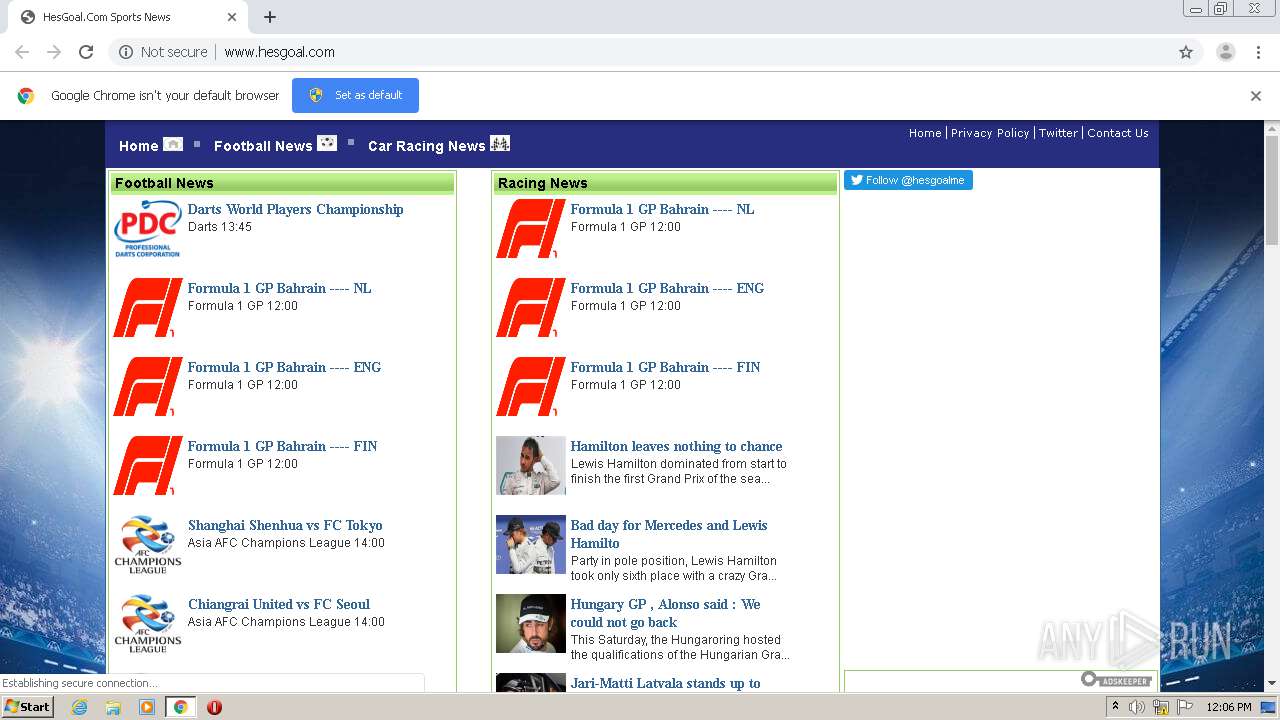
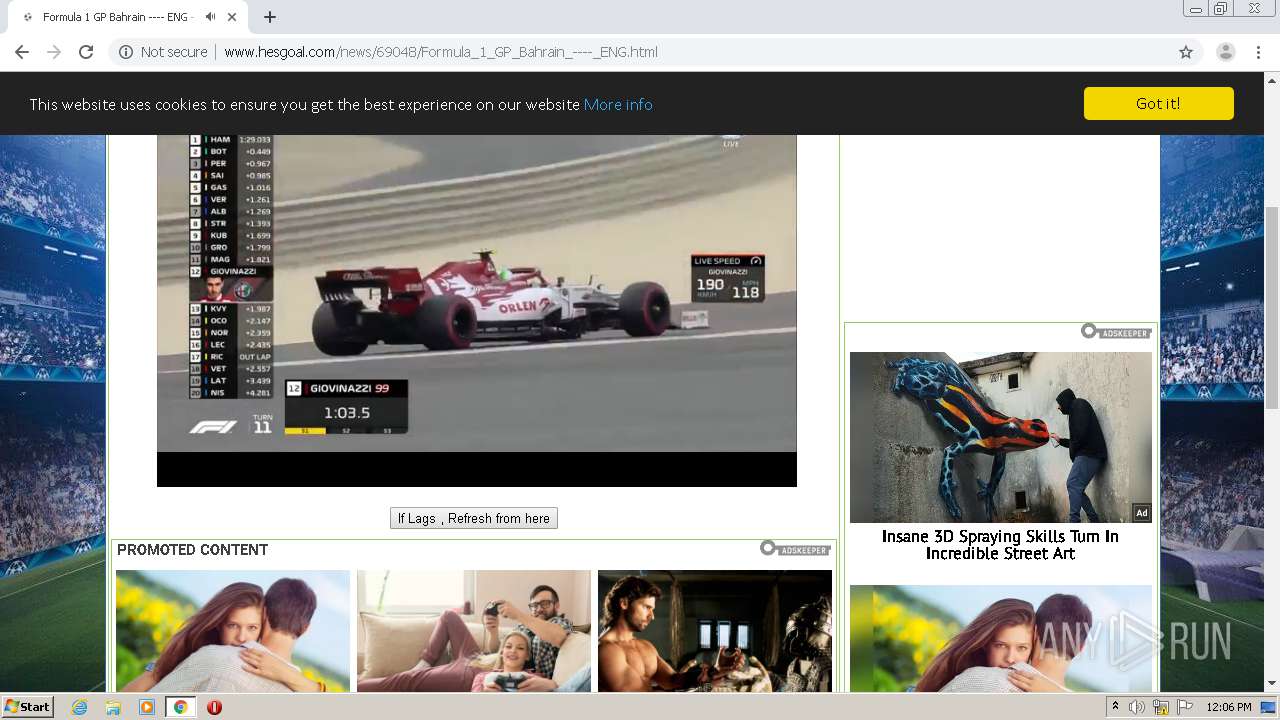
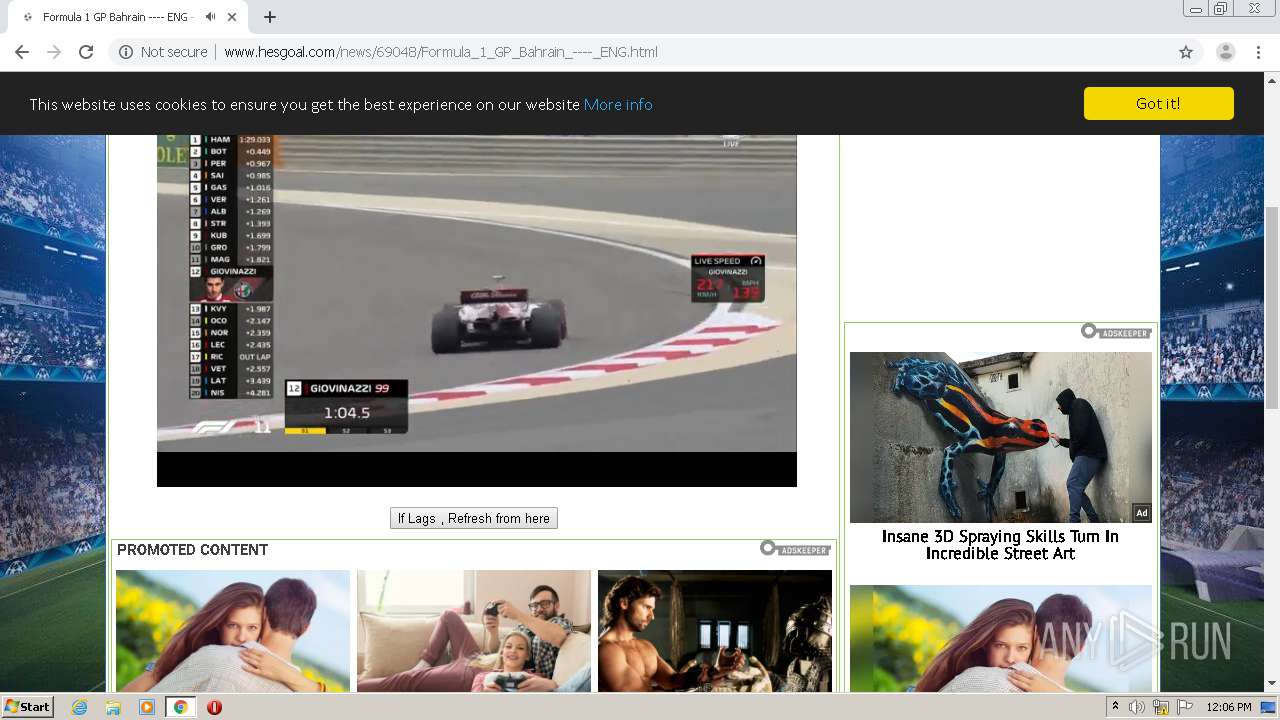
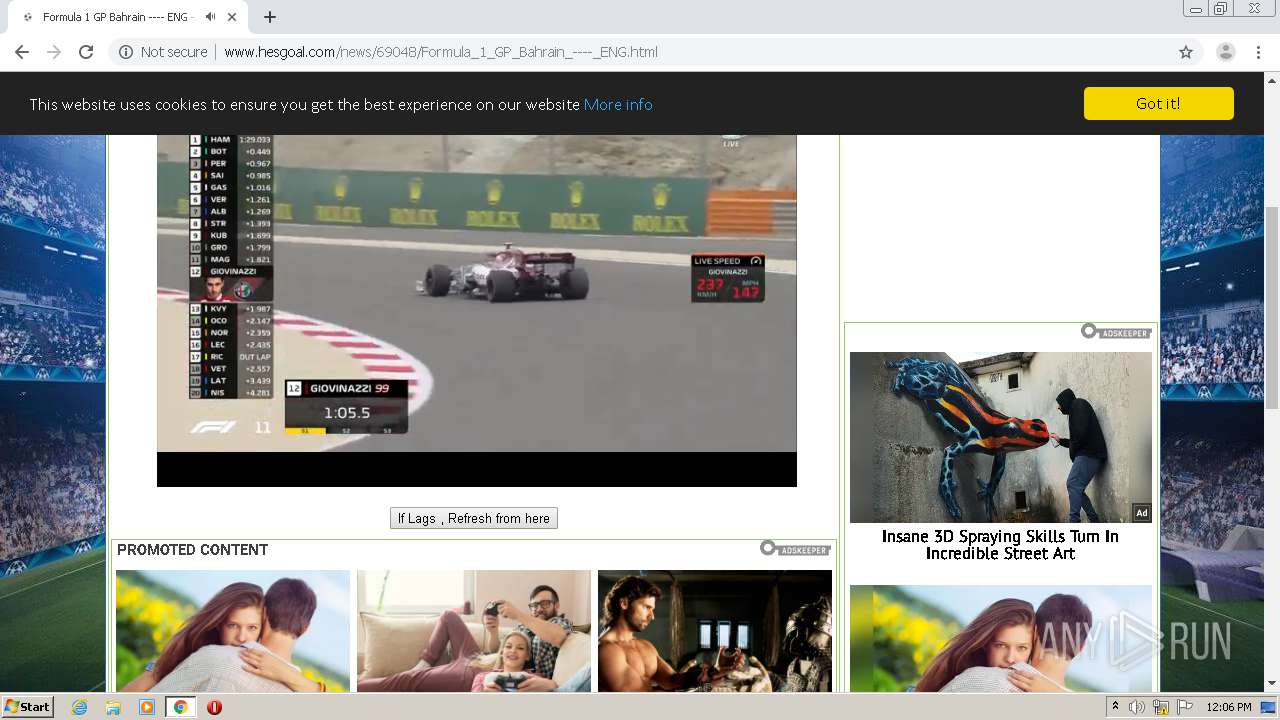
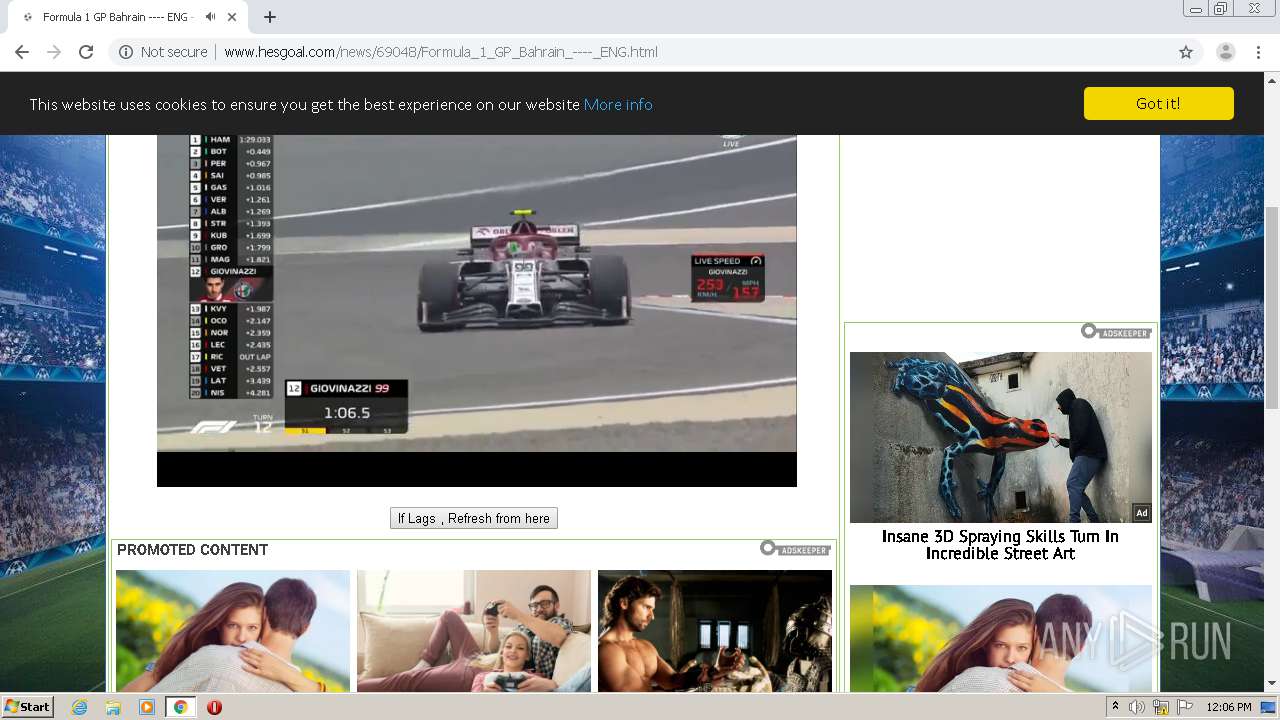
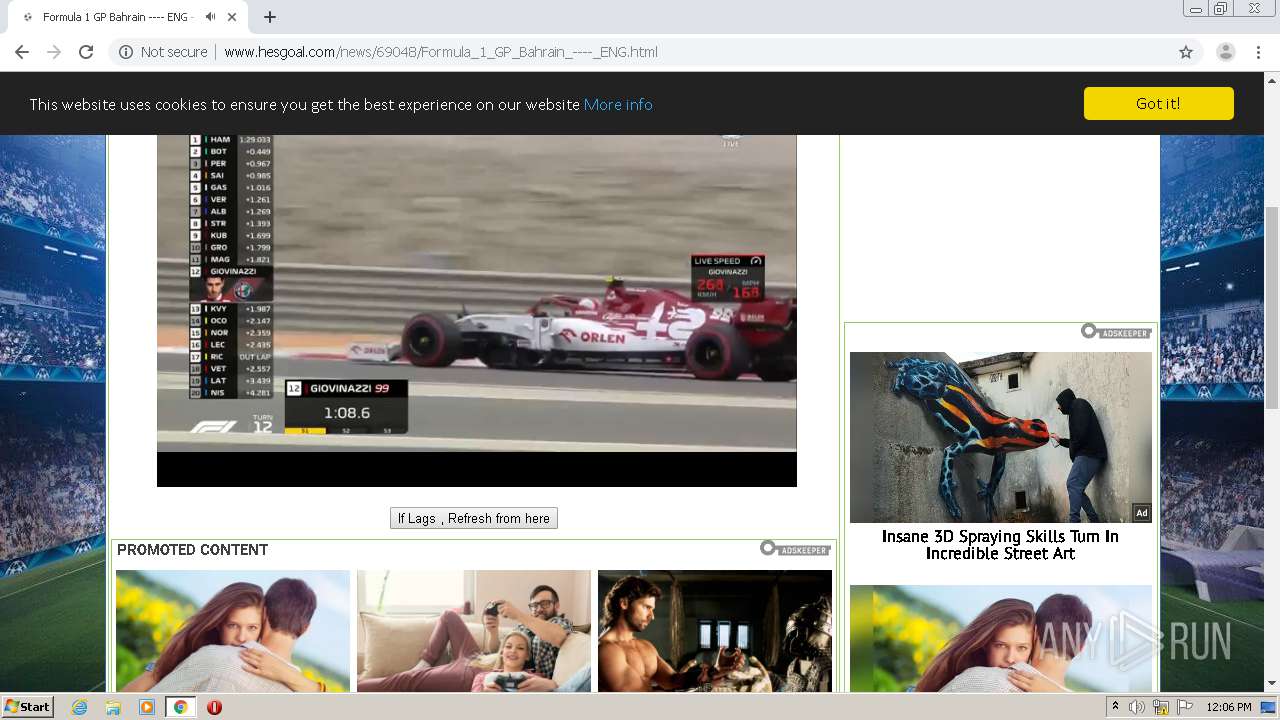
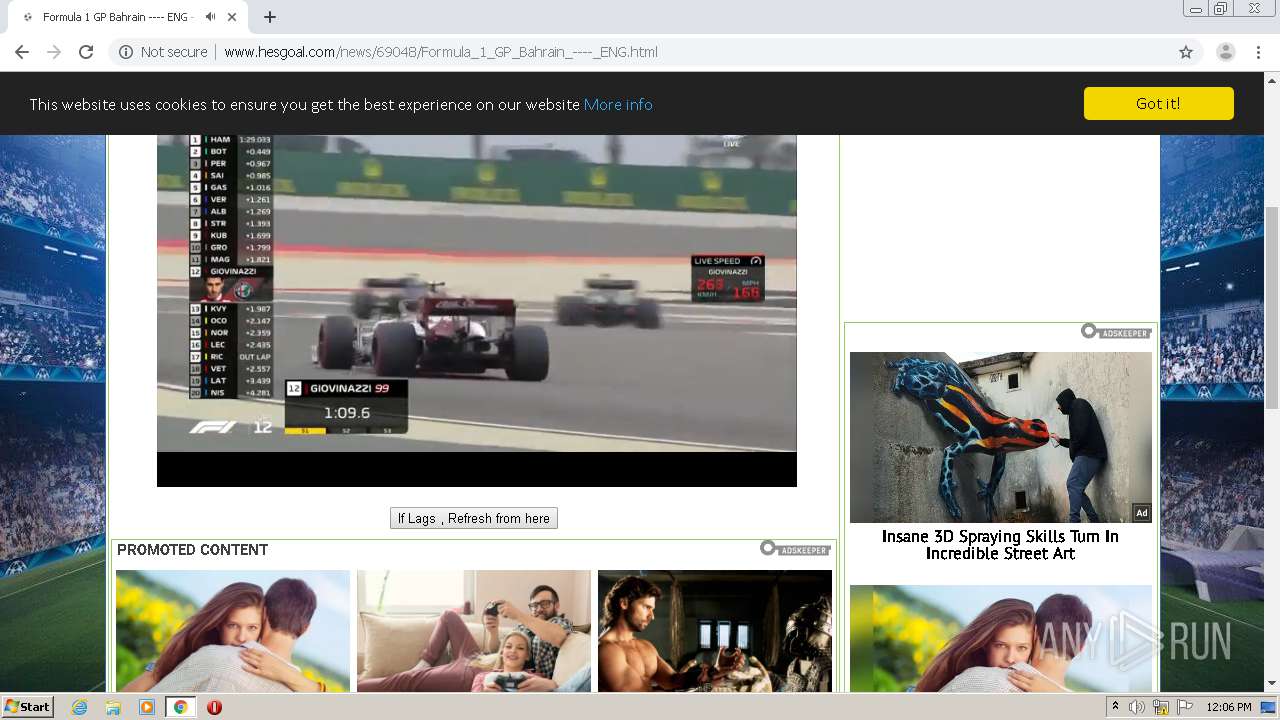
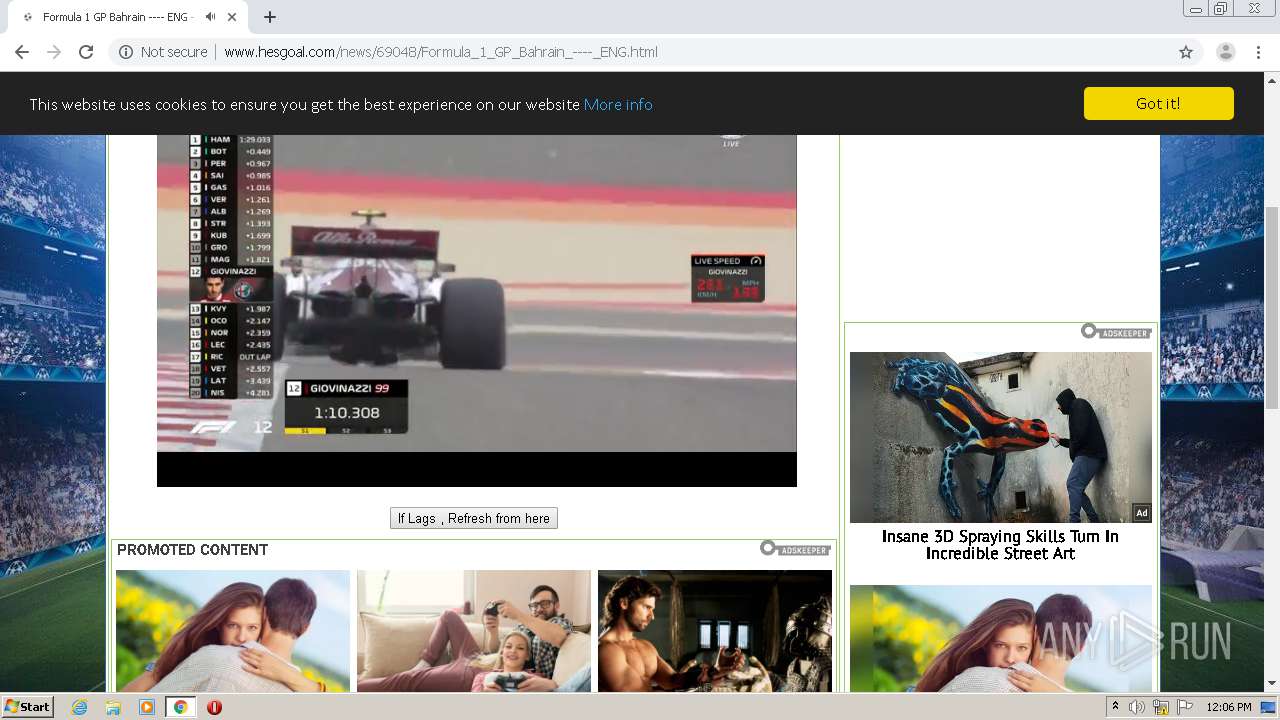
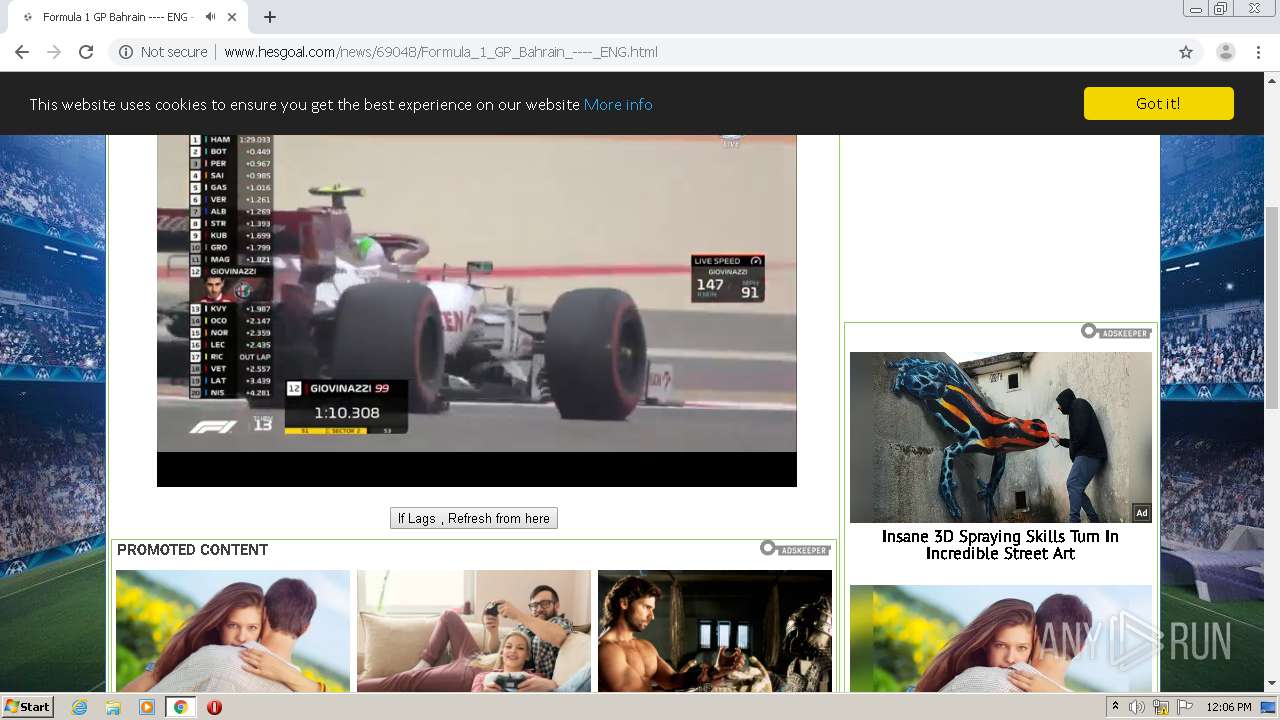
| URL: | http://www.hesgoal.com/ |
| Full analysis: | https://app.any.run/tasks/1276a0ef-f22e-42c4-a782-9654b59b368c |
| Verdict: | Malicious activity |
| Analysis date: | November 27, 2020, 12:05:49 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | CFBFBF87C08AF1F0D78425377384FD89 |
| SHA1: | D19AAADAF92480629B7D1F3DC325DF505DF0572F |
| SHA256: | 7E191E31D6A149C9D0A5C4D9C76E1C6EC5952C7769B71A6FB87106023E4322AC |
| SSDEEP: | 3:N1KJS4nE8K3:Cc4nE8K3 |
MALICIOUS
No malicious indicators.SUSPICIOUS
No suspicious indicators.INFO
Reads the hosts file
- chrome.exe (PID: 2204)
- chrome.exe (PID: 1508)
Application launched itself
- chrome.exe (PID: 2204)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
51
Monitored processes
15
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1508 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1000,12689776718022536173,8331701084874490687,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=network --service-request-channel-token=5298672278275090750 --mojo-platform-channel-handle=1544 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | chrome.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1708 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1000,12689776718022536173,8331701084874490687,131072 --enable-features=PasswordImport --lang=en-US --extension-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=1649023959541331330 --renderer-client-id=4 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2292 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1928 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=watcher --main-thread-id=2208 --on-initialized-event-handle=316 --parent-handle=320 /prefetch:6 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1972 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1000,12689776718022536173,8331701084874490687,131072 --enable-features=PasswordImport --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=15688206070872296814 --renderer-client-id=6 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2160 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2140 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1000,12689776718022536173,8331701084874490687,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=22363151816465469 --renderer-client-id=10 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3272 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2204 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --disk-cache-dir=null --disk-cache-size=1 --media-cache-size=1 --disable-gpu-shader-disk-cache --disable-background-networking "http://www.hesgoal.com/" | C:\Program Files\Google\Chrome\Application\chrome.exe | explorer.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2448 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1000,12689776718022536173,8331701084874490687,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=738105691762716499 --renderer-client-id=12 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3664 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2616 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1000,12689776718022536173,8331701084874490687,131072 --enable-features=PasswordImport --lang=en-US --no-sandbox --service-request-channel-token=2136014613628411398 --mojo-platform-channel-handle=1948 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2768 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1000,12689776718022536173,8331701084874490687,131072 --enable-features=PasswordImport --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=15239184568129816697 --renderer-client-id=5 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2172 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2808 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1000,12689776718022536173,8331701084874490687,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=18378037360375499352 --renderer-client-id=8 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3336 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
Total events
581
Read events
527
Write events
51
Delete events
3
Modification events
| (PID) Process: | (2204) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (2204) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (2204) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (2204) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (2204) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (1928) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 2204-13250952364740375 |
Value: 259 | |||
| (PID) Process: | (2204) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (2204) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (2204) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 3252-13245750958665039 |
Value: 0 | |||
| (PID) Process: | (2204) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
Executable files
0
Suspicious files
36
Text files
61
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2204 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\BrowserMetrics\BrowserMetrics-5FC0EBAD-89C.pma | — | |
MD5:— | SHA256:— | |||
| 2204 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\00659a35-c066-4e70-9e96-b0299c46cd03.tmp | — | |
MD5:— | SHA256:— | |||
| 2204 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000048.dbtmp | — | |
MD5:— | SHA256:— | |||
| 2204 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Feature Engagement Tracker\AvailabilityDB\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2204 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Session Storage\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2204 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old~RF142f8a.TMP | text | |
MD5:— | SHA256:— | |||
| 2204 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2204 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2204 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2204 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old~RF1432b7.TMP | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
93
TCP/UDP connections
70
DNS requests
39
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1508 | chrome.exe | GET | 301 | 104.26.1.100:80 | http://get.geojs.io/v1/ip/geo.js | US | — | — | suspicious |
1508 | chrome.exe | GET | 200 | 172.217.23.97:80 | http://3.bp.blogspot.com/-BWz0I98hji8/Vj-L-TczG9I/AAAAAAAAAvU/gX78JtIfkNE/s1600/pdc-logo.png | US | image | 17.8 Kb | whitelisted |
1508 | chrome.exe | GET | 200 | 172.217.23.97:80 | http://3.bp.blogspot.com/-ChkEoEmoNjQ/Vh5Wo0KrGXI/AAAAAAAAApQ/Qmi2q5KDE58/s1600/NIGEL1%2B%2528138%2Bx%2B99%2529.jpg | US | image | 6.84 Kb | whitelisted |
1508 | chrome.exe | GET | 200 | 172.217.23.97:80 | http://4.bp.blogspot.com/-oYivlVX1I-A/Vh5YC1MOpWI/AAAAAAAAAqw/yYXSDYB3H3U/s1600/djoo_m.jpg | US | image | 4.23 Kb | whitelisted |
1508 | chrome.exe | GET | 200 | 172.217.23.97:80 | http://4.bp.blogspot.com/-pGJo6x8PHjo/Vh5XNhMTuyI/AAAAAAAAAp4/9sLV4KdgNZc/s1600/suently-alberto1%2B%2528146%2Bx%2B69%2529.jpg | US | image | 4.41 Kb | whitelisted |
1508 | chrome.exe | GET | 200 | 172.217.23.97:80 | http://4.bp.blogspot.com/-lYlMdBw-m3g/Vh0nKZPr6iI/AAAAAAAAAhI/JAAAu7hBU7M/s1600/RACEFLAG2.jpg | US | image | 5.23 Kb | whitelisted |
1508 | chrome.exe | GET | 200 | 5.182.209.23:80 | http://www.hesgoal.com/ | unknown | html | 9.26 Kb | malicious |
1508 | chrome.exe | GET | 200 | 172.217.23.97:80 | http://3.bp.blogspot.com/-bSAAnMQrGTY/Vh5Z8lWj01I/AAAAAAAAAso/pDHE_Fkl05Q/s1600/BALL_m.jpg | US | image | 2.07 Kb | whitelisted |
1508 | chrome.exe | GET | 200 | 172.217.23.97:80 | http://1.bp.blogspot.com/-_YSypQd0Qow/Vh5WQg5w6gI/AAAAAAAAApA/5xZeMRffmwY/s1600/mmm_brugge_m.jpg | US | image | 4.13 Kb | whitelisted |
1508 | chrome.exe | GET | 200 | 172.217.23.97:80 | http://3.bp.blogspot.com/-YdHQ3ksth68/Vh5XsMnFZvI/AAAAAAAAAqY/GfIhD_V9PJE/s1600/soccer-Colombia-Falcao_m.jpg | US | image | 4.75 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1508 | chrome.exe | 104.18.16.65:443 | jsc.adskeeper.com | Cloudflare Inc | US | suspicious |
1508 | chrome.exe | 192.229.233.25:443 | platform.twitter.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
1508 | chrome.exe | 91.198.174.208:443 | upload.wikimedia.org | Wikimedia Foundation, Inc. | NL | suspicious |
1508 | chrome.exe | 5.182.209.23:80 | www.hesgoal.com | — | — | malicious |
1508 | chrome.exe | 172.217.18.173:443 | accounts.google.com | Google Inc. | US | whitelisted |
1508 | chrome.exe | 151.101.12.193:80 | i.imgur.com | Fastly | US | malicious |
1508 | chrome.exe | 151.101.12.193:443 | i.imgur.com | Fastly | US | malicious |
1508 | chrome.exe | 172.217.23.97:443 | 3.bp.blogspot.com | Google Inc. | US | whitelisted |
1508 | chrome.exe | 172.67.190.227:80 | www.nasarfsae.gq | — | US | suspicious |
1508 | chrome.exe | 104.244.42.8:443 | syndication.twitter.com | Twitter Inc. | US | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.hesgoal.com |
| malicious |
accounts.google.com |
| shared |
get.geojs.io |
| suspicious |
code.jquery.com |
| whitelisted |
cdnjs.cloudflare.com |
| whitelisted |
3.bp.blogspot.com |
| whitelisted |
4.bp.blogspot.com |
| whitelisted |
2.bp.blogspot.com |
| whitelisted |
jsc.adskeeper.com |
| suspicious |
platform.twitter.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1052 | svchost.exe | Potentially Bad Traffic | ET INFO DNS Query for Suspicious .gq Domain |