| File name: | PanDownload.exe |
| Full analysis: | https://app.any.run/tasks/8d3f7938-8799-495a-88b2-7ba0b58a2d23 |
| Verdict: | Malicious activity |
| Analysis date: | September 19, 2018, 08:28:37 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 9847D7586FB4680565763CE9A2DDECFC |
| SHA1: | FD1438616815CCD3F3296F5214E89327F807516D |
| SHA256: | 7E808E9929A48CEDED606FB00A39D60DA9C340AEF739A094C32568D35D2ED1D1 |
| SSDEEP: | 98304:l3WZhAUCQVDVx7l3NmaVSQJ/z0GoF8Cwkransxn1lyW9IwkuAG/QBxcCL:l30hNb7ldma/50GoRwkNn1vkG/QncC |
MALICIOUS
Application was dropped or rewritten from another process
- aria2c.exe (PID: 2008)
SUSPICIOUS
Executable content was dropped or overwritten
- PanDownload.exe (PID: 3432)
INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable (generic) (52.9) |
|---|---|---|
| .exe | | | Generic Win/DOS Executable (23.5) |
| .exe | | | DOS Executable Generic (23.5) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2018:03:08 10:28:16+01:00 |
| PEType: | PE32 |
| LinkerVersion: | 14 |
| CodeSize: | 1620480 |
| InitializedDataSize: | 6715904 |
| UninitializedDataSize: | - |
| EntryPoint: | 0xc90000 |
| OSVersion: | 5.1 |
| ImageVersion: | - |
| SubsystemVersion: | 5.1 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 1.5.4.0 |
| ProductVersionNumber: | 1.5.4.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Windows NT 32-bit |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Chinese (Simplified) |
| CharacterSet: | Unicode |
| CompanyName: | Kiryuu |
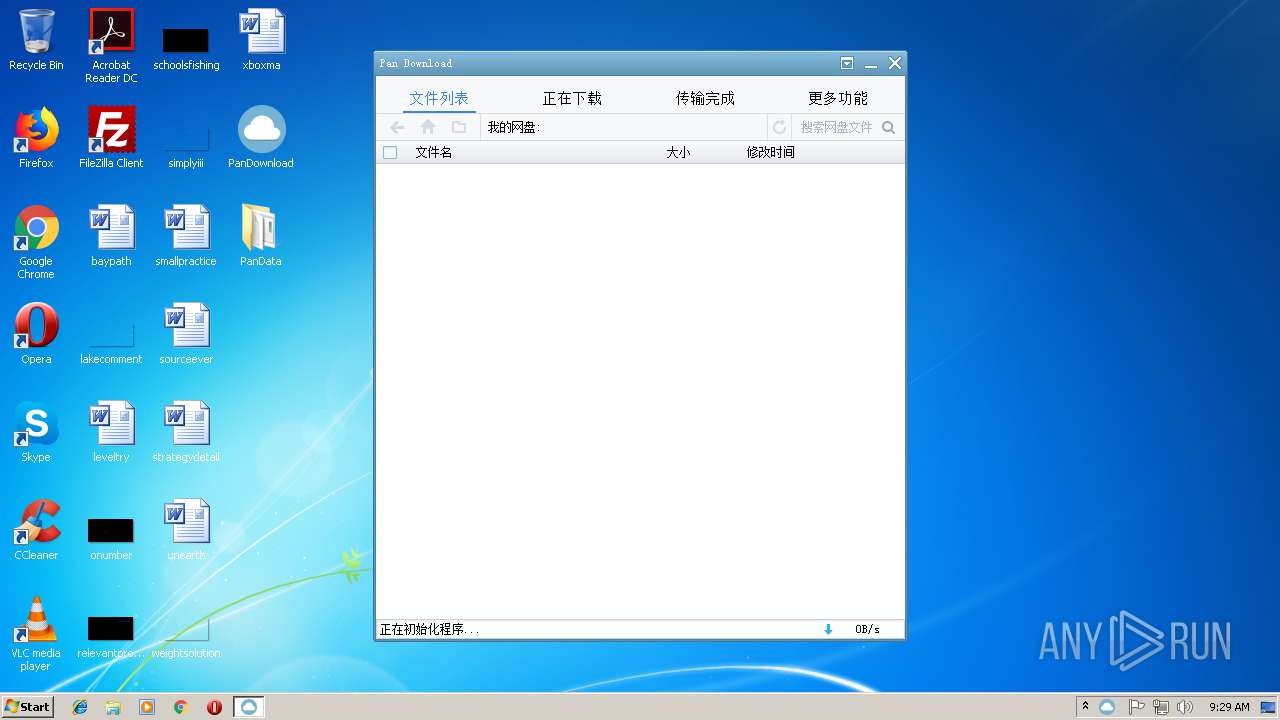
| FileDescription: | 网盘下载器 |
| FileVersion: | 1.5.4.0 |
| InternalName: | PanDownload.exe |
| LegalCopyright: | Copyright (C) 2017 |
| OriginalFileName: | PanDownload.exe |
| ProductName: | PanDownload |
| ProductVersion: | 1.5.4.0 |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 08-Mar-2018 09:28:16 |
| Detected languages: |
|
| CompanyName: | Kiryuu |
| FileDescription: | 网盘下载器 |
| FileVersion: | 1.5.4.0 |
| InternalName: | PanDownload.exe |
| LegalCopyright: | Copyright (C) 2017 |
| OriginalFilename: | PanDownload.exe |
| ProductName: | PanDownload |
| ProductVersion: | 1.5.4.0 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000130 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 6 |
| Time date stamp: | 08-Mar-2018 09:28:16 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
0x00001000 | 0x001F4000 | 0x000CF000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 7.95995 | |
.rsrc | 0x001F5000 | 0x005EA3F8 | 0x002C1800 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 7.99904 |
.idata | 0x007E0000 | 0x00001000 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 1.17411 |
0x007E1000 | 0x00304000 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0.260771 | |
gpfjxcfg | 0x00AE5000 | 0x001AB000 | 0x001AAC00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 7.95143 |
ssuajshl | 0x00C90000 | 0x00001000 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.15623 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.07176 | 640 | UNKNOWN | English - United States | RT_MANIFEST |
2 | 4.08465 | 1128 | UNKNOWN | Chinese - PRC | RT_ICON |
7 | 0 | 76 | UNKNOWN | Chinese - PRC | RT_STRING |
107 | 1.91924 | 20 | UNKNOWN | Chinese - PRC | RT_GROUP_ICON |
108 | 2.0815 | 20 | UNKNOWN | Chinese - PRC | RT_GROUP_ICON |
109 | 3.875 | 16 | UNKNOWN | Chinese - PRC | RT_ACCELERATOR |
129 | 7.99148 | 158250 | UNKNOWN | Chinese - PRC | ZIP |
130 | 7.99373 | 129596 | UNKNOWN | Chinese - PRC | WAVE |
131 | 7.97739 | 248768 | UNKNOWN | Chinese - PRC | WAVE |
132 | 7.98202 | 4569600 | UNKNOWN | Chinese - PRC | EXE |
Imports
comctl32.dll |
kernel32.dll |
Total processes
36
Monitored processes
2
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2008 | "C:\Users\admin\Desktop\PanData\aria2c.exe" --enable-rpc=true --rpc-allow-origin-all=true --rpc-listen-port=6801 -q --disable-ipv6=true --stop-with-process=3432 --check-certificate=false --rpc-secret=pandownload | C:\Users\admin\Desktop\PanData\aria2c.exe | — | PanDownload.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 3432 | "C:\Users\admin\Desktop\PanDownload.exe" | C:\Users\admin\Desktop\PanDownload.exe | explorer.exe | ||||||||||||
User: admin Company: Kiryuu Integrity Level: MEDIUM Description: 网盘下载器 Exit code: 0 Version: 1.5.4.0 Modules
| |||||||||||||||
Total events
40
Read events
40
Write events
0
Delete events
0
Modification events
Executable files
1
Suspicious files
0
Text files
4
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3432 | PanDownload.exe | C:\Users\admin\Desktop\PanData\aria2.conf | — | |
MD5:— | SHA256:— | |||
| 2008 | aria2c.exe | C:\Users\admin\Desktop\PanData\log\20180919092901.log | text | |
MD5:— | SHA256:— | |||
| 3432 | PanDownload.exe | C:\Users\admin\Desktop\PanData\pan.conf | text | |
MD5:— | SHA256:— | |||
| 3432 | PanDownload.exe | C:\Users\admin\Desktop\PanData\aria2c.exe | executable | |
MD5:— | SHA256:— | |||
| 3432 | PanDownload.exe | C:\Users\admin\Desktop\PanData\directui license.txt | text | |
MD5:AB54B14548A4CC76DD7C27414D971111 | SHA256:6033476BE3D1D41166B65984E2BE94C87AC98DCE55BFEC887E932B696E859295 | |||
| 3432 | PanDownload.exe | C:\Users\admin\Desktop\PanData\duilib license.txt | text | |
MD5:8E73AF2D5D89151133E4B80BF76FF570 | SHA256:58923C4A2D4876DEC670637E12D57554EDE9ADD488D45F55BAE3ED2224AC7462 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
7
TCP/UDP connections
5
DNS requests
4
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3432 | PanDownload.exe | GET | — | 104.27.184.233:80 | http://pandownload.com/api/update?version=1.5.4&plus=1&t=1537345742 | US | — | — | whitelisted |
3432 | PanDownload.exe | GET | — | 106.15.15.135:80 | http://ip.taobao.com/service/getIpInfo.php?ip=myip | CN | — | — | malicious |
3432 | PanDownload.exe | GET | 200 | 104.27.185.233:80 | http://s1.pandownload.com/api/update?version=1.5.4&plus=1&t=1537345742 | US | — | — | shared |
3432 | PanDownload.exe | GET | 200 | 66.112.211.226:80 | http://pandownload.club/api/update?version=1.5.4&plus=1&t=1537345742 | US | — | — | suspicious |
3432 | PanDownload.exe | GET | 200 | 104.27.184.233:80 | http://pandownload.com/api/update?version=1.5.4&plus=1&t=1537345742 | US | — | — | whitelisted |
3432 | PanDownload.exe | GET | 200 | 104.27.185.233:80 | http://s1.pandownload.com/api/update?version=1.5.4&plus=1&t=1537345742 | US | — | — | shared |
3432 | PanDownload.exe | GET | 200 | 66.112.211.226:80 | http://pandownload.club/api/update?version=1.5.4&plus=1&t=1537345742 | US | — | — | suspicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3432 | PanDownload.exe | 104.27.184.233:80 | pandownload.com | Cloudflare Inc | US | shared |
3432 | PanDownload.exe | 106.15.15.135:80 | ip.taobao.com | Hangzhou Alibaba Advertising Co.,Ltd. | CN | malicious |
3432 | PanDownload.exe | 104.27.185.233:80 | pandownload.com | Cloudflare Inc | US | shared |
3432 | PanDownload.exe | 66.112.211.226:80 | pandownload.club | IT7 Networks Inc | US | suspicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
pandownload.com |
| whitelisted |
ip.taobao.com |
| unknown |
s1.pandownload.com |
| unknown |
pandownload.club |
| suspicious |
Threats
1 ETPRO signatures available at the full report
Process | Message |
|---|---|
PanDownload.exe |
%s------------------------------------------------
--- Themida Professional ---
--- (c)2012 Oreans Technologies ---
------------------------------------------------
|