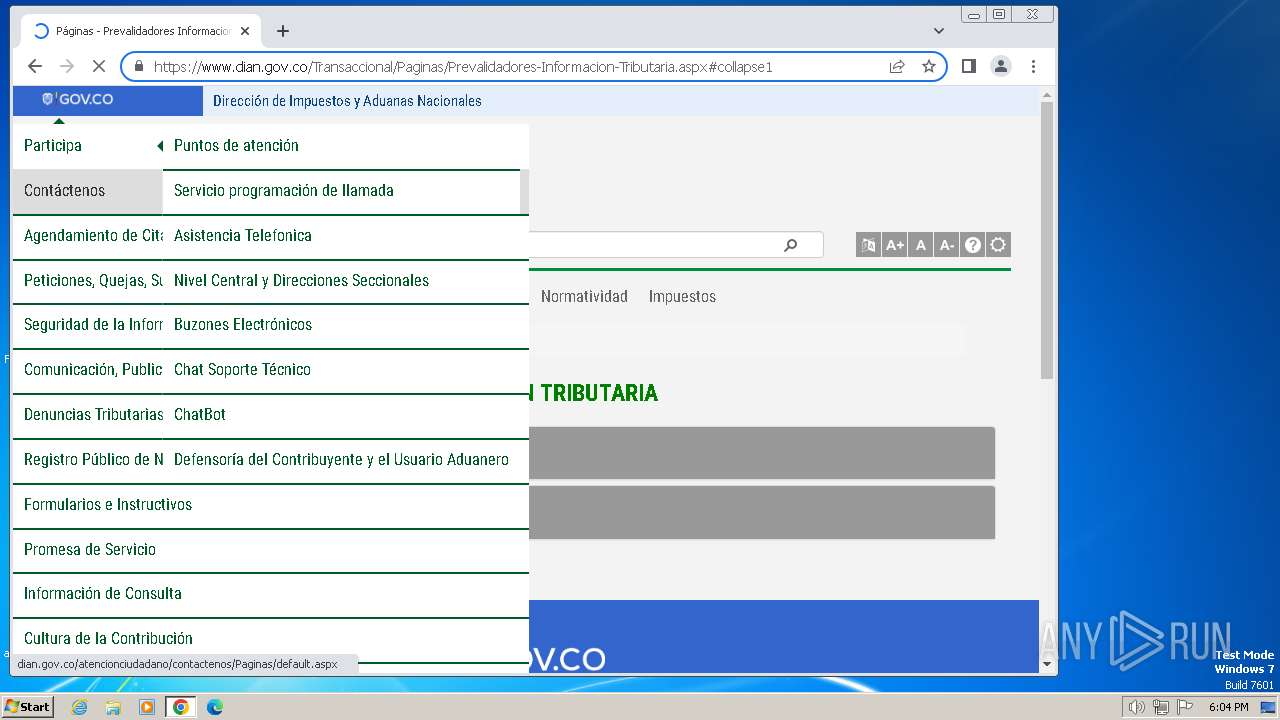
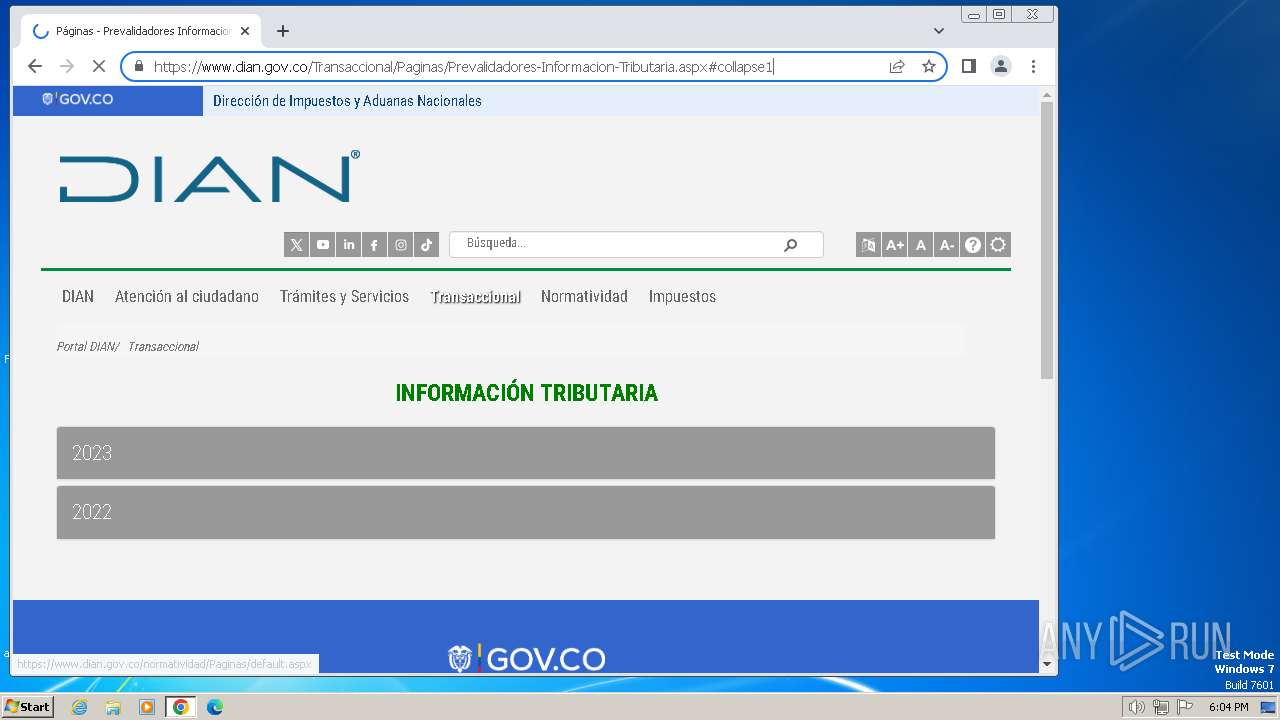
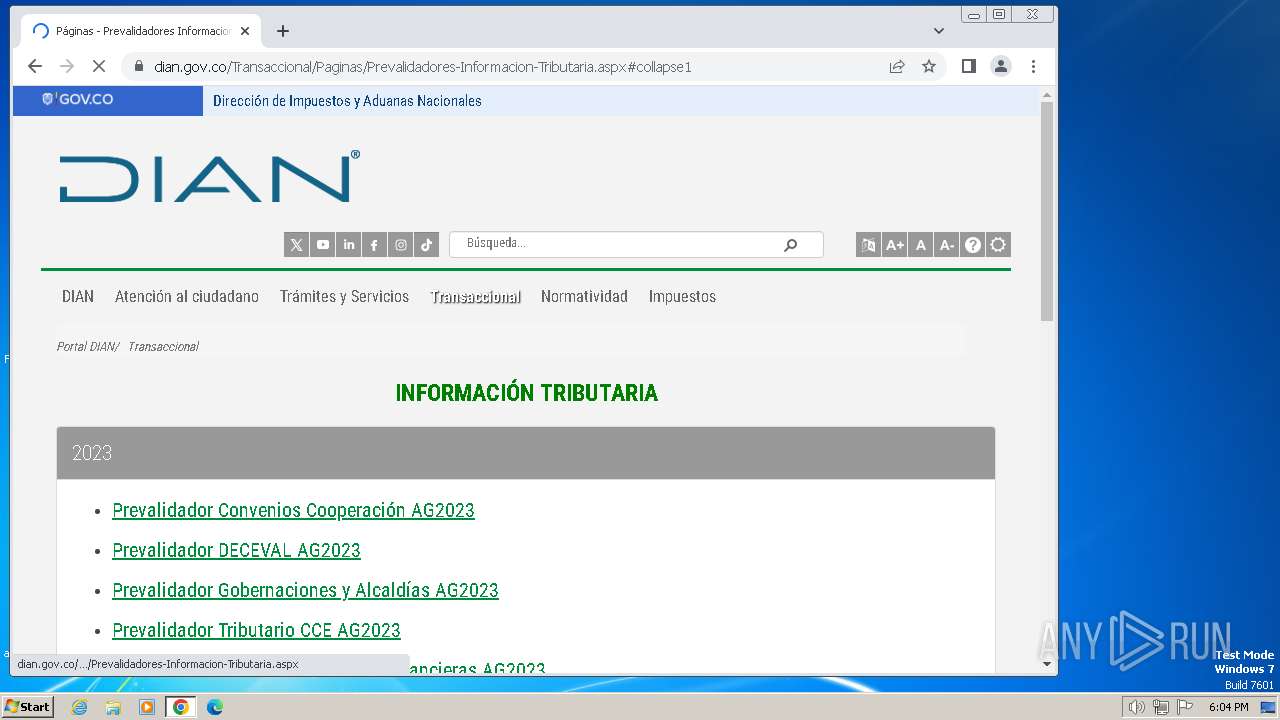
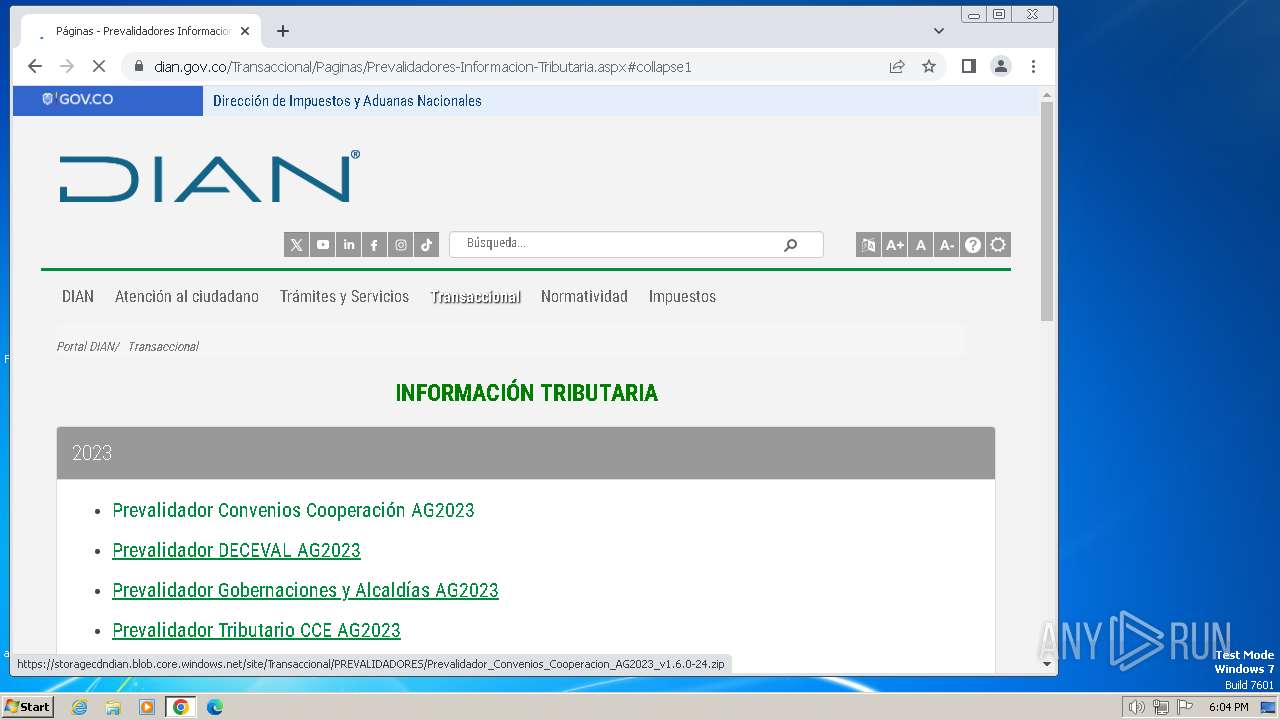
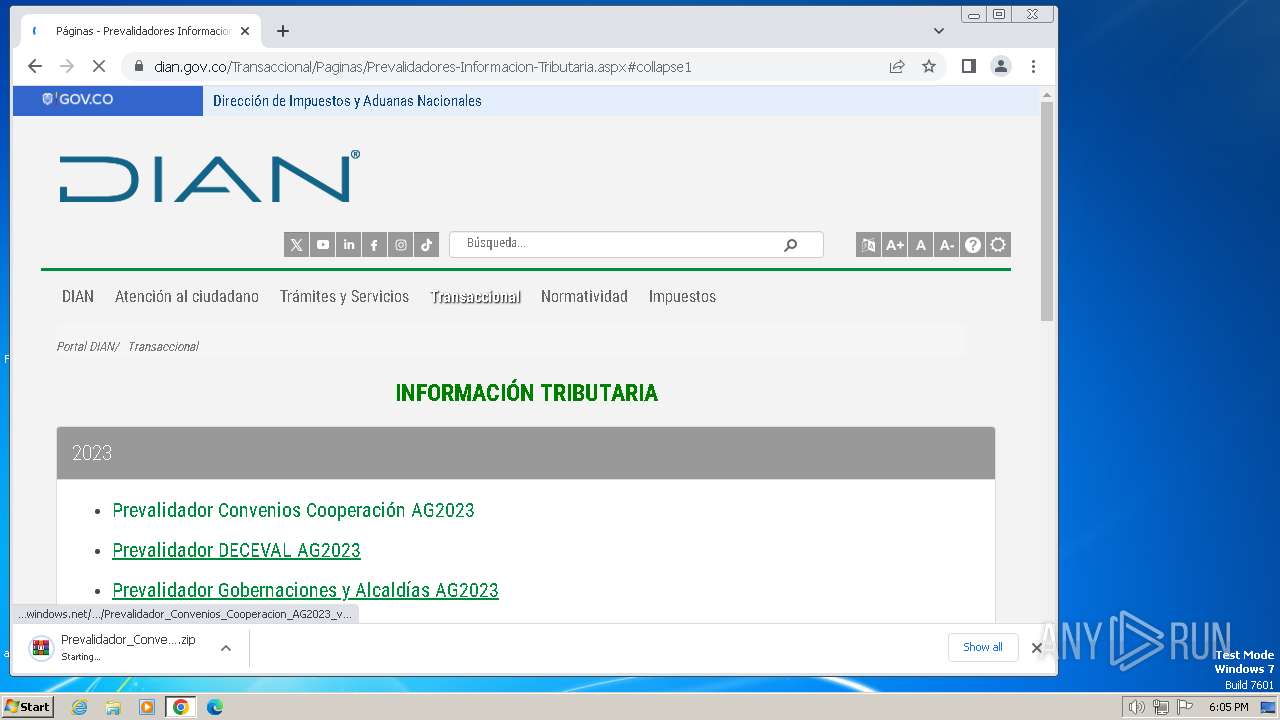
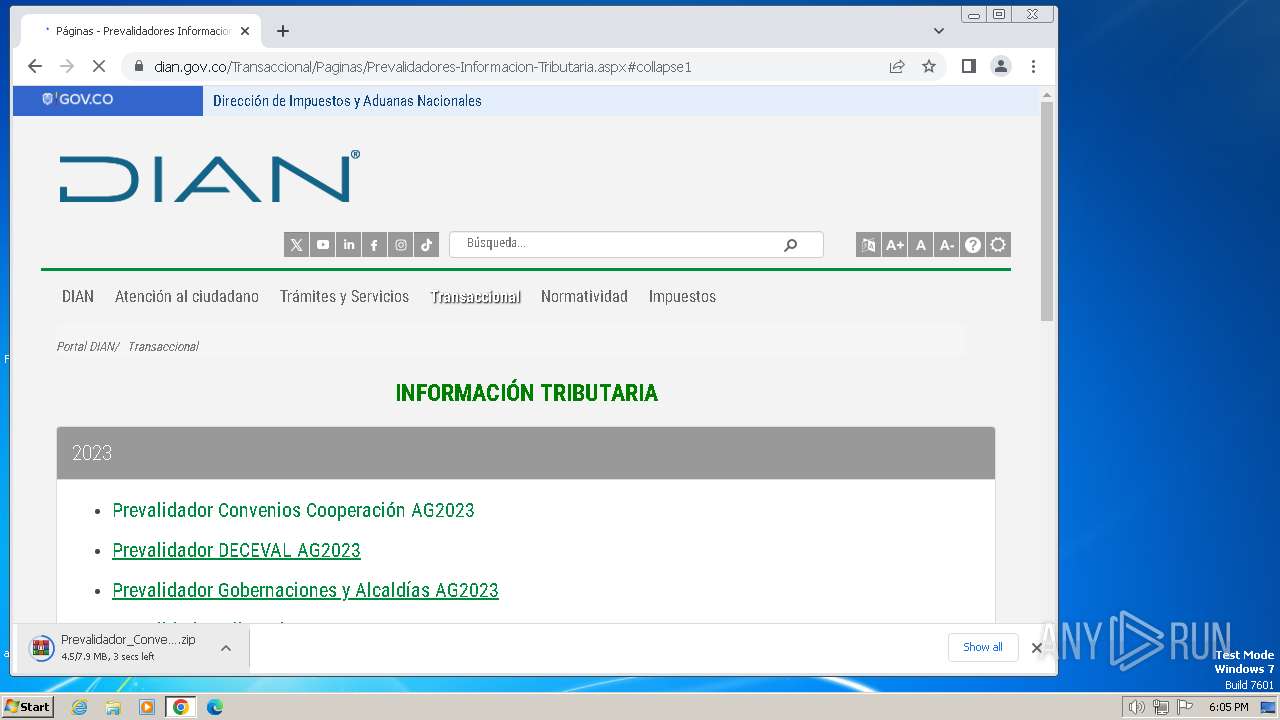
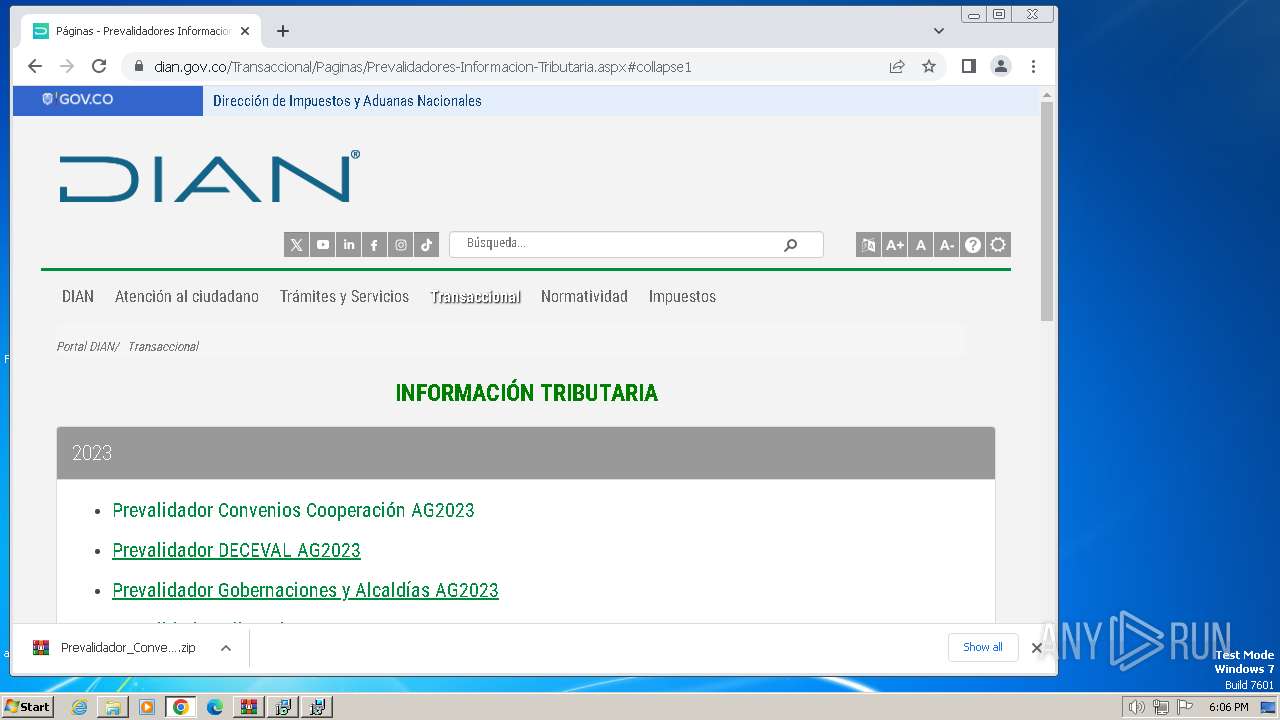
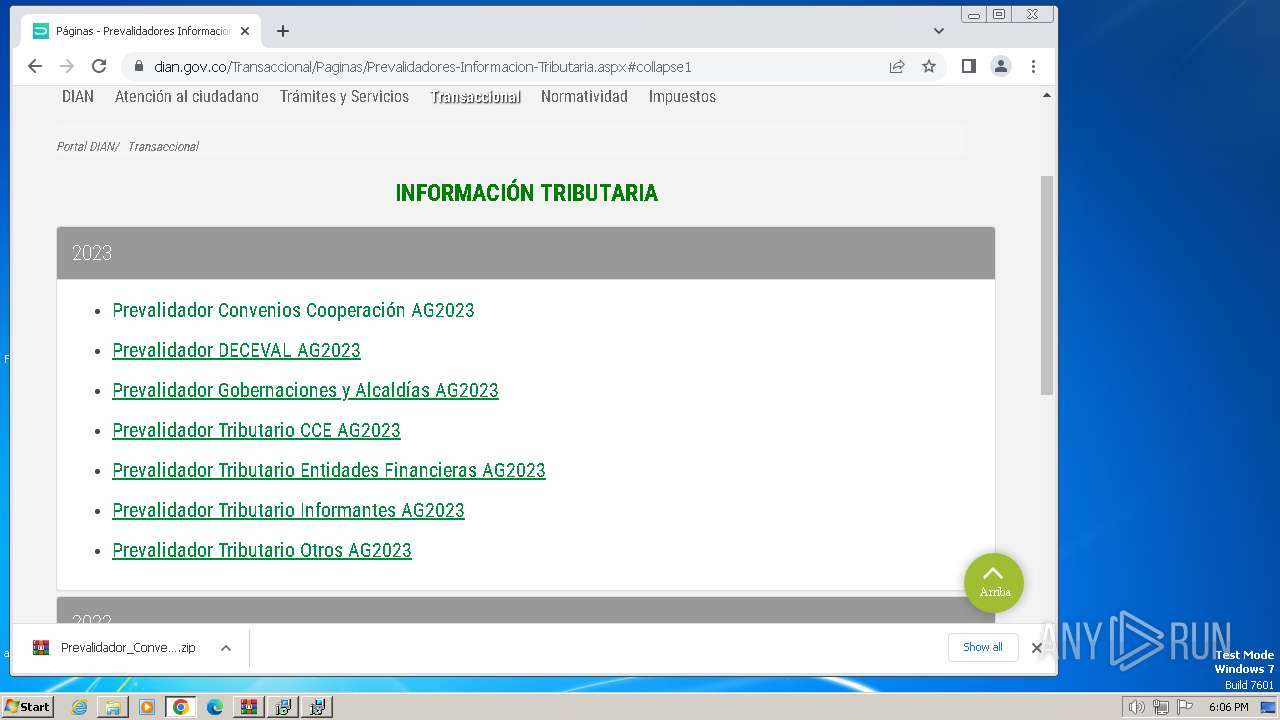
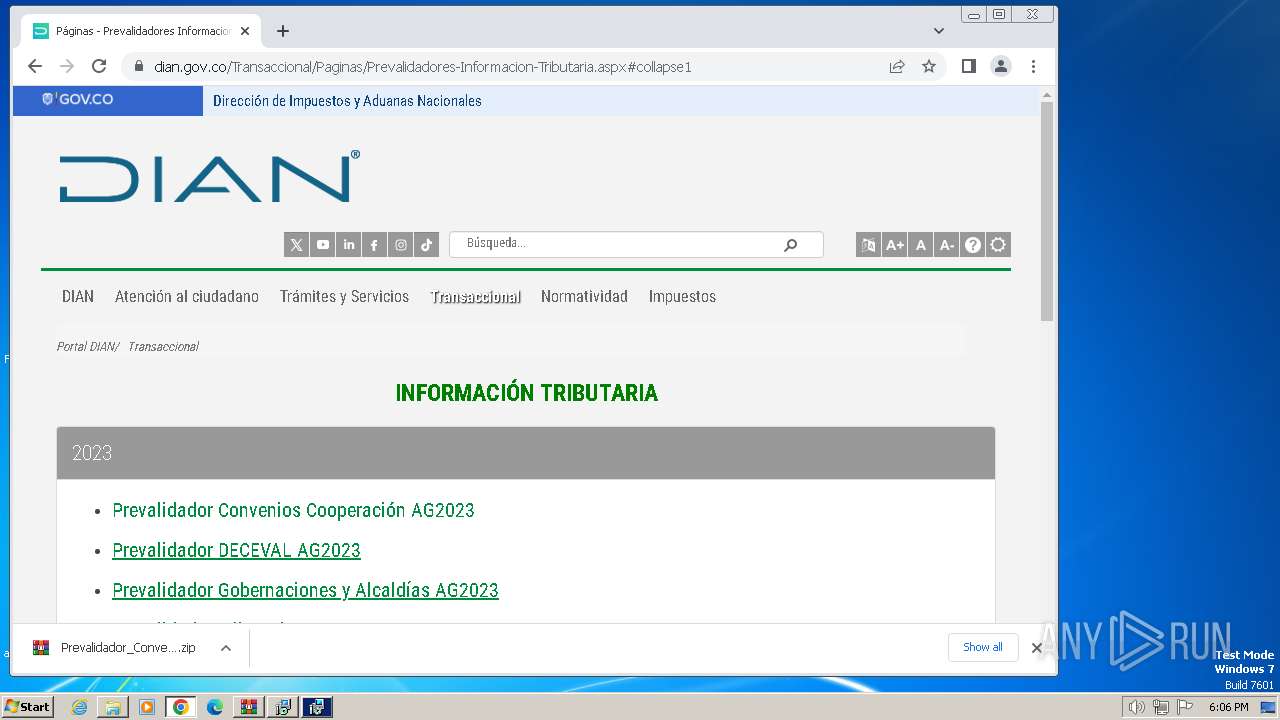
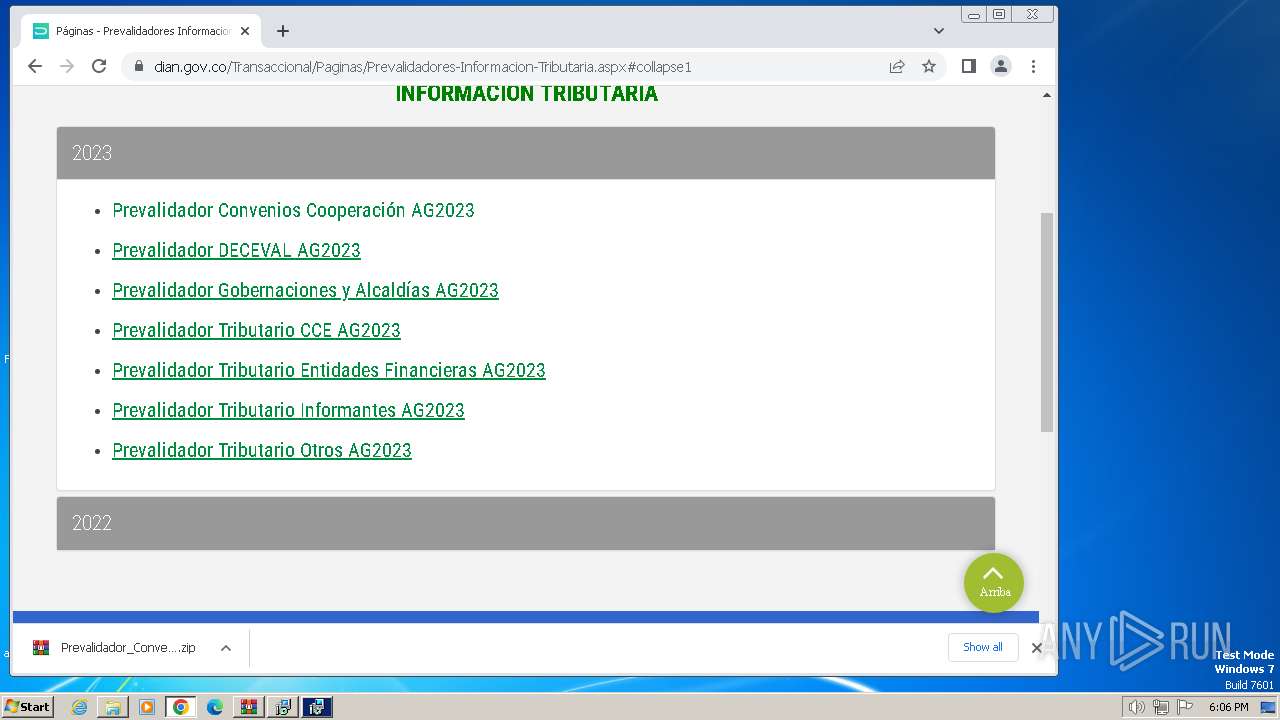
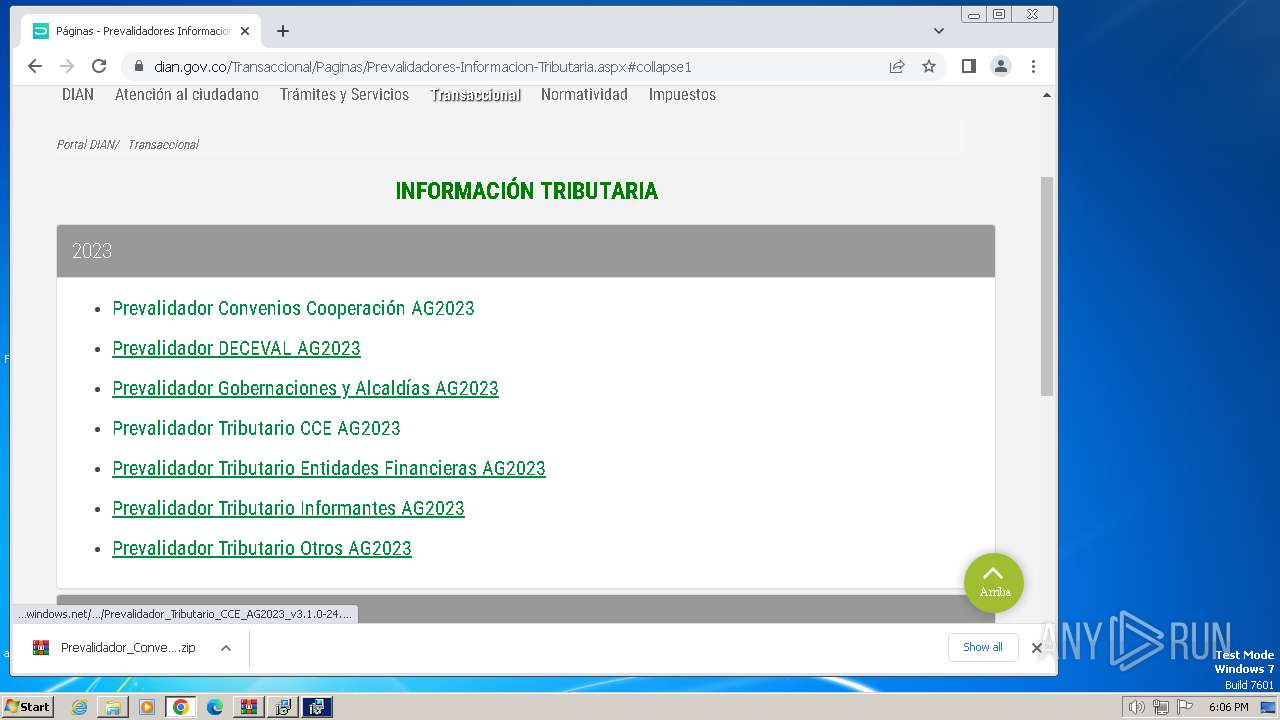
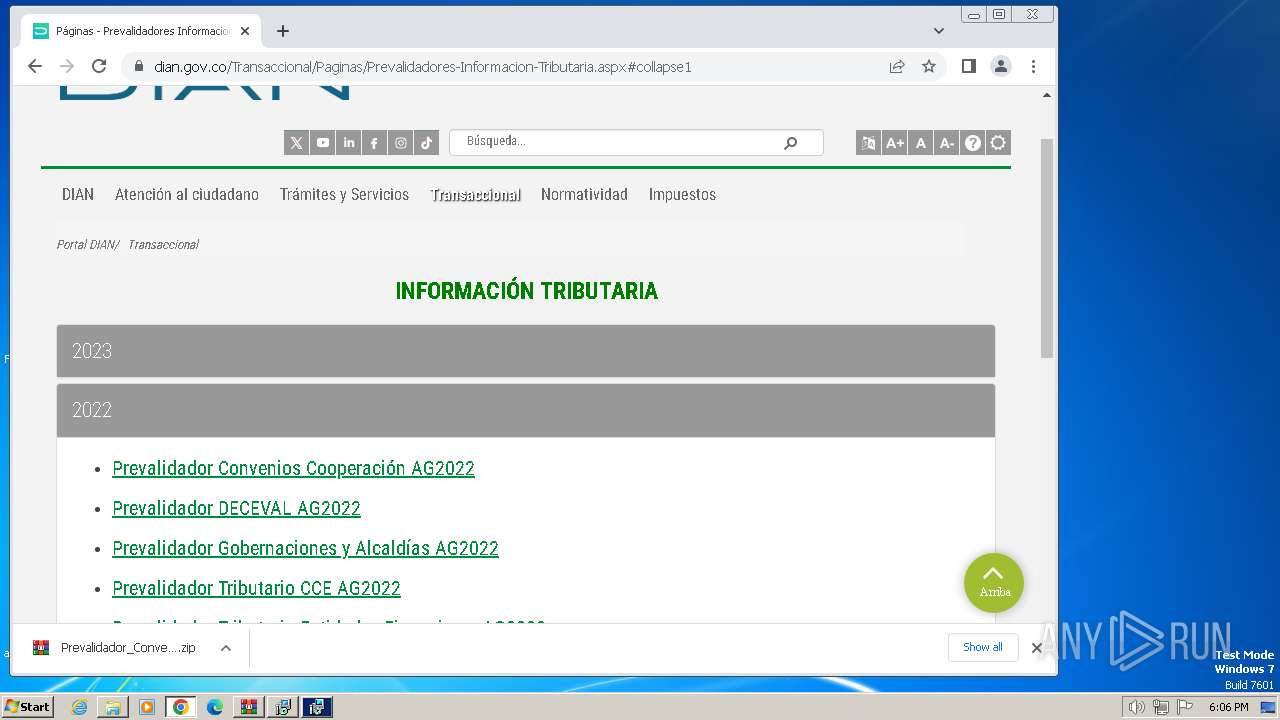
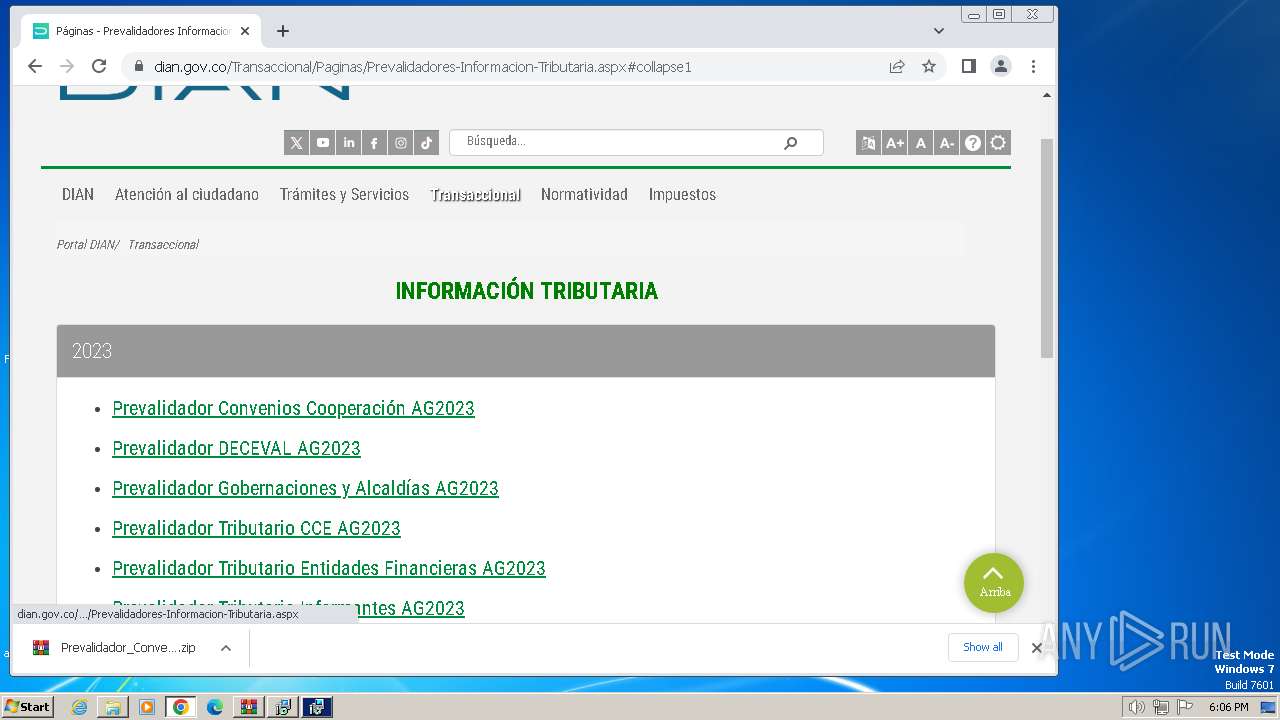
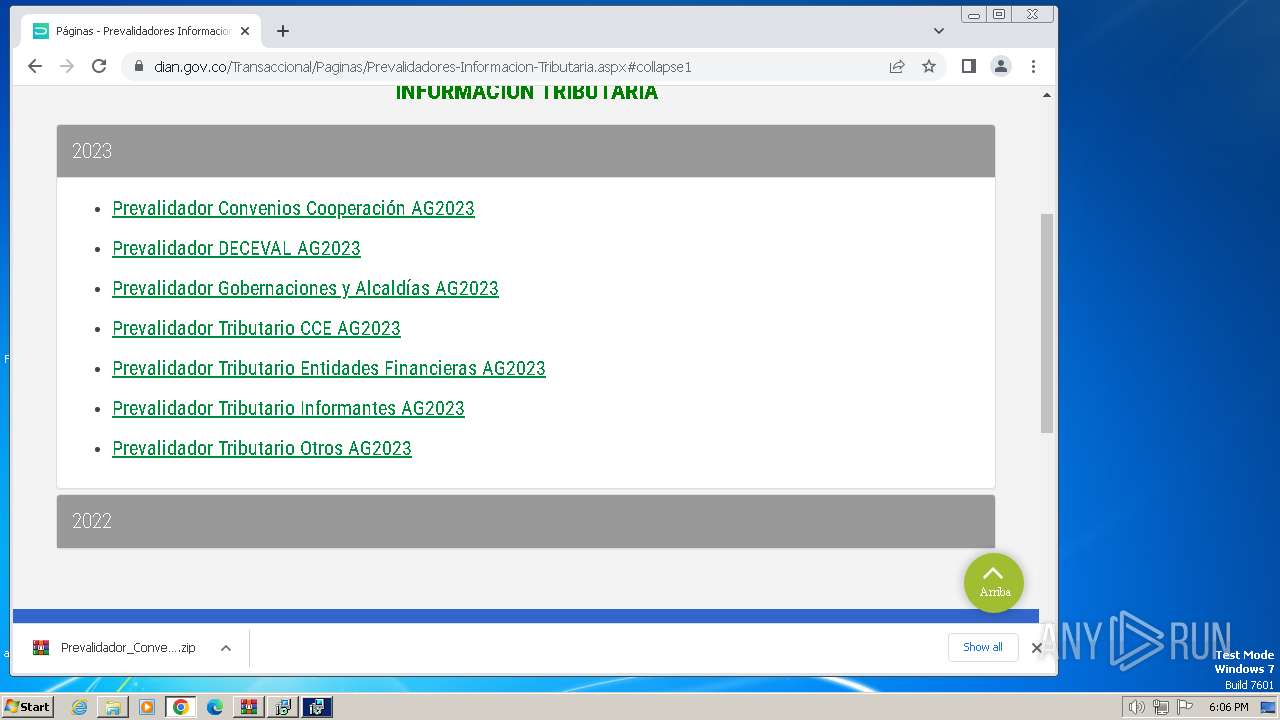
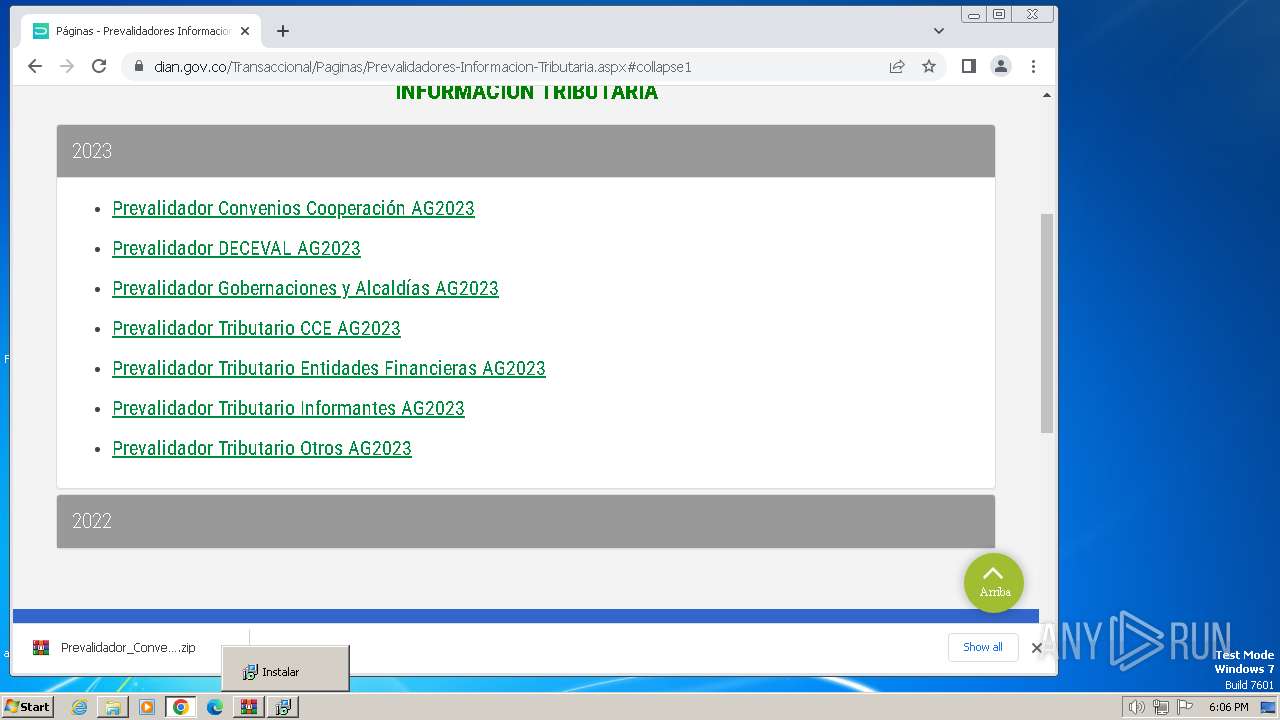
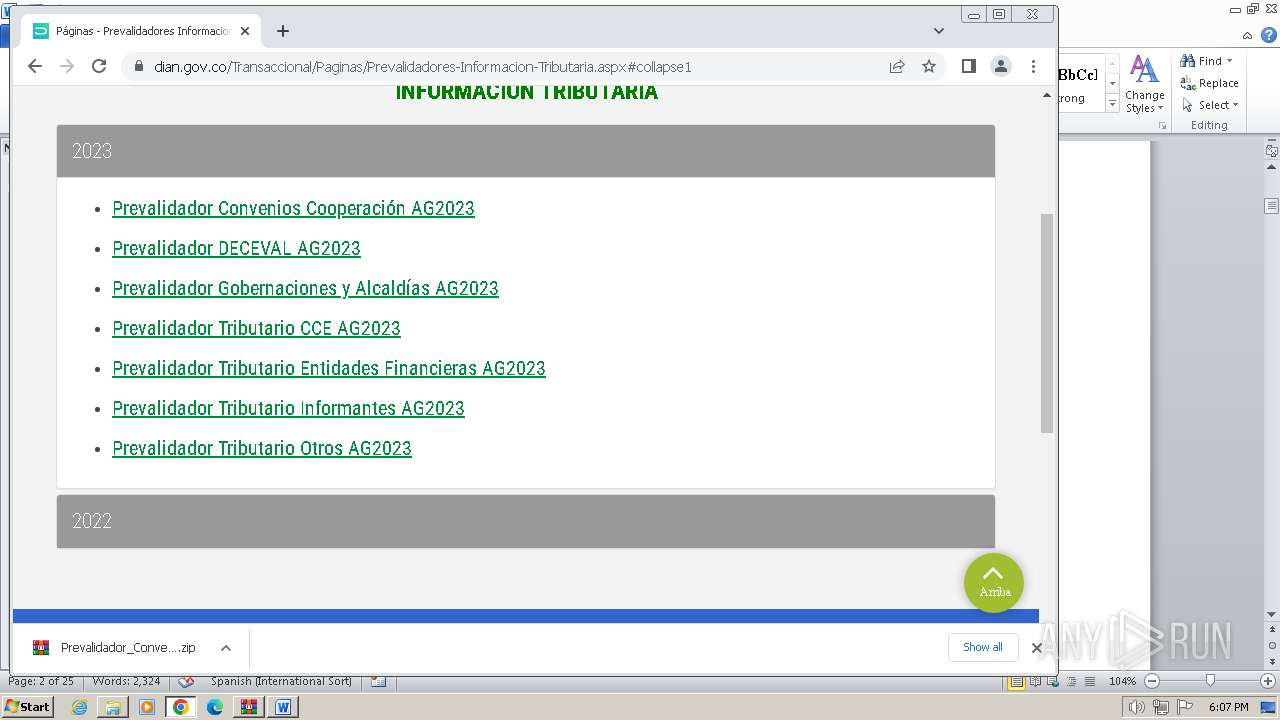
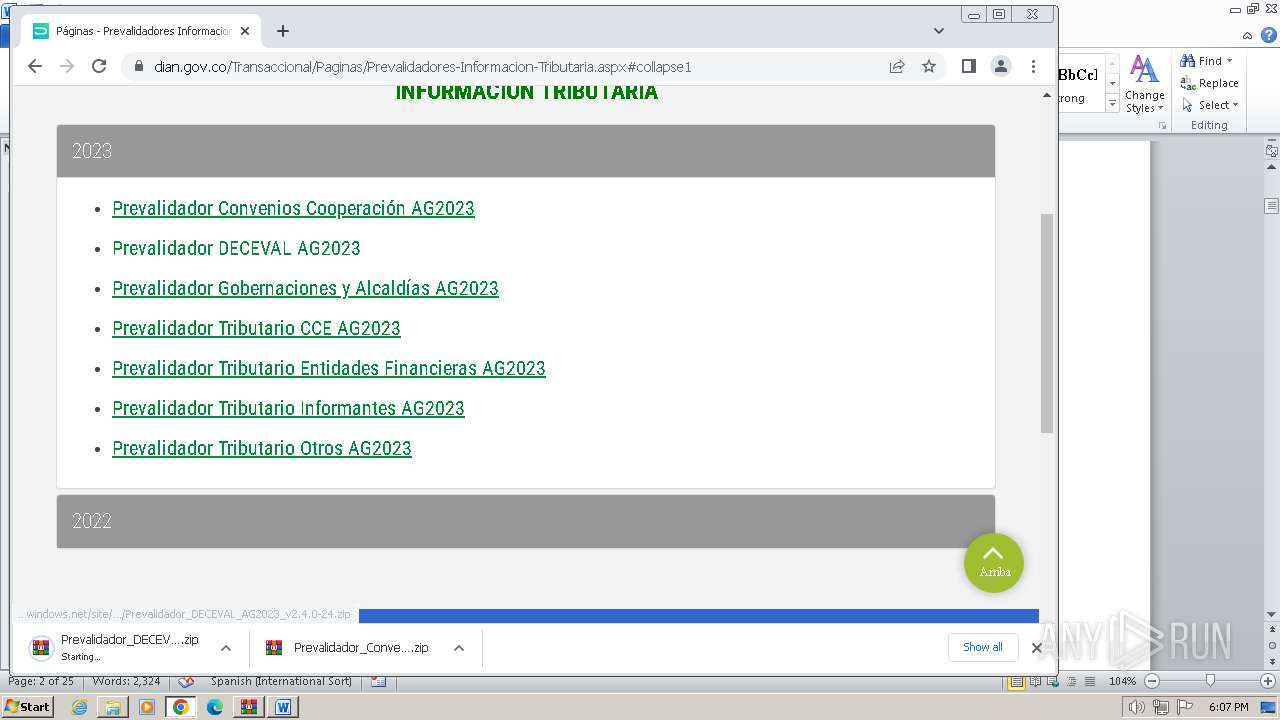
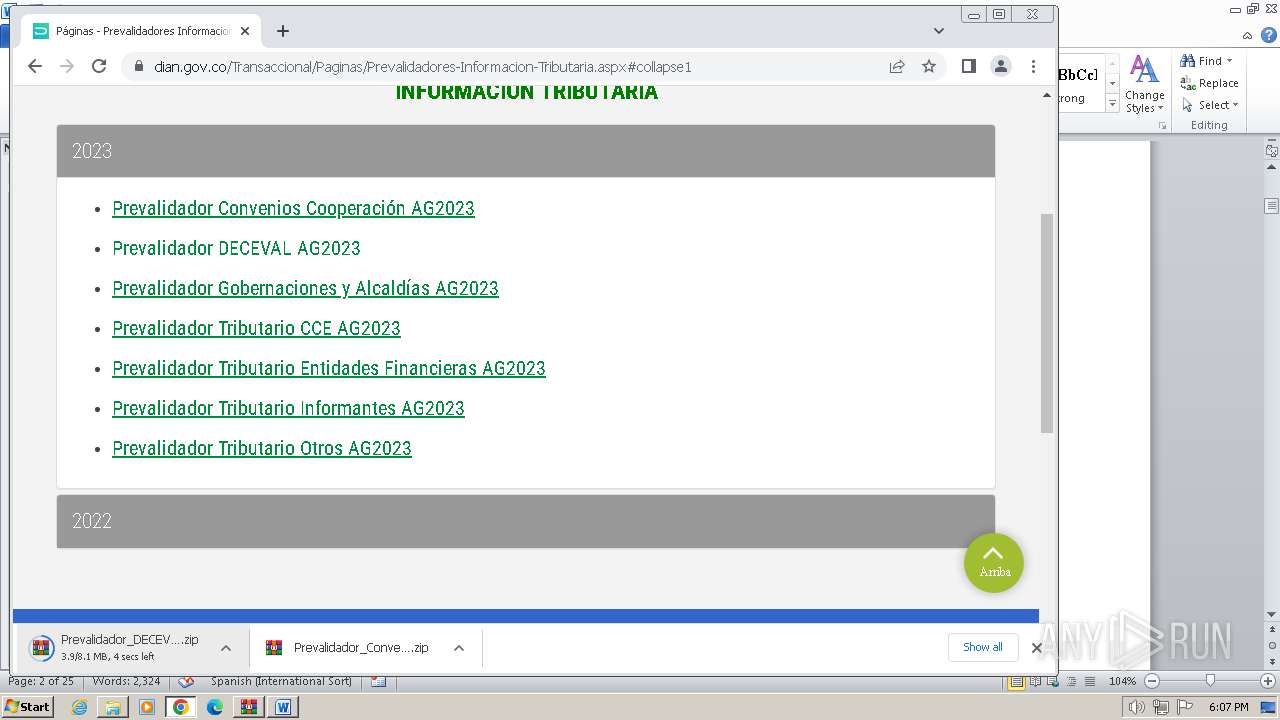
| URL: | https://www.dian.gov.co/Transaccional/Paginas/Prevalidadores-Informacion-Tributaria.aspx#collapse1 |
| Full analysis: | https://app.any.run/tasks/0c6b9e59-8216-4f8f-81f6-c0acc7ffb408 |
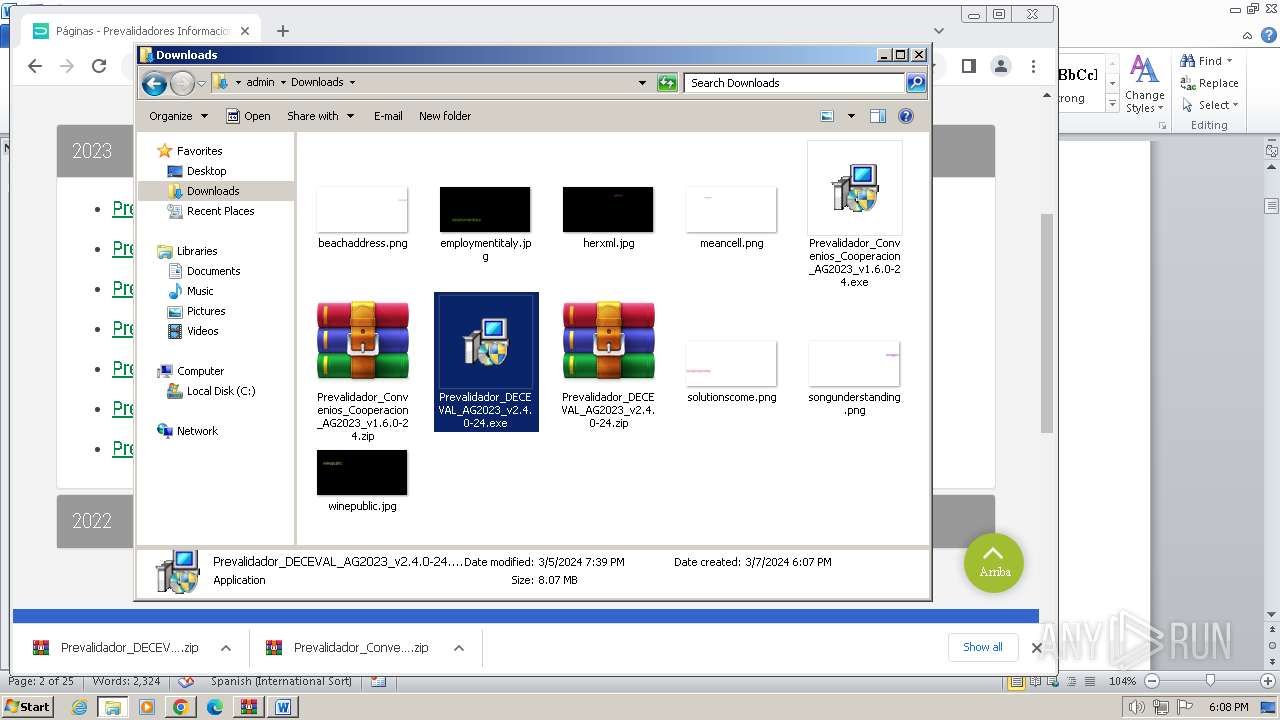
| Verdict: | Malicious activity |
| Analysis date: | March 07, 2024, 18:03:24 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
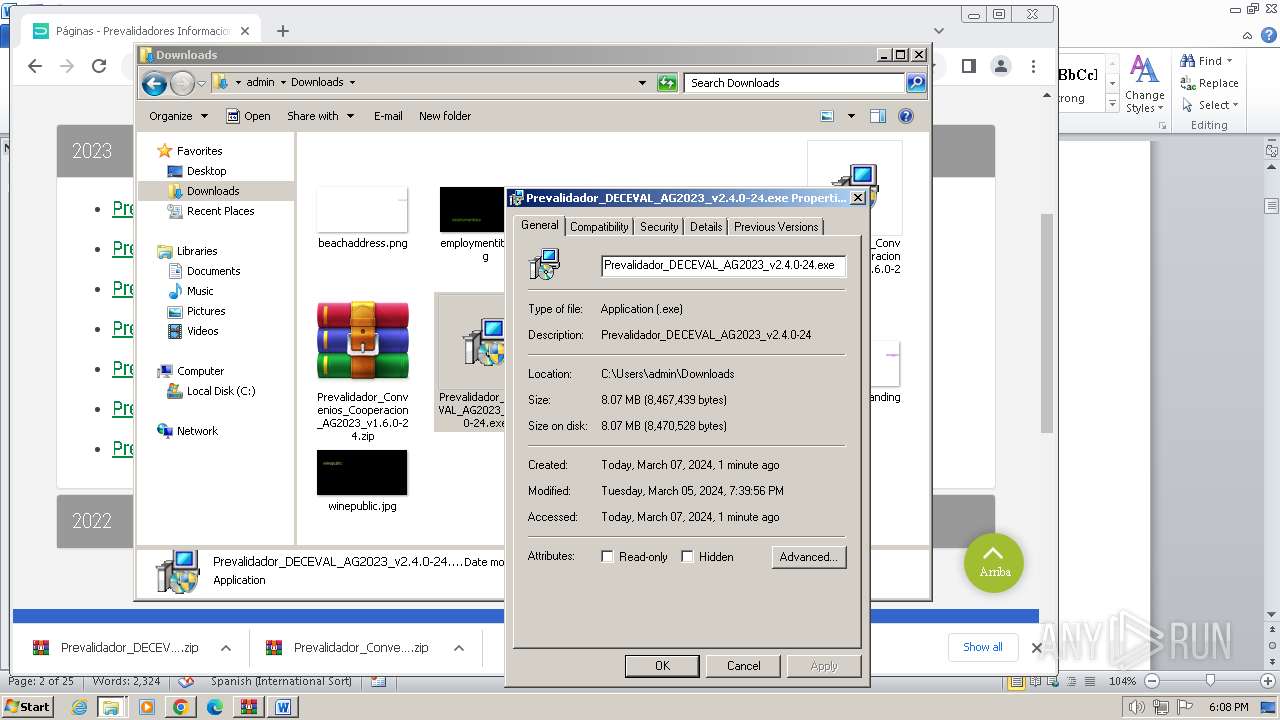
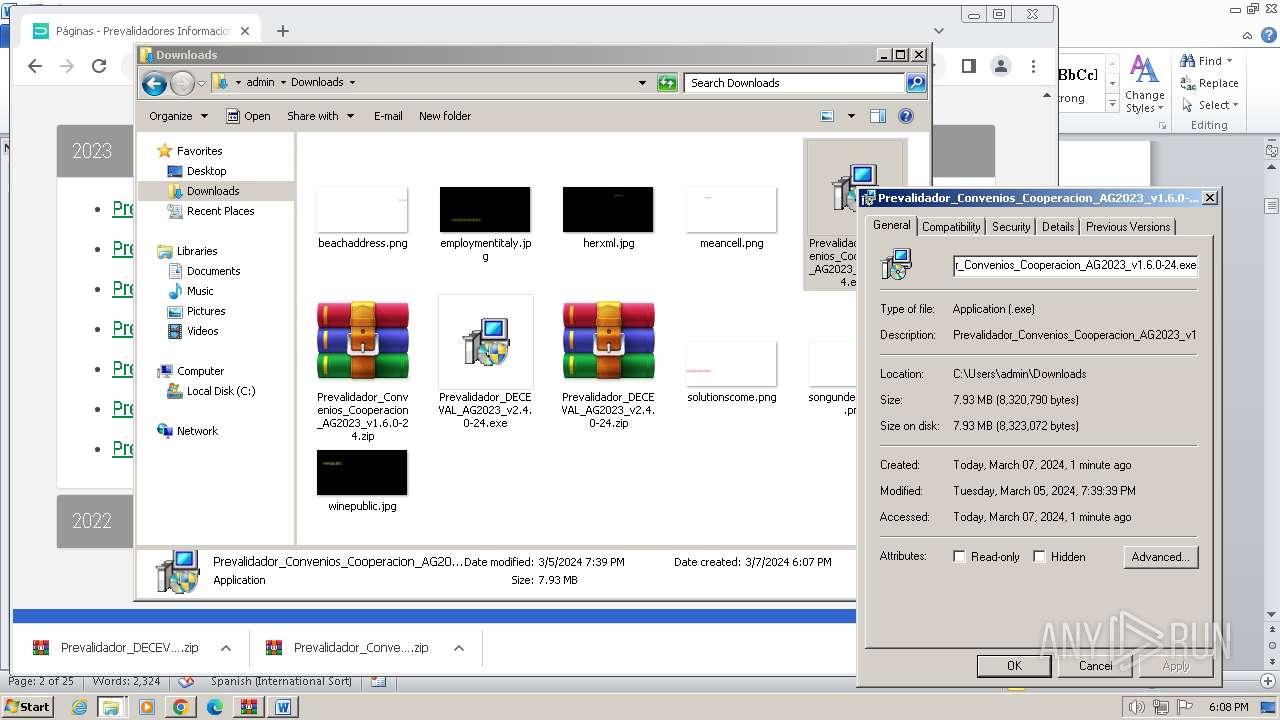
| MD5: | 73FEC81C7C9B215AE9DD8CA4F7D78169 |
| SHA1: | C5A0D27201E1600EFC7ADACEFC76E77D86F701C8 |
| SHA256: | 7DACE3CA79E9544F3ED7678AAAE8EBE15582BF954AC52250E85073309F3F80AC |
| SSDEEP: | 3:N8DSLH6xURMj2d2EC5XRQYM6EK3Gx:2OLH6iqSdG5XnP0 |
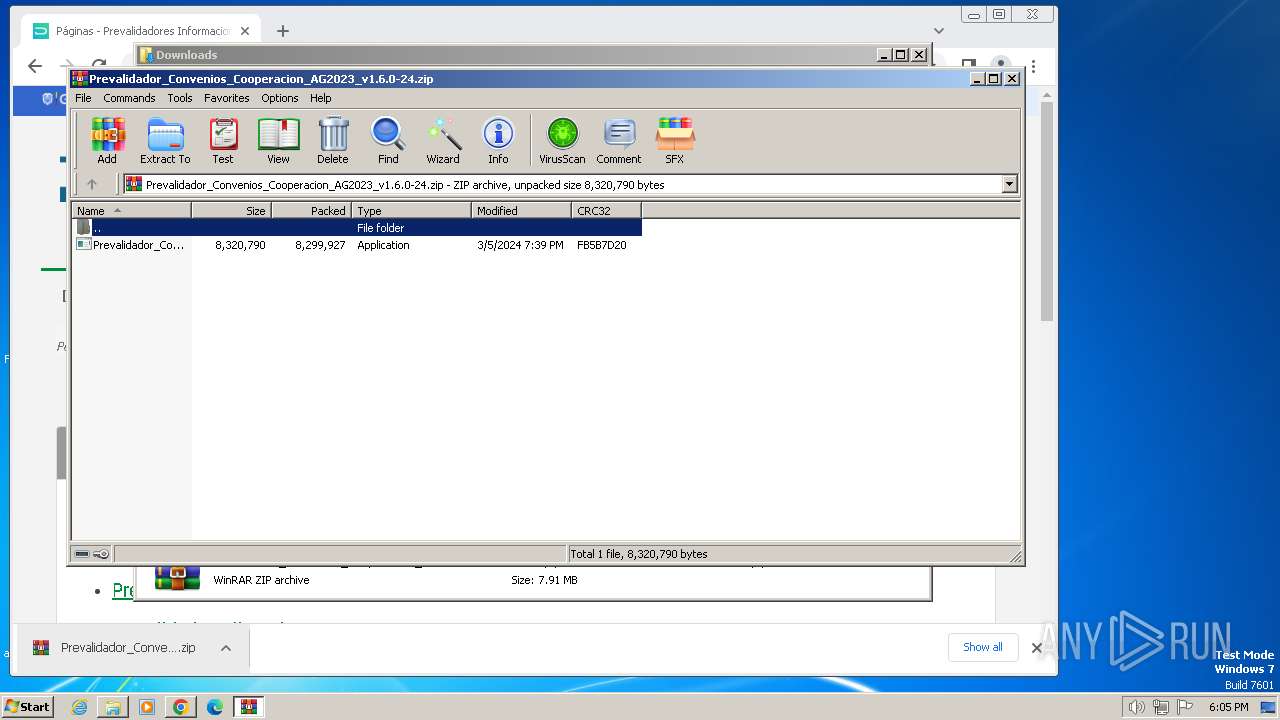
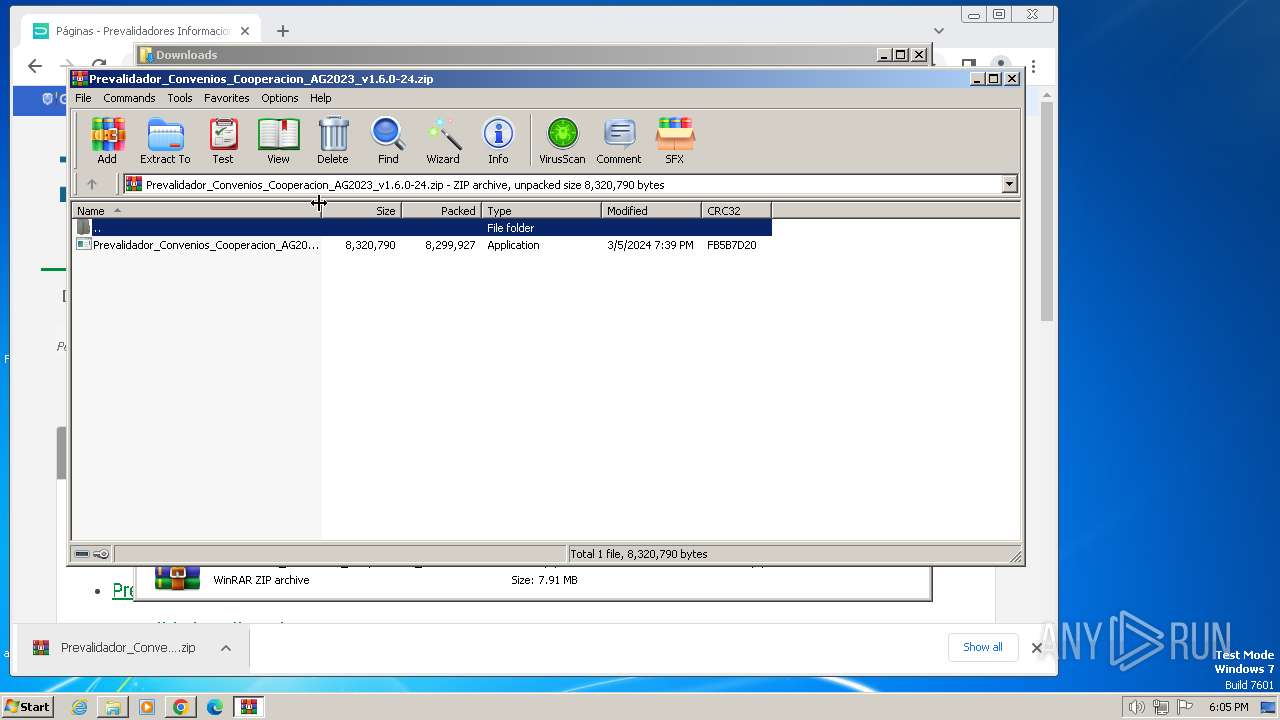
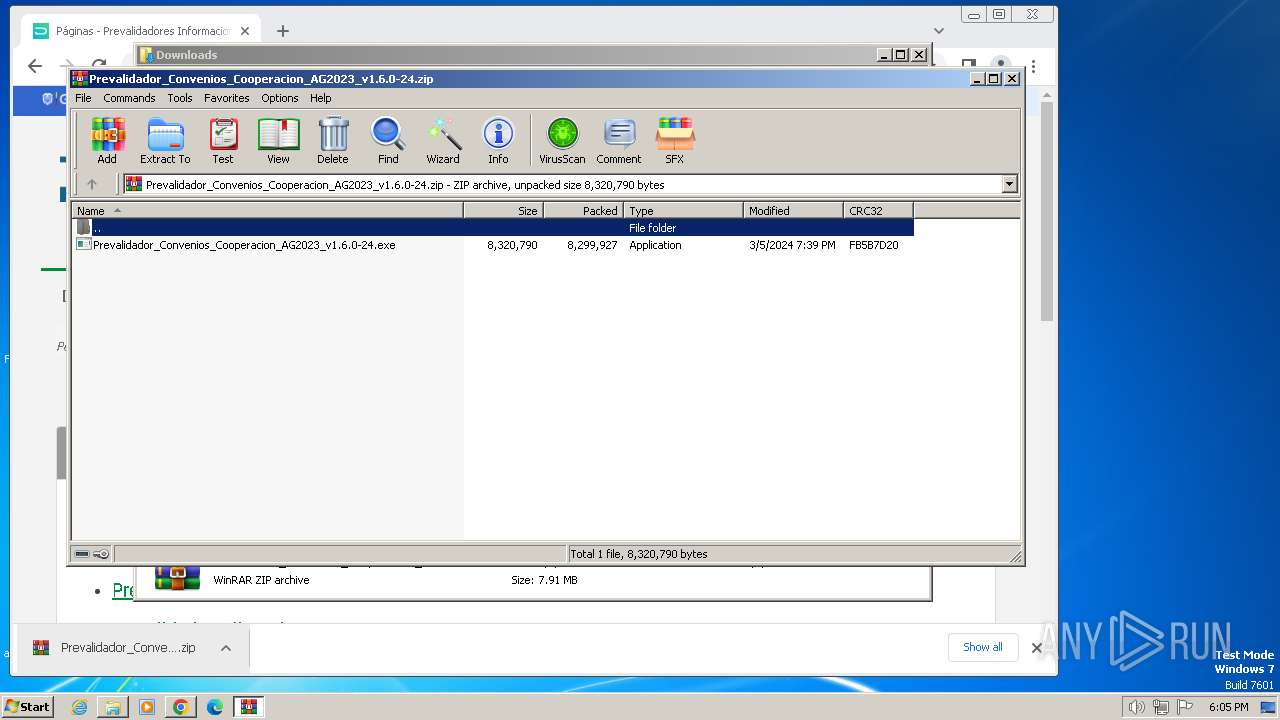
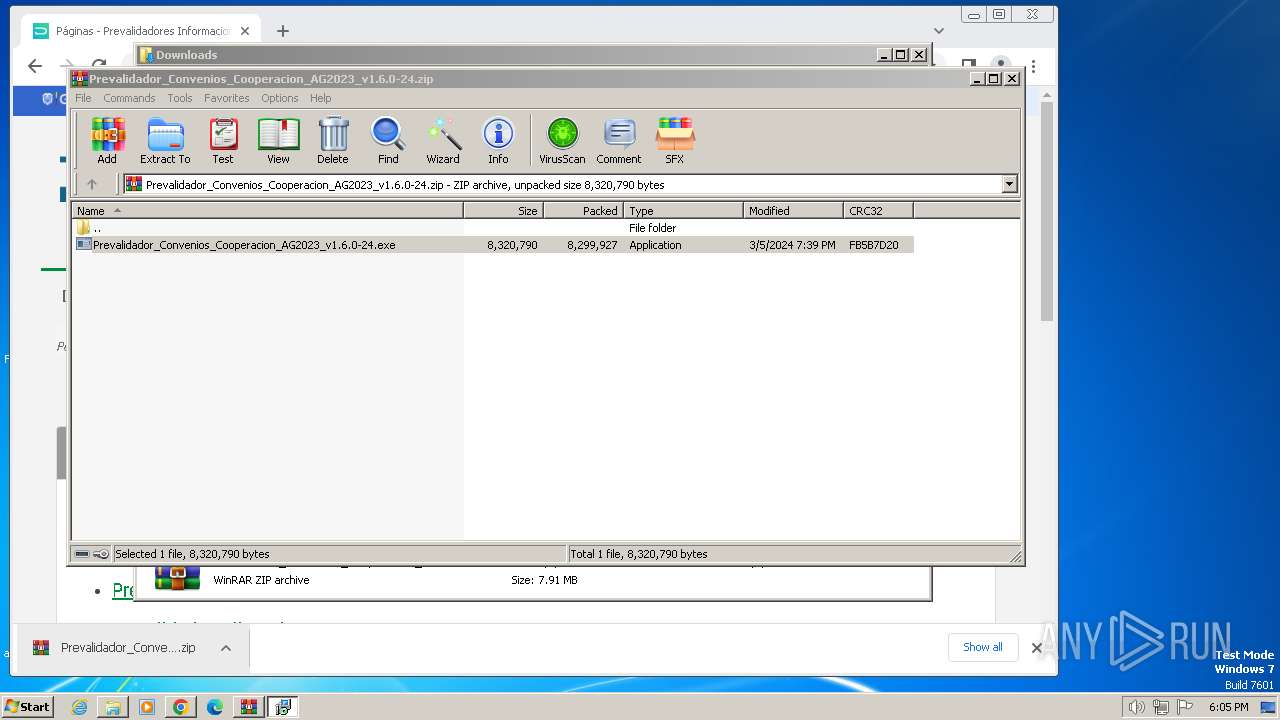
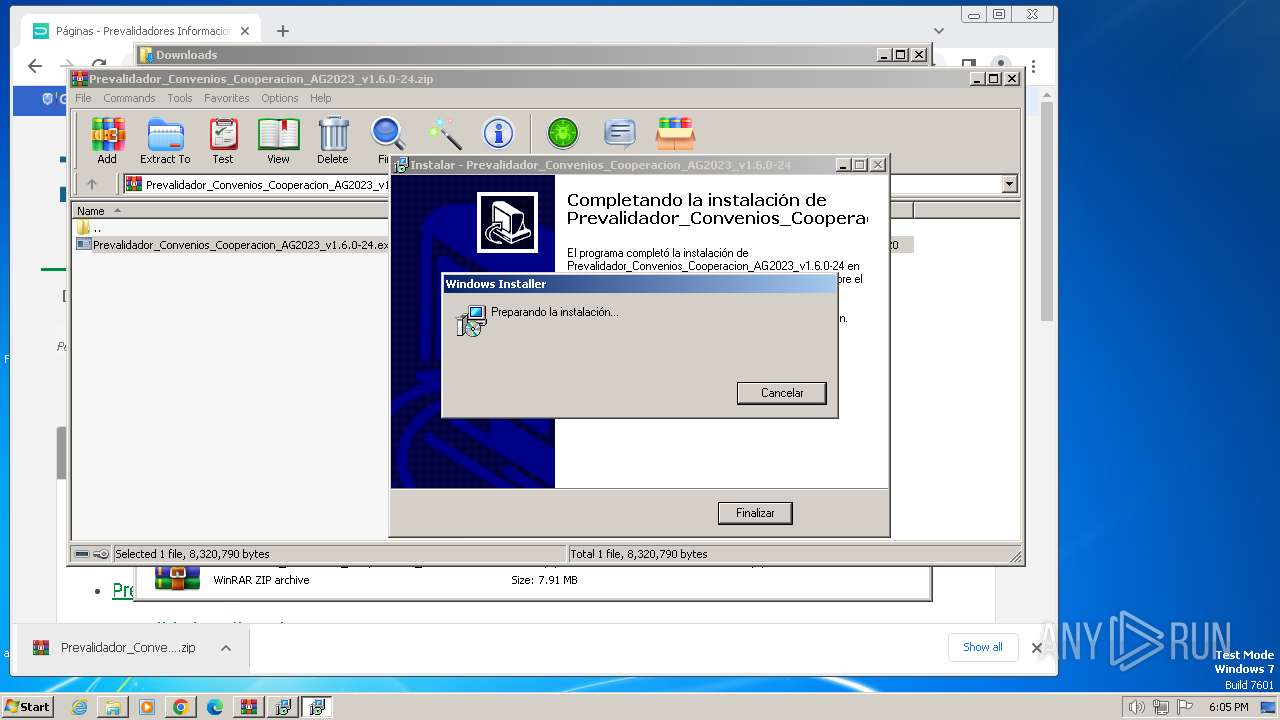
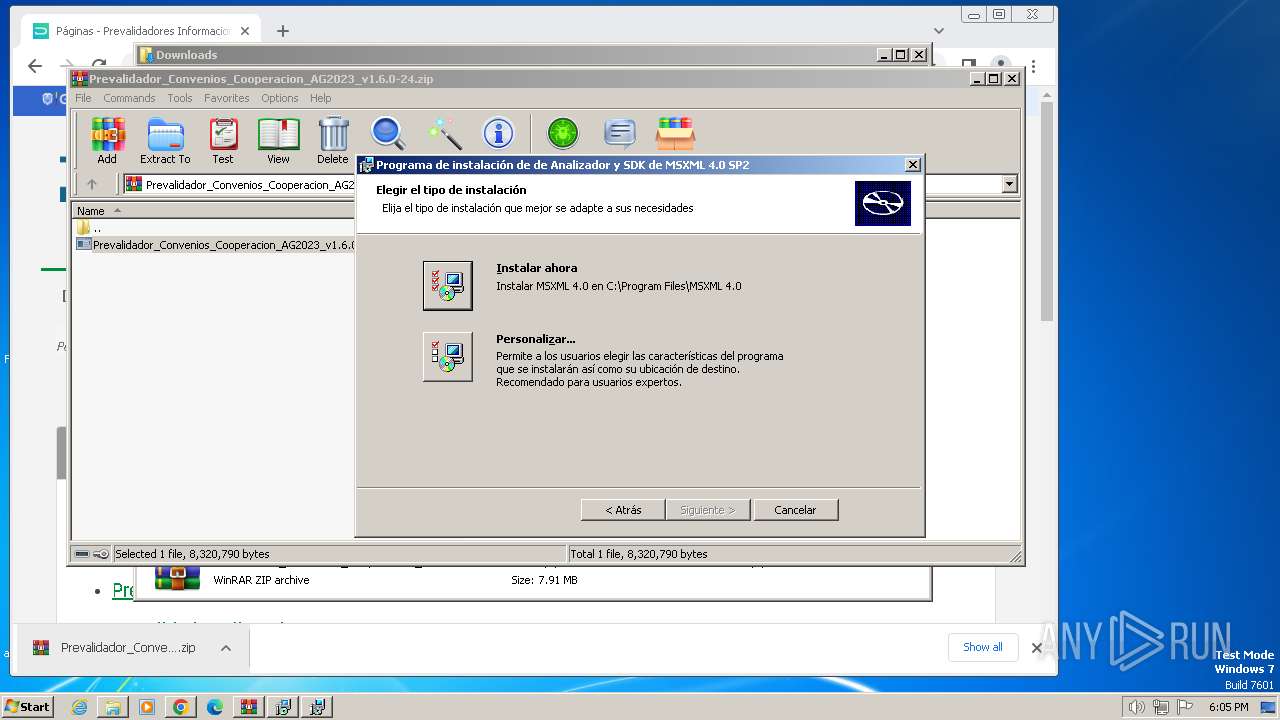
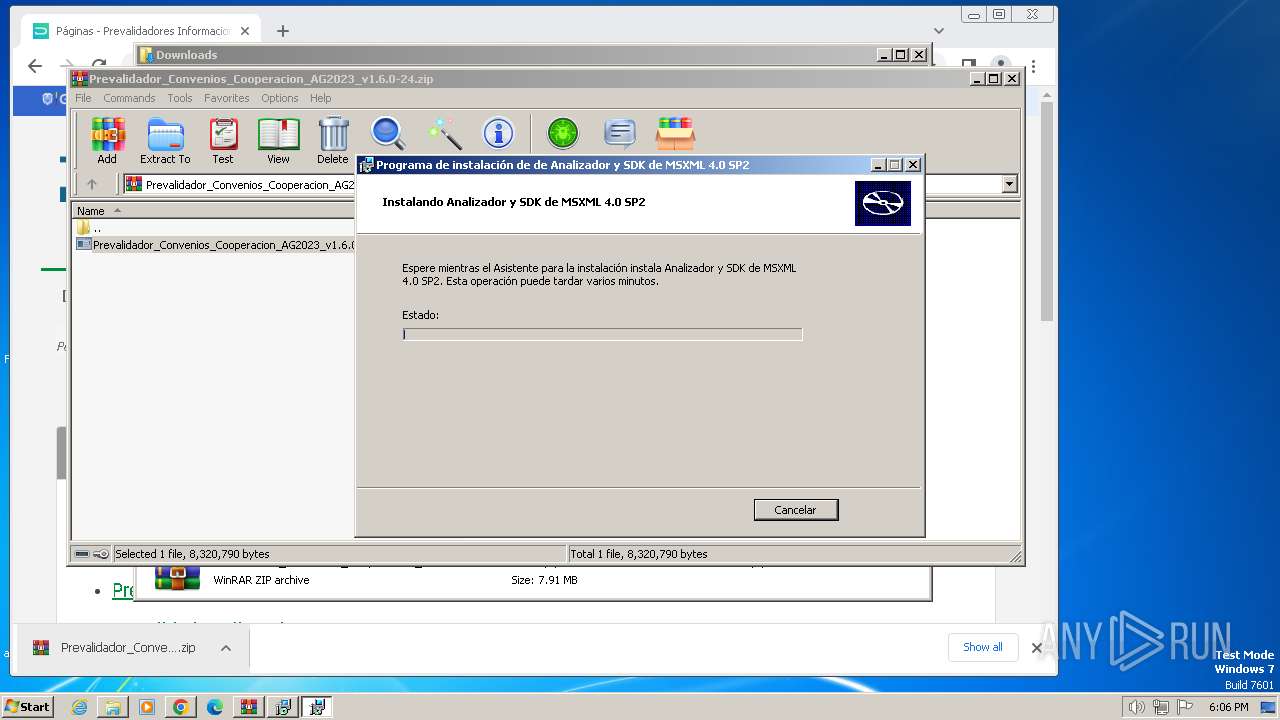
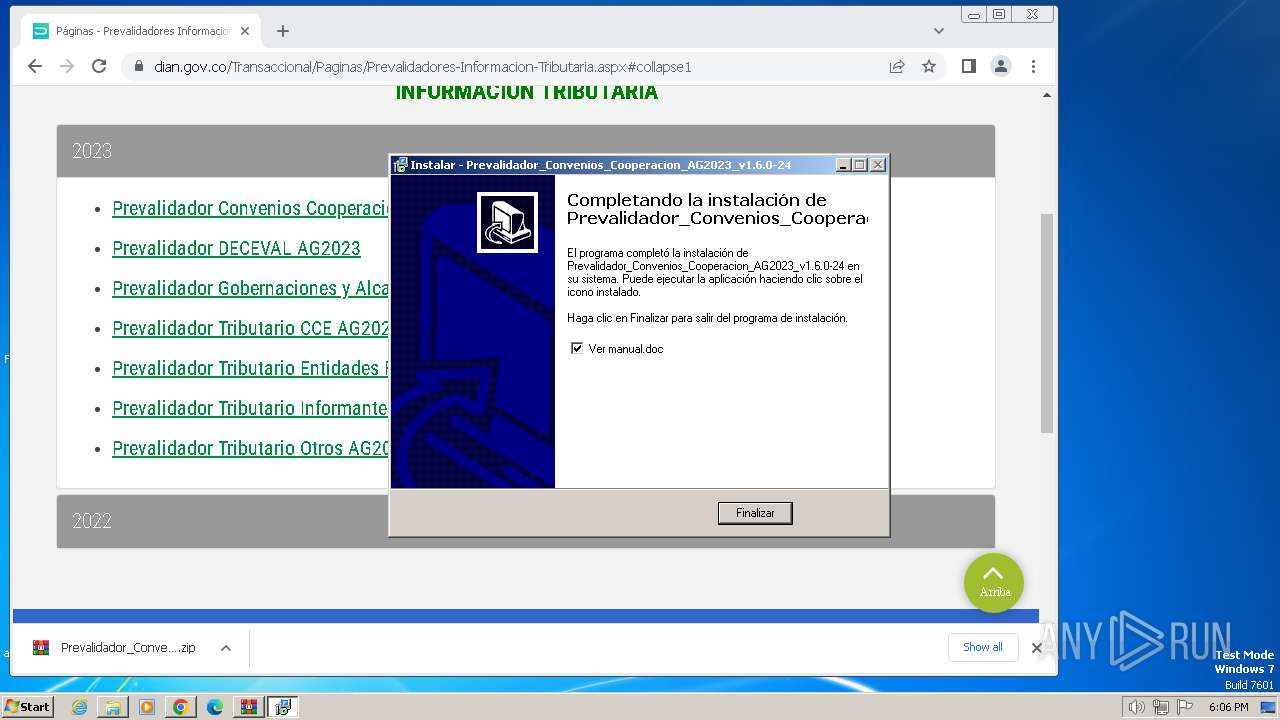
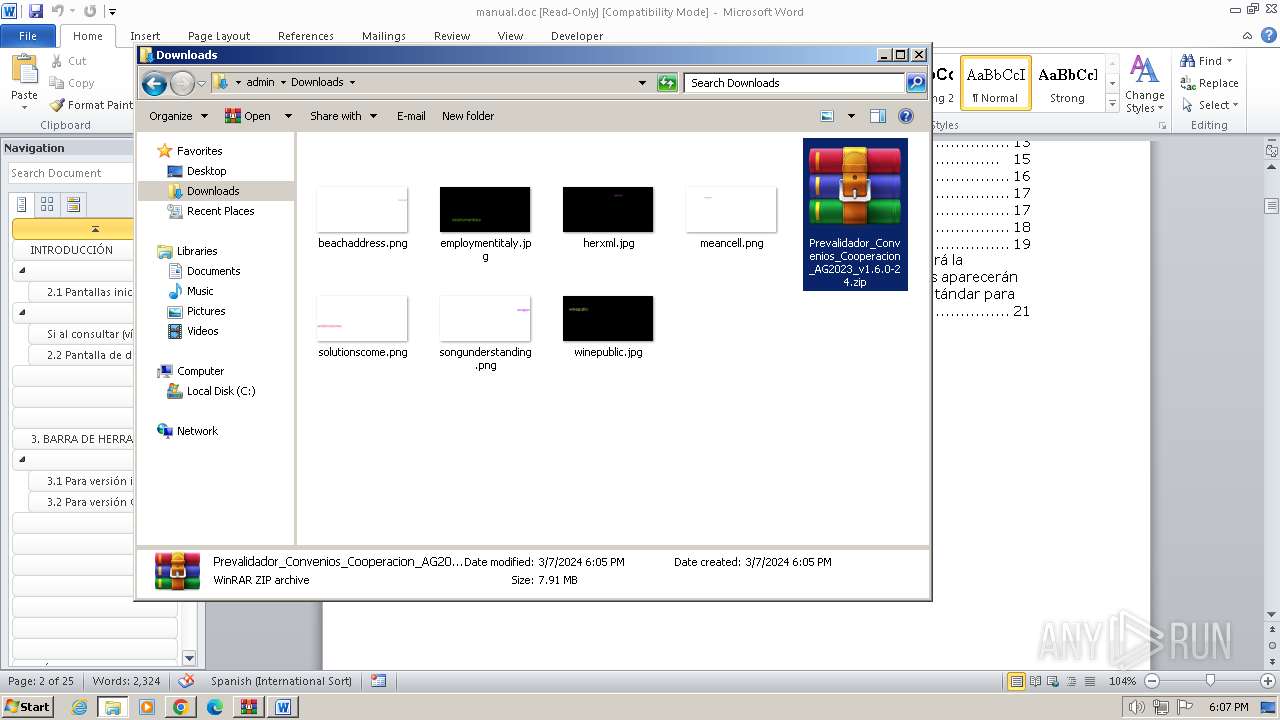
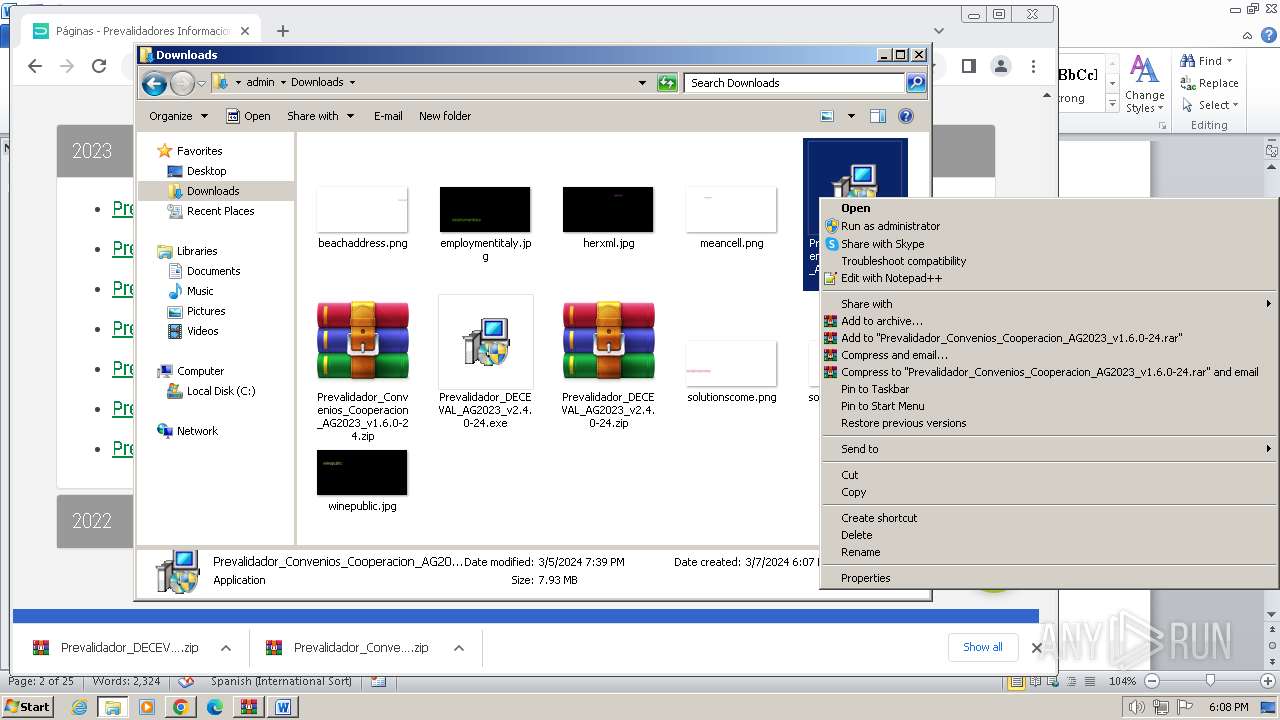
MALICIOUS
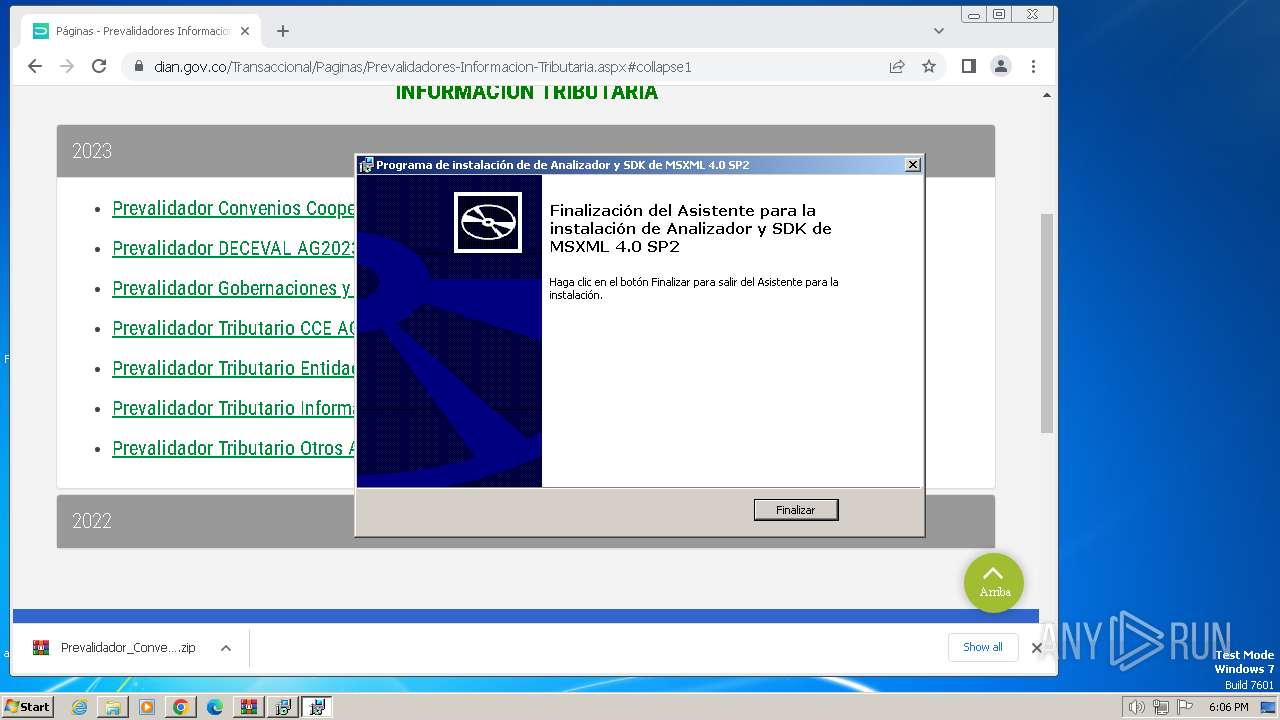
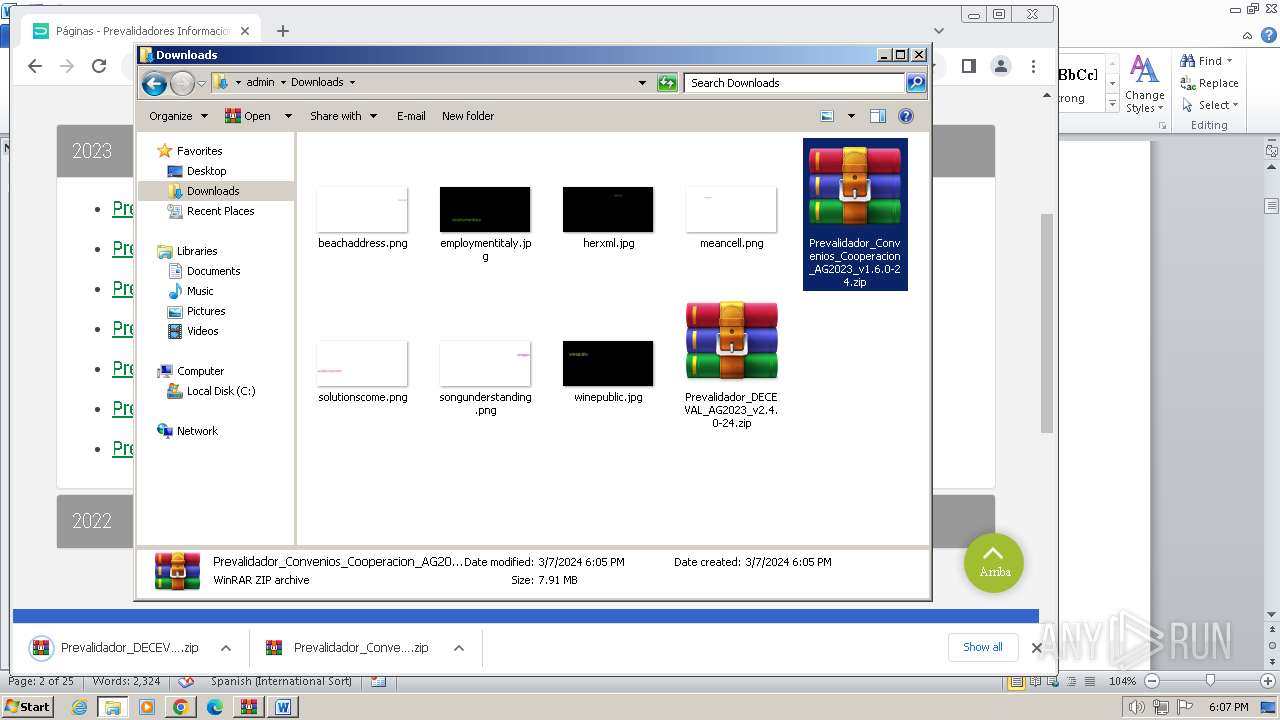
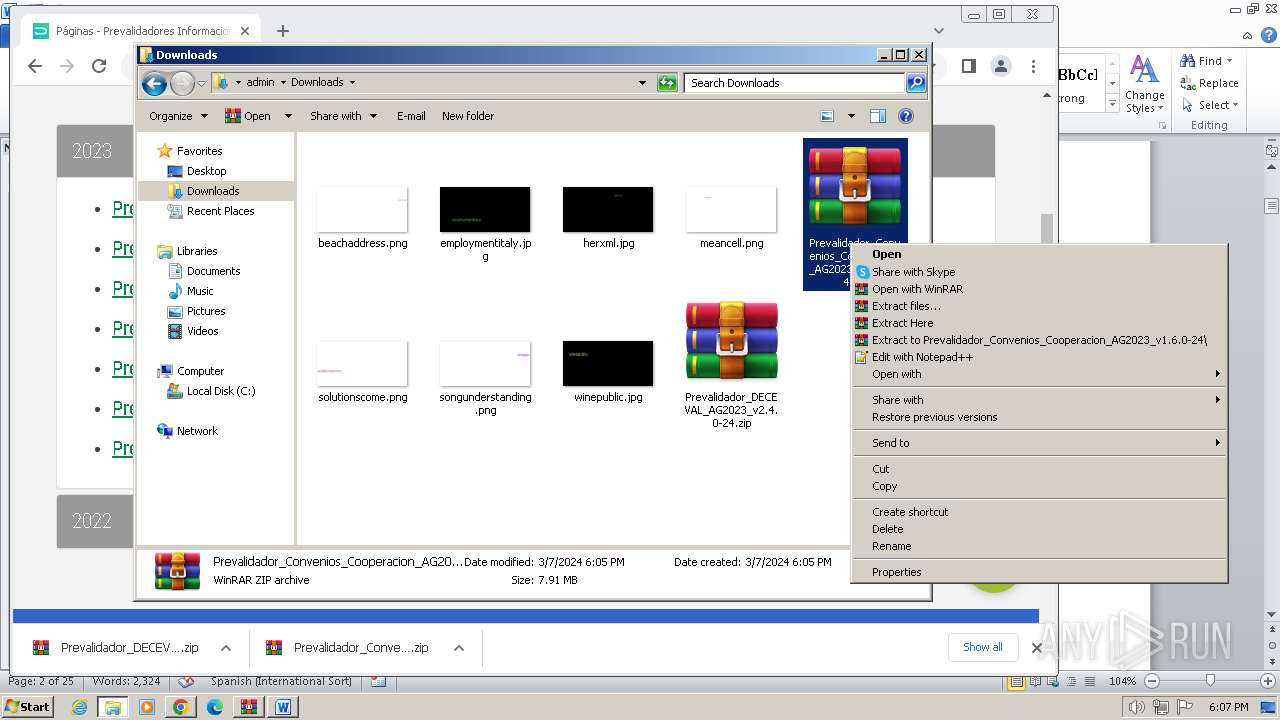
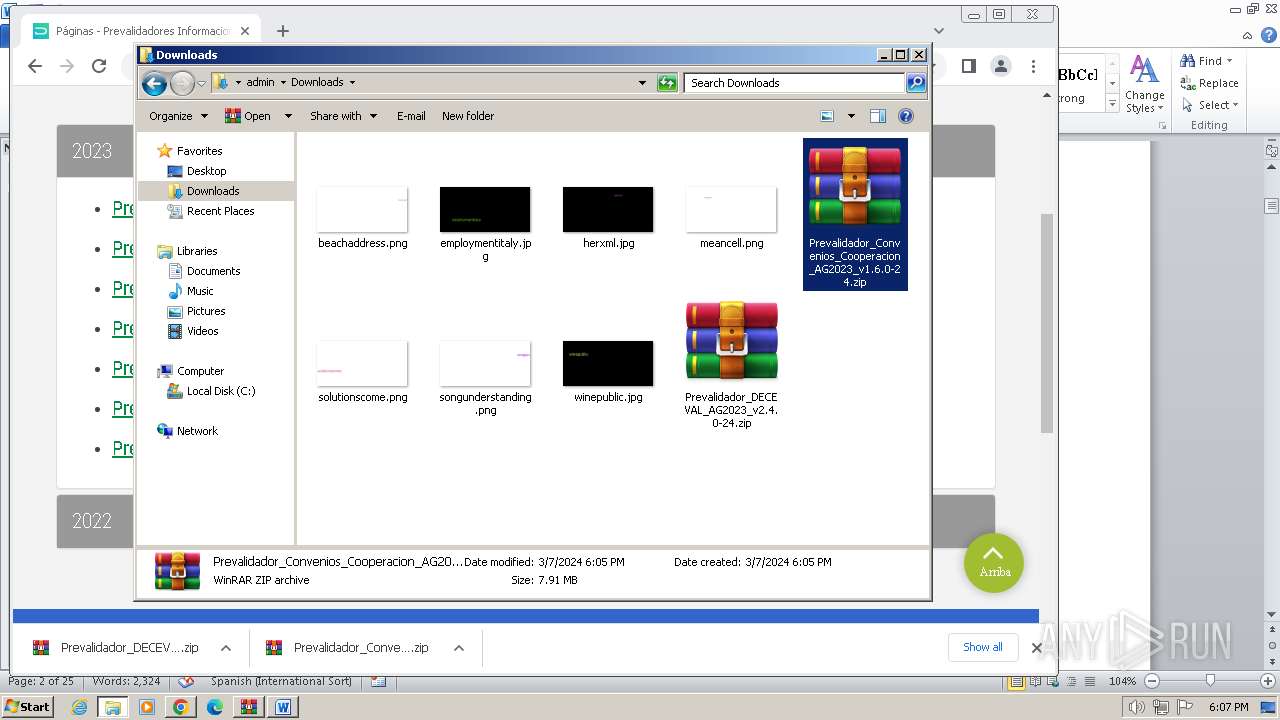
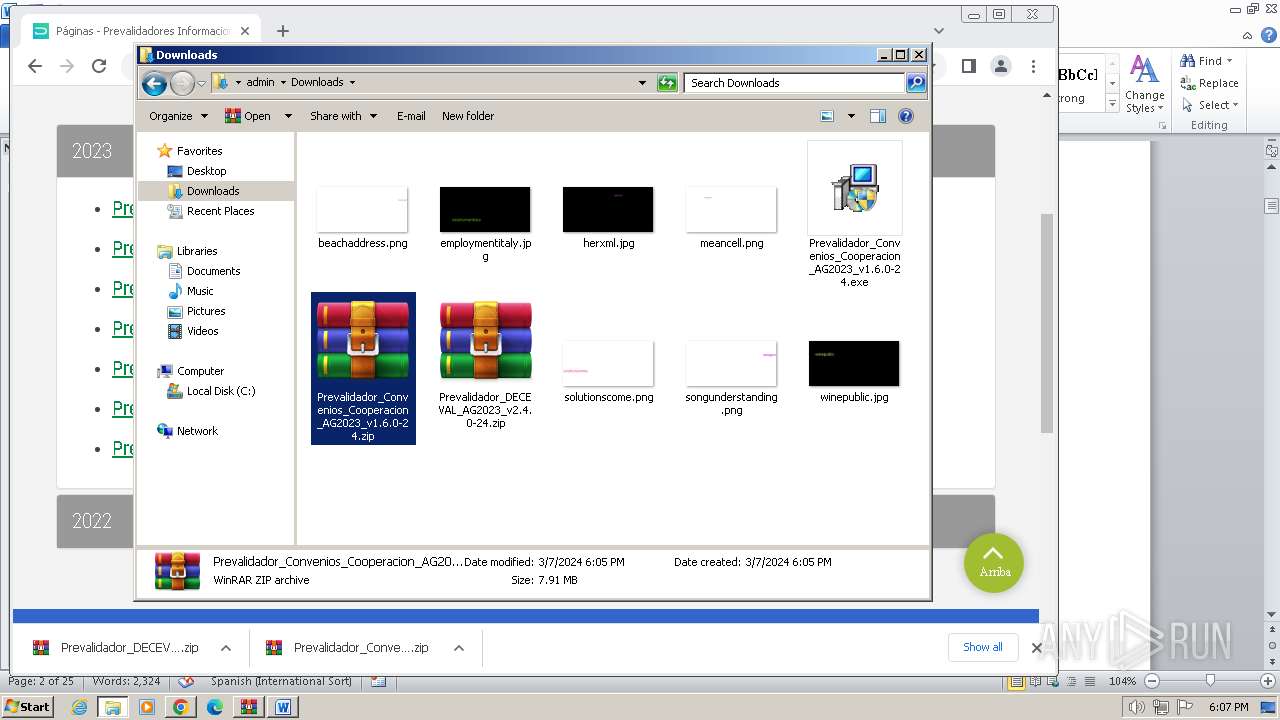
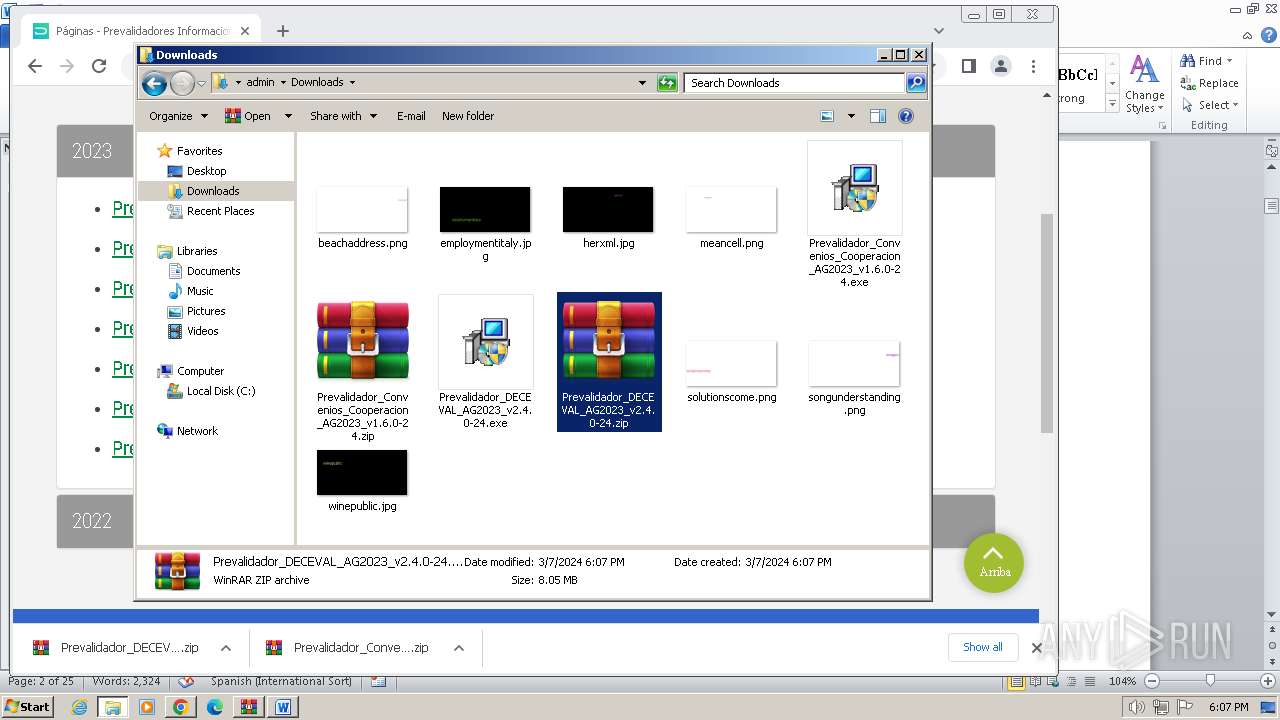
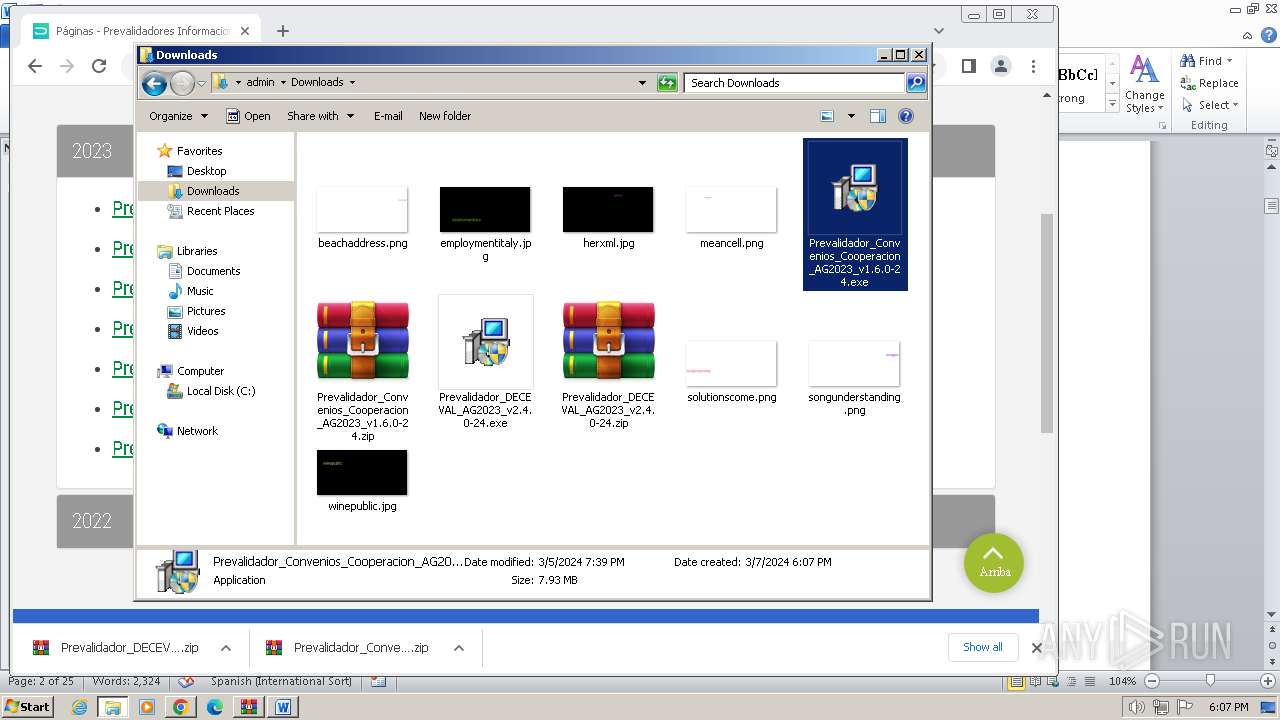
Drops the executable file immediately after the start
- Prevalidador_Convenios_Cooperacion_AG2023_v1.6.0-24.exe (PID: 2480)
- is-VIIN5.tmp (PID: 2516)
SUSPICIOUS
Reads security settings of Internet Explorer
- WinRAR.exe (PID: 2752)
- is-VIIN5.tmp (PID: 2516)
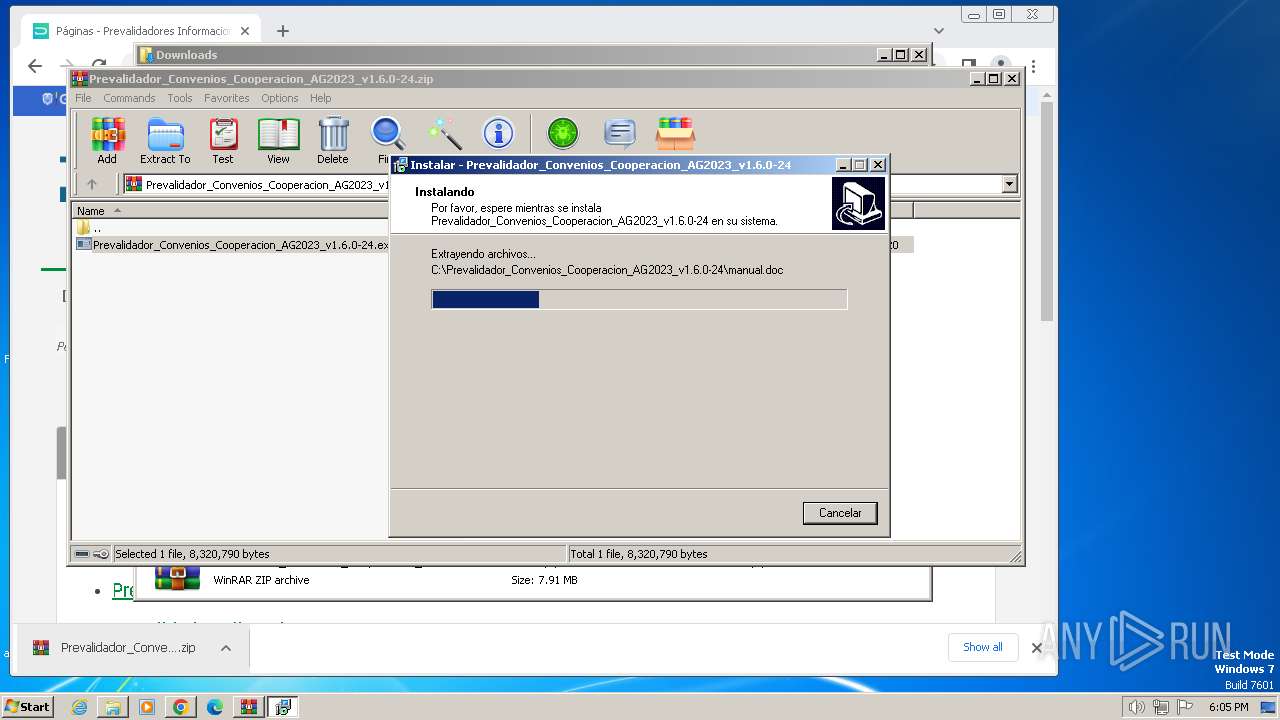
Executable content was dropped or overwritten
- Prevalidador_Convenios_Cooperacion_AG2023_v1.6.0-24.exe (PID: 2480)
- is-VIIN5.tmp (PID: 2516)
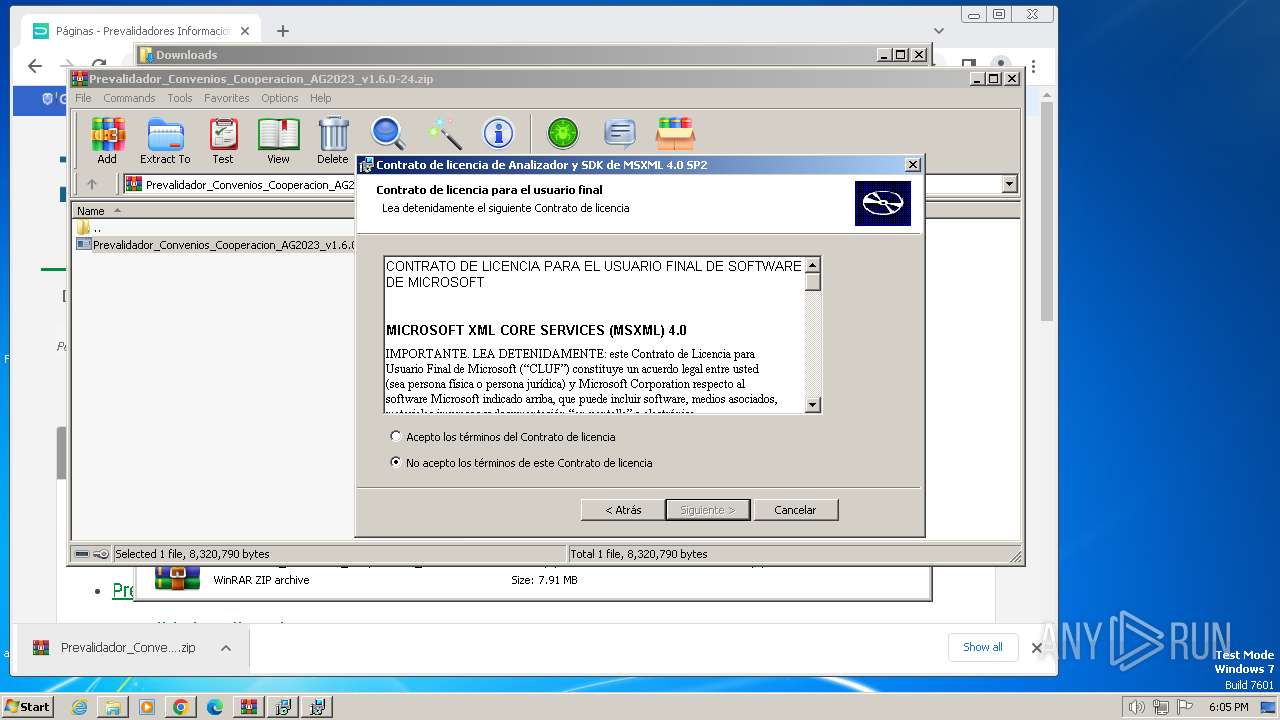
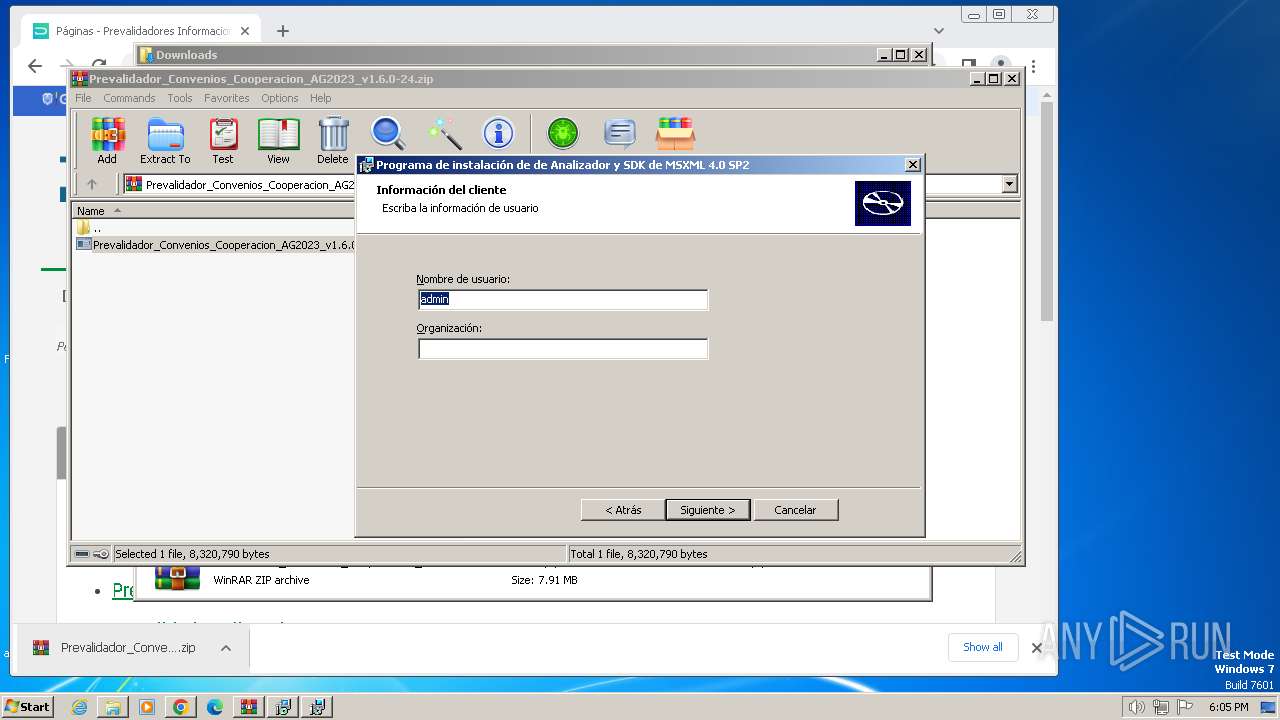
Reads the Windows owner or organization settings
- is-VIIN5.tmp (PID: 2516)
Process drops legitimate windows executable
- is-VIIN5.tmp (PID: 2516)
Non-standard symbols in registry
- WINWORD.EXE (PID: 3584)
Reads the Internet Settings
- is-VIIN5.tmp (PID: 2516)
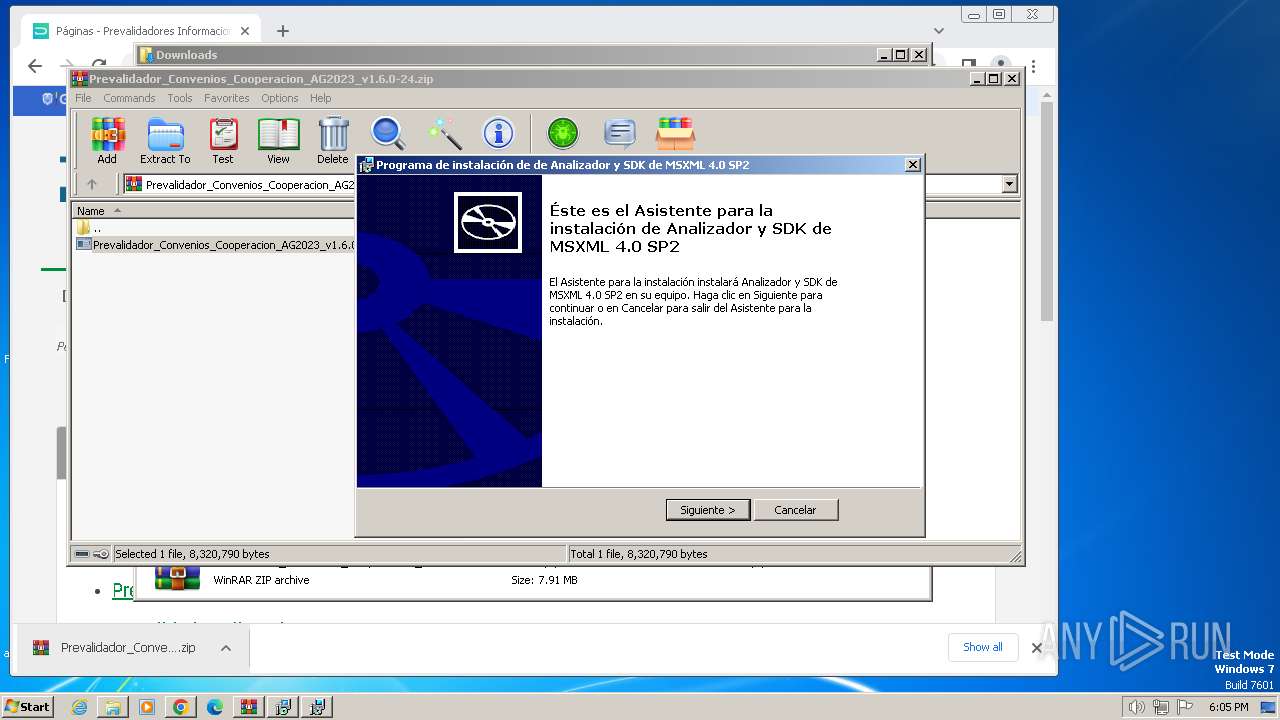
Adds/modifies Windows certificates
- msiexec.exe (PID: 3784)
Executes as Windows Service
- VSSVC.exe (PID: 664)
Creates/Modifies COM task schedule object
- WINWORD.EXE (PID: 3584)
Changes default file association
- WINWORD.EXE (PID: 3584)
INFO
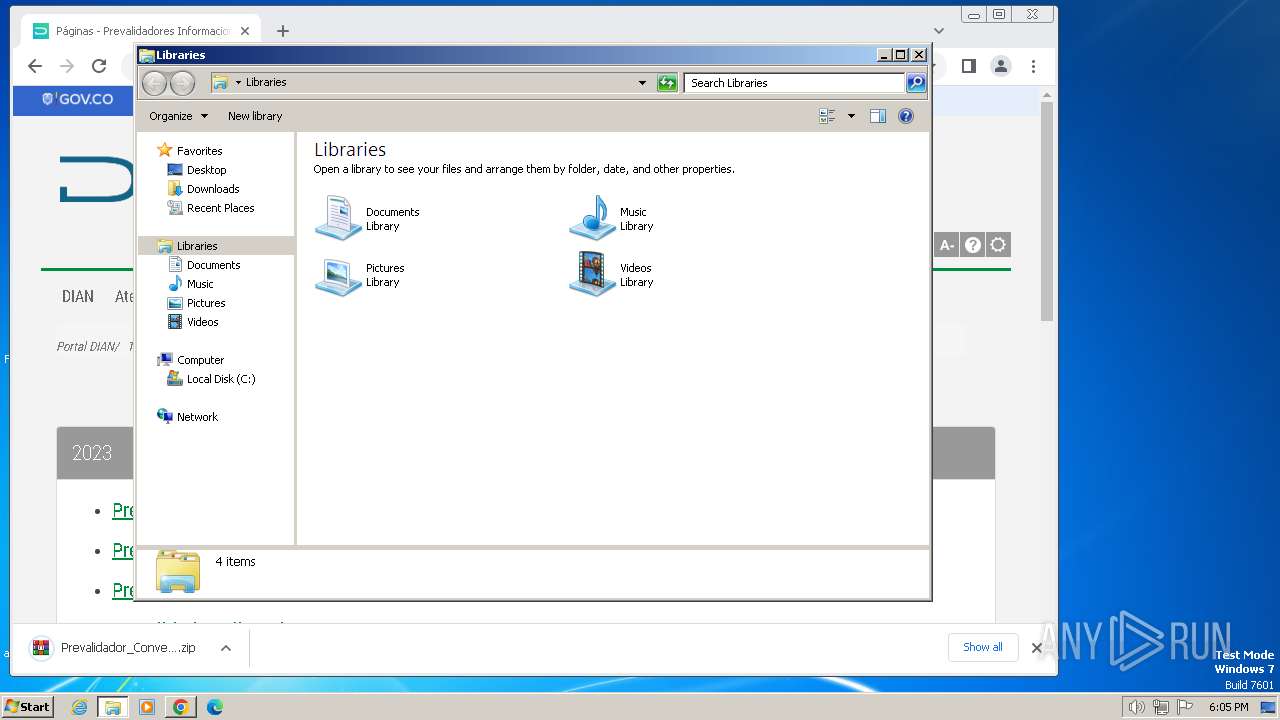
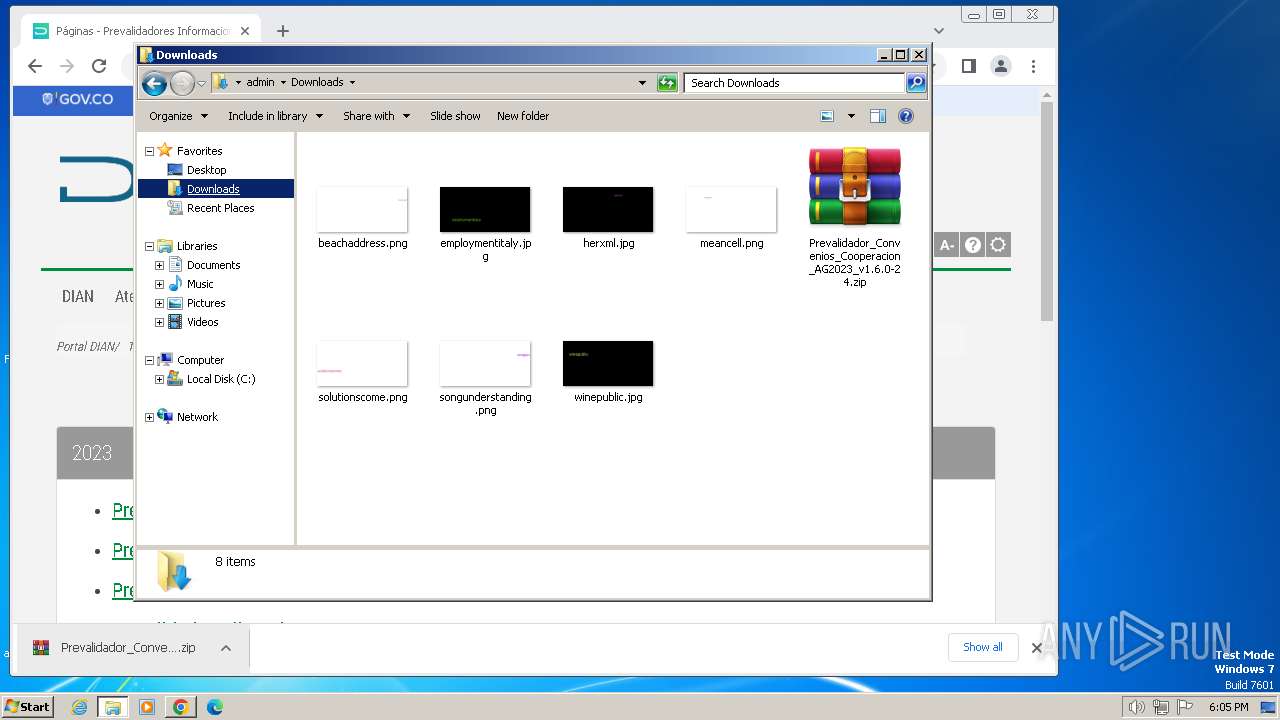
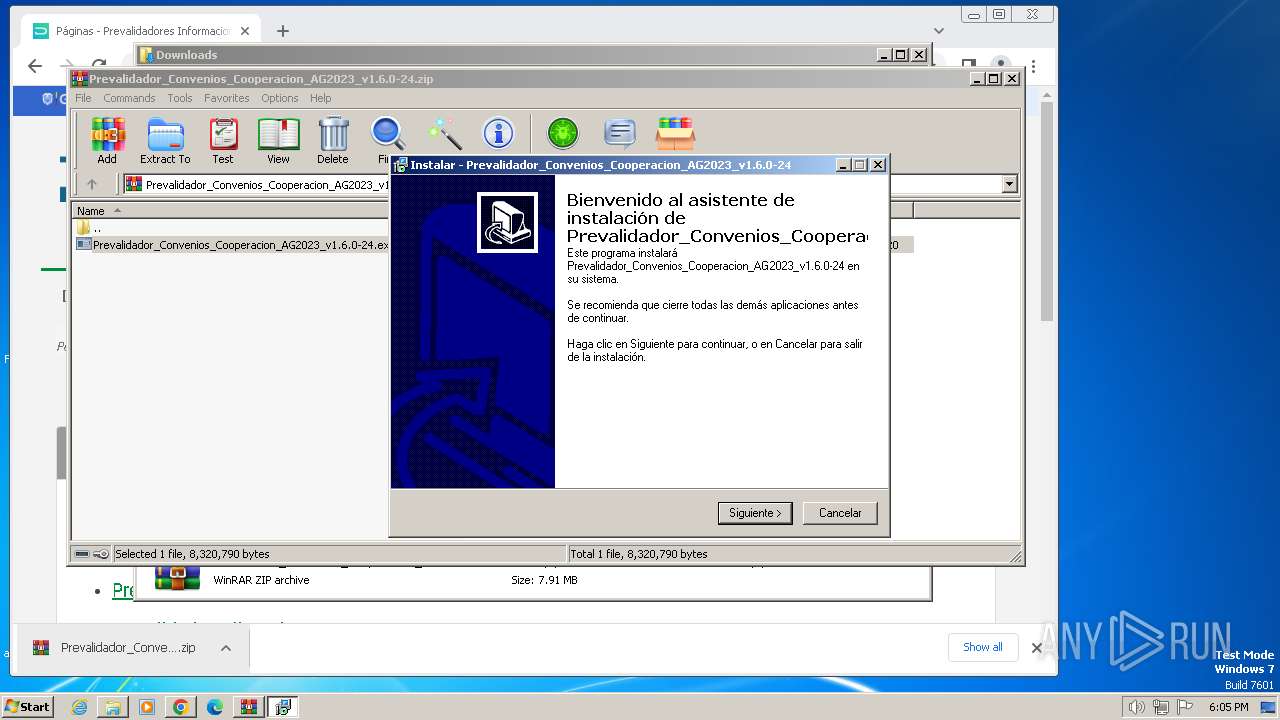
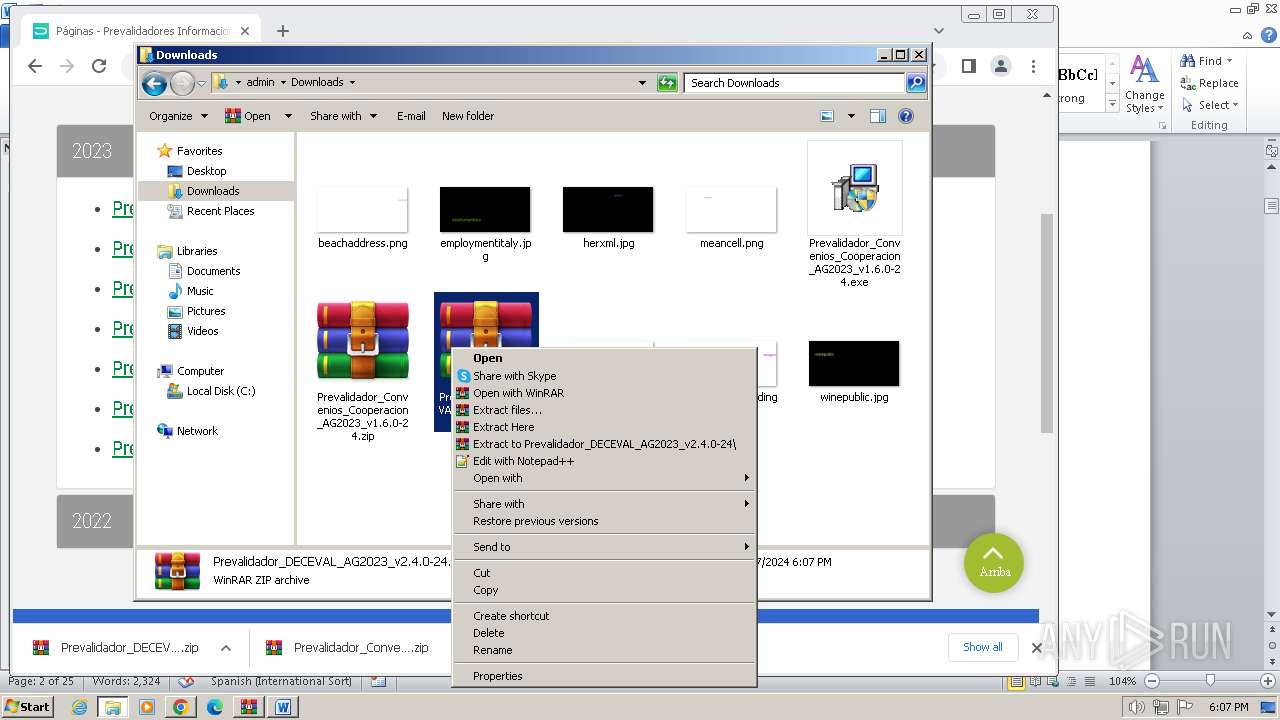
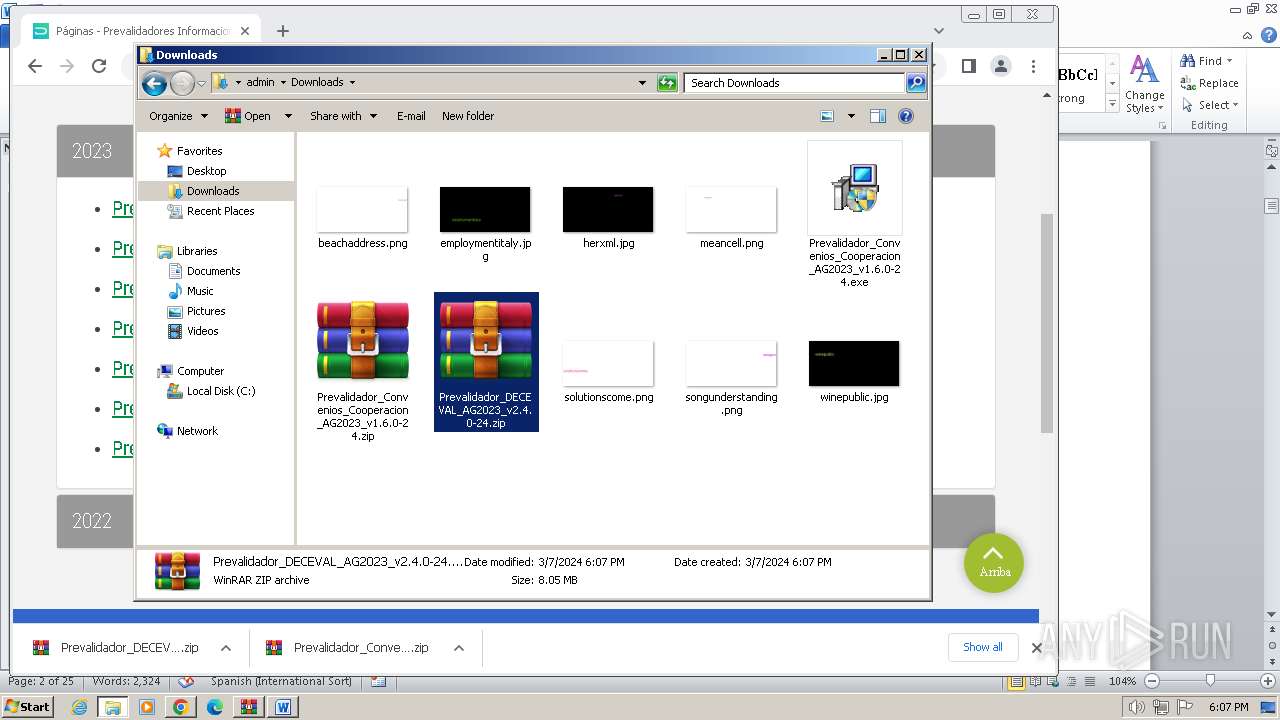
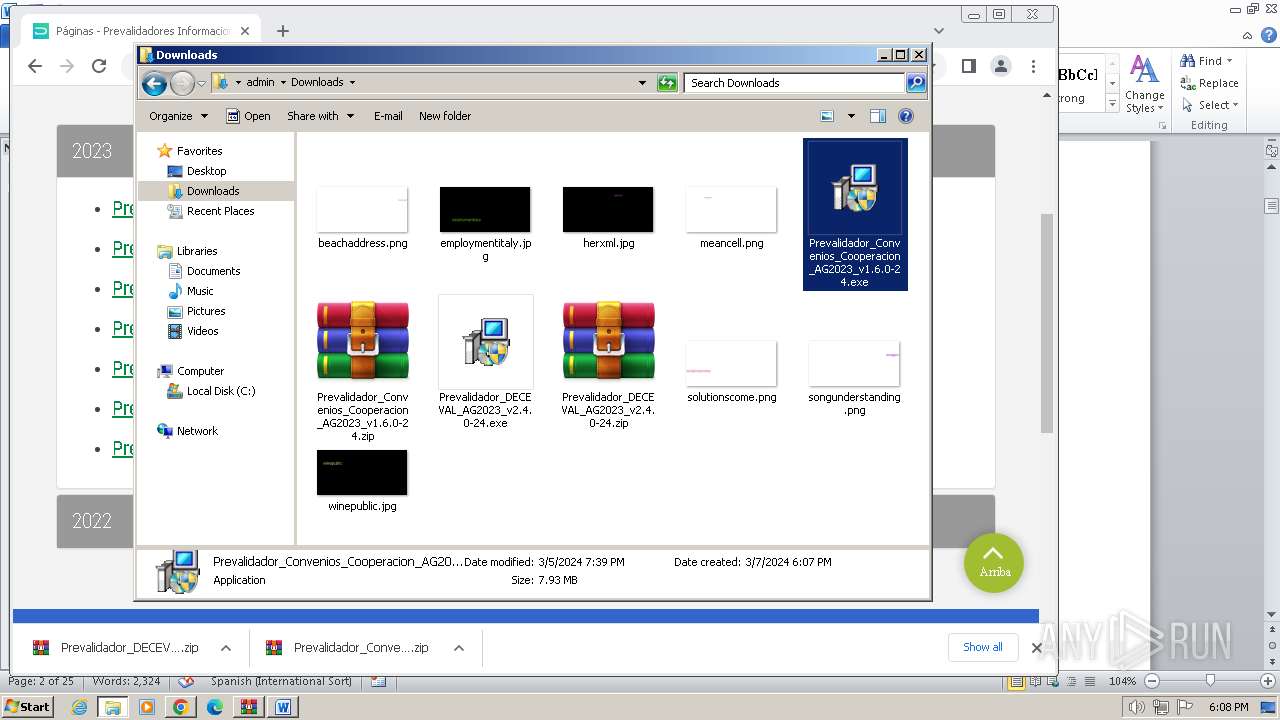
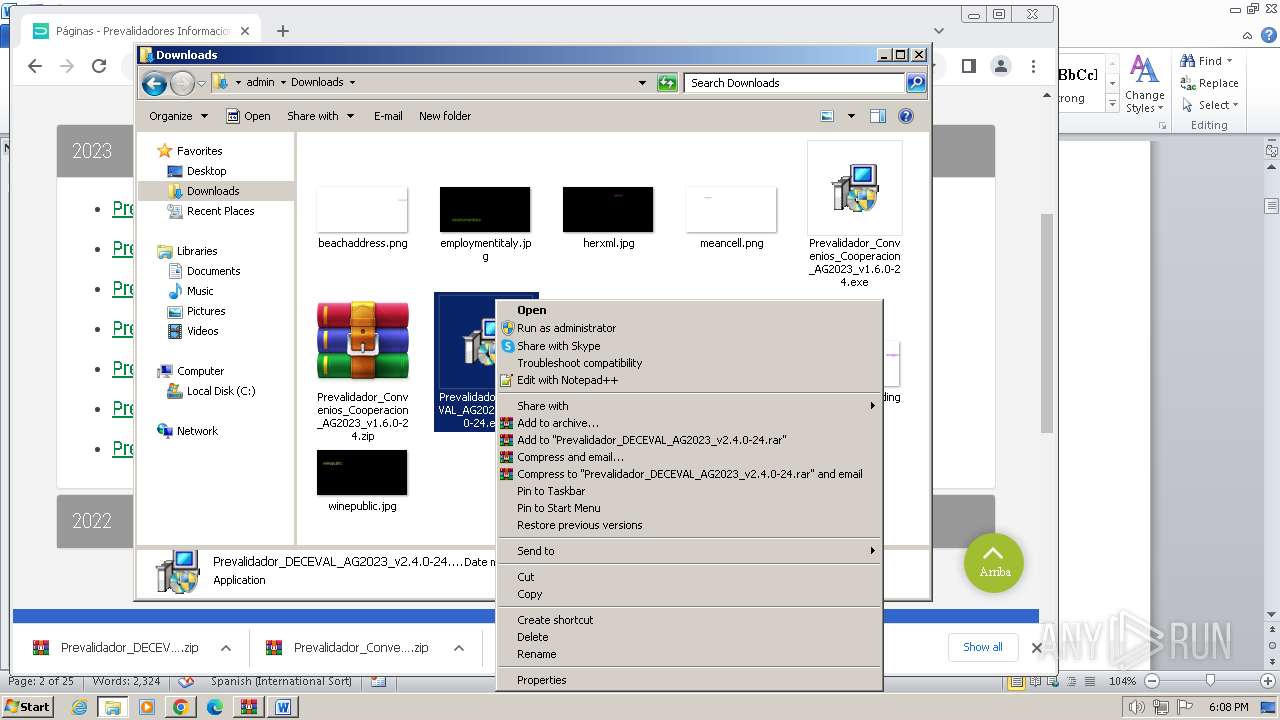
Manual execution by a user
- chrome.exe (PID: 3964)
- explorer.exe (PID: 3380)
- WinRAR.exe (PID: 2752)
- WinRAR.exe (PID: 3668)
- WinRAR.exe (PID: 2304)
Application launched itself
- iexplore.exe (PID: 3672)
- chrome.exe (PID: 3964)
Executable content was dropped or overwritten
- chrome.exe (PID: 2764)
- WinRAR.exe (PID: 2752)
- chrome.exe (PID: 2980)
- WinRAR.exe (PID: 3668)
- WinRAR.exe (PID: 2304)
- chrome.exe (PID: 3124)
Drops the executable file immediately after the start
- chrome.exe (PID: 2764)
- chrome.exe (PID: 3964)
- WinRAR.exe (PID: 2752)
- chrome.exe (PID: 2980)
- WinRAR.exe (PID: 2304)
- chrome.exe (PID: 3124)
- WinRAR.exe (PID: 3668)
The process uses the downloaded file
- chrome.exe (PID: 3432)
- WinRAR.exe (PID: 2752)
- chrome.exe (PID: 2524)
- WinRAR.exe (PID: 3668)
- WinRAR.exe (PID: 2304)
Checks supported languages
- Prevalidador_Convenios_Cooperacion_AG2023_v1.6.0-24.exe (PID: 2480)
- is-VIIN5.tmp (PID: 2516)
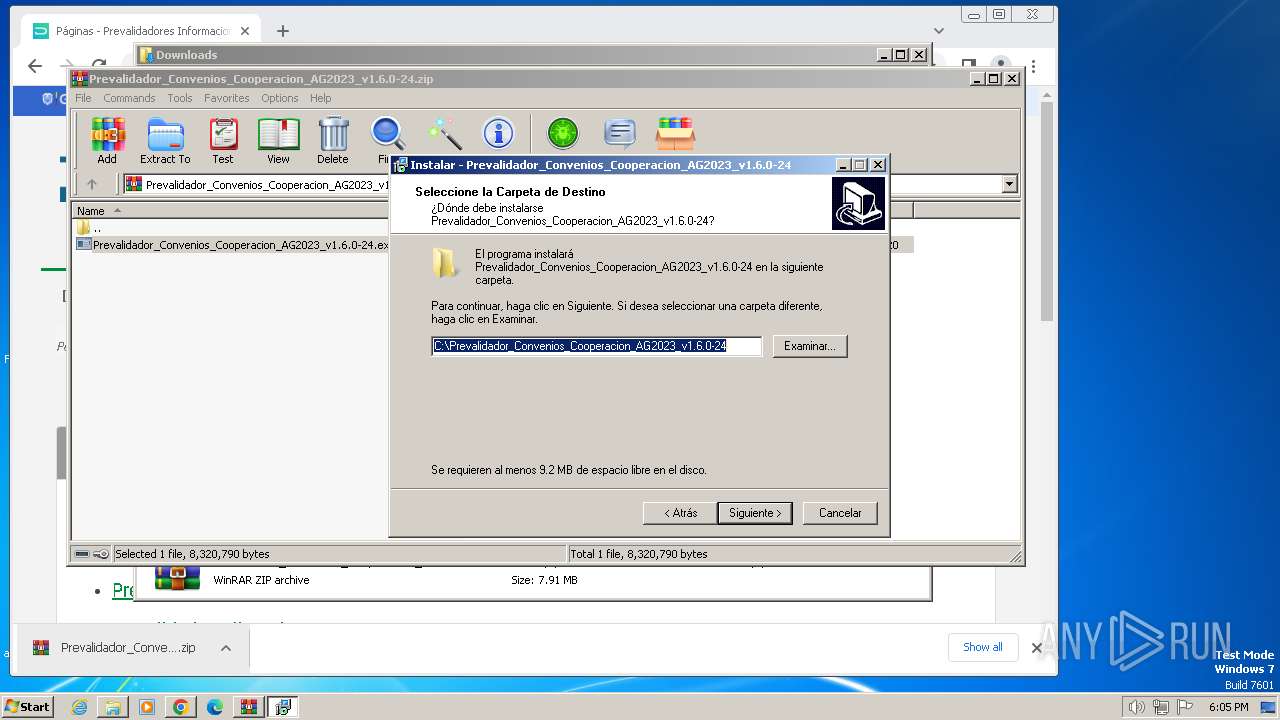
Create files in a temporary directory
- Prevalidador_Convenios_Cooperacion_AG2023_v1.6.0-24.exe (PID: 2480)
- is-VIIN5.tmp (PID: 2516)
Reads the computer name
- is-VIIN5.tmp (PID: 2516)
Creates files or folders in the user directory
- is-VIIN5.tmp (PID: 2516)
Creates a software uninstall entry
- is-VIIN5.tmp (PID: 2516)
Reads security settings of Internet Explorer
- msiexec.exe (PID: 3784)
Reads the software policy settings
- msiexec.exe (PID: 3784)
Reads Microsoft Office registry keys
- is-VIIN5.tmp (PID: 2516)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
87
Monitored processes
32
Malicious processes
4
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 128 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.UtilWin --lang=en-US --service-sandbox-type=none --disable-quic --mojo-platform-channel-handle=3756 --field-trial-handle=1180,i,763513514911130445,4315482816293312352,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 448 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --disable-quic --mojo-platform-channel-handle=3412 --field-trial-handle=1180,i,763513514911130445,4315482816293312352,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 664 | C:\Windows\system32\vssvc.exe | C:\Windows\System32\VSSVC.exe | — | services.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft® Volume Shadow Copy Service Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 844 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --disable-gpu-compositing --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=8 --mojo-platform-channel-handle=1324 --field-trial-handle=1180,i,763513514911130445,4315482816293312352,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 1028 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --disable-gpu-compositing --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=16 --mojo-platform-channel-handle=2024 --field-trial-handle=1180,i,763513514911130445,4315482816293312352,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 1264 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.UtilWin --lang=en-US --service-sandbox-type=none --disable-quic --mojo-platform-channel-handle=1860 --field-trial-handle=1180,i,763513514911130445,4315482816293312352,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 1352 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=5 --mojo-platform-channel-handle=2168 --field-trial-handle=1180,i,763513514911130445,4315482816293312352,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 1840 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --disable-gpu-compositing --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=11 --mojo-platform-channel-handle=3828 --field-trial-handle=1180,i,763513514911130445,4315482816293312352,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 2120 | "C:\Users\admin\AppData\Local\Temp\Rar$EXa2752.20336\Prevalidador_Convenios_Cooperacion_AG2023_v1.6.0-24.exe" | C:\Users\admin\AppData\Local\Temp\Rar$EXa2752.20336\Prevalidador_Convenios_Cooperacion_AG2023_v1.6.0-24.exe | — | WinRAR.exe | |||||||||||
User: admin Company: Dirección de Impuestos y Aduanas Nacionales - DIAN Integrity Level: MEDIUM Description: Prevalidador_Convenios_Cooperacion_AG2023_v1.6.0-24 Exit code: 3221226540 Version: 2.1 Modules
| |||||||||||||||
| 2152 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=storage.mojom.StorageService --lang=en-US --service-sandbox-type=service --disable-quic --mojo-platform-channel-handle=1620 --field-trial-handle=1180,i,763513514911130445,4315482816293312352,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
Total events
42 152
Read events
40 812
Write events
952
Delete events
388
Modification events
| (PID) Process: | (3672) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPDaysSinceLastAutoMigration |
Value: 1 | |||
| (PID) Process: | (3672) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchLowDateTime |
Value: | |||
| (PID) Process: | (3672) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchHighDateTime |
Value: 31092921 | |||
| (PID) Process: | (3672) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateLowDateTime |
Value: | |||
| (PID) Process: | (3672) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateHighDateTime |
Value: 31092921 | |||
| (PID) Process: | (3672) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (3672) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (3672) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (3672) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (3672) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
Executable files
12
Suspicious files
76
Text files
58
Unknown types
76
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3964 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\commerce_subscription_db\LOG.old~RF184a23.TMP | — | |
MD5:— | SHA256:— | |||
| 3964 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3672 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\Internet Explorer\Services\search_{0633EE93-D776-472f-A0FF-E1416B8B2E3A}.ico | image | |
MD5:DA597791BE3B6E732F0BC8B20E38EE62 | SHA256:5B2C34B3C4E8DD898B664DBA6C3786E2FF9869EFF55D673AA48361F11325ED07 | |||
| 3672 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\EAF8AA29A62AB29E614331747385D816_F9E4DC0B9D5C777357D7DB8DEF51118A | binary | |
MD5:F099AC53515B3B777A6BAE1BDC59EEDF | SHA256:87417AB87801049749BBF972E33D90DFB750344EBF1F72AB91B079B94B5F5435 | |||
| 3672 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\6Z2BCOUL\favicon[1].ico | image | |
MD5:DA597791BE3B6E732F0BC8B20E38EE62 | SHA256:5B2C34B3C4E8DD898B664DBA6C3786E2FF9869EFF55D673AA48361F11325ED07 | |||
| 3672 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\57C8EDB95DF3F0AD4EE2DC2B8CFD4157 | binary | |
MD5:14889C123D2120C869263BDEA58A5B3F | SHA256:AEA13F7133D5C4E145FE810CF0977519F32248D357E4971E28E3DB3944E26D31 | |||
| 3964 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old~RF184a23.TMP | text | |
MD5:05CF4C3C5148DA6355D3561A9EAA5E8A | SHA256:8D720243F6876898E4F197C8867C4CEE69F1C7335C55B8A29C120B1028D93E41 | |||
| 3964 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad\settings.dat | binary | |
MD5:9C016064A1F864C8140915D77CF3389A | SHA256:0E7265D4A8C16223538EDD8CD620B8820611C74538E420A88E333BE7F62AC787 | |||
| 3964 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Local Storage\leveldb\LOG.old~RF184adf.TMP | text | |
MD5:C383FD120B14BB0E98E99C1BCC9B43F6 | SHA256:56A3A5EACBD28BEE1CF8C1D0052321A5C27EE858BEF7B2FA1DE20806A0823CC1 | |||
| 3964 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\coupon_db\LOG.old~RF184c08.TMP | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
48
TCP/UDP connections
49
DNS requests
60
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3672 | iexplore.exe | GET | 304 | 2.22.28.151:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?b23edf5cfbe16fd7 | unknown | — | — | unknown |
3672 | iexplore.exe | GET | 304 | 2.22.28.177:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?76ad697231f9b13b | unknown | — | — | unknown |
3952 | iexplore.exe | GET | 200 | 104.18.21.226:80 | http://ocsp2.globalsign.com/rootr3/ME8wTTBLMEkwRzAJBgUrDgMCGgUABBT1nGh%2FJBjWKnkPdZIzB1bqhelHBwQUj%2FBLf6guRSSuTVD6Y5qL3uLdG7wCDkikAt0nkg2iCDSd0Zl7 | unknown | binary | 1.40 Kb | unknown |
3952 | iexplore.exe | GET | 200 | 104.18.21.226:80 | http://ocsp2.globalsign.com/gsextendvalsha2g3r3/ME0wSzBJMEcwRTAJBgUrDgMCGgUABBScTHEVwwIZyjbcuYshMwBMpKeO0wQU3bPnbagu6MVObs905nU8lBXO6B0CDAZixGRtE6LiVLLe1Q%3D%3D | unknown | binary | 1.41 Kb | unknown |
3672 | iexplore.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAzlnDD9eoNTLi0BRrMy%2BWU%3D | unknown | binary | 313 b | unknown |
1080 | svchost.exe | GET | 304 | 2.22.28.151:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?ae332821cb231d51 | unknown | compressed | 67.5 Kb | unknown |
1080 | svchost.exe | GET | 200 | 2.22.28.151:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab?aa4b77dd5ef709e5 | unknown | compressed | 67.5 Kb | unknown |
3672 | iexplore.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | binary | 471 b | unknown |
856 | svchost.exe | HEAD | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/k4ldha5kevpu7qn7k4s3mznvgu_4.10.2710.0/oimompecagnajdejgnnjijobebaeigek_4.10.2710.0_win32_ad2kbvs6jks3au5dsxn7cqflsiiq.crx3 | unknown | — | — | unknown |
856 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/k4ldha5kevpu7qn7k4s3mznvgu_4.10.2710.0/oimompecagnajdejgnnjijobebaeigek_4.10.2710.0_win32_ad2kbvs6jks3au5dsxn7cqflsiiq.crx3 | unknown | binary | 9.98 Kb | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
1080 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |
3952 | iexplore.exe | 190.83.78.1:443 | www.dian.gov.co | Telmex Colombia S.A. | CO | unknown |
3672 | iexplore.exe | 2.22.225.163:443 | www.bing.com | Akamai International B.V. | GB | unknown |
3672 | iexplore.exe | 2.22.28.151:80 | ctldl.windowsupdate.com | Administracion Nacional de Telecomunicaciones | UY | unknown |
3672 | iexplore.exe | 2.22.28.177:80 | ctldl.windowsupdate.com | Administracion Nacional de Telecomunicaciones | UY | unknown |
3672 | iexplore.exe | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
3964 | chrome.exe | 239.255.255.250:1900 | — | — | — | unknown |
2168 | chrome.exe | 142.250.185.227:443 | clientservices.googleapis.com | GOOGLE | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.dian.gov.co |
| unknown |
api.bing.com |
| whitelisted |
www.bing.com |
| whitelisted |
ctldl.windowsupdate.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
clientservices.googleapis.com |
| whitelisted |
accounts.google.com |
| shared |
www.google.com |
| whitelisted |
update.googleapis.com |
| whitelisted |
ocsp2.globalsign.com |
| whitelisted |