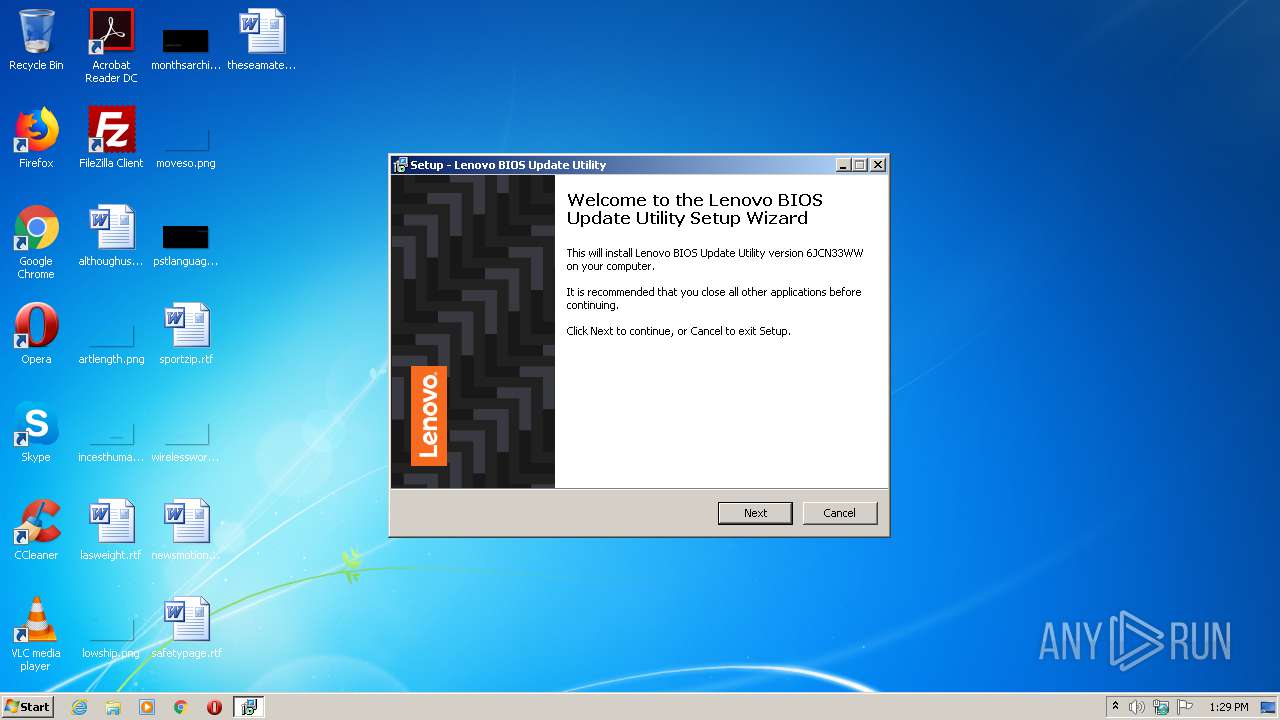
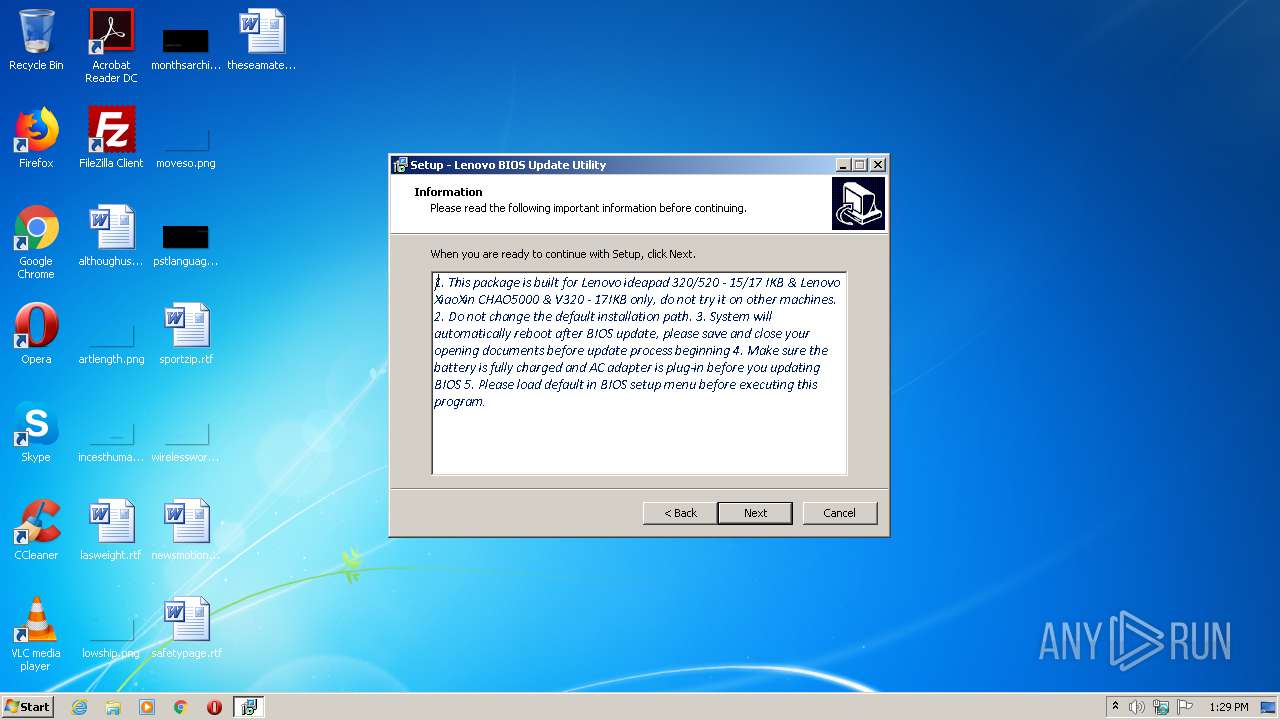
| File name: | 6jcn33ww.exe |
| Full analysis: | https://app.any.run/tasks/54e35e07-b39d-4723-aee7-c3c0f242c451 |
| Verdict: | Malicious activity |
| Analysis date: | October 04, 2020, 12:29:07 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 7305F6F7731A35FDE5AFE39B828B4439 |
| SHA1: | 7ADBB809E20540B13D52332A49A480DD7E8076A8 |
| SHA256: | 7EC39ECDD3360893D395127502152F40285DB0A0F05C6390F1D9C4132F28458A |
| SSDEEP: | 196608:xjtanah7PYSa5O/x6Q3ykN2SDqntWSzBP3Fblnh8fDj/I/Kc:xN7A/SxnCJ7wSl3FZh8iZ |
MALICIOUS
Application was dropped or rewritten from another process
- 6jcn33ww.tmp (PID: 308)
- 6JCN33WW.exe (PID: 3448)
- H2OFFT-W.exe (PID: 2804)
Uses Task Scheduler to run other applications
- 6jcn33ww.tmp (PID: 308)
Loads the Task Scheduler COM API
- schtasks.exe (PID: 2008)
- schtasks.exe (PID: 2580)
- schtasks.exe (PID: 2016)
- schtasks.exe (PID: 3976)
Changes settings of System certificates
- H2OFFT-W.exe (PID: 2804)
SUSPICIOUS
Creates files in the Windows directory
- 6jcn33ww.exe (PID: 3352)
- H2OFFT-W.exe (PID: 2804)
- DrvInst.exe (PID: 3420)
- DrvInst.exe (PID: 2528)
Executable content was dropped or overwritten
- 6jcn33ww.exe (PID: 3352)
- 6jcn33ww.exe (PID: 2924)
- 6JCN33WW.exe (PID: 3448)
- 6jcn33ww.tmp (PID: 308)
- DrvInst.exe (PID: 2528)
Reads the BIOS version
- 6jcn33ww.tmp (PID: 308)
Reads Windows owner or organization settings
- 6jcn33ww.tmp (PID: 308)
Adds / modifies Windows certificates
- H2OFFT-W.exe (PID: 2804)
Creates files in the driver directory
- DrvInst.exe (PID: 3420)
- DrvInst.exe (PID: 2528)
Executed via COM
- DrvInst.exe (PID: 2528)
- DrvInst.exe (PID: 3420)
Removes files from Windows directory
- DrvInst.exe (PID: 2528)
- DrvInst.exe (PID: 3420)
- 6jcn33ww.tmp (PID: 308)
- 6jcn33ww.exe (PID: 3352)
Starts application with an unusual extension
- 6jcn33ww.exe (PID: 3352)
Reads the Windows organization settings
- 6jcn33ww.tmp (PID: 308)
Uses ICACLS.EXE to modify access control list
- 6jcn33ww.tmp (PID: 308)
INFO
Application was dropped or rewritten from another process
- 6jcn33ww.tmp (PID: 3412)
Dropped object may contain Bitcoin addresses
- 6JCN33WW.exe (PID: 3448)
Reads settings of System Certificates
- H2OFFT-W.exe (PID: 2804)
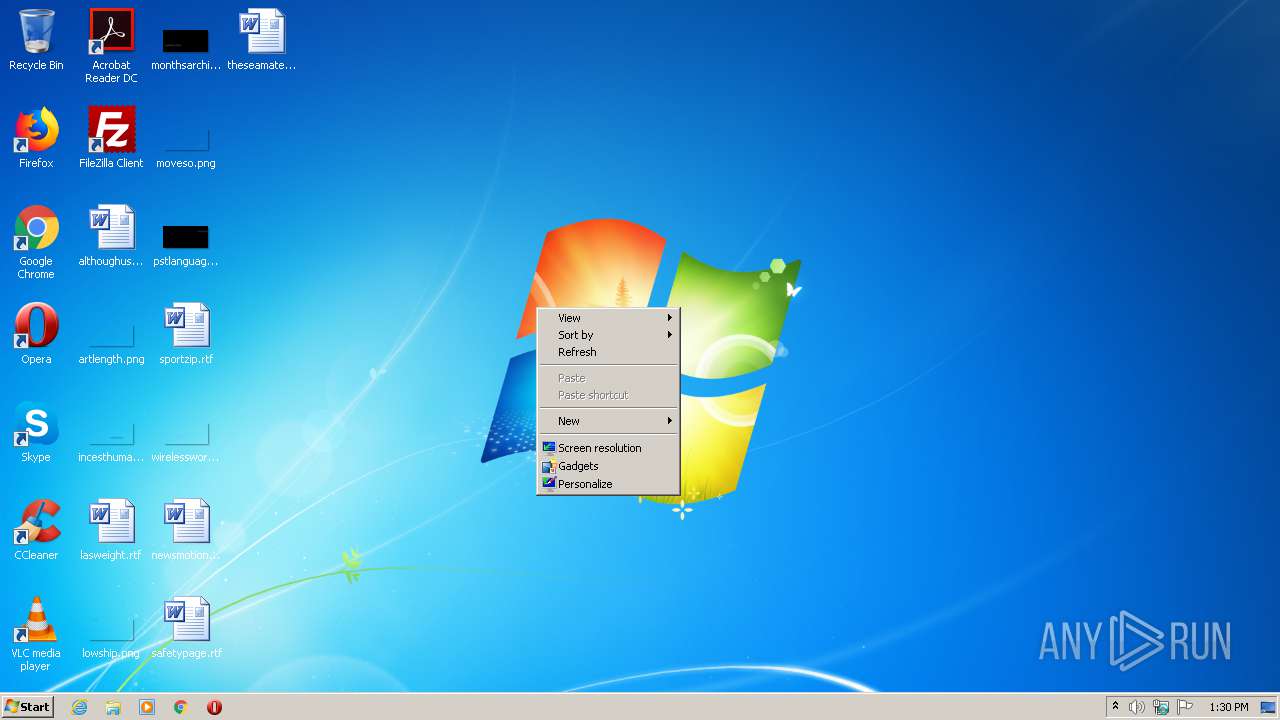
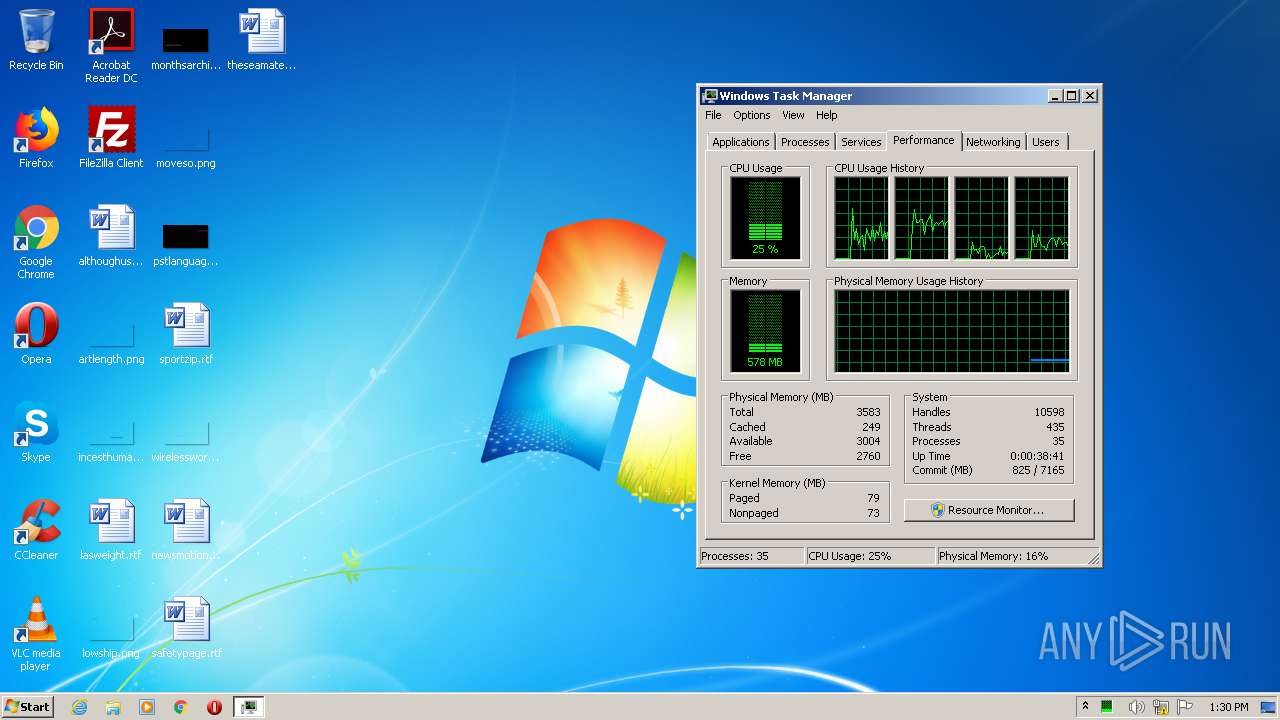
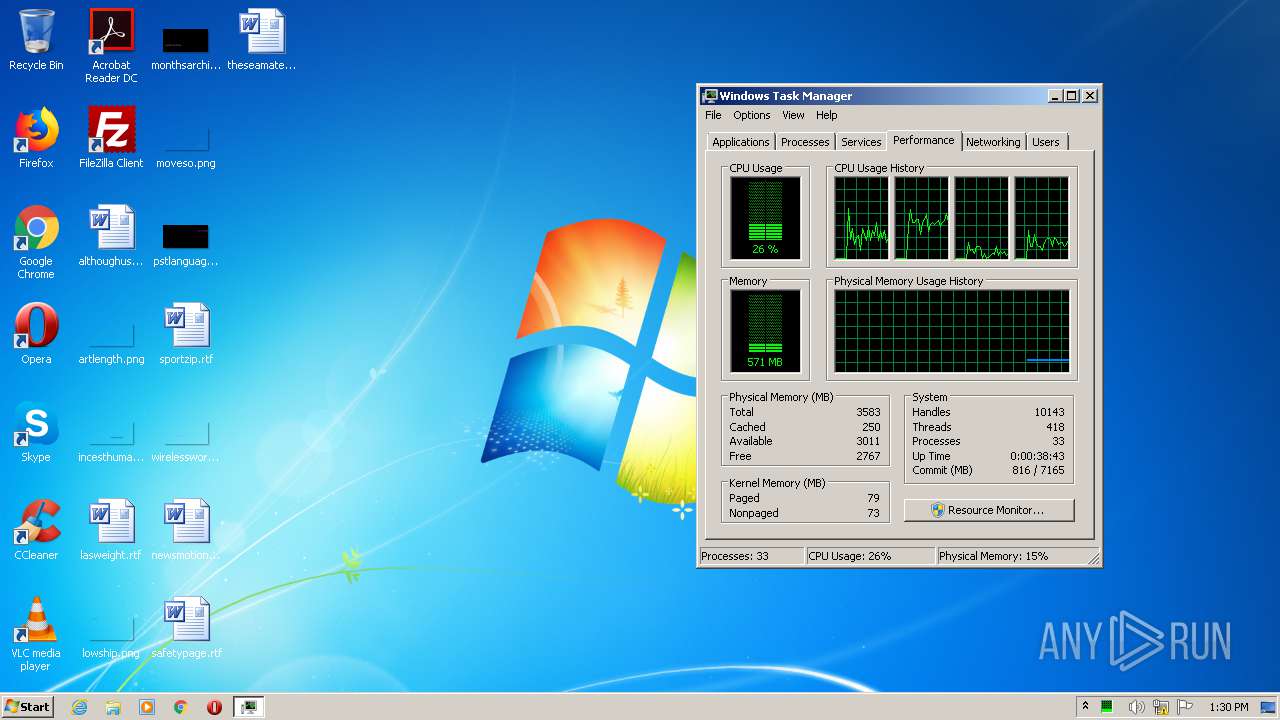
Manual execution by user
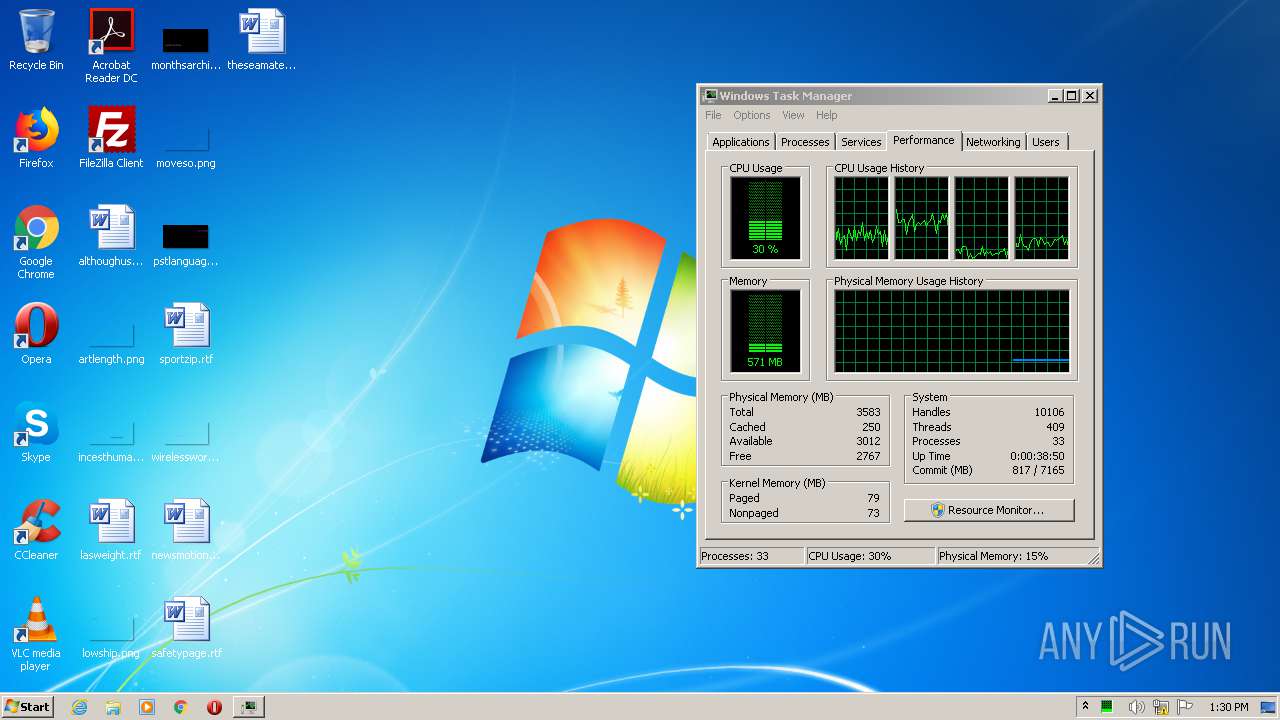
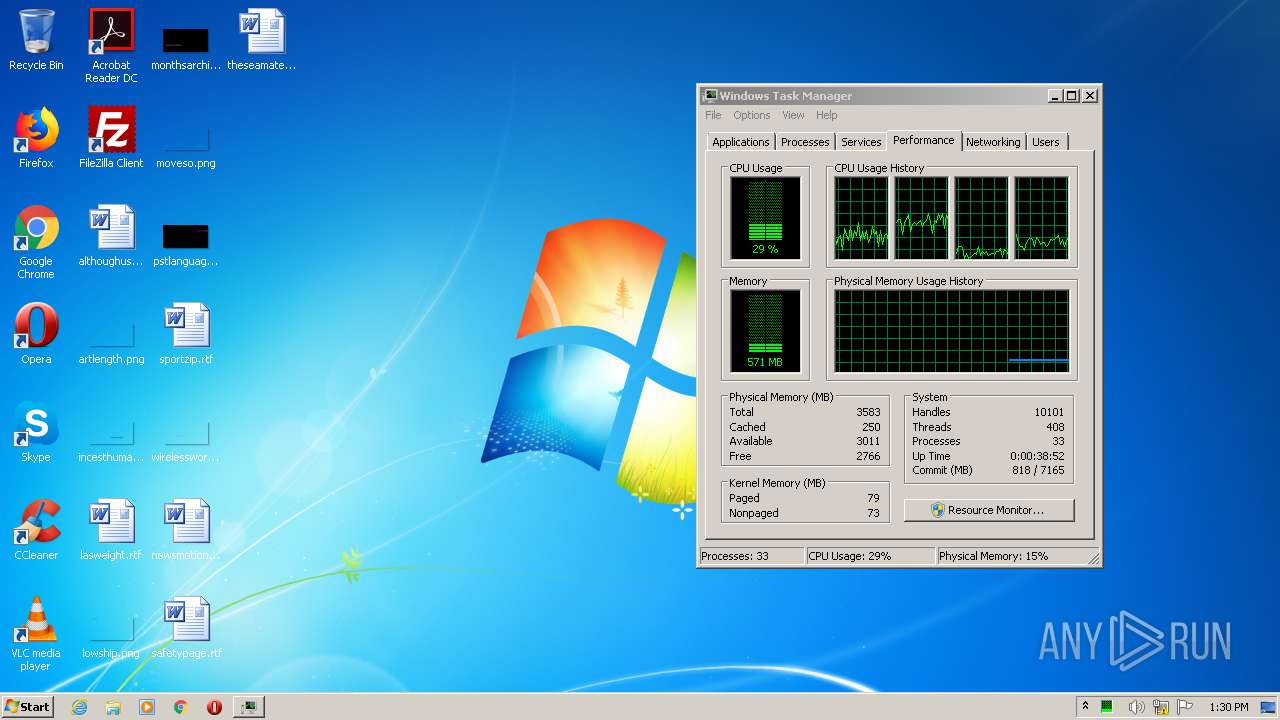
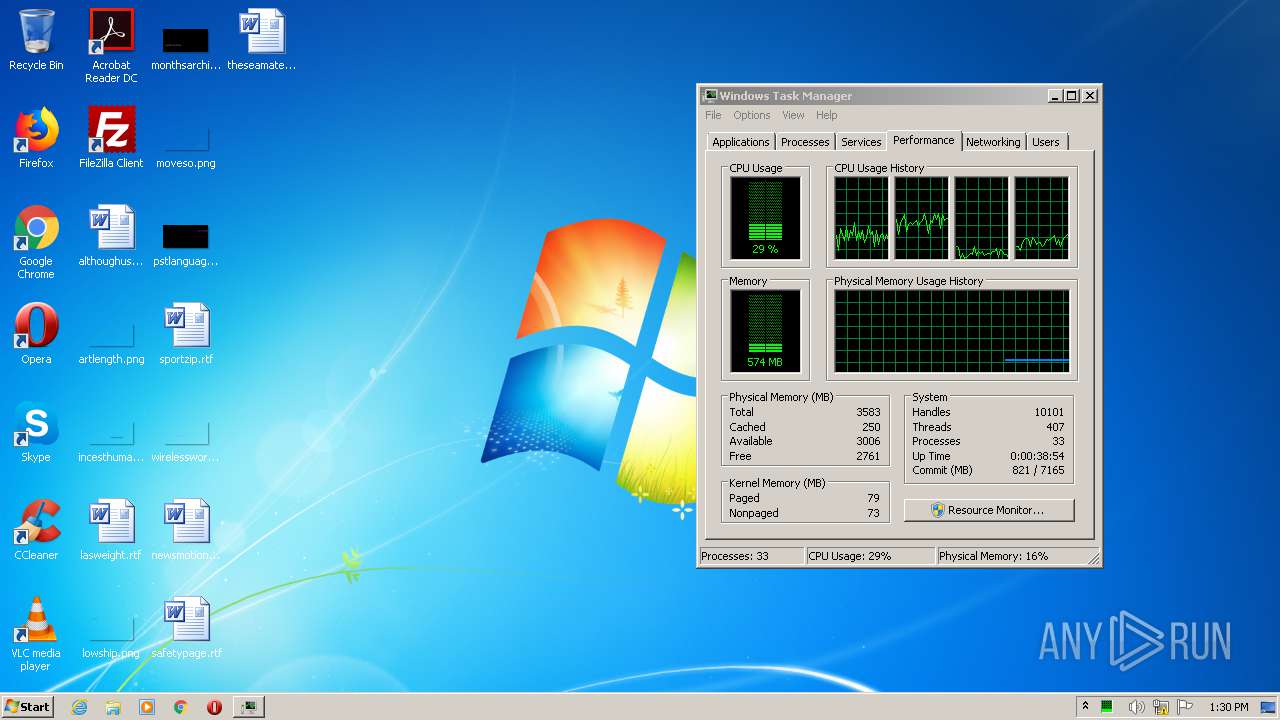
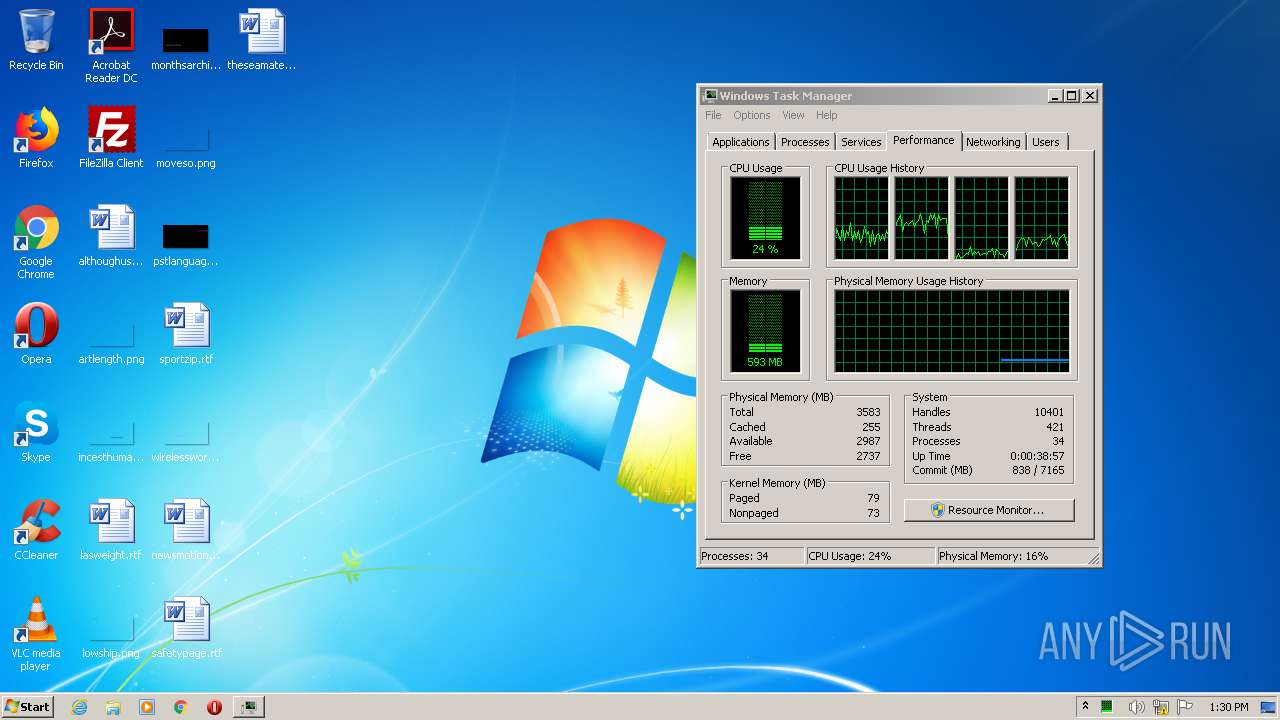
- taskmgr.exe (PID: 2496)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | InstallShield setup (42.2) |
|---|---|---|
| .exe | | | Win32 EXE PECompact compressed (generic) (40.8) |
| .dll | | | Win32 Dynamic Link Library (generic) (6.4) |
| .exe | | | Win32 Executable (generic) (4.4) |
| .exe | | | Win16/32 Executable Delphi generic (2) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2020:01:06 07:31:46+01:00 |
| PEType: | PE32 |
| LinkerVersion: | 2.25 |
| CodeSize: | 151552 |
| InitializedDataSize: | 27648 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x25be0 |
| OSVersion: | 5 |
| ImageVersion: | 6 |
| SubsystemVersion: | 5 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 1.0.0.0 |
| ProductVersionNumber: | 1.33.0.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Unicode |
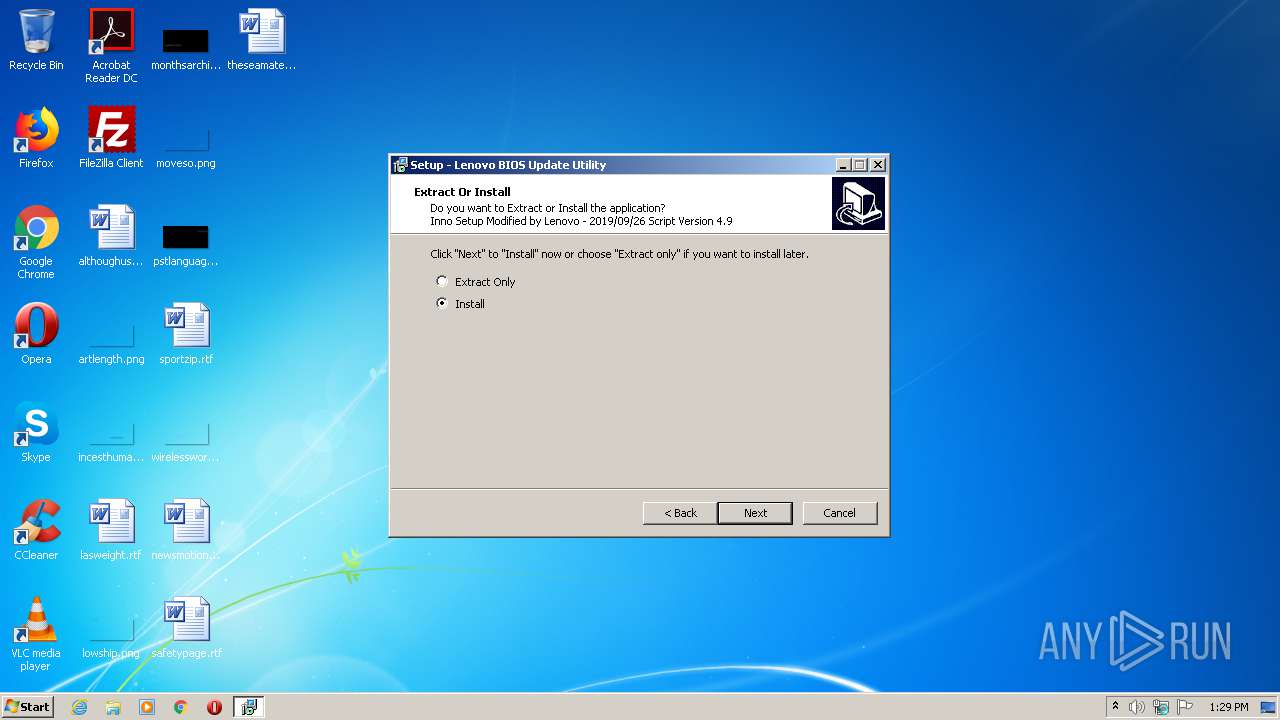
| Comments: | This installation was built with Inno Setup. |
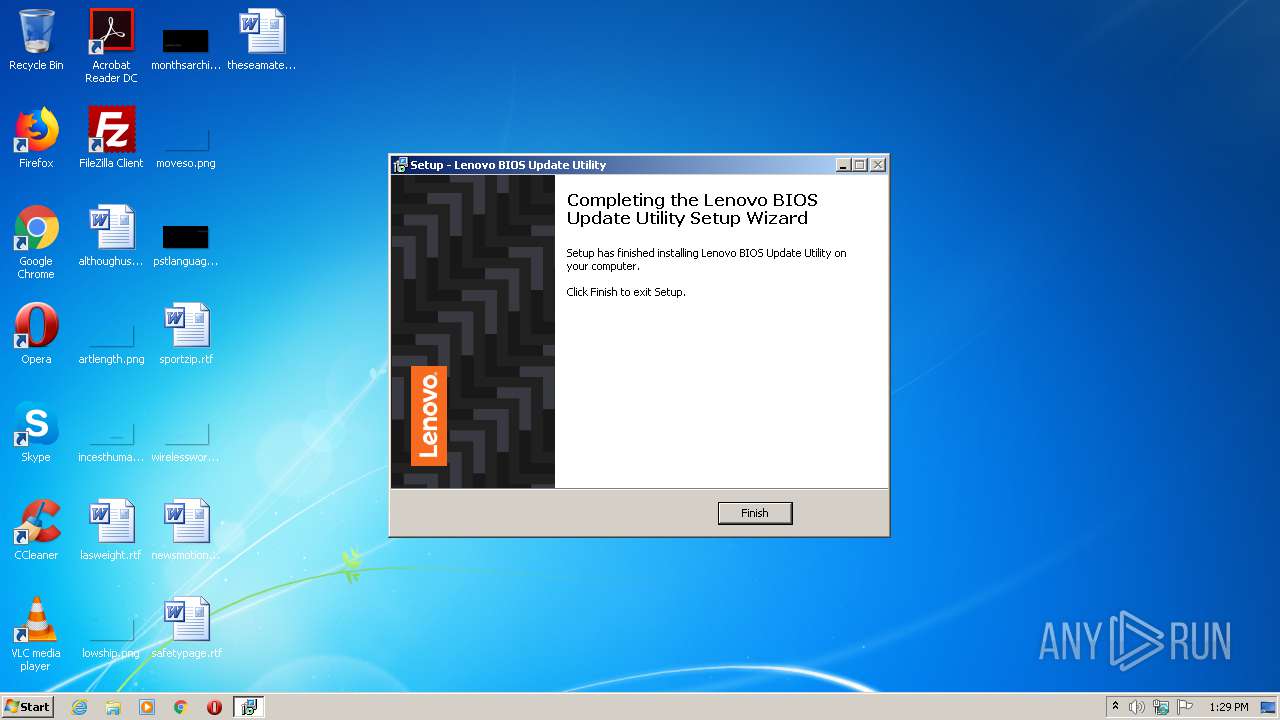
| CompanyName: | Lenovo Group Limited |
| FileDescription: | For Lenovo BIOS Updates |
| FileVersion: | 1.0.0.0 |
| LegalCopyright: | Copyright © Lenovo 2020 |
| ProductName: | Lenovo BIOS Update Utility |
| ProductVersion: | 1.33 |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 06-Jan-2020 06:31:46 |
| Detected languages: |
|
| Comments: | This installation was built with Inno Setup. |
| CompanyName: | Lenovo Group Limited |
| FileDescription: | For Lenovo BIOS Updates |
| FileVersion: | 1.0.0.0 |
| LegalCopyright: | Copyright © Lenovo 2020 |
| ProductName: | Lenovo BIOS Update Utility |
| ProductVersion: | 1.33 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0050 |
| Pages in file: | 0x0002 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x000F |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x001A |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000100 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 10 |
| Time date stamp: | 06-Jan-2020 06:31:46 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x00023AA0 | 0x00023C00 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.32291 |
.itext | 0x00025000 | 0x00001368 | 0x00001400 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 5.91348 |
.data | 0x00027000 | 0x00001628 | 0x00001800 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 3.32921 |
.bss | 0x00029000 | 0x00006158 | 0x00000000 | IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.idata | 0x00030000 | 0x00000648 | 0x00000800 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.08948 |
.didata | 0x00031000 | 0x00000E3E | 0x00001000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.2563 |
.edata | 0x00032000 | 0x00000071 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 1.3265 |
.tls | 0x00033000 | 0x00000014 | 0x00000000 | IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.rdata | 0x00034000 | 0x0000005D | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 1.37999 |
.rsrc | 0x00035000 | 0x00003800 | 0x00003800 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 4.78197 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.18481 | 2676 | UNKNOWN | English - United States | RT_MANIFEST |
2 | 3.47151 | 1384 | UNKNOWN | Dutch - Netherlands | RT_ICON |
3 | 3.91708 | 744 | UNKNOWN | Dutch - Netherlands | RT_ICON |
4 | 3.91366 | 2216 | UNKNOWN | Dutch - Netherlands | RT_ICON |
4090 | 3.19198 | 480 | UNKNOWN | UNKNOWN | RT_STRING |
4091 | 3.49576 | 404 | UNKNOWN | UNKNOWN | RT_STRING |
4092 | 3.34698 | 204 | UNKNOWN | UNKNOWN | RT_STRING |
4093 | 3.3307 | 468 | UNKNOWN | UNKNOWN | RT_STRING |
4094 | 3.29214 | 736 | UNKNOWN | UNKNOWN | RT_STRING |
4095 | 3.31877 | 852 | UNKNOWN | UNKNOWN | RT_STRING |
Imports
advapi32.dll |
comctl32.dll |
kernel32.dll |
kernel32.dll (delay-loaded) |
oleaut32.dll |
user32.dll |
Exports
Title | Ordinal | Address |
|---|---|---|
dbkFCallWrapperAddr | 1 | 0x0002C58C |
__dbk_fcall_wrapper | 2 | 0x0000B294 |
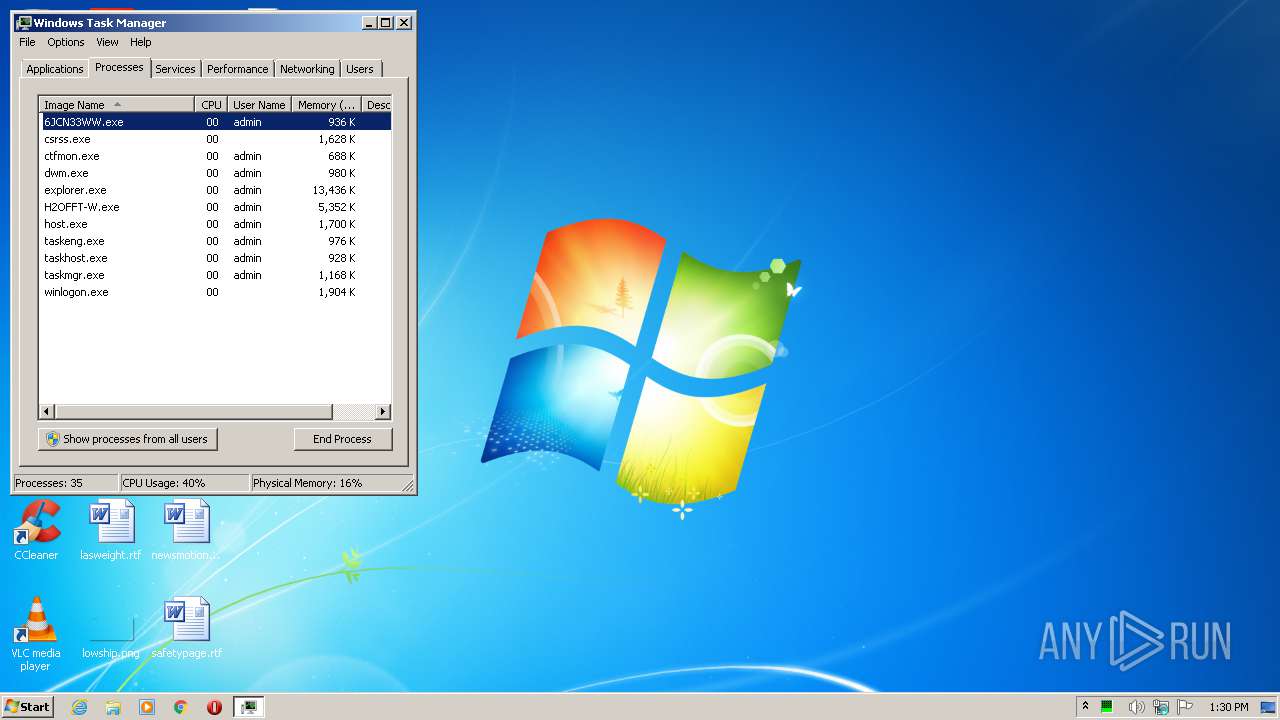
Total processes
61
Monitored processes
17
Malicious processes
8
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 308 | "C:\Windows\TempInst\is-CC2C9.tmp\6jcn33ww.tmp" /SL5="$2013C,6695201,180224,C:\Users\admin\AppData\Local\Temp\6jcn33ww.exe" /SPAWNWND=$20132 /NOTIFYWND=$20138 | C:\Windows\TempInst\is-CC2C9.tmp\6jcn33ww.tmp | 6jcn33ww.exe | ||||||||||||
User: admin Integrity Level: HIGH Description: Setup/Uninstall Exit code: 0 Version: 51.1052.0.0 Modules
| |||||||||||||||
| 2008 | "C:\Windows\system32\schtasks.exe" /CHANGE /TN "\LenovoCleanupTasks-20200410.132943" /TR "C:\Windows\system32\cmd.exe /C 'C:\Windows\system32\schtasks.exe /Delete /TN LenovoCleanupFolder-20200410.132943 /F && C:\Windows\system32\schtasks.exe /Delete /TN LenovoCleanupTasks-20200410.132943 /F'" | C:\Windows\system32\schtasks.exe | — | 6jcn33ww.tmp | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Manages scheduled tasks Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2016 | "C:\Windows\system32\schtasks.exe" /CREATE /XML C:\Drivers\Flash\20200410.13292998\DeleteTasks.xml /TN "\LenovoCleanupTasks-20200410.132943" | C:\Windows\system32\schtasks.exe | — | 6jcn33ww.tmp | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Manages scheduled tasks Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2268 | "C:\Windows\system32\icacls.exe" C:\Drivers /inheritance:r /C /L /Q | C:\Windows\system32\icacls.exe | — | 6jcn33ww.tmp | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2372 | "C:\Windows\system32\icacls.exe" C:\Drivers /inheritance:e /grant:r *S-1-5-32-544:(OI)(CI)F *S-1-5-18:(OI)(CI)F *S-1-5-32-545:(OI)(CI)RX /T /C /L /Q | C:\Windows\system32\icacls.exe | — | 6jcn33ww.tmp | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2396 | "C:\Windows\system32\takeown.exe" /f C:\Drivers /a /r /d y | C:\Windows\system32\takeown.exe | — | 6jcn33ww.tmp | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Takes ownership of a file Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2496 | "C:\Windows\system32\taskmgr.exe" /4 | C:\Windows\system32\taskmgr.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Task Manager Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2528 | DrvInst.exe "2" "211" "ROOT\INSYDEDEVICE\0000" "C:\Windows\INF\oem4.inf" "h2offt.inf:Standard.NTx86:Insyde_Device32:6.1.7600.16385:{416c2604-443b-436f-9e1d-607bdc3cc785}\h2offt" "6ddc5e3bb" "00000568" "000005C8" "000005CC" | C:\Windows\system32\DrvInst.exe | svchost.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Driver Installation Module Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2580 | "C:\Windows\system32\schtasks.exe" /CHANGE /TN "\LenovoCleanupFolder-20200410.132943" /TR "C:\Windows\system32\cmd.exe /C 'rd /s /q C:\Drivers\Flash\20200410.13292998\" | C:\Windows\system32\schtasks.exe | — | 6jcn33ww.tmp | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Manages scheduled tasks Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2804 | .\H2OFFT-W.exe -sfx7z "C:\Drivers\Flash\20200410.13292998" execApp | C:\Users\admin\AppData\Local\Temp\7zSCB78.tmp\H2OFFT-W.exe | 6JCN33WW.exe | ||||||||||||
User: admin Company: Insyde Software Corp. Integrity Level: HIGH Description: Insyde H2OFFT Exit code: 0 Version: 6.20 Modules
| |||||||||||||||
Total events
522
Read events
471
Write events
45
Delete events
6
Modification events
| (PID) Process: | (308) 6jcn33ww.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\RestartManager\Session0000 |
| Operation: | write | Name: | Owner |
Value: 3401000020B7F7004A9AD601 | |||
| (PID) Process: | (308) 6jcn33ww.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\RestartManager\Session0000 |
| Operation: | write | Name: | SessionHash |
Value: E401D9204D1CE678067268686F064944EA658059DA3CF0911CAE261004BDD7E4 | |||
| (PID) Process: | (308) 6jcn33ww.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\RestartManager\Session0000 |
| Operation: | write | Name: | Sequence |
Value: 1 | |||
| (PID) Process: | (308) 6jcn33ww.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\RestartManager\Session0000 |
| Operation: | write | Name: | RegFiles0000 |
Value: C:\Drivers\Flash\20200410.13292998\6JCN33WW.exe | |||
| (PID) Process: | (308) 6jcn33ww.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\RestartManager\Session0000 |
| Operation: | write | Name: | RegFilesHash |
Value: 3C2E06AB9071FF43198A342D5D784F4447DEB2D34D6FA1E8D8A3903778499C55 | |||
| (PID) Process: | (308) 6jcn33ww.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\RestartManager\Session0000 |
| Operation: | delete value | Name: | RegFilesHash |
Value: 3C2E06AB9071FF43198A342D5D784F4447DEB2D34D6FA1E8D8A3903778499C55 | |||
| (PID) Process: | (308) 6jcn33ww.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\RestartManager\Session0000 |
| Operation: | delete value | Name: | RegFiles0000 |
Value: C:\Drivers\Flash\20200410.13292998\6JCN33WW.exe | |||
| (PID) Process: | (308) 6jcn33ww.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\RestartManager\Session0000 |
| Operation: | delete value | Name: | Sequence |
Value: 1 | |||
| (PID) Process: | (308) 6jcn33ww.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\RestartManager\Session0000 |
| Operation: | delete value | Name: | SessionHash |
Value: E401D9204D1CE678067268686F064944EA658059DA3CF0911CAE261004BDD7E4 | |||
| (PID) Process: | (308) 6jcn33ww.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\RestartManager\Session0000 |
| Operation: | delete value | Name: | Owner |
Value: 3401000020B7F7004A9AD601 | |||
Executable files
15
Suspicious files
15
Text files
57
Unknown types
8
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
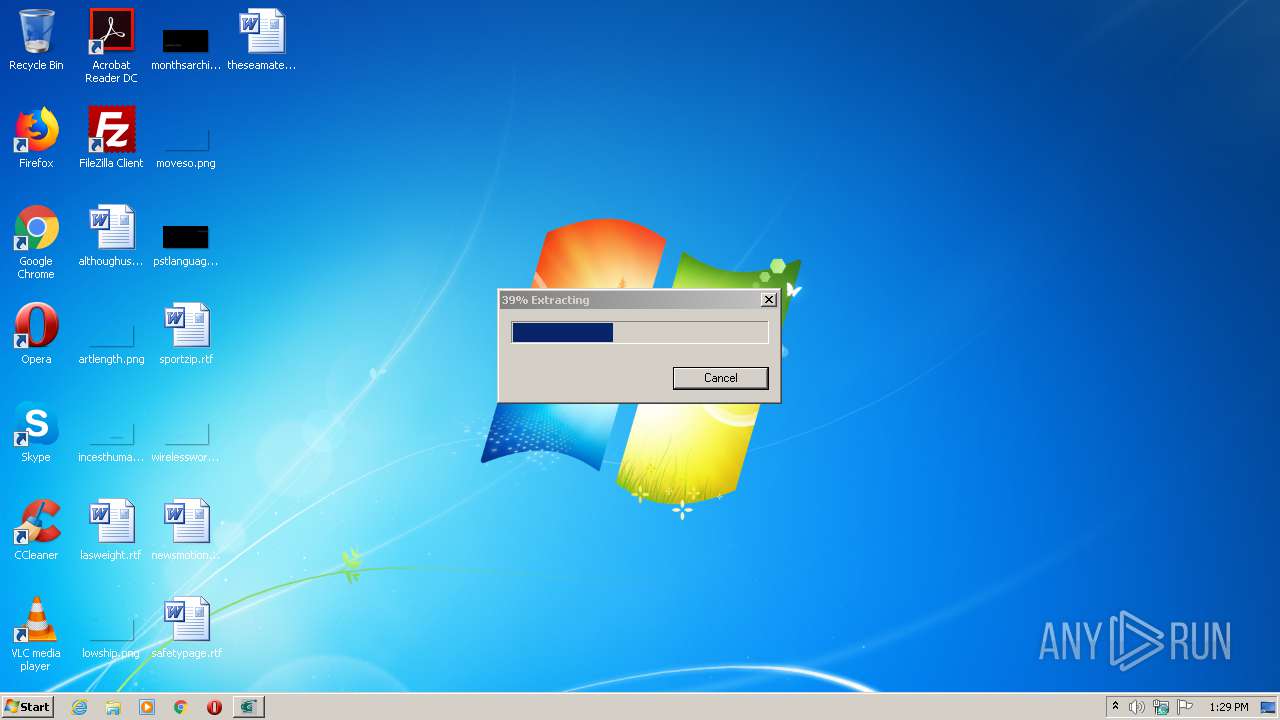
| 308 | 6jcn33ww.tmp | C:\Drivers\Flash\20200410.13292998\is-6D7MA.tmp | — | |
MD5:— | SHA256:— | |||
| 308 | 6jcn33ww.tmp | C:\Drivers\Flash\20200410.13292998\is-BVEHQ.tmp | — | |
MD5:— | SHA256:— | |||
| 3448 | 6JCN33WW.exe | C:\Users\admin\AppData\Local\Temp\7zSCB78.tmp\platform.ini | text | |
MD5:— | SHA256:— | |||
| 2804 | H2OFFT-W.exe | C:\Users\admin\AppData\Local\Temp\CabCF70.tmp | — | |
MD5:— | SHA256:— | |||
| 2804 | H2OFFT-W.exe | C:\Users\admin\AppData\Local\Temp\TarCF71.tmp | — | |
MD5:— | SHA256:— | |||
| 2804 | H2OFFT-W.exe | C:\Users\admin\AppData\Local\Temp\CabCF81.tmp | — | |
MD5:— | SHA256:— | |||
| 2804 | H2OFFT-W.exe | C:\Users\admin\AppData\Local\Temp\TarCF92.tmp | — | |
MD5:— | SHA256:— | |||
| 308 | 6jcn33ww.tmp | C:\Drivers\Flash\20200410.13292998\6JCN33WW.exe | executable | |
MD5:— | SHA256:— | |||
| 3448 | 6JCN33WW.exe | C:\Users\admin\AppData\Local\Temp\7zSCB78.tmp\BIOS.fd | executable | |
MD5:— | SHA256:— | |||
| 2804 | H2OFFT-W.exe | C:\Users\admin\AppData\Local\Temp\CabD06E.tmp | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
3
TCP/UDP connections
1
DNS requests
1
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2804 | H2OFFT-W.exe | GET | 304 | 2.16.106.186:80 | http://www.download.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab | unknown | compressed | 57.5 Kb | whitelisted |
2804 | H2OFFT-W.exe | GET | 200 | 2.16.106.186:80 | http://www.download.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab | unknown | compressed | 57.5 Kb | whitelisted |
2804 | H2OFFT-W.exe | GET | 304 | 2.16.106.186:80 | http://www.download.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab | unknown | compressed | 57.5 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2804 | H2OFFT-W.exe | 2.16.106.186:80 | www.download.windowsupdate.com | Akamai International B.V. | — | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.download.windowsupdate.com |
| whitelisted |