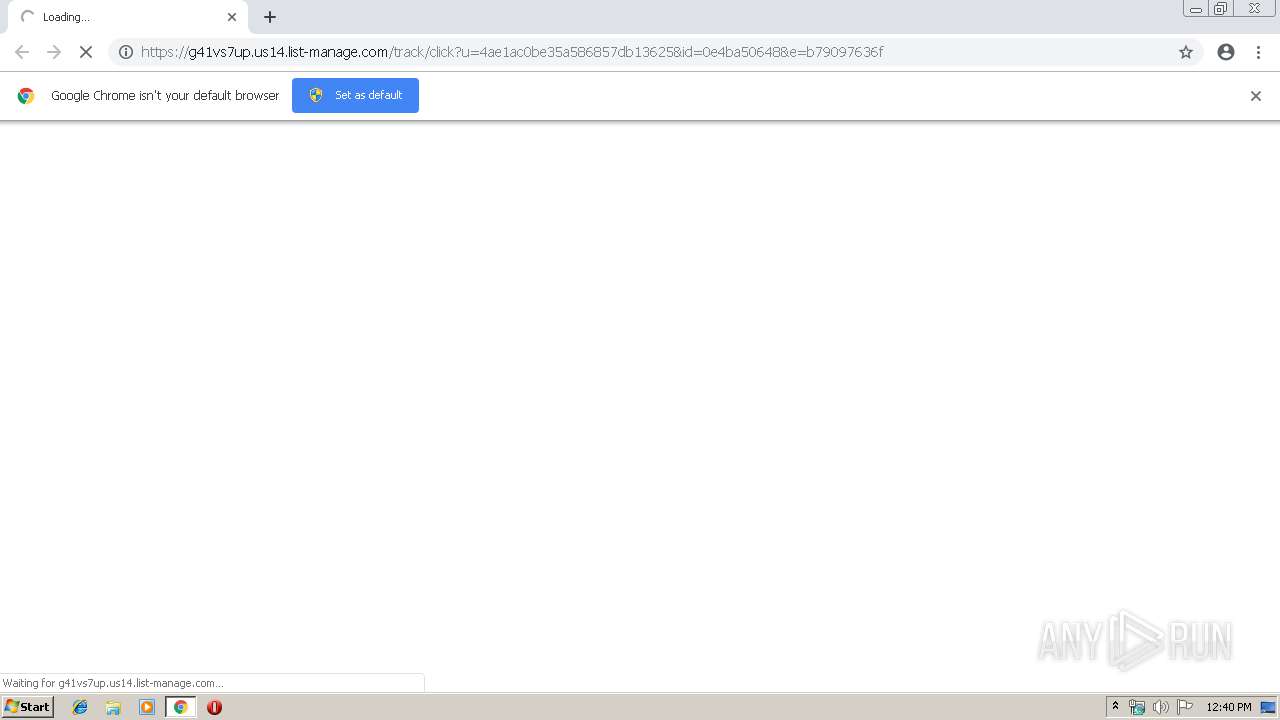
| URL: | https://G41Vs7Up.us14.list-manage.com/track/click?u=4ae1ac0be35a586857db13625&id=0e4ba50648&e=b79097636f |
| Full analysis: | https://app.any.run/tasks/aae4bd2d-14da-4610-9a0b-ddb49412e19d |
| Verdict: | Malicious activity |
| Analysis date: | March 21, 2019, 12:40:04 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 081B7DDC5DFC0DA65F9EE1092D1CF1C9 |
| SHA1: | EA10A1AE2BA44BAC6FD8096385AB5905EA8898FA |
| SHA256: | 7EB3411560205747F83BE076AD62F4C67517E4B3A8E982180E33D2C2ADBBA6E7 |
| SSDEEP: | 3:N8Mw7IVULGGRXEGcJMkN4t8EQd2E0j0HRdDDvUD:2V7kULEGcJMpqEQdba0HRdDe |
MALICIOUS
No malicious indicators.SUSPICIOUS
No suspicious indicators.INFO
Application launched itself
- chrome.exe (PID: 1748)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
40
Monitored processes
11
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 660 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=904,6907526002362335447,9360612466800495537,131072 --enable-features=PasswordImport --lang=en-US --no-sandbox --service-request-channel-token=15680428166537765216 --mojo-platform-channel-handle=948 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 720 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=watcher --main-thread-id=1708 --on-initialized-event-handle=308 --parent-handle=312 /prefetch:6 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 892 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=904,6907526002362335447,9360612466800495537,131072 --enable-features=PasswordImport --service-pipe-token=301226273589791017 --lang=en-US --extension-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=301226273589791017 --renderer-client-id=4 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2292 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 1088 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=904,6907526002362335447,9360612466800495537,131072 --enable-features=PasswordImport --disable-gpu-compositing --service-pipe-token=674033160786936128 --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=674033160786936128 --renderer-client-id=7 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3068 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 1748 | "C:\Program Files\Google\Chrome\Application\chrome.exe" https://G41Vs7Up.us14.list-manage.com/track/click?u=4ae1ac0be35a586857db13625&id=0e4ba50648&e=b79097636f | C:\Program Files\Google\Chrome\Application\chrome.exe | explorer.exe | ||||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 1908 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=904,6907526002362335447,9360612466800495537,131072 --enable-features=PasswordImport --service-pipe-token=7192034131873126549 --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=7192034131873126549 --renderer-client-id=6 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2108 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 2268 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=904,6907526002362335447,9360612466800495537,131072 --enable-features=PasswordImport --service-pipe-token=10240530172174390553 --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=10240530172174390553 --renderer-client-id=5 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=1920 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 2600 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=904,6907526002362335447,9360612466800495537,131072 --enable-features=PasswordImport --disable-gpu-sandbox --use-gl=disabled --gpu-preferences=KAAAAAAAAACAAwAAAQAAAAAAAAAAAGAAAAAAAAEAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --service-request-channel-token=13098599831608435319 --mojo-platform-channel-handle=2224 /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 2732 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" /prefetch:7 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad" "--metrics-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" --url=https://clients2.google.com/cr/report --annotation=channel= --annotation=plat=Win32 --annotation=prod=Chrome --annotation=ver=73.0.3683.75 --initial-client-data=0x7c,0x80,0x84,0x78,0x88,0x6f620f18,0x6f620f28,0x6f620f34 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 3116 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=904,6907526002362335447,9360612466800495537,131072 --enable-features=PasswordImport --gpu-preferences=KAAAAAAAAACAAwAAAQAAAAAAAAAAAGAAAAAAAAEAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --service-request-channel-token=8909249717440743738 --mojo-platform-channel-handle=1004 --ignored=" --type=renderer " /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
Total events
521
Read events
469
Write events
49
Delete events
3
Modification events
| (PID) Process: | (1748) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (1748) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (1748) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (1748) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (1748) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (720) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 1748-13197645622260750 |
Value: 259 | |||
| (PID) Process: | (1748) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (1748) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (1748) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 3488-13197474229333984 |
Value: 0 | |||
| (PID) Process: | (1748) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
Executable files
0
Suspicious files
12
Text files
47
Unknown types
3
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1748 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\index | — | |
MD5:— | SHA256:— | |||
| 1748 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_0 | — | |
MD5:— | SHA256:— | |||
| 1748 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_1 | — | |
MD5:— | SHA256:— | |||
| 1748 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_2 | — | |
MD5:— | SHA256:— | |||
| 1748 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_3 | — | |
MD5:— | SHA256:— | |||
| 1748 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\473d17f0-265c-4963-9586-a36b0dfc3a68.tmp | — | |
MD5:— | SHA256:— | |||
| 1748 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000018.dbtmp | — | |
MD5:— | SHA256:— | |||
| 1748 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\GPUCache\index | — | |
MD5:— | SHA256:— | |||
| 1748 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\GPUCache\data_0 | — | |
MD5:— | SHA256:— | |||
| 1748 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\GPUCache\data_1 | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
57
TCP/UDP connections
65
DNS requests
10
Threats
58
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
4004 | chrome.exe | GET | — | 47.254.145.114:80 | http://landmoney.su/crypto-pre/2164/pre/images/zz1.jpg | US | — | — | suspicious |
4004 | chrome.exe | GET | 302 | 91.215.153.90:80 | http://top.nov.ru/hBm79Q | BG | — | — | suspicious |
4004 | chrome.exe | GET | — | 47.254.145.114:80 | http://landmoney.su/crypto-pre/2164/pre/images/mst1.jpg | US | — | — | suspicious |
4004 | chrome.exe | GET | 200 | 47.254.145.114:80 | http://landmoney.su/crypto-pre/2164/pre/css/bootstrap.css | US | text | 19.5 Kb | suspicious |
4004 | chrome.exe | GET | 200 | 47.254.145.114:80 | http://landmoney.su/crypto-pre/2164/pre/images/asseenin.jpg | US | image | 17.2 Kb | suspicious |
4004 | chrome.exe | GET | 200 | 47.254.145.114:80 | http://landmoney.su/crypto-pre/?flow=77&l=41&dm=landmoney.su | US | html | 13.8 Kb | suspicious |
4004 | chrome.exe | GET | 200 | 47.254.145.114:80 | http://landmoney.su/crypto-pre/2164/pre/css/font-awesome.css | US | text | 4.92 Kb | suspicious |
4004 | chrome.exe | GET | 200 | 47.254.145.114:80 | http://landmoney.su/crypto-pre/2164/pre/js/timer2.js | US | text | 9.61 Kb | suspicious |
4004 | chrome.exe | GET | 200 | 47.254.145.114:80 | http://landmoney.su/crypto-pre/2164/pre/css/style.css | US | text | 8.96 Kb | suspicious |
4004 | chrome.exe | GET | 200 | 47.254.145.114:80 | http://landmoney.su/crypto-pre/2164/pre/js/timer.js | US | text | 32.0 Kb | suspicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4004 | chrome.exe | 172.217.16.195:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
4004 | chrome.exe | 104.111.241.197:443 | g41vs7up.us14.list-manage.com | Akamai International B.V. | NL | whitelisted |
4004 | chrome.exe | 172.217.18.173:443 | accounts.google.com | Google Inc. | US | whitelisted |
4004 | chrome.exe | 91.215.153.90:80 | top.nov.ru | ITL Company | BG | suspicious |
4004 | chrome.exe | 47.254.145.114:80 | moneyone.su | Alibaba (China) Technology Co., Ltd. | US | suspicious |
4004 | chrome.exe | 104.18.45.204:443 | cdn.dolly.media | Cloudflare Inc | US | shared |
4004 | chrome.exe | 172.217.16.142:443 | clients1.google.com | Google Inc. | US | whitelisted |
4004 | chrome.exe | 172.217.22.67:443 | ssl.gstatic.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
g41vs7up.us14.list-manage.com |
| unknown |
clientservices.googleapis.com |
| whitelisted |
accounts.google.com |
| shared |
top.nov.ru |
| suspicious |
moneyone.su |
| suspicious |
landmoney.su |
| suspicious |
cdn.dolly.media |
| whitelisted |
www.facebook.com |
| whitelisted |
clients1.google.com |
| whitelisted |
ssl.gstatic.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1072 | svchost.exe | Potentially Bad Traffic | ET DNS Query for .su TLD (Soviet Union) Often Malware Related |
4004 | chrome.exe | Potentially Bad Traffic | ET CURRENT_EVENTS Possible Keitaro TDS Redirect |
4004 | chrome.exe | Potentially Bad Traffic | ET POLICY HTTP Request to .su TLD (Soviet Union) Often Malware Related |
1072 | svchost.exe | Potentially Bad Traffic | ET DNS Query for .su TLD (Soviet Union) Often Malware Related |
4004 | chrome.exe | Potentially Bad Traffic | ET POLICY HTTP Request to .su TLD (Soviet Union) Often Malware Related |
4004 | chrome.exe | Potentially Bad Traffic | ET POLICY HTTP Request to .su TLD (Soviet Union) Often Malware Related |
4004 | chrome.exe | Potentially Bad Traffic | ET POLICY HTTP Request to .su TLD (Soviet Union) Often Malware Related |
4004 | chrome.exe | Potentially Bad Traffic | ET POLICY HTTP Request to .su TLD (Soviet Union) Often Malware Related |
4004 | chrome.exe | Potentially Bad Traffic | ET POLICY HTTP Request to .su TLD (Soviet Union) Often Malware Related |
4004 | chrome.exe | Potentially Bad Traffic | ET POLICY HTTP Request to .su TLD (Soviet Union) Often Malware Related |