| File name: | Un_A.exe |
| Full analysis: | https://app.any.run/tasks/689bb004-703d-4d76-84eb-a6e8406eee09 |
| Verdict: | Malicious activity |
| Analysis date: | October 06, 2024, 07:26:08 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, Nullsoft Installer self-extracting archive |
| MD5: | 0A5C25E3CD2BE05BD66D913DAF651928 |
| SHA1: | 3077ABD0E78B2C8C441944130E98DF74B9843693 |
| SHA256: | 7DE0B18CE9840E97EC87F948AB0ED8FFF2AD4D47B8EB160C6F15BB02FC55FA04 |
| SSDEEP: | 3072:Nv13JusSX04MSP5vb6CcfcJvicr9HJ166ilqOM8SZP7bEr19C07atwjf+NNhB:B1Rm04MSZb6CcEJvNRSSZP7kSwjgNhB |
MALICIOUS
No malicious indicators.SUSPICIOUS
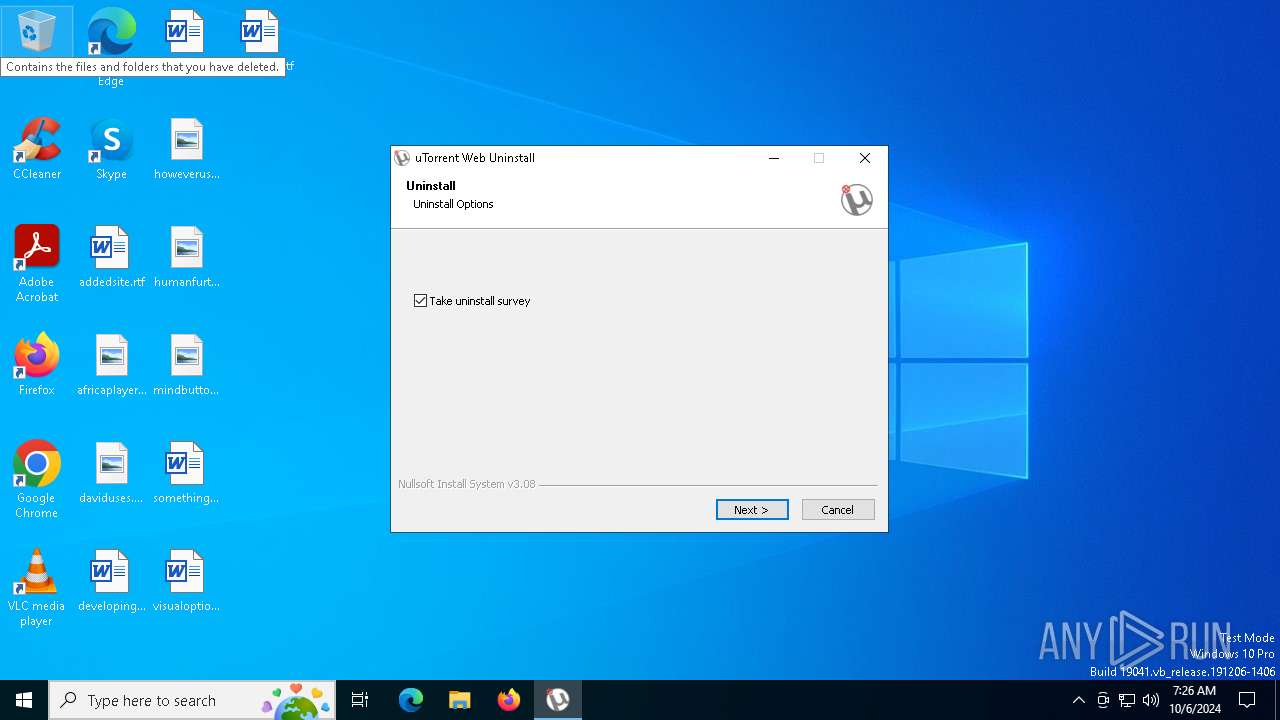
Malware-specific behavior (creating "System.dll" in Temp)
- Un_A.exe (PID: 7032)
- Un_A.exe (PID: 4284)
The process creates files with name similar to system file names
- Un_A.exe (PID: 7032)
Executable content was dropped or overwritten
- Un_A.exe (PID: 5080)
- Un_A.exe (PID: 7032)
- Un_A.exe (PID: 4284)
Starts itself from another location
- Un_A.exe (PID: 5080)
Reads security settings of Internet Explorer
- Un_A.exe (PID: 7032)
Application launched itself
- Un_A.exe (PID: 7032)
INFO
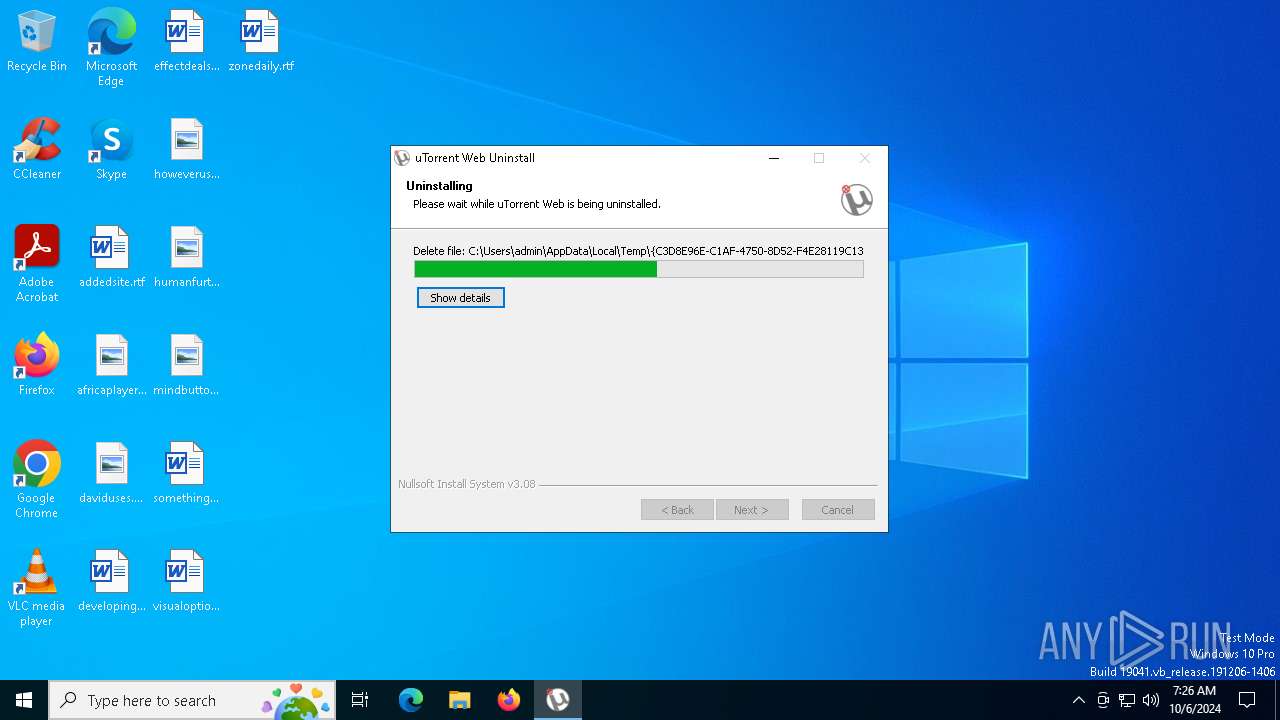
Create files in a temporary directory
- Un_A.exe (PID: 5080)
- Un_A.exe (PID: 7032)
Checks supported languages
- Un_A.exe (PID: 5080)
- Un_A.exe (PID: 7032)
Process checks computer location settings
- Un_A.exe (PID: 7032)
Reads the computer name
- Un_A.exe (PID: 7032)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (67.4) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (14.2) |
| .exe | | | Win32 Executable (generic) (9.7) |
| .exe | | | Generic Win/DOS Executable (4.3) |
| .exe | | | DOS Executable Generic (4.3) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2021:09:25 21:55:49+00:00 |
| ImageFileCharacteristics: | No relocs, Executable, No line numbers, No symbols, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 6 |
| CodeSize: | 26112 |
| InitializedDataSize: | 141824 |
| UninitializedDataSize: | 2048 |
| EntryPoint: | 0x34f7 |
| OSVersion: | 4 |
| ImageVersion: | 6 |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 1.4.0.5871 |
| ProductVersionNumber: | 1.4.0.5871 |
| FileFlagsMask: | 0x0000 |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Windows, Latin1 |
| CompanyName: | BitTorrent Limited |
| FileDescription: | uTorrent Web |
| FileVersion: | 1.4.0.5871 |
| InternalName: | utweb |
| LegalCopyright: | (c) 2023 BitTorrent Limited All Rights Reserved. |
| ProductName: | uTorrent Web |
| ProductVersion: | 1.4.0.5871 |
Total processes
134
Monitored processes
3
Malicious processes
0
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
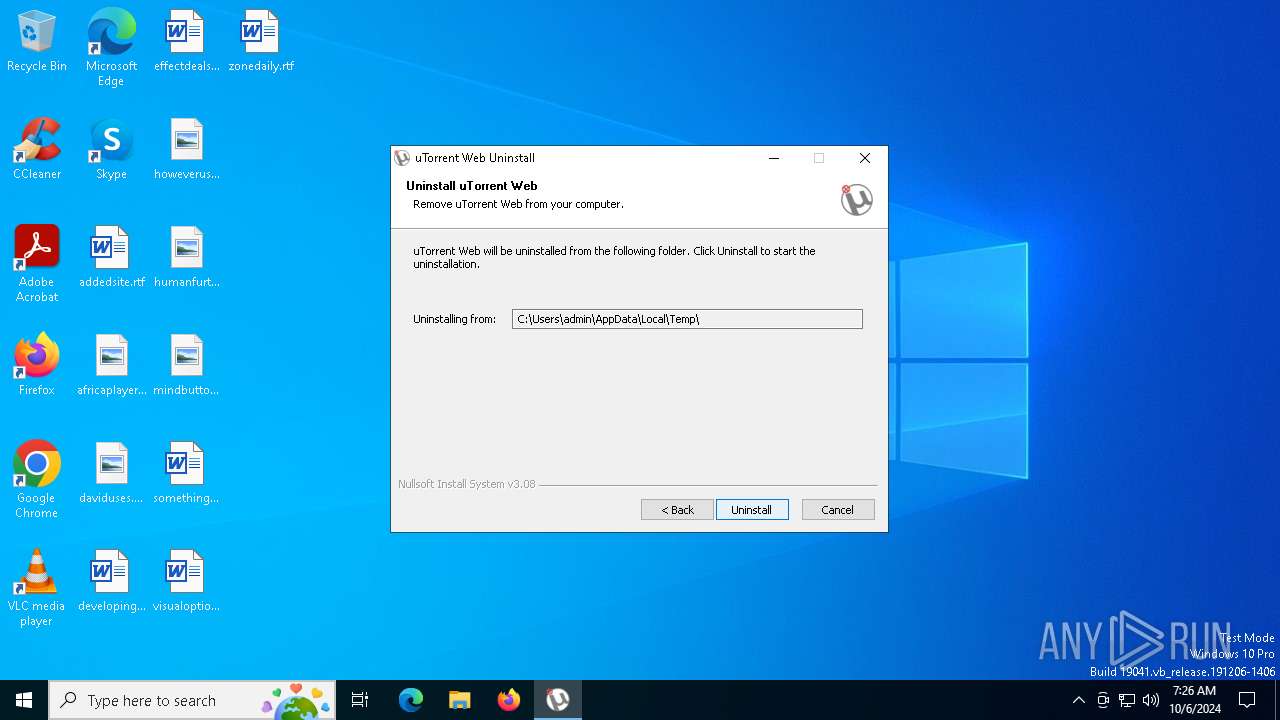
| 4284 | "C:\Users\admin\AppData\Local\Temp\~nsu.tmp\Un_A.exe" /UAC:C03A4 /NCRC _?=C:\Users\admin\AppData\Local\Temp\ | C:\Users\admin\AppData\Local\Temp\~nsu.tmp\Un_A.exe | Un_A.exe | ||||||||||||
User: admin Company: BitTorrent Limited Integrity Level: HIGH Description: uTorrent Web Exit code: 2 Version: 1.4.0.5871 Modules
| |||||||||||||||
| 5080 | "C:\Users\admin\AppData\Local\Temp\Un_A.exe" | C:\Users\admin\AppData\Local\Temp\Un_A.exe | explorer.exe | ||||||||||||
User: admin Company: BitTorrent Limited Integrity Level: MEDIUM Description: uTorrent Web Exit code: 0 Version: 1.4.0.5871 Modules
| |||||||||||||||
| 7032 | "C:\Users\admin\AppData\Local\Temp\~nsu.tmp\Un_A.exe" _?=C:\Users\admin\AppData\Local\Temp\ | C:\Users\admin\AppData\Local\Temp\~nsu.tmp\Un_A.exe | Un_A.exe | ||||||||||||
User: admin Company: BitTorrent Limited Integrity Level: MEDIUM Description: uTorrent Web Exit code: 2 Version: 1.4.0.5871 Modules
| |||||||||||||||
Total events
1 005
Read events
1 000
Write events
3
Delete events
2
Modification events
| (PID) Process: | (4284) Un_A.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\.torrent\OpenWithProgIDs |
| Operation: | delete key | Name: | (default) |
Value: | |||
| (PID) Process: | (4284) Un_A.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\.torrent |
| Operation: | delete key | Name: | (default) |
Value: | |||
| (PID) Process: | (4284) Un_A.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (4284) Un_A.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (4284) Un_A.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
Executable files
9
Suspicious files
1
Text files
1
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 4284 | Un_A.exe | C:\Users\admin\AppData\Local\Temp\nse6AAF.tmp\nsisFirewall.dll | executable | |
MD5:F5BF81A102DE52A4ADD21B8A367E54E0 | SHA256:53BE5716AD80945CB99681D5DBDA60492F5DFB206FBFDB776B769B3EEB18D2C2 | |||
| 7032 | Un_A.exe | C:\Users\admin\AppData\Local\Temp\nsr65DC.tmp\System.dll | executable | |
MD5:CFF85C549D536F651D4FB8387F1976F2 | SHA256:8DC562CDA7217A3A52DB898243DE3E2ED68B80E62DDCB8619545ED0B4E7F65A8 | |||
| 4284 | Un_A.exe | C:\Users\admin\AppData\Local\Temp\nse6AAF.tmp\INetC.dll | executable | |
MD5:640BFF73A5F8E37B202D911E4749B2E9 | SHA256:C1E568E25EC111184DEB1B87CFDA4BFEC529B1ABEAB39B66539D998012F33502 | |||
| 4284 | Un_A.exe | C:\Users\admin\AppData\Local\Temp\nse6AAF.tmp\System.dll | executable | |
MD5:CFF85C549D536F651D4FB8387F1976F2 | SHA256:8DC562CDA7217A3A52DB898243DE3E2ED68B80E62DDCB8619545ED0B4E7F65A8 | |||
| 4284 | Un_A.exe | C:\Users\admin\AppData\Local\Temp\utweb_install.log | binary | |
MD5:BA38B9F417707A68B53F2D393099CDD8 | SHA256:31F0DB7B07CB2DA344004F2943662A3026F9FF71B5B320221C3D370562EBA746 | |||
| 4284 | Un_A.exe | C:\Users\admin\AppData\Local\Temp\nse6AAF.tmp\FindProcDLL.dll | executable | |
MD5:B4FAF654DE4284A89EAF7D073E4E1E63 | SHA256:C0948B2EC36A69F82C08935FAC4B212238B6792694F009B93B4BDB478C4F26E3 | |||
| 4284 | Un_A.exe | C:\Users\admin\AppData\Local\Temp\nse6AAF.tmp\modern-wizard.bmp | image | |
MD5:CBE40FD2B1EC96DAEDC65DA172D90022 | SHA256:3AD2DC318056D0A2024AF1804EA741146CFC18CC404649A44610CBF8B2056CF2 | |||
| 5080 | Un_A.exe | C:\Users\admin\AppData\Local\Temp\~nsu.tmp\Un_A.exe | executable | |
MD5:0A5C25E3CD2BE05BD66D913DAF651928 | SHA256:7DE0B18CE9840E97EC87F948AB0ED8FFF2AD4D47B8EB160C6F15BB02FC55FA04 | |||
| 7032 | Un_A.exe | C:\Users\admin\AppData\Local\Temp\nsr65DC.tmp\UAC.dll | executable | |
MD5:ADB29E6B186DAA765DC750128649B63D | SHA256:2F7F8FC05DC4FD0D5CDA501B47E4433357E887BBFED7292C028D99C73B52DC08 | |||
| 4284 | Un_A.exe | C:\Users\admin\AppData\Local\Temp\nse6AAF.tmp\nsDialogs.dll | executable | |
MD5:6C3F8C94D0727894D706940A8A980543 | SHA256:56B96ADD1978B1ABBA286F7F8982B0EFBE007D4A48B3DED6A4D408E01D753FE2 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
8
TCP/UDP connections
44
DNS requests
17
Threats
2
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2120 | MoUsoCoreWorker.exe | GET | 200 | 23.52.120.96:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
1504 | svchost.exe | GET | 200 | 23.52.120.96:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
4412 | svchost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
4284 | Un_A.exe | POST | 200 | 52.20.193.171:80 | http://i-4101.b-5871.utweb.bench.utorrent.com/e?i=4101 | unknown | — | — | whitelisted |
6028 | backgroundTaskHost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | unknown | — | — | whitelisted |
4284 | Un_A.exe | POST | 200 | 52.20.193.171:80 | http://i-4101.b-5871.utweb.bench.utorrent.com/e?i=4101 | unknown | — | — | whitelisted |
2872 | SIHClient.exe | GET | 200 | 23.52.120.96:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
2872 | SIHClient.exe | GET | 200 | 23.52.120.96:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2280 | svchost.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
3888 | svchost.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
— | — | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
1504 | svchost.exe | 23.52.120.96:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
2120 | MoUsoCoreWorker.exe | 23.52.120.96:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
4324 | svchost.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
2280 | svchost.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4412 | svchost.exe | 20.190.159.73:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
login.live.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
go.microsoft.com |
| whitelisted |
i-4101.b-5871.utweb.bench.utorrent.com |
| whitelisted |
arc.msn.com |
| whitelisted |
fd.api.iris.microsoft.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
4284 | Un_A.exe | Potentially Bad Traffic | ET USER_AGENTS Observed Suspicious UA (NSIS_Inetc (Mozilla)) |
4284 | Un_A.exe | Potentially Bad Traffic | ET USER_AGENTS Observed Suspicious UA (NSIS_Inetc (Mozilla)) |