| File name: | Supremo.exe |
| Full analysis: | https://app.any.run/tasks/c71a5bbb-5b9b-4719-b934-b7eed9d5ad6d |
| Verdict: | Malicious activity |
| Analysis date: | November 23, 2018, 06:15:52 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, UPX compressed |
| MD5: | EB1BD995891320EA9CE06436AF9F99F2 |
| SHA1: | 98CDA1869CF57BD29B8B559178902F7575DD1E49 |
| SHA256: | 7E5150348D6614D62CCC643E29041BAA2A4851FD11D97E05AD4ADD386E2F0407 |
| SSDEEP: | 196608:ESbIcF9yeOXODUfL/wjBdW8yEVI0Kj8gzWm:jNFo5X0UTmE8y+Kjpf |
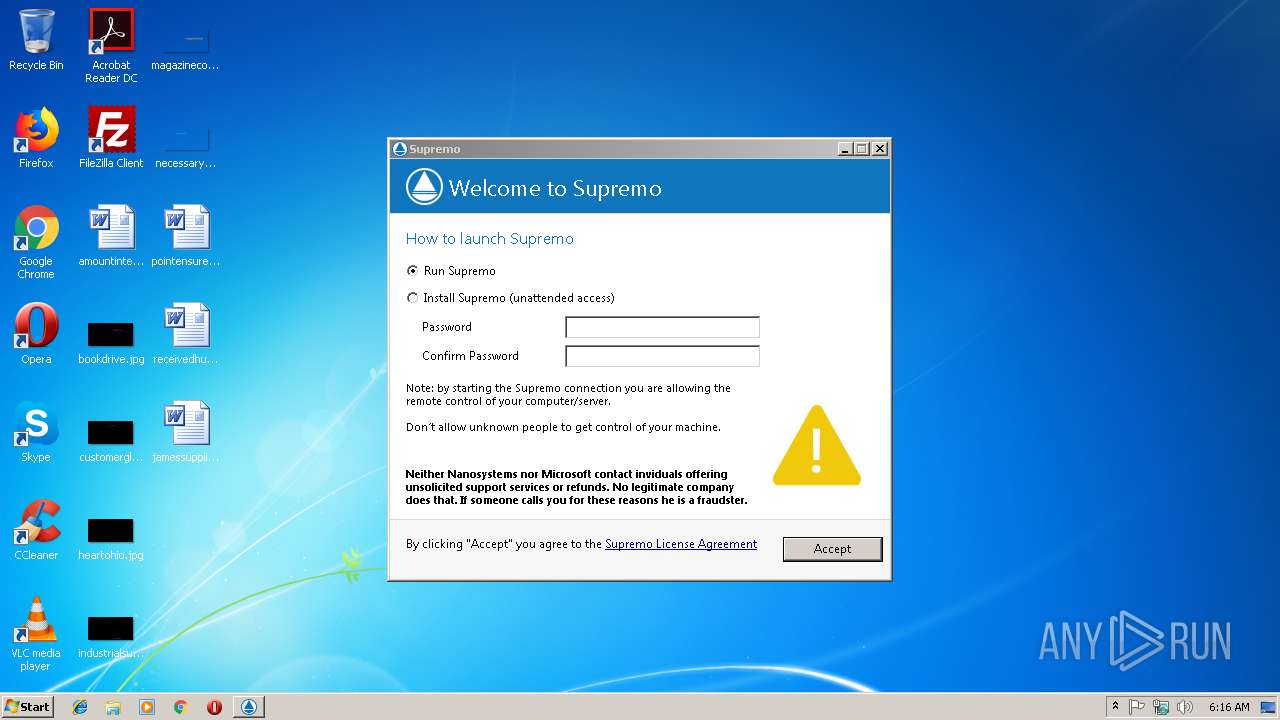
MALICIOUS
Application was dropped or rewritten from another process
- SupremoSystem.exe (PID: 1472)
- SupremoSystem.exe (PID: 2944)
- SupremoHelper.exe (PID: 2760)
LATENTBOT was detected
- Supremo.exe (PID: 2152)
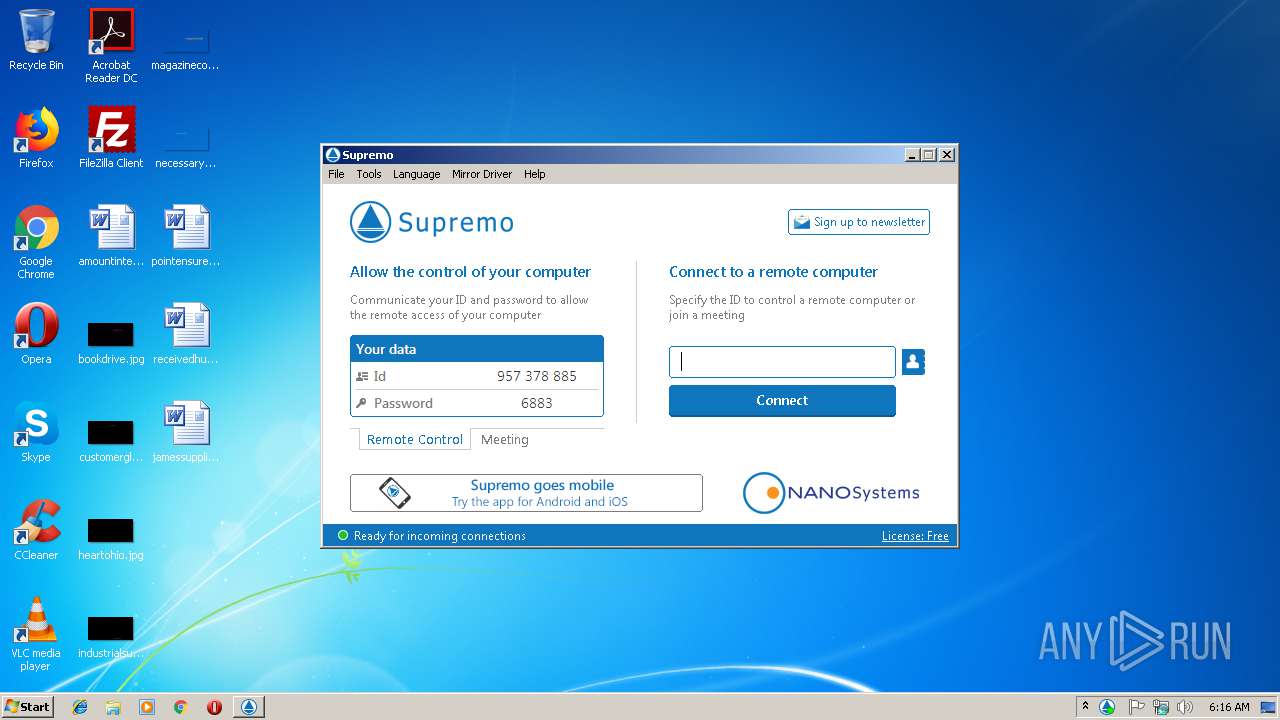
Connects to CnC server
- Supremo.exe (PID: 2152)
Changes settings of System certificates
- Supremo.exe (PID: 2152)
SUSPICIOUS
Reads Windows Product ID
- Supremo.exe (PID: 3140)
Executable content was dropped or overwritten
- Supremo.exe (PID: 3140)
- Supremo.exe (PID: 2152)
Removes files from Windows directory
- Supremo.exe (PID: 2152)
Modifies the open verb of a shell class
- Supremo.exe (PID: 2152)
Creates files in the Windows directory
- Supremo.exe (PID: 2152)
Creates files in the program directory
- Supremo.exe (PID: 2152)
- Supremo.exe (PID: 3140)
Adds / modifies Windows certificates
- Supremo.exe (PID: 2152)
Checks for external IP
- Supremo.exe (PID: 2152)
INFO
Reads settings of System Certificates
- Supremo.exe (PID: 2152)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | UPX compressed Win32 Executable (43.5) |
|---|---|---|
| .exe | | | Win32 EXE Yoda's Crypter (42.7) |
| .exe | | | Win32 Executable (generic) (7.2) |
| .exe | | | Generic Win/DOS Executable (3.2) |
| .exe | | | DOS Executable Generic (3.2) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2018:11:15 09:49:26+01:00 |
| PEType: | PE32 |
| LinkerVersion: | 2.25 |
| CodeSize: | 6393856 |
| InitializedDataSize: | 106496 |
| UninitializedDataSize: | 22142976 |
| EntryPoint: | 0x1b36610 |
| OSVersion: | 5 |
| ImageVersion: | - |
| SubsystemVersion: | 5 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 3.3.4.995 |
| ProductVersionNumber: | 3.3.4.0 |
| FileFlagsMask: | 0x0000 |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Windows, Latin1 |
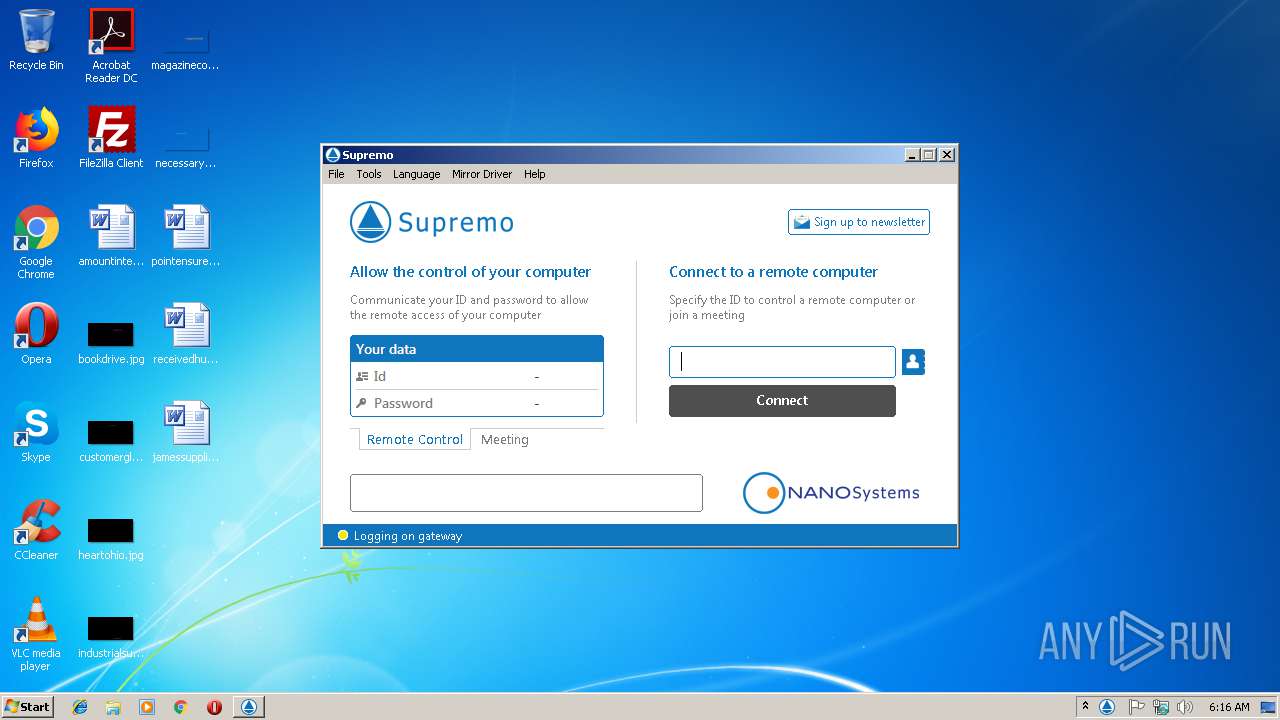
| CompanyName: | Nanosystems S.r.l. |
| FileDescription: | Supremo |
| FileVersion: | 3.3.4.995 |
| InternalName: | Supremo |
| LegalCopyright: | Nanosystems S.r.l. |
| OriginalFileName: | Supremo.exe |
| ProductName: | Supremo Remote Control |
| ProductVersion: | 3.3.4 |
| Comments: | Major Version Release |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 15-Nov-2018 08:49:26 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0050 |
| Pages in file: | 0x0002 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x000F |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x001A |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000100 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 3 |
| Time date stamp: | 15-Nov-2018 08:49:26 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
UPX0 | 0x00001000 | 0x0151E000 | 0x00000000 | IMAGE_SCN_CNT_UNINITIALIZED_DATA, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
UPX1 | 0x0151F000 | 0x00619000 | 0x00618A00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 7.99994 |
.rsrc | 0x01B38000 | 0x0001A000 | 0x00019600 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 5.18142 |
Imports
KERNEL32.DLL |
SHFolder.dll |
advapi32.dll |
comctl32.dll |
comdlg32.dll |
crypt32.dll |
gdi32.dll |
iphlpapi.dll |
kernel32 |
mpr.dll |
Total processes
37
Monitored processes
5
Malicious processes
2
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1472 | "C:\Users\admin\AppData\Local\Temp\SupremoRemoteDesktop\SupremoSystem.exe" "C:\Users\admin\AppData\Local\Temp\Supremo.exe" "/SYSRUN" | C:\Users\admin\AppData\Local\Temp\SupremoRemoteDesktop\SupremoSystem.exe | Supremo.exe | ||||||||||||
User: admin Company: Nanosystems Srl Integrity Level: HIGH Description: Supremo System Exit code: 0 Version: 1.0.0.0000 Modules
| |||||||||||||||
| 2152 | "C:\Users\admin\AppData\Local\Temp\Supremo.exe" /SYSRUN | C:\Users\admin\AppData\Local\Temp\Supremo.exe | SupremoSystem.exe | ||||||||||||
User: SYSTEM Company: Nanosystems S.r.l. Integrity Level: SYSTEM Description: Supremo Exit code: 0 Version: 3.3.4.995 Modules
| |||||||||||||||
| 2760 | C:\Windows\Temp\SupremoRemoteDesktop\SupremoHelper.exe | C:\Windows\Temp\SupremoRemoteDesktop\SupremoHelper.exe | — | Supremo.exe | |||||||||||
User: admin Company: Nanosystems S.r.l. Integrity Level: MEDIUM Description: Supremo Helper Exit code: 0 Version: 3.3.4.995 Modules
| |||||||||||||||
| 2944 | C:\Users\admin\AppData\Local\Temp\SupremoRemoteDesktop\SupremoSystem.exe | C:\Users\admin\AppData\Local\Temp\SupremoRemoteDesktop\SupremoSystem.exe | — | services.exe | |||||||||||
User: SYSTEM Company: Nanosystems Srl Integrity Level: SYSTEM Description: Supremo System Exit code: 0 Version: 1.0.0.0000 Modules
| |||||||||||||||
| 3140 | "C:\Users\admin\AppData\Local\Temp\Supremo.exe" | C:\Users\admin\AppData\Local\Temp\Supremo.exe | explorer.exe | ||||||||||||
User: admin Company: Nanosystems S.r.l. Integrity Level: MEDIUM Description: Supremo Exit code: 0 Version: 3.3.4.995 Modules
| |||||||||||||||
Total events
440
Read events
413
Write events
27
Delete events
0
Modification events
| (PID) Process: | (3140) Supremo.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (3140) Supremo.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (2152) Supremo.exe | Key: | HKEY_USERS\.DEFAULT\Software\Microsoft\Windows\CurrentVersion\Shell Extensions\Cached |
| Operation: | write | Name: | {D9144DCD-E998-4ECA-AB6A-DCD83CCBA16D} {0C6C4200-C589-11D0-999A-00C04FD655E1} 0xFFFF |
Value: 01000000000000006225B809F482D401 | |||
| (PID) Process: | (2152) Supremo.exe | Key: | HKEY_USERS\.DEFAULT\Software\Microsoft\Windows\CurrentVersion\Shell Extensions\Cached |
| Operation: | write | Name: | {4E77131D-3629-431C-9818-C5679DC83E81} {0C6C4200-C589-11D0-999A-00C04FD655E1} 0xFFFF |
Value: 01000000000000006225B809F482D401 | |||
| (PID) Process: | (2152) Supremo.exe | Key: | HKEY_USERS\.DEFAULT\Software\Microsoft\Windows\CurrentVersion\Shell Extensions\Cached |
| Operation: | write | Name: | {08244EE6-92F0-47F2-9FC9-929BAA2E7235} {0C6C4200-C589-11D0-999A-00C04FD655E1} 0xFFFF |
Value: 0100000000000000BC87BA09F482D401 | |||
| (PID) Process: | (2152) Supremo.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\supremo |
| Operation: | write | Name: | |
Value: Supremo URI | |||
| (PID) Process: | (2152) Supremo.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\supremo |
| Operation: | write | Name: | URL Protocol |
Value: | |||
| (PID) Process: | (2152) Supremo.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\supremo |
| Operation: | write | Name: | Content Type |
Value: application/x-supremo | |||
| (PID) Process: | (2152) Supremo.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\supremo\shell |
| Operation: | write | Name: | |
Value: open | |||
| (PID) Process: | (2152) Supremo.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\supremo\shell\open\command |
| Operation: | write | Name: | |
Value: "C:\Users\admin\AppData\Local\Temp\Supremo.exe" "%1" | |||
Executable files
2
Suspicious files
12
Text files
28
Unknown types
1
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2152 | Supremo.exe | C:\ProgramData\SupremoRemoteDesktop\Languages\Supremo.cs.lng | text | |
MD5:— | SHA256:— | |||
| 2152 | Supremo.exe | C:\ProgramData\SupremoRemoteDesktop\Languages\Supremo.bg.lng | text | |
MD5:— | SHA256:— | |||
| 3140 | Supremo.exe | C:\ProgramData\SupremoRemoteDesktop\Log\Supremo.00.Client.log | text | |
MD5:— | SHA256:— | |||
| 3140 | Supremo.exe | C:\Users\admin\AppData\Local\Temp\SupremoRemoteDesktop\SupremoSystem.exe | executable | |
MD5:— | SHA256:— | |||
| 2152 | Supremo.exe | C:\ProgramData\SupremoRemoteDesktop\Languages\Supremo.ca.lng | text | |
MD5:— | SHA256:— | |||
| 2152 | Supremo.exe | C:\ProgramData\SupremoRemoteDesktop\Languages\Supremo.br.lng | text | |
MD5:— | SHA256:— | |||
| 2152 | Supremo.exe | C:\ProgramData\SupremoRemoteDesktop\Languages\Supremo.bs.lng | text | |
MD5:— | SHA256:— | |||
| 2152 | Supremo.exe | C:\ProgramData\SupremoRemoteDesktop\Languages\Supremo.de.lng | text | |
MD5:— | SHA256:— | |||
| 2152 | Supremo.exe | C:\ProgramData\SupremoRemoteDesktop\Languages\Supremo.el.lng | text | |
MD5:— | SHA256:— | |||
| 2152 | Supremo.exe | C:\ProgramData\SupremoRemoteDesktop\Languages\Supremo.fr.lng | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
15
TCP/UDP connections
9
DNS requests
6
Threats
29
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2152 | Supremo.exe | POST | 200 | 136.243.108.154:443 | http://136.243.108.154:443/$rdgate?ACTION=HELLO&ID=NEW | DE | binary | 25 b | suspicious |
2152 | Supremo.exe | POST | 200 | 136.243.108.154:443 | http://136.243.108.154:443/$rdgate?ID=7F99BAACC3F748708D98829AC9B97268 | DE | binary | 16 b | suspicious |
2152 | Supremo.exe | POST | 200 | 136.243.108.154:443 | http://136.243.108.154:443/$rdgate?ID=7F99BAACC3F748708D98829AC9B97268 | DE | binary | 16 b | suspicious |
2152 | Supremo.exe | POST | 200 | 136.243.108.154:443 | http://136.243.108.154:443/$rdgate?ID=7F99BAACC3F748708D98829AC9B97268 | DE | binary | 15 b | suspicious |
2152 | Supremo.exe | POST | 200 | 136.243.108.154:443 | http://136.243.108.154:443/$rdgate?ACTION=START&ID=7F99BAACC3F748708D98829AC9B97268 | DE | binary | 28 b | suspicious |
2152 | Supremo.exe | POST | 200 | 136.243.108.154:443 | http://136.243.108.154:443/$rdgate?ACTION=START&ID=DE2F9FE234EE4E11BCA6774FCE27B43E | DE | binary | 25 b | suspicious |
2152 | Supremo.exe | POST | 200 | 136.243.108.154:443 | http://136.243.108.154:443/$rdgate?ACTION=HELLO&ID=NEW | DE | binary | 25 b | suspicious |
2152 | Supremo.exe | POST | — | 136.243.108.154:443 | http://136.243.108.154:443/$rdgate?ID=7F99BAACC3F748708D98829AC9B97268 | DE | — | — | suspicious |
2152 | Supremo.exe | POST | 200 | 136.243.108.154:443 | http://136.243.108.154:443/$rdgate?ID=7F99BAACC3F748708D98829AC9B97268 | DE | binary | 12 b | suspicious |
2152 | Supremo.exe | POST | 200 | 136.243.108.154:443 | http://136.243.108.154:443/$rdgate?ID=DE2F9FE234EE4E11BCA6774FCE27B43E | DE | binary | 16 b | suspicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2152 | Supremo.exe | 151.80.237.21:443 | www.nanosystems.it | OVH SAS | FR | suspicious |
2152 | Supremo.exe | 104.16.92.188:80 | crt.comodoca.com | Cloudflare Inc | US | shared |
2152 | Supremo.exe | 216.58.206.14:443 | www.google-analytics.com | Google Inc. | US | whitelisted |
2152 | Supremo.exe | 138.201.35.164:80 | supremogw32.nanosystems.it | Hetzner Online GmbH | DE | unknown |
2152 | Supremo.exe | 136.243.108.154:443 | supremogw27.nanosystems.it | Hetzner Online GmbH | DE | suspicious |
2152 | Supremo.exe | 216.239.38.21:443 | ipinfo.io | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
ipinfo.io |
| shared |
www.nanosystems.it |
| suspicious |
supremogw32.nanosystems.it |
| suspicious |
supremogw27.nanosystems.it |
| malicious |
www.google-analytics.com |
| whitelisted |
crt.comodoca.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2152 | Supremo.exe | A Network Trojan was detected | ET POLICY Possible External IP Lookup Domain Observed in SNI (ipinfo. io) |
2152 | Supremo.exe | Potential Corporate Privacy Violation | ET POLICY Possible External IP Lookup SSL Cert Observed (ipinfo.io) |
2152 | Supremo.exe | A Network Trojan was detected | SUSPICIOUS [PTsecurity] eStream SQL Remote Desktop |
2152 | Supremo.exe | A Network Trojan was detected | MALWARE [PTsecurity] LatentBot HTTP POST Checkin |
2152 | Supremo.exe | Potentially Bad Traffic | ET POLICY HTTP traffic on port 443 (POST) |
2152 | Supremo.exe | A Network Trojan was detected | SUSPICIOUS [PTsecurity] eStream SQL Remote Desktop |
2152 | Supremo.exe | Potentially Bad Traffic | ET POLICY HTTP traffic on port 443 (POST) |
2152 | Supremo.exe | A Network Trojan was detected | SUSPICIOUS [PTsecurity] eStream SQL Remote Desktop |
2152 | Supremo.exe | Potentially Bad Traffic | ET POLICY HTTP traffic on port 443 (POST) |
2152 | Supremo.exe | A Network Trojan was detected | SUSPICIOUS [PTsecurity] eStream SQL Remote Desktop |
4 ETPRO signatures available at the full report