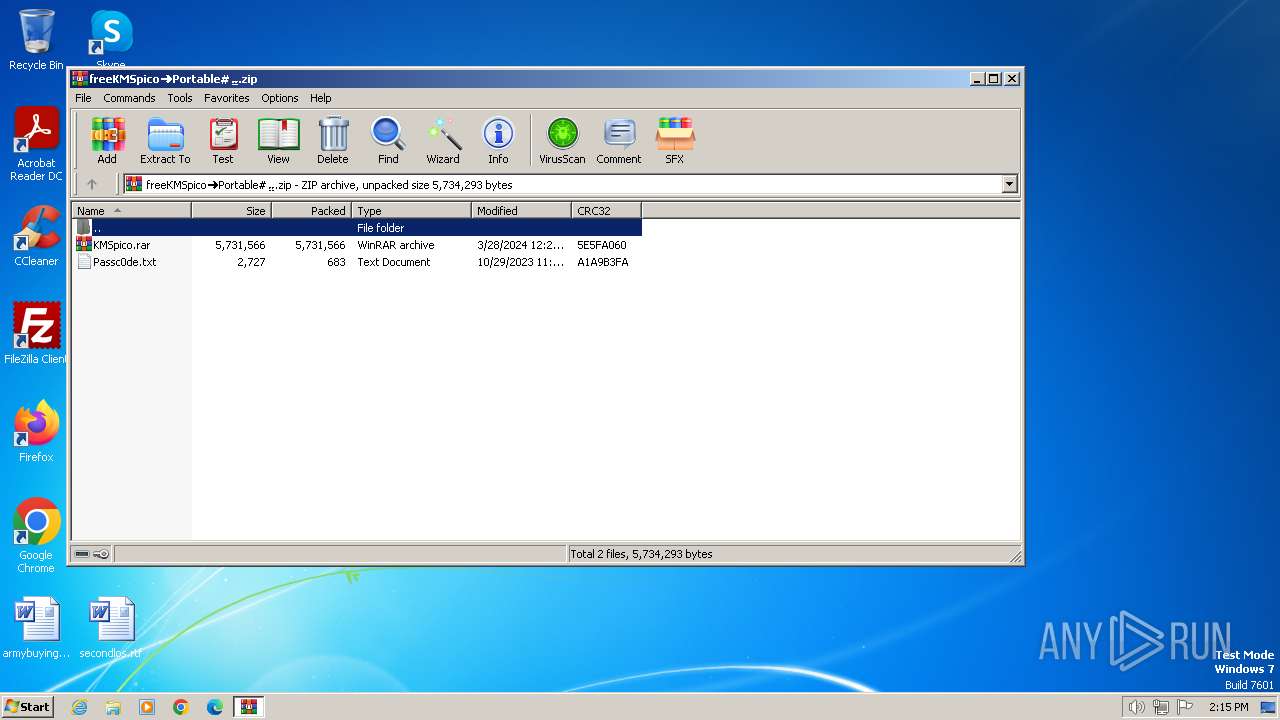
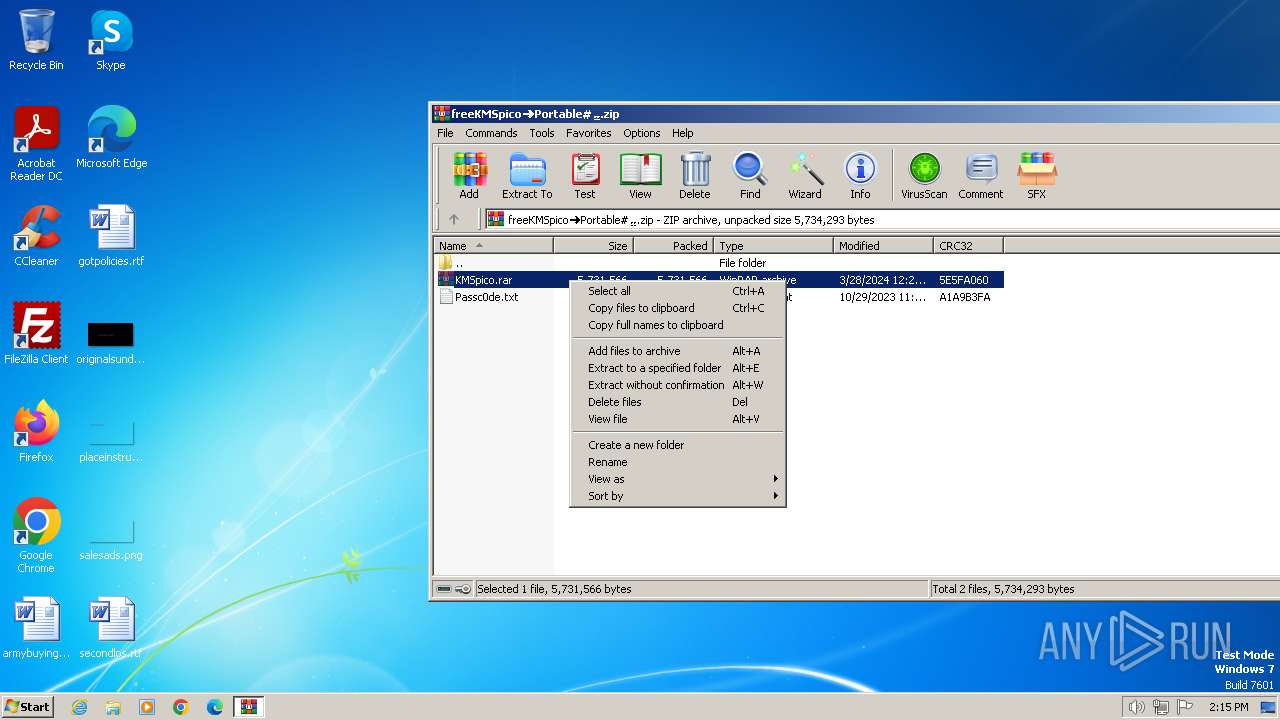
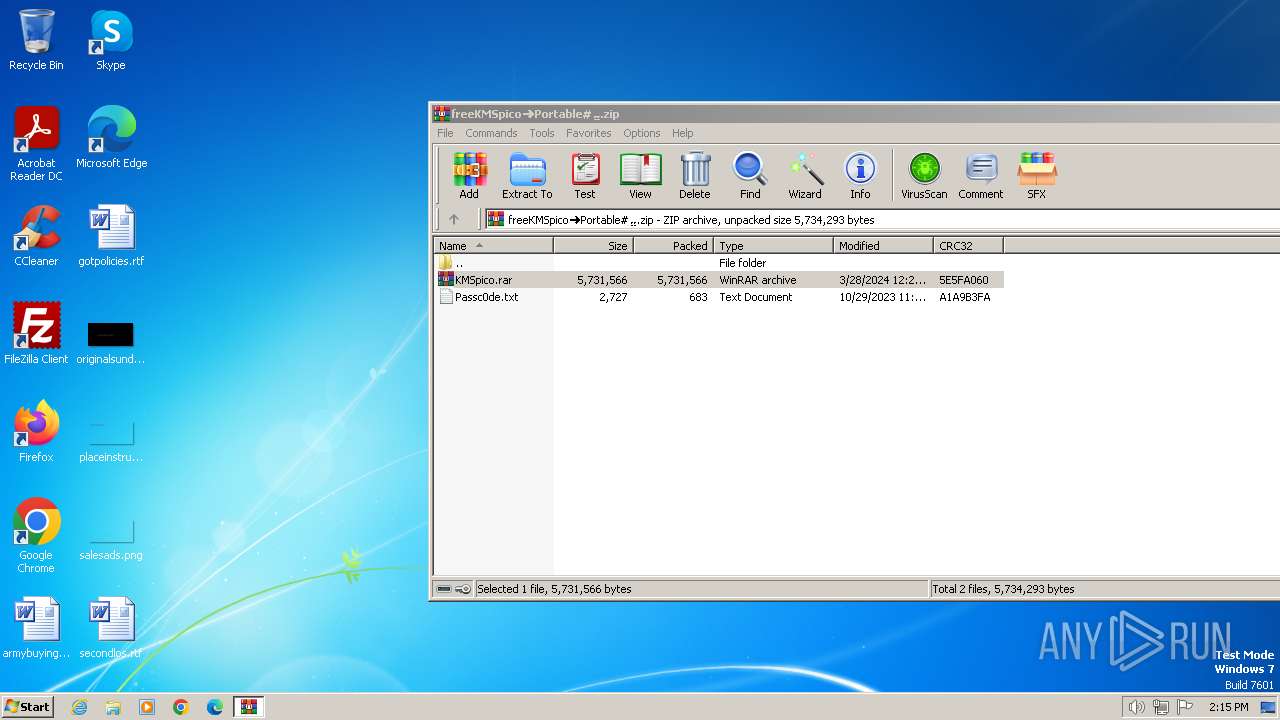
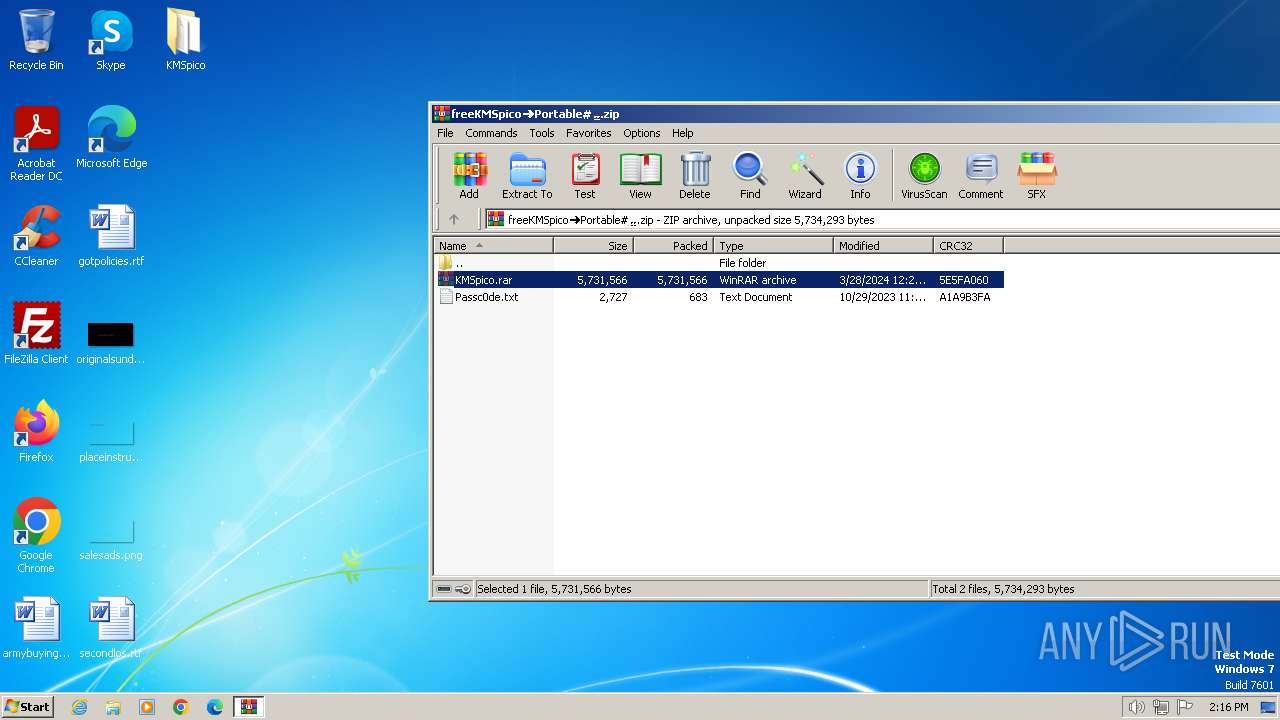
| File name: | frееКMSpico➜Portable#⣤.zip |
| Full analysis: | https://app.any.run/tasks/3808c69f-bc44-4a26-a6e1-a337929fea37 |
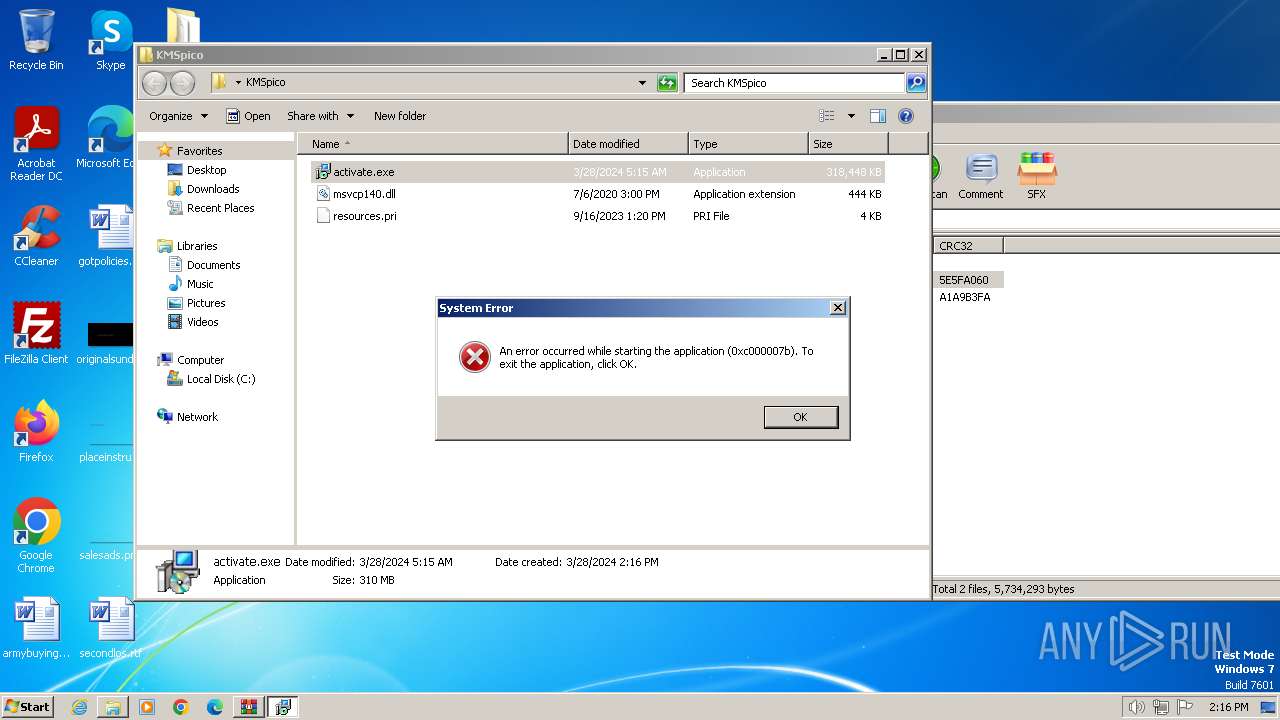
| Verdict: | Malicious activity |
| Analysis date: | March 28, 2024, 14:15:31 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v1.0 to extract, compression method=store |
| MD5: | DF1AB606A179EFE52F18FAFDBF14D787 |
| SHA1: | E2F44366906572D0C3DDC2BE56226EEA0A8E0750 |
| SHA256: | 7E4979445F16BD11D0C07B12375BD0A6958441F1772E3516BB0E3622F429842C |
| SSDEEP: | 98304:sjajAtU0/9RVoyllmRLZbgeKcJivMjVj2rBXpQspZoJqjWx4ISDM7EOFSEib+4cC:5kyYXhOwEYEon |
MALICIOUS
Actions looks like stealing of personal data
- activate.exe (PID: 3180)
SUSPICIOUS
Application launched itself
- WinRAR.exe (PID: 2120)
Process drops legitimate windows executable
- WinRAR.exe (PID: 2648)
Reads security settings of Internet Explorer
- WinRAR.exe (PID: 2120)
- activate.exe (PID: 3180)
Searches for installed software
- activate.exe (PID: 3180)
Reads browser cookies
- activate.exe (PID: 3180)
Reads the Internet Settings
- activate.exe (PID: 3180)
Starts CMD.EXE for commands execution
- activate.exe (PID: 3180)
INFO
Reads the computer name
- wmpnscfg.exe (PID: 1824)
- activate.exe (PID: 3180)
Checks supported languages
- wmpnscfg.exe (PID: 1824)
- activate.exe (PID: 3180)
- activate.exe (PID: 2148)
Manual execution by a user
- wmpnscfg.exe (PID: 1824)
- activate.exe (PID: 3180)
- rundll32.exe (PID: 2152)
- activate.exe (PID: 2148)
- activate.exe (PID: 1340)
Drops the executable file immediately after the start
- WinRAR.exe (PID: 2648)
- expand.exe (PID: 2432)
Creates files or folders in the user directory
- activate.exe (PID: 3180)
- expand.exe (PID: 2432)
Reads CPU info
- activate.exe (PID: 3180)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 10 |
|---|---|
| ZipBitFlag: | - |
| ZipCompression: | None |
| ZipModifyDate: | 2024:03:28 15:25:34 |
| ZipCRC: | 0x5e5fa060 |
| ZipCompressedSize: | 5731566 |
| ZipUncompressedSize: | 5731566 |
| ZipFileName: | KMSpico.rar |
Total processes
50
Monitored processes
11
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1236 | "C:\Windows\system32\cmd.exe" /c schtasks /create /tn \Service\Data /tr """"C:\Users\admin\AppData\Roaming\ServiceData\Davonevur.exe""" """C:\Users\admin\AppData\Roaming\ServiceData\Davonevur.jpg"""" /st 00:01 /du 9800:59 /sc once /ri 1 /f | C:\Windows\System32\cmd.exe | — | activate.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
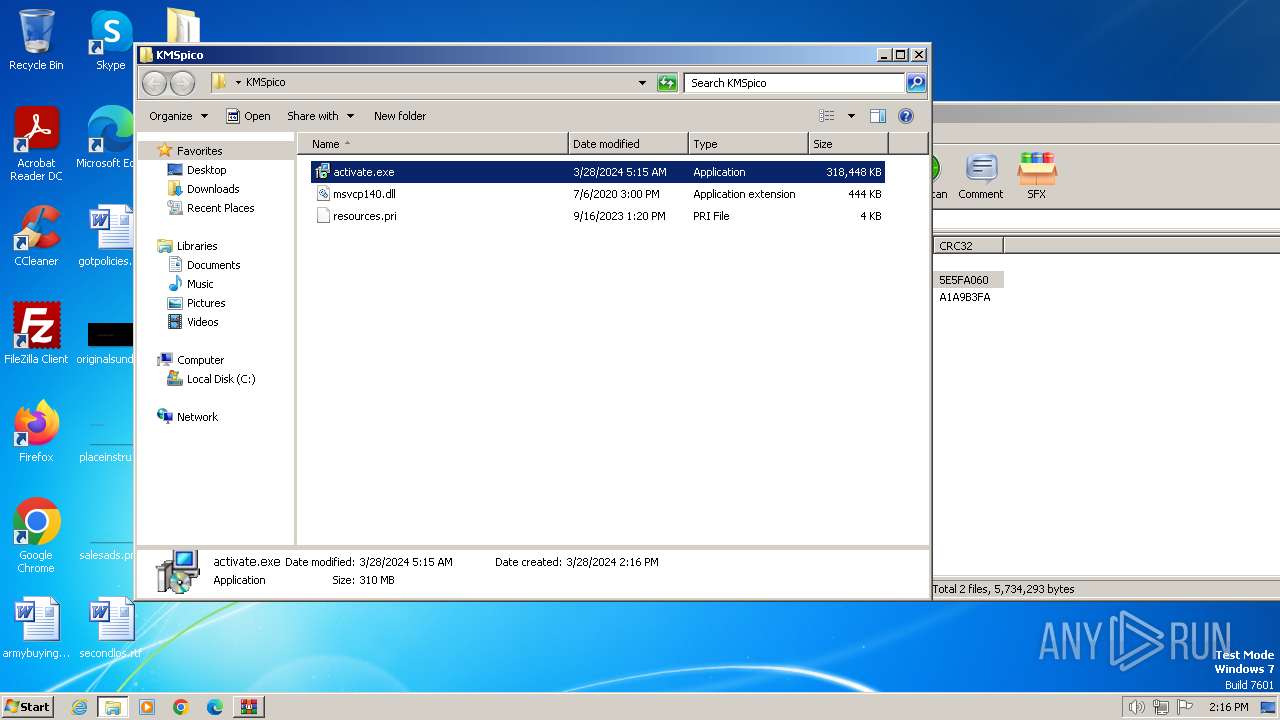
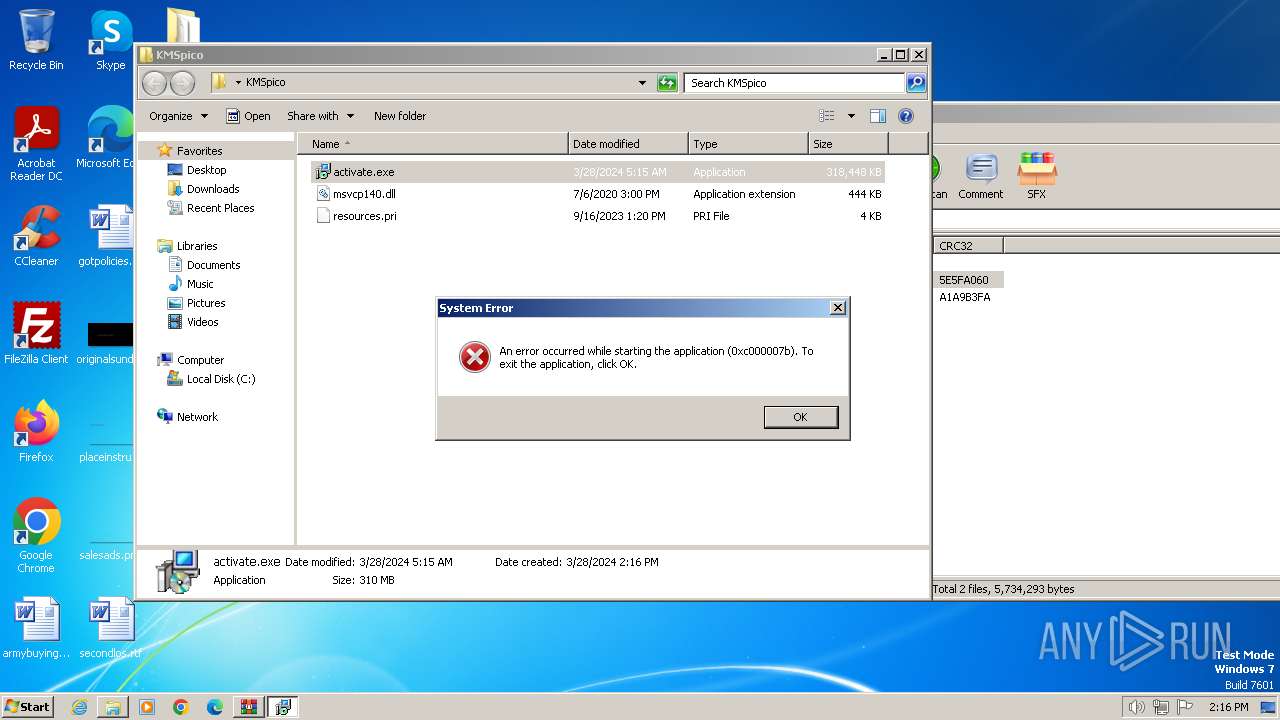
| 1340 | "C:\Users\admin\Desktop\KMSpico\activate.exe" | C:\Users\admin\Desktop\KMSpico\activate.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Modules
| |||||||||||||||
| 1824 | "C:\Program Files\Windows Media Player\wmpnscfg.exe" | C:\Program Files\Windows Media Player\wmpnscfg.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Media Player Network Sharing Service Configuration Application Exit code: 0 Version: 12.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2060 | schtasks /create /tn \Service\Data /tr """"C:\Users\admin\AppData\Roaming\ServiceData\Davonevur.exe""" """C:\Users\admin\AppData\Roaming\ServiceData\Davonevur.jpg"""" /st 00:01 /du 9800:59 /sc once /ri 1 /f | C:\Windows\System32\schtasks.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Manages scheduled tasks Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
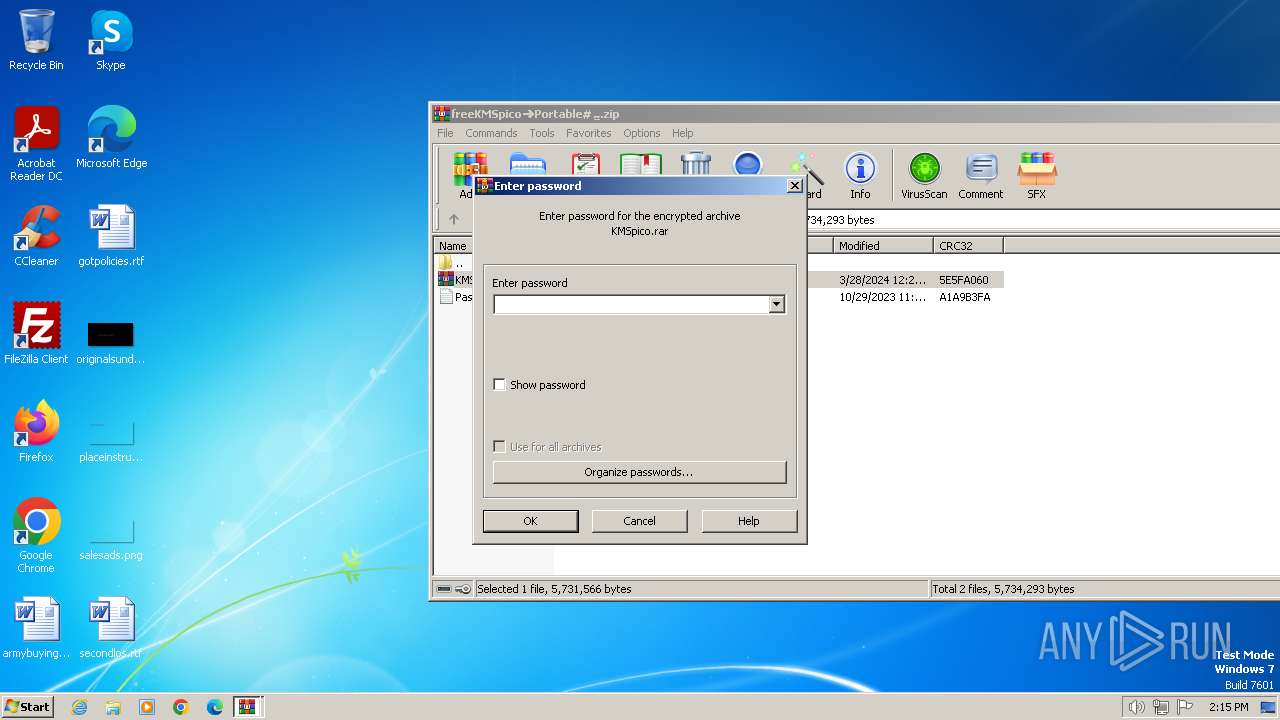
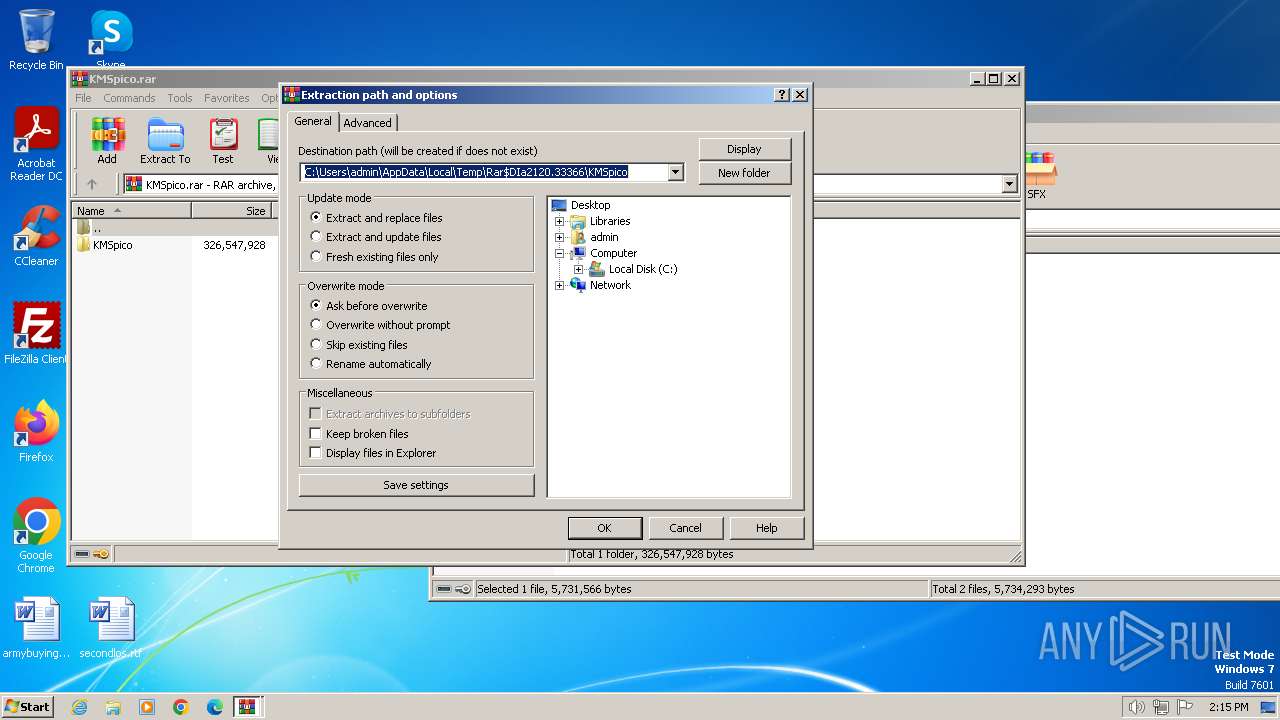
| 2120 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Temp\frееКMSpico➜Portable#⣤.zip" | C:\Program Files\WinRAR\WinRAR.exe | — | explorer.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Version: 5.91.0 Modules
| |||||||||||||||
| 2148 | "C:\Users\admin\Desktop\KMSpico\activate.exe" | C:\Users\admin\Desktop\KMSpico\activate.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
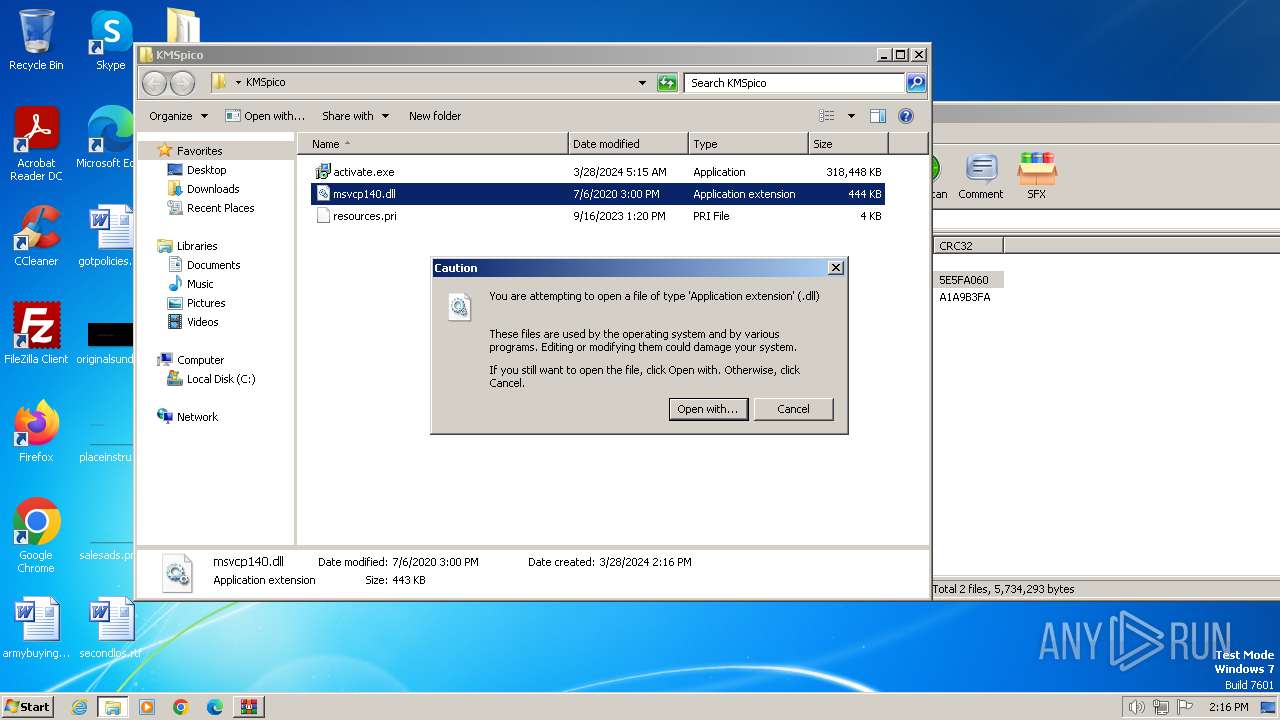
| 2152 | "C:\Windows\system32\rundll32.exe" C:\Windows\system32\shell32.dll,OpenAs_RunDLL C:\Users\admin\Desktop\KMSpico\msvcp140.dll | C:\Windows\System32\rundll32.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2432 | expand.exe "C:\Users\admin\AppData\Roaming\ServiceData\c2Gt4H.tmp" -F:* "C:\Users\admin\AppData\Roaming\ServiceData" | C:\Windows\System32\expand.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: LZ Expansion Utility Exit code: 0 Version: 6.1.7601.24535 (win7sp1_ldr_escrow.191105-1059) Modules
| |||||||||||||||
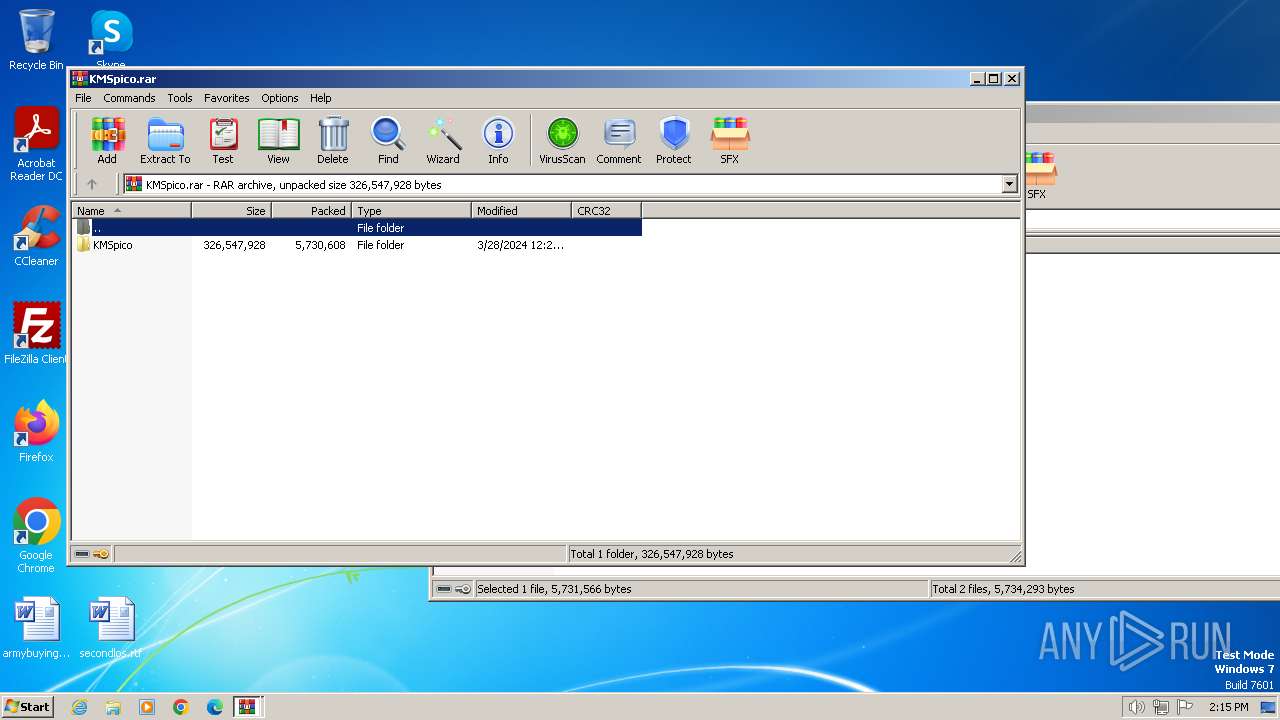
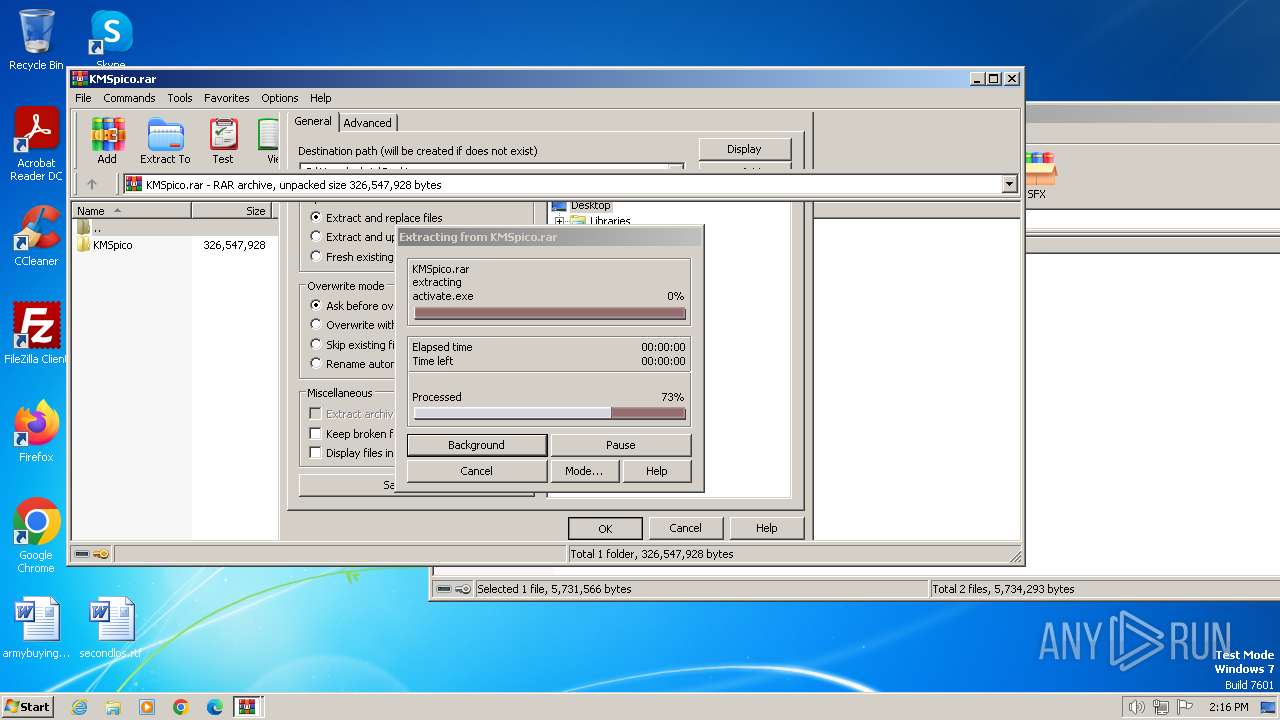
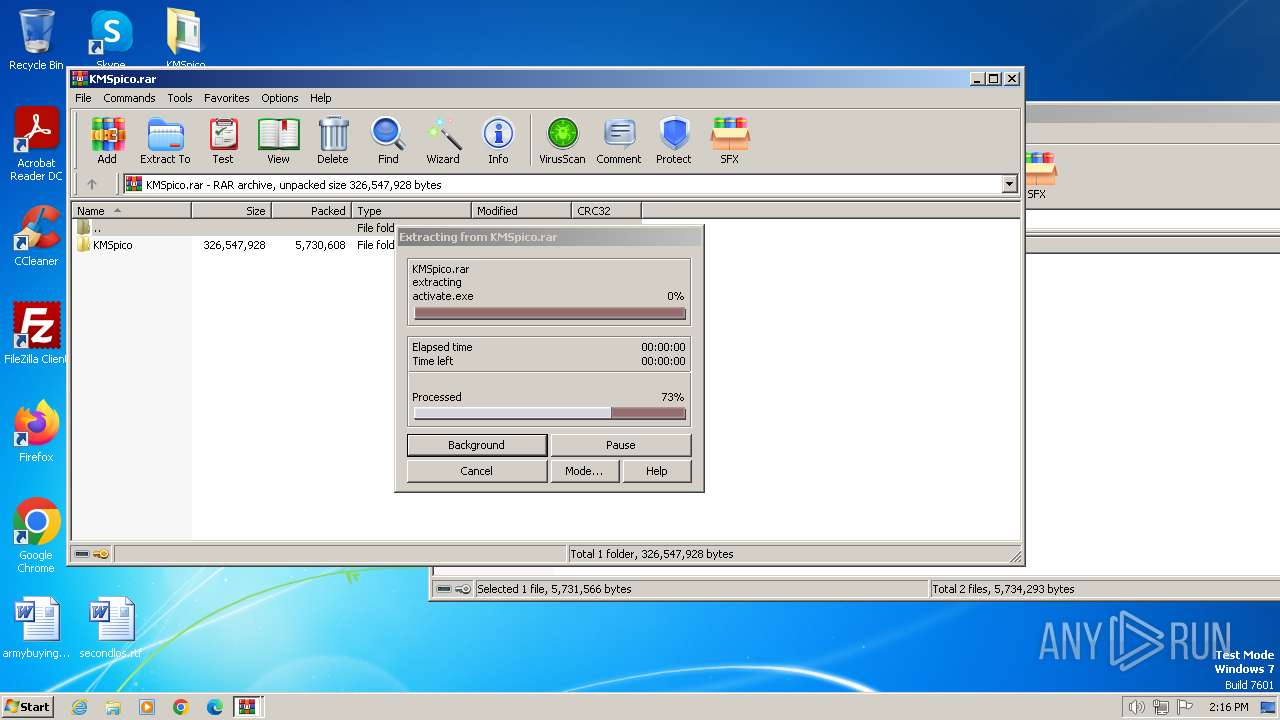
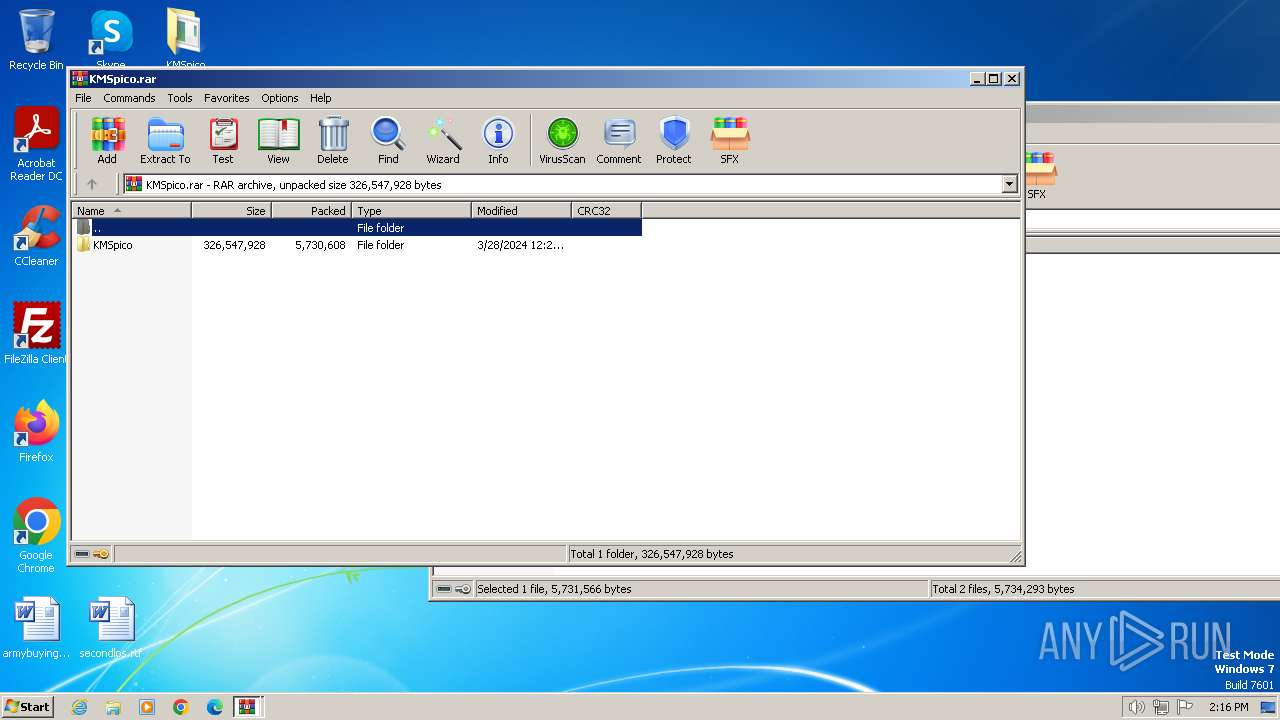
| 2648 | "C:\Program Files\WinRAR\WinRAR.exe" C:\Users\admin\AppData\Local\Temp\Rar$DIa2120.33366\KMSpico.rar | C:\Program Files\WinRAR\WinRAR.exe | — | WinRAR.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.91.0 Modules
| |||||||||||||||
| 3180 | "C:\Users\admin\Desktop\KMSpico\activate.exe" | C:\Users\admin\Desktop\KMSpico\activate.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
Total events
8 533
Read events
8 472
Write events
61
Delete events
0
Modification events
| (PID) Process: | (2120) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (2120) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (2120) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\182\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (2120) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 3 |
Value: C:\Users\admin\Desktop\phacker.zip | |||
| (PID) Process: | (2120) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\Win7-KB3191566-x86.zip | |||
| (PID) Process: | (2120) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\curl-8.5.0_1-win32-mingw.zip | |||
| (PID) Process: | (2120) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\frееКMSpico➜Portable#⣤.zip | |||
| (PID) Process: | (2120) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (2120) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (2120) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
Executable files
3
Suspicious files
2
Text files
2
Unknown types
0
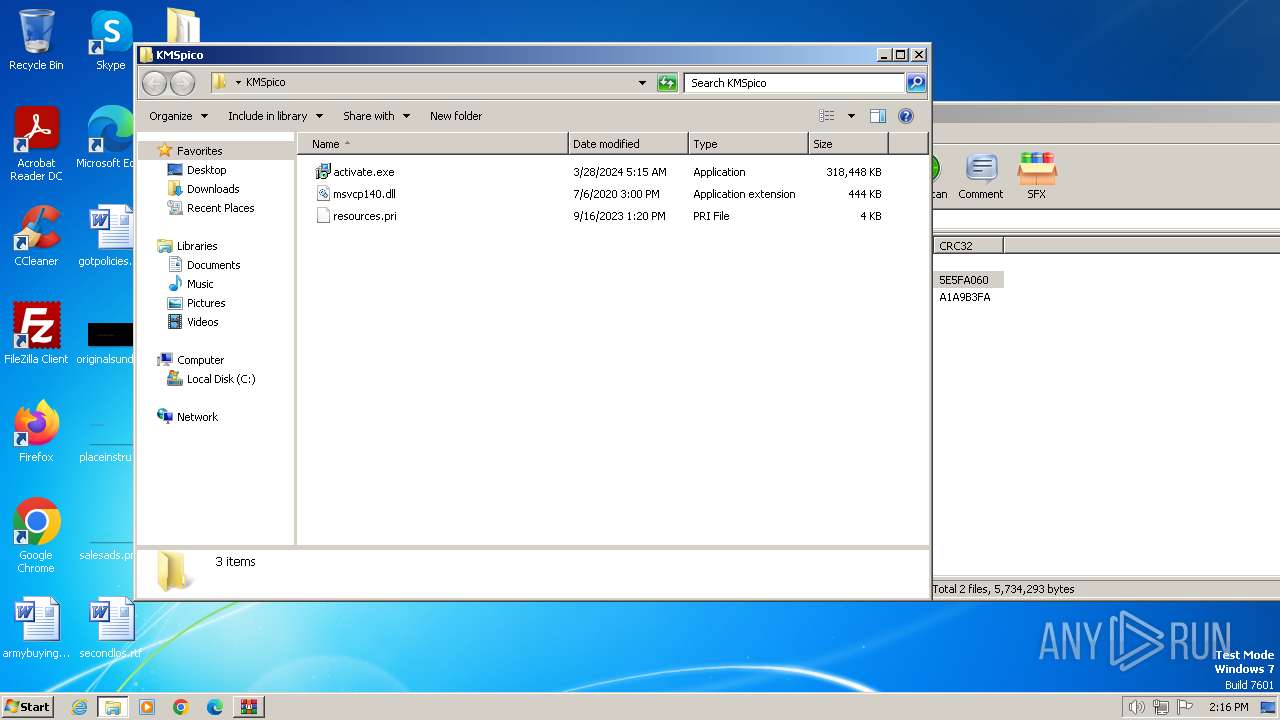
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2120 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DIa2120.33366\KMSpico.rar | — | |
MD5:— | SHA256:— | |||
| 2648 | WinRAR.exe | C:\Users\admin\Desktop\KMSpico\msvcp140.dll | executable | |
MD5:— | SHA256:— | |||
| 2648 | WinRAR.exe | C:\Users\admin\Desktop\KMSpico\resources.pri | binary | |
MD5:— | SHA256:— | |||
| 3180 | activate.exe | C:\Users\admin\AppData\Roaming\ServiceData\c2Gt4H.tmp | compressed | |
MD5:— | SHA256:— | |||
| 2432 | expand.exe | C:\Users\admin\AppData\Roaming\ServiceData\Davonevur.exe | executable | |
MD5:— | SHA256:— | |||
| 2432 | expand.exe | C:\Users\admin\AppData\Roaming\ServiceData\Davonevur.jpg | — | |
MD5:— | SHA256:— | |||
| 2432 | expand.exe | C:\Windows\Logs\DPX\setupact.log | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
3
TCP/UDP connections
8
DNS requests
1
Threats
5
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3180 | activate.exe | POST | 200 | 45.91.8.229:80 | http://bmseven7ht.top/upload.php | RU | text | 2 b | unknown |
3180 | activate.exe | POST | 200 | 45.91.8.229:80 | http://bmseven7ht.top/upload.php | RU | text | 2 b | unknown |
3180 | activate.exe | POST | 200 | 45.91.8.229:80 | http://bmseven7ht.top/upload.php | RU | text | 2 b | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 224.0.0.252:5355 | — | — | — | unknown |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
1080 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |
3180 | activate.exe | 45.91.8.229:80 | bmseven7ht.top | Sprinthost.ru LLC | RU | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
bmseven7ht.top |
| unknown |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1080 | svchost.exe | Potentially Bad Traffic | ET DNS Query to a *.top domain - Likely Hostile |
— | — | Potentially Bad Traffic | ET INFO HTTP Request to a *.top domain |
3 ETPRO signatures available at the full report