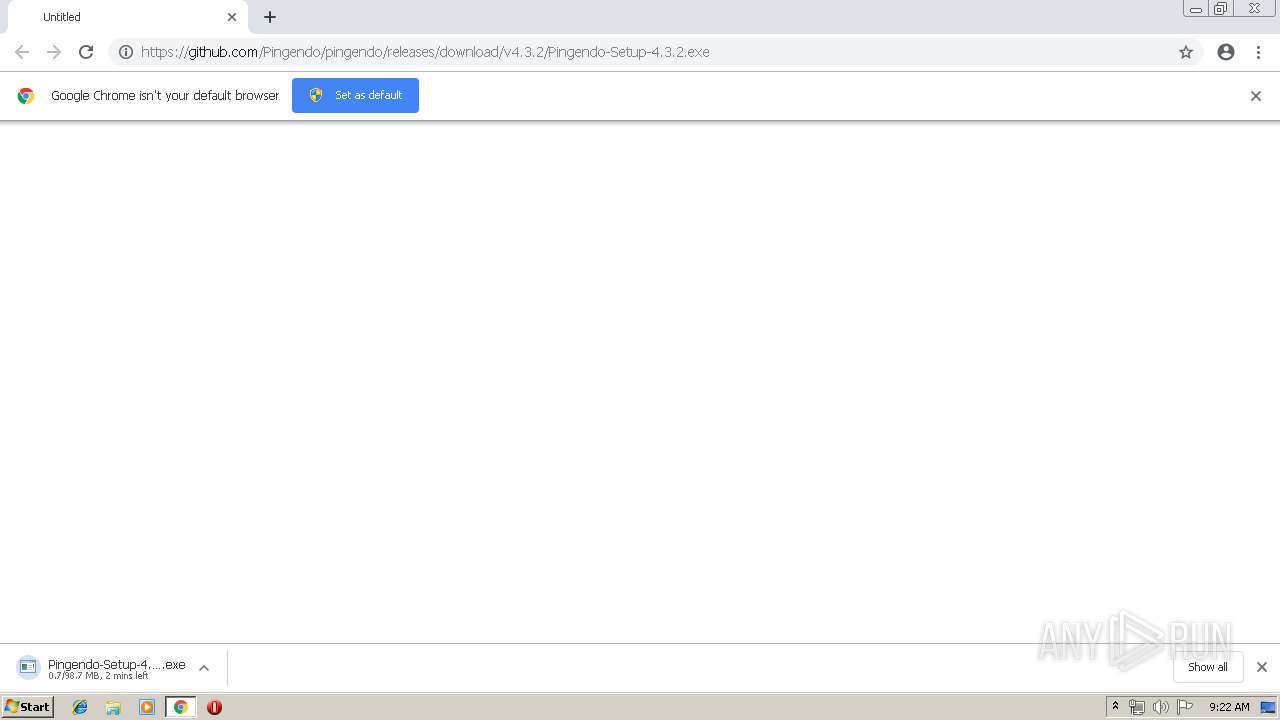
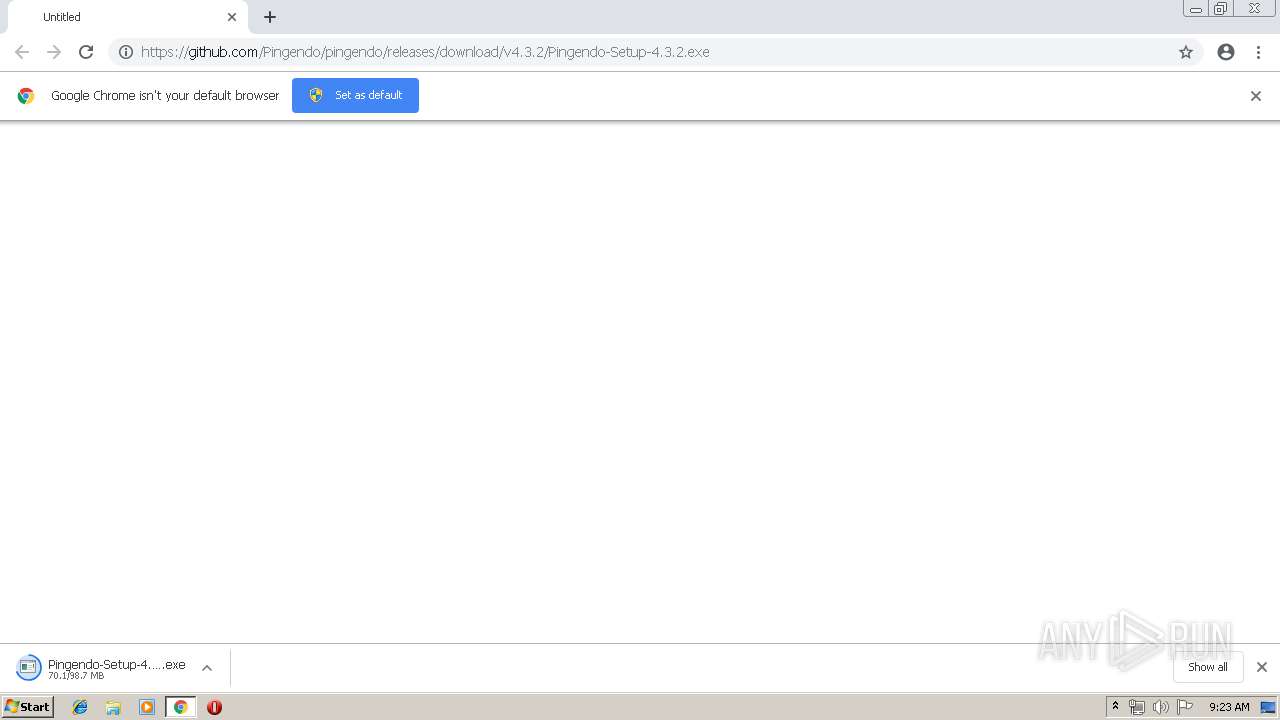
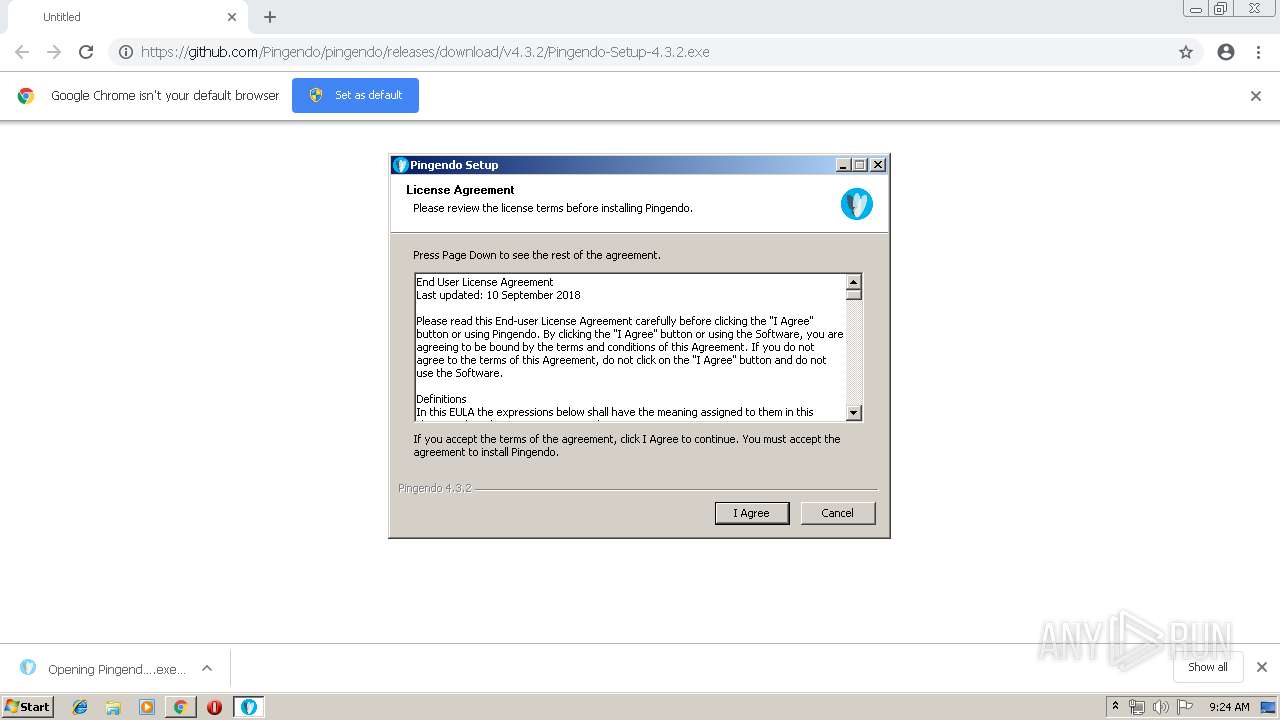
| URL: | https://github.com/Pingendo/pingendo/releases/download/v4.3.2/Pingendo-Setup-4.3.2.exe |
| Full analysis: | https://app.any.run/tasks/cda5187b-0dc6-4c5c-be4a-6649c5d6cdf1 |
| Verdict: | Malicious activity |
| Analysis date: | April 16, 2019, 08:22:05 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 0ACA70A0199C7EF3D6EE646E6F67D72D |
| SHA1: | 462A78040A95FB8D9E48F79E077FBF3C4066FA79 |
| SHA256: | 7DC1900ADFF6380D61105C4540BC8C04D8DCAA5851122F8606DE6673492918FF |
| SSDEEP: | 3:N8tEdjuBKj2l/MkCPGLXBKNjJ:2u4u0CjJ |
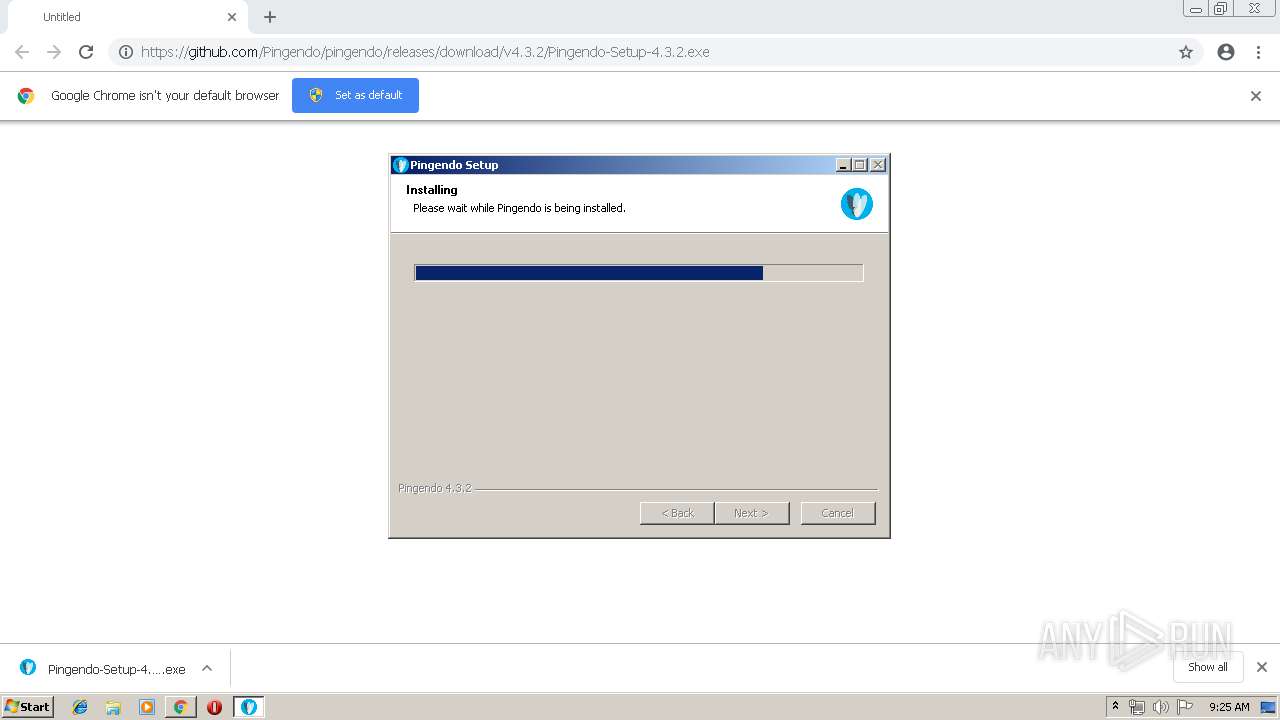
MALICIOUS
Application was dropped or rewritten from another process
- Pingendo-Setup-4.3.2.exe (PID: 3308)
- Pingendo-Setup-4.3.2.exe (PID: 2960)
Loads dropped or rewritten executable
- Pingendo-Setup-4.3.2.exe (PID: 3308)
- Pingendo.exe (PID: 2672)
- Pingendo.exe (PID: 628)
- Pingendo.exe (PID: 3868)
- Pingendo.exe (PID: 1644)
- Pingendo.exe (PID: 3496)
- Pingendo.exe (PID: 3492)
- Pingendo.exe (PID: 3560)
SUSPICIOUS
Executable content was dropped or overwritten
- Pingendo-Setup-4.3.2.exe (PID: 3308)
- chrome.exe (PID: 3044)
- Pingendo.exe (PID: 3496)
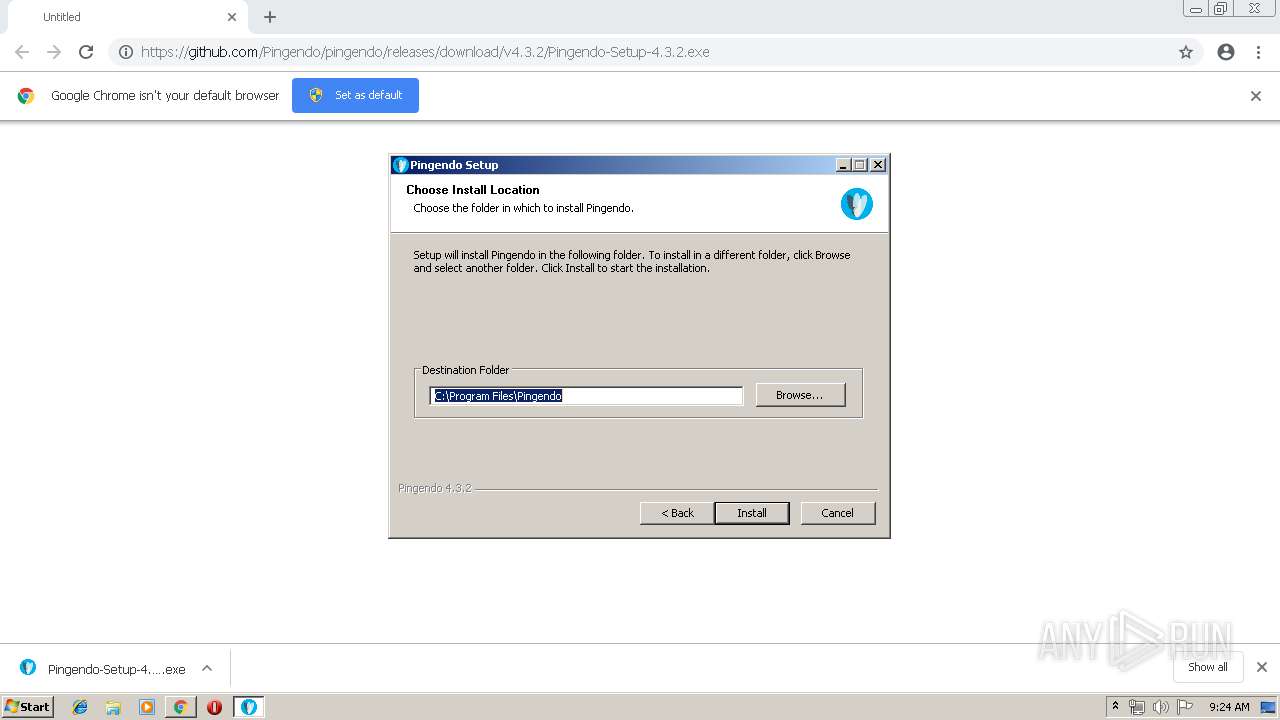
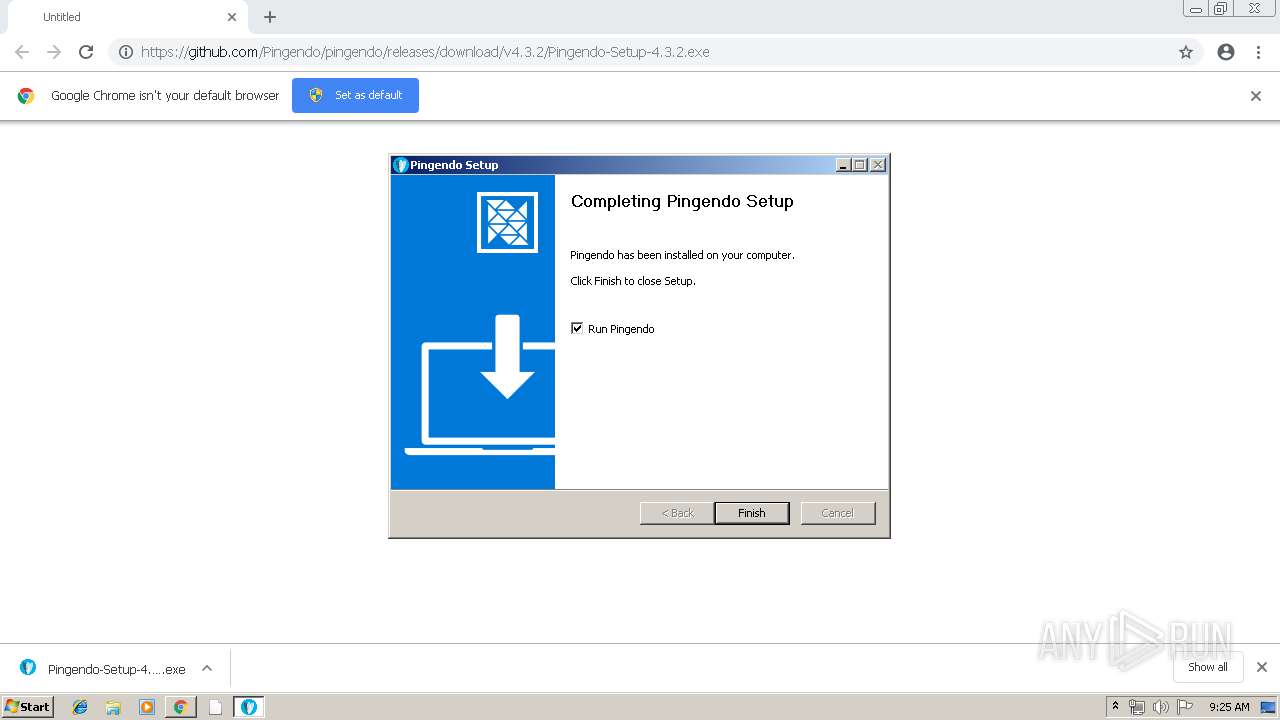
Creates a software uninstall entry
- Pingendo-Setup-4.3.2.exe (PID: 3308)
Creates files in the user directory
- Pingendo.exe (PID: 3868)
Modifies files in Chrome extension folder
- chrome.exe (PID: 3044)
Application launched itself
- Pingendo.exe (PID: 3868)
Creates files in the program directory
- Pingendo-Setup-4.3.2.exe (PID: 3308)
INFO
Reads settings of System Certificates
- chrome.exe (PID: 2248)
- Pingendo.exe (PID: 3868)
Application launched itself
- chrome.exe (PID: 3044)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
61
Monitored processes
26
Malicious processes
10
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 628 | "C:\Program Files\Pingendo\Pingendo.exe" --type=gpu-process --enable-features=FixAltGraph --no-sandbox --gpu-preferences=KAAAAAAAAACAAwCAAQAAAAAAAAAAAGAAEAAAAAAAAAAAAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAKAAAAEAAAAAAAAAAAAAAACwAAABAAAAAAAAAAAQAAAAoAAAAQAAAAAAAAAAEAAAALAAAA --use-gl=swiftshader-webgl --service-request-channel-token=F490DCD0F925F6CF096FDA5570749C45 --mojo-platform-channel-handle=1560 /prefetch:2 | C:\Program Files\Pingendo\Pingendo.exe | — | Pingendo.exe | |||||||||||
User: admin Company: Pingendo Inc. Integrity Level: MEDIUM Description: Pingendo Exit code: 4 Version: 4.3.2.438 Modules
| |||||||||||||||
| 828 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" /prefetch:7 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad" "--metrics-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" --url=https://clients2.google.com/cr/report --annotation=channel= --annotation=plat=Win32 --annotation=prod=Chrome --annotation=ver=73.0.3683.75 --initial-client-data=0x7c,0x80,0x84,0x78,0x88,0x6fa10f18,0x6fa10f28,0x6fa10f34 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 1152 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=964,8857211242881081657,3085108593435089620,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=9636553460708806832 --mojo-platform-channel-handle=3968 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 1336 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=964,8857211242881081657,3085108593435089620,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=1313722319225249298 --mojo-platform-channel-handle=3752 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 1348 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=964,8857211242881081657,3085108593435089620,131072 --enable-features=PasswordImport --disable-gpu-compositing --service-pipe-token=9612353711569762642 --lang=en-US --extension-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=9612353711569762642 --renderer-client-id=15 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3848 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 1644 | "C:\Program Files\Pingendo\Pingendo.exe" --type=gpu-process --enable-features=FixAltGraph --no-sandbox --gpu-preferences=KAAAAAAAAACAAwCAAQAAAAAAAAAAAGAAEAAAAAAAAAAAAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAKAAAAEAAAAAAAAAAAAAAACwAAABAAAAAAAAAAAQAAAAoAAAAQAAAAAAAAAAEAAAALAAAA --service-request-channel-token=41E7B92BA00A1998F18B0F26E3D19518 --mojo-platform-channel-handle=1104 /prefetch:2 | C:\Program Files\Pingendo\Pingendo.exe | — | Pingendo.exe | |||||||||||
User: admin Company: Pingendo Inc. Integrity Level: MEDIUM Description: Pingendo Exit code: 4 Version: 4.3.2.438 Modules
| |||||||||||||||
| 1824 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=964,8857211242881081657,3085108593435089620,131072 --enable-features=PasswordImport --service-pipe-token=12133985021958363888 --lang=en-US --extension-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=12133985021958363888 --renderer-client-id=4 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2236 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 2248 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=964,8857211242881081657,3085108593435089620,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=network --service-request-channel-token=9315772942753854730 --mojo-platform-channel-handle=1484 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | chrome.exe | ||||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 2616 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=964,8857211242881081657,3085108593435089620,131072 --enable-features=PasswordImport --disable-gpu-sandbox --use-gl=disabled --gpu-preferences=KAAAAAAAAACAAwAAAQAAAAAAAAAAAGAAAAAAAAEAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --service-request-channel-token=15629850732880037146 --mojo-platform-channel-handle=2772 /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 2672 | "C:\Program Files\Pingendo\Pingendo.exe" --type=renderer --no-sandbox --enable-features=FixAltGraph --service-pipe-token=0B360E93B499C36B399CA1A3A6539DFB --lang=en-US --app-path="C:\Program Files\Pingendo\resources\app.asar" --node-integration=true --webview-tag=true --no-sandbox --background-color=#fff --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --enable-compositor-image-animations --service-request-channel-token=0B360E93B499C36B399CA1A3A6539DFB --renderer-client-id=6 --mojo-platform-channel-handle=1520 /prefetch:1 | C:\Program Files\Pingendo\Pingendo.exe | — | Pingendo.exe | |||||||||||
User: admin Company: Pingendo Inc. Integrity Level: MEDIUM Description: Pingendo Exit code: 0 Version: 4.3.2.438 Modules
| |||||||||||||||
Total events
1 359
Read events
1 245
Write events
110
Delete events
4
Modification events
| (PID) Process: | (3044) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (3044) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (3044) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (3044) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (3044) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (3048) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 3044-13199876540241750 |
Value: 259 | |||
| (PID) Process: | (3044) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (3044) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (3044) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 3488-13197474229333984 |
Value: 0 | |||
| (PID) Process: | (3044) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
Executable files
61
Suspicious files
34
Text files
900
Unknown types
68
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3044 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\index | — | |
MD5:— | SHA256:— | |||
| 3044 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_0 | — | |
MD5:— | SHA256:— | |||
| 3044 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_1 | — | |
MD5:— | SHA256:— | |||
| 3044 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_2 | — | |
MD5:— | SHA256:— | |||
| 3044 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_3 | — | |
MD5:— | SHA256:— | |||
| 3044 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3044 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old~RF10642a.TMP | — | |
MD5:— | SHA256:— | |||
| 3044 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\906d55dc-dfa3-4abd-8541-c3a1fefb6ff6.tmp | — | |
MD5:— | SHA256:— | |||
| 3044 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000018.dbtmp | — | |
MD5:— | SHA256:— | |||
| 3044 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\GPUCache\index | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
4
TCP/UDP connections
34
DNS requests
19
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2248 | chrome.exe | GET | 200 | 173.194.129.202:80 | http://r5---sn-aigzrn7s.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvMjJlQUFXRC12Ny1ldUFnMXF3SDlXZDlFZw/7319.128.0.1_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx?cms_redirect=yes&mip=109.169.22.99&mm=28&mn=sn-aigzrn7s&ms=nvh&mt=1555402669&mv=u&pl=22&shardbypass=yes | US | crx | 842 Kb | whitelisted |
2248 | chrome.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBRJ9L2KGL92BpjF3kAtaDtxauTmhgQUPdNQpdagre7zSmAKZdMh1Pj41g8CEAoGMEJ%2FW7ztaVc5ZZO2RR8%3D | US | der | 471 b | whitelisted |
2248 | chrome.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTfqhLjKLEJQZPin0KCzkdAQpVYowQUsT7DaQP4v0cB1JgmGggC72NkK8MCEAx5qUSwjBGVIJJhX%2BJrHYM%3D | US | der | 471 b | whitelisted |
2248 | chrome.exe | GET | 302 | 172.217.23.174:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvMjJlQUFXRC12Ny1ldUFnMXF3SDlXZDlFZw/7319.128.0.1_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx | US | html | 504 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2248 | chrome.exe | 172.217.23.131:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
2248 | chrome.exe | 192.30.253.112:443 | github.com | GitHub, Inc. | US | shared |
2248 | chrome.exe | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
2248 | chrome.exe | 54.231.98.88:443 | github-production-release-asset-2e65be.s3.amazonaws.com | Amazon.com, Inc. | US | unknown |
2248 | chrome.exe | 216.58.208.35:443 | www.gstatic.com | Google Inc. | US | whitelisted |
2248 | chrome.exe | 172.217.18.13:443 | accounts.google.com | Google Inc. | US | whitelisted |
2248 | chrome.exe | 216.58.207.35:443 | ssl.gstatic.com | Google Inc. | US | whitelisted |
2248 | chrome.exe | 172.217.23.170:443 | safebrowsing.googleapis.com | Google Inc. | US | whitelisted |
2248 | chrome.exe | 216.58.207.46:443 | clients1.google.com | Google Inc. | US | whitelisted |
— | — | 167.99.129.42:443 | pingendo.com | — | US | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
github.com |
| malicious |
clientservices.googleapis.com |
| whitelisted |
accounts.google.com |
| shared |
ocsp.digicert.com |
| whitelisted |
github-production-release-asset-2e65be.s3.amazonaws.com |
| shared |
ssl.gstatic.com |
| whitelisted |
www.gstatic.com |
| whitelisted |
safebrowsing.googleapis.com |
| whitelisted |
clients1.google.com |
| whitelisted |
sb-ssl.google.com |
| whitelisted |