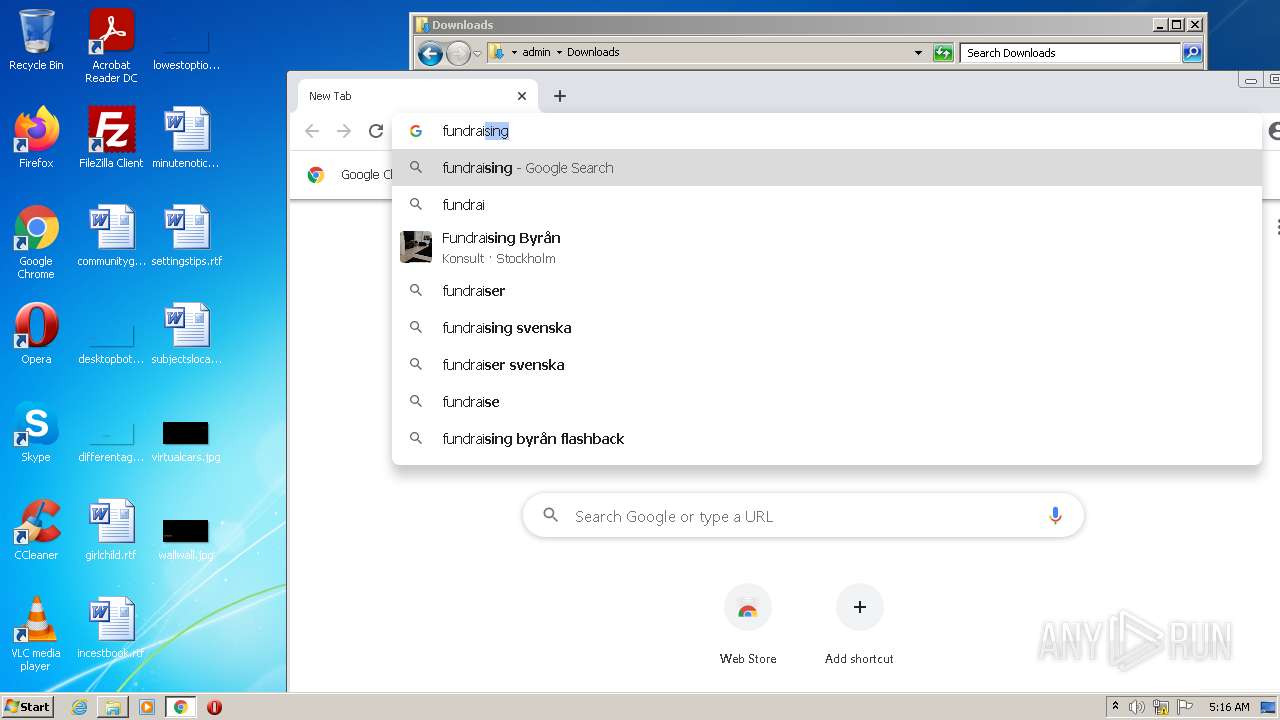
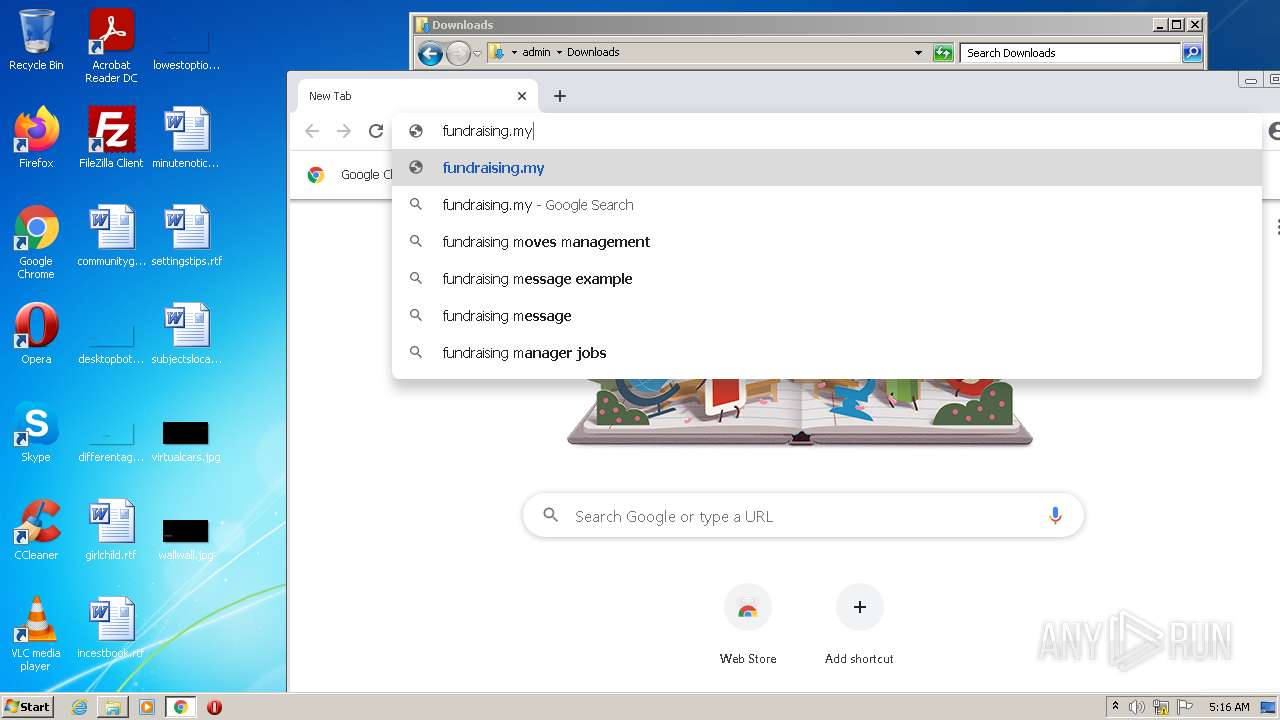
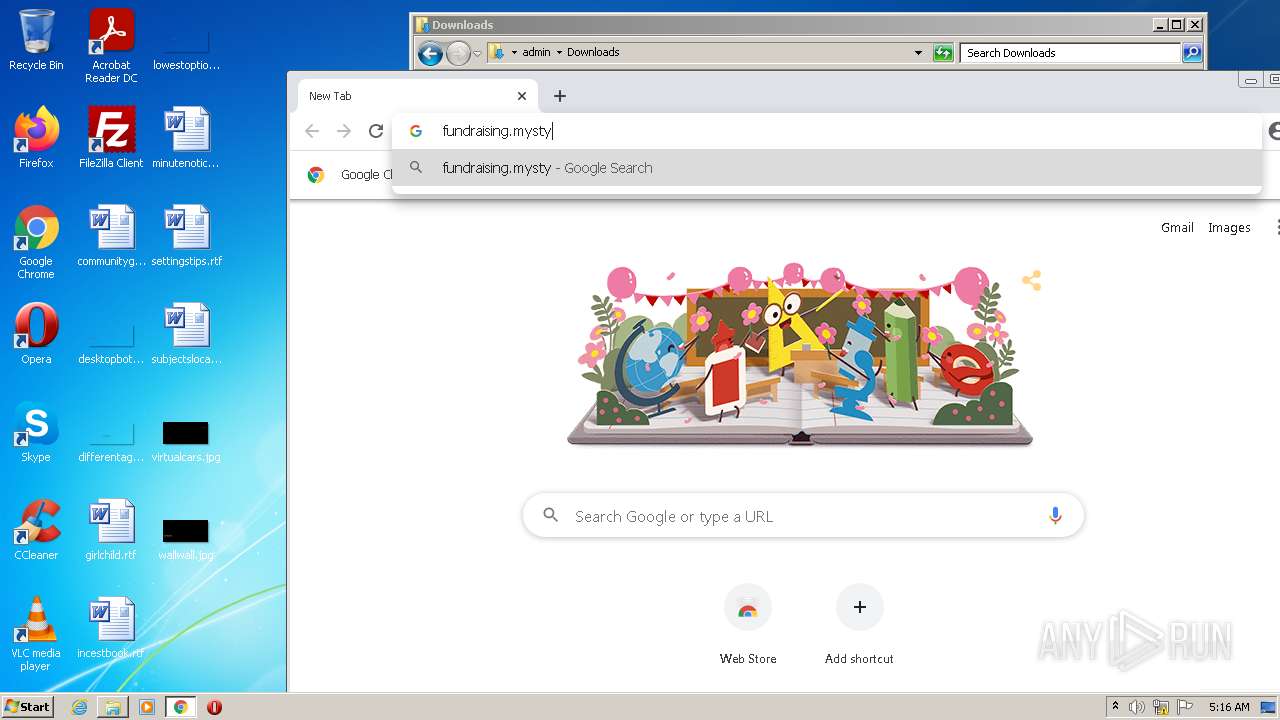
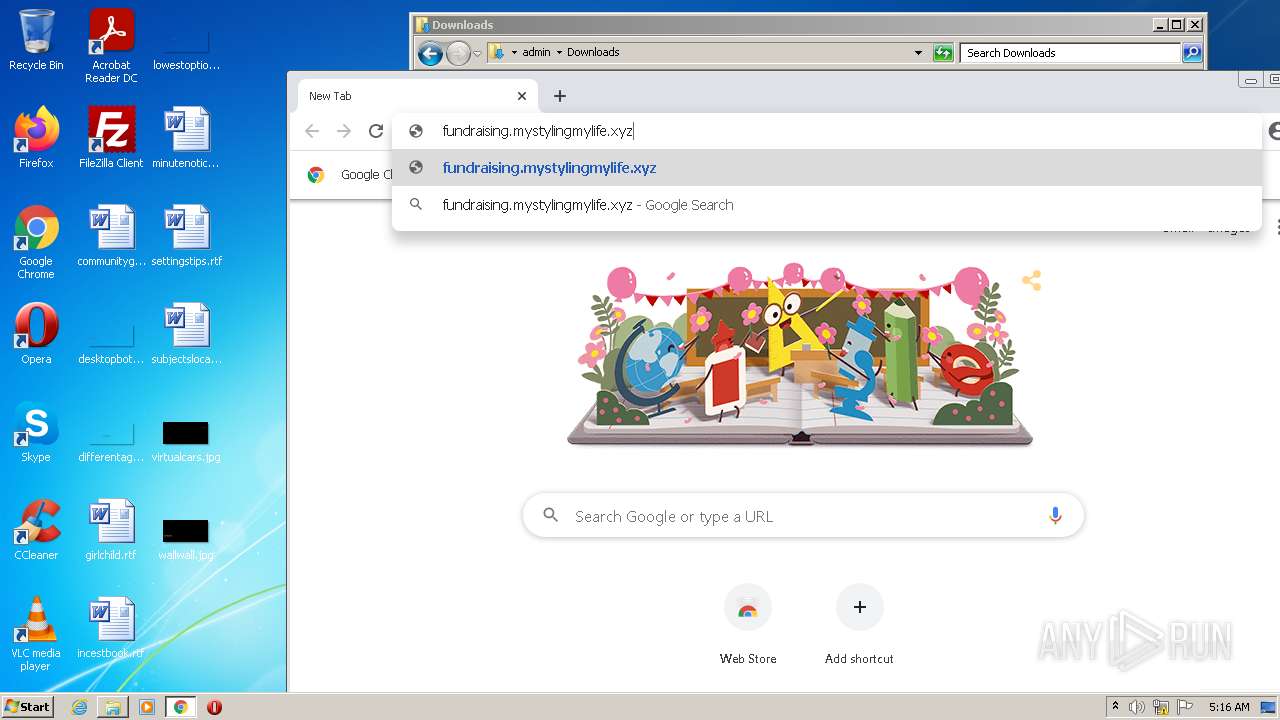
| URL: | https://fundraising.mystylingmylife.xyz/report |
| Full analysis: | https://app.any.run/tasks/fefbc256-eef3-495c-8a4b-f9a2c1c5fe04 |
| Verdict: | Malicious activity |
| Analysis date: | October 05, 2022, 04:13:46 |
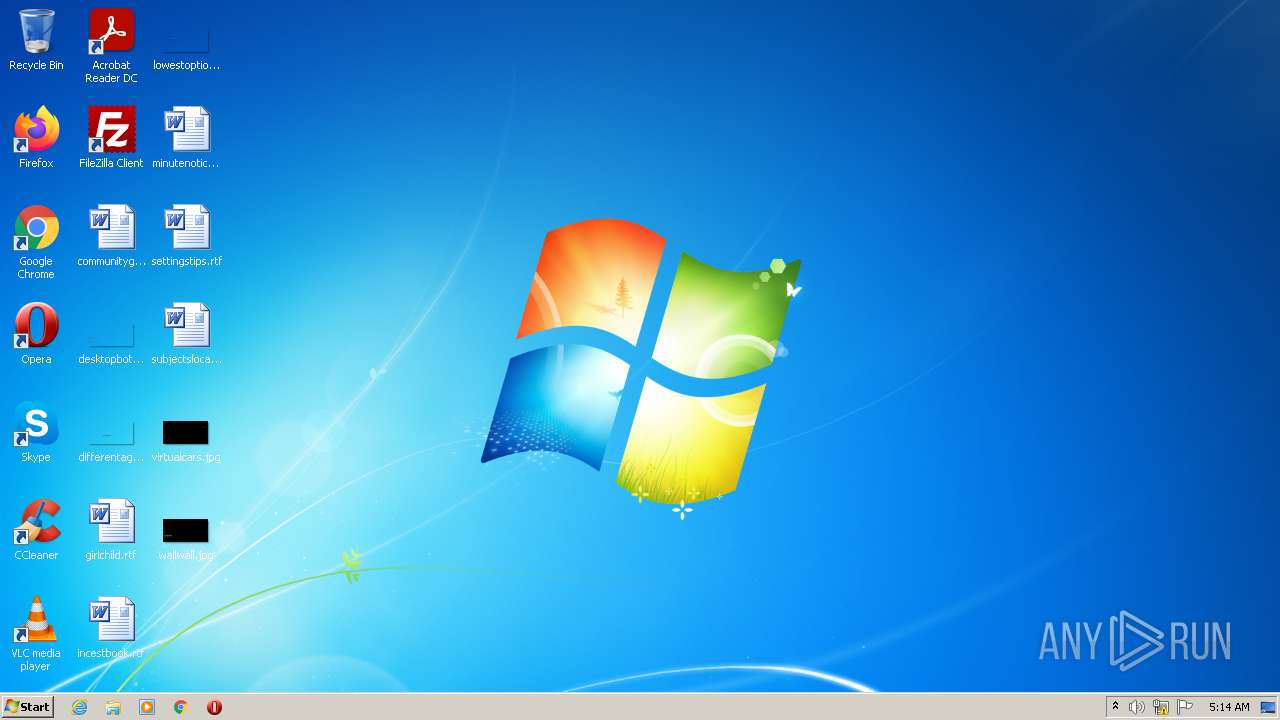
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 023540EDEB75594CAACE85162E0738CF |
| SHA1: | 2E2920E149B1A78AAA67675DDCCE4117F4D0A102 |
| SHA256: | 7E65968A0F5131D52BA0C0FED14E608CAB984C050065B2708C8AA120631B63B7 |
| SSDEEP: | 3:N8cXEMWK1v2IcCcLe0AVMR:2cUMove5VMR |
MALICIOUS
No malicious indicators.SUSPICIOUS
Reads Microsoft Outlook installation path
- iexplore.exe (PID: 1252)
Reads the computer name
- WScript.exe (PID: 3620)
Executes scripts
- iexplore.exe (PID: 3160)
Checks supported languages
- WScript.exe (PID: 3620)
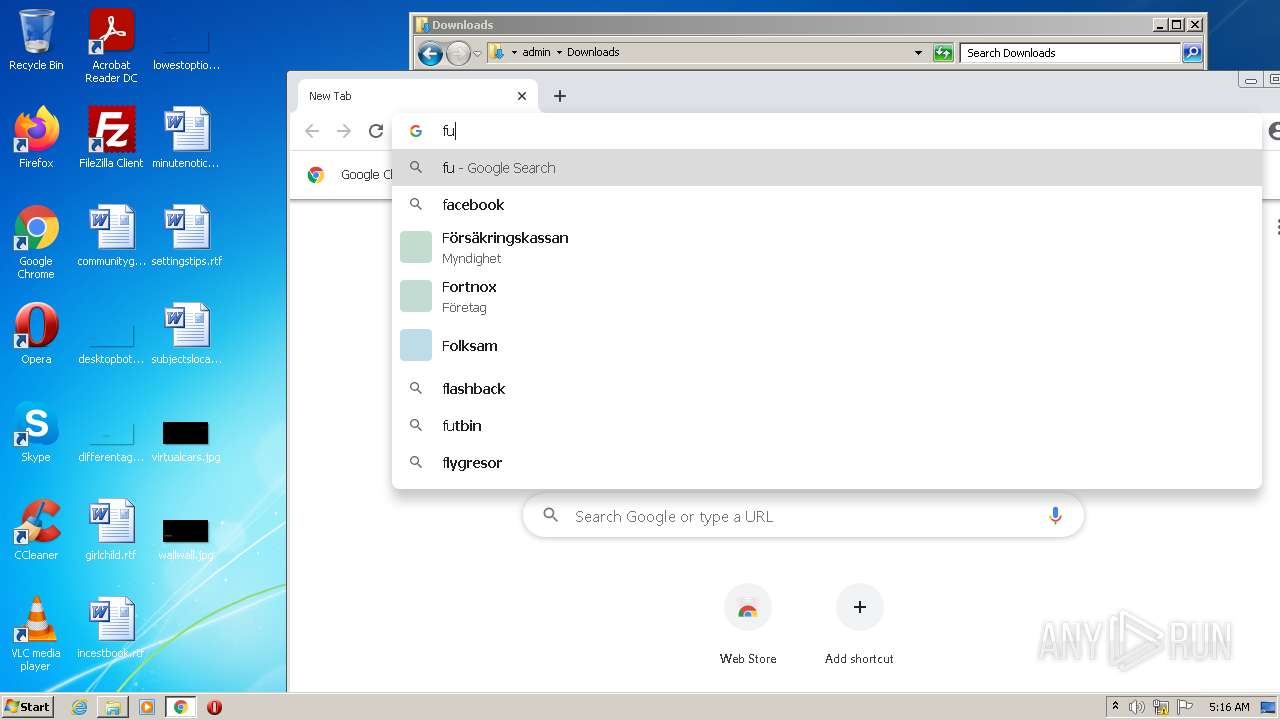
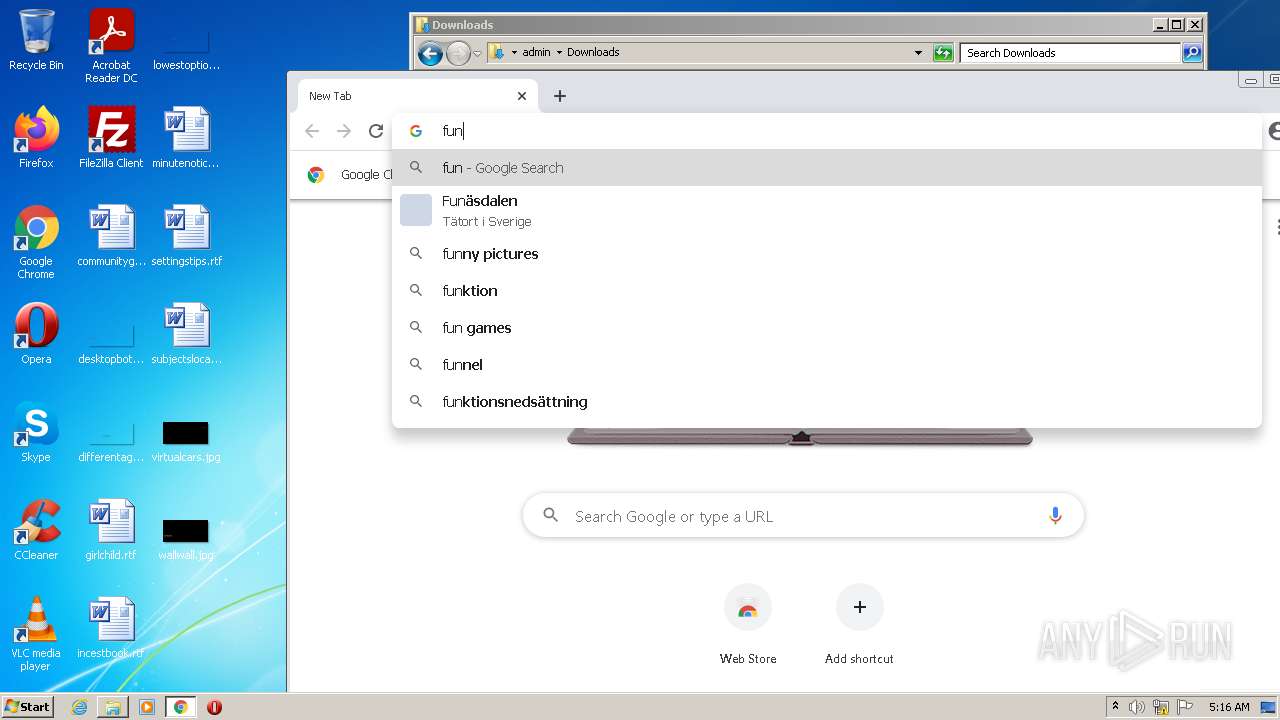
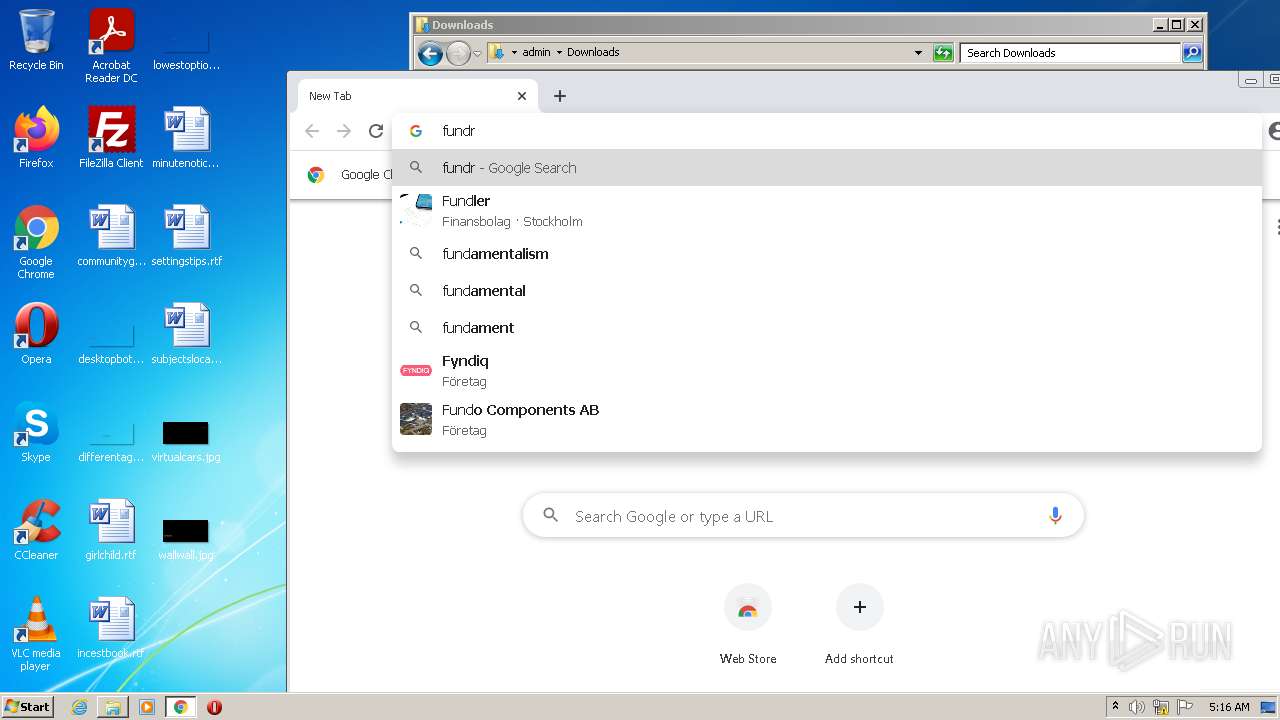
Modifies files in Chrome extension folder
- chrome.exe (PID: 3832)
INFO
Reads the computer name
- iexplore.exe (PID: 3160)
- iexplore.exe (PID: 1252)
- chrome.exe (PID: 3832)
- chrome.exe (PID: 3308)
- chrome.exe (PID: 2428)
- chrome.exe (PID: 2276)
- chrome.exe (PID: 3460)
- chrome.exe (PID: 3860)
- chrome.exe (PID: 1856)
- chrome.exe (PID: 3268)
- chrome.exe (PID: 2852)
Checks supported languages
- iexplore.exe (PID: 3160)
- iexplore.exe (PID: 1252)
- chrome.exe (PID: 3832)
- chrome.exe (PID: 2128)
- chrome.exe (PID: 2828)
- chrome.exe (PID: 3308)
- chrome.exe (PID: 2428)
- chrome.exe (PID: 868)
- chrome.exe (PID: 1972)
- chrome.exe (PID: 2276)
- chrome.exe (PID: 2448)
- chrome.exe (PID: 2508)
- chrome.exe (PID: 3180)
- chrome.exe (PID: 3616)
- chrome.exe (PID: 3460)
- chrome.exe (PID: 2304)
- chrome.exe (PID: 976)
- chrome.exe (PID: 3684)
- chrome.exe (PID: 2800)
- chrome.exe (PID: 328)
- chrome.exe (PID: 660)
- chrome.exe (PID: 2592)
- chrome.exe (PID: 3360)
- chrome.exe (PID: 3948)
- chrome.exe (PID: 1024)
- chrome.exe (PID: 280)
- chrome.exe (PID: 2208)
- chrome.exe (PID: 3956)
- chrome.exe (PID: 3884)
- chrome.exe (PID: 3996)
- chrome.exe (PID: 1996)
- chrome.exe (PID: 3268)
- chrome.exe (PID: 3860)
- chrome.exe (PID: 3048)
- chrome.exe (PID: 888)
- chrome.exe (PID: 1856)
- chrome.exe (PID: 3268)
- chrome.exe (PID: 3136)
- chrome.exe (PID: 3896)
- chrome.exe (PID: 1900)
- chrome.exe (PID: 3976)
- chrome.exe (PID: 364)
- chrome.exe (PID: 3740)
- chrome.exe (PID: 3176)
- chrome.exe (PID: 2852)
- chrome.exe (PID: 3260)
- chrome.exe (PID: 2536)
- chrome.exe (PID: 2704)
- chrome.exe (PID: 3400)
- chrome.exe (PID: 3252)
- chrome.exe (PID: 564)
- chrome.exe (PID: 3360)
- chrome.exe (PID: 3136)
Application launched itself
- iexplore.exe (PID: 3160)
- chrome.exe (PID: 3832)
Reads settings of System Certificates
- iexplore.exe (PID: 3160)
- iexplore.exe (PID: 1252)
- chrome.exe (PID: 2428)
Modifies the phishing filter of IE
- iexplore.exe (PID: 3160)
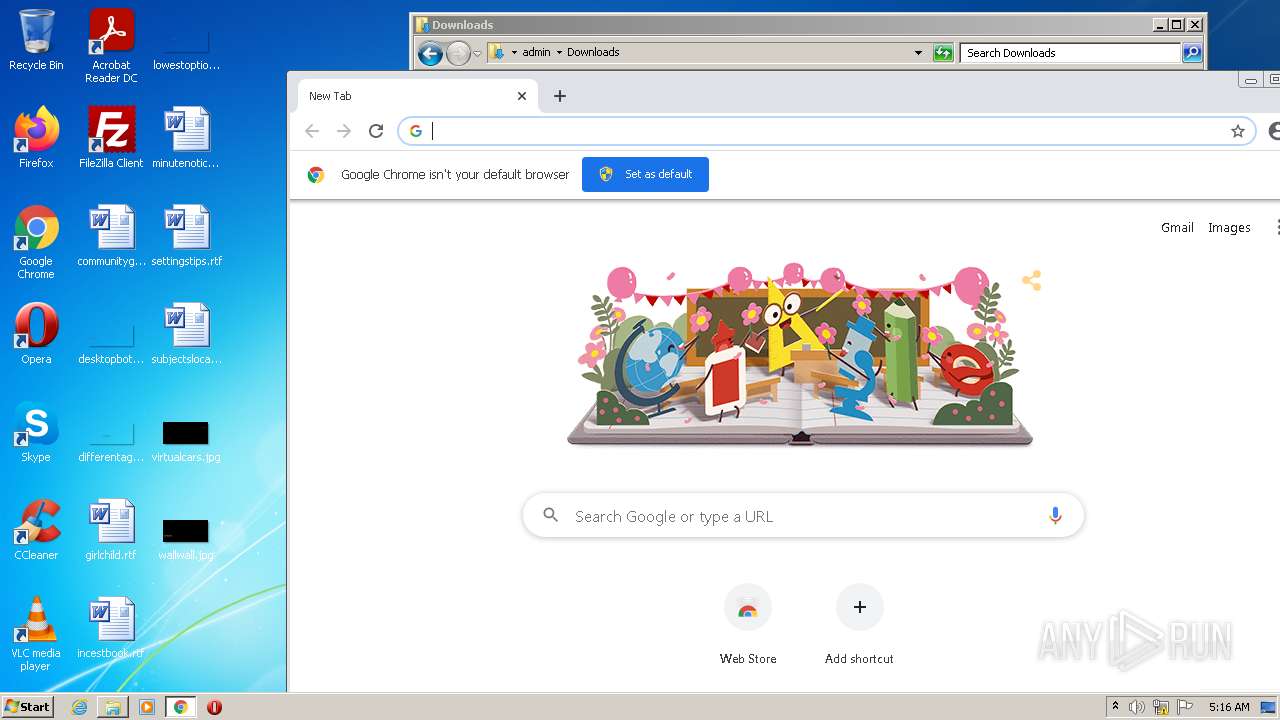
Manual execution by user
- chrome.exe (PID: 3832)
Reads the date of Windows installation
- iexplore.exe (PID: 3160)
- chrome.exe (PID: 1856)
Changes internet zones settings
- iexplore.exe (PID: 3160)
Checks Windows Trust Settings
- iexplore.exe (PID: 1252)
- iexplore.exe (PID: 3160)
- WScript.exe (PID: 3620)
Reads the hosts file
- chrome.exe (PID: 3832)
- chrome.exe (PID: 2428)
Creates files in the user directory
- chrome.exe (PID: 3832)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
91
Monitored processes
54
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 280 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --field-trial-handle=1040,12047009621778547704,1527542264504957726,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --mojo-platform-channel-handle=3400 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 328 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --field-trial-handle=1040,12047009621778547704,1527542264504957726,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --mojo-platform-channel-handle=2340 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 364 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --field-trial-handle=1040,12047009621778547704,1527542264504957726,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --mojo-platform-channel-handle=996 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 564 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --field-trial-handle=1040,12047009621778547704,1527542264504957726,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --mojo-platform-channel-handle=3724 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 660 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --field-trial-handle=1040,12047009621778547704,1527542264504957726,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --mojo-platform-channel-handle=2372 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 868 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1040,12047009621778547704,1527542264504957726,131072 --enable-features=PasswordImport --lang=en-US --extension-process --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=4 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2336 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 888 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --field-trial-handle=1040,12047009621778547704,1527542264504957726,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --mojo-platform-channel-handle=536 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 976 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --field-trial-handle=1040,12047009621778547704,1527542264504957726,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --mojo-platform-channel-handle=2380 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1024 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --field-trial-handle=1040,12047009621778547704,1527542264504957726,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --mojo-platform-channel-handle=3012 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1252 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:3160 CREDAT:267521 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
Total events
27 355
Read events
27 116
Write events
230
Delete events
9
Modification events
| (PID) Process: | (3160) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPDaysSinceLastAutoMigration |
Value: 1 | |||
| (PID) Process: | (3160) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchLowDateTime |
Value: | |||
| (PID) Process: | (3160) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchHighDateTime |
Value: 30988400 | |||
| (PID) Process: | (3160) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateLowDateTime |
Value: | |||
| (PID) Process: | (3160) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateHighDateTime |
Value: 30988400 | |||
| (PID) Process: | (3160) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (3160) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (3160) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (3160) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (3160) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
Executable files
1
Suspicious files
181
Text files
192
Unknown types
14
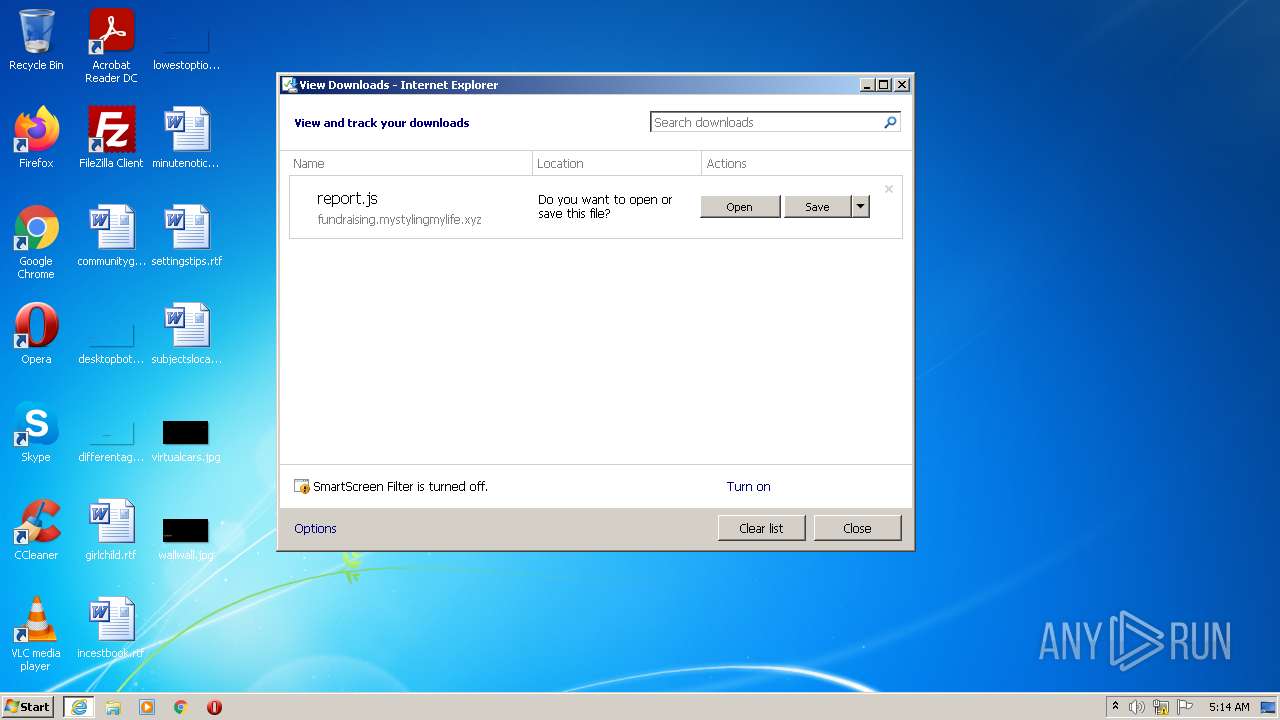
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3160 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\78RFYB7Z\report.js | — | |
MD5:— | SHA256:— | |||
| 1252 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\57C8EDB95DF3F0AD4EE2DC2B8CFD4157 | binary | |
MD5:— | SHA256:— | |||
| 3160 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\6BADA8974A10C4BD62CC921D13E43B18_1DC6D7385EA816C957BA2B715AC5C442 | binary | |
MD5:— | SHA256:— | |||
| 1252 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\B2FAF7692FD9FFBD64EDE317E42334BA_D7393C8F62BDE4D4CB606228BC7A711E | der | |
MD5:— | SHA256:— | |||
| 1252 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\0B2A314CA49BC097ACBD717E4540C486 | binary | |
MD5:— | SHA256:— | |||
| 3160 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\6BADA8974A10C4BD62CC921D13E43B18_1DC6D7385EA816C957BA2B715AC5C442 | der | |
MD5:— | SHA256:— | |||
| 1252 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\07CEF2F654E3ED6050FFC9B6EB844250_34D61B4A2A4AE0D3DDAB879224BCA77B | binary | |
MD5:— | SHA256:— | |||
| 3832 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\BrowserMetrics\BrowserMetrics-633D04EF-EF8.pma | — | |
MD5:— | SHA256:— | |||
| 1252 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\0B2A314CA49BC097ACBD717E4540C486 | der | |
MD5:— | SHA256:— | |||
| 1252 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\07CEF2F654E3ED6050FFC9B6EB844250_34D61B4A2A4AE0D3DDAB879224BCA77B | der | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
38
TCP/UDP connections
44
DNS requests
32
Threats
7
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
924 | svchost.exe | HEAD | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvODJiQUFYYVJaZ0k5di1hUFlXS1prX2xDZw/1.0.0.13_llkgjffcdpffmhiakmfcdcblohccpfmo.crx | US | — | — | whitelisted |
1252 | iexplore.exe | GET | 200 | 172.64.155.188:80 | http://ocsp.usertrust.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTNMNJMNDqCqx8FcBWK16EHdimS6QQUU3m%2FWqorSs9UgOHYm8Cd8rIDZssCEGxVq9vQB5LHnQcM2BGe1r8%3D | US | der | 2.18 Kb | whitelisted |
1252 | iexplore.exe | GET | 200 | 104.18.32.68:80 | http://ocsp.comodoca.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBRTtU9uFqgVGHhJwXZyWCNXmVR5ngQUoBEKIz6W8Qfs4q8p74Klf9AwpLQCEDlyRDr5IrdR19NsEN0xNZU%3D | US | der | 1.42 Kb | whitelisted |
1252 | iexplore.exe | GET | 200 | 104.18.32.68:80 | http://zerossl.ocsp.sectigo.com/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBQILj%2F5BYz%2BinwYvRPv3x0WYHB6awQUyNl4aKLZGWjVPXLeXwo%2B3LWGhqYCEQDZ8YTGysdHnEaBbjF9lozw | US | der | 728 b | whitelisted |
3160 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | US | der | 471 b | whitelisted |
924 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/kwwzs7t4dq4pu3zh4drhohnhia_2875/jflookgnkcckhobaglndicnbbgbonegd_2875_all_acr4yh57ursmal3v5c7ephahtyxq.crx3 | US | binary | 10.2 Kb | whitelisted |
924 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/kwwzs7t4dq4pu3zh4drhohnhia_2875/jflookgnkcckhobaglndicnbbgbonegd_2875_all_acr4yh57ursmal3v5c7ephahtyxq.crx3 | US | binary | 5.63 Kb | whitelisted |
924 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/kwwzs7t4dq4pu3zh4drhohnhia_2875/jflookgnkcckhobaglndicnbbgbonegd_2875_all_acr4yh57ursmal3v5c7ephahtyxq.crx3 | US | binary | 11.0 Kb | whitelisted |
924 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/kwwzs7t4dq4pu3zh4drhohnhia_2875/jflookgnkcckhobaglndicnbbgbonegd_2875_all_acr4yh57ursmal3v5c7ephahtyxq.crx3 | US | binary | 20.9 Kb | whitelisted |
924 | svchost.exe | HEAD | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/acjv7zhir6jmdb7jzkcjxgs7n24q_2022.9.20.1141/ggkkehgbnfjpeggfpleeakpidbkibbmn_2022.9.20.1141_all_fs6e42p6n4oiiglkfie4nusfri.crx3 | US | binary | 11.0 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1252 | iexplore.exe | 179.43.133.40:443 | fundraising.mystylingmylife.xyz | Private Layer INC | CH | malicious |
1252 | iexplore.exe | 104.18.32.68:80 | ocsp.comodoca.com | CLOUDFLARENET | — | suspicious |
1252 | iexplore.exe | 172.64.155.188:80 | ocsp.comodoca.com | CLOUDFLARENET | US | suspicious |
3160 | iexplore.exe | 13.107.21.200:443 | www.bing.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
3160 | iexplore.exe | 93.184.220.29:80 | ocsp.digicert.com | EDGECAST | GB | whitelisted |
3160 | iexplore.exe | 204.79.197.200:443 | www.bing.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
3160 | iexplore.exe | 152.199.19.161:443 | iecvlist.microsoft.com | EDGECAST | US | whitelisted |
2428 | chrome.exe | 142.250.186.142:443 | clients2.google.com | GOOGLE | US | whitelisted |
2428 | chrome.exe | 216.58.212.132:443 | www.google.com | GOOGLE | US | whitelisted |
2428 | chrome.exe | 142.250.185.225:443 | clients2.googleusercontent.com | GOOGLE | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
fundraising.mystylingmylife.xyz |
| malicious |
ctldl.windowsupdate.com |
| whitelisted |
ocsp.comodoca.com |
| whitelisted |
ocsp.usertrust.com |
| whitelisted |
api.bing.com |
| whitelisted |
www.bing.com |
| whitelisted |
zerossl.ocsp.sectigo.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
iecvlist.microsoft.com |
| whitelisted |
r20swj13mr.microsoft.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1252 | iexplore.exe | Potentially Bad Traffic | ET INFO Observed ZeroSSL Certificate for Suspicious TLD (.xyz) |
1252 | iexplore.exe | Potentially Bad Traffic | ET INFO Observed ZeroSSL SSL/TLS Certificate |
1252 | iexplore.exe | Potentially Bad Traffic | ET INFO Observed ZeroSSL Certificate for Suspicious TLD (.xyz) |
1252 | iexplore.exe | Potentially Bad Traffic | ET INFO Observed ZeroSSL SSL/TLS Certificate |
2428 | chrome.exe | Potentially Bad Traffic | AV INFO HTTP Request to a *.xyz domain |
2428 | chrome.exe | Potentially Bad Traffic | ET INFO Observed ZeroSSL Certificate for Suspicious TLD (.xyz) |
2428 | chrome.exe | Potentially Bad Traffic | ET INFO Observed ZeroSSL SSL/TLS Certificate |