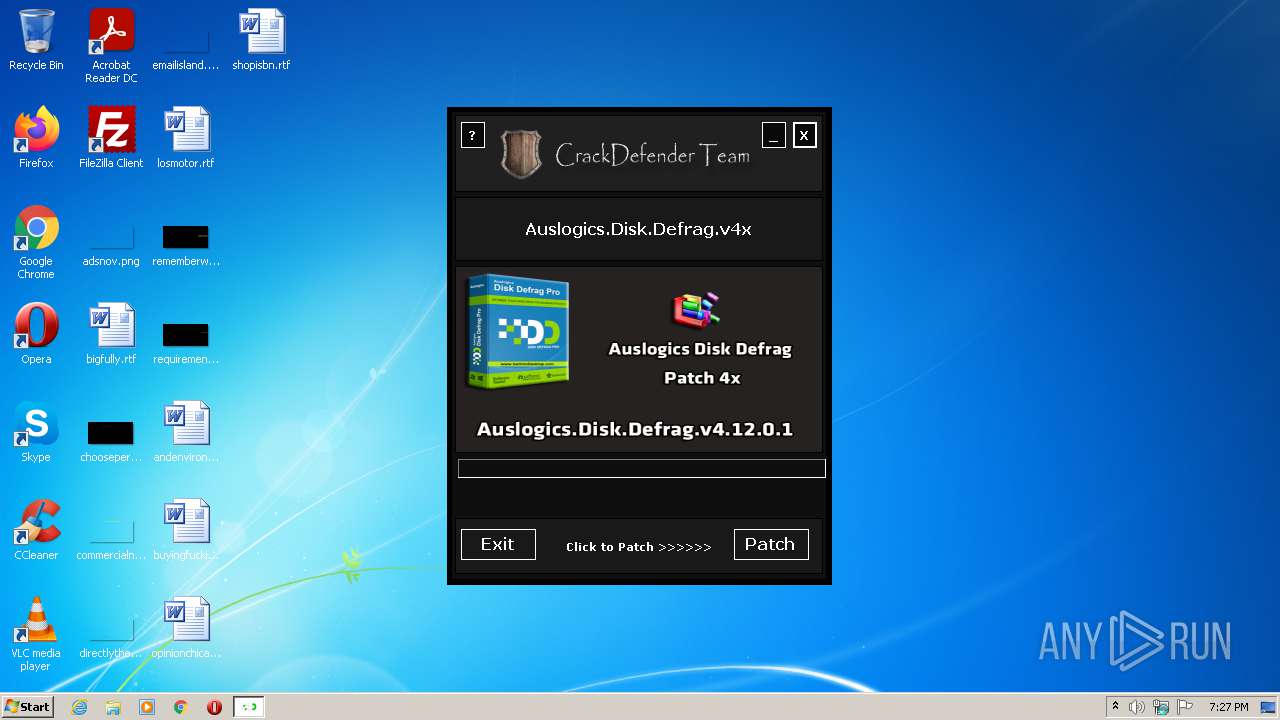
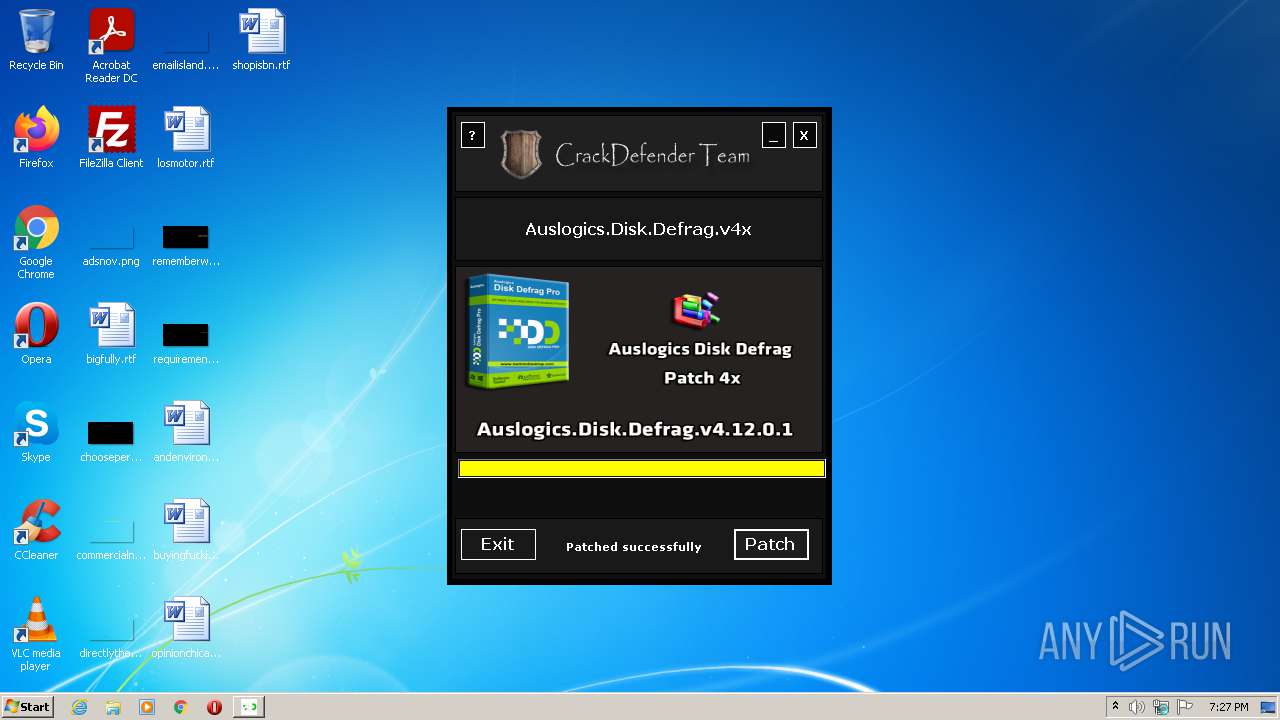
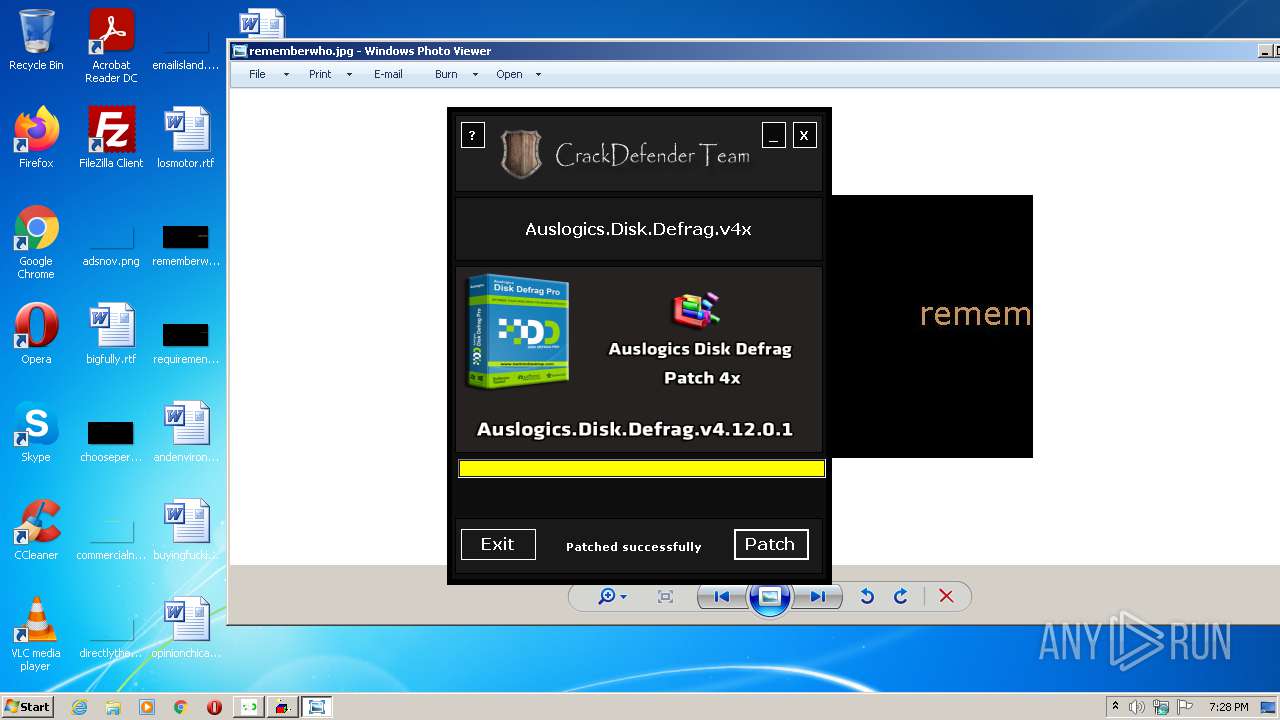
| File name: | AuslogicsDiskDefragPatch.exe |
| Full analysis: | https://app.any.run/tasks/3cfe01be-db38-4498-b494-89d1e583e479 |
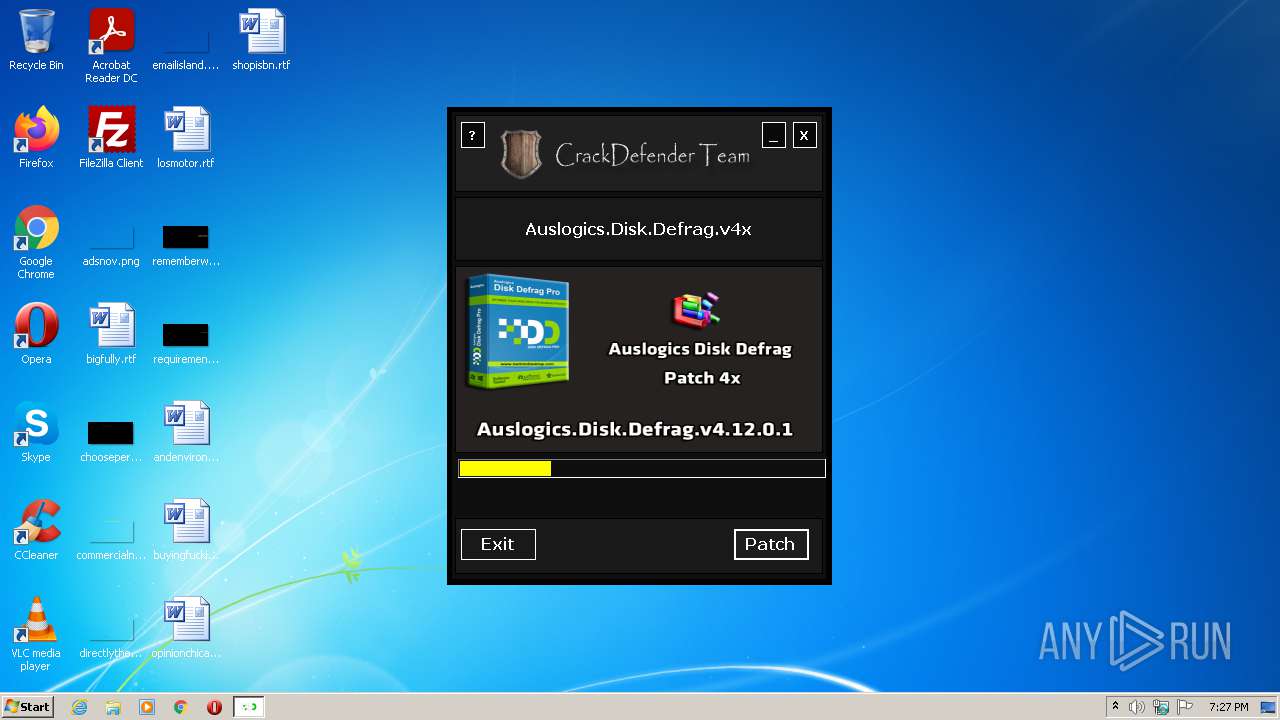
| Verdict: | Malicious activity |
| Analysis date: | June 20, 2021, 18:27:02 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 363A332D7C8D78B65C2F94E90AD6A4E0 |
| SHA1: | 8909BE858A372834DB71D8F01ED176E046A562CB |
| SHA256: | 7E821ED33676EF2B6B330327E1CC6F9688B2C5033B400ED47784942A47A473B9 |
| SSDEEP: | 98304:I9ZfT+z8qE/yRhsdMB9kCsVb1qOG16qv8W9NaSU9AgNHVQ4eQA:IPEEaCMB9hsDfw6qUiNabAg3RK |
MALICIOUS
Uses Task Scheduler to run other applications
- AuslogicsDiskDefragPatch.exe (PID: 1480)
Loads the Task Scheduler COM API
- schtasks.exe (PID: 2844)
- schtasks.exe (PID: 2104)
Drops executable file immediately after starts
- tmpAA80.tmp.exe (PID: 2616)
- auslogics-disk-defrag-fix-x64.exe (PID: 4068)
Application was dropped or rewritten from another process
- auslogics-disk-defrag-fix-x64.exe (PID: 4068)
- tmpAA80.tmp.exe (PID: 2616)
- tmpE1AF.tmp.exe (PID: 3316)
- auslogics-disk-defrag-fix-x64.exe (PID: 1788)
SUSPICIOUS
Checks supported languages
- AuslogicsDiskDefragPatch.exe (PID: 1480)
- Powershell.exe (PID: 2704)
- cmd.exe (PID: 2408)
- tmpAA80.tmp.exe (PID: 2616)
- cmd.exe (PID: 2688)
- auslogics-disk-defrag-fix-x64.exe (PID: 4068)
- WScript.exe (PID: 2296)
- tmpE1AF.tmp.exe (PID: 3316)
- cmd.exe (PID: 3500)
- cmd.exe (PID: 2448)
- auslogics-disk-defrag-fix-x64.exe (PID: 1788)
- WScript.exe (PID: 2556)
Creates files in the user directory
- Powershell.exe (PID: 2704)
- AuslogicsDiskDefragPatch.exe (PID: 1480)
- tmpAA80.tmp.exe (PID: 2616)
- tmpE1AF.tmp.exe (PID: 3316)
Reads the computer name
- Powershell.exe (PID: 2704)
- AuslogicsDiskDefragPatch.exe (PID: 1480)
- tmpAA80.tmp.exe (PID: 2616)
- WScript.exe (PID: 2296)
- tmpE1AF.tmp.exe (PID: 3316)
- auslogics-disk-defrag-fix-x64.exe (PID: 4068)
- auslogics-disk-defrag-fix-x64.exe (PID: 1788)
- WScript.exe (PID: 2556)
Reads the date of Windows installation
- Powershell.exe (PID: 2704)
Executes PowerShell scripts
- AuslogicsDiskDefragPatch.exe (PID: 1480)
Drops a file with a compile date too recent
- AuslogicsDiskDefragPatch.exe (PID: 1480)
Drops a file that was compiled in debug mode
- AuslogicsDiskDefragPatch.exe (PID: 1480)
- tmpAA80.tmp.exe (PID: 2616)
Executable content was dropped or overwritten
- AuslogicsDiskDefragPatch.exe (PID: 1480)
- tmpAA80.tmp.exe (PID: 2616)
- auslogics-disk-defrag-fix-x64.exe (PID: 4068)
Starts CMD.EXE for commands execution
- AuslogicsDiskDefragPatch.exe (PID: 1480)
- tmpAA80.tmp.exe (PID: 2616)
- tmpE1AF.tmp.exe (PID: 3316)
Uses TASKKILL.EXE to kill process
- cmd.exe (PID: 2688)
- cmd.exe (PID: 2408)
- cmd.exe (PID: 3500)
- cmd.exe (PID: 2448)
Starts itself from another location
- tmpAA80.tmp.exe (PID: 2616)
- tmpE1AF.tmp.exe (PID: 3316)
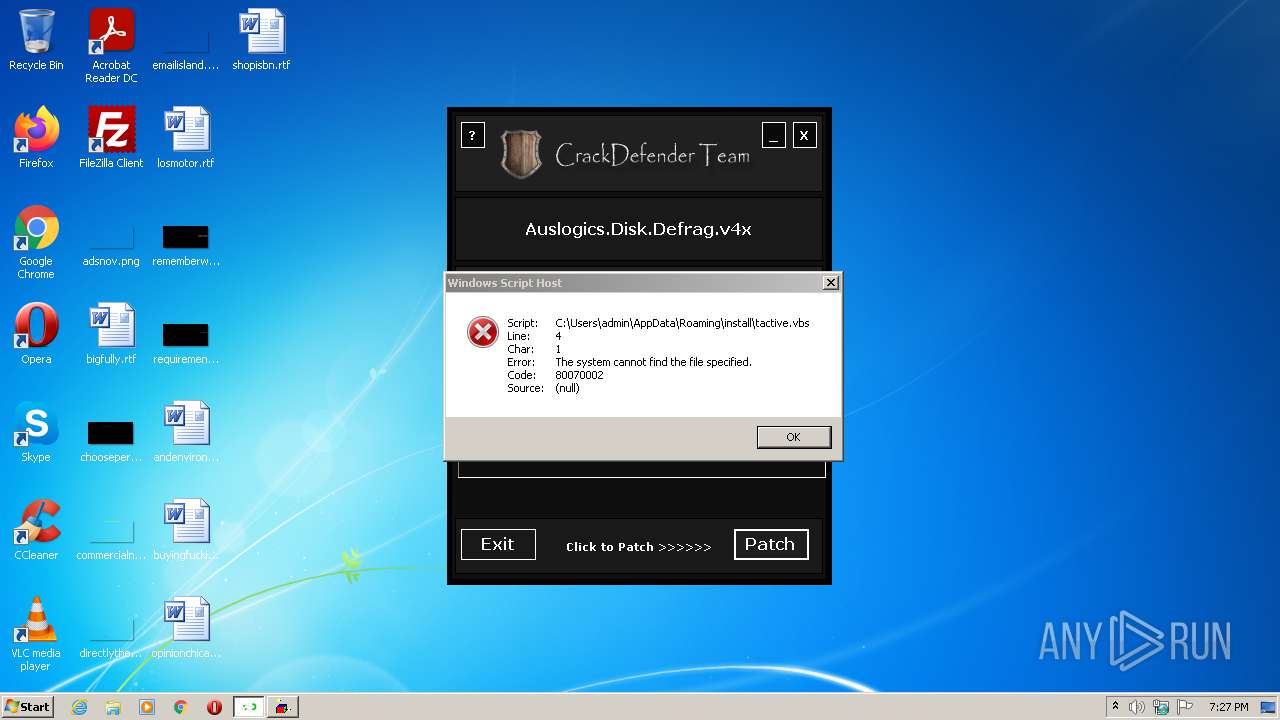
Executes scripts
- tmpAA80.tmp.exe (PID: 2616)
- tmpE1AF.tmp.exe (PID: 3316)
Creates a directory in Program Files
- auslogics-disk-defrag-fix-x64.exe (PID: 4068)
Creates files in the program directory
- auslogics-disk-defrag-fix-x64.exe (PID: 4068)
- auslogics-disk-defrag-fix-x64.exe (PID: 1788)
Executed via COM
- DllHost.exe (PID: 2968)
INFO
Checks supported languages
- schtasks.exe (PID: 2844)
- schtasks.exe (PID: 2104)
- taskkill.exe (PID: 1844)
- taskkill.exe (PID: 2452)
- taskkill.exe (PID: 3572)
- taskkill.exe (PID: 1840)
- DllHost.exe (PID: 2968)
Reads the computer name
- schtasks.exe (PID: 2844)
- schtasks.exe (PID: 2104)
- taskkill.exe (PID: 1844)
- taskkill.exe (PID: 2452)
- taskkill.exe (PID: 3572)
- taskkill.exe (PID: 1840)
- DllHost.exe (PID: 2968)
Checks Windows Trust Settings
- WScript.exe (PID: 2296)
- WScript.exe (PID: 2556)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (42.2) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (37.3) |
| .dll | | | Win32 Dynamic Link Library (generic) (8.8) |
| .exe | | | Win32 Executable (generic) (6) |
| .exe | | | Generic Win/DOS Executable (2.7) |
EXIF
EXE
| AssemblyVersion: | 1.0.0.0 |
|---|---|
| ProductVersion: | 1.0.0.0 |
| ProductName: | AuslogicsDiskDefragPatch |
| OriginalFileName: | AuslogicsDiskDefragPatch.exe |
| LegalTrademarks: | - |
| LegalCopyright: | Copyright © 2021 |
| InternalName: | AuslogicsDiskDefragPatch.exe |
| FileVersion: | 1.0.0.0 |
| FileDescription: | AuslogicsDiskDefragPatch |
| CompanyName: | - |
| Comments: | - |
| CharacterSet: | Unicode |
| LanguageCode: | Neutral |
| FileSubtype: | - |
| ObjectFileType: | Executable application |
| FileOS: | Win32 |
| FileFlags: | (none) |
| FileFlagsMask: | 0x003f |
| ProductVersionNumber: | 1.0.0.0 |
| FileVersionNumber: | 1.0.0.0 |
| Subsystem: | Windows GUI |
| SubsystemVersion: | 5 |
| ImageVersion: | - |
| OSVersion: | 5 |
| EntryPoint: | 0xccef |
| UninitializedDataSize: | - |
| InitializedDataSize: | 4729344 |
| CodeSize: | 104448 |
| LinkerVersion: | 9 |
| PEType: | PE32 |
| TimeStamp: | 2021:06:18 02:02:40+02:00 |
| MachineType: | Intel 386 or later, and compatibles |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 18-Jun-2021 00:02:40 |
| Debug artifacts: | |
| Comments: | - |
| CompanyName: | - |
| FileDescription: | AuslogicsDiskDefragPatch |
| FileVersion: | 1.0.0.0 |
| InternalName: | AuslogicsDiskDefragPatch.exe |
| LegalCopyright: | Copyright © 2021 |
| LegalTrademarks: | - |
| OriginalFilename: | AuslogicsDiskDefragPatch.exe |
| ProductName: | AuslogicsDiskDefragPatch |
| ProductVersion: | 1.0.0.0 |
| Assembly Version: | 1.0.0.0 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x000000D0 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 4 |
| Time date stamp: | 18-Jun-2021 00:02:40 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x000196D8 | 0x00019800 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.74606 |
.rdata | 0x0001B000 | 0x00006DF2 | 0x00006E00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 6.44313 |
.data | 0x00022000 | 0x000030C0 | 0x00001600 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 3.26244 |
.rsrc | 0x00026000 | 0x0047A474 | 0x0047A600 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 7.94529 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.0055 | 3174 | Latin 1 / Western European | UNKNOWN | RT_MANIFEST |
2 | 2.88807 | 2440 | Latin 1 / Western European | UNKNOWN | RT_ICON |
3 | 2.76015 | 4264 | Latin 1 / Western European | UNKNOWN | RT_ICON |
4 | 2.77014 | 9640 | Latin 1 / Western European | UNKNOWN | RT_ICON |
5 | 2.61622 | 165640 | Latin 1 / Western European | UNKNOWN | RT_ICON |
32512 | 2.86004 | 76 | Latin 1 / Western European | UNKNOWN | RT_GROUP_ICON |
__ | 7.99995 | 4507205 | Latin 1 / Western European | UNKNOWN | RT_RCDATA |
~ | 4.9375 | 32 | Latin 1 / Western European | UNKNOWN | RT_RCDATA |
Imports
KERNEL32.dll |
OLEAUT32.dll |
mscoree.dll |
ole32.dll |
Total processes
63
Monitored processes
20
Malicious processes
4
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1480 | "C:\Users\admin\AppData\Local\Temp\AuslogicsDiskDefragPatch.exe" | C:\Users\admin\AppData\Local\Temp\AuslogicsDiskDefragPatch.exe | Explorer.EXE | ||||||||||||
User: admin Integrity Level: HIGH Description: AuslogicsDiskDefragPatch Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
| 1788 | "C:\Users\admin\AppData\Roaming\install\auslogics-disk-defrag-fix-x64.exe" | C:\Users\admin\AppData\Roaming\install\auslogics-disk-defrag-fix-x64.exe | — | tmpE1AF.tmp.exe | |||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 1840 | taskkill /F /IM "DiskDefragPro.exe" | C:\Windows\system32\taskkill.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Terminates Processes Exit code: 128 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1844 | taskkill /F /IM "Hetman Partition Recovery.exe" | C:\Windows\system32\taskkill.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Terminates Processes Exit code: 128 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2104 | "C:\Windows\System32\schtasks.exe" /create /sc minute /mo 7 /f /tn SecurityHealthService /tr "C:\Users\admin\AppData\Roaming\windows\microsoft.foundation.diagnostics.exe" | C:\Windows\System32\schtasks.exe | — | AuslogicsDiskDefragPatch.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Manages scheduled tasks Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2296 | "C:\Windows\System32\WScript.exe" "C:\Users\admin\AppData\Roaming\install\tactive.vbs" | C:\Windows\System32\WScript.exe | — | tmpAA80.tmp.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft � Windows Based Script Host Exit code: 0 Version: 5.8.7600.16385 Modules
| |||||||||||||||
| 2408 | C:\Windows\system32\cmd.exe /c ""C:\Users\admin\AppData\Local\Temp\tmpA957.tmp.bat" " | C:\Windows\system32\cmd.exe | — | AuslogicsDiskDefragPatch.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 128 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2448 | C:\Windows\system32\cmd.exe /c ""C:\Users\admin\AppData\Roaming\install\active.bat" " | C:\Windows\system32\cmd.exe | — | tmpE1AF.tmp.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 128 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2452 | taskkill /F /IM "DiskDefragPro.exe" | C:\Windows\system32\taskkill.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Terminates Processes Exit code: 128 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2556 | "C:\Windows\System32\WScript.exe" "C:\Users\admin\AppData\Roaming\install\tactive.vbs" | C:\Windows\System32\WScript.exe | — | tmpE1AF.tmp.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft � Windows Based Script Host Exit code: 0 Version: 5.8.7600.16385 Modules
| |||||||||||||||
Total events
4 114
Read events
4 035
Write events
79
Delete events
0
Modification events
| (PID) Process: | (2704) Powershell.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\16B\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (1480) AuslogicsDiskDefragPatch.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (1480) AuslogicsDiskDefragPatch.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (1480) AuslogicsDiskDefragPatch.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (1480) AuslogicsDiskDefragPatch.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
| (PID) Process: | (2616) tmpAA80.tmp.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (2616) tmpAA80.tmp.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (2616) tmpAA80.tmp.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (2616) tmpAA80.tmp.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
| (PID) Process: | (3316) tmpE1AF.tmp.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
Executable files
6
Suspicious files
3
Text files
6
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2704 | Powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms~RF1997b2.TMP | binary | |
MD5:— | SHA256:— | |||
| 2616 | tmpAA80.tmp.exe | C:\Users\admin\AppData\Roaming\install\active.bat | text | |
MD5:— | SHA256:— | |||
| 2704 | Powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms | binary | |
MD5:— | SHA256:— | |||
| 1480 | AuslogicsDiskDefragPatch.exe | C:\Users\admin\AppData\Roaming\windows\SecurityCryptography.exe | executable | |
MD5:— | SHA256:— | |||
| 1480 | AuslogicsDiskDefragPatch.exe | C:\Users\admin\AppData\Local\Temp\tmpA957.tmp.bat | text | |
MD5:— | SHA256:— | |||
| 1480 | AuslogicsDiskDefragPatch.exe | C:\Users\admin\AppData\Local\Temp\tmpAA80.tmp.exe | executable | |
MD5:— | SHA256:— | |||
| 2704 | Powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\TH996K7H8EQEPBD0G1YA.temp | binary | |
MD5:— | SHA256:— | |||
| 1480 | AuslogicsDiskDefragPatch.exe | C:\Users\admin\AppData\Local\Temp\tmp9706.tmp.ps1 | text | |
MD5:B1481C7CEFA4A7063D453F726E3B3658 | SHA256:C42EB405A28D493899EBD7574011B45F121AB0DA8D6CA96B379F9F3199B0B566 | |||
| 1480 | AuslogicsDiskDefragPatch.exe | C:\Users\admin\AppData\Roaming\windows\microsoft.foundation.diagnostics.exe | executable | |
MD5:F0D93E6CF54CA72F3478F4AFC2403163 | SHA256:26E84BAC6F97B4009CC6737C62B42A5BBEE4DD0B014D3E771A8F89366F6AE0FE | |||
| 1480 | AuslogicsDiskDefragPatch.exe | C:\Users\admin\AppData\Local\Temp\tmpE1AF.tmp.exe | executable | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report