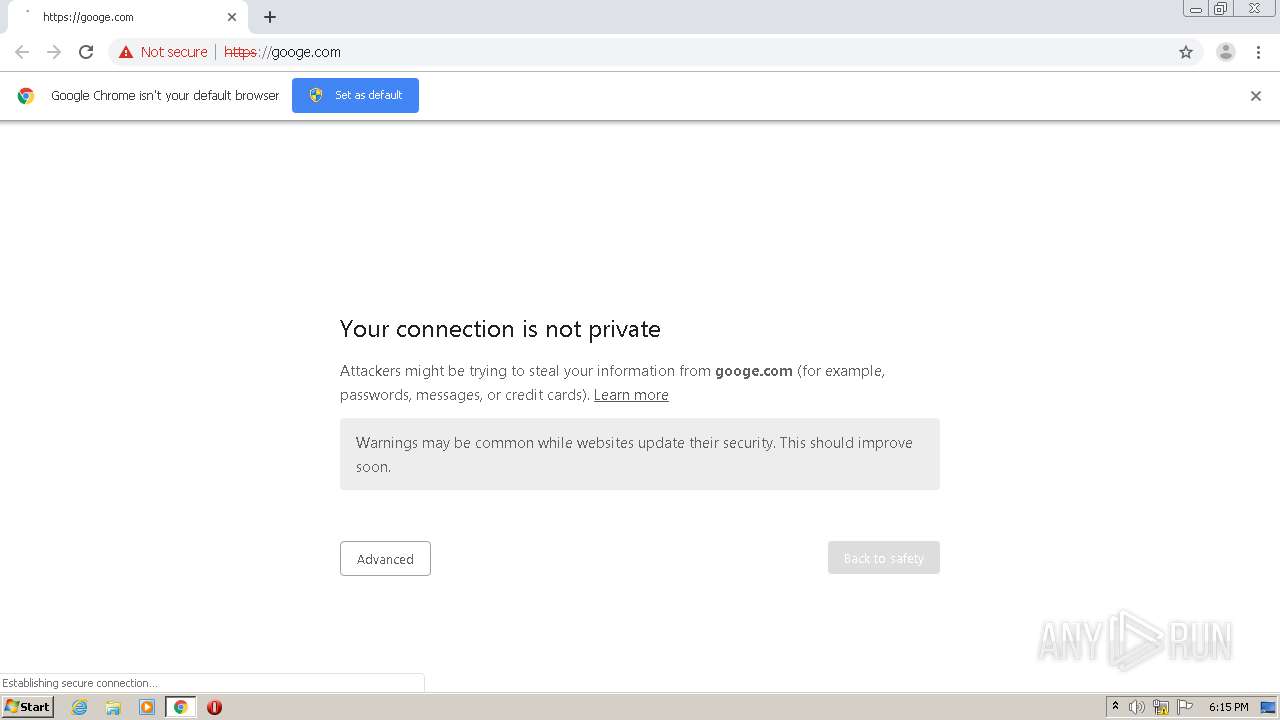
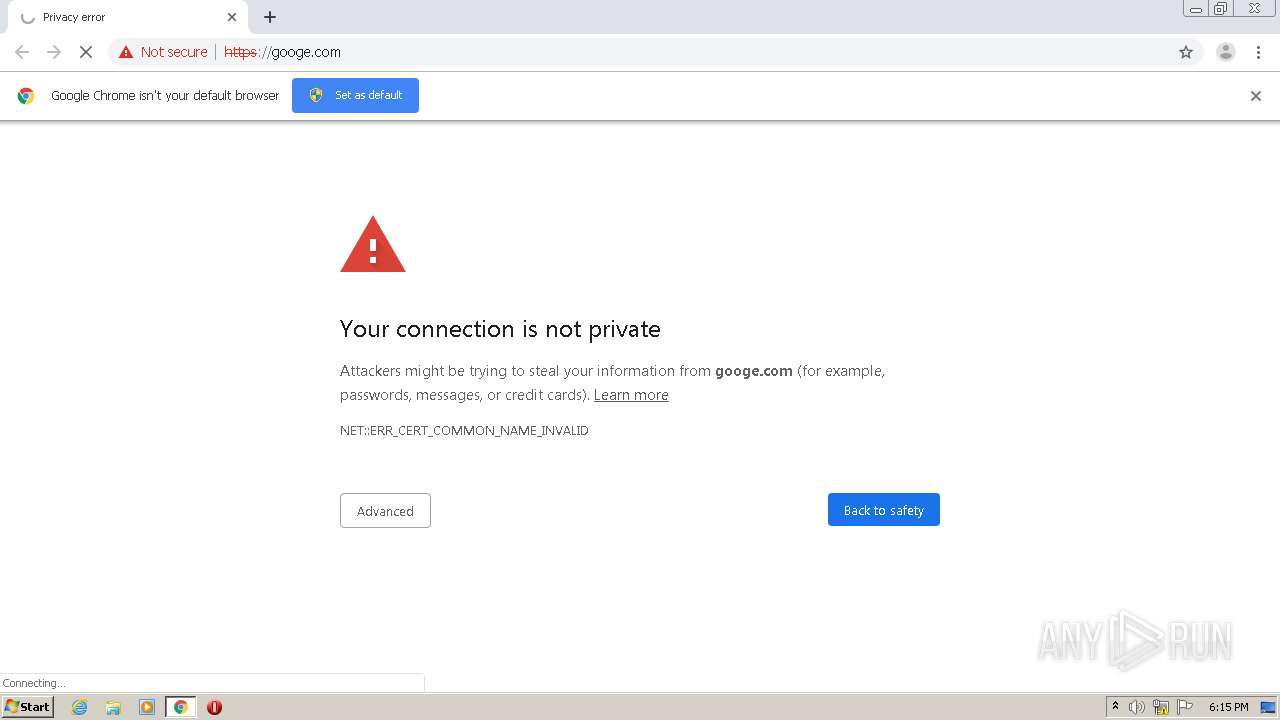
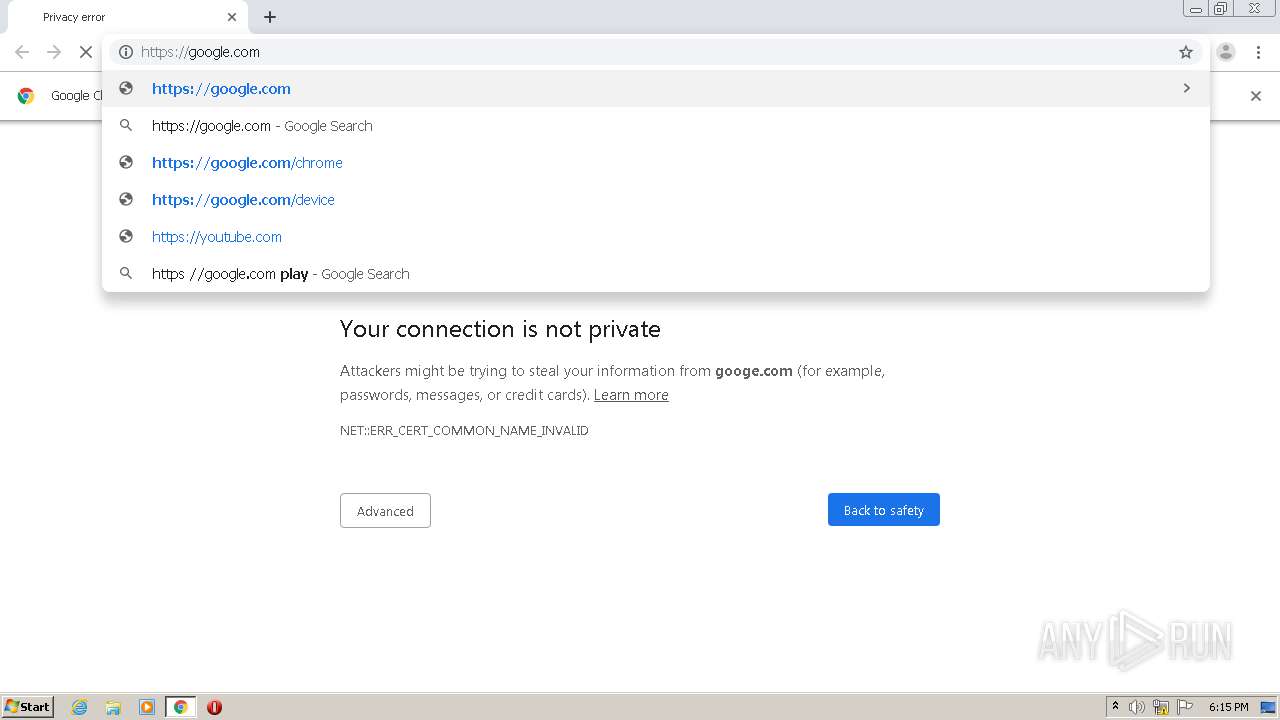
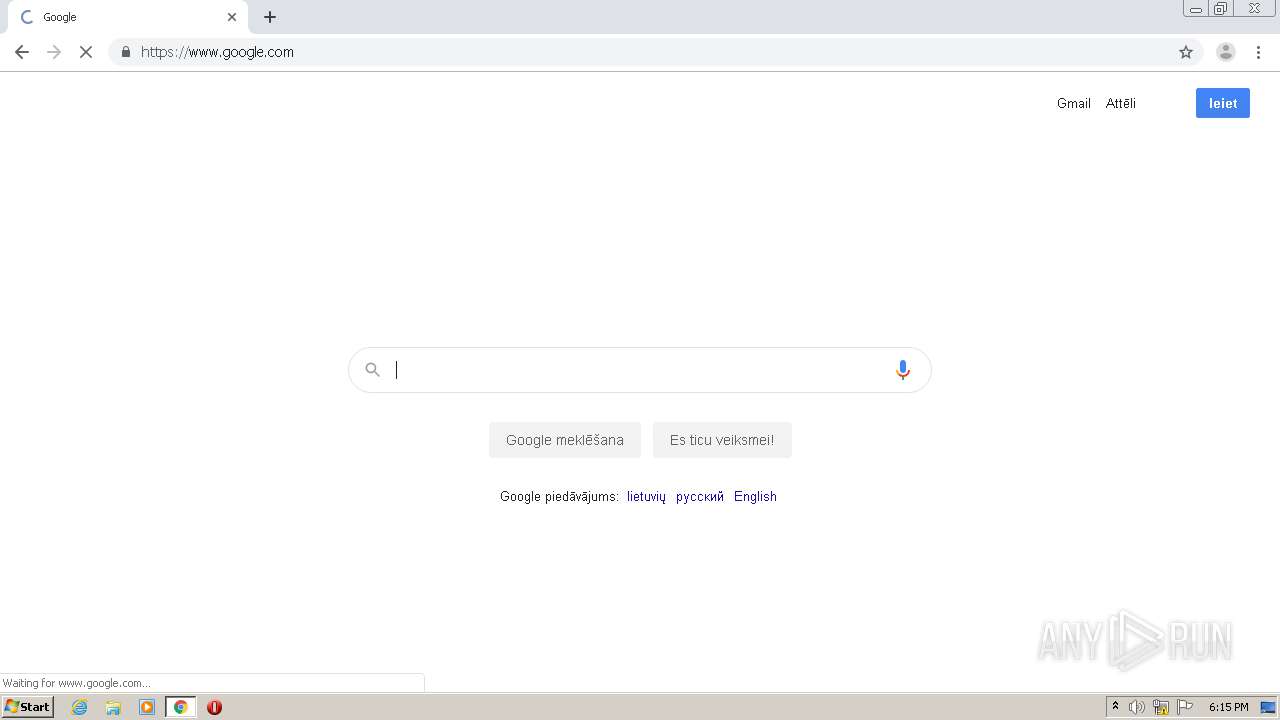
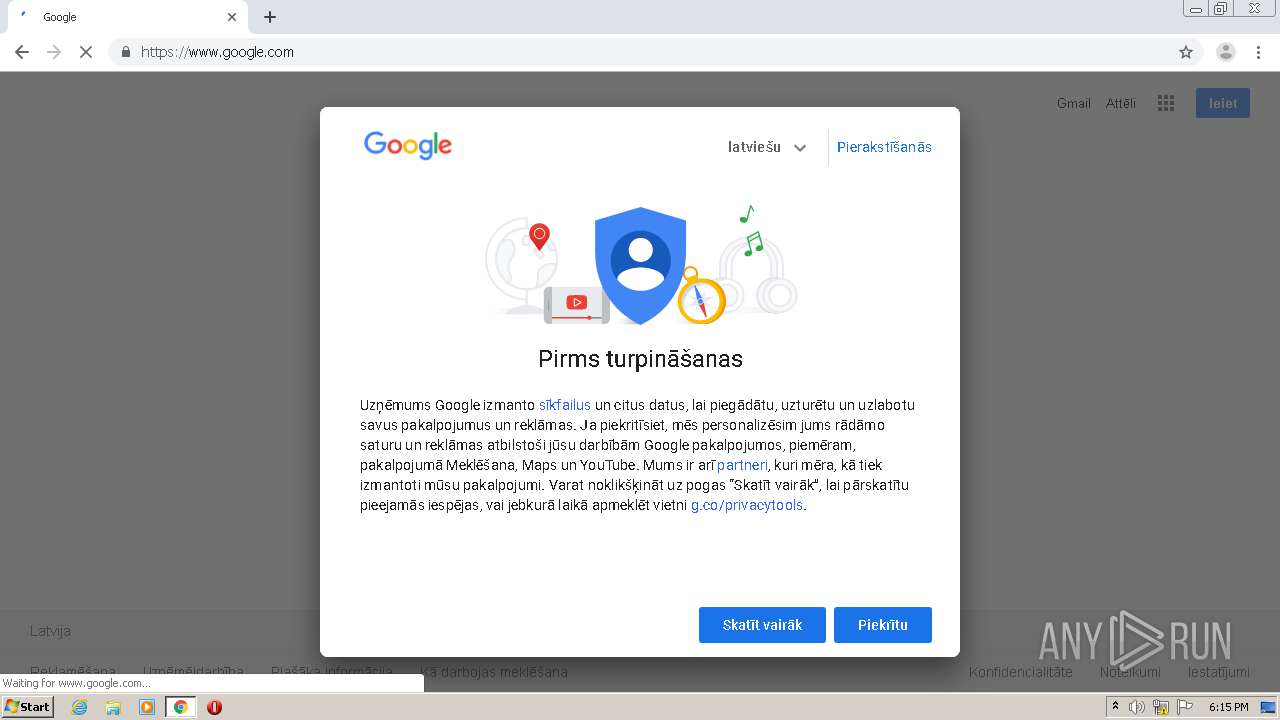
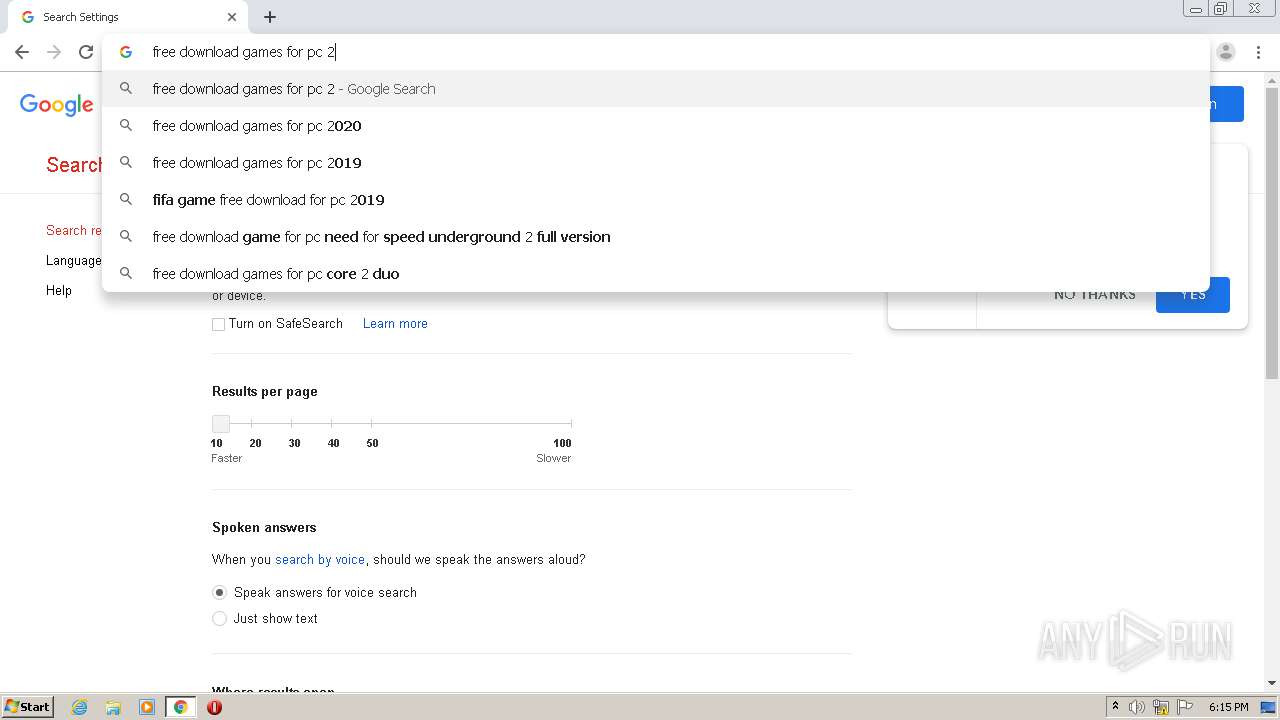
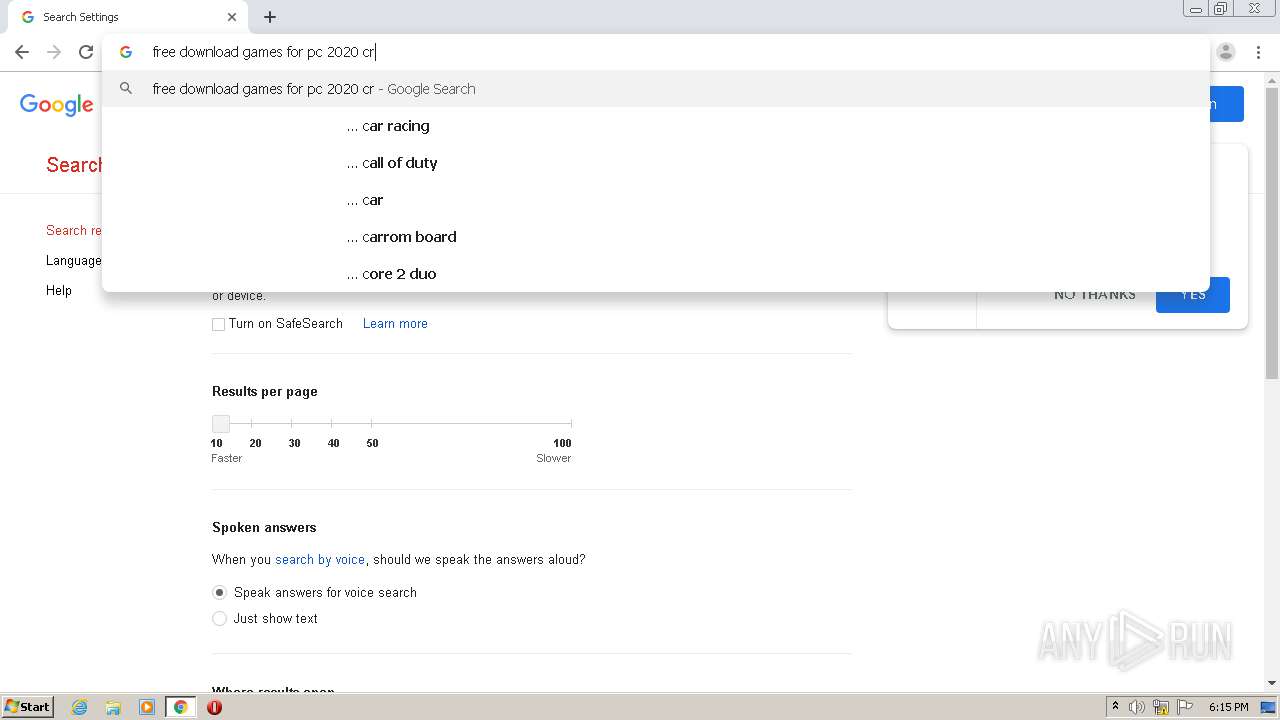
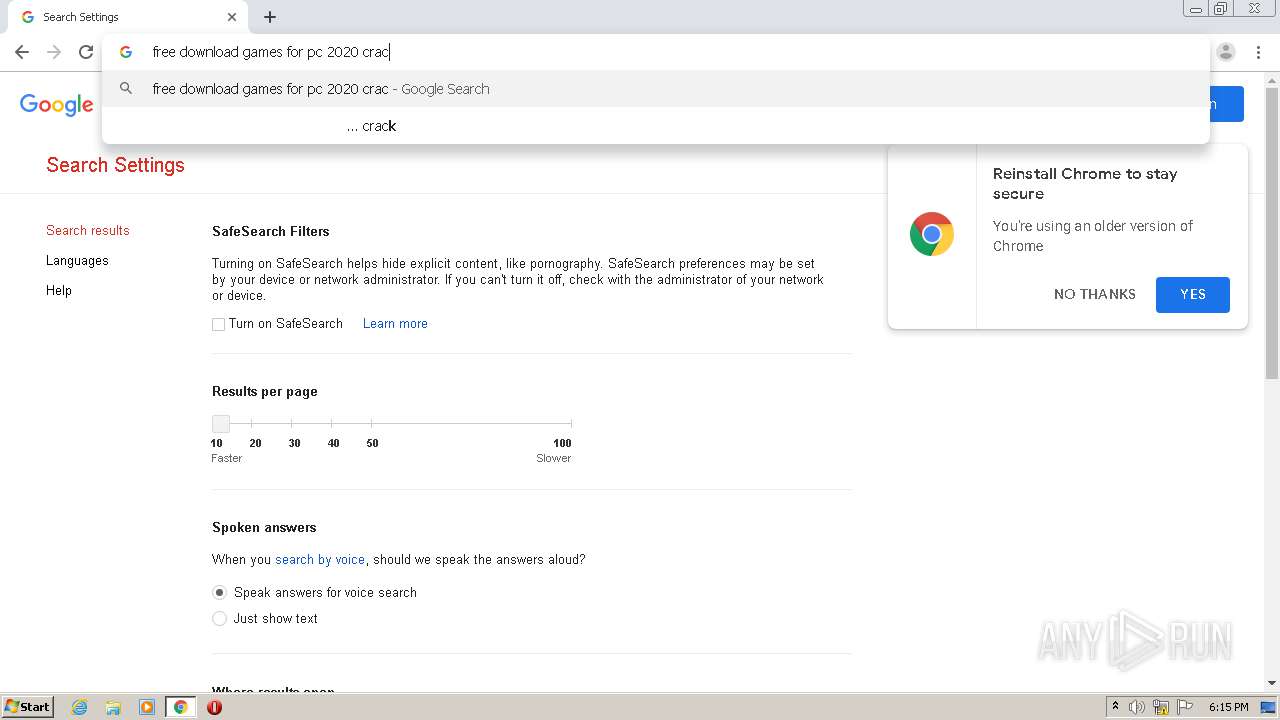
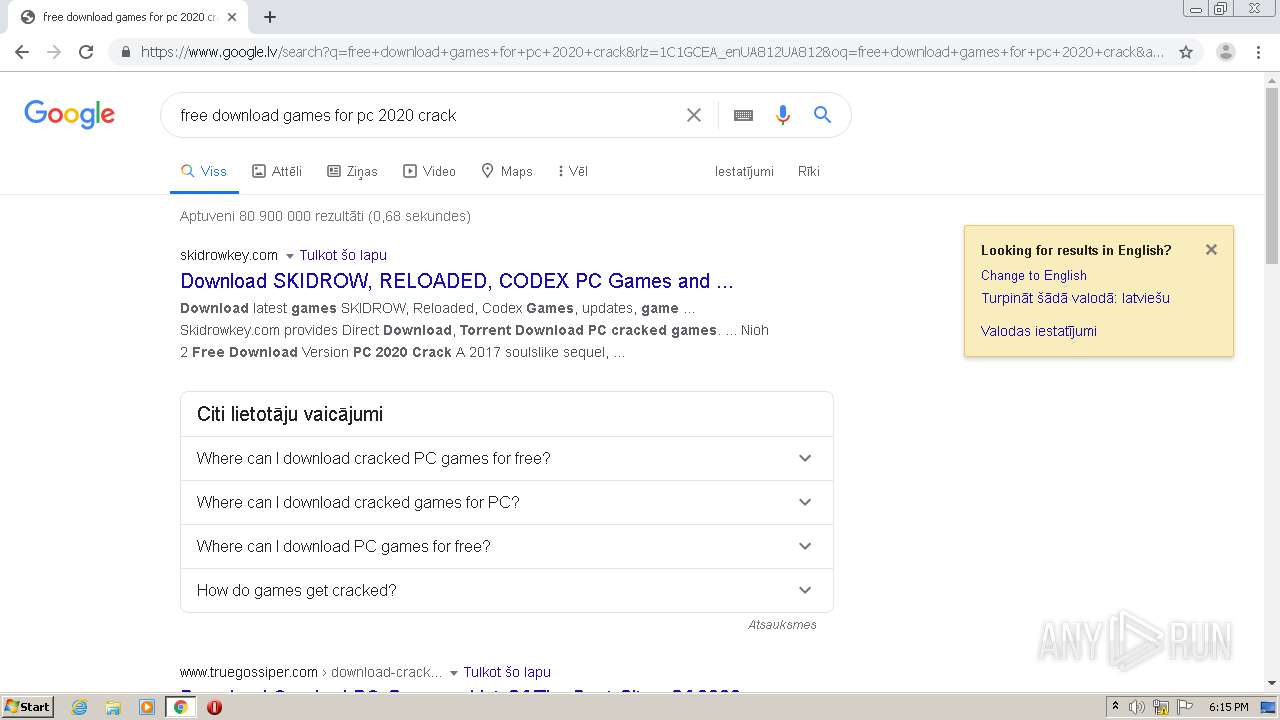
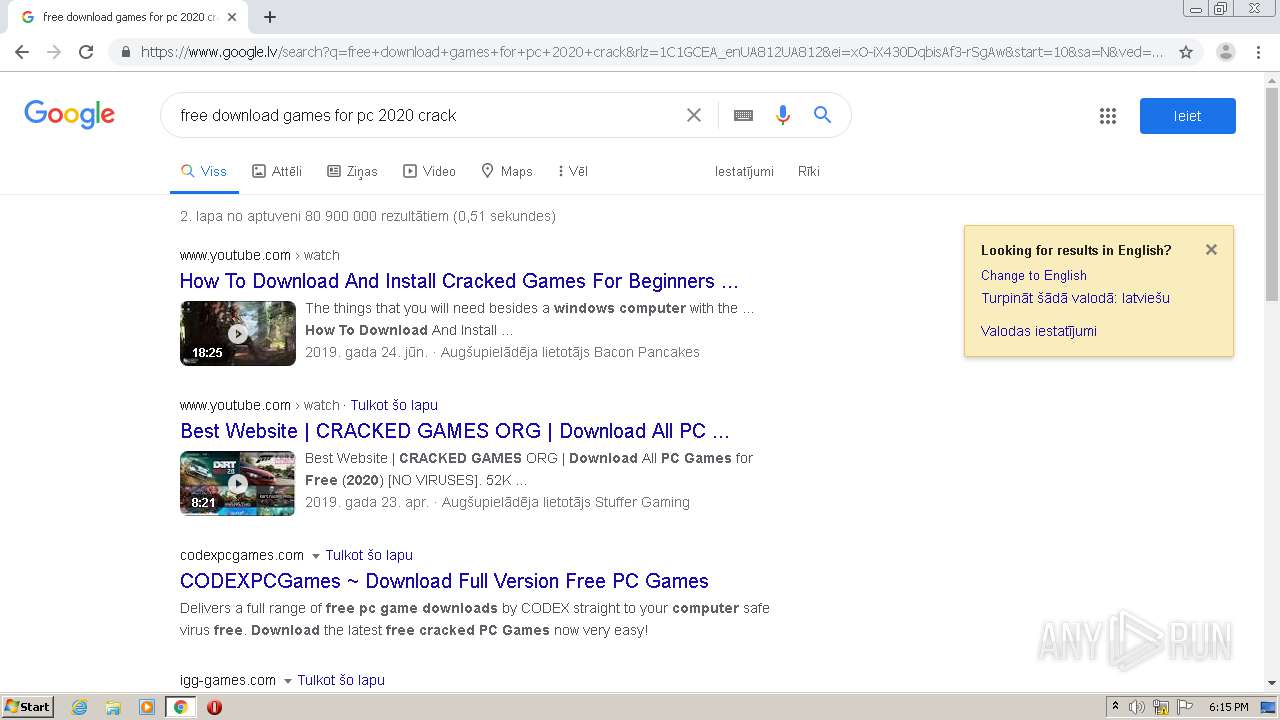
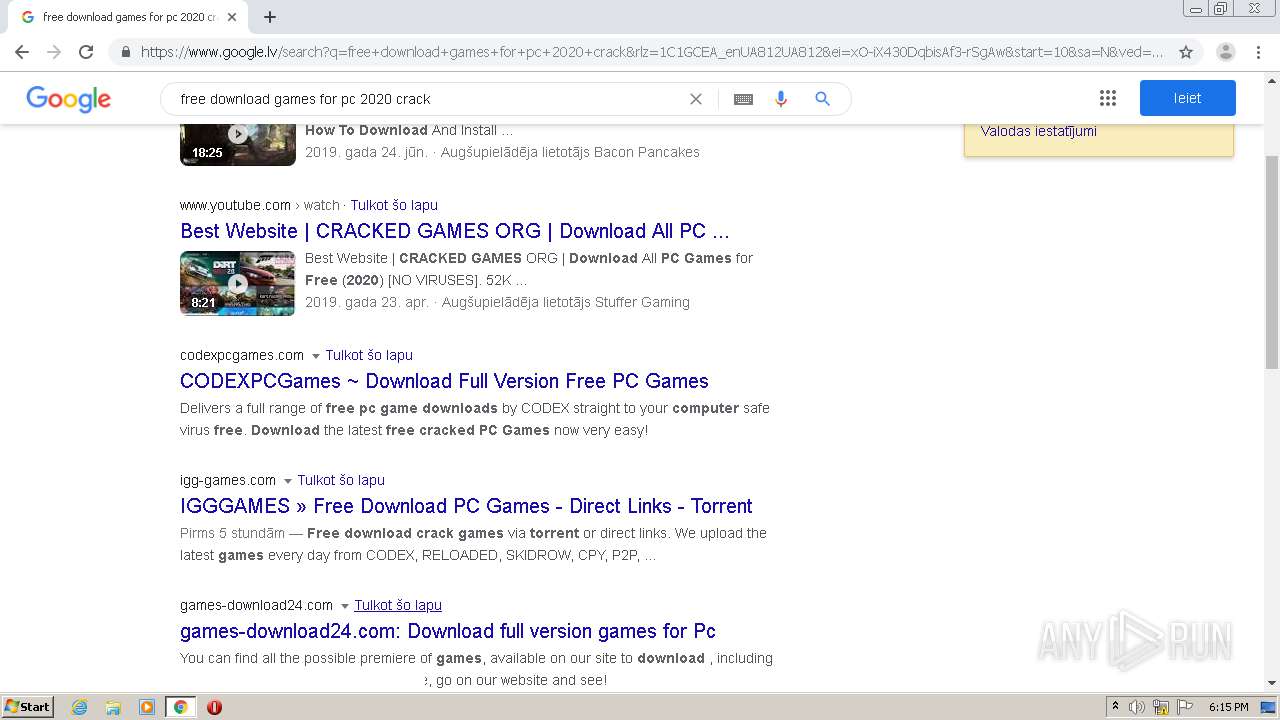
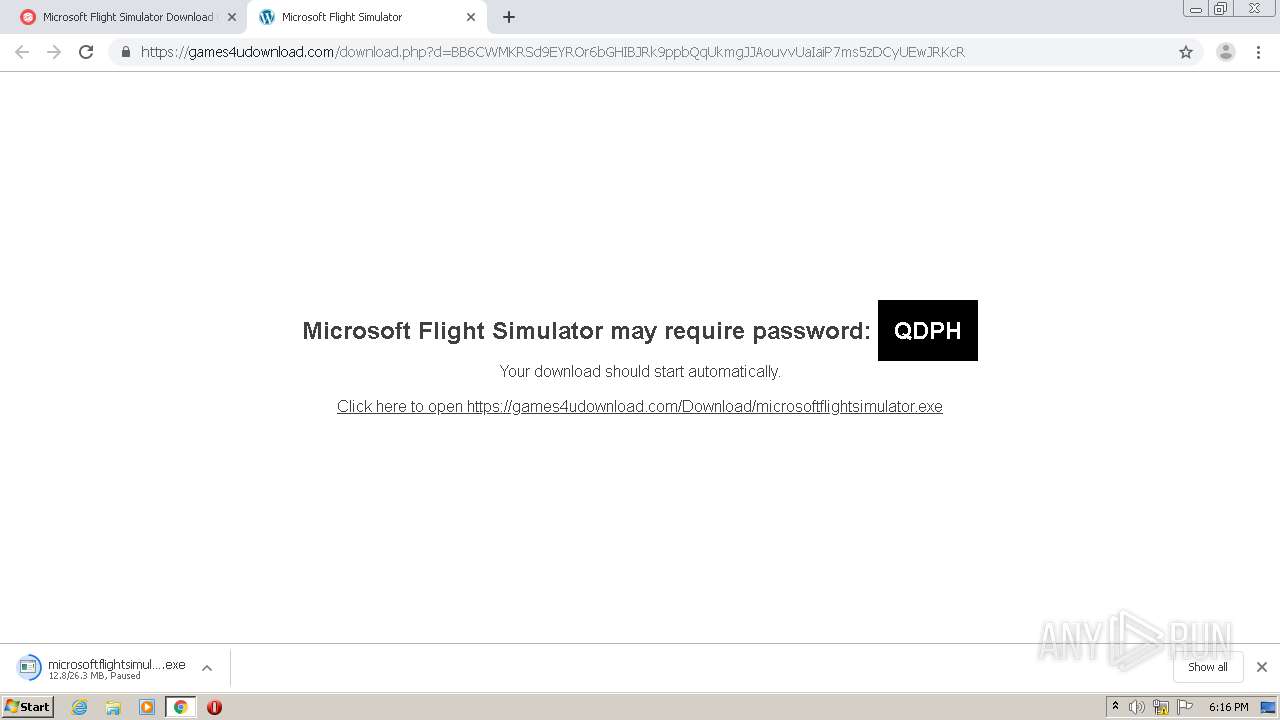
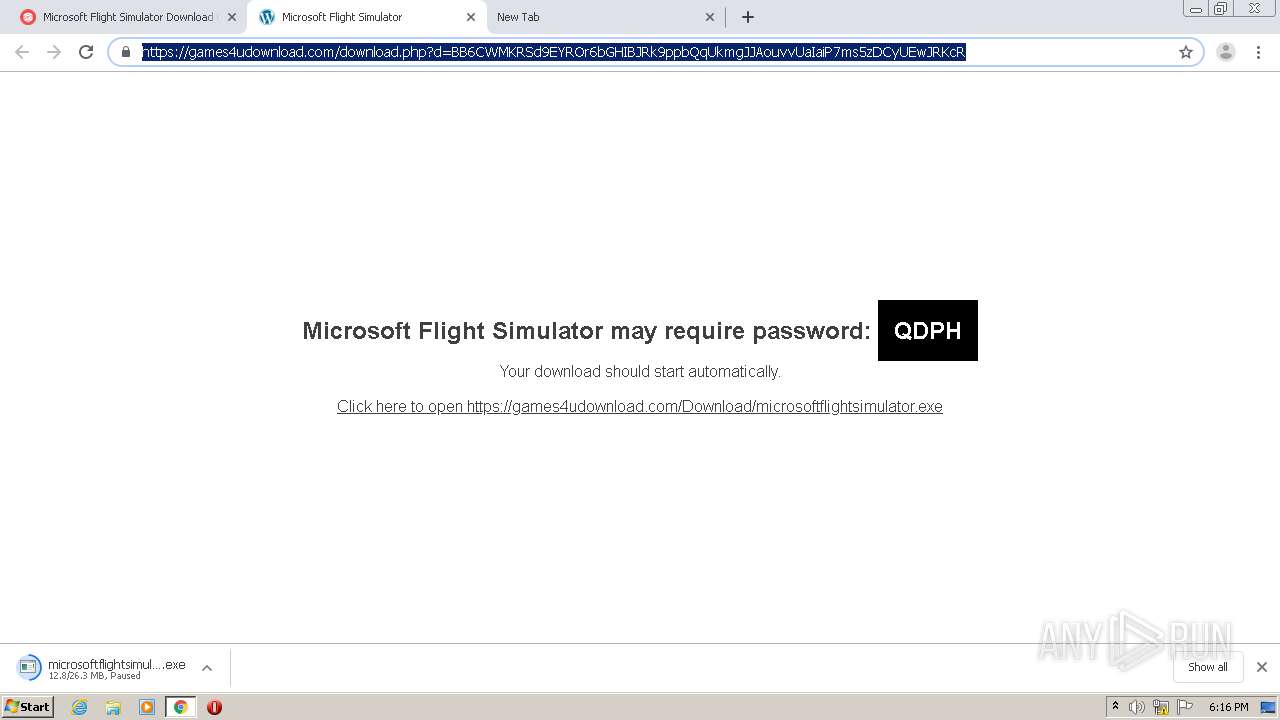
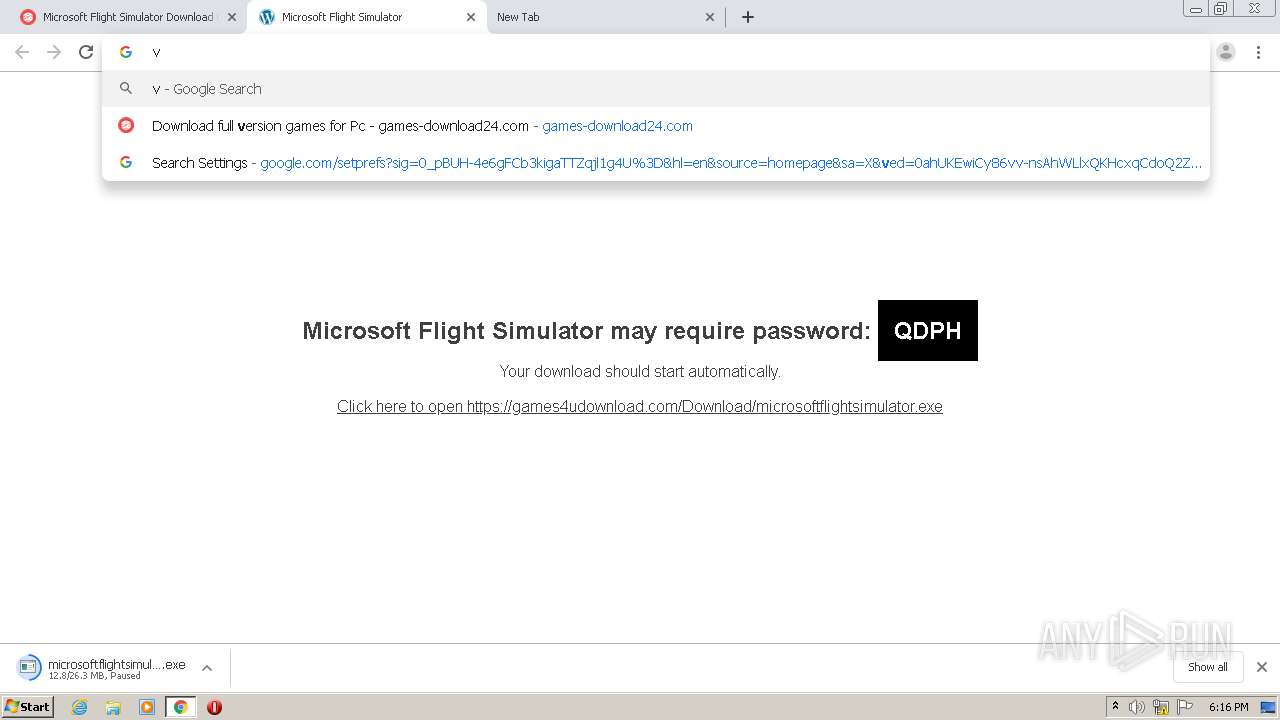
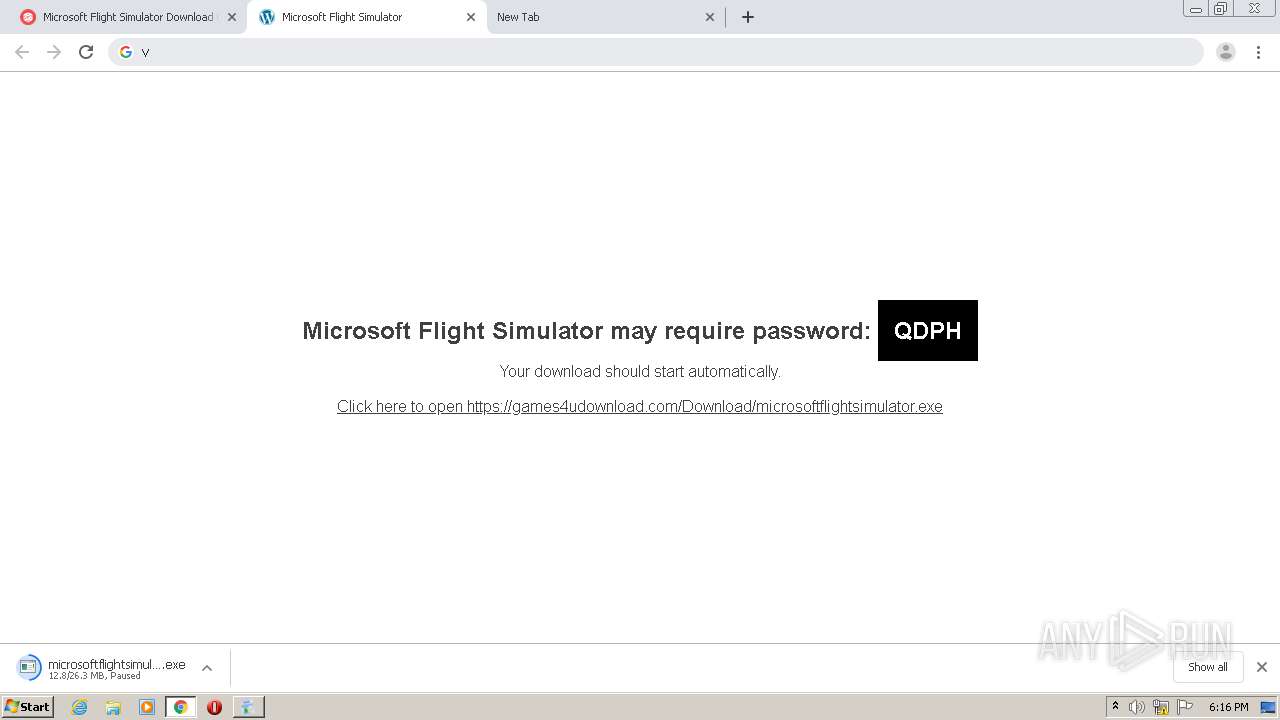
| URL: | https://googe.com |
| Full analysis: | https://app.any.run/tasks/01edda24-9e30-48b7-b805-d936c82a6094 |
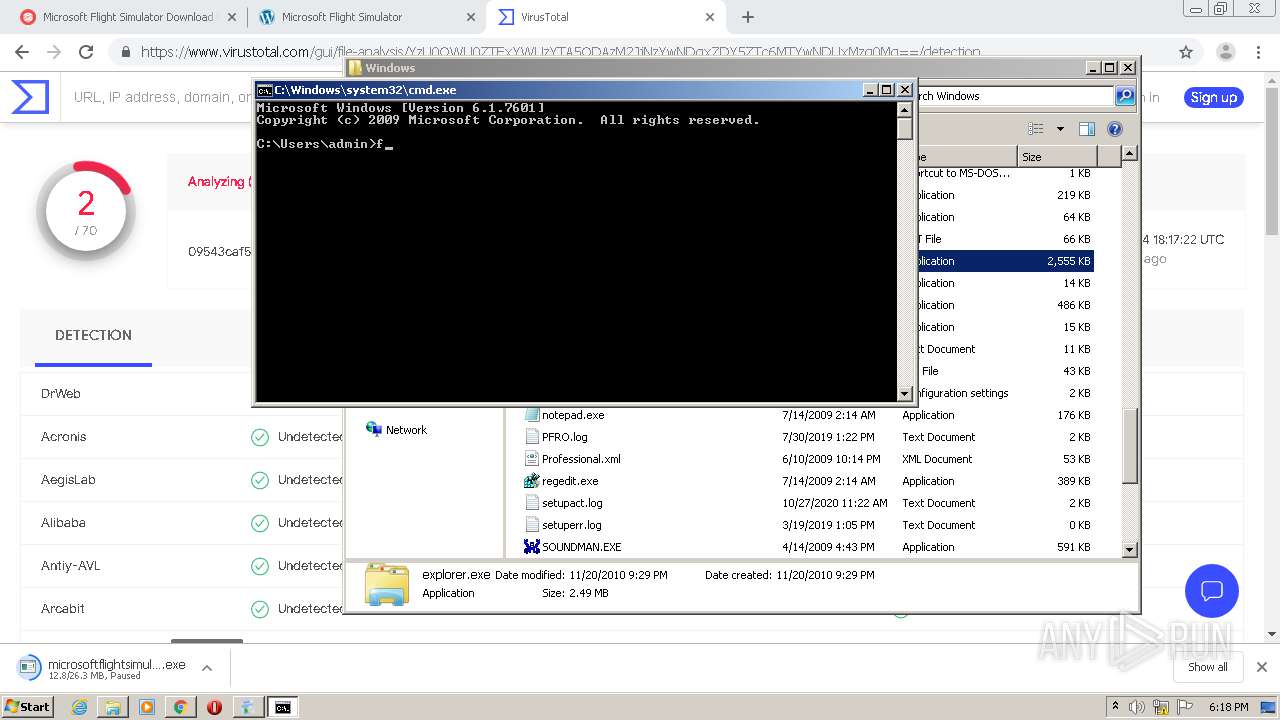
| Verdict: | Malicious activity |
| Analysis date: | November 04, 2020, 18:14:32 |
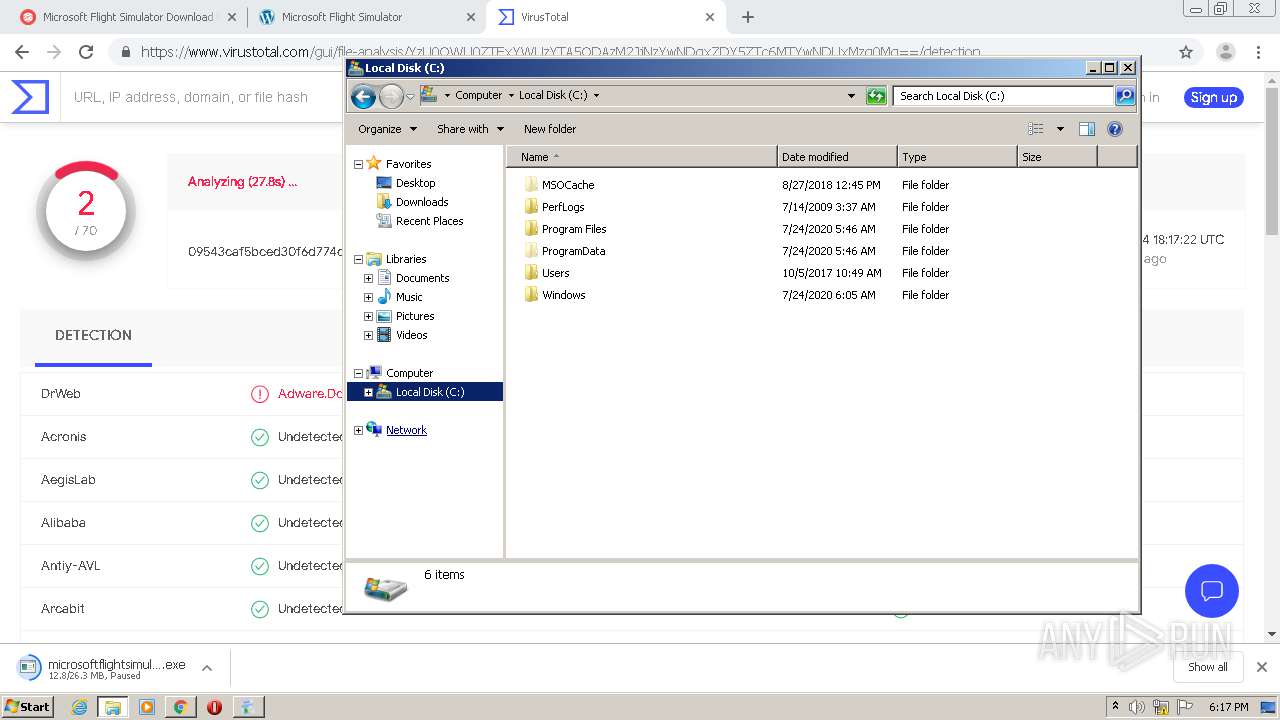
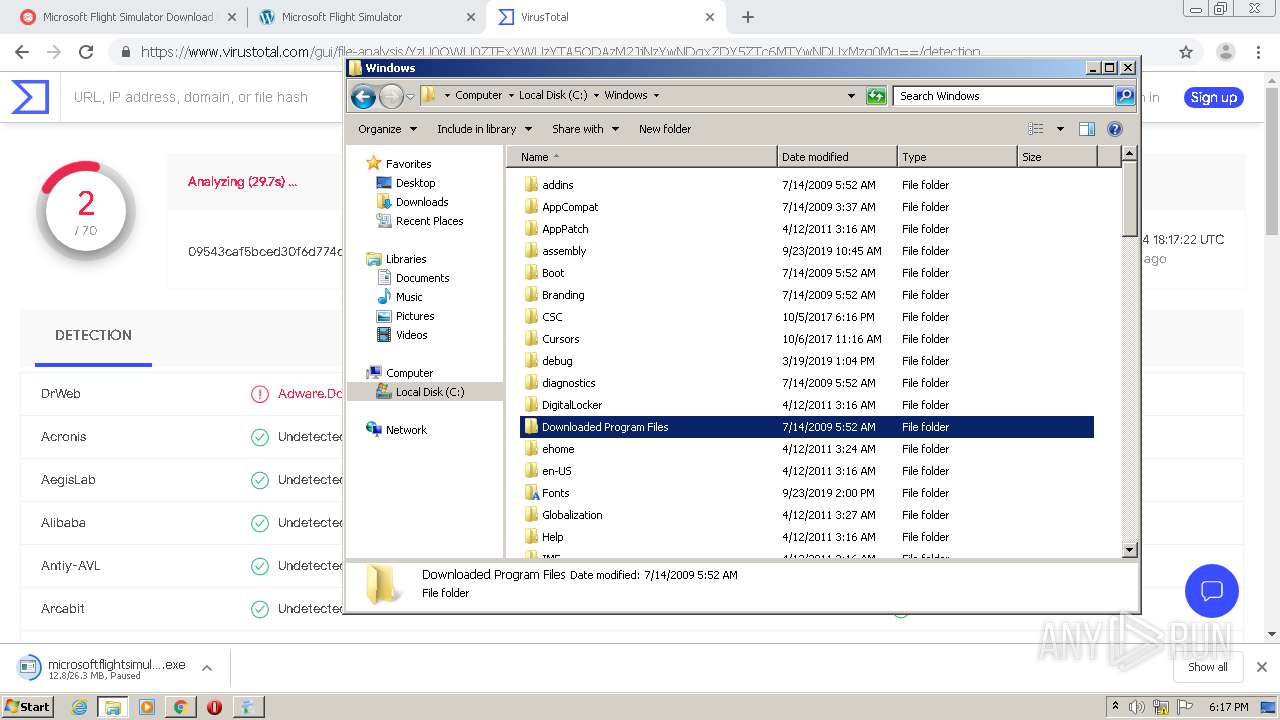
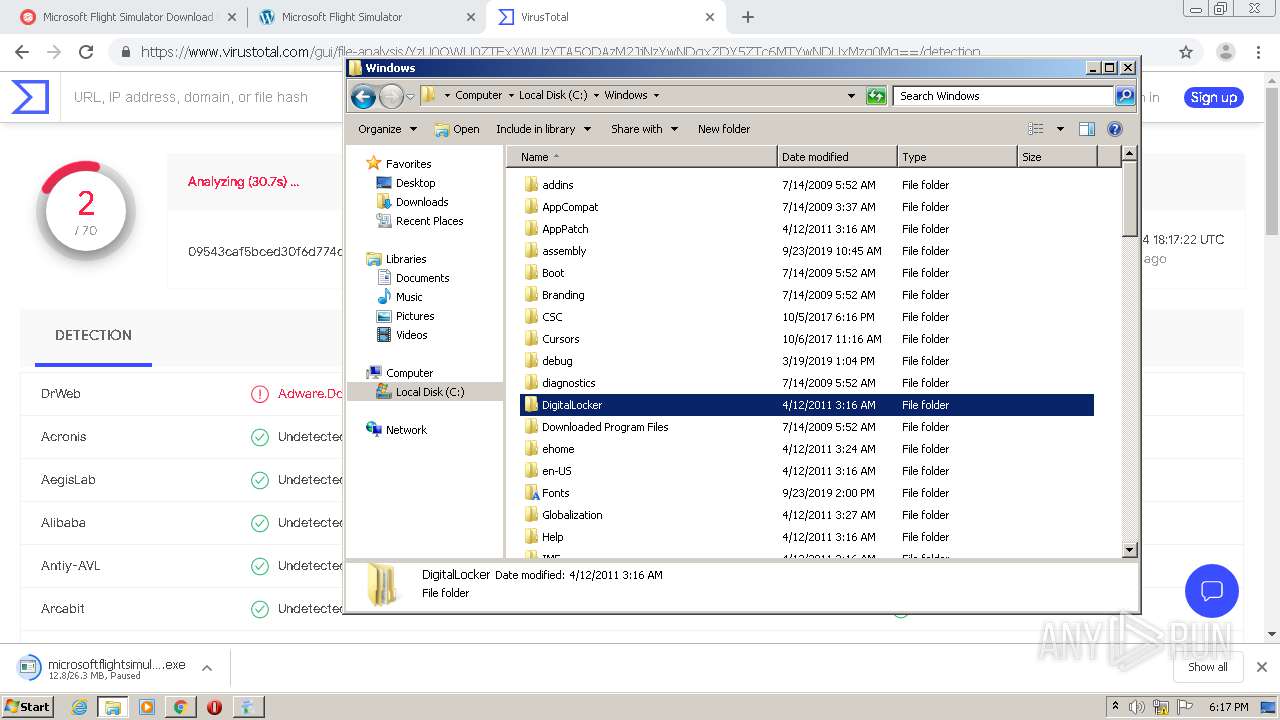
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
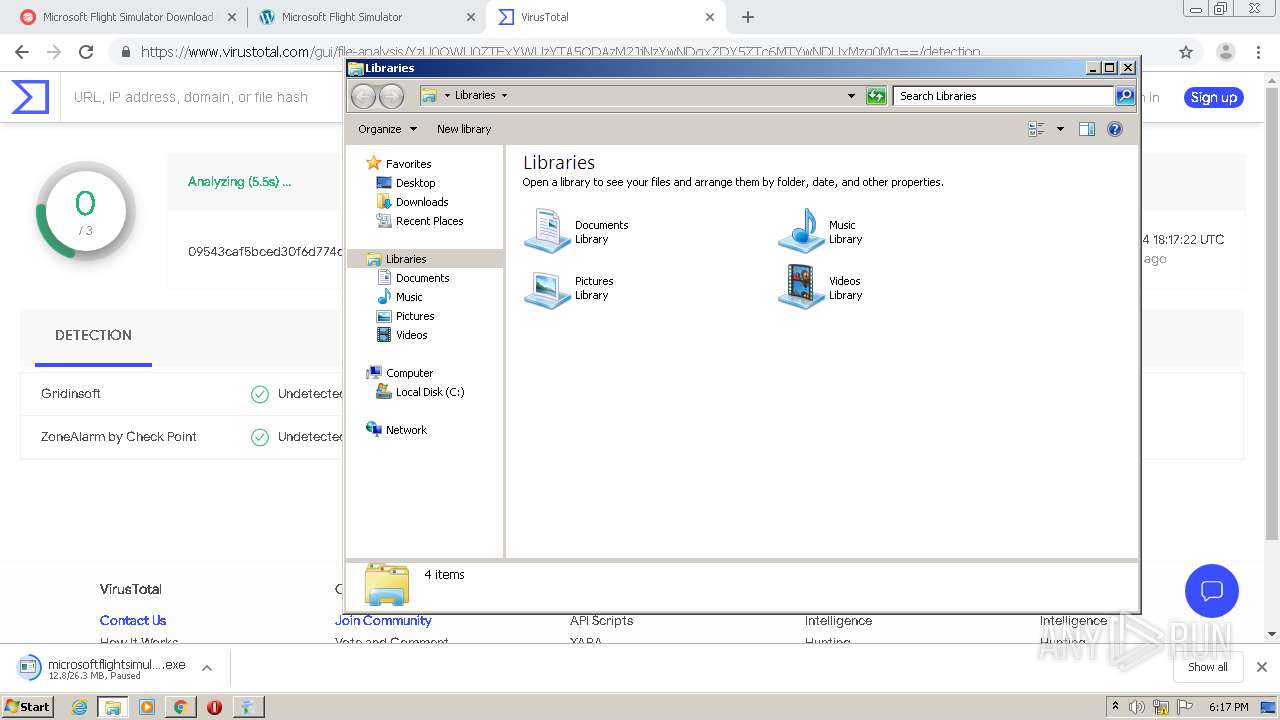
| MD5: | 1AB1EB9678AD9F3A10BBBA4F614FACB7 |
| SHA1: | C6ED49A077068129B548F9CB9309380E2A112BDC |
| SHA256: | 7E850130E703102F50DB38C2271A44DDC4ACBFFB847001FE572F17EA4557B971 |
| SSDEEP: | 3:N8r+2:2n |
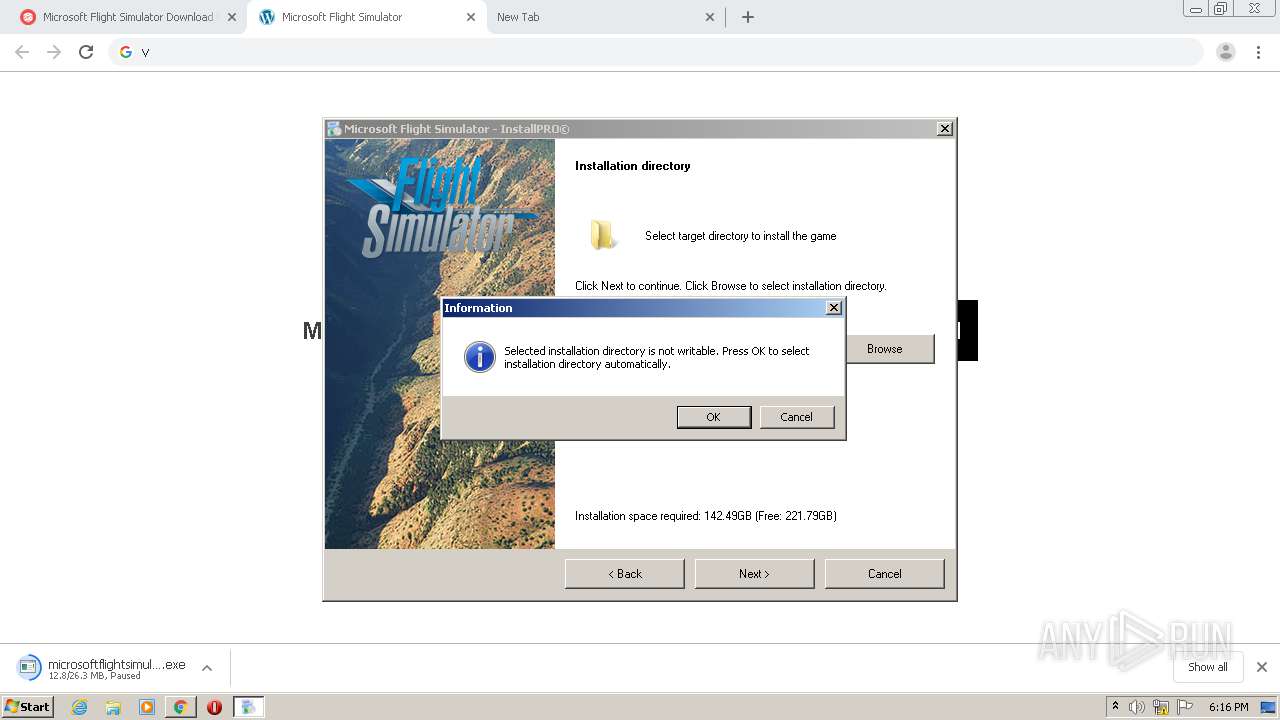
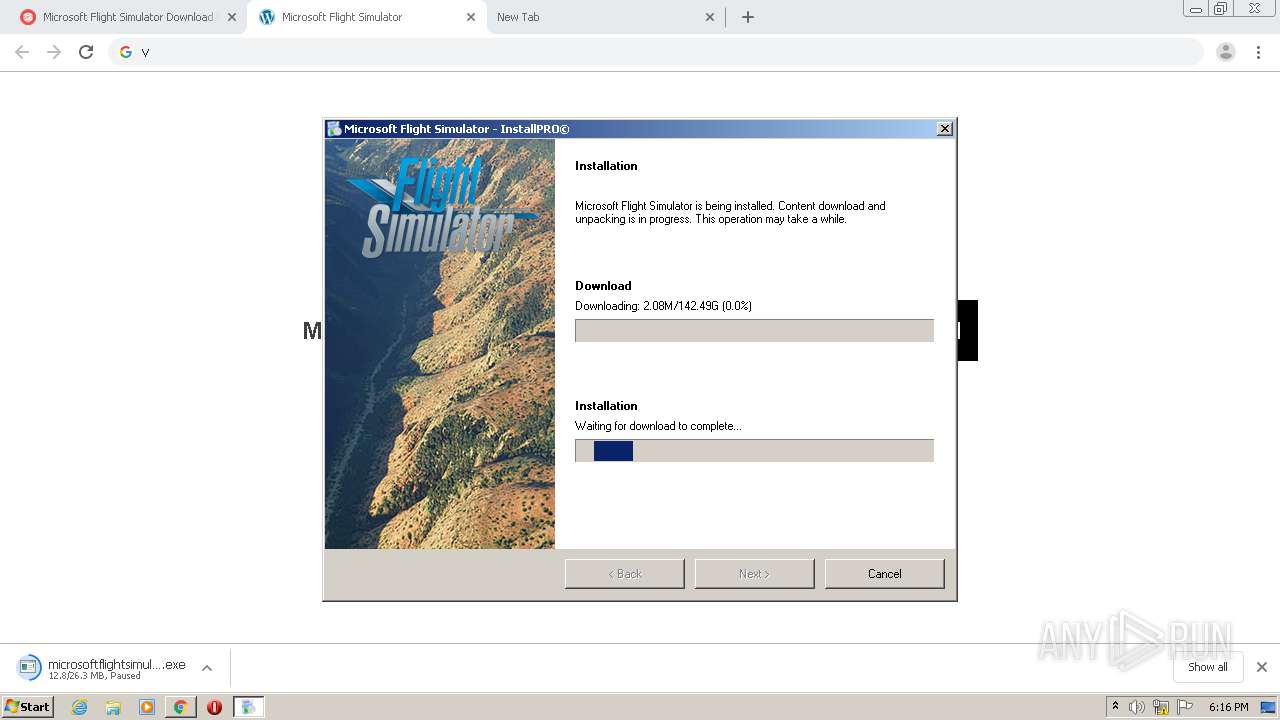
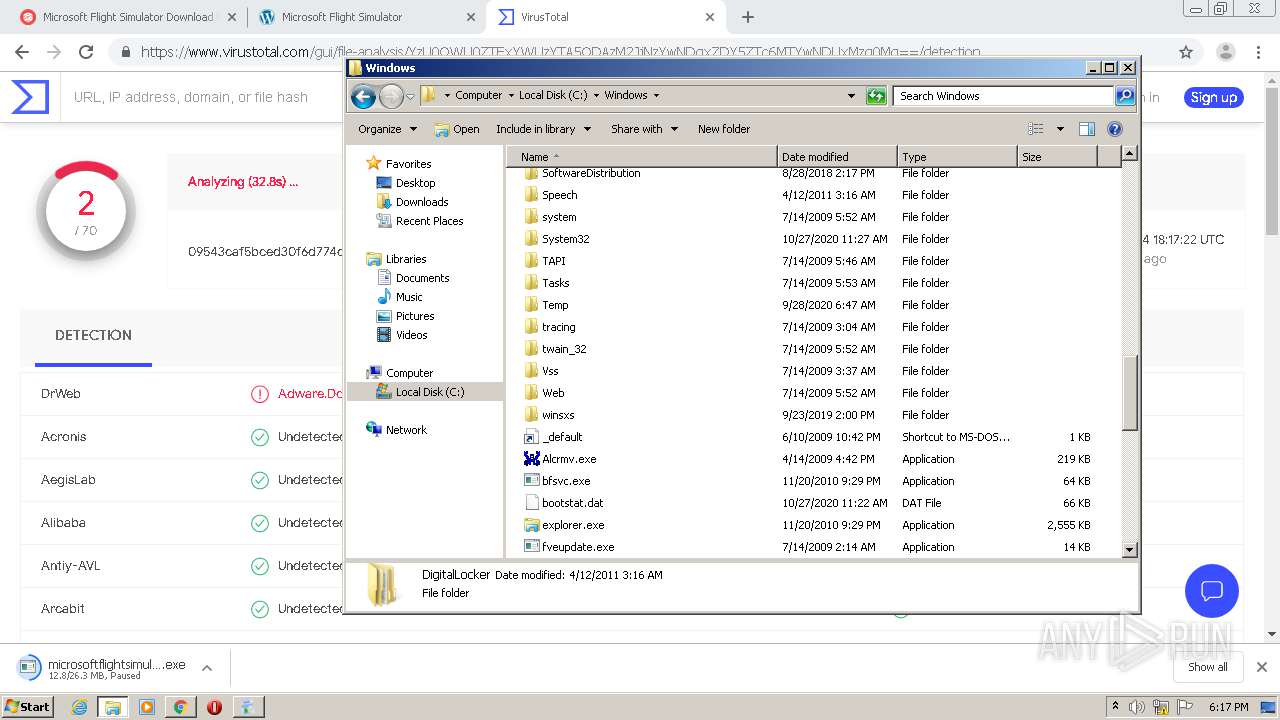
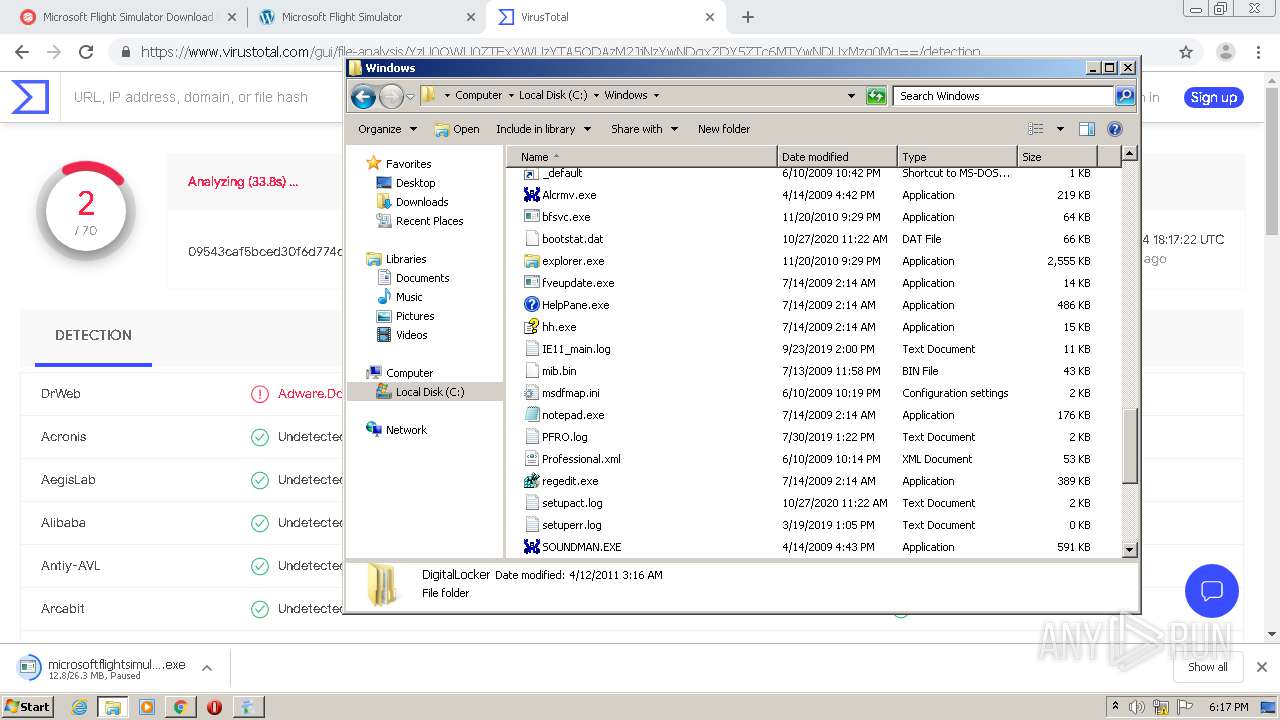
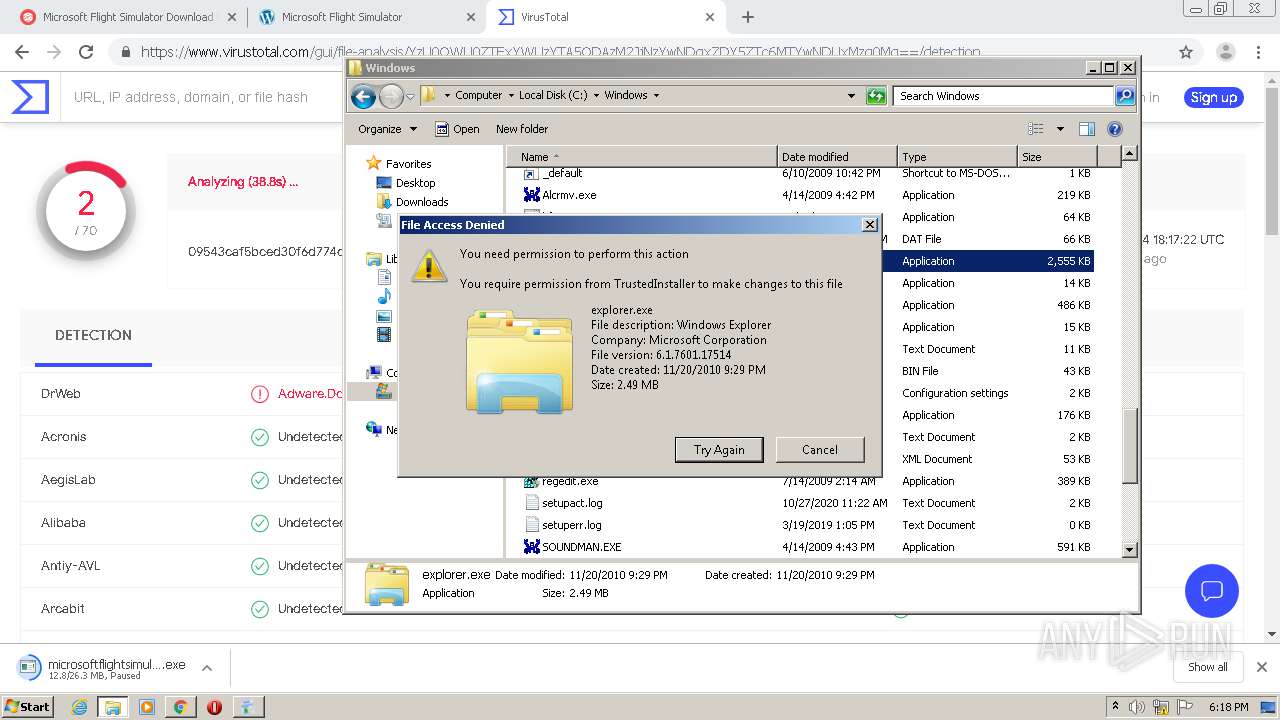
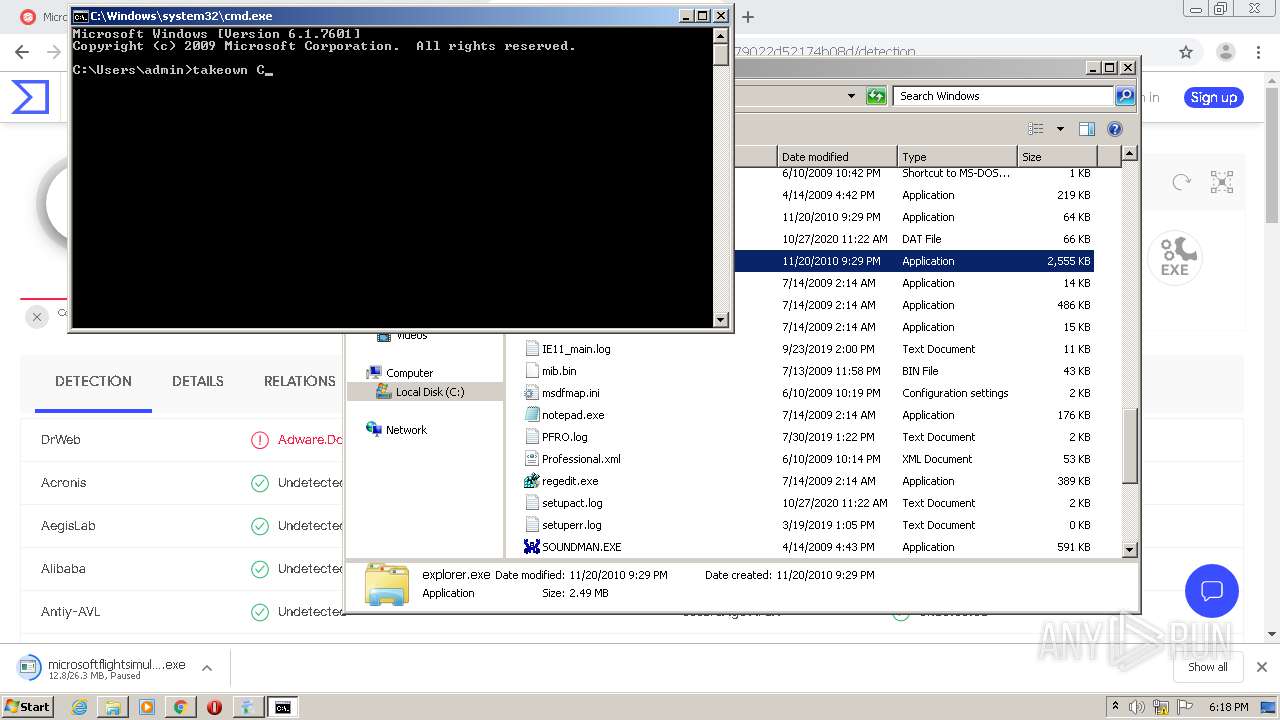
MALICIOUS
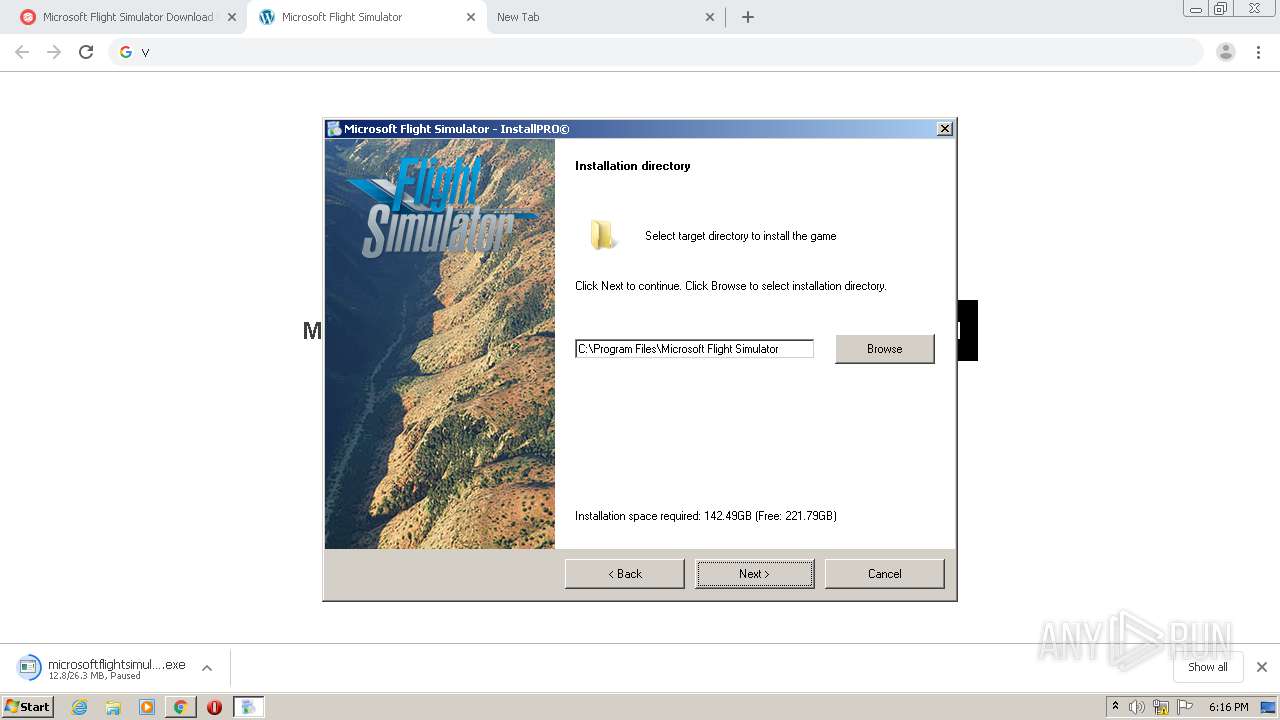
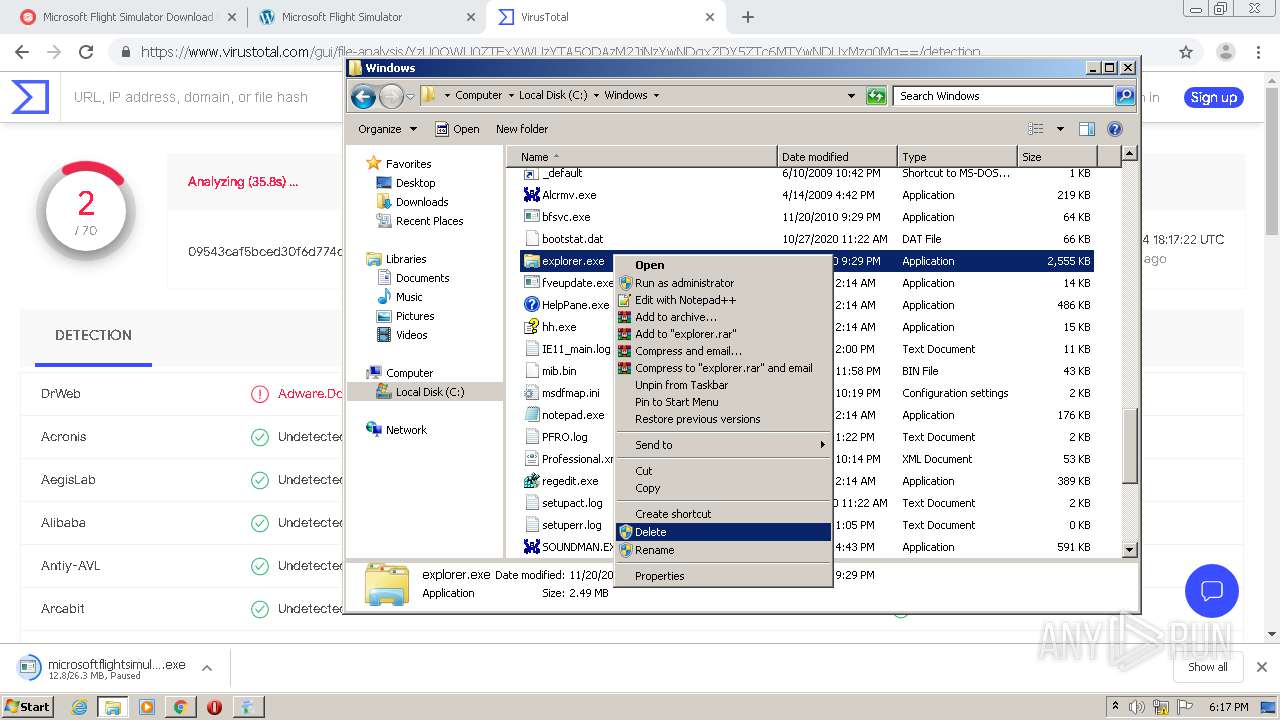
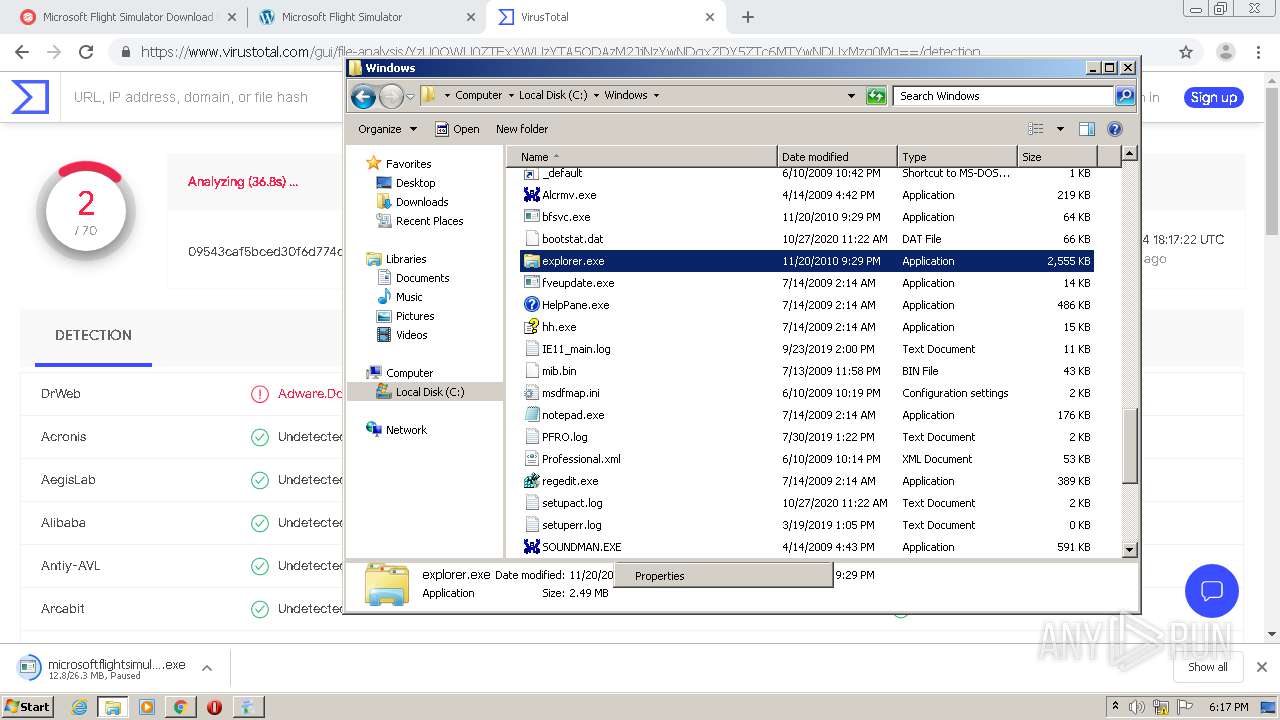
Application was dropped or rewritten from another process
- pas.exe (PID: 3640)
- microsoftflightsimulator (1).exe (PID: 768)
Changes the autorun value in the registry
- microsoftflightsimulator (1).exe (PID: 768)
SUSPICIOUS
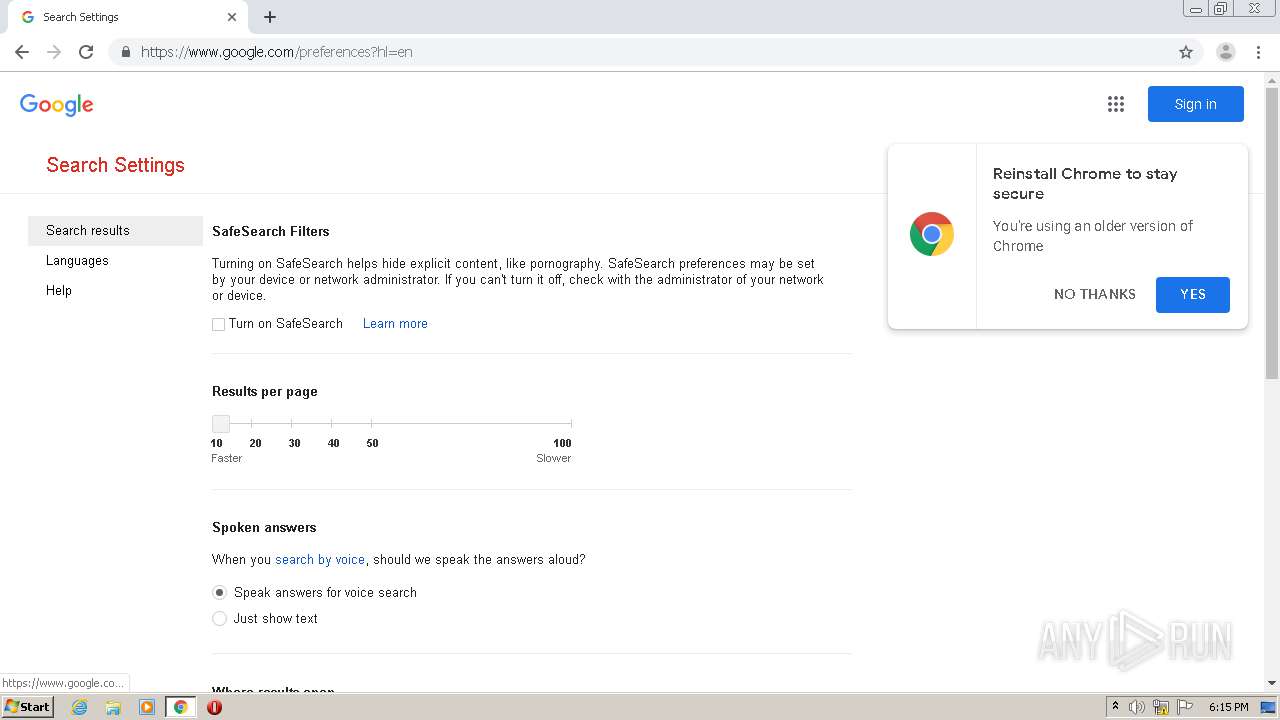
Modifies files in Chrome extension folder
- chrome.exe (PID: 1624)
Executed via COM
- DllHost.exe (PID: 3744)
Reads Internet Cache Settings
- microsoftflightsimulator (1).exe (PID: 768)
- pas.exe (PID: 3640)
Executable content was dropped or overwritten
- chrome.exe (PID: 1624)
- microsoftflightsimulator (1).exe (PID: 768)
Creates files in the user directory
- microsoftflightsimulator (1).exe (PID: 768)
INFO
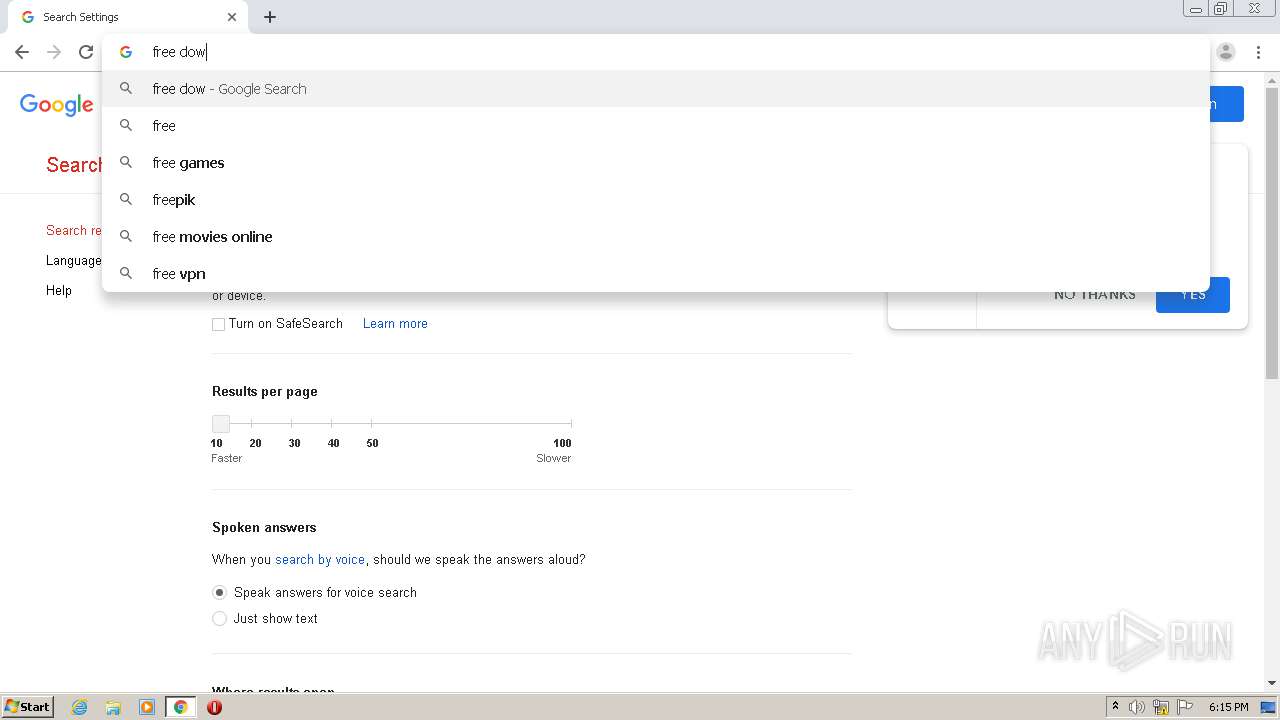
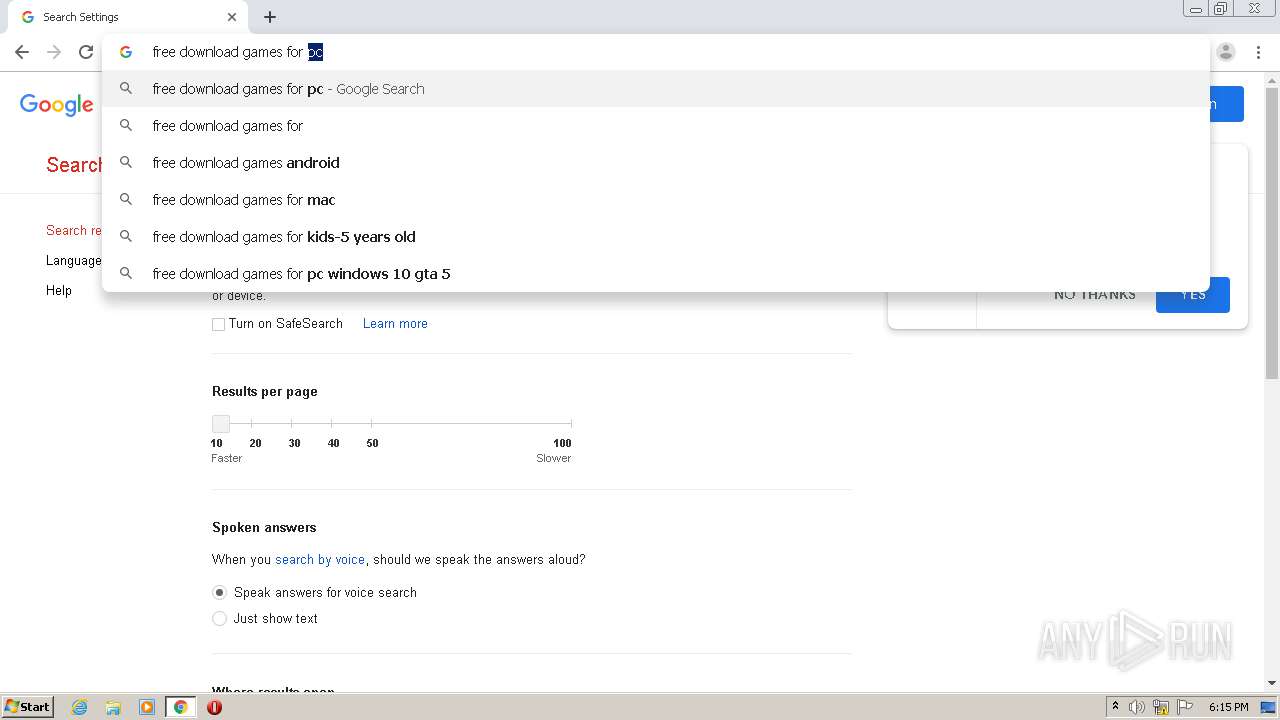
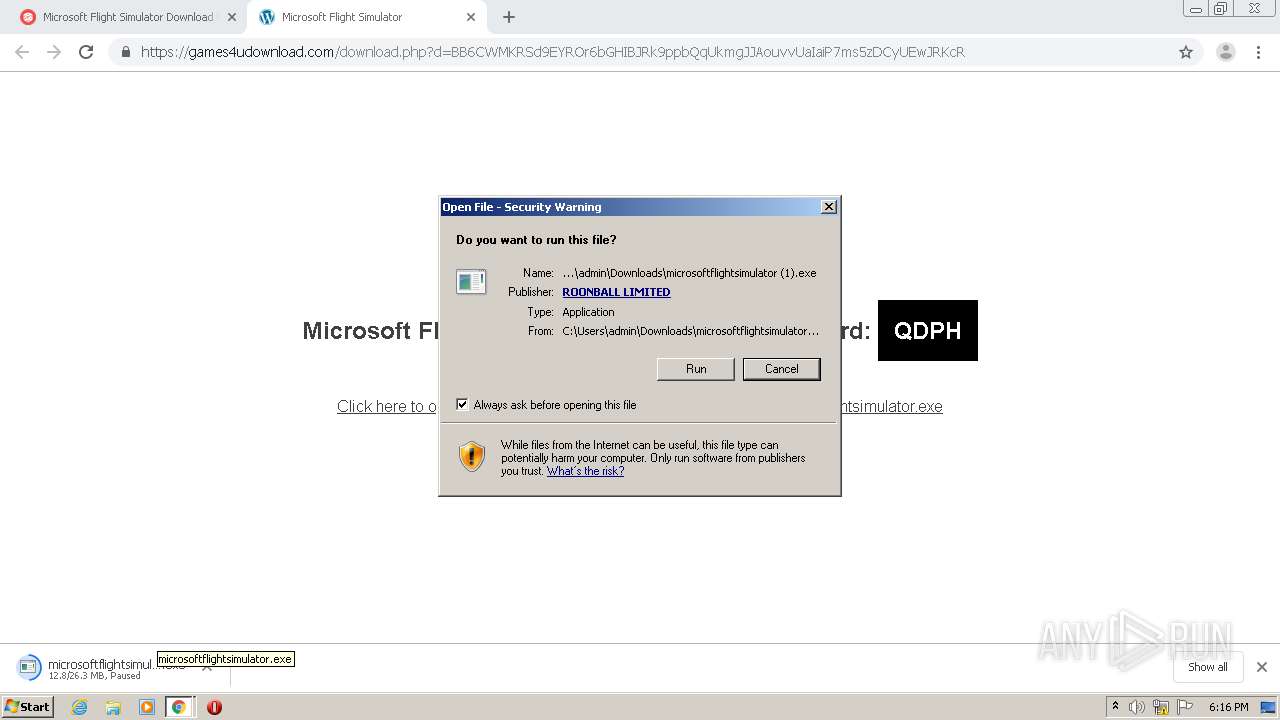
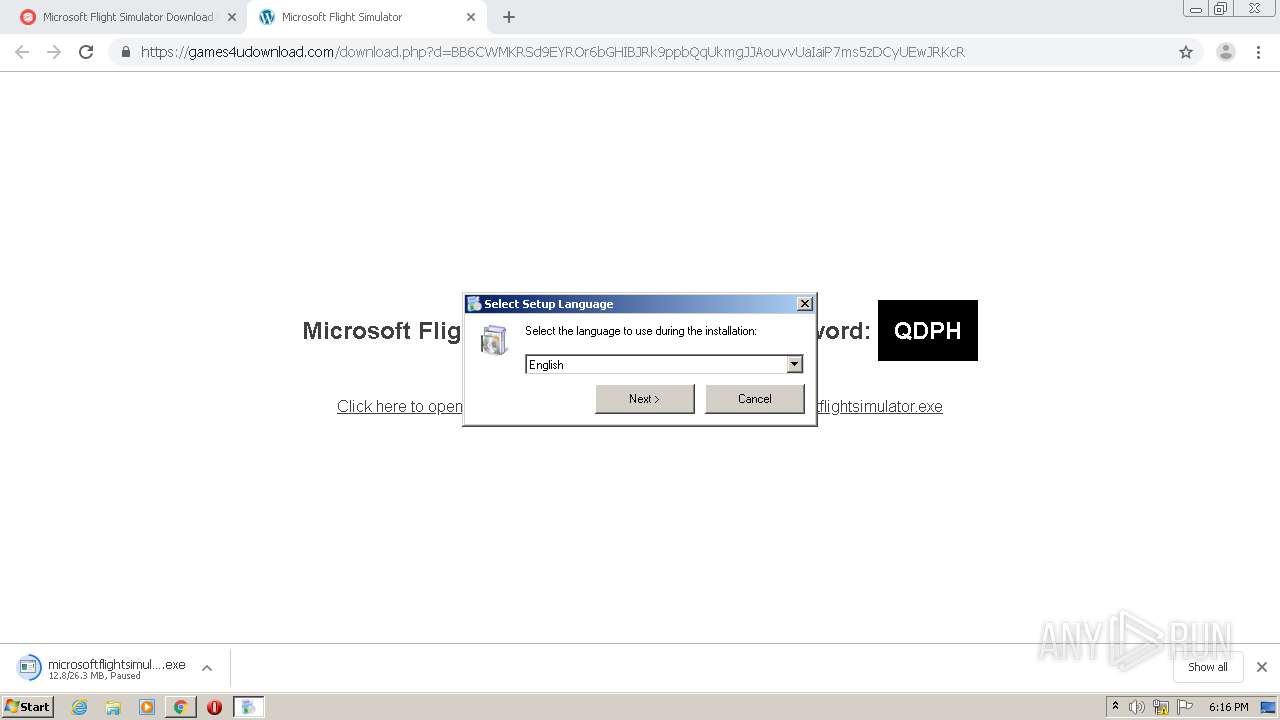
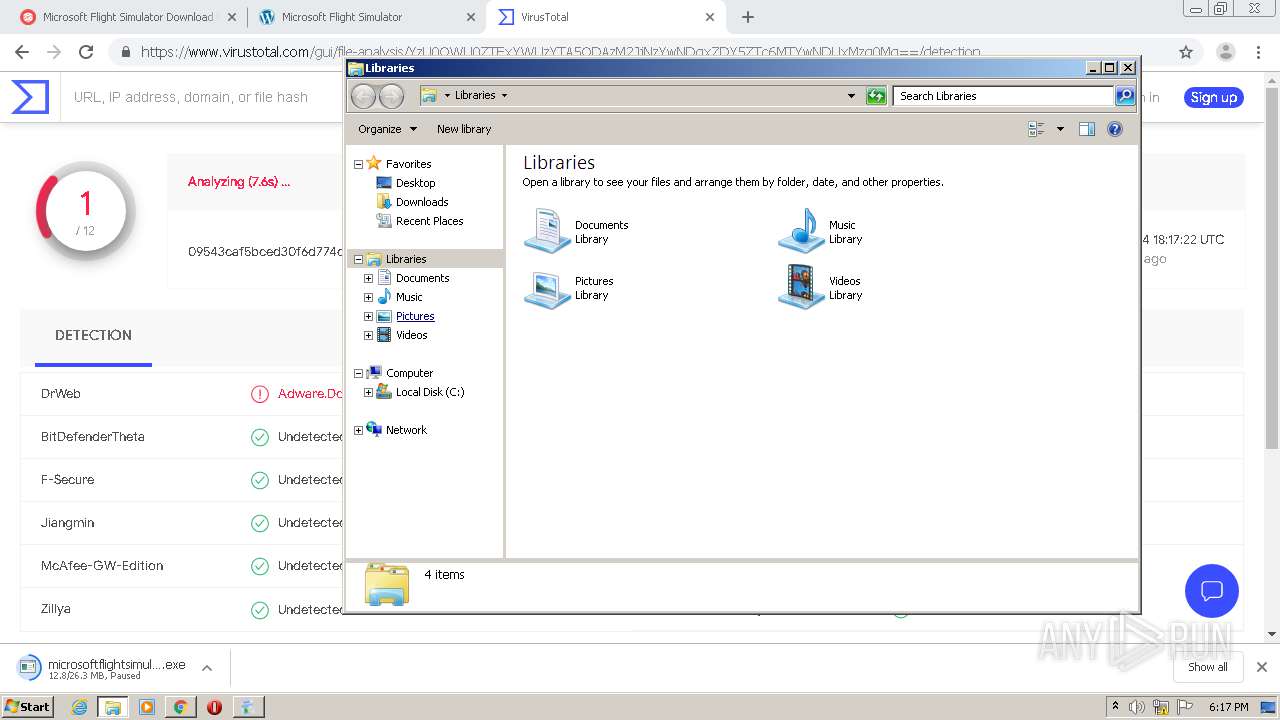
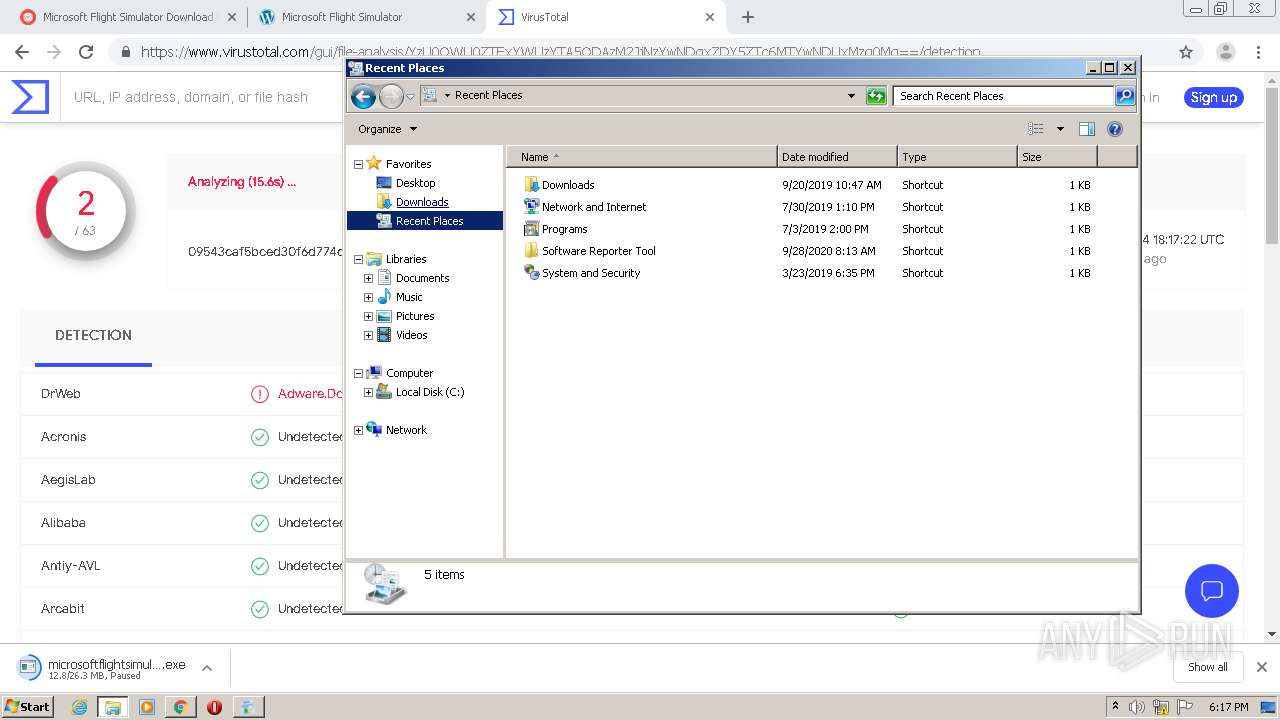
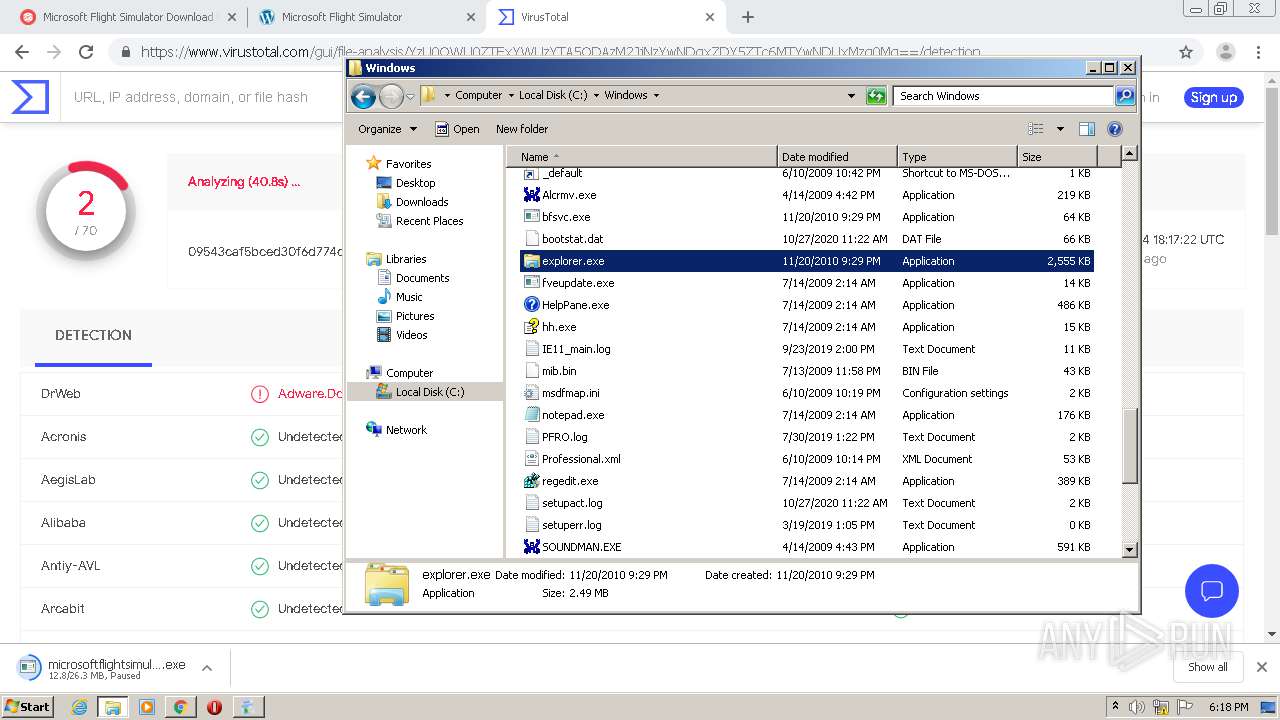
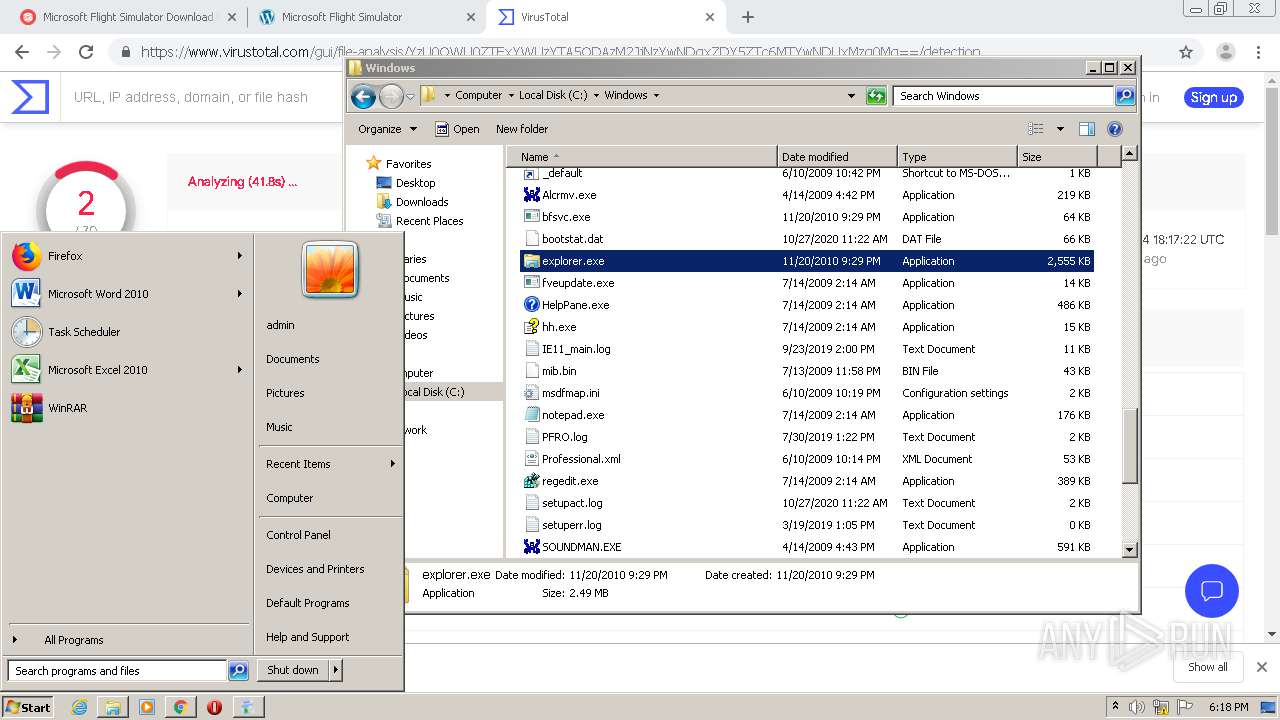
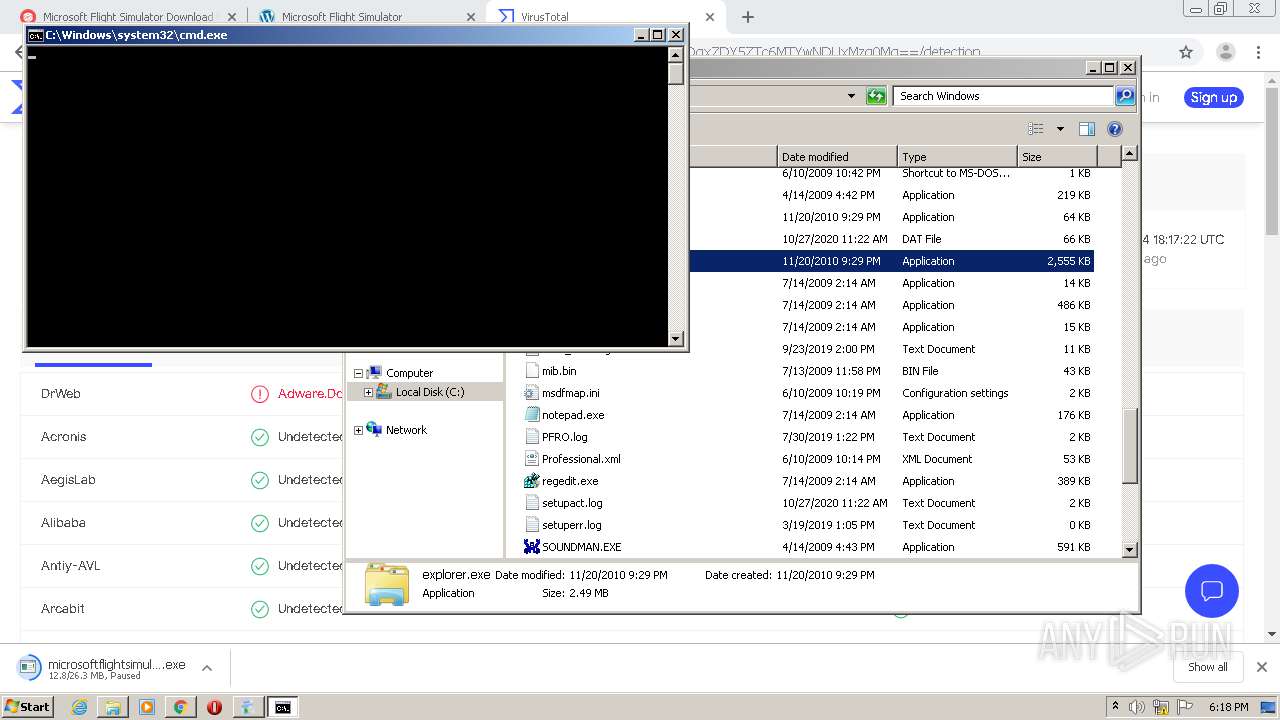
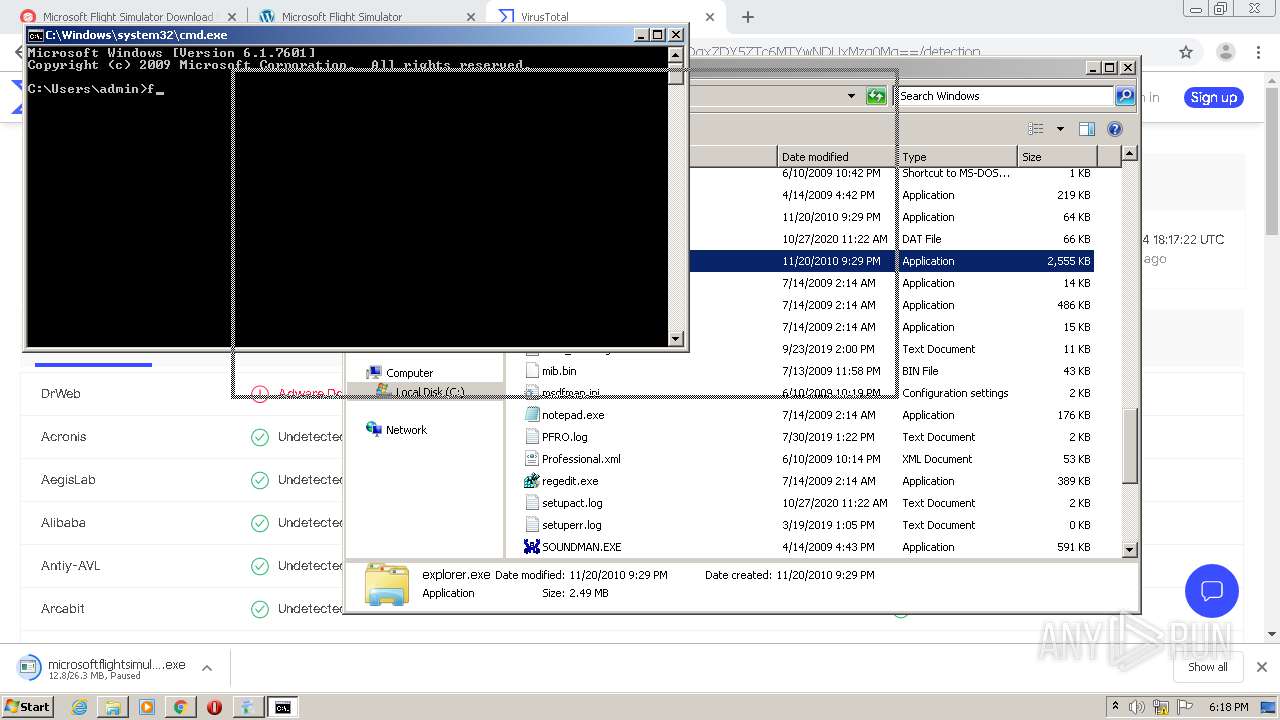
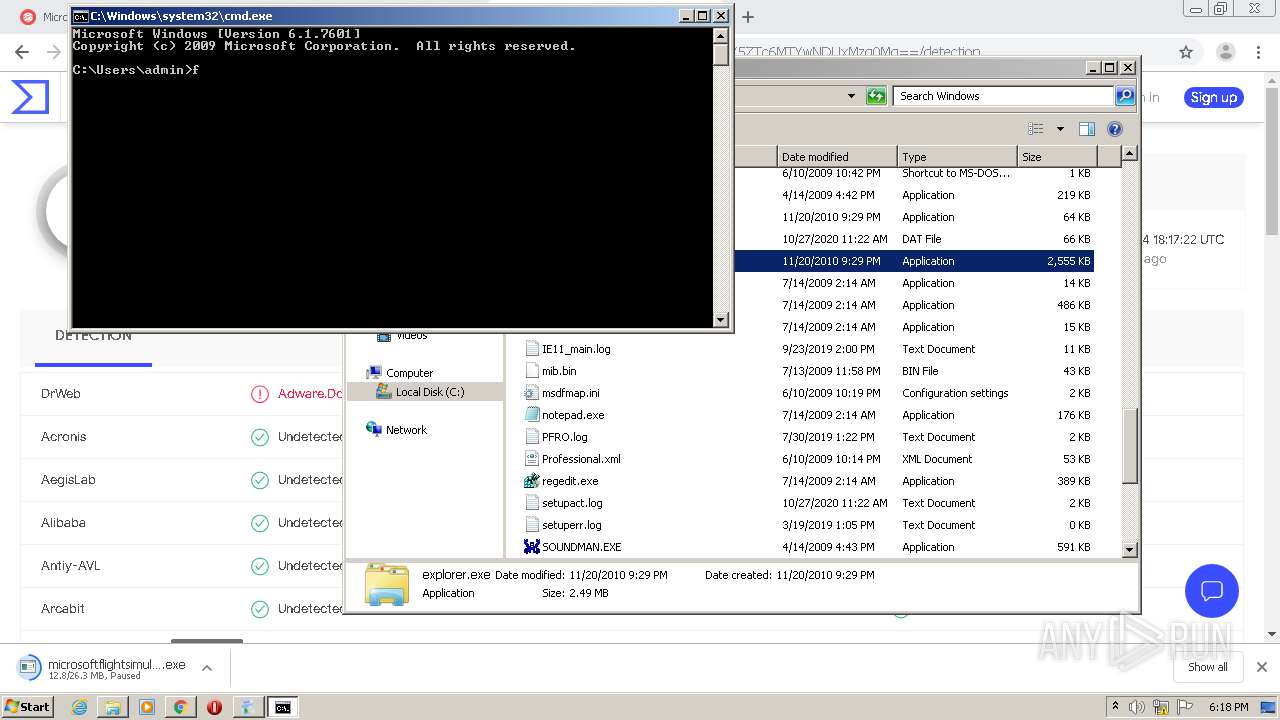
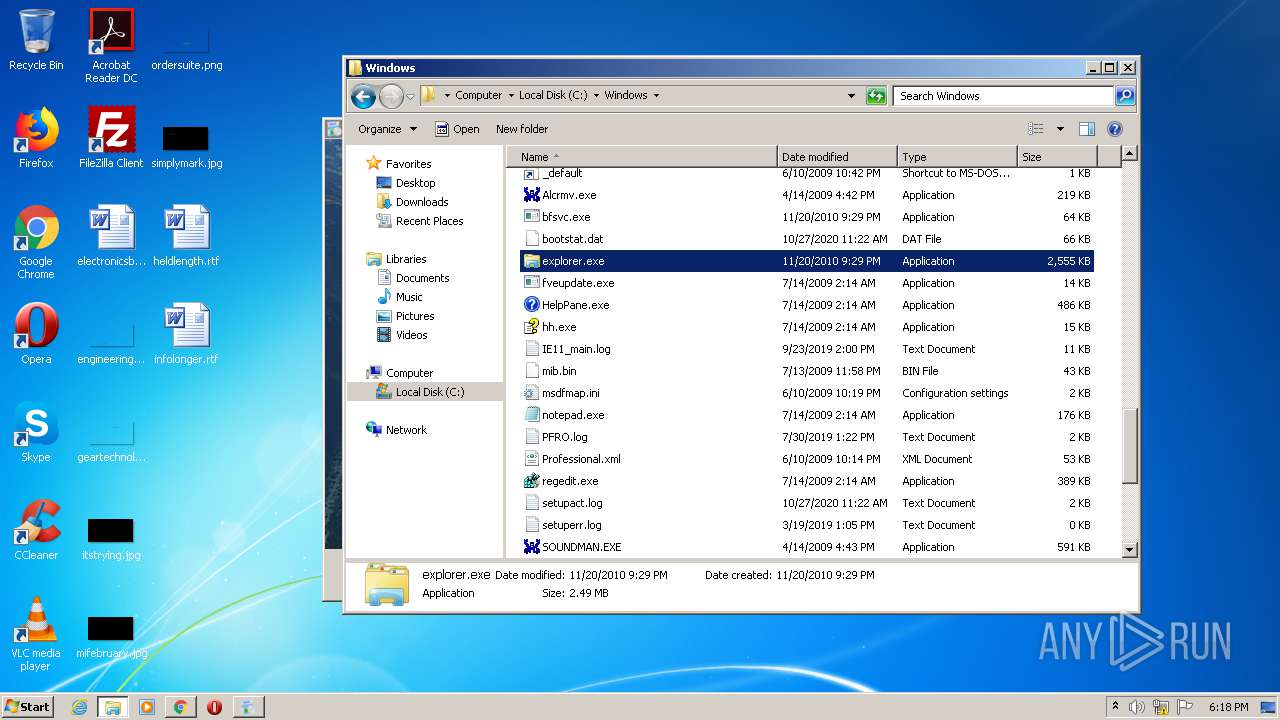
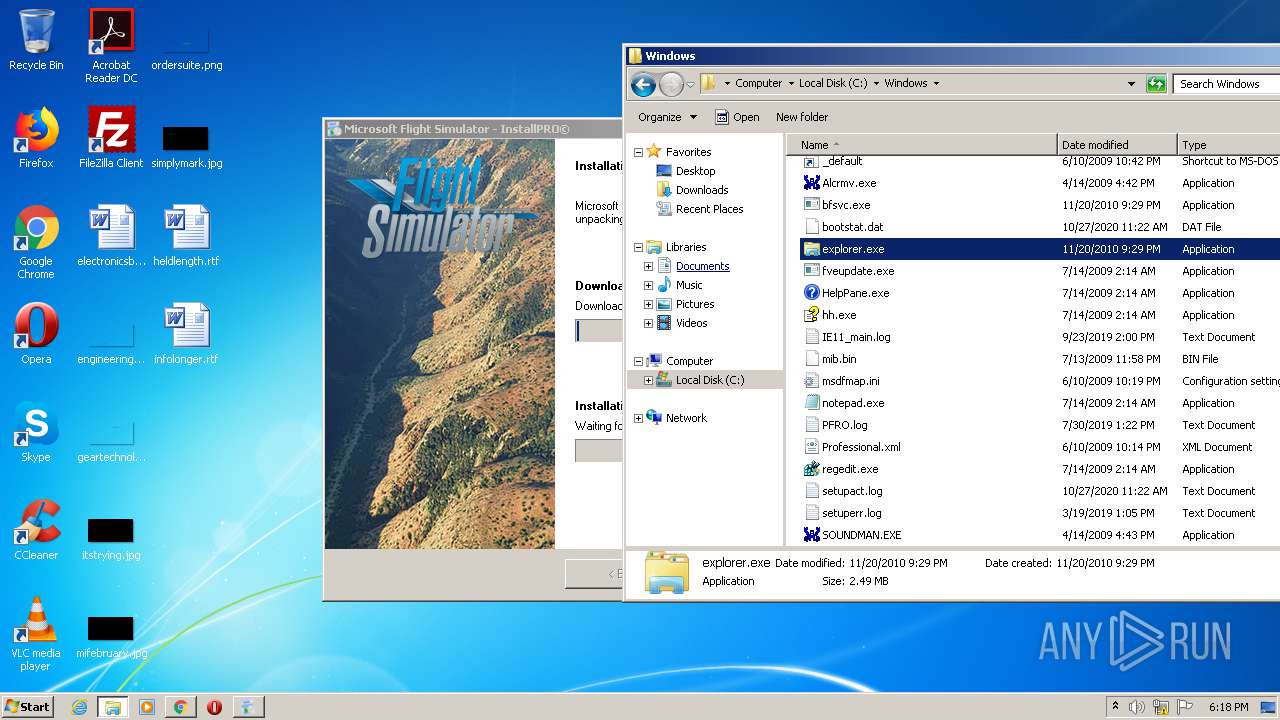
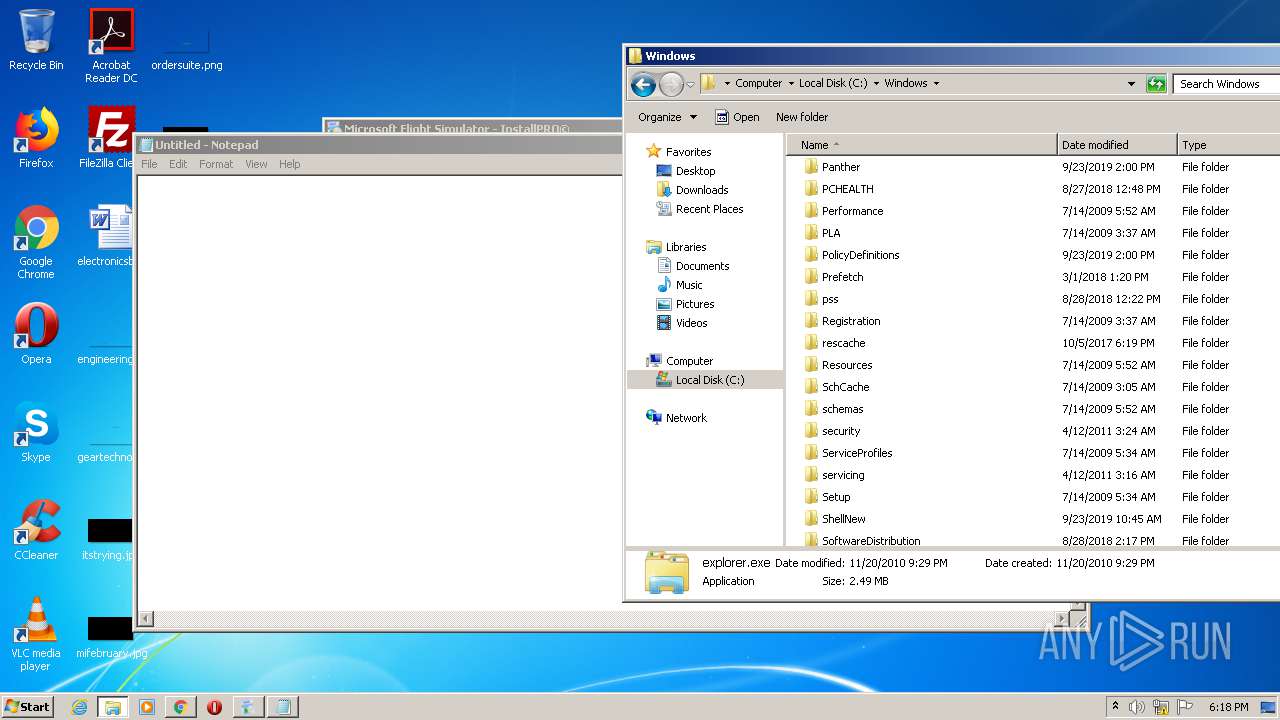
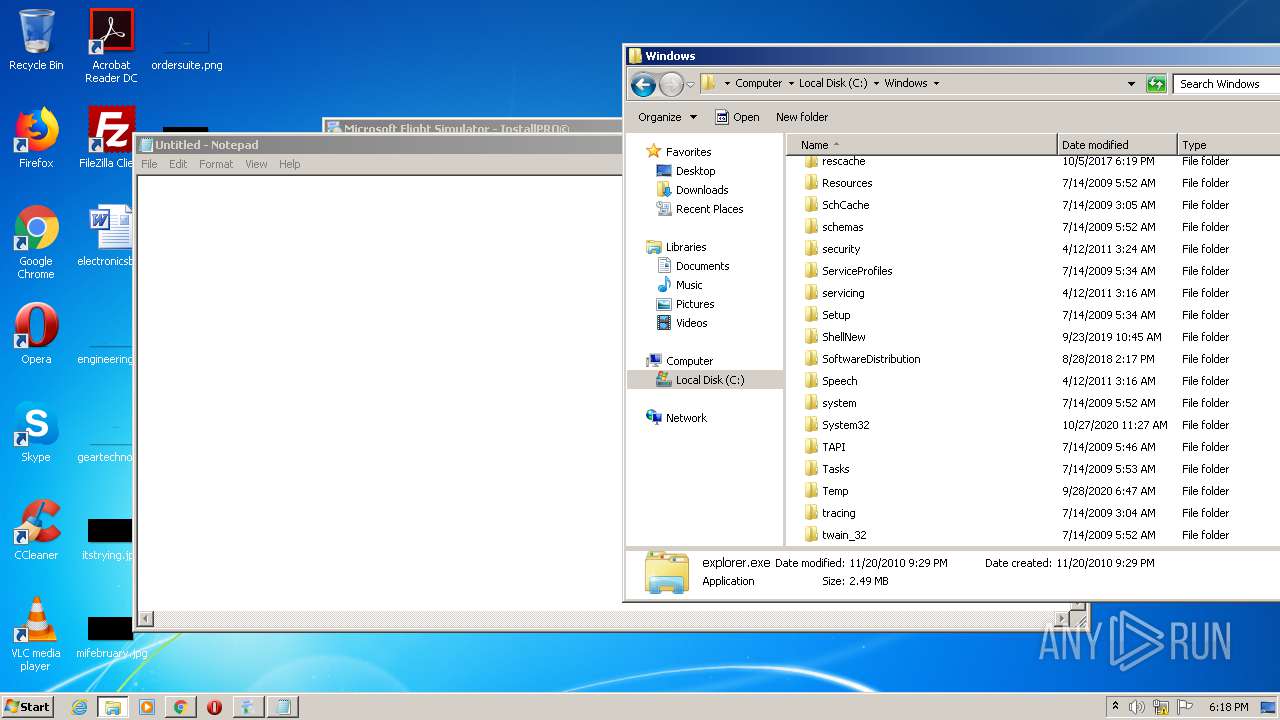
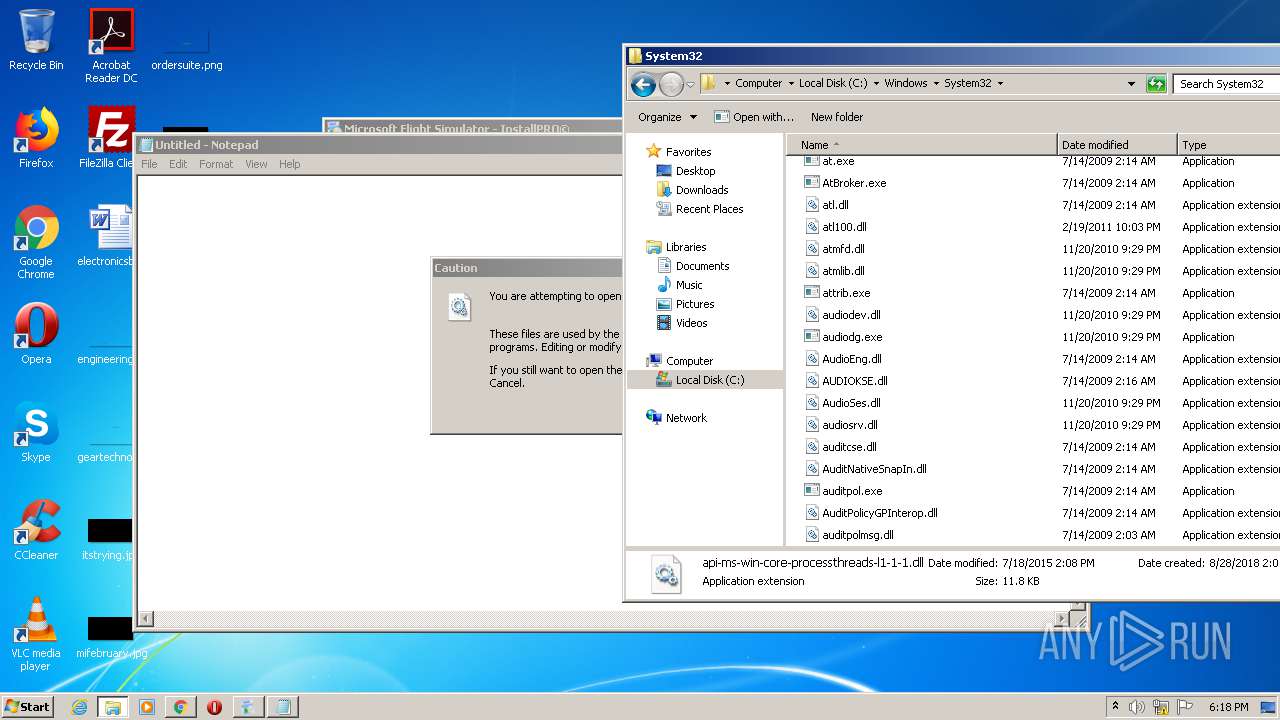
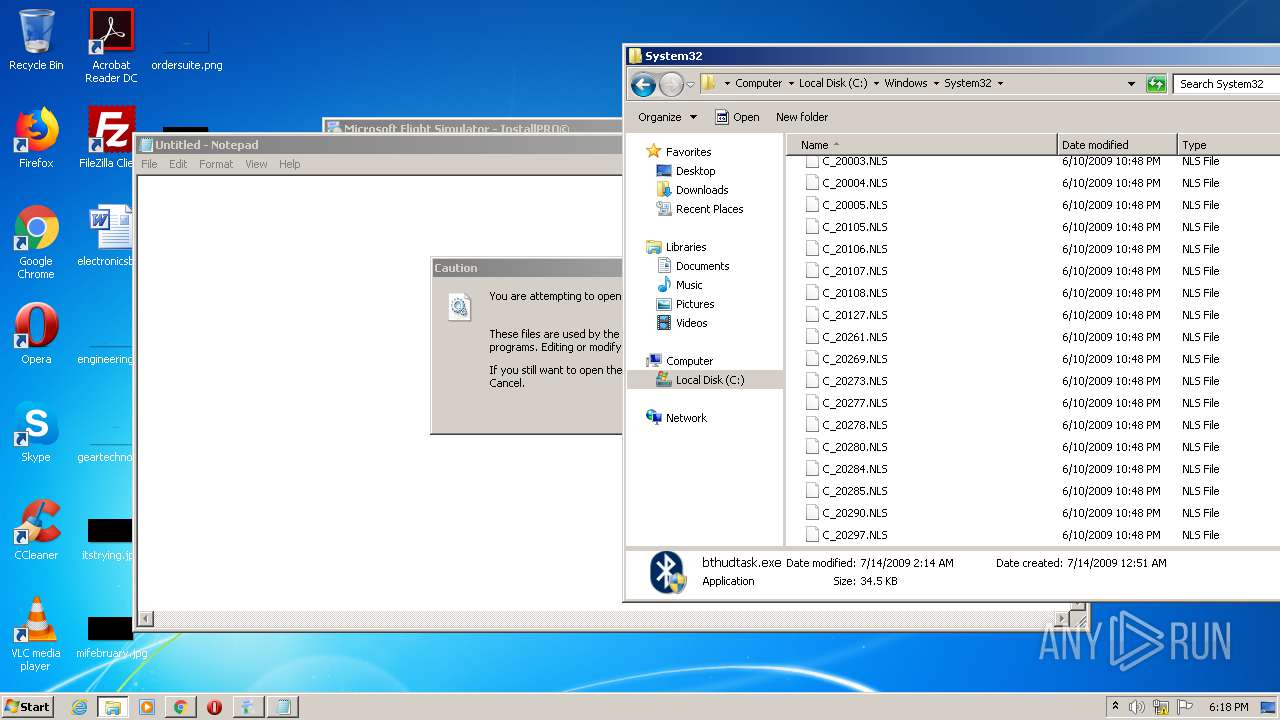
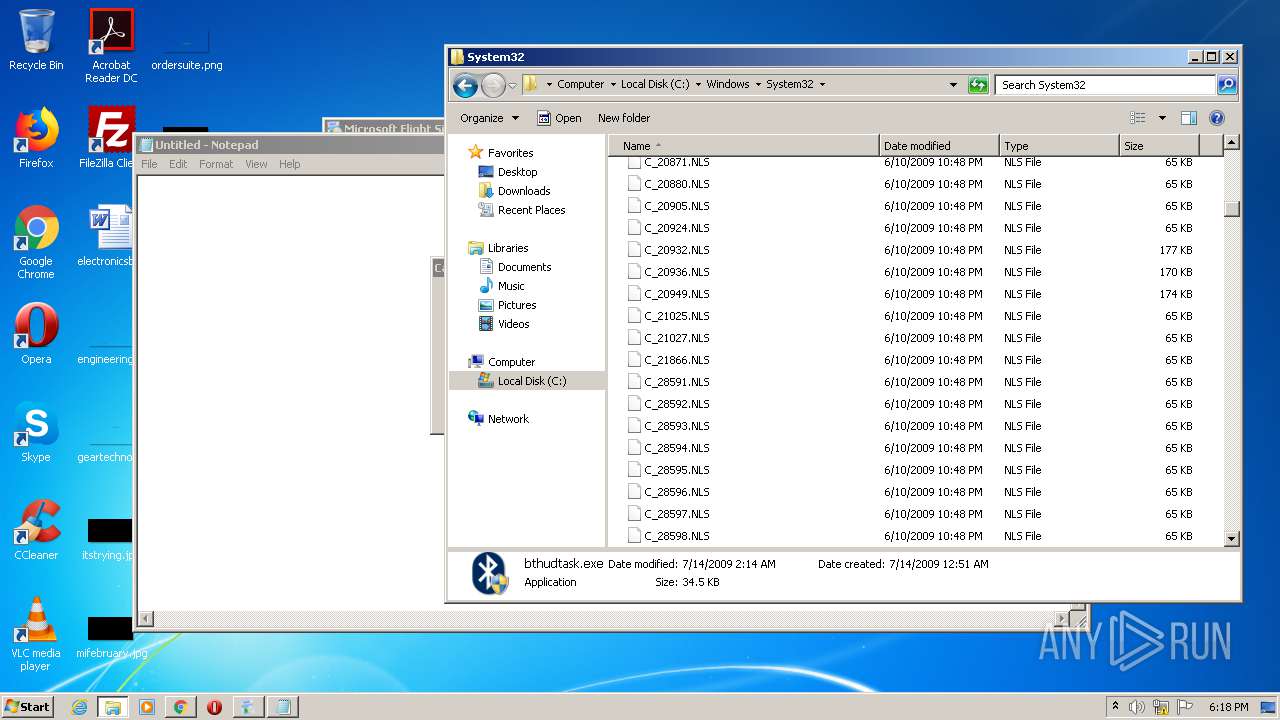
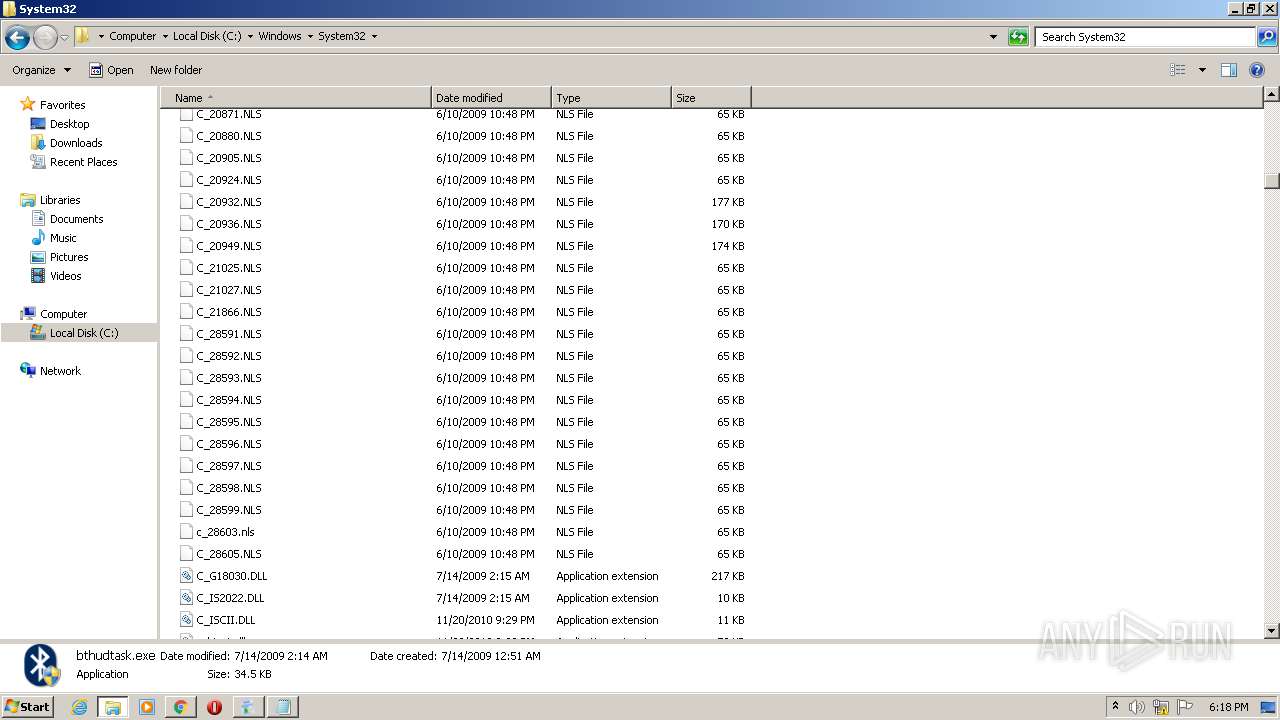
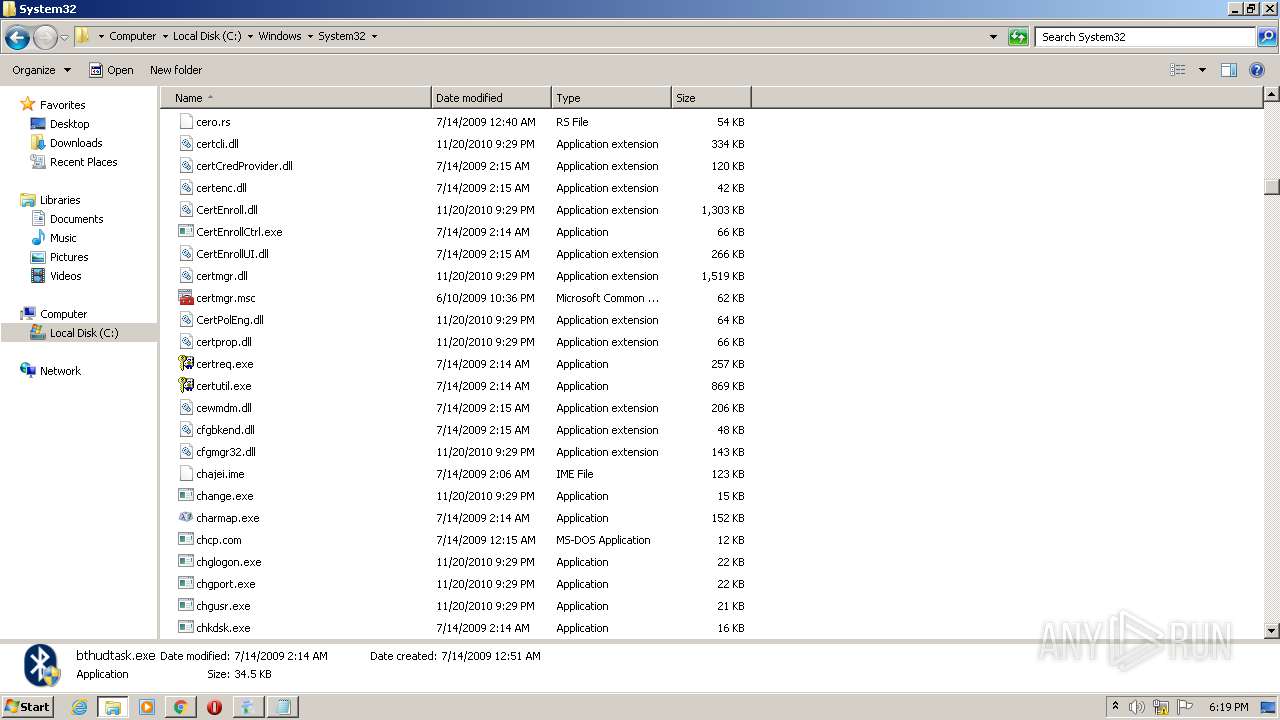
Manual execution by user
- explorer.exe (PID: 2368)
- cmd.exe (PID: 1484)
- notepad.exe (PID: 3096)
- explorer.exe (PID: 2644)
- rundll32.exe (PID: 1684)
- rundll32.exe (PID: 2536)
- cofire.exe (PID: 2276)
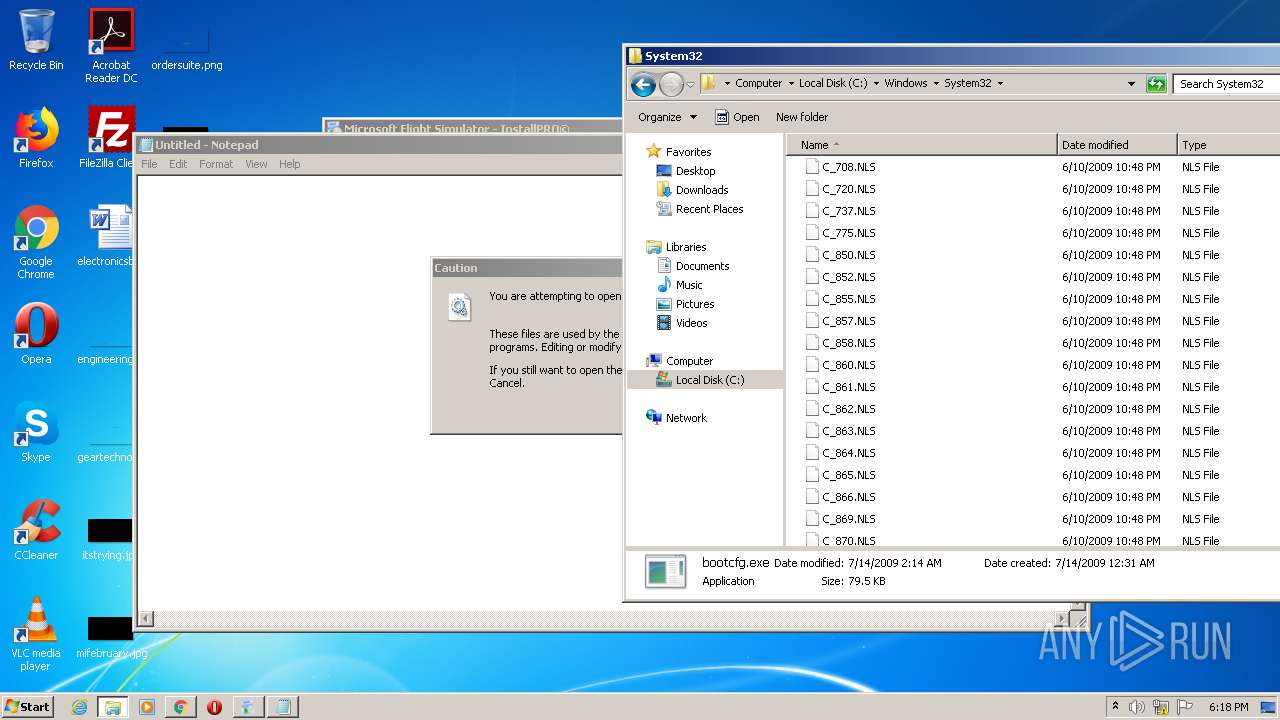
- bootcfg.exe (PID: 2572)
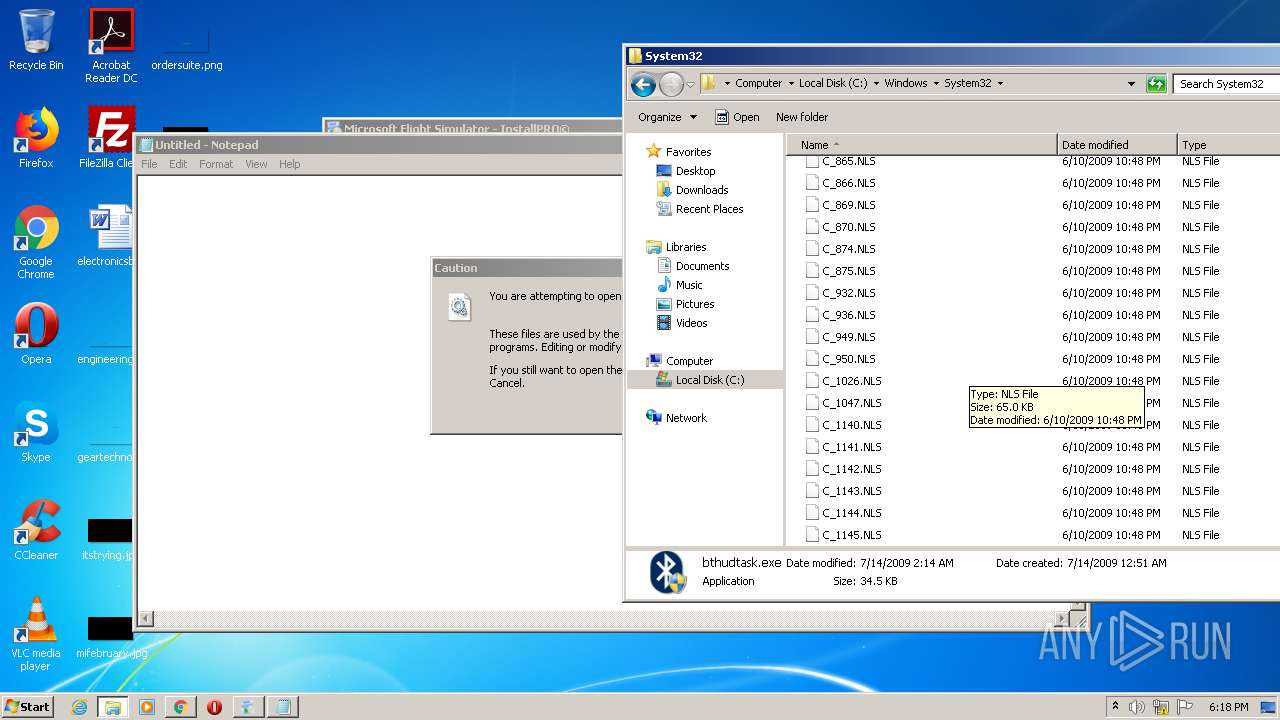
- Bubbles.scr (PID: 2792)
- cmmon32.exe (PID: 2184)
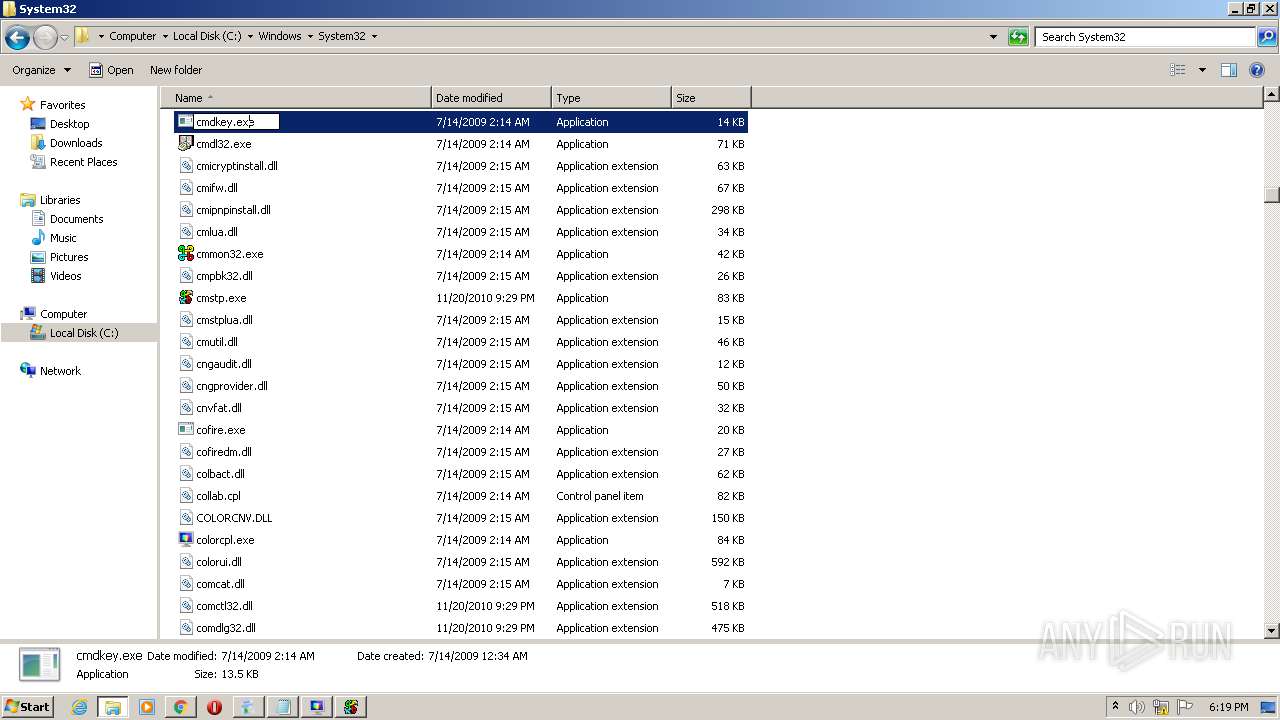
- cmdkey.exe (PID: 3984)
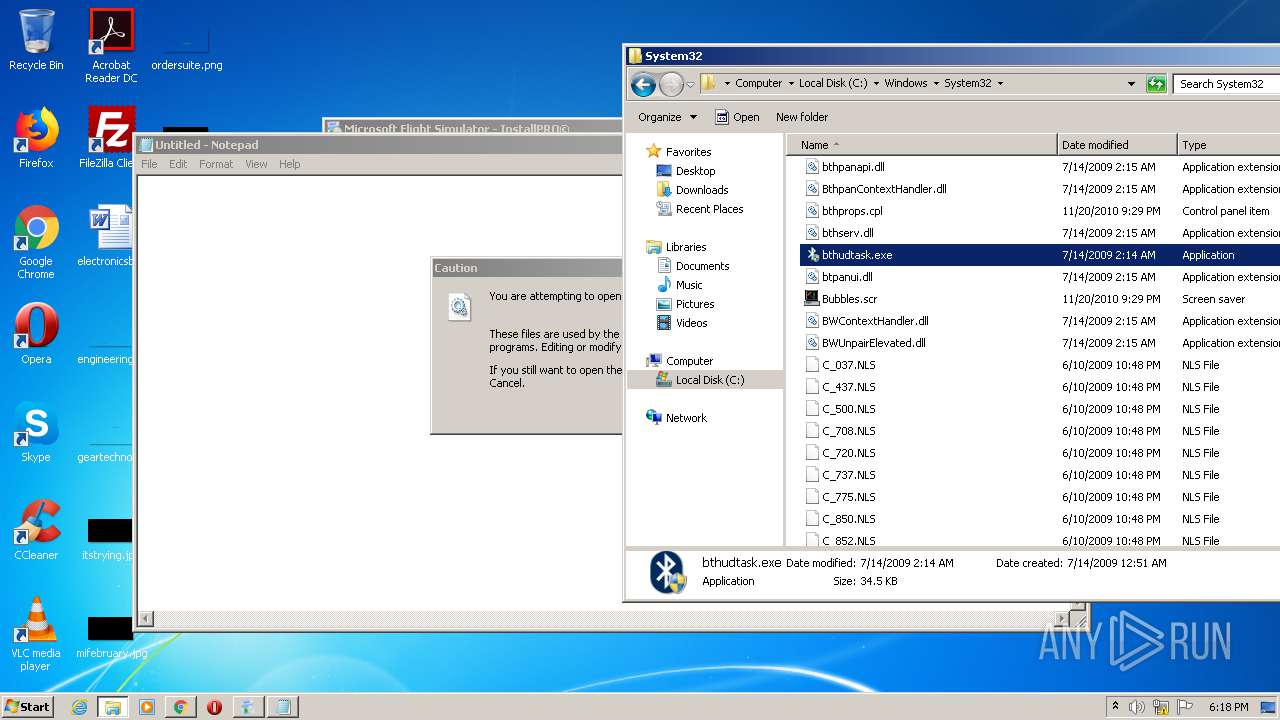
- bthudtask.exe (PID: 1348)
- bthudtask.exe (PID: 560)
- cmdl32.exe (PID: 2212)
- rundll32.exe (PID: 3036)
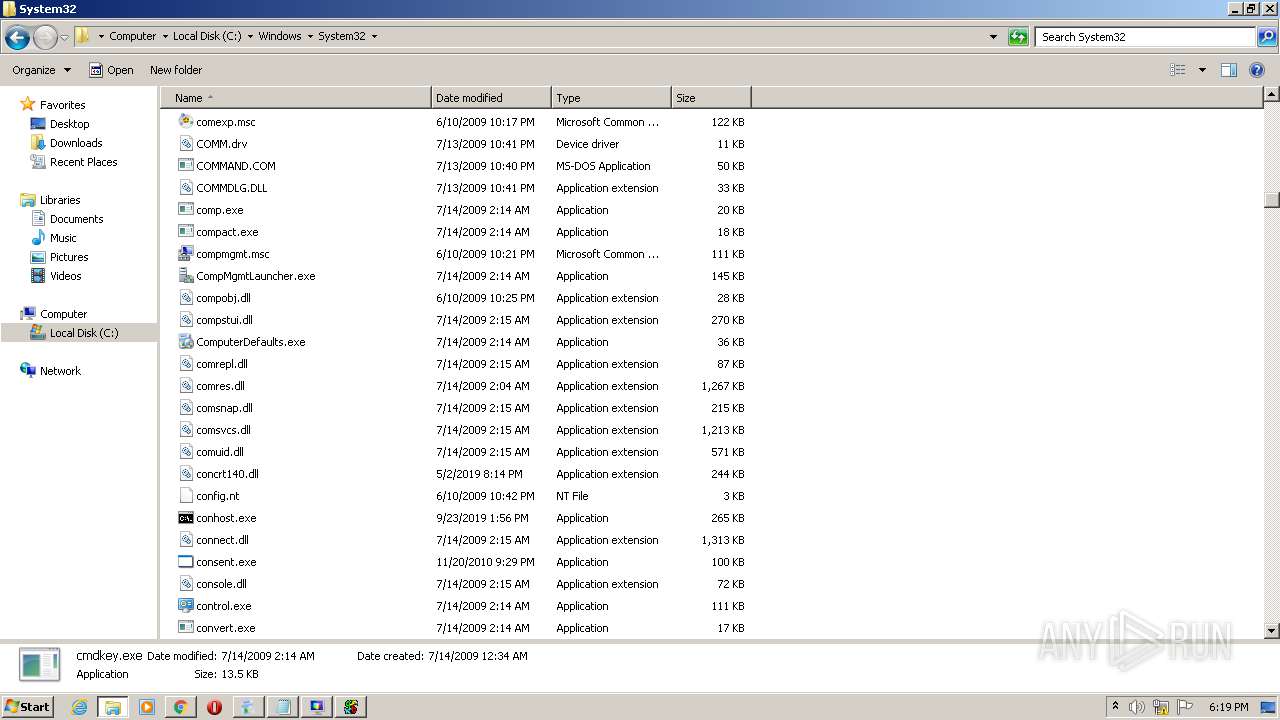
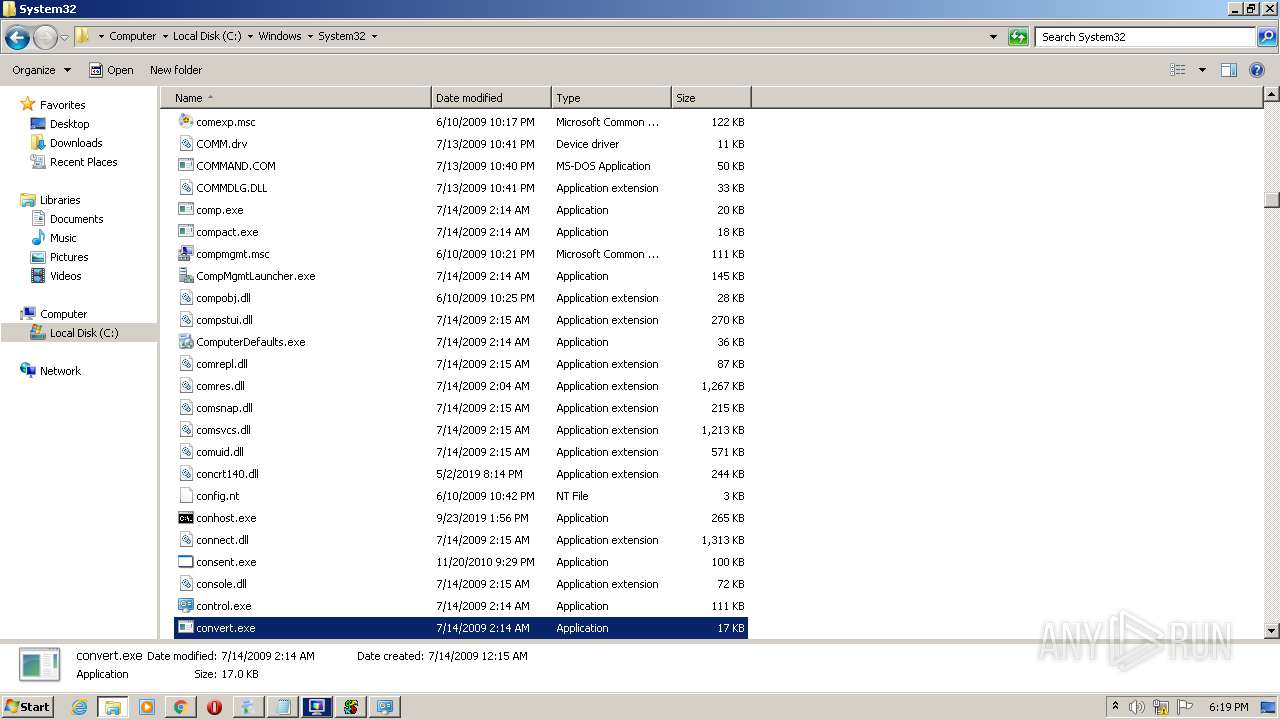
- convert.exe (PID: 2820)
- ComputerDefaults.exe (PID: 576)
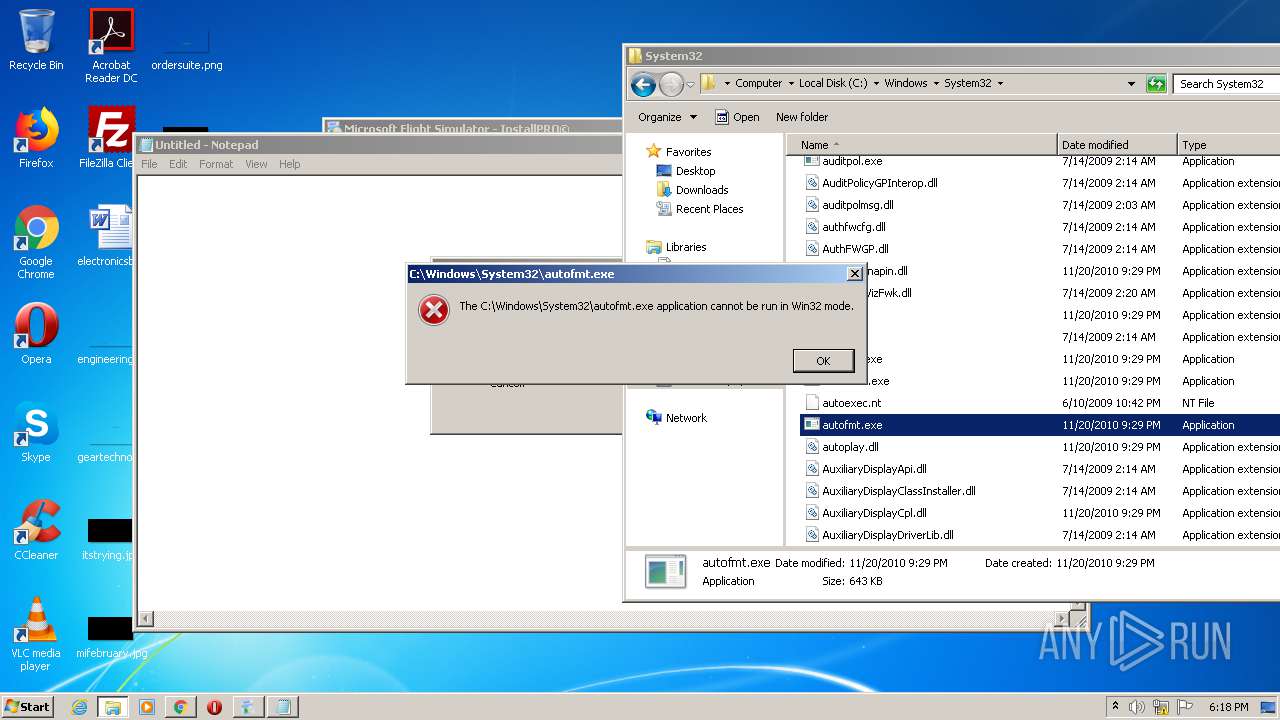
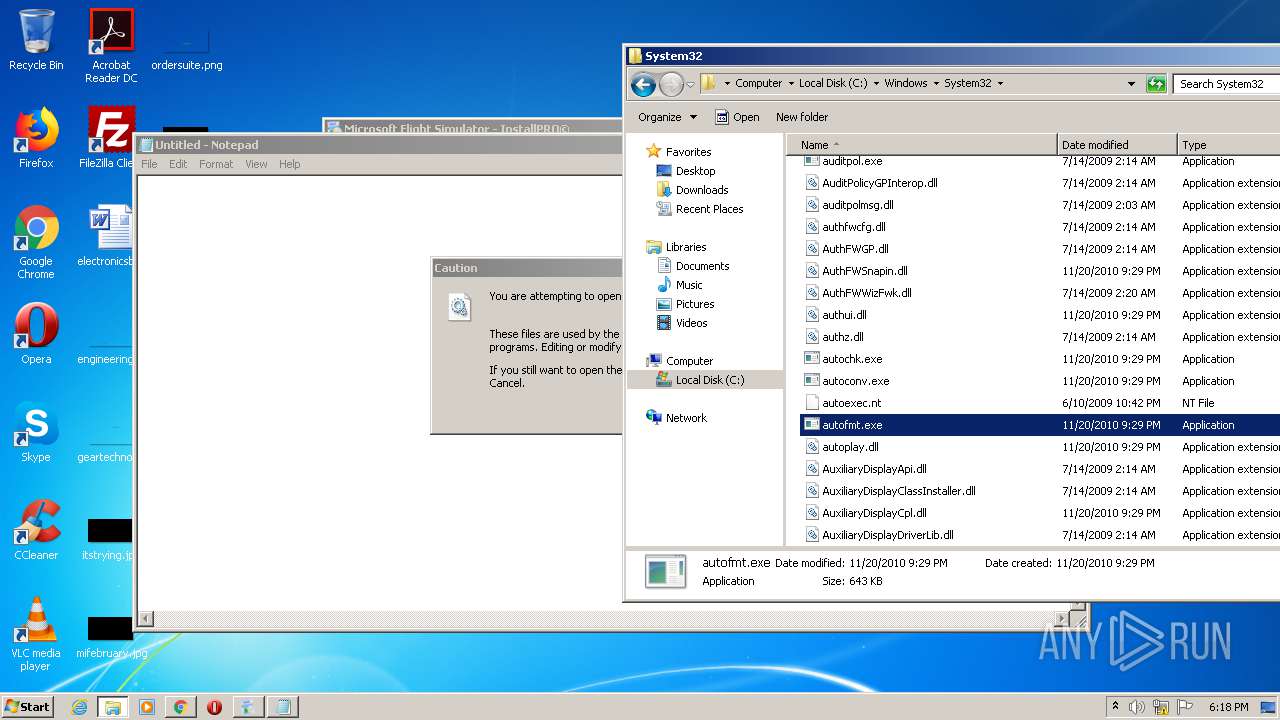
- autofmt.exe (PID: 2348)
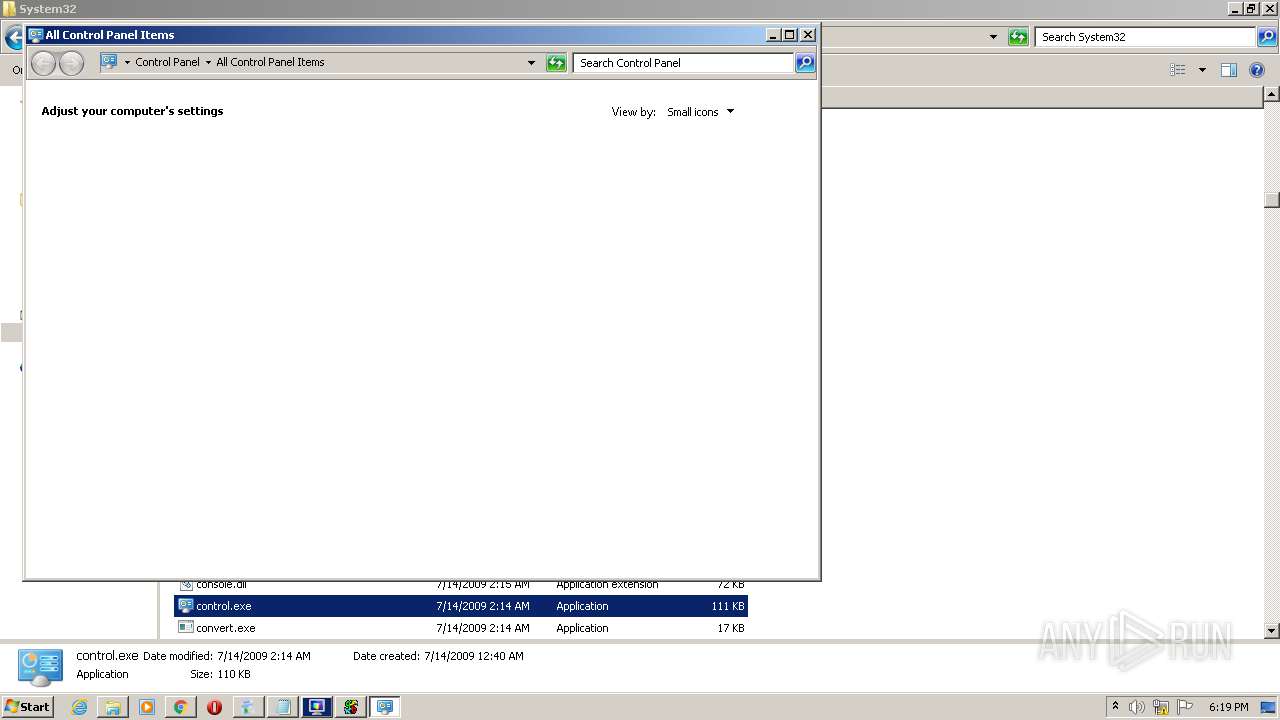
- control.exe (PID: 2584)
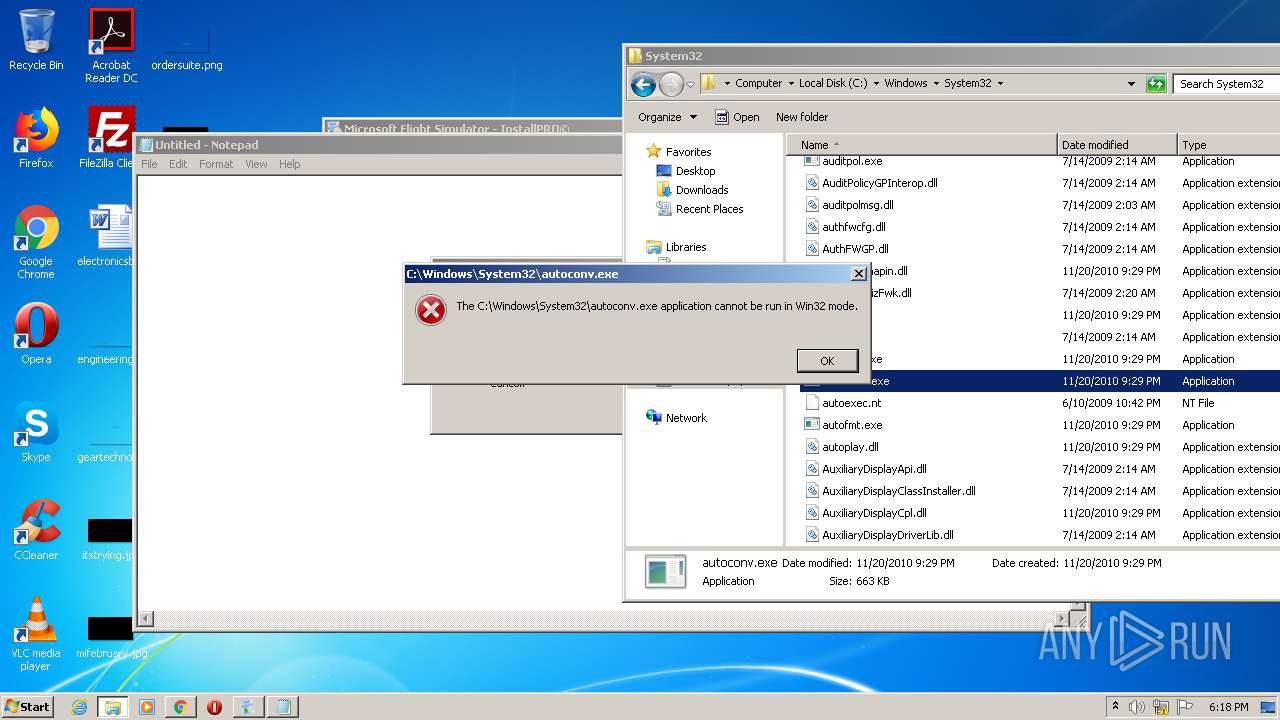
- autoconv.exe (PID: 3160)
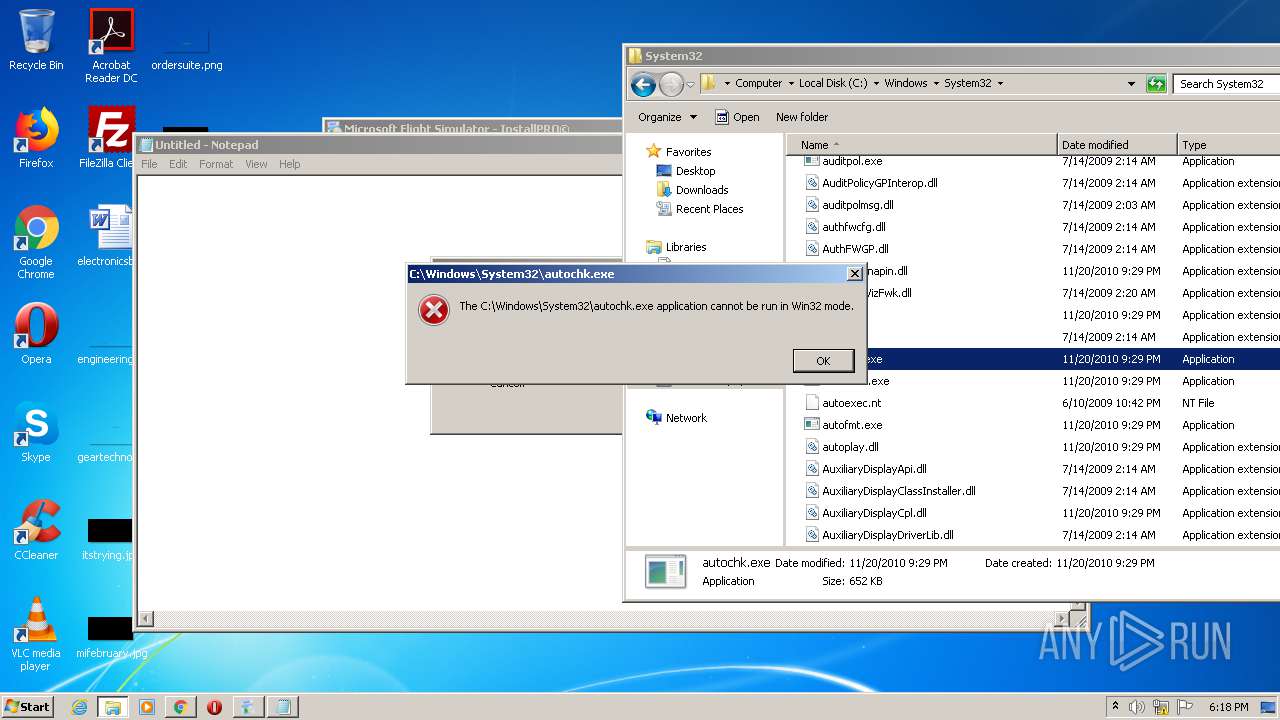
- autochk.exe (PID: 1192)
- conhost.exe (PID: 3848)
- control.exe (PID: 3148)
- ComputerDefaults.exe (PID: 2772)
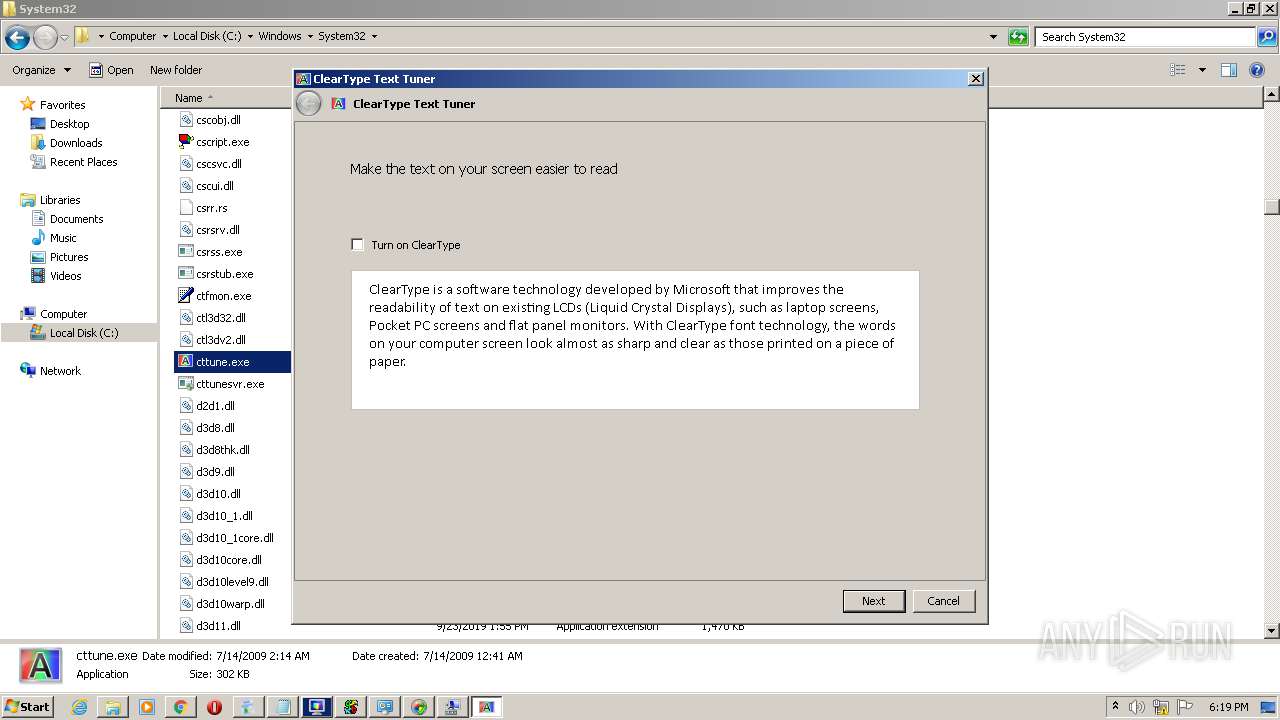
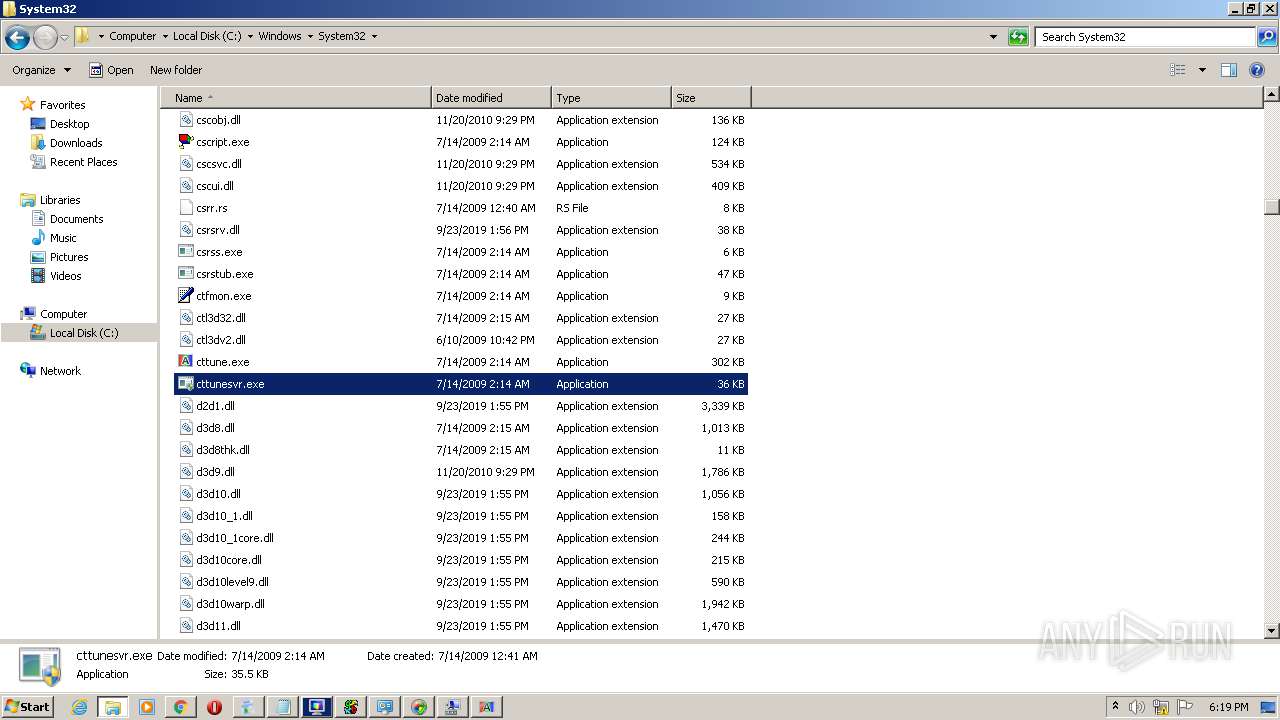
- cttune.exe (PID: 3736)
- cttunesvr.exe (PID: 2172)
- cttunesvr.exe (PID: 2528)
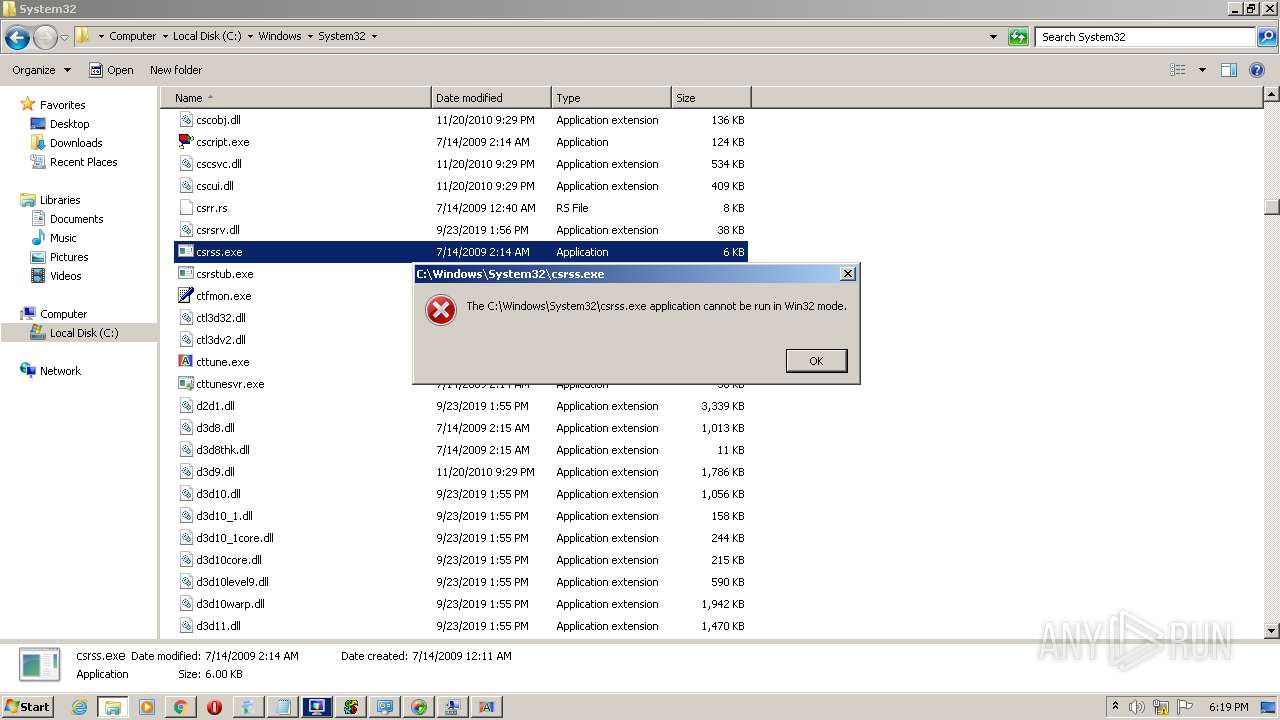
- csrstub.exe (PID: 1856)
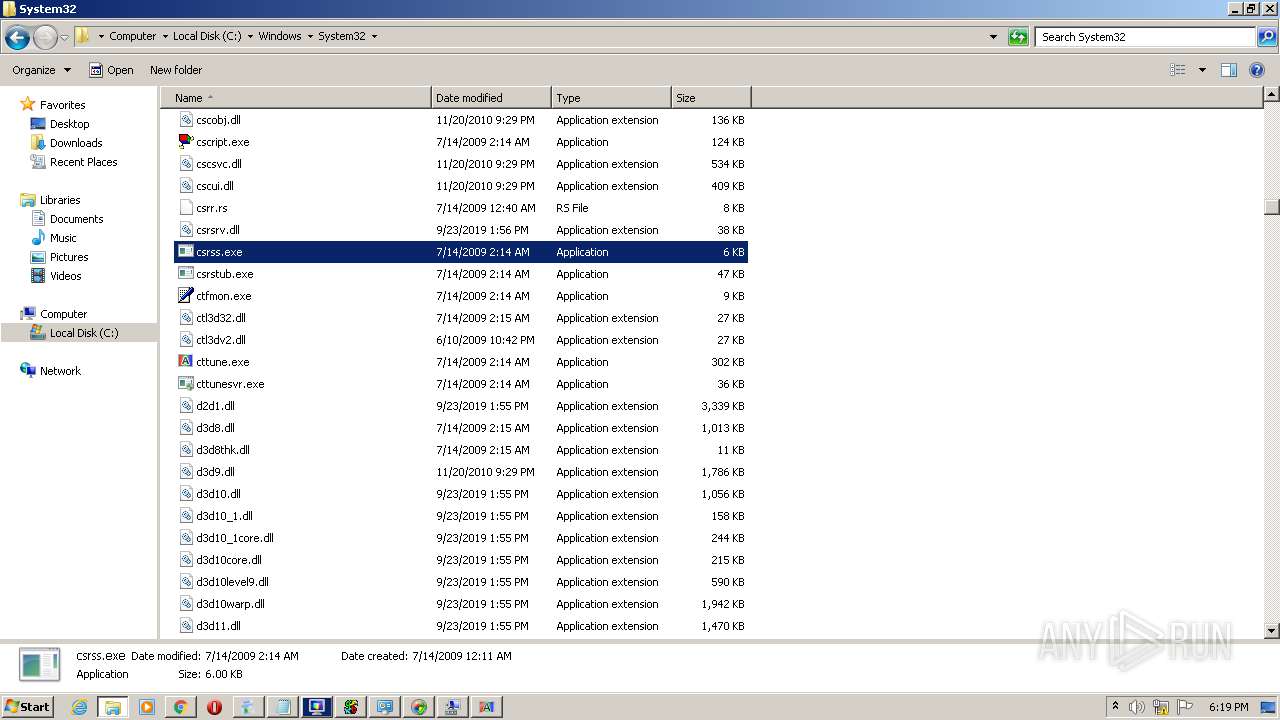
- csrss.exe (PID: 2348)
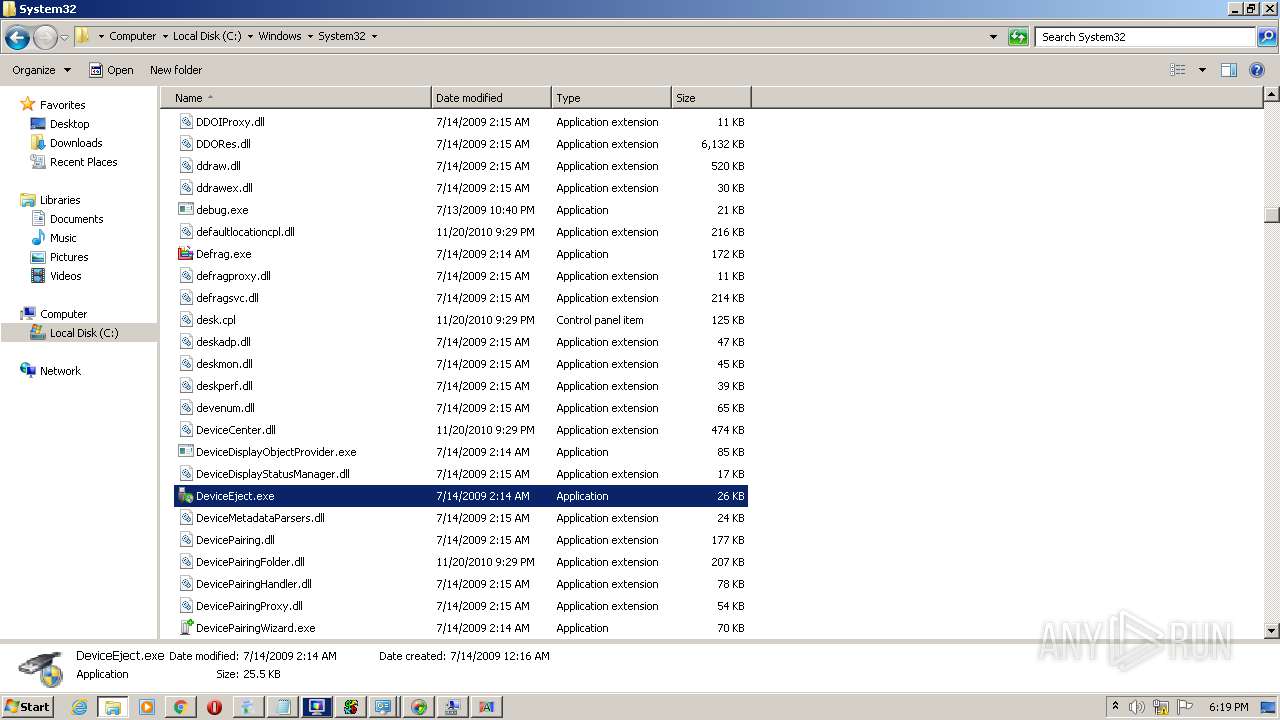
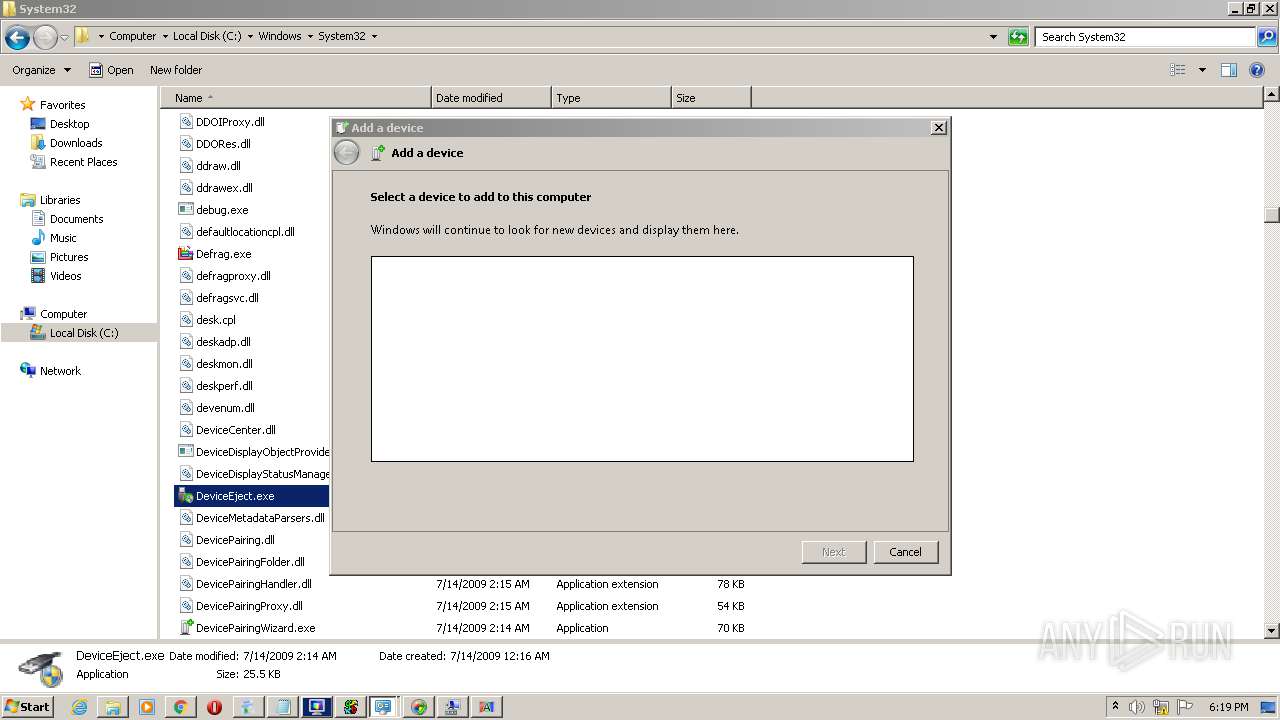
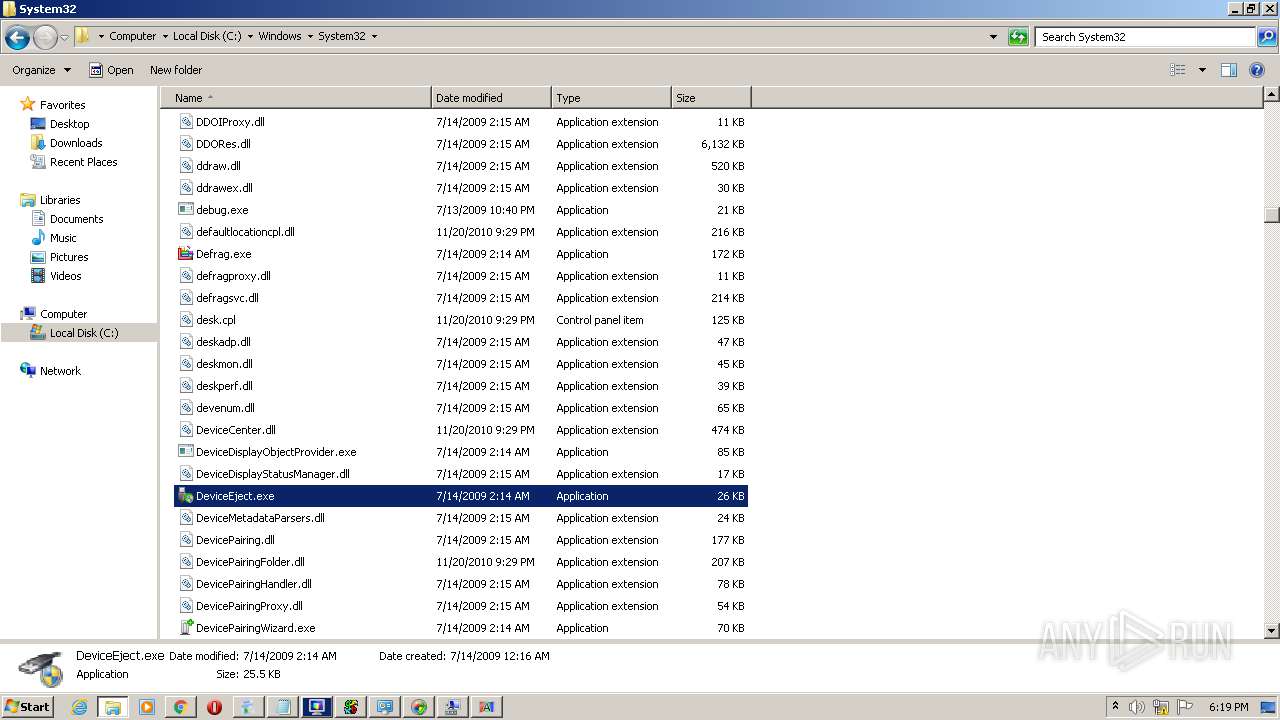
- DeviceEject.exe (PID: 3988)
- DeviceEject.exe (PID: 3360)
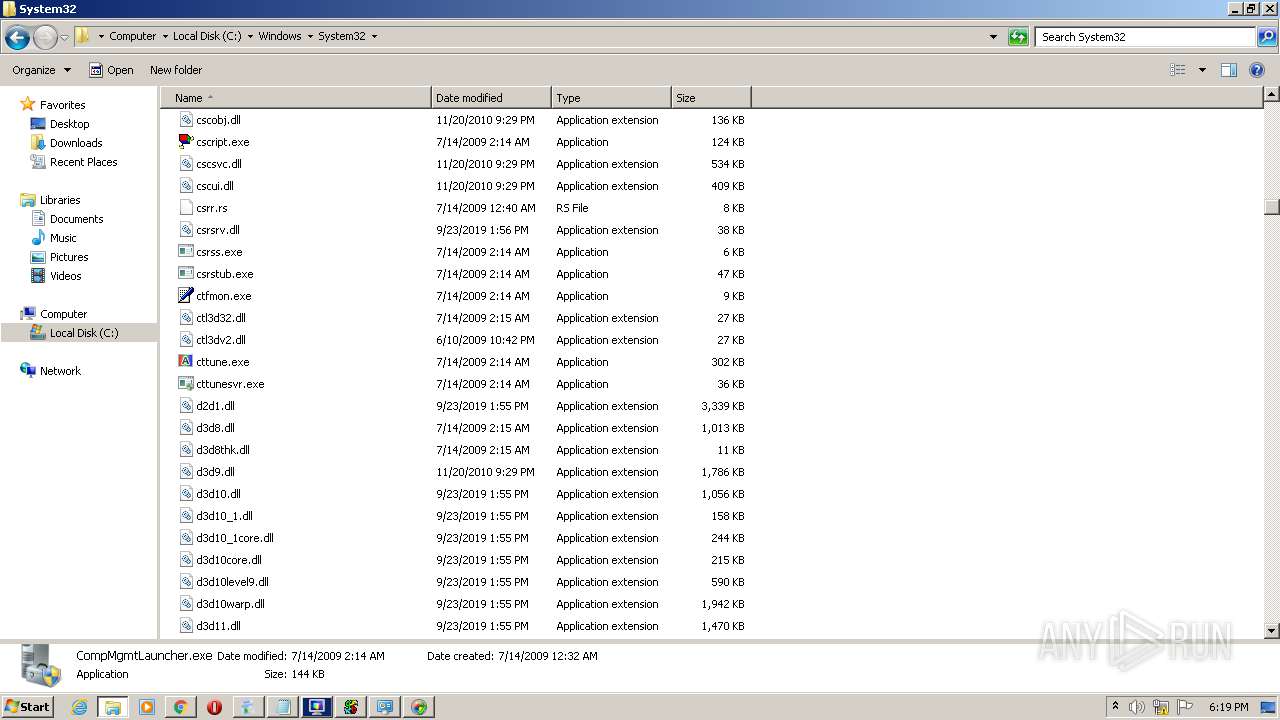
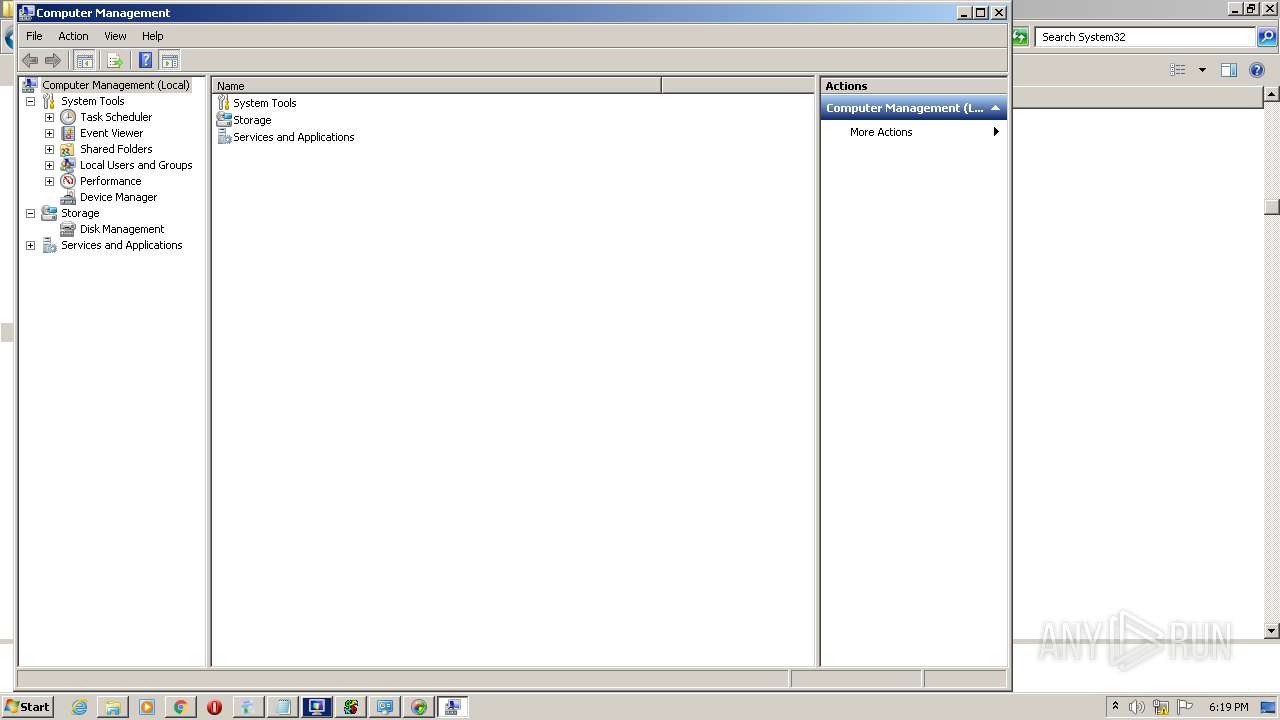
- CompMgmtLauncher.exe (PID: 1348)
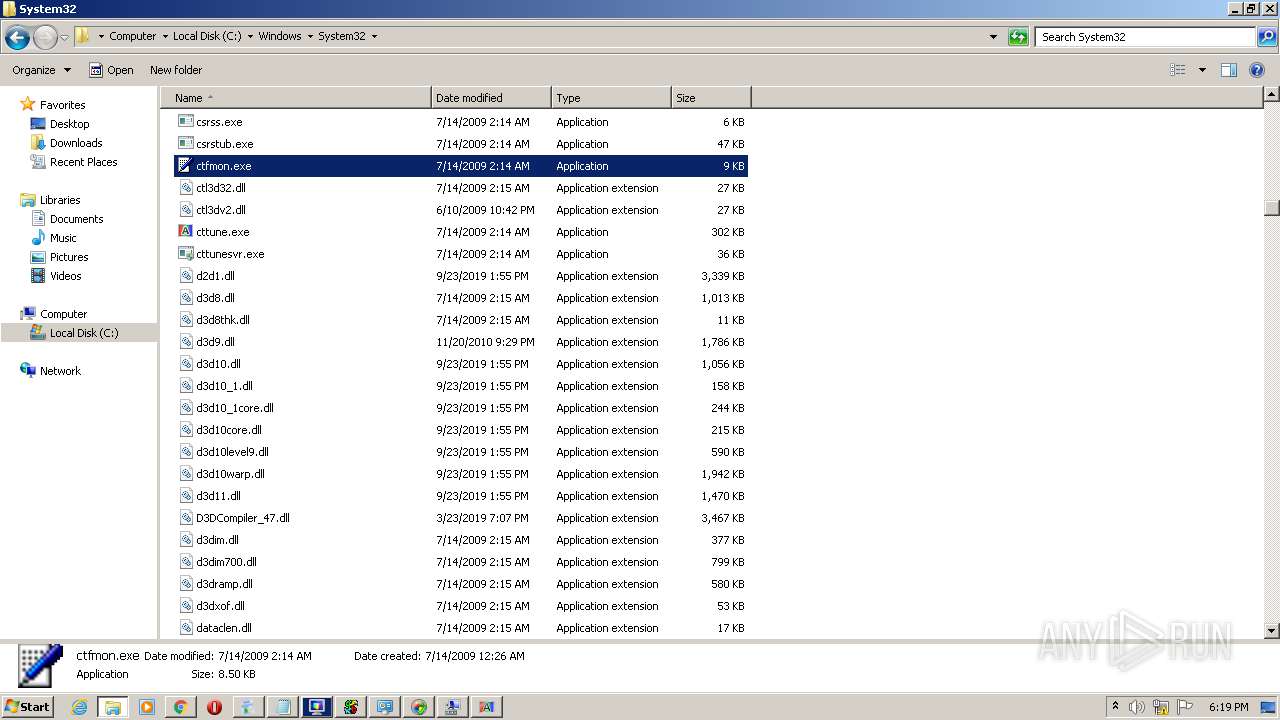
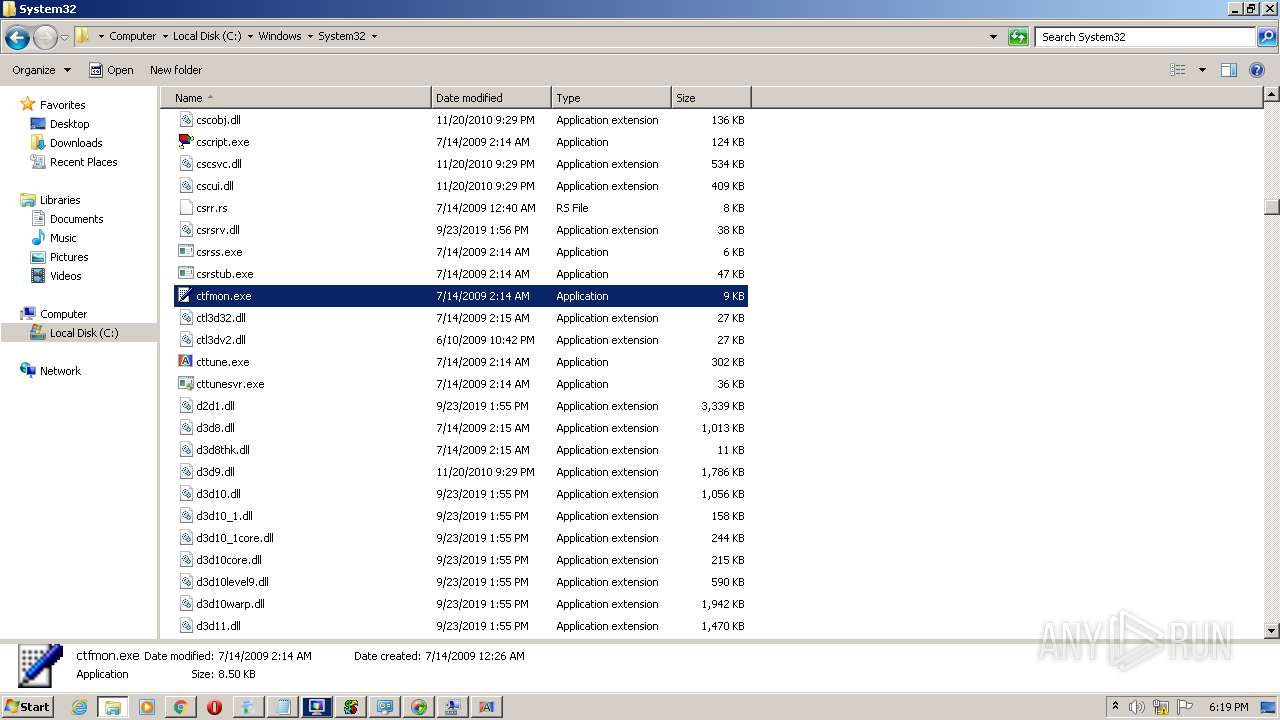
- ctfmon.exe (PID: 2656)
- DevicePairingWizard.exe (PID: 2912)
- CompMgmtLauncher.exe (PID: 2780)
- colorcpl.exe (PID: 2904)
- cmstp.exe (PID: 4012)
Reads the hosts file
- chrome.exe (PID: 1624)
- chrome.exe (PID: 1972)
Application launched itself
- chrome.exe (PID: 1624)
Reads settings of System Certificates
- chrome.exe (PID: 1624)
Reads Internet Cache Settings
- chrome.exe (PID: 1624)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
156
Monitored processes
86
Malicious processes
3
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 560 | "C:\Windows\System32\bthudtask.exe" | C:\Windows\System32\bthudtask.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Bluetooth Uninstall Device Task Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 576 | "C:\Windows\System32\ComputerDefaults.exe" | C:\Windows\System32\ComputerDefaults.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Set Program Access and Computer Defaults Control Panel Exit code: 3221226540 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 692 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1044,15161964132569291214,9290868077513736562,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=156531815559107644 --mojo-platform-channel-handle=3548 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 760 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1044,15161964132569291214,9290868077513736562,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=4688920067985556251 --mojo-platform-channel-handle=2616 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
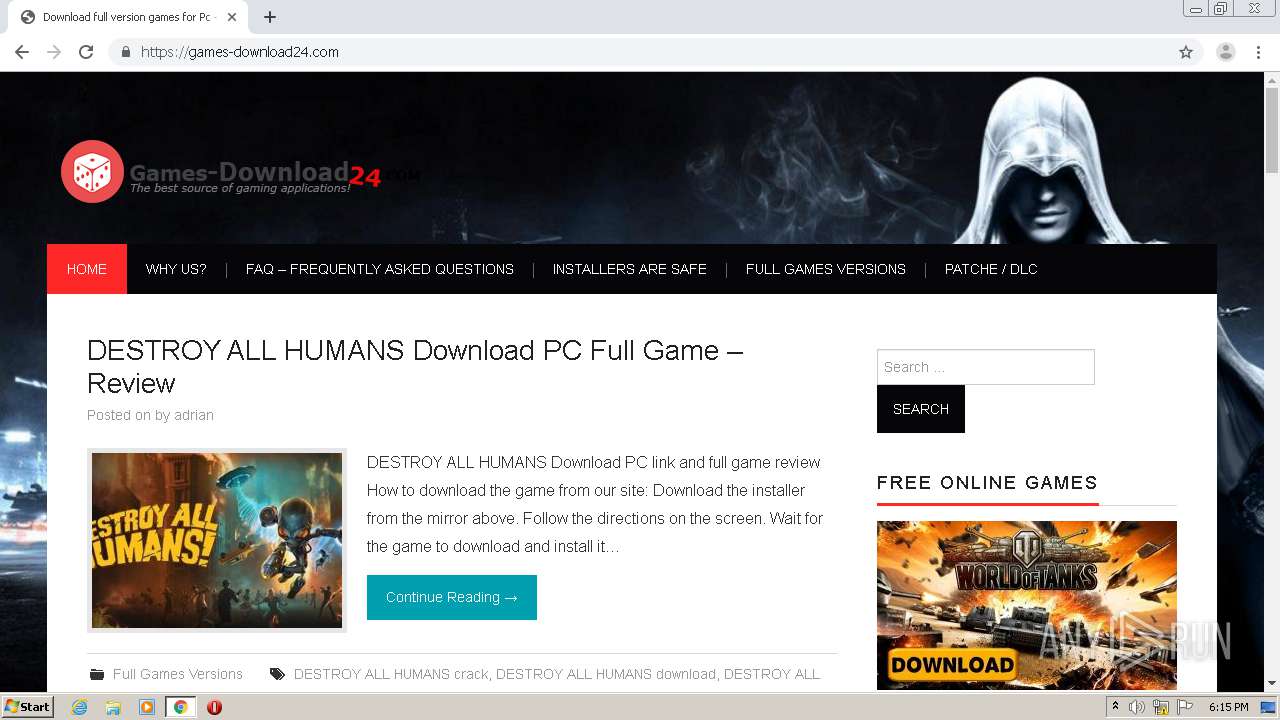
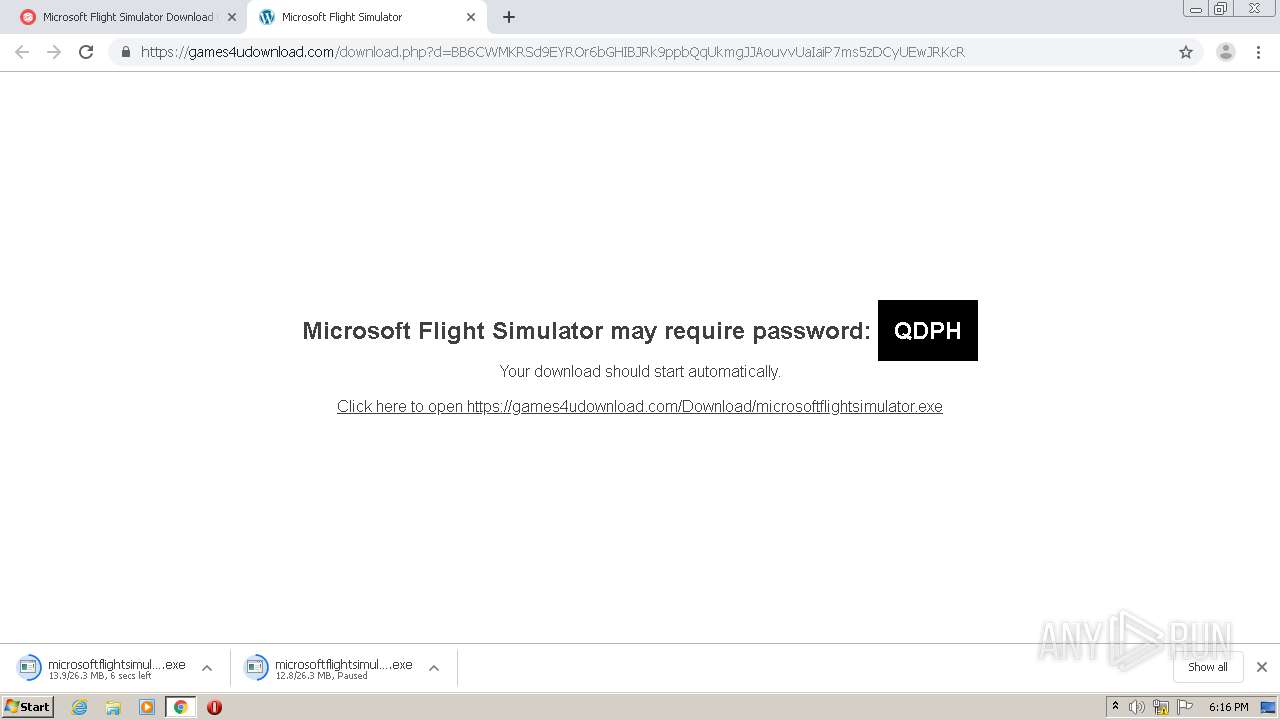
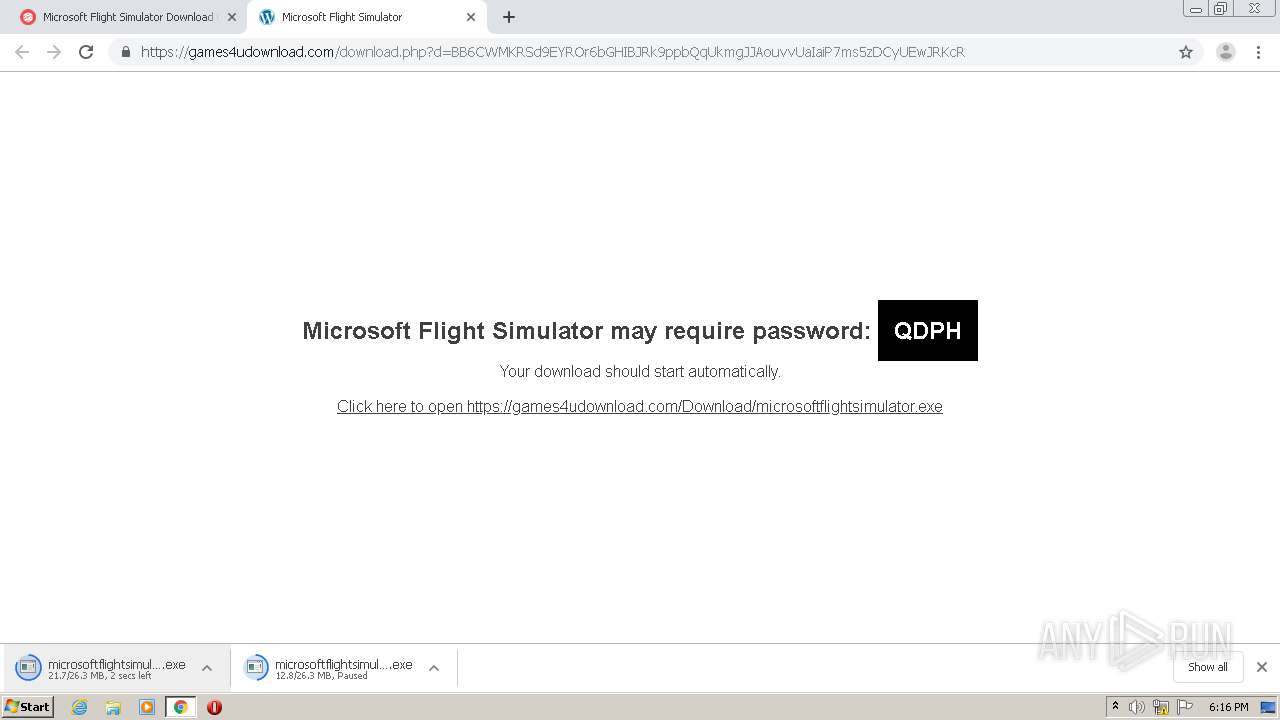
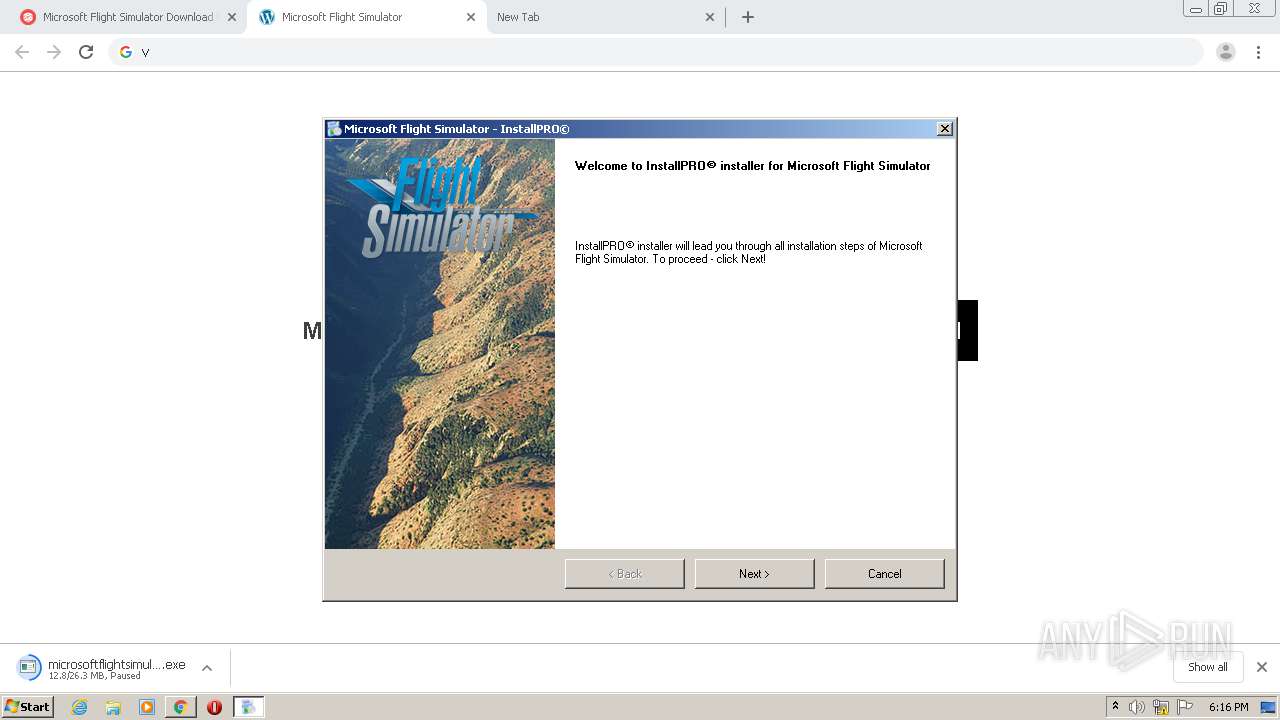
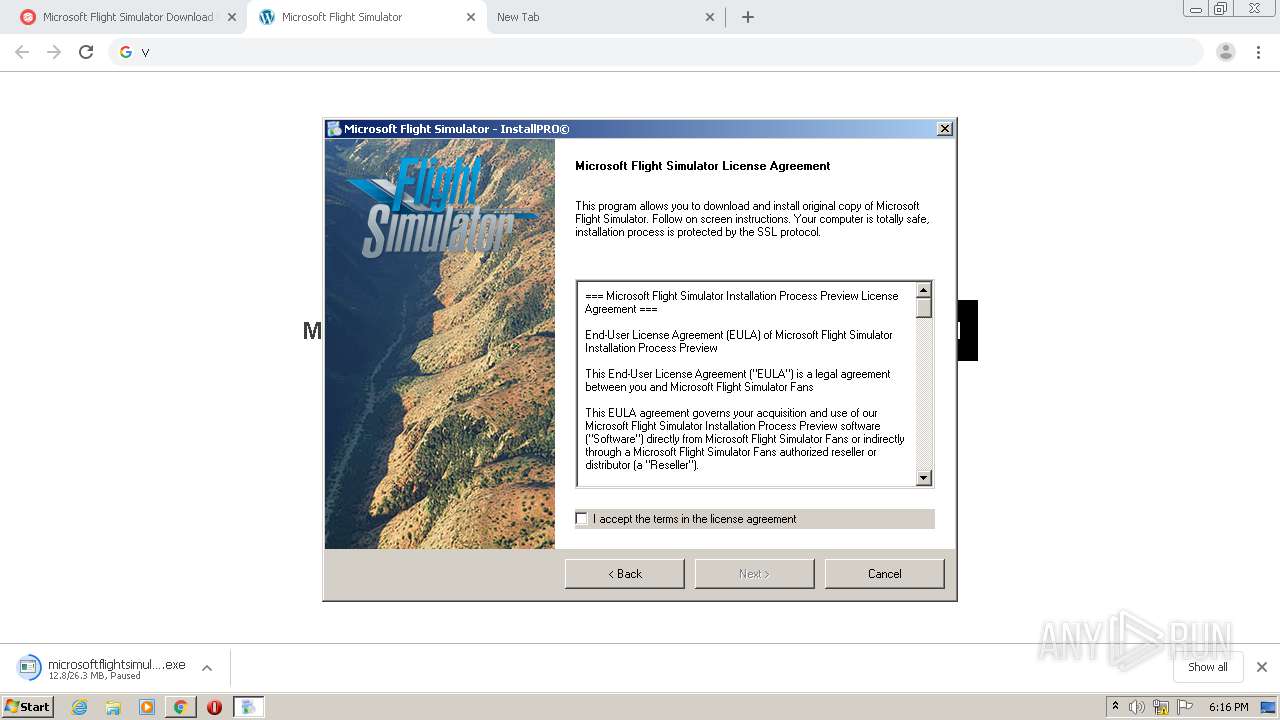
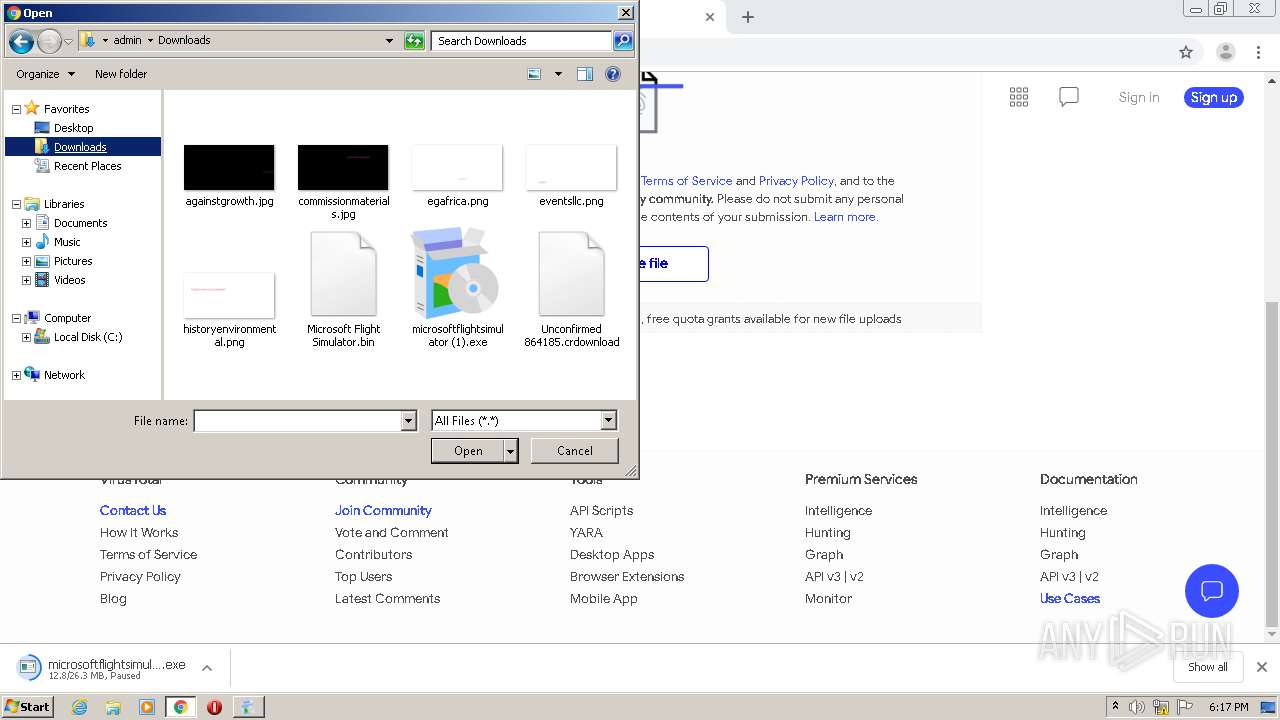
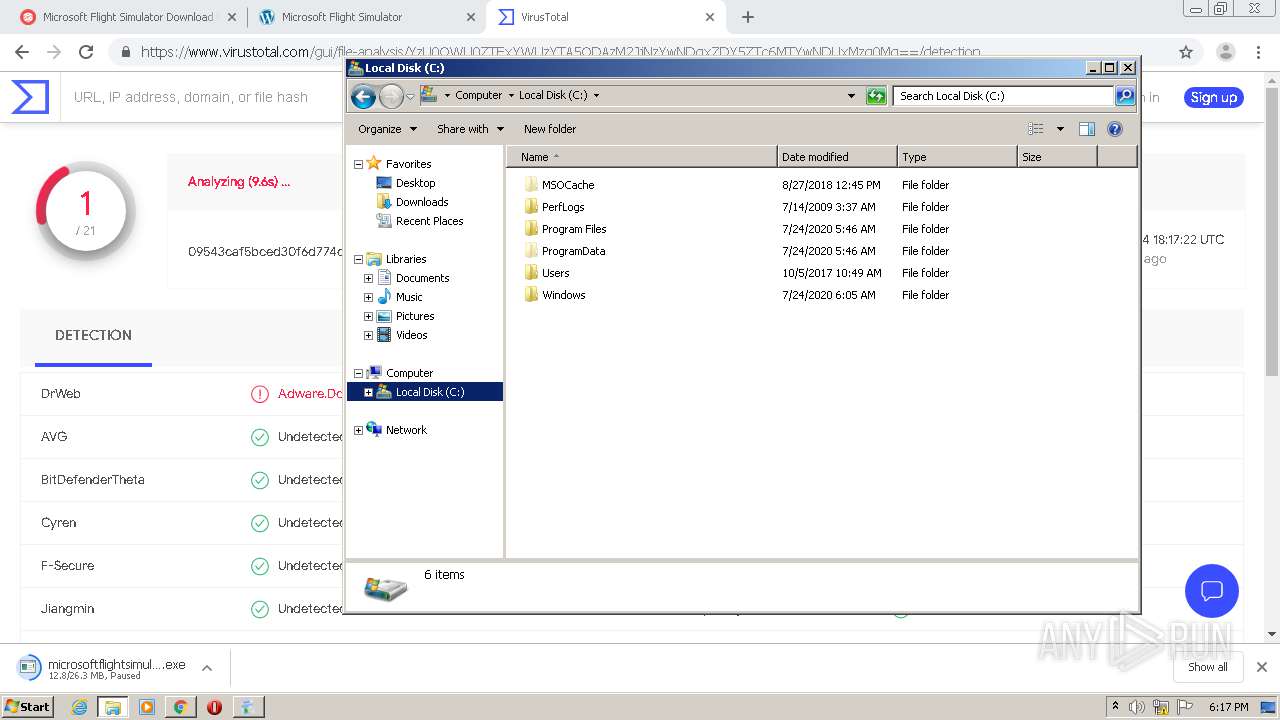
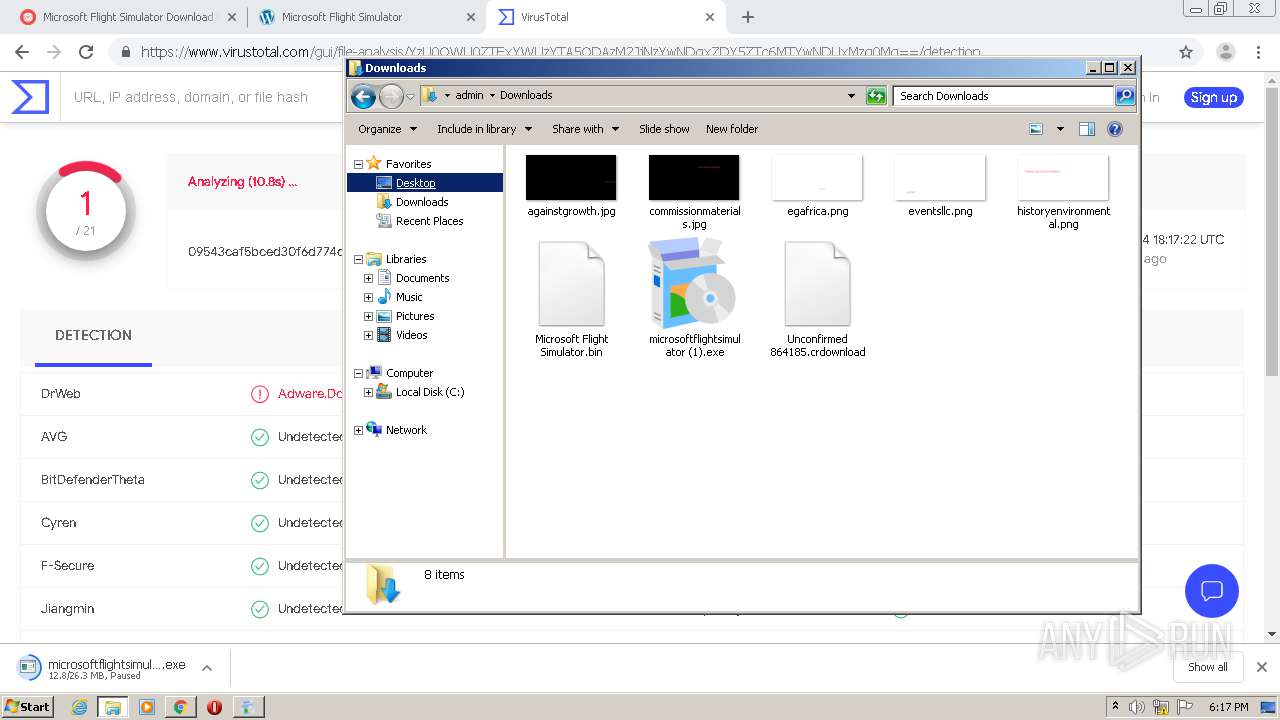
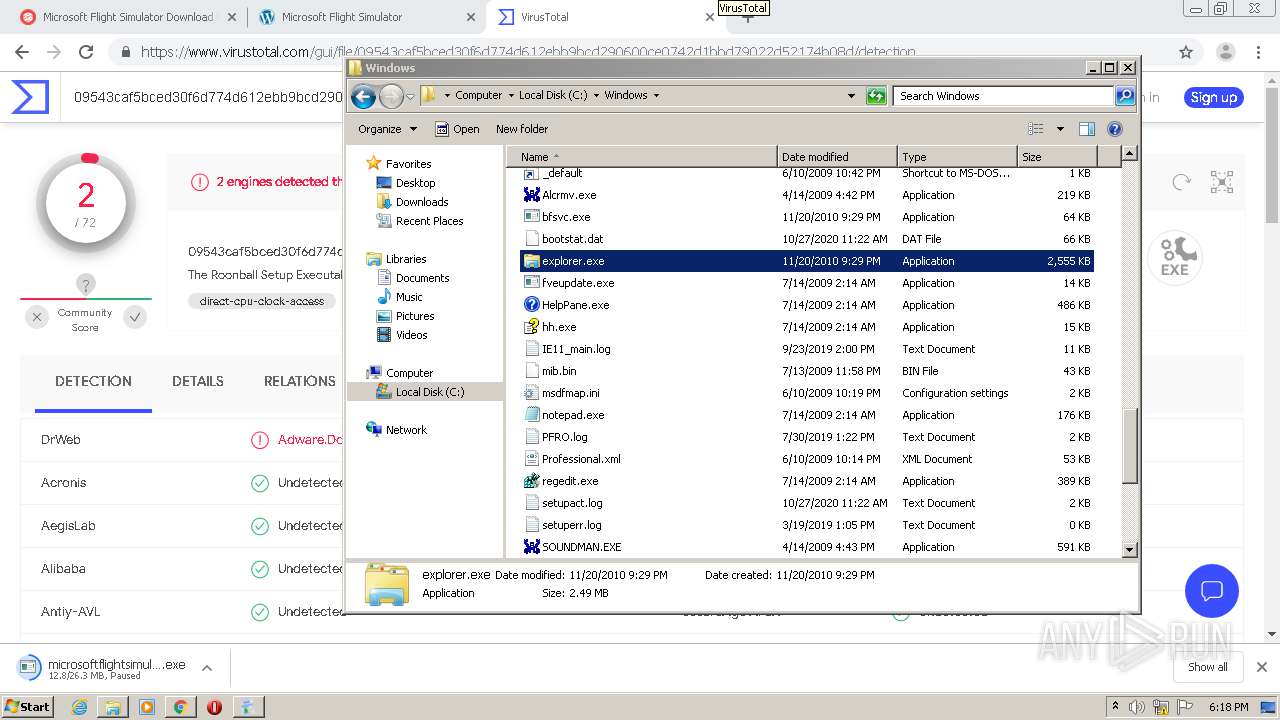
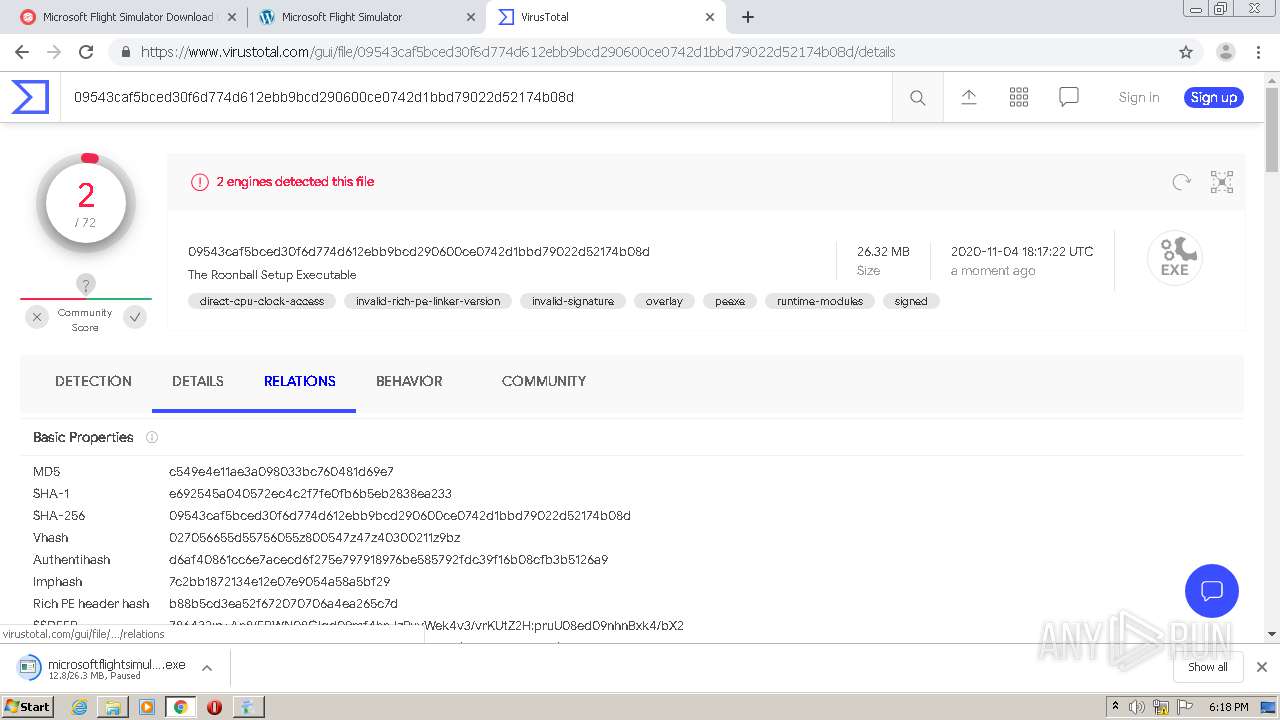
| 768 | "C:\Users\admin\Downloads\microsoftflightsimulator (1).exe" | C:\Users\admin\Downloads\microsoftflightsimulator (1).exe | chrome.exe | ||||||||||||
User: admin Company: Roonball Ltd. Integrity Level: MEDIUM Description: The Roonball Setup Executable Exit code: 0 Version: 1.4.188.10084 Modules
| |||||||||||||||
| 1096 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1044,15161964132569291214,9290868077513736562,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=2221342561874621526 --renderer-client-id=10 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=1416 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1192 | "C:\Windows\System32\autochk.exe" | C:\Windows\System32\autochk.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Auto Check Utility Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1348 | "C:\Windows\System32\bthudtask.exe" | C:\Windows\System32\bthudtask.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Bluetooth Uninstall Device Task Exit code: 3221226540 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1348 | "C:\Windows\System32\CompMgmtLauncher.exe" | C:\Windows\System32\CompMgmtLauncher.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Computer Management Snapin Launcher Exit code: 3221226540 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1484 | "C:\Windows\system32\cmd.exe" | C:\Windows\system32\cmd.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 3221225786 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
Total events
2 922
Read events
2 429
Write events
488
Delete events
5
Modification events
| (PID) Process: | (1624) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (1624) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (1624) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (1624) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (1624) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (2720) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 1624-13248987287245875 |
Value: 259 | |||
| (PID) Process: | (1624) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (1624) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (1624) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 3252-13245750958665039 |
Value: 0 | |||
| (PID) Process: | (1624) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
Executable files
6
Suspicious files
156
Text files
321
Unknown types
12
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1624 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\BrowserMetrics\BrowserMetrics-5FA2EF98-658.pma | — | |
MD5:— | SHA256:— | |||
| 1624 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\489fe449-9bfd-42a9-9d30-9b409dad5a87.tmp | — | |
MD5:— | SHA256:— | |||
| 1624 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000048.dbtmp | — | |
MD5:— | SHA256:— | |||
| 1624 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old | text | |
MD5:— | SHA256:— | |||
| 1624 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old~RF14ea3f.TMP | text | |
MD5:— | SHA256:— | |||
| 1624 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\BudgetDatabase\LOG.old | text | |
MD5:— | SHA256:— | |||
| 1624 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\metadata\LOG.old | — | |
MD5:— | SHA256:— | |||
| 1624 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Last Tabs | binary | |
MD5:— | SHA256:— | |||
| 1624 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 1624 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old~RF14ec23.TMP | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
11
TCP/UDP connections
80
DNS requests
55
Threats
0
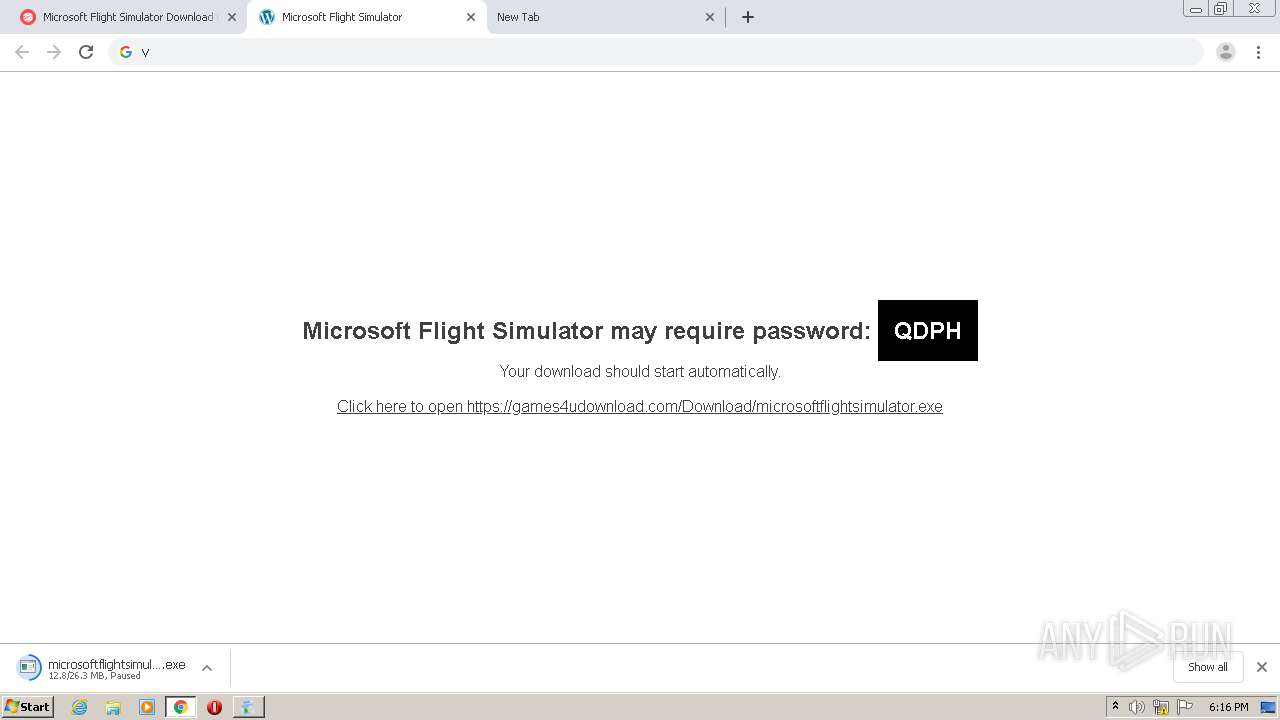
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
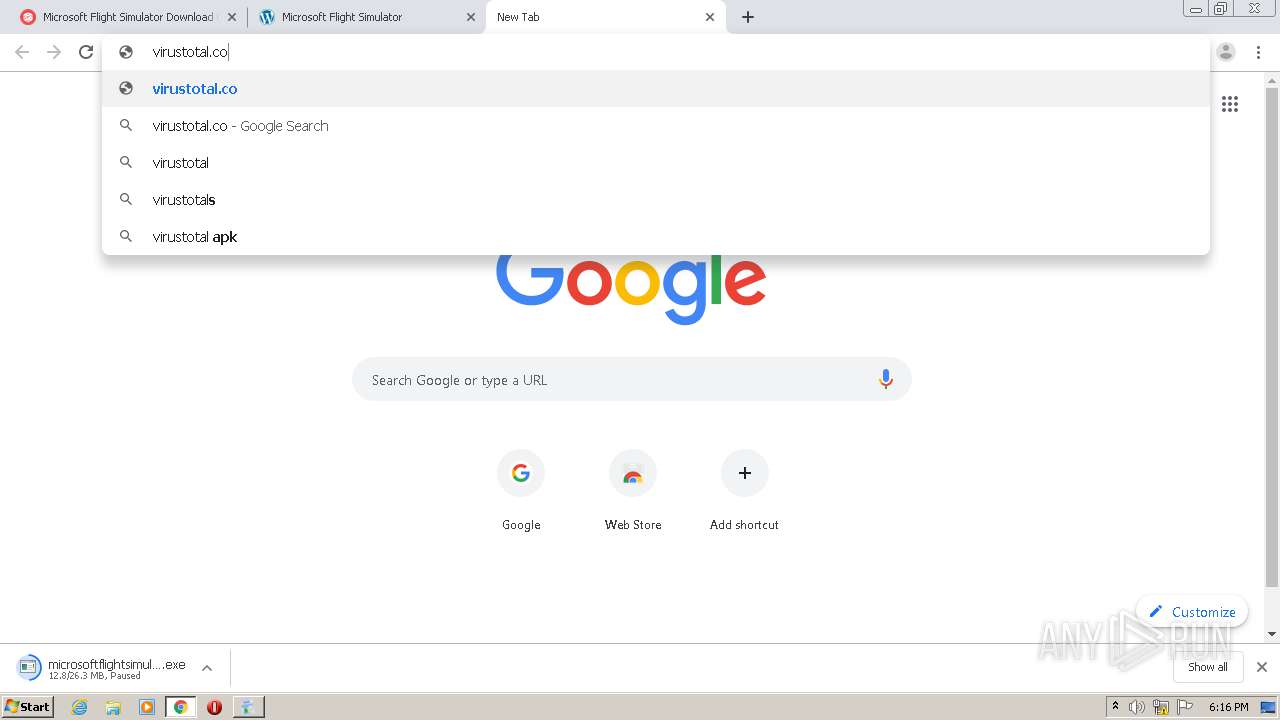
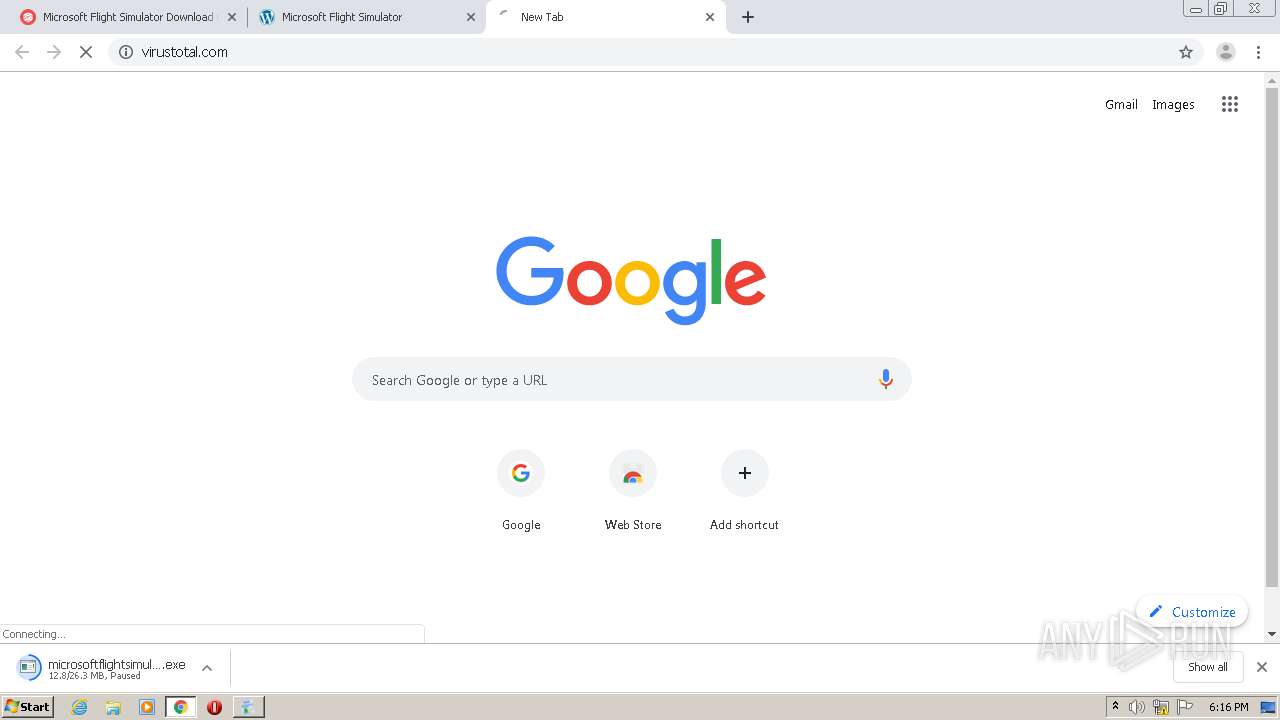
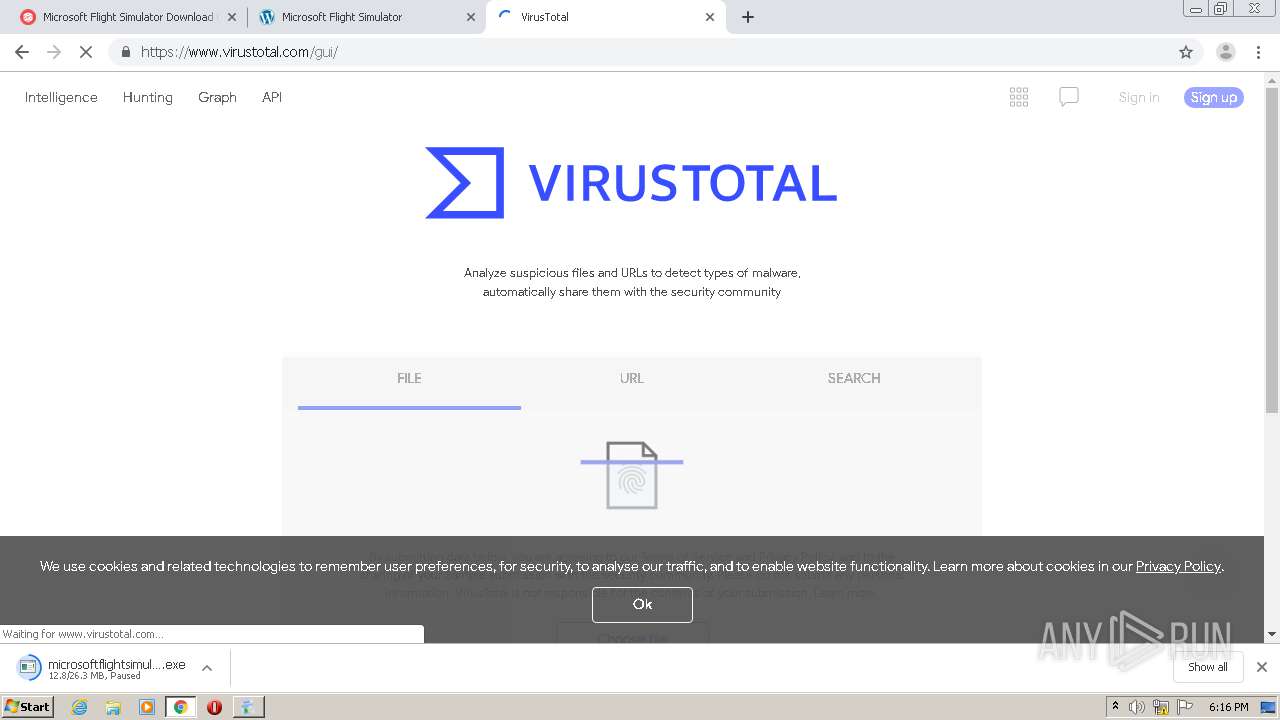
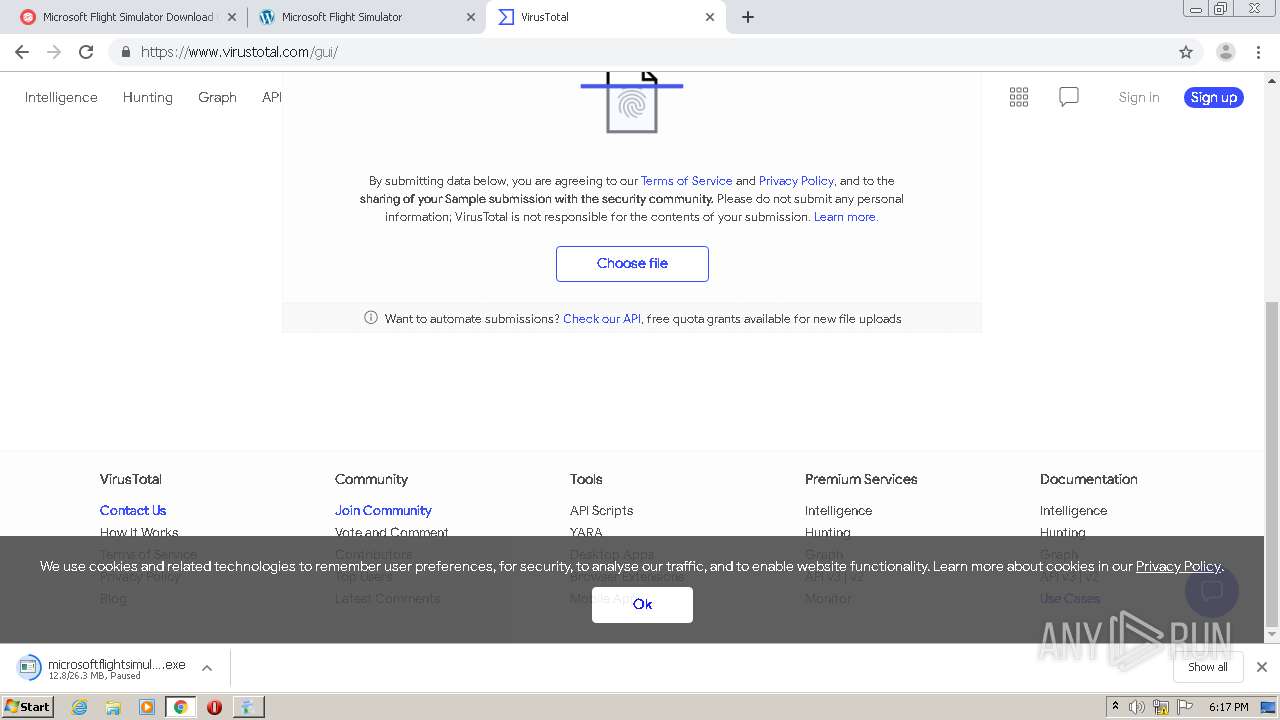
1972 | chrome.exe | GET | 302 | 216.239.38.21:80 | http://virustotal.com/ | US | — | — | whitelisted |
3640 | pas.exe | POST | 200 | 142.93.142.222:80 | http://api.cc.client.dvjlimited.com/s/r | CA | text | 31 b | unknown |
3640 | pas.exe | POST | 200 | 142.93.142.222:80 | http://api.cc.client.dvjlimited.com/s/o | CA | text | 78 b | unknown |
3640 | pas.exe | POST | 200 | 142.93.142.222:80 | http://api.cc.client.dvjlimited.com/u/m | CA | text | 34 b | unknown |
1972 | chrome.exe | GET | 302 | 172.217.18.110:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvZDM4QUFXaVZ5bThYeHlpdXd5bzU1RzRQUQ/8220.313.1.2_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx | US | html | 531 b | whitelisted |
1972 | chrome.exe | GET | 200 | 159.148.69.143:80 | http://r4---sn-a5uoxu-gpme.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvZDM4QUFXaVZ5bThYeHlpdXd5bzU1RzRQUQ/8220.313.1.2_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx?cms_redirect=yes&mh=i8&mip=80.233.134.134&mm=28&mn=sn-a5uoxu-gpme&ms=nvh&mt=1604513595&mv=m&mvi=4&pl=24&shardbypass=yes | LV | crx | 839 Kb | whitelisted |
1972 | chrome.exe | GET | 200 | 2.16.106.186:80 | http://www.download.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab | unknown | compressed | 57.5 Kb | whitelisted |
1972 | chrome.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTfqhLjKLEJQZPin0KCzkdAQpVYowQUsT7DaQP4v0cB1JgmGggC72NkK8MCEAx5qUSwjBGVIJJhX%2BJrHYM%3D | US | der | 471 b | whitelisted |
768 | microsoftflightsimulator (1).exe | GET | 200 | 23.55.163.77:80 | http://isrg.trustid.ocsp.identrust.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBRv9GhNQxLSSGKBnMArPUcsHYovpgQUxKexpHsscfrb4UuQdf%2FEFWCFiRACEAoBQUIAAAFThXNqC4Xspwg%3D | US | der | 1.37 Kb | whitelisted |
768 | microsoftflightsimulator (1).exe | GET | 200 | 192.35.177.64:80 | http://crl.identrust.com/DSTROOTCAX3CRL.crl | US | der | 1.16 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1972 | chrome.exe | 162.243.10.151:443 | googe.com | Digital Ocean, Inc. | US | unknown |
1972 | chrome.exe | 172.217.18.164:443 | www.google.com | Google Inc. | US | whitelisted |
1972 | chrome.exe | 216.58.208.35:443 | ssl.gstatic.com | Google Inc. | US | whitelisted |
1972 | chrome.exe | 172.217.18.3:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
1972 | chrome.exe | 2.16.106.186:80 | www.download.windowsupdate.com | Akamai International B.V. | — | whitelisted |
1972 | chrome.exe | 216.58.205.77:443 | accounts.google.com | Google Inc. | US | unknown |
1972 | chrome.exe | 172.217.22.14:443 | consent.google.com | Google Inc. | US | whitelisted |
1972 | chrome.exe | 172.217.22.110:443 | apis.google.com | Google Inc. | US | whitelisted |
1972 | chrome.exe | 216.58.198.35:443 | www.google.com.ua | Google Inc. | US | whitelisted |
1972 | chrome.exe | 2.16.106.171:80 | www.download.windowsupdate.com | Akamai International B.V. | — | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
clientservices.googleapis.com |
| whitelisted |
googe.com |
| whitelisted |
accounts.google.com |
| shared |
www.download.windowsupdate.com |
| whitelisted |
www.google.com |
| malicious |
ssl.gstatic.com |
| whitelisted |
www.google.com.ua |
| whitelisted |
www.gstatic.com |
| whitelisted |
consent.google.com |
| shared |
id.google.com |
| whitelisted |
Threats
Process | Message |
|---|---|
mmc.exe | ViewerViewsFolderPath = 'C:\ProgramData\Microsoft\Event Viewer\Views': Microsoft.Windows.ManagementUI.CombinedControls.EventsNode
|
mmc.exe | ViewerViewsFolderPath = 'C:\ProgramData\Microsoft\Event Viewer\Views': Microsoft.Windows.ManagementUI.CombinedControls.EventsNode
|
mmc.exe | ViewerExternalLogsPath = 'C:\ProgramData\Microsoft\Event Viewer\ExternalLogs': Microsoft.Windows.ManagementUI.CombinedControls.EventsNode
|
mmc.exe | ViewerAdminViewsPath = 'C:\ProgramData\Microsoft\Event Viewer\Views\ApplicationViewsRootNode': Microsoft.Windows.ManagementUI.CombinedControls.EventsNode
|
mmc.exe | AddIcons: Microsoft.TaskScheduler.SnapIn.TaskSchedulerExtension
|