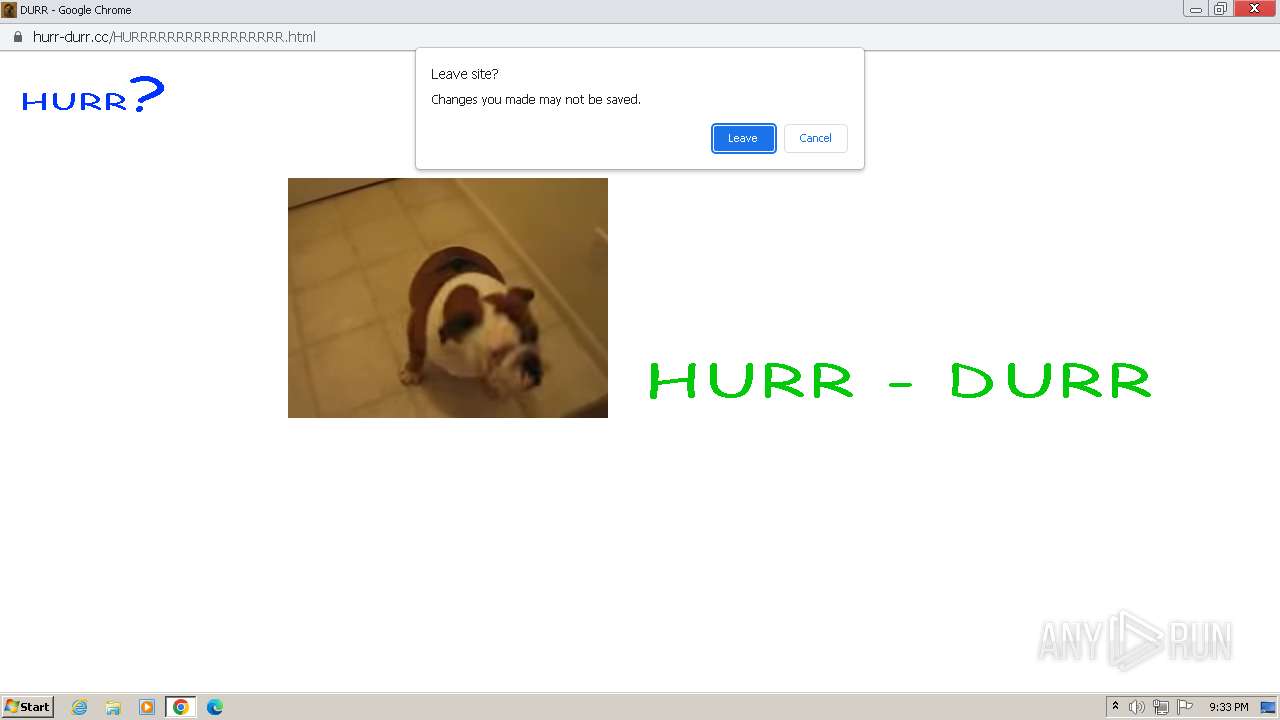
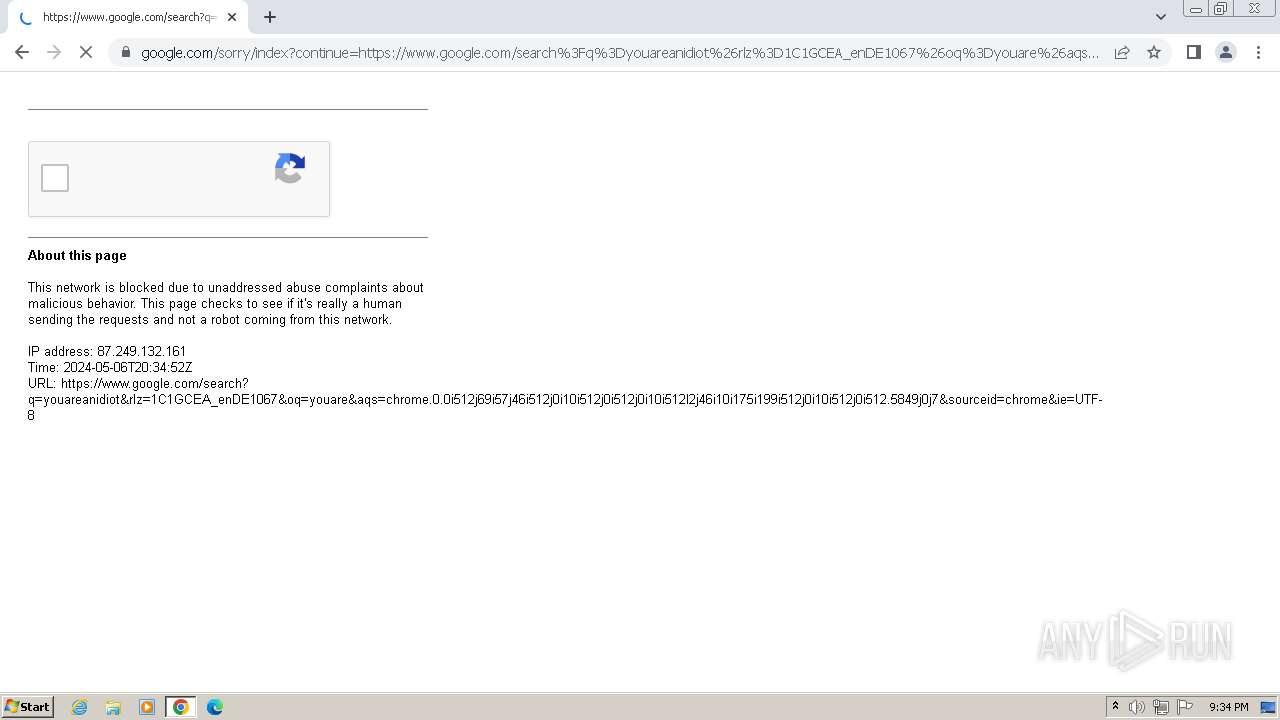
| URL: | hurr-durr.cc |
| Full analysis: | https://app.any.run/tasks/694ea0a4-a0c6-43fc-91e4-5621f5269c38 |
| Verdict: | Malicious activity |
| Analysis date: | May 06, 2024, 20:32:11 |
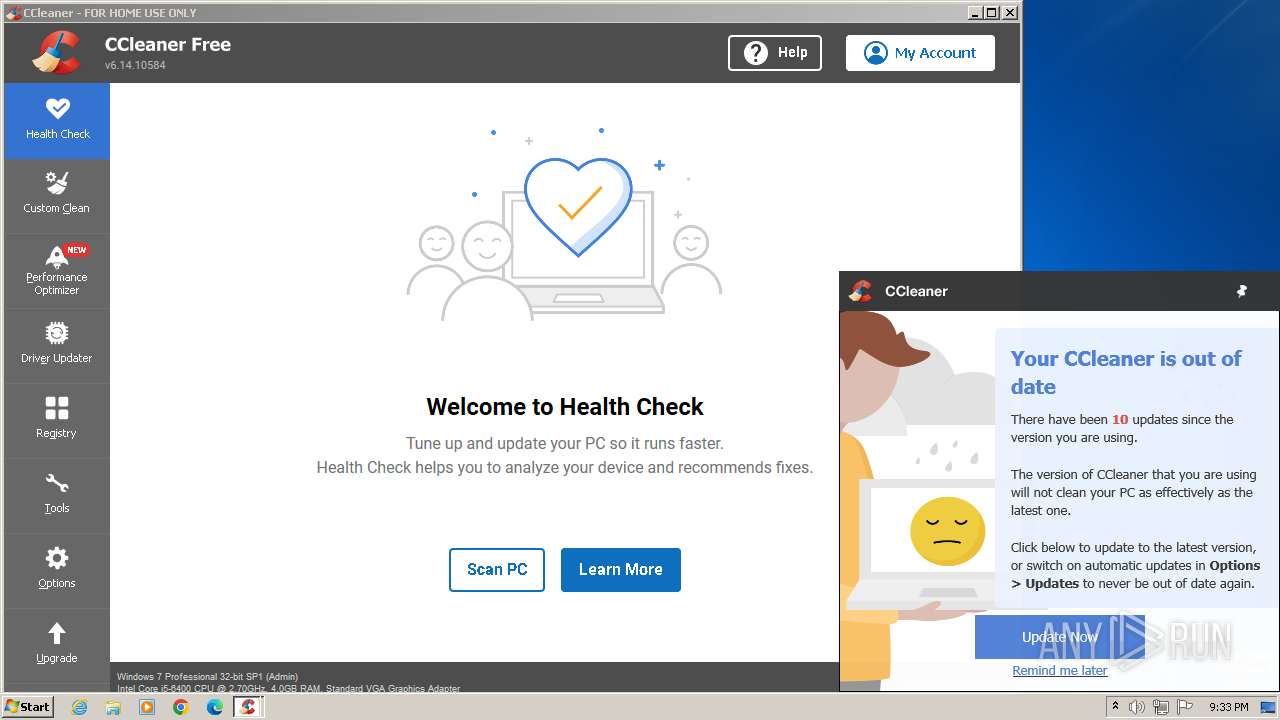
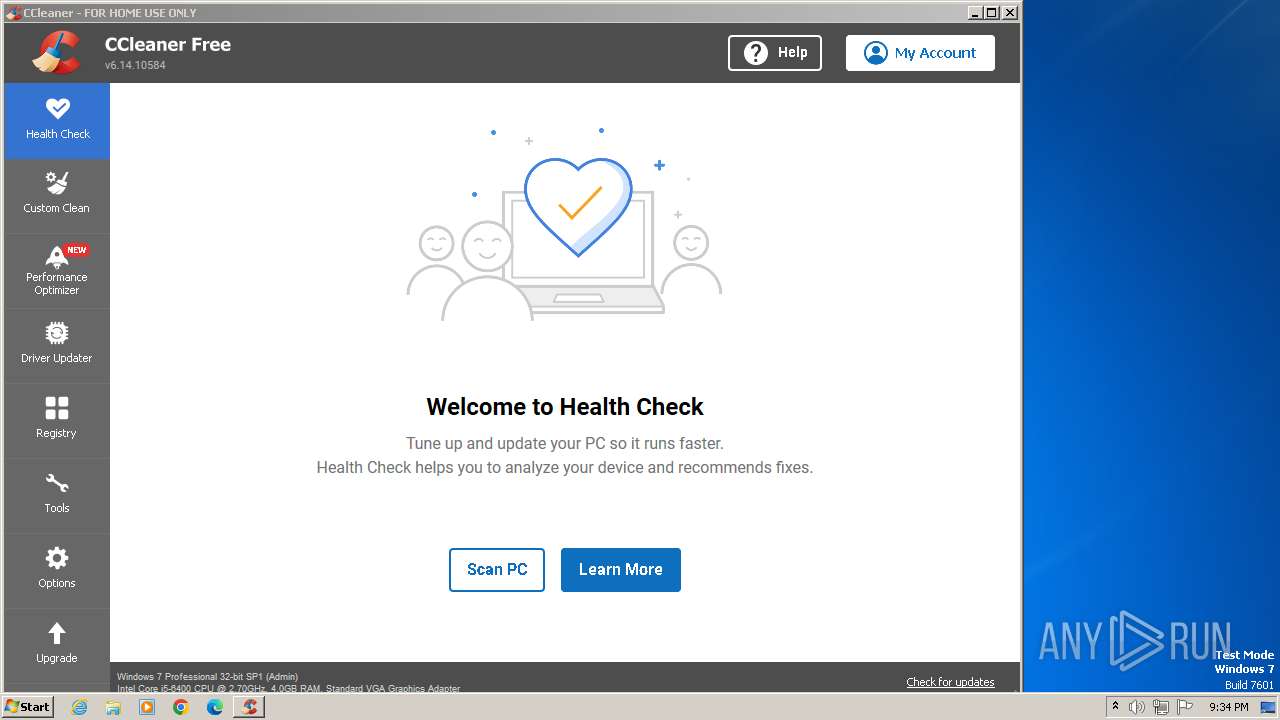
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 8A0CD526FDAFB5285BDB2D9B13B4687E |
| SHA1: | D5E5EC1513B04720612111753EF2081868E157EA |
| SHA256: | 7E4A1F20FBF9F4F6BA7E5F715B81FE1758FB23A0A180AD38BB9FF47347BCD022 |
| SSDEEP: | 3:nBCXV:BM |
MALICIOUS
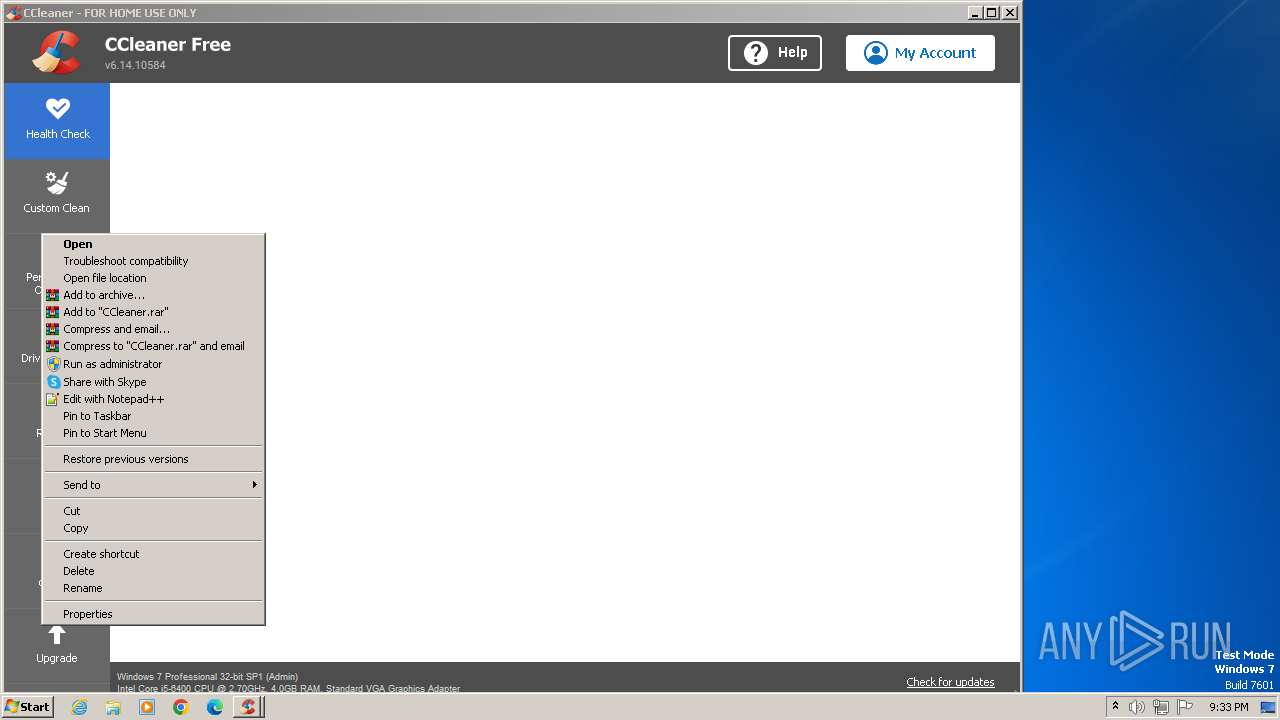
Actions looks like stealing of personal data
- CCleaner.exe (PID: 1480)
- CCleaner.exe (PID: 1644)
Drops the executable file immediately after the start
- CCleaner.exe (PID: 1480)
- CCleaner.exe (PID: 1644)
Steals credentials from Web Browsers
- CCleaner.exe (PID: 1480)
- taskhost.exe (PID: 588)
- taskhost.exe (PID: 2236)
- taskhost.exe (PID: 2028)
- CCleaner.exe (PID: 1644)
SUSPICIOUS
The process executes via Task Scheduler
- CCleaner.exe (PID: 1480)
- CCleaner.exe (PID: 1644)
Reads Internet Explorer settings
- CCleaner.exe (PID: 1480)
- CCleaner.exe (PID: 1644)
Executable content was dropped or overwritten
- CCleaner.exe (PID: 1480)
- CCleaner.exe (PID: 1644)
Reads security settings of Internet Explorer
- CCleaner.exe (PID: 1480)
- CCleaner.exe (PID: 1644)
Checks Windows Trust Settings
- CCleaner.exe (PID: 1480)
- CCleaner.exe (PID: 1644)
Reads settings of System Certificates
- CCleaner.exe (PID: 1480)
- CCleaner.exe (PID: 1644)
Reads the date of Windows installation
- CCleaner.exe (PID: 1644)
- CCleaner.exe (PID: 1480)
Searches for installed software
- CCleaner.exe (PID: 1480)
- CCleaner.exe (PID: 1644)
Reads the Internet Settings
- CCleaner.exe (PID: 1480)
- CCleaner.exe (PID: 1644)
- taskhost.exe (PID: 588)
- taskhost.exe (PID: 2236)
Reads Microsoft Outlook installation path
- CCleaner.exe (PID: 1480)
- CCleaner.exe (PID: 1644)
The process verifies whether the antivirus software is installed
- CCleaner.exe (PID: 1644)
Executes as Windows Service
- taskhost.exe (PID: 588)
- taskhost.exe (PID: 2028)
- taskhost.exe (PID: 2236)
Starts application from unusual location
- CCleaner.exe (PID: 1644)
Reads browser cookies
- CCleaner.exe (PID: 1644)
INFO
Manual execution by a user
- wmpnscfg.exe (PID: 1940)
- CCleaner.exe (PID: 2700)
- CCleaner.exe (PID: 2760)
- chrome.exe (PID: 1792)
Checks supported languages
- wmpnscfg.exe (PID: 1940)
- CCleaner.exe (PID: 2700)
- CCleaner.exe (PID: 1480)
- CCleaner.exe (PID: 2760)
- CCleaner.exe (PID: 1644)
Reads the computer name
- wmpnscfg.exe (PID: 1940)
- CCleaner.exe (PID: 2700)
- CCleaner.exe (PID: 1480)
- CCleaner.exe (PID: 2760)
- CCleaner.exe (PID: 1644)
Application launched itself
- chrome.exe (PID: 3992)
- chrome.exe (PID: 1792)
Reads Environment values
- CCleaner.exe (PID: 2700)
- CCleaner.exe (PID: 1480)
- CCleaner.exe (PID: 2760)
- CCleaner.exe (PID: 1644)
Reads CPU info
- CCleaner.exe (PID: 1480)
- CCleaner.exe (PID: 1644)
Reads the machine GUID from the registry
- CCleaner.exe (PID: 1480)
- CCleaner.exe (PID: 1644)
Reads product name
- CCleaner.exe (PID: 1480)
- CCleaner.exe (PID: 1644)
Creates files in the program directory
- CCleaner.exe (PID: 1480)
- CCleaner.exe (PID: 1644)
Reads the software policy settings
- CCleaner.exe (PID: 1480)
- CCleaner.exe (PID: 1644)
Checks proxy server information
- CCleaner.exe (PID: 1644)
- CCleaner.exe (PID: 1480)
Creates files or folders in the user directory
- CCleaner.exe (PID: 1480)
- CCleaner.exe (PID: 1644)
- taskhost.exe (PID: 588)
- taskhost.exe (PID: 2236)
Create files in a temporary directory
- CCleaner.exe (PID: 1644)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
73
Monitored processes
32
Malicious processes
4
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 316 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=5 --mojo-platform-channel-handle=2032 --field-trial-handle=1128,i,4881350820338584677,3830941063281152851,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 552 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --first-renderer-process --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=6 --mojo-platform-channel-handle=2020 --field-trial-handle=1128,i,4881350820338584677,3830941063281152851,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 588 | "taskhost.exe" | C:\Windows\System32\taskhost.exe | services.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Host Process for Windows Tasks Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 748 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --gpu-preferences=UAAAAAAAAADgACAYAAAAAAAAAAAAAAAAAABgAAAAAAAwAAAAAAAAAAAAAAAQAAAAAAAAAAAAAAAAAAAAAAAAAEgAAAAAAAAASAAAAAAAAAAYAAAAAgAAABAAAAAAAAAAGAAAAAAAAAAQAAAAAAAAAAAAAAAOAAAAEAAAAAAAAAABAAAADgAAAAgAAAAAAAAACAAAAAAAAAA= --mojo-platform-channel-handle=1148 --field-trial-handle=1128,i,4881350820338584677,3830941063281152851,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 1064 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=network.mojom.NetworkService --lang=en-US --service-sandbox-type=none --disable-quic --mojo-platform-channel-handle=1284 --field-trial-handle=1128,i,4881350820338584677,3830941063281152851,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | chrome.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 1236 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" /prefetch:7 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad" --url=https://clients2.google.com/cr/report --annotation=channel= --annotation=plat=Win32 --annotation=prod=Chrome --annotation=ver=109.0.5414.120 --initial-client-data=0xc8,0xcc,0xd0,0x9c,0xd4,0x6e698b38,0x6e698b48,0x6e698b54 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Version: 109.0.5414.120 Modules
| |||||||||||||||
| 1244 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=storage.mojom.StorageService --lang=en-US --service-sandbox-type=service --disable-quic --mojo-platform-channel-handle=1592 --field-trial-handle=1164,i,6861507475960899274,8509674733791602308,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Version: 109.0.5414.120 Modules
| |||||||||||||||
| 1480 | "C:\Program Files\CCleaner\CCleaner.exe" /uac | C:\Program Files\CCleaner\CCleaner.exe | taskeng.exe | ||||||||||||
User: admin Company: Piriform Software Ltd Integrity Level: HIGH Description: CCleaner Exit code: 0 Version: 6.14.0.10584 Modules
| |||||||||||||||
| 1644 | "C:\Program Files\CCleaner\CCleaner.exe" /uac | C:\Program Files\CCleaner\CCleaner.exe | taskeng.exe | ||||||||||||
User: admin Company: Piriform Software Ltd Integrity Level: HIGH Description: CCleaner Exit code: 0 Version: 6.14.0.10584 Modules
| |||||||||||||||
| 1792 | "C:\Program Files\Google\Chrome\Application\chrome.exe" "--disable-features=OptimizationGuideModelDownloading,OptimizationHintsFetching,OptimizationTargetPrediction,OptimizationHints" | C:\Program Files\Google\Chrome\Application\chrome.exe | explorer.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Version: 109.0.5414.120 Modules
| |||||||||||||||
Total events
60 150
Read events
59 372
Write events
524
Delete events
254
Modification events
| (PID) Process: | (3992) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (3992) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (3992) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (3992) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (3992) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (3992) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (3992) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (3992) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (3992) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
| (PID) Process: | (3992) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | metricsid |
Value: | |||
Executable files
6
Suspicious files
175
Text files
81
Unknown types
10
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3992 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\commerce_subscription_db\LOG.old~RF10593d.TMP | — | |
MD5:— | SHA256:— | |||
| 3992 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3992 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Variations | binary | |
MD5:961E3604F228B0D10541EBF921500C86 | SHA256:F7B24F2EB3D5EB0550527490395D2F61C3D2FE74BB9CB345197DAD81B58B5FED | |||
| 3992 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\coupon_db\LOG.old~RF105ebc.TMP | — | |
MD5:— | SHA256:— | |||
| 3992 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\coupon_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3992 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old | text | |
MD5:456D3EF989973A7C218E338A6CFFAD25 | SHA256:75631D994431F254B94255C50038A3657BFC45D76FCE9D794D514E57CA678872 | |||
| 3992 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old | text | |
MD5:825B582C78EC88D54C215EFDF1EAD639 | SHA256:367995D01A8F13E5C30C79499F86B034775BFD009D83DC97635DE438D47DFA37 | |||
| 3992 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\metadata\LOG.old~RF105d74.TMP | text | |
MD5:4E2B7997F4C3647F8D1ADA88339BBBA5 | SHA256:C33226C460208AA10537A23CB5128FD887DCBAA335C7DC8BFFBE08A607CCFDF5 | |||
| 3992 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Local Storage\leveldb\LOG.old | text | |
MD5:FA25AF7098FC1571F24F200A9D105D58 | SHA256:4F40C87070B7A151FB241CCF36E7027AA703C15CA0ACB0A1759DA07B2C318574 | |||
| 3992 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\AutofillStrikeDatabase\LOG.old~RF1073f9.TMP | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
47
TCP/UDP connections
73
DNS requests
74
Threats
9
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1480 | CCleaner.exe | GET | 304 | 199.232.214.172:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?ff635b2c4430f9d1 | unknown | — | — | unknown |
1480 | CCleaner.exe | GET | 200 | 104.102.251.170:80 | http://ncc.avast.com/ncc.txt | unknown | — | — | unknown |
1480 | CCleaner.exe | GET | 304 | 199.232.214.172:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?c5d938c1cfce3db5 | unknown | — | — | unknown |
1644 | CCleaner.exe | GET | 200 | 104.102.251.170:80 | http://ncc.avast.com/ncc.txt | unknown | — | — | unknown |
1644 | CCleaner.exe | GET | 304 | 199.232.210.172:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?0fd0ec3a00f29d70 | unknown | — | — | unknown |
1644 | CCleaner.exe | GET | 304 | 199.232.210.172:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?f941e12b1496751b | unknown | — | — | unknown |
1480 | CCleaner.exe | GET | 304 | 199.232.210.172:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?9f1f1c87e75cba72 | unknown | — | — | unknown |
1644 | CCleaner.exe | GET | 304 | 199.232.210.172:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?f70a5b6d633649d3 | unknown | — | — | unknown |
1644 | CCleaner.exe | GET | 200 | 216.58.212.131:80 | http://ocsp.pki.goog/gsr1/MFEwTzBNMEswSTAJBgUrDgMCGgUABBS3V7W2nAf4FiMTjpDJKg6%2BMgGqMQQUYHtmGkUNl8qJUC99BM00qP%2F8%2FUsCEHe9DWzbNvka6iEPxPBY0w0%3D | unknown | — | — | unknown |
1644 | CCleaner.exe | GET | 200 | 216.58.212.131:80 | http://ocsp.pki.goog/gtsr1/ME4wTDBKMEgwRjAJBgUrDgMCGgUABBQwkcLWD4LqGJ7bE7B1XZsEbmfwUAQU5K8rJnEaK0gnhS9SZizv8IkTcT4CDQIAjrICMzZli2TN25s%3D | unknown | — | — | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1064 | chrome.exe | 74.125.133.84:443 | accounts.google.com | GOOGLE | US | unknown |
3992 | chrome.exe | 239.255.255.250:1900 | — | — | — | unknown |
1064 | chrome.exe | 188.114.96.3:443 | hurr-durr.cc | CLOUDFLARENET | NL | unknown |
1064 | chrome.exe | 142.250.185.132:443 | www.google.com | GOOGLE | US | whitelisted |
3992 | chrome.exe | 224.0.0.251:5353 | — | — | — | unknown |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
1064 | chrome.exe | 35.190.80.1:443 | a.nel.cloudflare.com | GOOGLE | US | unknown |
1064 | chrome.exe | 142.250.185.234:443 | www.googleapis.com | GOOGLE | US | whitelisted |
1480 | CCleaner.exe | 104.102.251.170:80 | ncc.avast.com | Akamai International B.V. | US | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
hurr-durr.cc |
| unknown |
accounts.google.com |
| shared |
www.google.com |
| whitelisted |
a.nel.cloudflare.com |
| whitelisted |
www.googleapis.com |
| whitelisted |
ncc.avast.com |
| whitelisted |
analytics.ff.avast.com |
| whitelisted |
shepherd.ff.avast.com |
| whitelisted |
ip-info.ff.avast.com |
| whitelisted |
ipm-provider.ff.avast.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1064 | chrome.exe | Potentially Bad Traffic | ET DNS Query for .cc TLD |
1064 | chrome.exe | Potentially Bad Traffic | ET DNS Query for .cc TLD |
1064 | chrome.exe | Potentially Bad Traffic | ET DNS Query for .cc TLD |
1064 | chrome.exe | Potentially Bad Traffic | ET DNS Query for .cc TLD |
1064 | chrome.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare Network Error Logging (NEL) |
1088 | svchost.exe | Misc activity | ET INFO External IP Lookup Service in DNS Query (ip-info .ff .avast .com) |
1088 | svchost.exe | Misc activity | ET INFO External IP Lookup Service in DNS Query (ip-info .ff .avast .com) |
1480 | CCleaner.exe | Misc activity | ET INFO Observed External IP Lookup Domain (ip-info .ff .avast .com) in TLS SNI |
1644 | CCleaner.exe | Misc activity | ET INFO Observed External IP Lookup Domain (ip-info .ff .avast .com) in TLS SNI |
Process | Message |
|---|---|
CCleaner.exe | [2024-05-06 20:33:18.487] [error ] [settings ] [ 1480: 2400] [6000C4: 356] Failed to get program directory
Exception: Unable to determine program folder of product 'piriform-cc'!
Code: 0x000000c0 (192)
|
CCleaner.exe | Failed to open log file 'C:\Program Files\CCleaner' |
CCleaner.exe | OnLanguage - en
|
CCleaner.exe | [2024-05-06 20:33:20.159] [error ] [settings ] [ 1480: 2668] [9434E9: 359] Failed to get program directory
Exception: Unable to determine program folder of product 'piriform-cc'!
Code: 0x000000c0 (192)
|
CCleaner.exe | [2024-05-06 20:33:20.175] [error ] [Burger ] [ 1480: 2668] [FDA25D: 244] [23.1.806.0] [BurgerReporter.cpp] [244] asw::standalone_svc::BurgerReporter::BurgerSwitch: Could not read property BURGER_SETTINGS_PANCAKE_HOSTNAME (0x00000003)
|
CCleaner.exe | [2024-05-06 20:33:20.175] [error ] [Burger ] [ 1480: 2668] [FDA25D: 244] [23.1.806.0] [BurgerReporter.cpp] [244] asw::standalone_svc::BurgerReporter::BurgerSwitch: Could not read property BURGER_SETTINGS_PANCAKE_HOSTNAME (0x00000003)
|
CCleaner.exe | [2024-05-06 20:33:20.222] [error ] [settings ] [ 1644: 2740] [6000C4: 356] Failed to get program directory
Exception: Unable to determine program folder of product 'piriform-cc'!
Code: 0x000000c0 (192)
|
CCleaner.exe | Failed to open log file 'C:\Program Files\CCleaner' |
CCleaner.exe | OnLanguage - en
|
CCleaner.exe | [2024-05-06 20:33:20.800] [error ] [settings ] [ 1644: 2824] [9434E9: 359] Failed to get program directory
Exception: Unable to determine program folder of product 'piriform-cc'!
Code: 0x000000c0 (192)
|