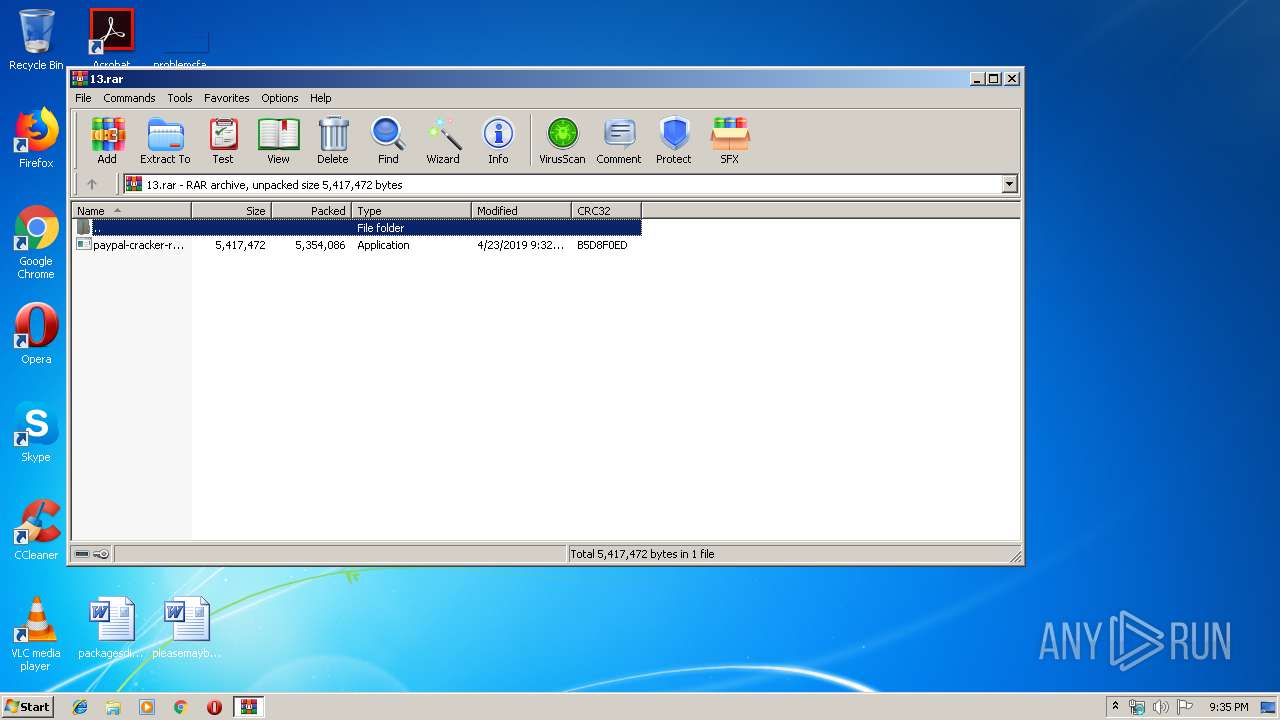
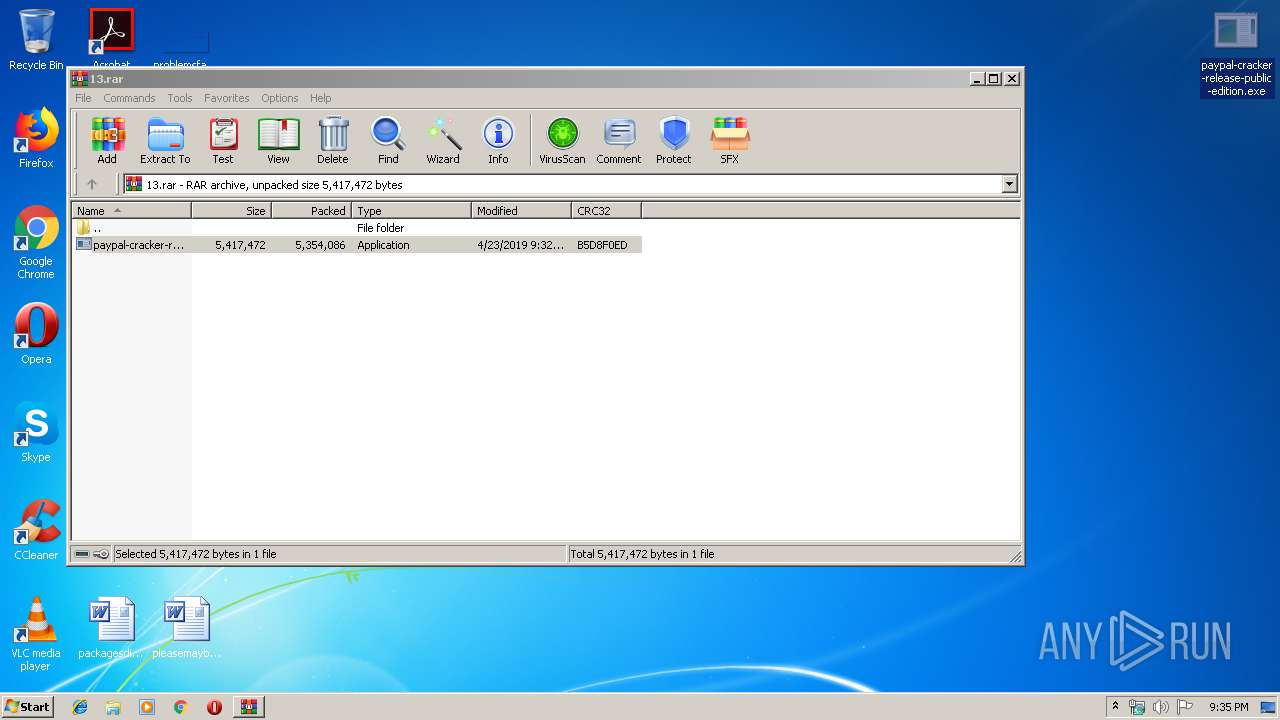
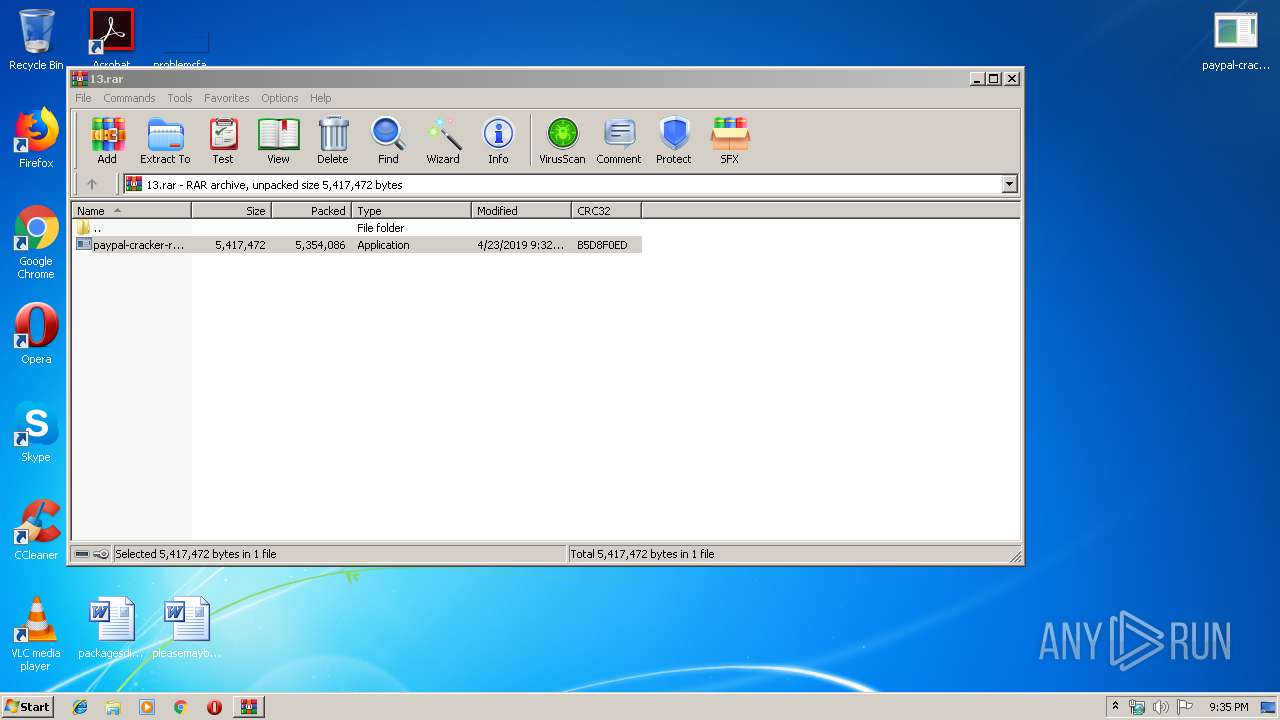
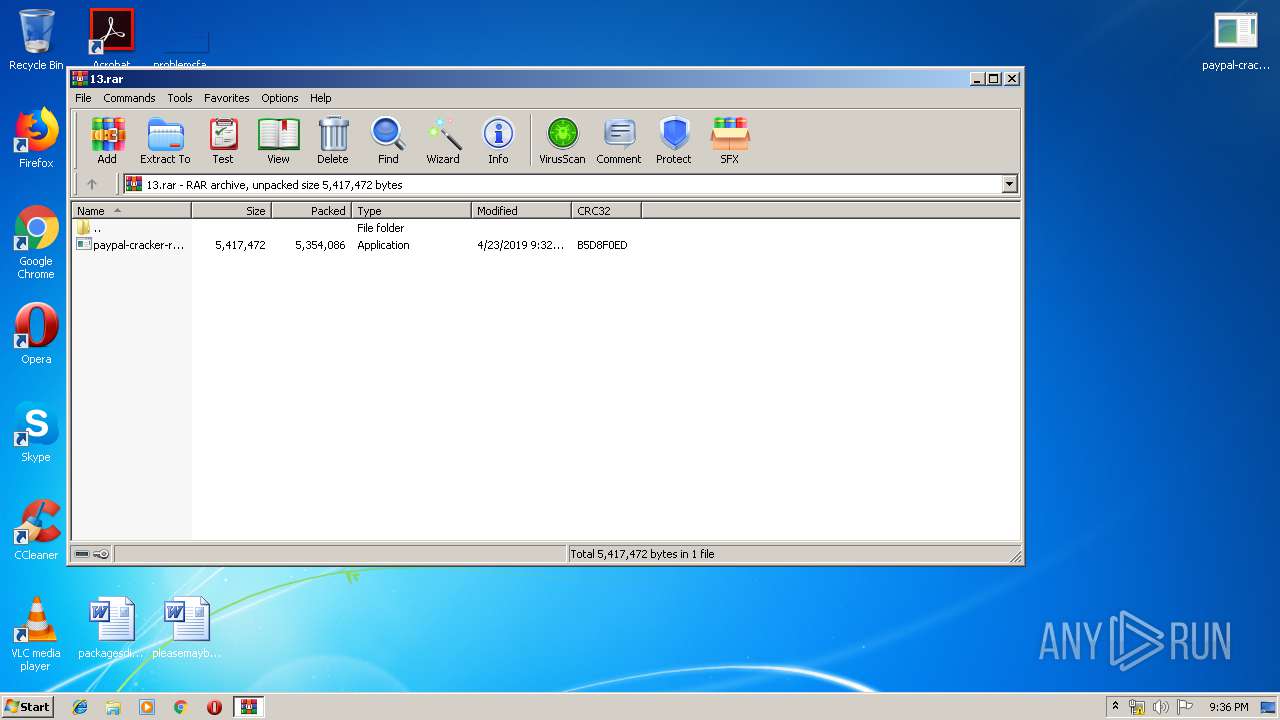
| File name: | 13.rar |
| Full analysis: | https://app.any.run/tasks/52ef92b6-30a0-494d-a1da-856dd18af789 |
| Verdict: | Malicious activity |
| Analysis date: | April 23, 2019, 20:34:41 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-rar |
| File info: | RAR archive data, v5 |
| MD5: | 2CA57DAA1789B47B42C2C8B0570380DB |
| SHA1: | 9BC87907C09E6ACF49F8D0B1F59F54512A62FF3A |
| SHA256: | 7E5E9D3FBE51D3EEAEE09FF9546D68AA9F23F70114F63086180935289F845687 |
| SSDEEP: | 98304:0VVm4e8MKvG6aYvIZqa5Goamr72R7Q/icm5DVLC2GPdNWNwBpe4er5IHXED+kUrg:im4bbaYtjG9YkPdYNxFrTCkv8Cz |
MALICIOUS
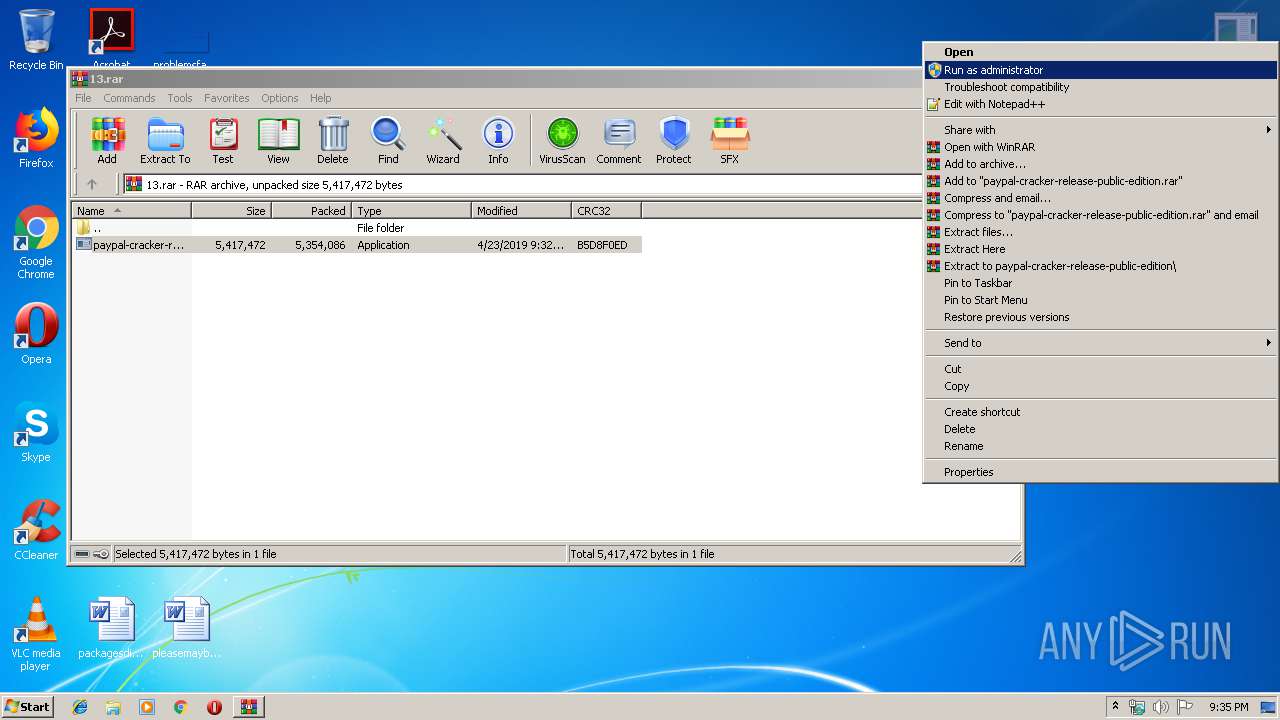
Application was dropped or rewritten from another process
- paypal-cracker-release-public-edition.exe (PID: 2700)
- ARM1K.EXE (PID: 3436)
- ARM1K.EXE (PID: 3132)
- ARMIK.EXE (PID: 3244)
- ARMIK.EXE (PID: 3664)
Loads the Task Scheduler COM API
- schtasks.exe (PID: 2932)
- schtasks.exe (PID: 3932)
Loads dropped or rewritten executable
- ARM1K.EXE (PID: 3436)
- ARM1K.EXE (PID: 3132)
Uses Task Scheduler to run other applications
- cmd.exe (PID: 2492)
- cmd.exe (PID: 3440)
Changes the autorun value in the registry
- paypal-cracker-release-public-edition.exe (PID: 2700)
SUSPICIOUS
Executable content was dropped or overwritten
- paypal-cracker-release-public-edition.exe (PID: 2700)
- ARM1K.EXE (PID: 3436)
Starts CMD.EXE for commands execution
- ARMIK.EXE (PID: 3244)
- ARMIK.EXE (PID: 3664)
Starts itself from another location
- paypal-cracker-release-public-edition.exe (PID: 2700)
Reads the BIOS version
- ARM1K.EXE (PID: 3132)
INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .rar | | | RAR compressed archive (v5.0) (61.5) |
|---|---|---|
| .rar | | | RAR compressed archive (gen) (38.4) |
Total processes
52
Monitored processes
11
Malicious processes
2
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2436 | "C:\Windows\explorer.exe" | C:\Windows\explorer.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2492 | "C:\Windows\System32\cmd.exe" /C SCHTASKS.exe /DELETE /TN svhost /F | C:\Windows\System32\cmd.exe | — | ARMIK.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 1 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
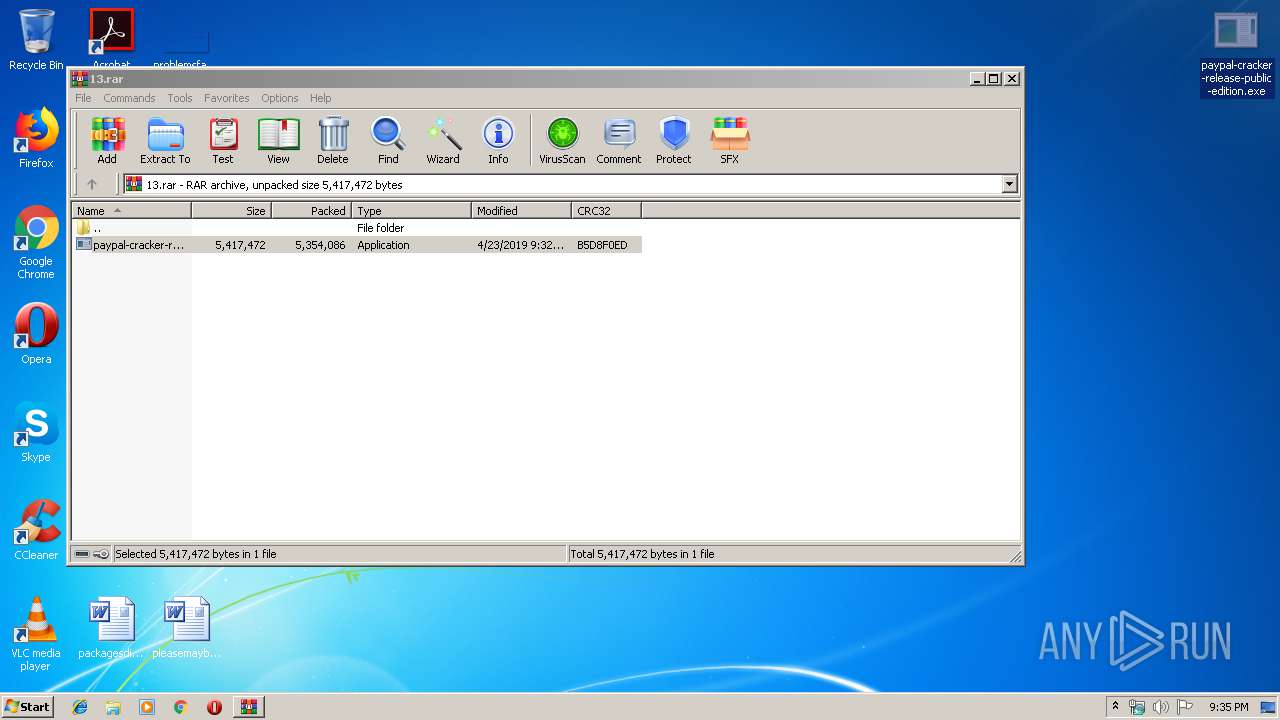
| 2700 | "C:\Users\admin\Desktop\paypal-cracker-release-public-edition.exe" | C:\Users\admin\Desktop\paypal-cracker-release-public-edition.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Integrity Level: HIGH Description: ExploreFramework Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
| 2932 | SCHTASKS.exe /DELETE /TN svhost /F | C:\Windows\system32\schtasks.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Manages scheduled tasks Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3060 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Temp\13.rar" | C:\Program Files\WinRAR\WinRAR.exe | — | explorer.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
| 3132 | "C:\Users\admin\AppData\Local\Temp\ARM1K.EXE" | C:\Users\admin\AppData\Local\Temp\ARM1K.EXE | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Integrity Level: MEDIUM Description: SurfaceFramework Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
| 3244 | "C:\Users\admin\AppData\Local\Temp\ARMIK.EXE" | C:\Users\admin\AppData\Local\Temp\ARMIK.EXE | — | paypal-cracker-release-public-edition.exe | |||||||||||
User: admin Company: Microsoft Integrity Level: HIGH Description: ExploreFramework Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
| 3436 | "C:\Users\admin\AppData\Local\Temp\ARM1K.EXE" | C:\Users\admin\AppData\Local\Temp\ARM1K.EXE | paypal-cracker-release-public-edition.exe | ||||||||||||
User: admin Company: Microsoft Integrity Level: HIGH Description: SurfaceFramework Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
| 3440 | "C:\Windows\System32\cmd.exe" /C SCHTASKS.exe /DELETE /TN svhost /F | C:\Windows\System32\cmd.exe | — | ARMIK.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 1 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 3664 | "C:\Users\admin\AppData\Local\Temp\ARMIK.EXE" | C:\Users\admin\AppData\Local\Temp\ARMIK.EXE | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Integrity Level: MEDIUM Description: ExploreFramework Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
Total events
965
Read events
944
Write events
21
Delete events
0
Modification events
| (PID) Process: | (3060) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (3060) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (3060) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\62\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (3060) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\13.rar | |||
| (PID) Process: | (3060) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (3060) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (3060) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (3060) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (2700) paypal-cracker-release-public-edition.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Run |
| Operation: | write | Name: | Winit Updater |
Value: "C:\Users\admin\AppData\Local\Temp\ARMIK.EXE" | |||
| (PID) Process: | (3244) ARMIK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
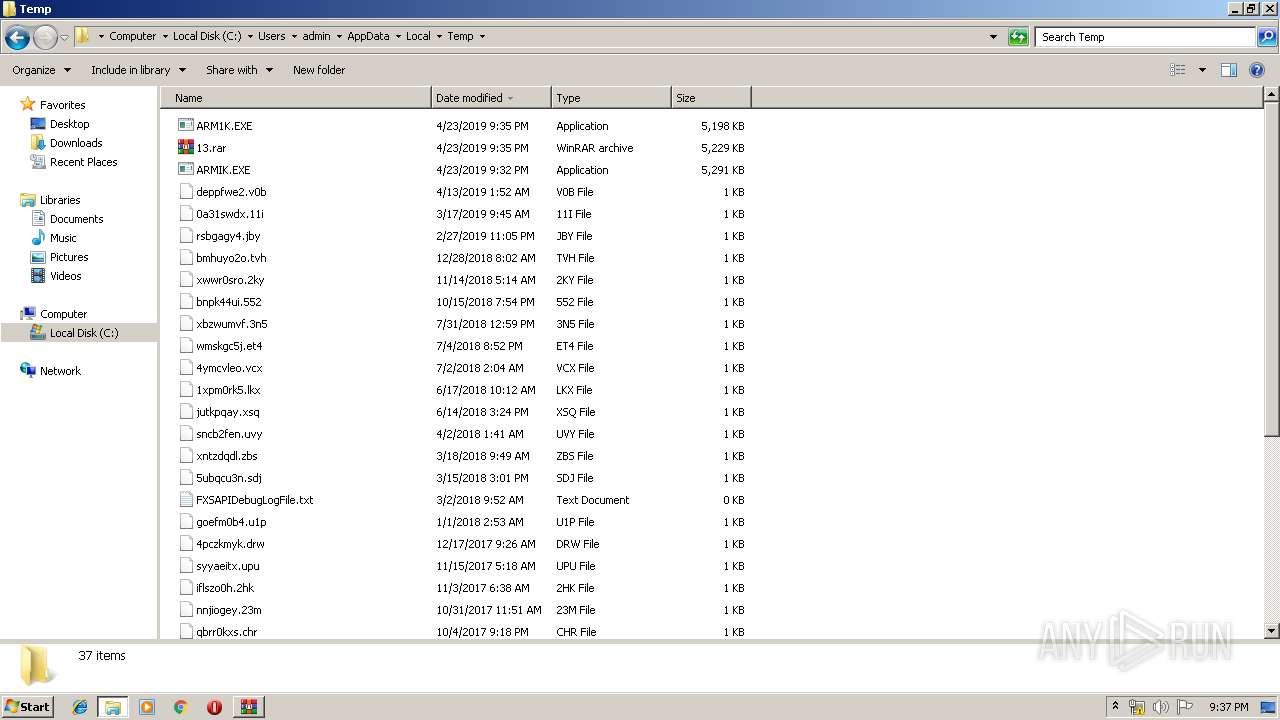
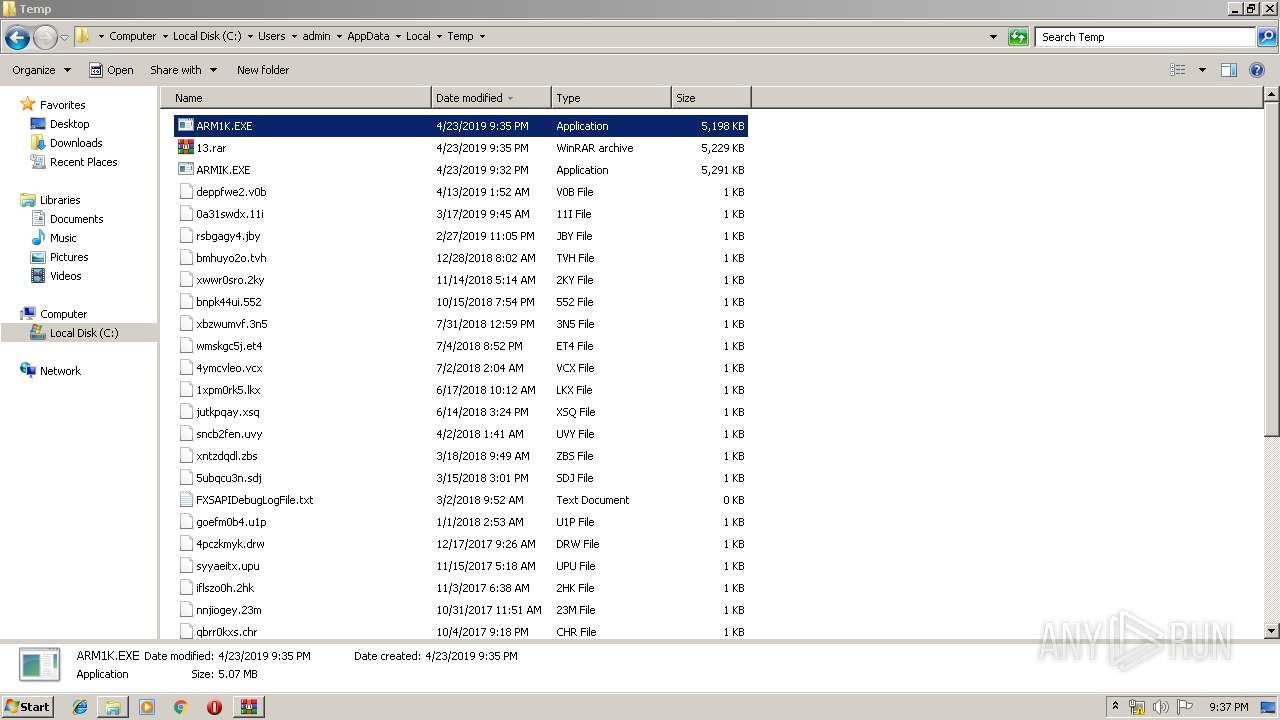
Executable files
3
Suspicious files
0
Text files
0
Unknown types
0
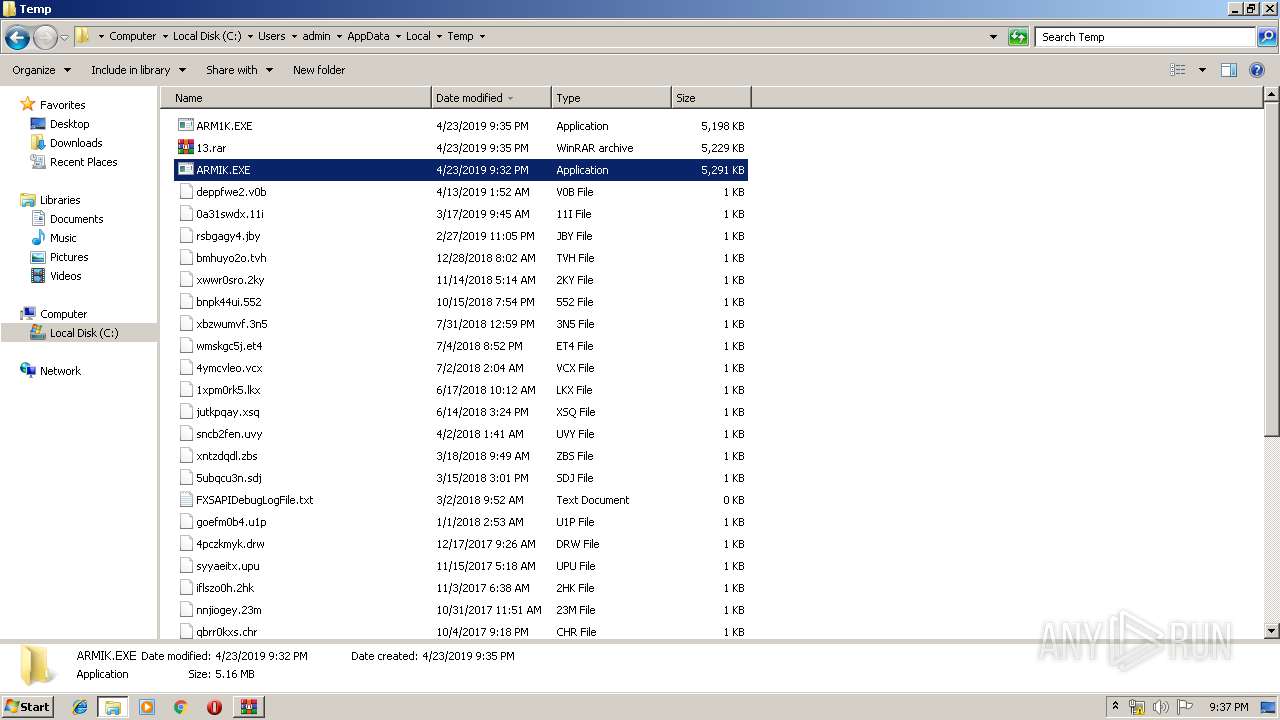
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3060 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa3060.21924\paypal-cracker-release-public-edition.exe | — | |
MD5:— | SHA256:— | |||
| 2700 | paypal-cracker-release-public-edition.exe | C:\Users\admin\AppData\Local\Temp\ARMIK.EXE | executable | |
MD5:— | SHA256:— | |||
| 2700 | paypal-cracker-release-public-edition.exe | C:\Users\admin\AppData\Local\Temp\ARM1K.EXE | executable | |
MD5:— | SHA256:— | |||
| 3436 | ARM1K.EXE | C:\Users\admin\AppData\Local\Temp\97e9b7f8-d1fa-4666-b562-c8182cf4b82b\AgileDotNetRT.dll | executable | |
MD5:DB956A02DABA647F229B01D56EA5D892 | SHA256:5B4F5E6CC52DF647673B94249E5392E6F00CC5FFB7E1FC7C4219351762618CDD | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report