| download: | wa.exe |
| Full analysis: | https://app.any.run/tasks/4adeda2a-f0c9-4f87-a34b-4f33243db687 |
| Verdict: | Malicious activity |
| Analysis date: | March 29, 2018, 08:52:24 |
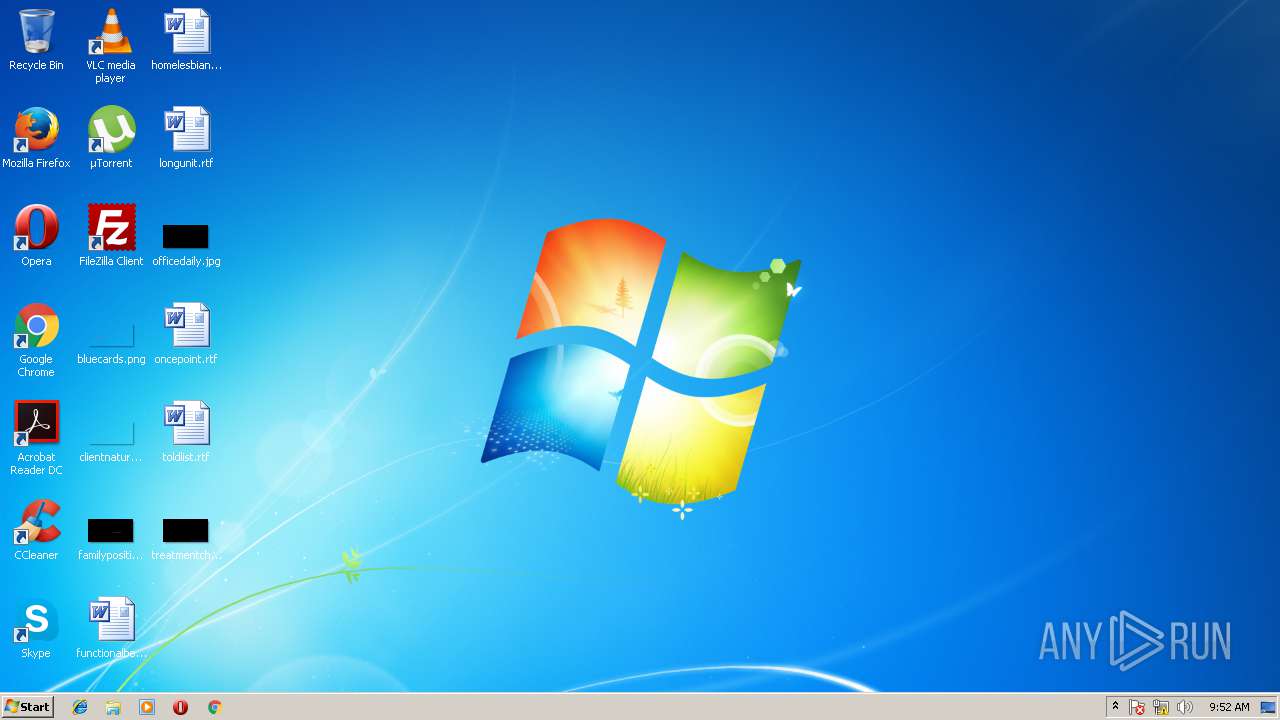
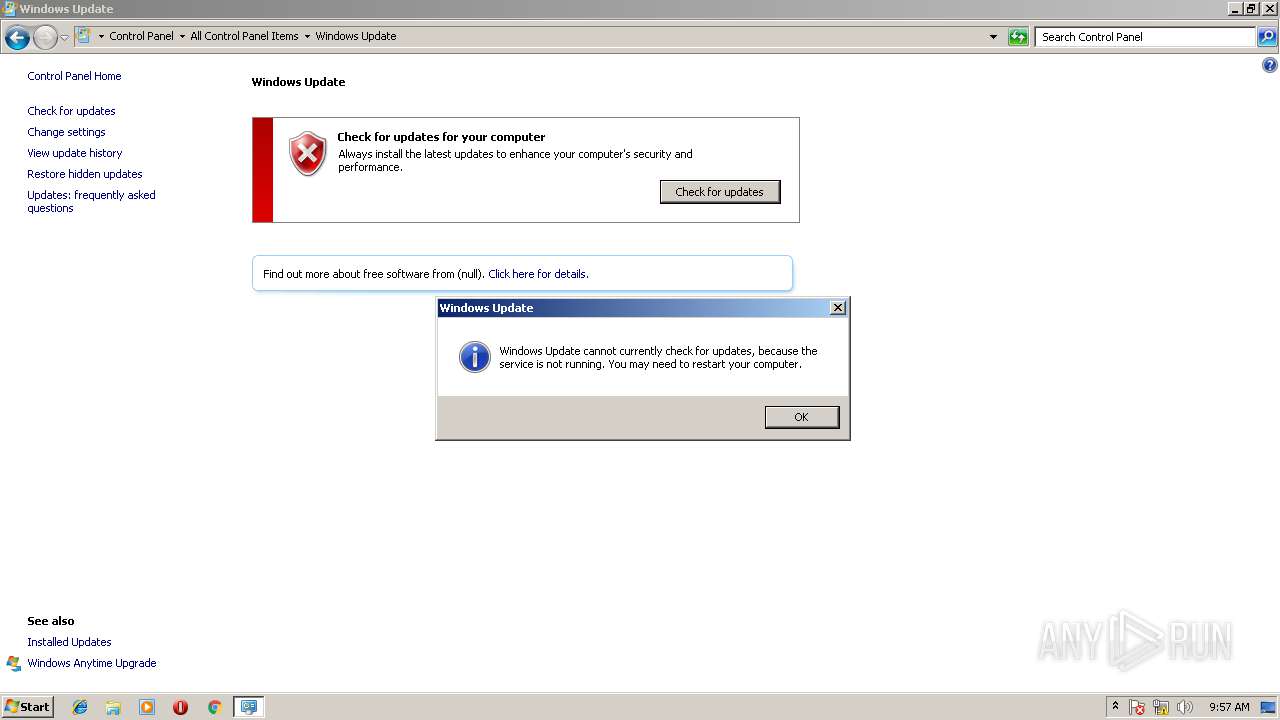
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 8710D88748DDECC1AC70BE1D7EA7F0B1 |
| SHA1: | 9B7B612233C49B3FB8E1982FFC07C57A3C281451 |
| SHA256: | 7E62DF9E16A62F6C1412986D5BD12B754B895528A09A9A2E653C91588550BA24 |
| SSDEEP: | 3072:zL80wnEzlJiXHpAYyzGRoux/jWAsyszXe:zL80zzJti/SxzX |
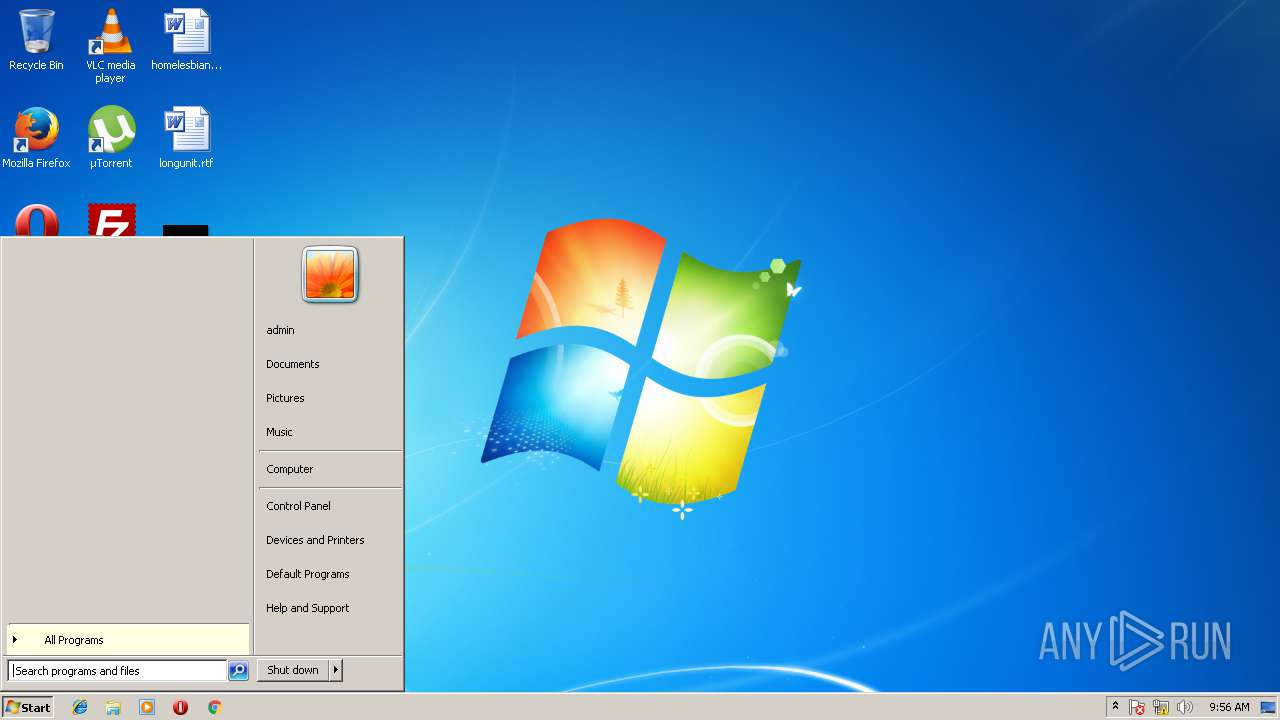
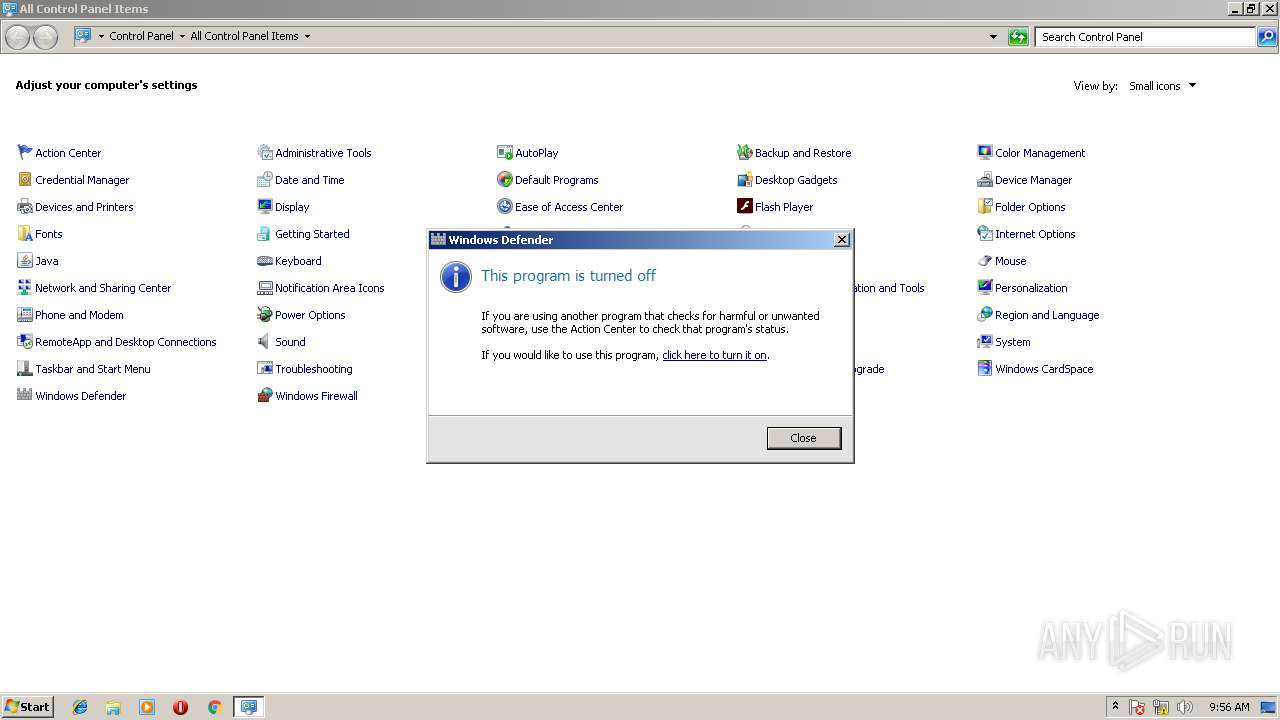
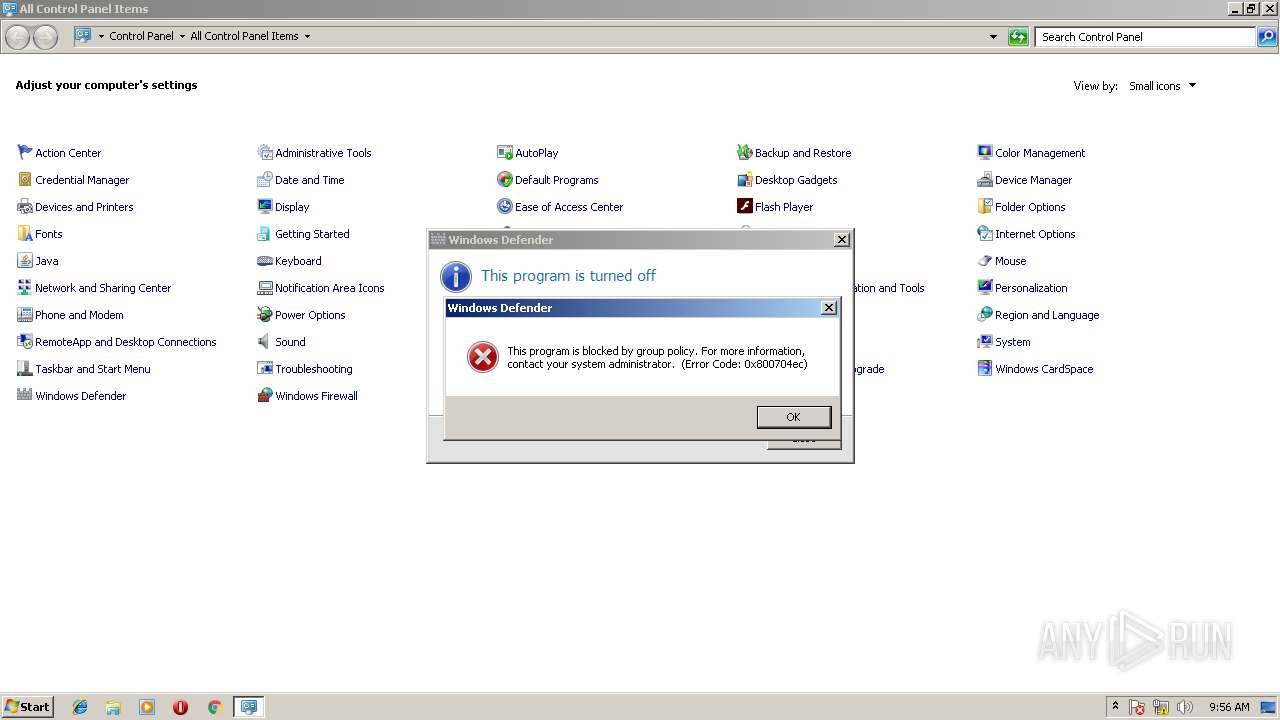
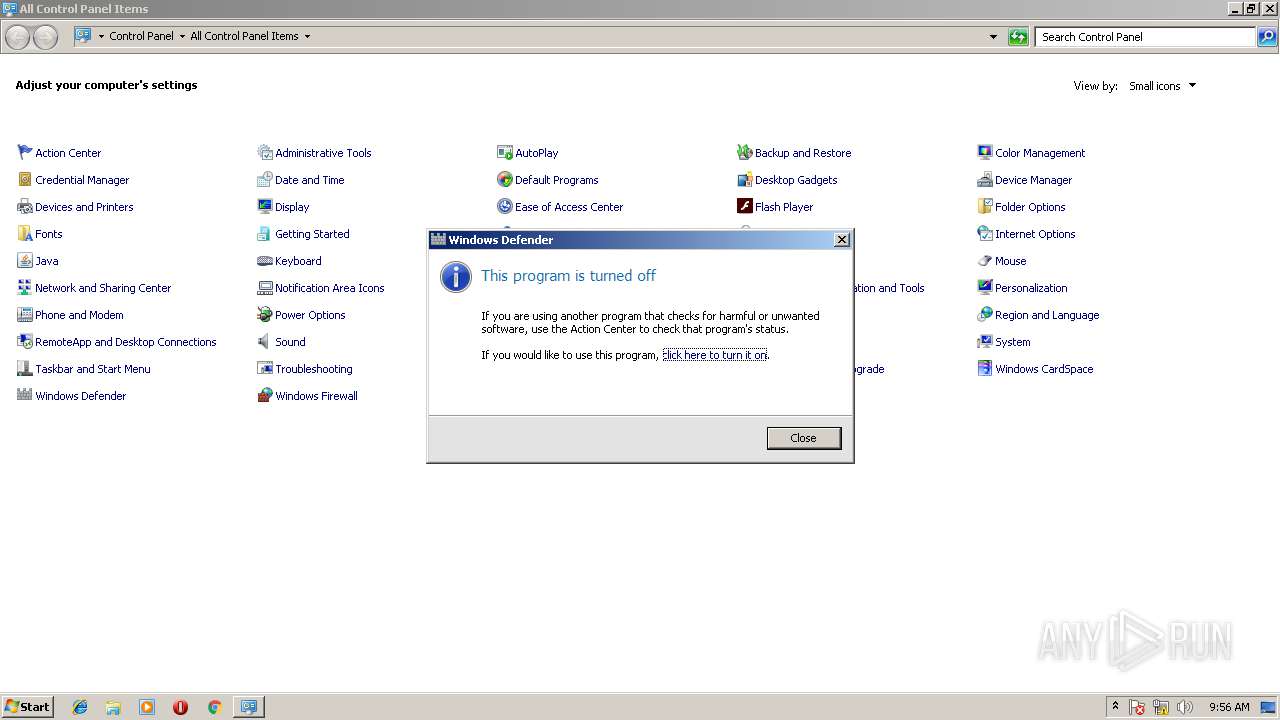
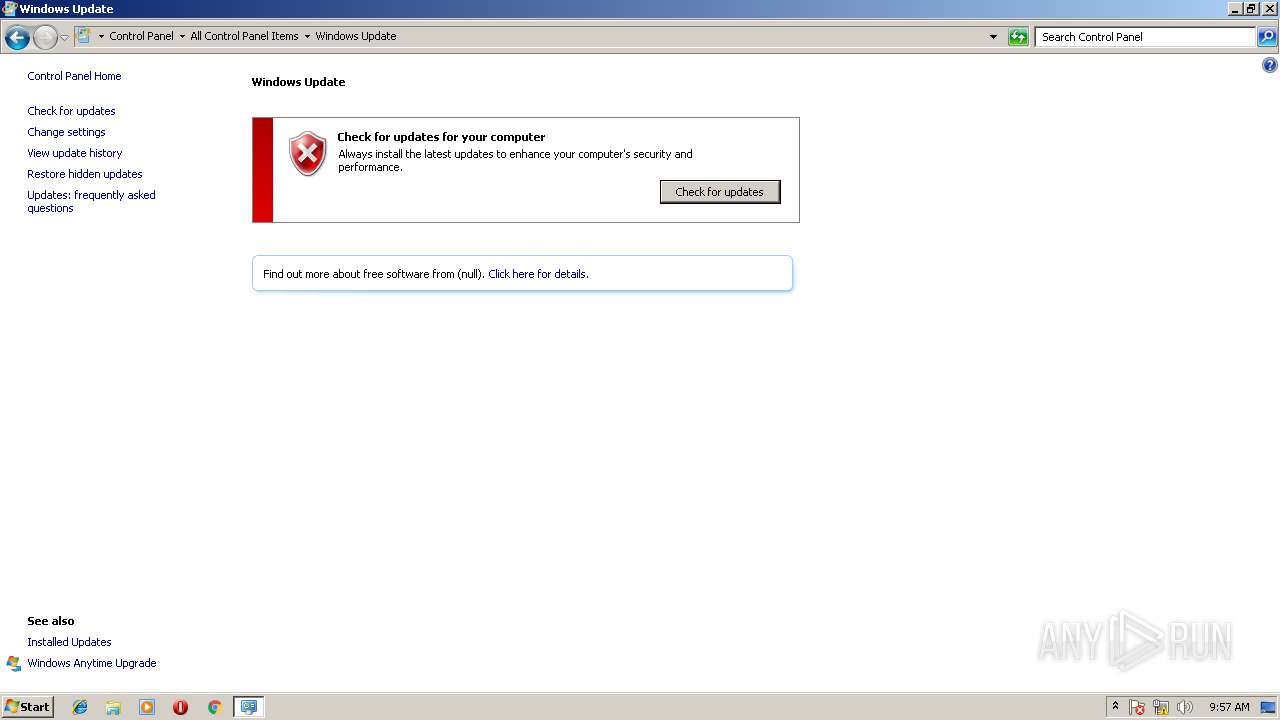
MALICIOUS
Changes the autorun value in the registry
- wa.exe (PID: 2888)
SUSPICIOUS
Starts itself from another location
- wa.exe (PID: 2888)
INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (42.2) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (37.3) |
| .dll | | | Win32 Dynamic Link Library (generic) (8.8) |
| .exe | | | Win32 Executable (generic) (6) |
| .exe | | | Generic Win/DOS Executable (2.7) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2018:03:25 11:33:41+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 9 |
| CodeSize: | 69632 |
| InitializedDataSize: | 122880 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x12fb |
| OSVersion: | 5 |
| ImageVersion: | - |
| SubsystemVersion: | 5 |
| Subsystem: | Windows GUI |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 25-Mar-2018 09:33:41 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x000000E0 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 5 |
| Time date stamp: | 25-Mar-2018 09:33:41 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x00010E20 | 0x00011000 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.60014 |
.rdata | 0x00012000 | 0x00002FB4 | 0x00003000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.51213 |
.data | 0x00015000 | 0x00003A5C | 0x00001000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 2.12768 |
.rsrc | 0x00019000 | 0x0001709A | 0x00017200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 6.16934 |
.reloc | 0x00031000 | 0x00000EB4 | 0x00001000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 6.20847 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 4.24791 | 3752 | UNKNOWN | UNKNOWN | RT_ICON |
2 | 4.88799 | 2216 | UNKNOWN | UNKNOWN | RT_ICON |
3 | 5.05671 | 1736 | UNKNOWN | UNKNOWN | RT_ICON |
4 | 4.90729 | 1384 | UNKNOWN | UNKNOWN | RT_ICON |
5 | 2.92046 | 9640 | UNKNOWN | UNKNOWN | RT_ICON |
6 | 3.29218 | 4264 | UNKNOWN | UNKNOWN | RT_ICON |
7 | 3.31836 | 2440 | UNKNOWN | UNKNOWN | RT_ICON |
8 | 3.64186 | 1128 | UNKNOWN | UNKNOWN | RT_ICON |
9 | 4.87462 | 3752 | UNKNOWN | UNKNOWN | RT_ICON |
10 | 5.12902 | 2216 | UNKNOWN | UNKNOWN | RT_ICON |
Imports
GDI32.dll |
KERNEL32.dll |
USER32.dll |
WINSPOOL.DRV |
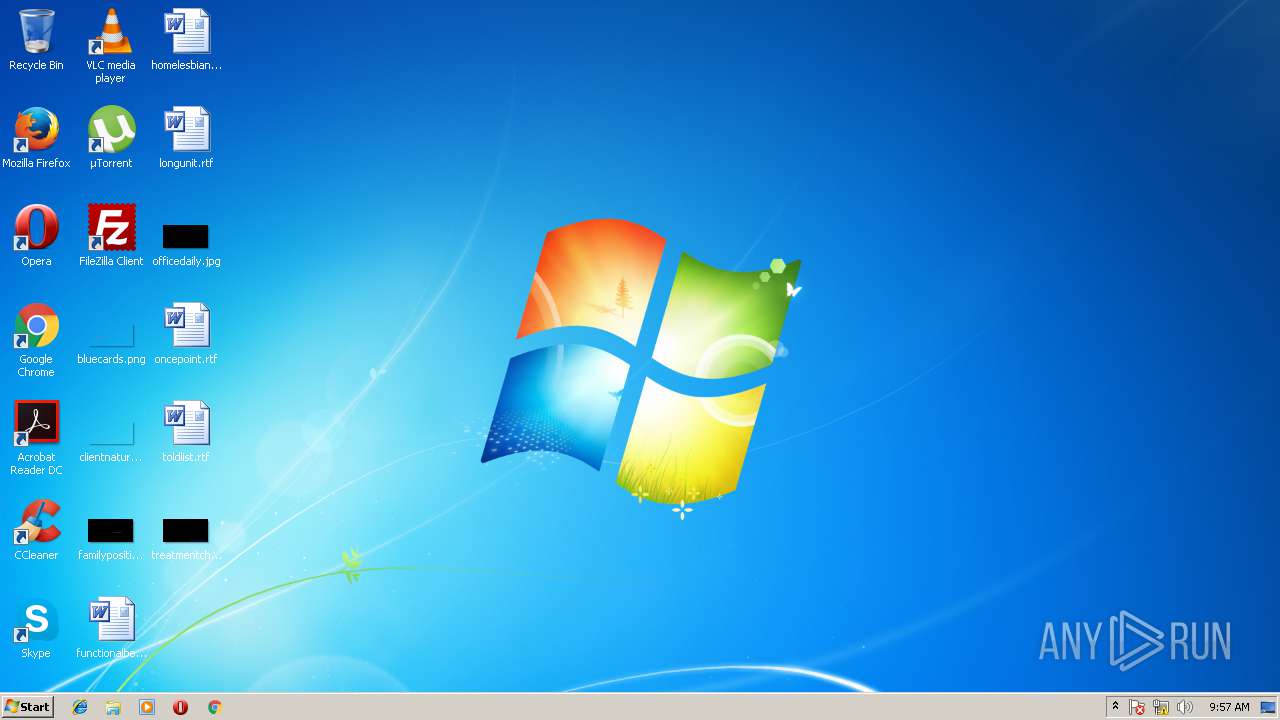
Total processes
35
Monitored processes
3
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2224 | C:\Users\admin\M-505050275092606084506800685065020\winmgr.exe | C:\Users\admin\M-505050275092606084506800685065020\winmgr.exe | — | wa.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 2888 | "C:\Users\admin\AppData\Local\Temp\wa.exe" | C:\Users\admin\AppData\Local\Temp\wa.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 3632 | "C:\Program Files\Windows Defender\MSASCui.exe" | C:\Program Files\Windows Defender\MSASCui.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Defender User Interface Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
8
Read events
6
Write events
2
Delete events
0
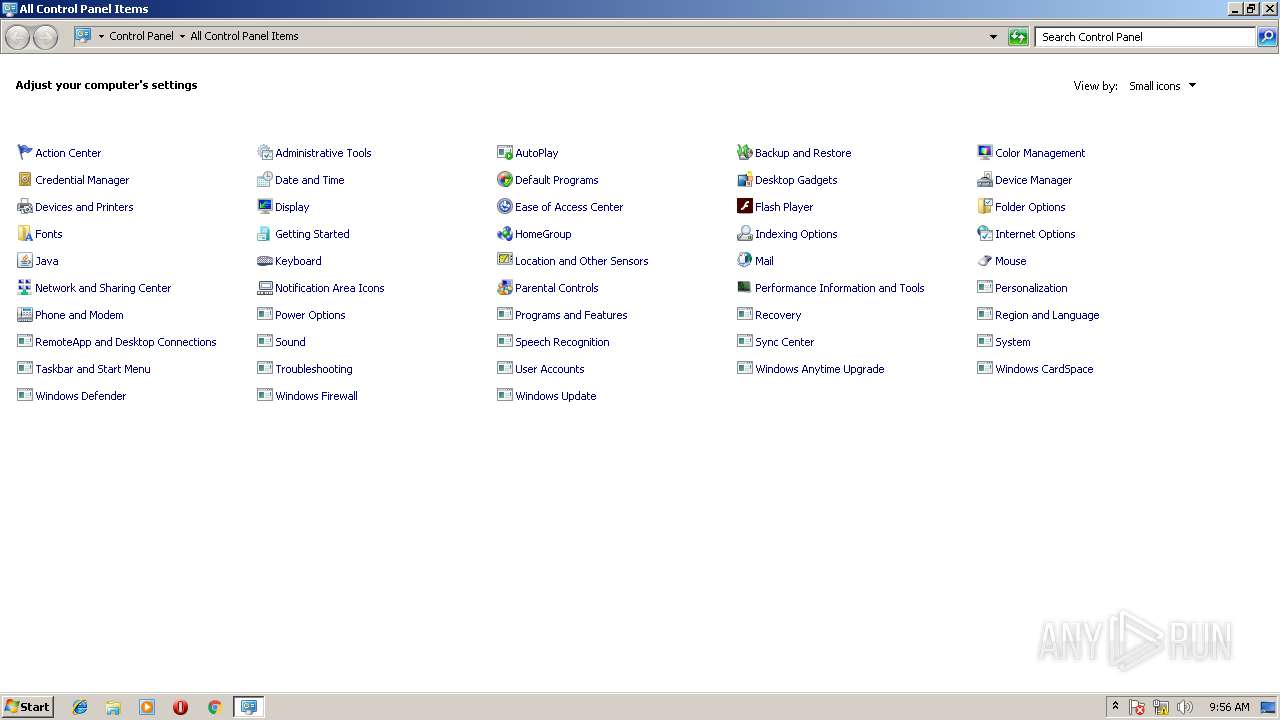
Modification events
| (PID) Process: | (2888) wa.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Run |
| Operation: | write | Name: | Microsoft Windows Manager |
Value: C:\Users\admin\M-505050275092606084506800685065020\winmgr.exe | |||
| (PID) Process: | (2888) wa.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Run |
| Operation: | write | Name: | Microsoft Windows Manager |
Value: C:\Users\admin\M-505050275092606084506800685065020\winmgr.exe | |||
Executable files
1
Suspicious files
0
Text files
0
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2888 | wa.exe | C:\Users\admin\M-505050275092606084506800685065020\winmgr.exe | executable | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
4
DNS requests
102
Threats
1
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 220.181.87.80:5050 | auoegfiaefuageudn.ru | IDC, China Telecommunications Corporation | CN | malicious |
— | — | 176.58.104.168:5050 | uoiaefnouegiajifj.nl | Linode, LLC | GB | malicious |
— | — | 212.227.20.93:5050 | rohgoruhgsorhugih.at | 1&1 Internet SE | DE | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
dns.msftncsi.com |
| shared |
auoegfiaefuageudn.ru |
| malicious |
zeaigfiagefagfzgi.ru |
| malicious |
iugeaifeifauegeai.ru |
| unknown |
oeboufanecoauegfe.ru |
| unknown |
uoiaefnouegiajifj.ru |
| unknown |
oahefaefoehgfueuu.ru |
| unknown |
eoahegohaeohgeehr.ru |
| unknown |
fauoeguuaoeoufhue.ru |
| unknown |
goiaegodbuebieibg.ru |
| malicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
— | — | A Network Trojan was detected | ET CNC Shadowserver Reported CnC Server IP group 24 |