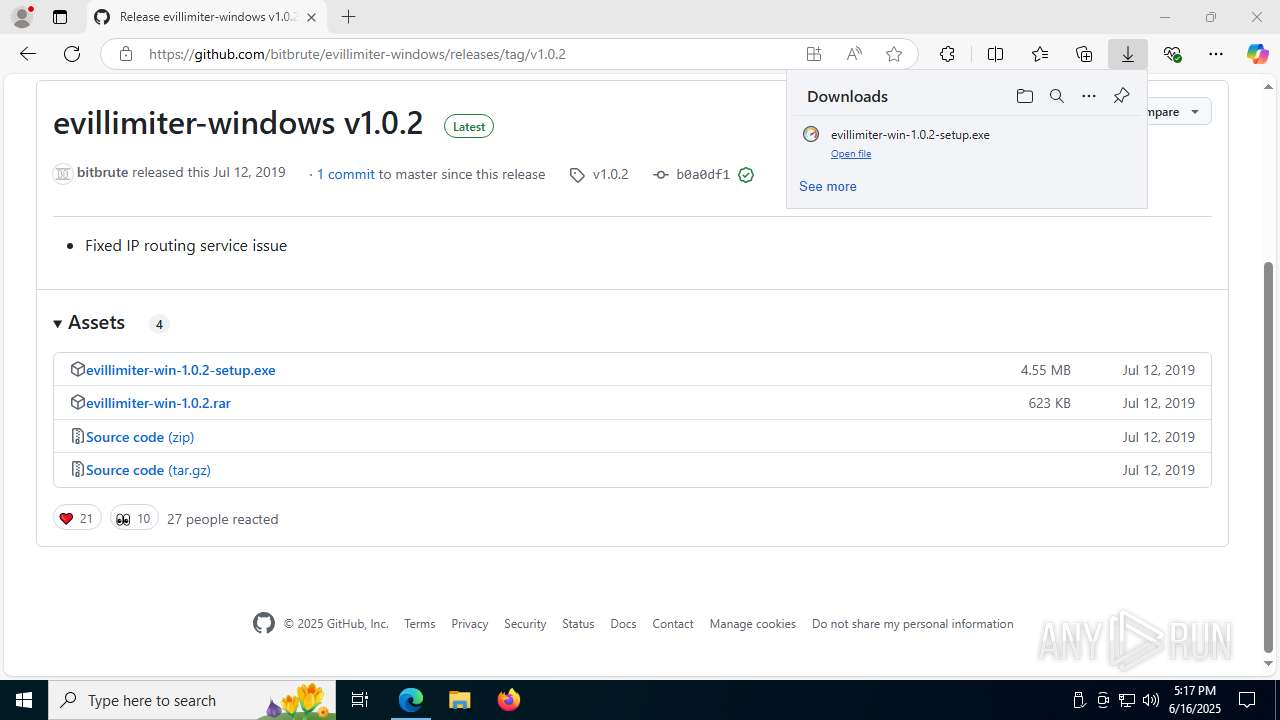
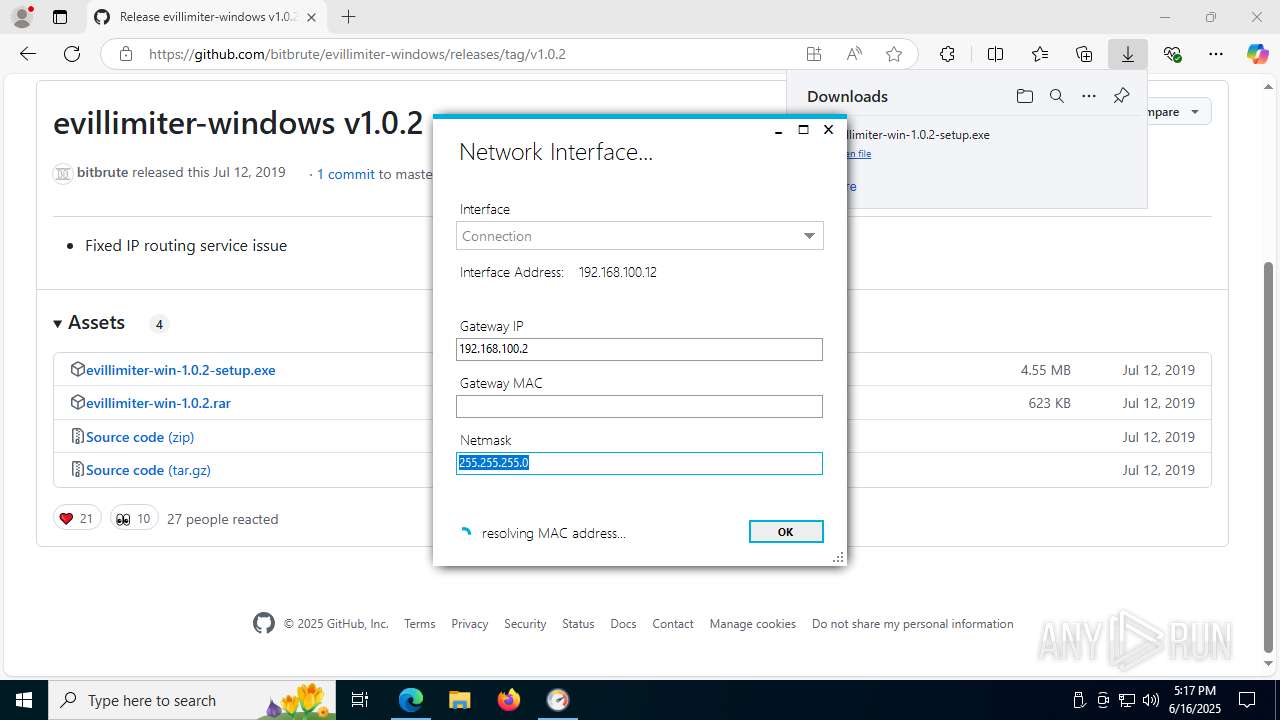
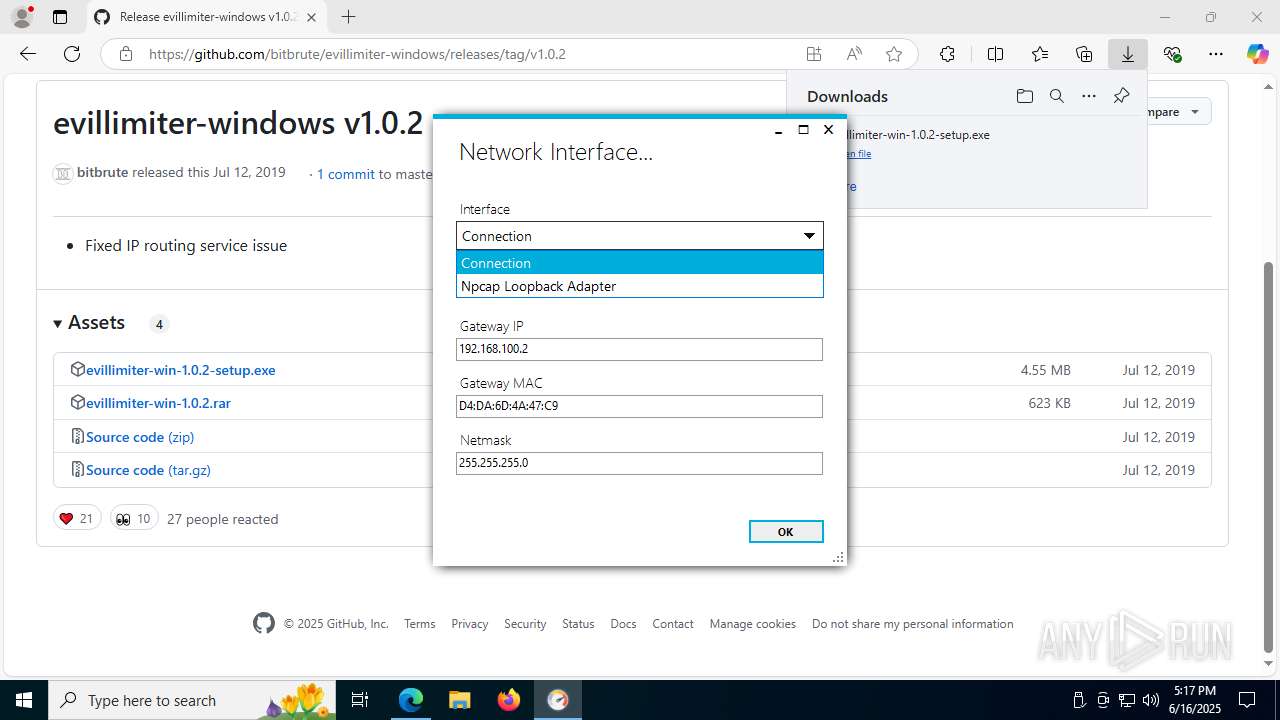
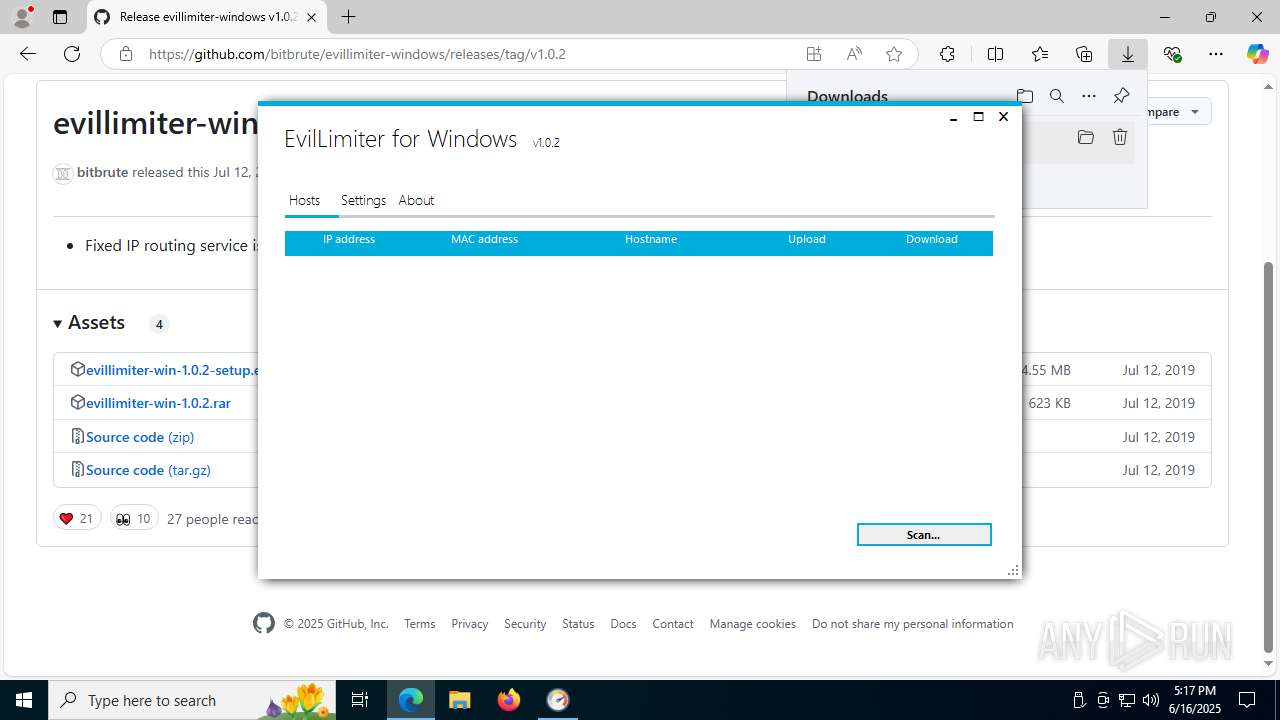
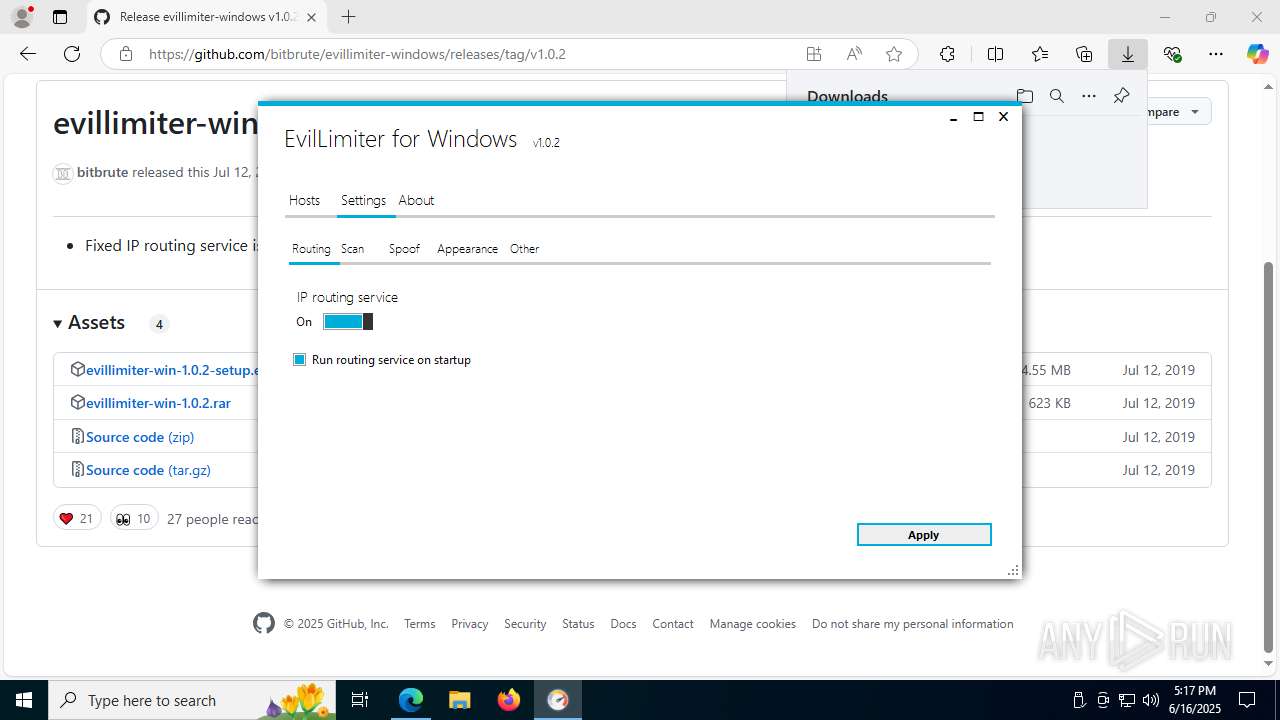
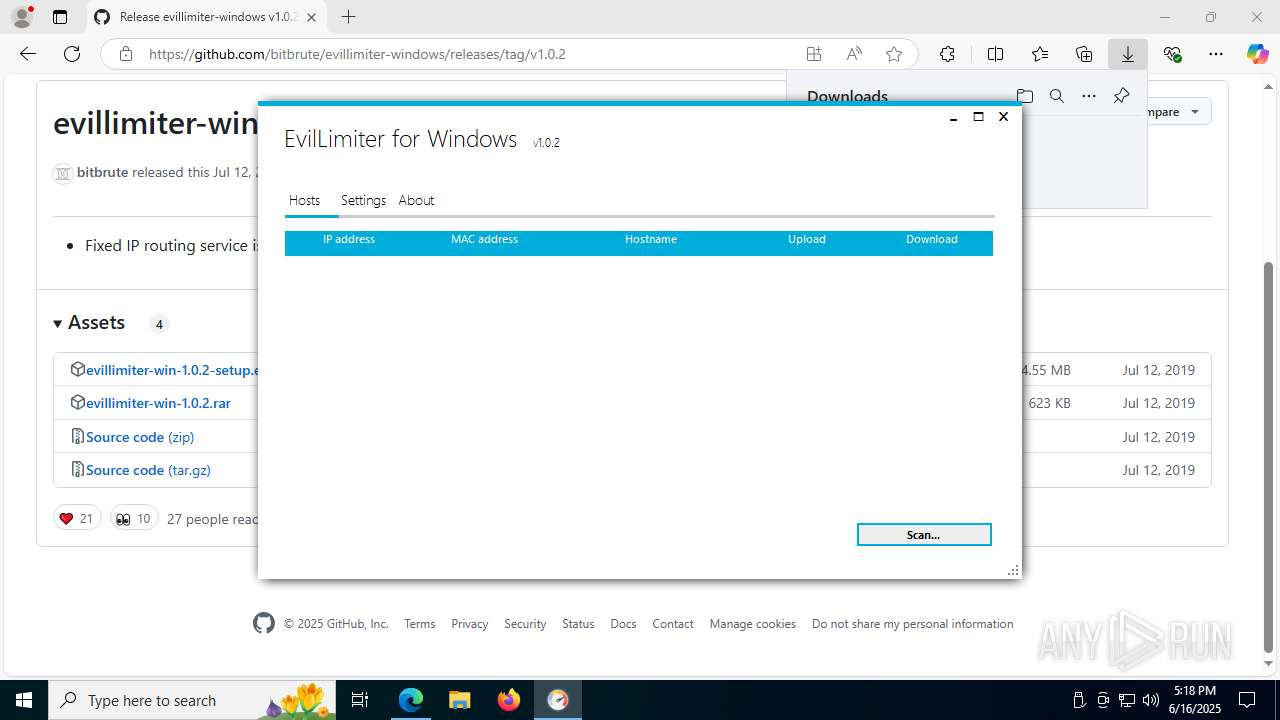
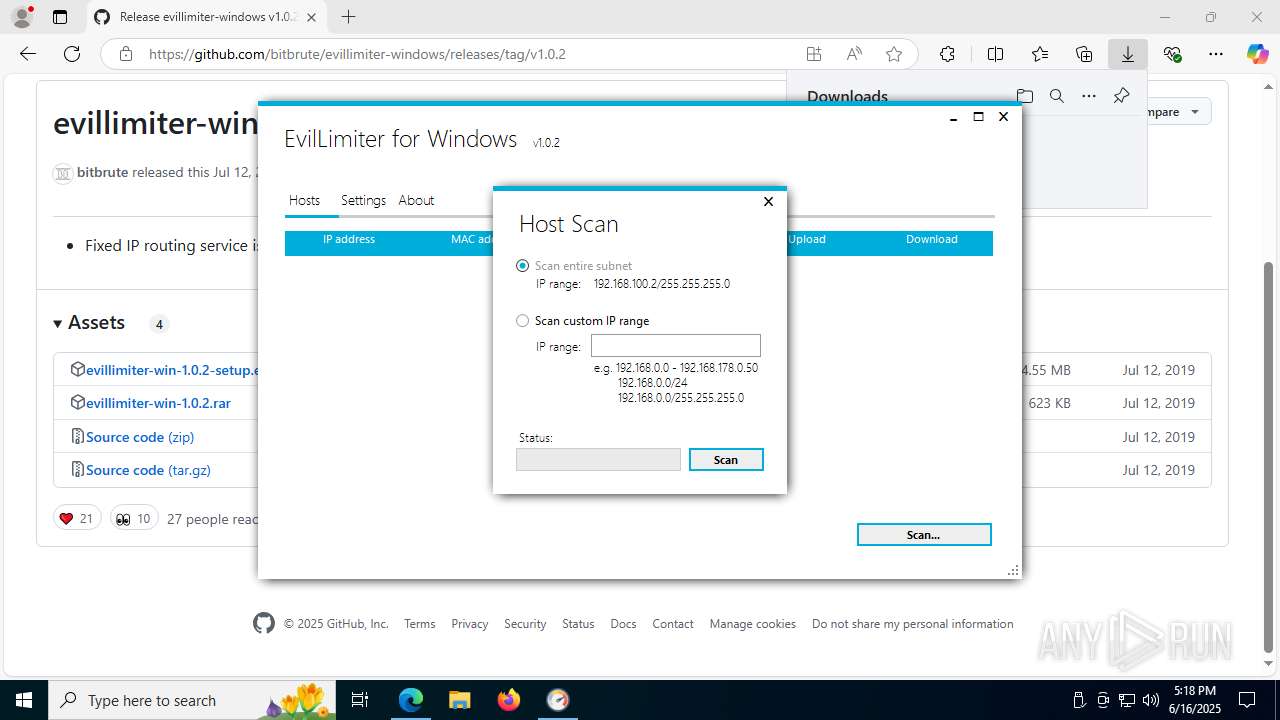
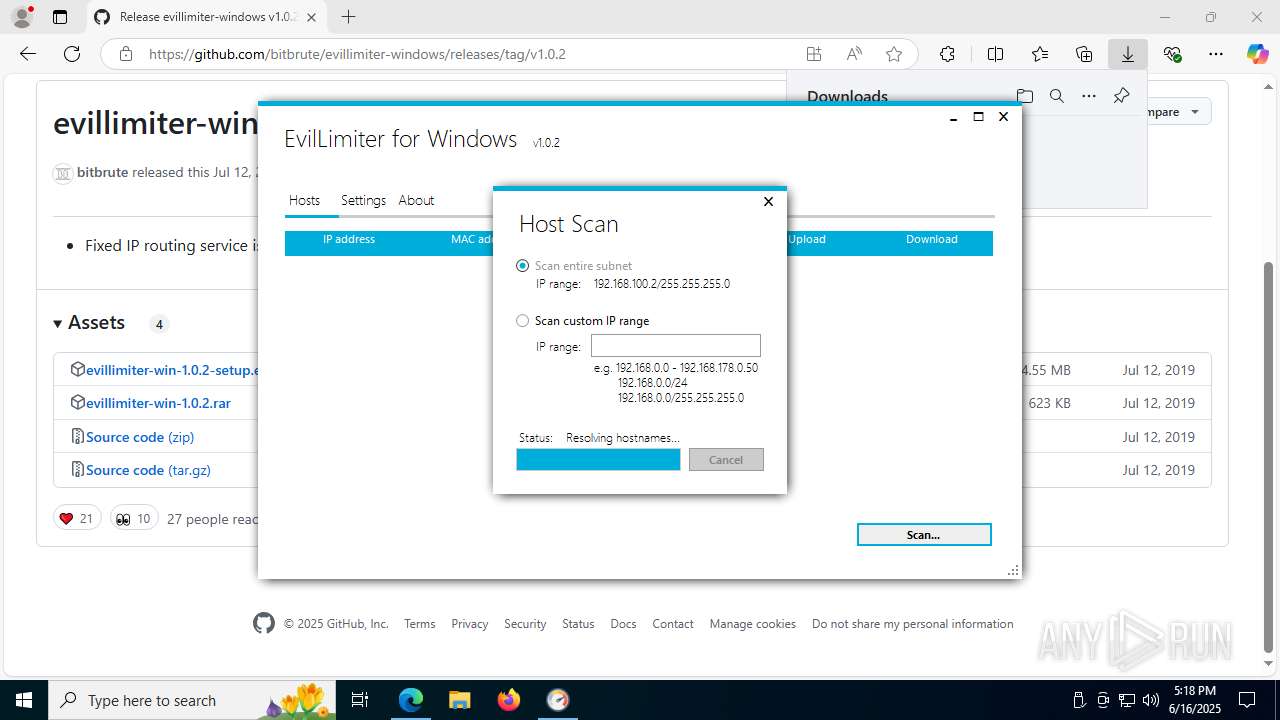
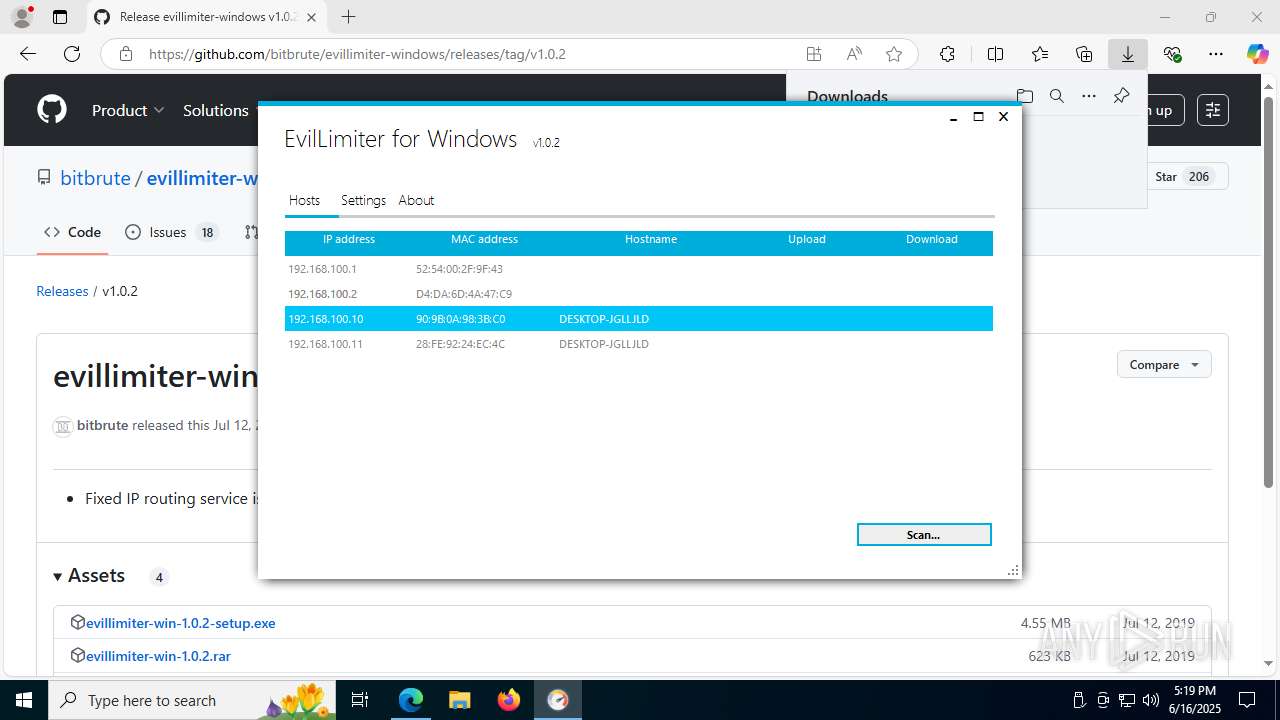
Manual execution by a user
- EvilLimiter.exe (PID: 7436)
- EvilLimiter.exe (PID: 1164)
Launching a file from the Downloads directory
- msedge.exe (PID: 2708)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
242
Monitored processes
89
Malicious processes
4
Suspicious processes
6
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1164 | "C:\Program Files (x86)\EvilLimiter\EvilLimiter.exe" | C:\Program Files (x86)\EvilLimiter\EvilLimiter.exe | — | explorer.exe | |||||||||||
User: admin Company: bitbrute Integrity Level: MEDIUM Description: EvilLimiter for Windows Exit code: 3221226540 Version: 1.0.2.0 Modules
| |||||||||||||||
| 1496 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Microsoft\Edge\User Data" /prefetch:4 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Crashpad" --annotation=IsOfficialBuild=1 --annotation=channel= --annotation=chromium-version=133.0.6943.142 "--annotation=exe=C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --annotation=plat=Win64 --annotation=prod=Edge --annotation=ver=133.0.3065.92 --initial-client-data=0x304,0x308,0x30c,0x2fc,0x314,0x7ffc4312f208,0x7ffc4312f214,0x7ffc4312f220 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Version: 133.0.3065.92 Modules
| |||||||||||||||
| 1512 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=chrome.mojom.UtilWin --lang=en-US --service-sandbox-type=none --disable-quic --message-loop-type-ui --string-annotations --always-read-main-dll --field-trial-handle=1516,i,11556458653457856112,6615660773561985196,262144 --variations-seed-version --mojo-platform-channel-handle=6160 /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 1700 | C:\WINDOWS\system32\srtasks.exe ExecuteScopeRestorePoint /WaitForRestorePoint:11 | C:\Windows\System32\SrTasks.exe | — | msiexec.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft® Windows System Protection background tasks. Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1712 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=storage.mojom.StorageService --lang=en-US --service-sandbox-type=service --disable-quic --string-annotations --always-read-main-dll --field-trial-handle=2636,i,11556458653457856112,6615660773561985196,262144 --variations-seed-version --mojo-platform-channel-handle=2720 /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Version: 133.0.3065.92 Modules
| |||||||||||||||
| 2072 | pnputil.exe -e | C:\Windows\System32\pnputil.exe | — | NPFInstall.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft PnP Utility - Tool to add, delete, export, and enumerate driver packages. Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2232 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | NPFInstall.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2512 | C:\WINDOWS\system32\DllHost.exe /Processid:{48DA6741-1BF0-4A44-8325-293086C79077} | C:\Windows\System32\dllhost.exe | — | svchost.exe | |||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: COM Surrogate Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2524 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --disable-quic --string-annotations --always-read-main-dll --field-trial-handle=7080,i,11556458653457856112,6615660773561985196,262144 --variations-seed-version --mojo-platform-channel-handle=6848 /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 2528 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --disable-quic --string-annotations --always-read-main-dll --field-trial-handle=7740,i,11556458653457856112,6615660773561985196,262144 --variations-seed-version --mojo-platform-channel-handle=7848 /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
Total events
36 289
Read events
35 829
Write events
431
Delete events
29
Modification events
| (PID) Process: | (2708) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (2708) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (2708) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (2708) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (2708) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (2708) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (2708) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: 0D3B86D749962F00 | |||
| (PID) Process: | (2708) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\590702 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {82E9CFEB-2679-4F58-ACC7-DFFA68C1454C} | |||
| (PID) Process: | (2708) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\590702 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {35D71C82-3D3B-4336-B66F-16965CDD4AD6} | |||
| (PID) Process: | (2708) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\590702 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {7C9756AA-3BD9-4D41-9C18-CA943F554D12} | |||
Executable files
86
Suspicious files
305
Text files
94
Unknown types
56
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2708 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old~RF176503.TMP | — | |
MD5:— | SHA256:— | |||
| 2708 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old~RF176503.TMP | — | |
MD5:— | SHA256:— | |||
| 2708 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2708 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old~RF176513.TMP | — | |
MD5:— | SHA256:— | |||
| 2708 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2708 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2708 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\ClientCertificates\LOG.old~RF176542.TMP | — | |
MD5:— | SHA256:— | |||
| 2708 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\ClientCertificates\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2708 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old~RF176551.TMP | — | |
MD5:— | SHA256:— | |||
| 2708 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
28
TCP/UDP connections
134
DNS requests
115
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3572 | msedge.exe | GET | 200 | 150.171.28.11:80 | http://edge.microsoft.com/browsernetworktime/time/1/current?cup2key=2:C1jIZ8u2oy-zxmKTSL1184nGsrMcsOzL63NUYjTrnmU&cup2hreq=e3b0c44298fc1c149afbf4c8996fb92427ae41e4649b934ca495991b7852b855 | unknown | — | — | whitelisted |
2764 | svchost.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
1268 | svchost.exe | GET | 200 | 23.216.77.18:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
1268 | svchost.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
8180 | msiexec.exe | GET | 200 | 104.18.20.213:80 | http://r11.c.lencr.org/66.crl | unknown | — | — | whitelisted |
7516 | SIHClient.exe | GET | 200 | 23.219.150.101:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
7200 | svchost.exe | HEAD | 200 | 23.50.131.218:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/bf8090eb-6e5c-4c51-9250-5bf9b46cf160?P1=1750546044&P2=404&P3=2&P4=C4fSscplVa9n%2fkA%2bkpywERqoH%2b4xknoV3%2bRXtl87%2bslLumfqjElU5E7uH4rfEiOexQnEv5bqDlDeojHMjK6hpA%3d%3d | unknown | — | — | whitelisted |
7516 | SIHClient.exe | GET | 200 | 23.219.150.101:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
7200 | svchost.exe | GET | 206 | 23.50.131.218:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/bf8090eb-6e5c-4c51-9250-5bf9b46cf160?P1=1750546044&P2=404&P3=2&P4=C4fSscplVa9n%2fkA%2bkpywERqoH%2b4xknoV3%2bRXtl87%2bslLumfqjElU5E7uH4rfEiOexQnEv5bqDlDeojHMjK6hpA%3d%3d | unknown | — | — | whitelisted |
7200 | svchost.exe | GET | 206 | 23.50.131.218:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/bf8090eb-6e5c-4c51-9250-5bf9b46cf160?P1=1750546044&P2=404&P3=2&P4=C4fSscplVa9n%2fkA%2bkpywERqoH%2b4xknoV3%2bRXtl87%2bslLumfqjElU5E7uH4rfEiOexQnEv5bqDlDeojHMjK6hpA%3d%3d | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
5944 | MoUsoCoreWorker.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
1268 | svchost.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
5528 | RUXIMICS.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
3572 | msedge.exe | 150.171.28.11:80 | edge.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
3572 | msedge.exe | 13.107.42.16:443 | config.edge.skype.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
3572 | msedge.exe | 140.82.121.3:443 | github.com | GITHUB | US | whitelisted |
3572 | msedge.exe | 150.171.28.11:443 | edge.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
3572 | msedge.exe | 2.23.227.211:443 | copilot.microsoft.com | Ooredoo Q.S.C. | QA | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
edge.microsoft.com |
| whitelisted |
config.edge.skype.com |
| whitelisted |
github.com |
| whitelisted |
copilot.microsoft.com |
| whitelisted |
www.bing.com |
| whitelisted |
github.githubassets.com |
| whitelisted |
avatars.githubusercontent.com |
| whitelisted |
camo.githubusercontent.com |
| whitelisted |