| File name: | AÐºÑ cвepки взaимopacÑeÑoв пo cocÑoÑÐ½Ð¸Ñ Ð½a 24.06.2025 гoдa.pdf.exe |
| Full analysis: | https://app.any.run/tasks/4202c583-a882-40f6-8d92-0396d4c2cb42 |
| Verdict: | Malicious activity |
| Analysis date: | June 30, 2025, 07:33:35 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32 executable (GUI) Intel 80386 Mono/.Net assembly, for MS Windows, 3 sections |
| MD5: | B0E54DDB1CBE04194B8101E35134B5D1 |
| SHA1: | 9D241A56877D672A19B9DC0B3574D41486E57DF2 |
| SHA256: | 7E2EFC2689F5D93877689C72246A6A632E0F642E7E7F0874920455D7D2ECB612 |
| SSDEEP: | 1536:9wgWZbIVzL6kHFjqEDV81vV/i6625ZOv+N6dTG/Du8TIs:U8kkHsUah5ZOvDdSD1X |
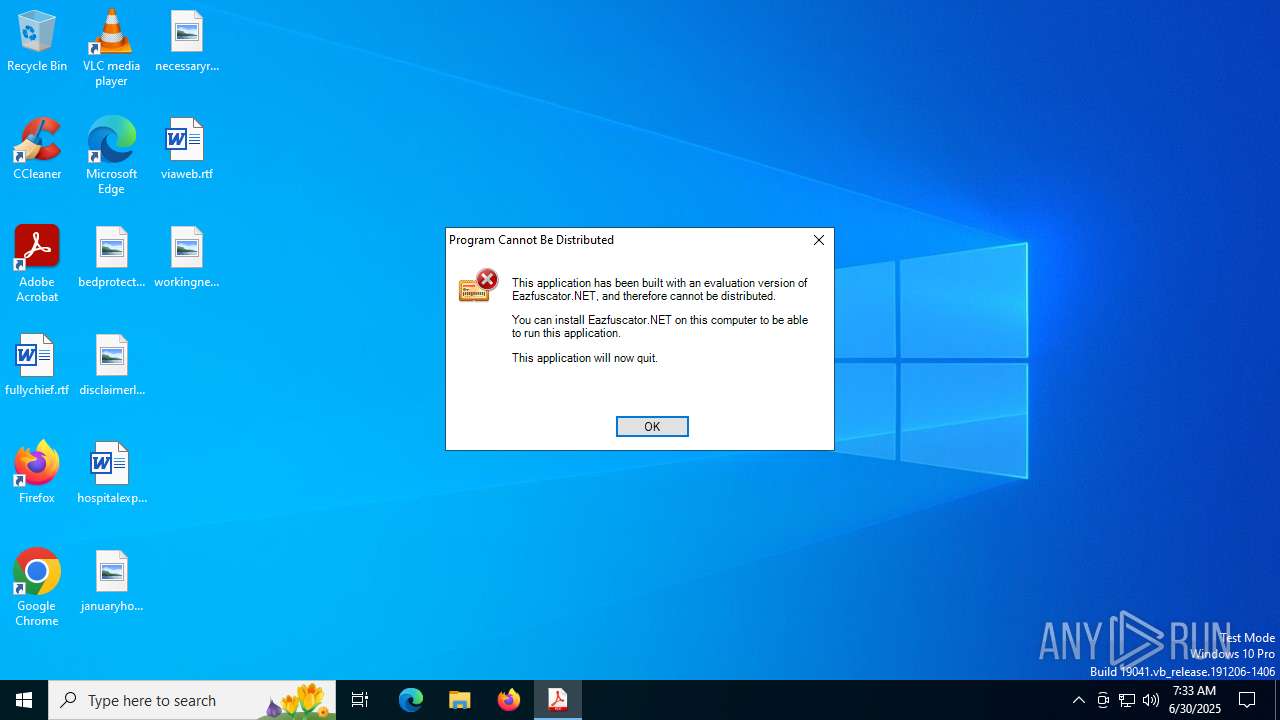
MALICIOUS
Executing a file with an untrusted certificate
- AÐºÑ cвepки взaимopacÑeÑoв пo cocÑoÑÐ½Ð¸Ñ Ð½a 24.06.2025 гoдa.pdf.exe (PID: 3400)
SUSPICIOUS
Reads security settings of Internet Explorer
- AÐºÑ cвepки взaимopacÑeÑoв пo cocÑoÑÐ½Ð¸Ñ Ð½a 24.06.2025 гoдa.pdf.exe (PID: 3400)
INFO
Reads the machine GUID from the registry
- AÐºÑ cвepки взaимopacÑeÑoв пo cocÑoÑÐ½Ð¸Ñ Ð½a 24.06.2025 гoдa.pdf.exe (PID: 3400)
Checks proxy server information
- AÐºÑ cвepки взaимopacÑeÑoв пo cocÑoÑÐ½Ð¸Ñ Ð½a 24.06.2025 гoдa.pdf.exe (PID: 3400)
- slui.exe (PID: 1828)
Checks supported languages
- AÐºÑ cвepки взaимopacÑeÑoв пo cocÑoÑÐ½Ð¸Ñ Ð½a 24.06.2025 гoдa.pdf.exe (PID: 3400)
Reads the computer name
- AÐºÑ cвepки взaимopacÑeÑoв пo cocÑoÑÐ½Ð¸Ñ Ð½a 24.06.2025 гoдa.pdf.exe (PID: 3400)
Reads the software policy settings
- AÐºÑ cвepки взaимopacÑeÑoв пo cocÑoÑÐ½Ð¸Ñ Ð½a 24.06.2025 гoдa.pdf.exe (PID: 3400)
- slui.exe (PID: 1828)
Creates files or folders in the user directory
- AÐºÑ cвepки взaимopacÑeÑoв пo cocÑoÑÐ½Ð¸Ñ Ð½a 24.06.2025 гoдa.pdf.exe (PID: 3400)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win64 Executable (generic) (64.6) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (15.4) |
| .exe | | | Win32 Executable (generic) (10.5) |
| .exe | | | Generic Win/DOS Executable (4.6) |
| .exe | | | DOS Executable Generic (4.6) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2025:06:24 08:48:22+00:00 |
| ImageFileCharacteristics: | Executable, No line numbers, No symbols, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 6 |
| CodeSize: | 36352 |
| InitializedDataSize: | 101888 |
| UninitializedDataSize: | - |
| EntryPoint: | 0xacee |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 8.9.6.3 |
| ProductVersionNumber: | 8.9.6.3 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Windows NT 32-bit |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Unicode |
| FileVersion: | 8.9.6.3 |
| ProductVersion: | 8.9.6.3 |
| FileDescription: | profext |
| CompanyName: | SyncController for managing sync of mail, contacts, calendar |
| LegalCopyright: | Copyright (C) 2004-2016 IDuXACoH9lWPct2LS8cqWzr1RnKBtDkssFXQ7SgQTLreyxP7wrstFaVmcoGsp3xlWE99ZI5IhHaF, Inc. All rights reserved. |
| ProductName: | |
| Comments: | gKdLbK14QmqnpRIff3Egy9ao7AlEc8iMPqRCoVVView9WwxVQgCt7fh |
| InternalName: | eudcedit.exe |
Total processes
139
Monitored processes
2
Malicious processes
0
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1828 | C:\WINDOWS\System32\slui.exe -Embedding | C:\Windows\System32\slui.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Activation Client Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3400 | "C:\Users\admin\AppData\Local\Temp\AÐºÑ cвepки взaимopacÑeÑoв пo cocÑoÑÐ½Ð¸Ñ Ð½a 24.06.2025 гoдa.pdf.exe" | C:\Users\admin\AppData\Local\Temp\AÐºÑ cвepки взaимopacÑeÑoв пo cocÑoÑÐ½Ð¸Ñ Ð½a 24.06.2025 гoдa.pdf.exe | explorer.exe | ||||||||||||
User: admin Company: SyncController for managing sync of mail, contacts, calendar Integrity Level: MEDIUM Description: profext Exit code: 0 Version: 8.9.6.3 Modules
| |||||||||||||||
Total events
4 113
Read events
4 113
Write events
0
Delete events
0
Modification events
Executable files
0
Suspicious files
2
Text files
0
Unknown types
2
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3400 | AÐºÑ cвepки взaимopacÑeÑoв пo cocÑoÑÐ½Ð¸Ñ Ð½a 24.06.2025 гoдa.pdf.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\9CB4373A4252DE8D2212929836304EC5_1AB74AA2E3A56E1B8AD8D3FEC287554E | der | |
MD5:929D65EB740FF4D23379A44E4E91DDCD | SHA256:4EA9B105AAAA2D10E83D1CD4212DAD668FA3509A7E2C670CF2A569B725360403 | |||
| 3400 | AÐºÑ cвepки взaимopacÑeÑoв пo cocÑoÑÐ½Ð¸Ñ Ð½a 24.06.2025 гoдa.pdf.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\357F04AD41BCF5FE18FCB69F60C6680F_E443B4F6C45CA27D3F7224E678C3DC74 | der | |
MD5:FDD26D6742F39EB5DE9C2AD1F222174F | SHA256:C263805628366B390054D9A282D394CF9335E111B183314414785461FD7685A2 | |||
| 3400 | AÐºÑ cвepки взaимopacÑeÑoв пo cocÑoÑÐ½Ð¸Ñ Ð½a 24.06.2025 гoдa.pdf.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\9CB4373A4252DE8D2212929836304EC5_1AB74AA2E3A56E1B8AD8D3FEC287554E | binary | |
MD5:86072E2DB97CF1D65AC0B81D599E4829 | SHA256:9C66F95360380C2E81D65B7D4A25547FC4D656F4F696D3AB2557F8047C440F27 | |||
| 3400 | AÐºÑ cвepки взaимopacÑeÑoв пo cocÑoÑÐ½Ð¸Ñ Ð½a 24.06.2025 гoдa.pdf.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\357F04AD41BCF5FE18FCB69F60C6680F_E443B4F6C45CA27D3F7224E678C3DC74 | binary | |
MD5:439F6BC22E30C91439CDECB8B569AE50 | SHA256:1DA24D372B3A44DEABFC02D02F436F5010B7B98930975F4BE8F2722238976412 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
8
TCP/UDP connections
25
DNS requests
18
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3400 | AÐºÑ cвepки взaимopacÑeÑoв пo cocÑoÑÐ½Ð¸Ñ Ð½a 24.06.2025 гoдa.pdf.exe | GET | 200 | 151.101.2.133:80 | http://ocsp.globalsign.com/codesigningrootr45/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQVFZP5vqhCrtRN5SWf40Rn6NM1IAQUHwC%2FRoAK%2FHg5t6W0Q9lWULvOljsCEHe9DgW3WQu2HUdhUx4%2Fde0%3D | US | binary | 1.67 Kb | whitelisted |
3400 | AÐºÑ cвepки взaимopacÑeÑoв пo cocÑoÑÐ½Ð¸Ñ Ð½a 24.06.2025 гoдa.pdf.exe | GET | 200 | 151.101.2.133:80 | http://ocsp.globalsign.com/gsgccr45evcodesignca2020/ME0wSzBJMEcwRTAJBgUrDgMCGgUABBQaCbVYh07WONuW4e63Ydlu4AlbDAQUJZ3Q%2FFkJhmPF7POxEztXHAOSNhECDEdHt7UkWrgED1V1Tw%3D%3D | US | binary | 1.65 Kb | whitelisted |
1268 | svchost.exe | GET | 200 | 23.216.77.28:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | DE | binary | 825 b | whitelisted |
1268 | svchost.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | DE | binary | 814 b | whitelisted |
2464 | svchost.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | DE | binary | 471 b | whitelisted |
4120 | SIHClient.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | NL | binary | 420 b | whitelisted |
4120 | SIHClient.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | NL | binary | 408 b | whitelisted |
2940 | svchost.exe | GET | 200 | 23.209.209.135:80 | http://x1.c.lencr.org/ | ID | binary | 734 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
5944 | MoUsoCoreWorker.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
3148 | RUXIMICS.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
1268 | svchost.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
3400 | AÐºÑ cвepки взaимopacÑeÑoв пo cocÑoÑÐ½Ð¸Ñ Ð½a 24.06.2025 гoдa.pdf.exe | 151.101.2.133:80 | ocsp.globalsign.com | FASTLY | US | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
1268 | svchost.exe | 23.216.77.28:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
1268 | svchost.exe | 184.30.21.171:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
2464 | svchost.exe | 20.190.159.71:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
2464 | svchost.exe | 2.17.190.73:80 | ocsp.digicert.com | AKAMAI-AS | DE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
google.com |
| whitelisted |
ocsp.globalsign.com |
| whitelisted |
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
nexusrules.officeapps.live.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |