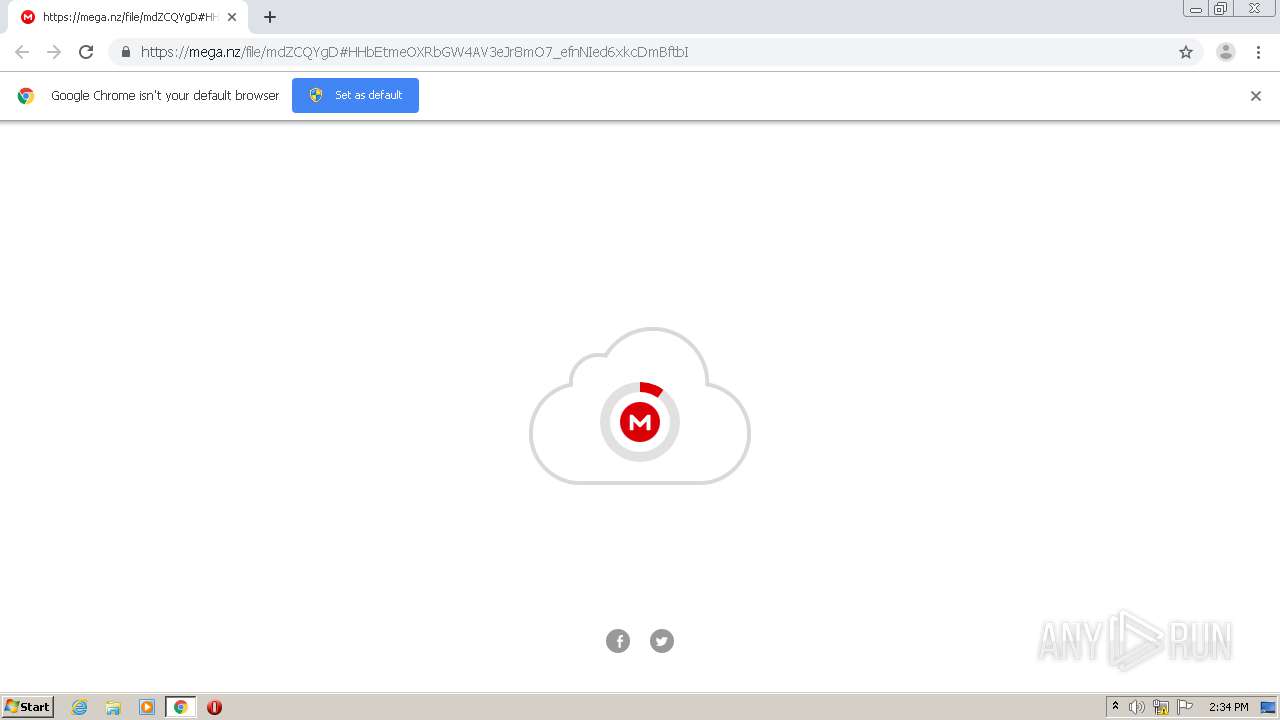
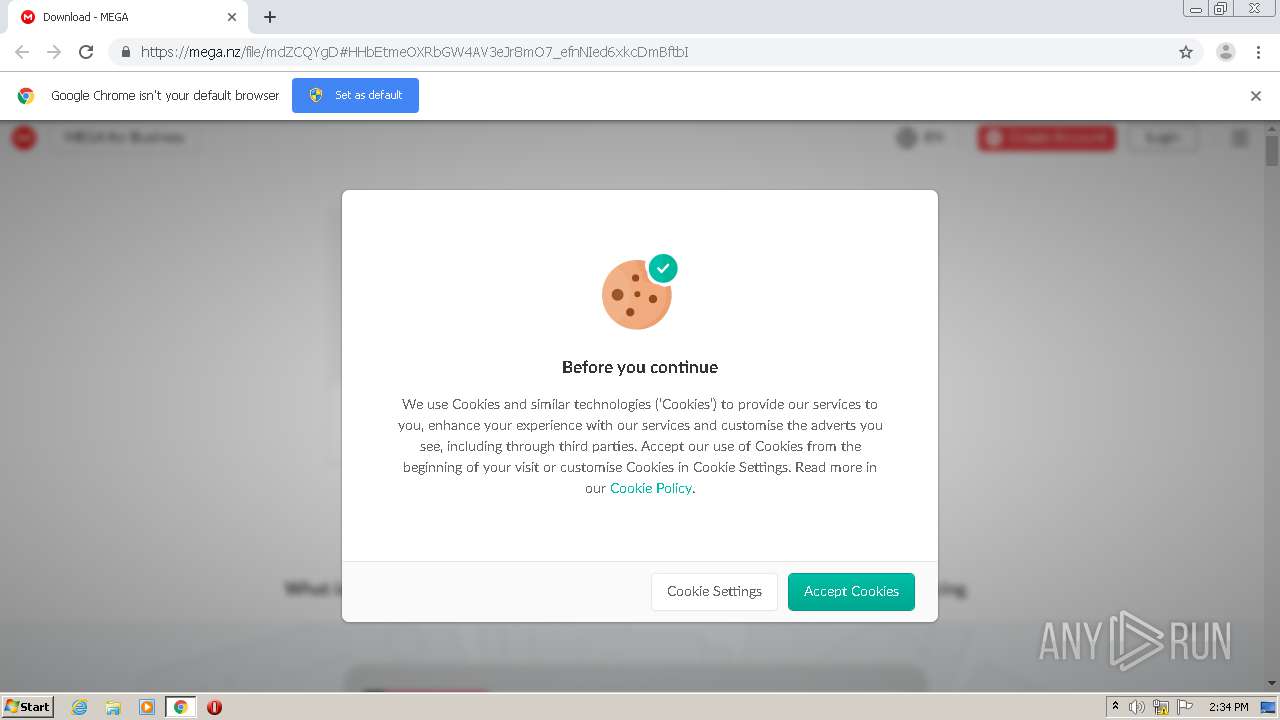
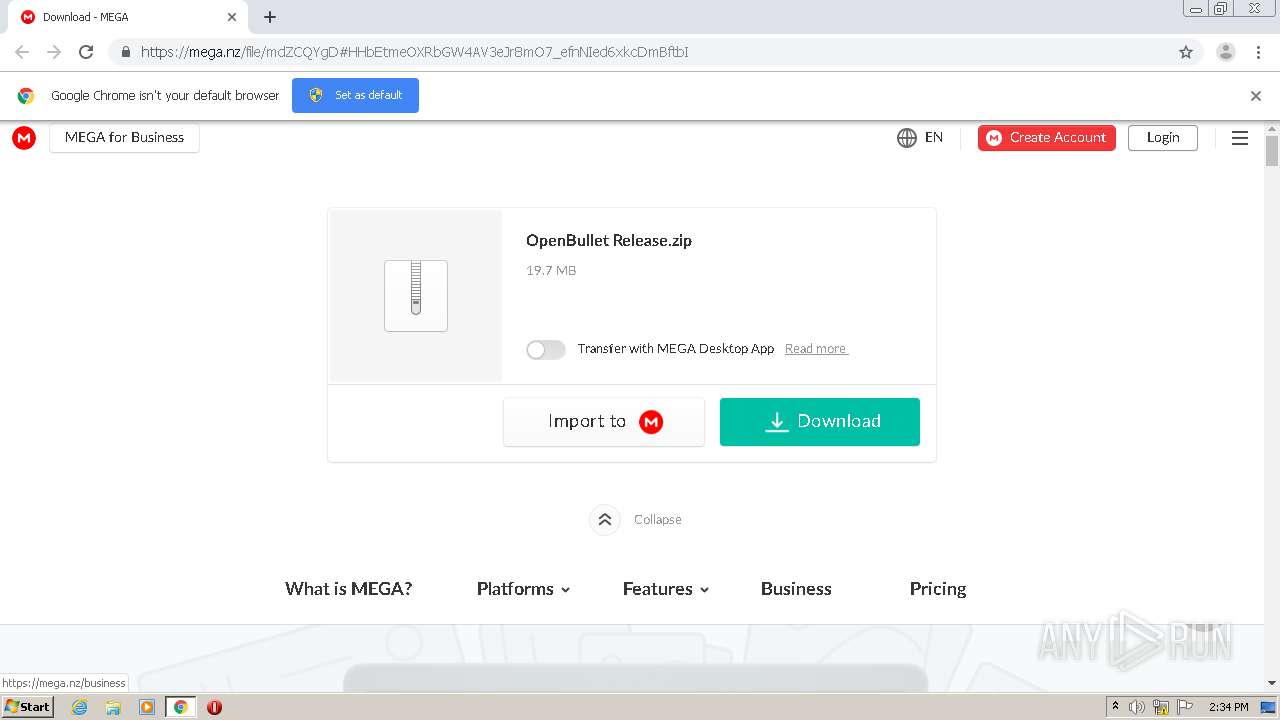
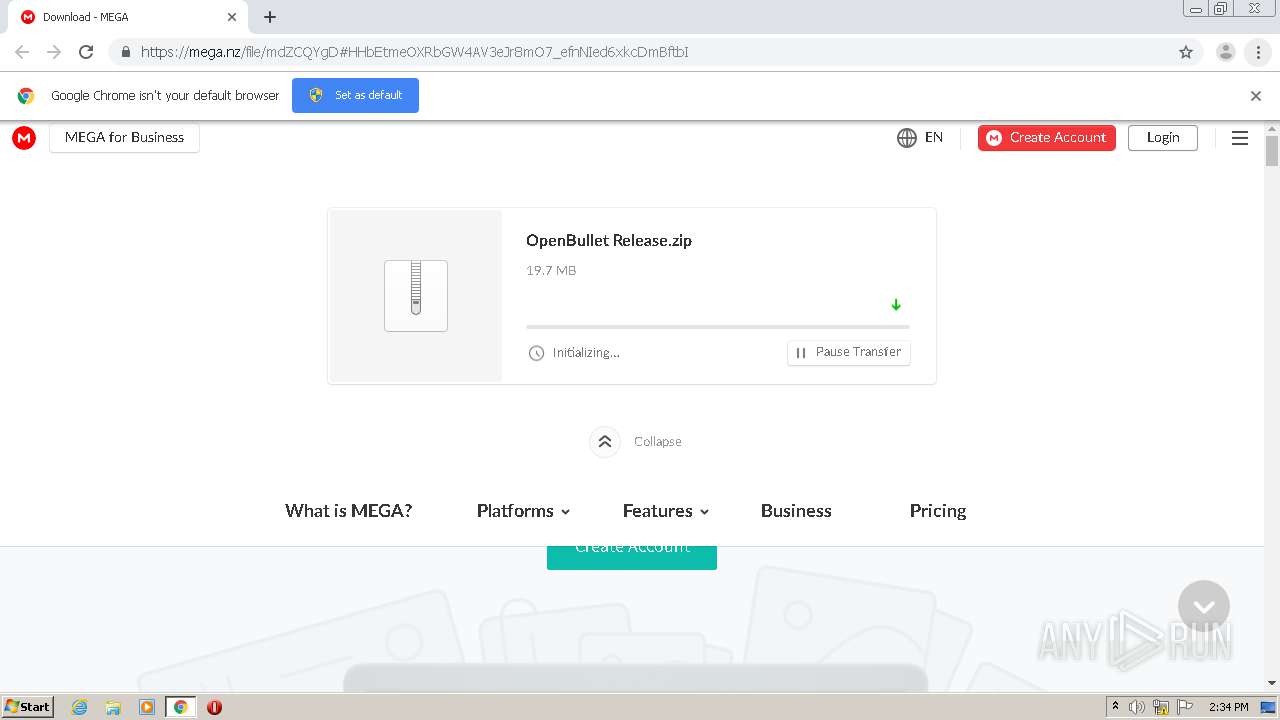
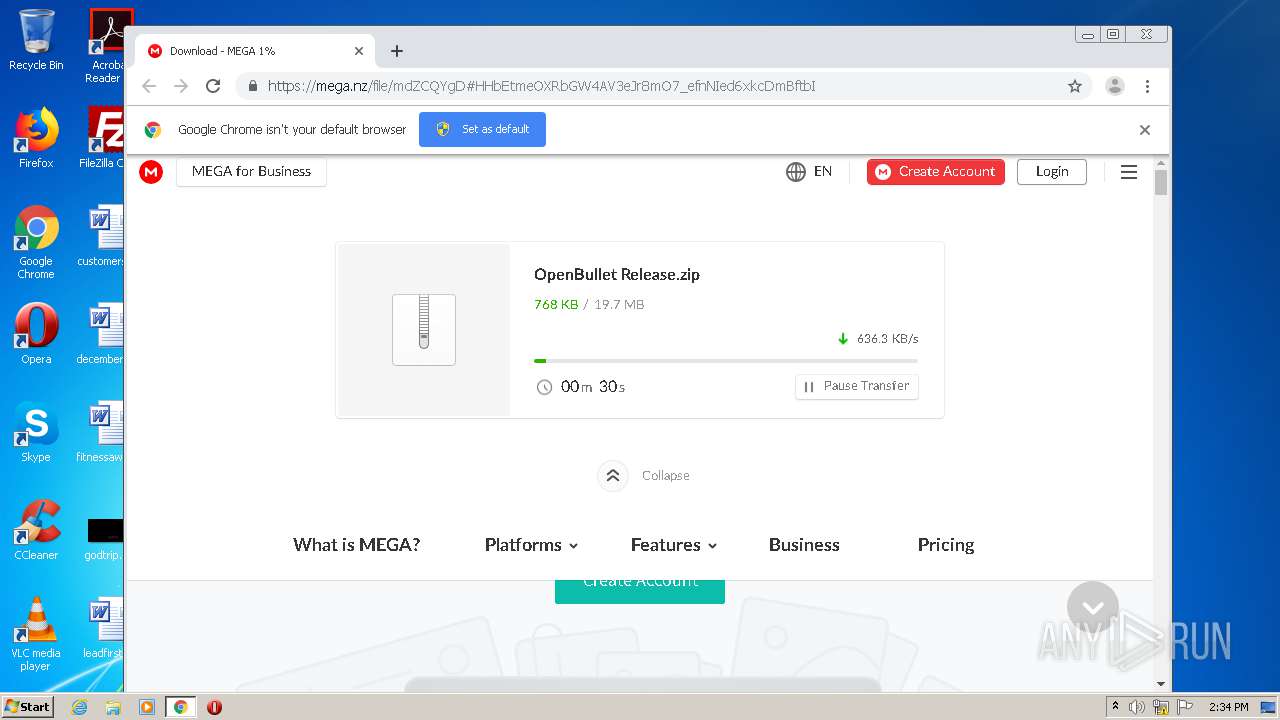
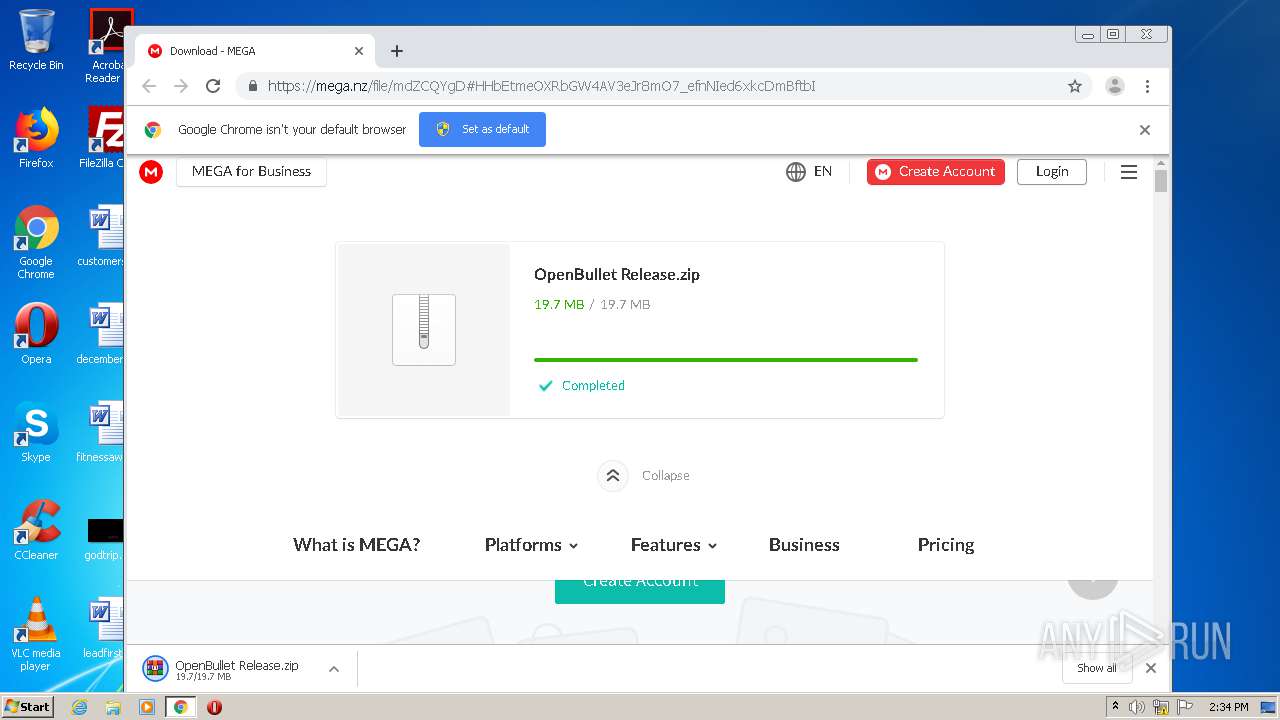
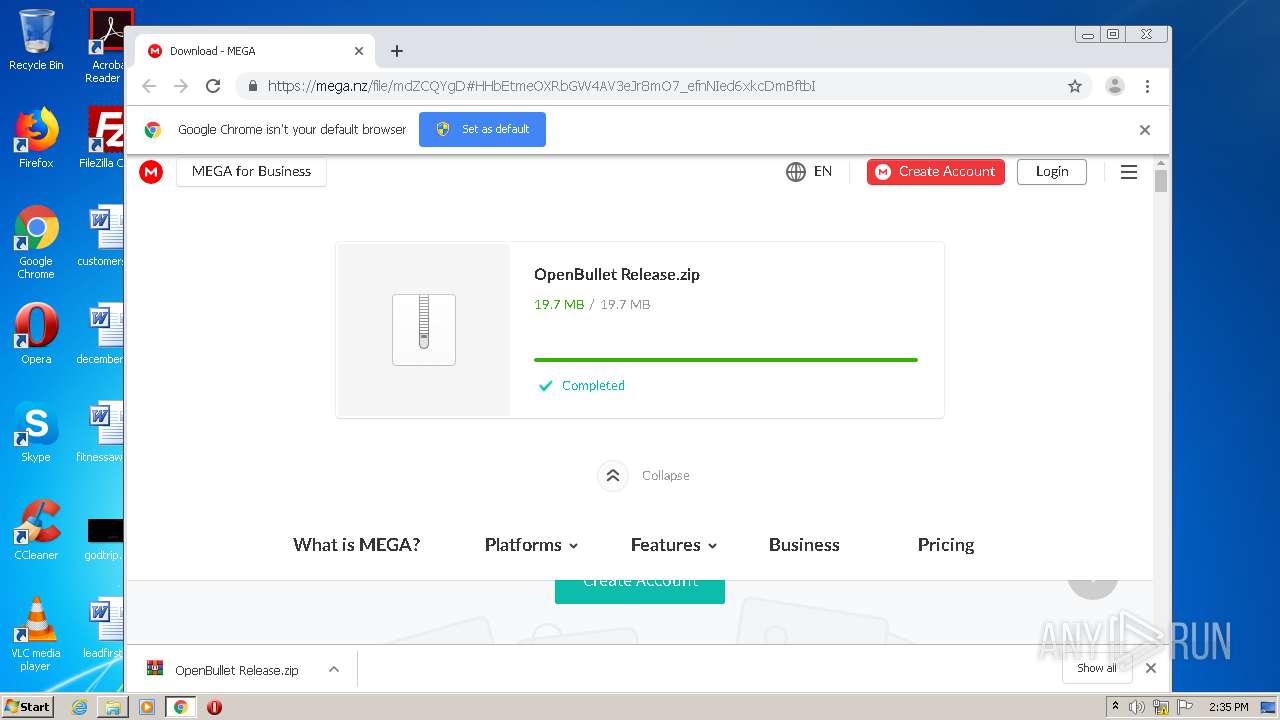
| URL: | https://mega.nz/file/mdZCQYgD#HHbEtmeOXRbGW4AV3eJr8mO7_efnNIed6xkcDmBftbI |
| Full analysis: | https://app.any.run/tasks/c8d18878-56c2-49dd-a507-27ba4b99db89 |
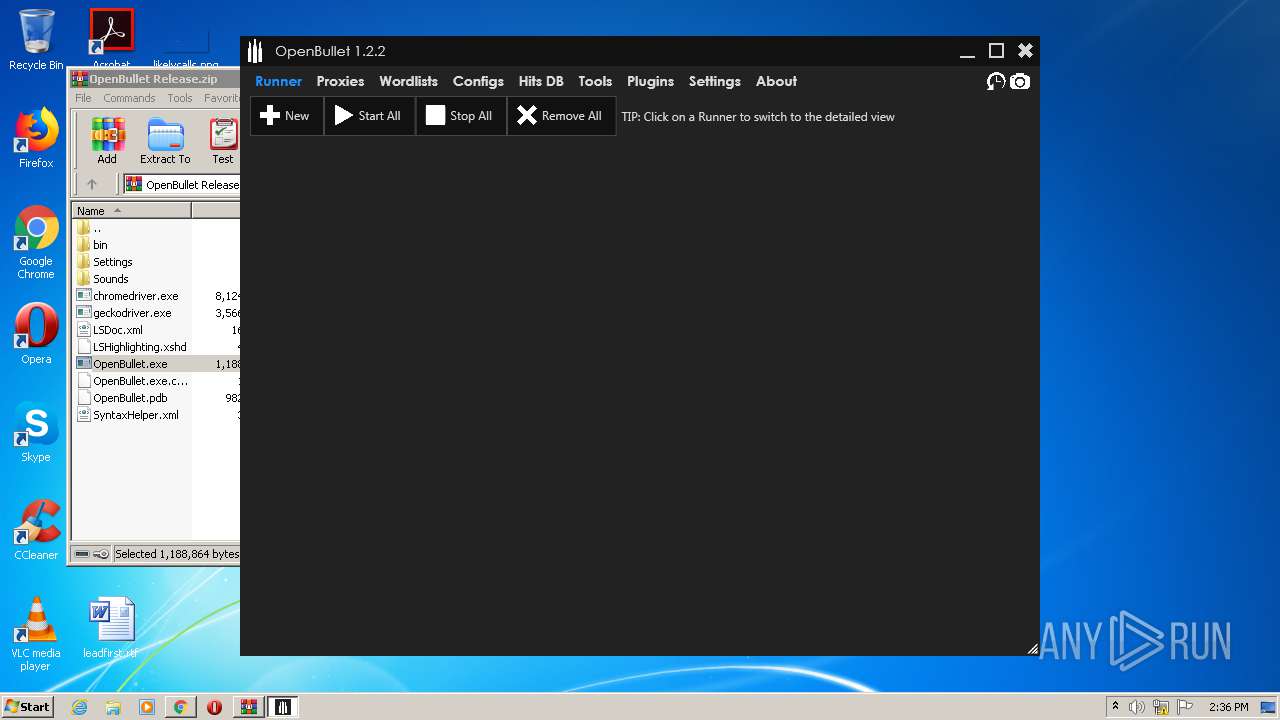
| Verdict: | Malicious activity |
| Analysis date: | January 29, 2021, 14:34:07 |
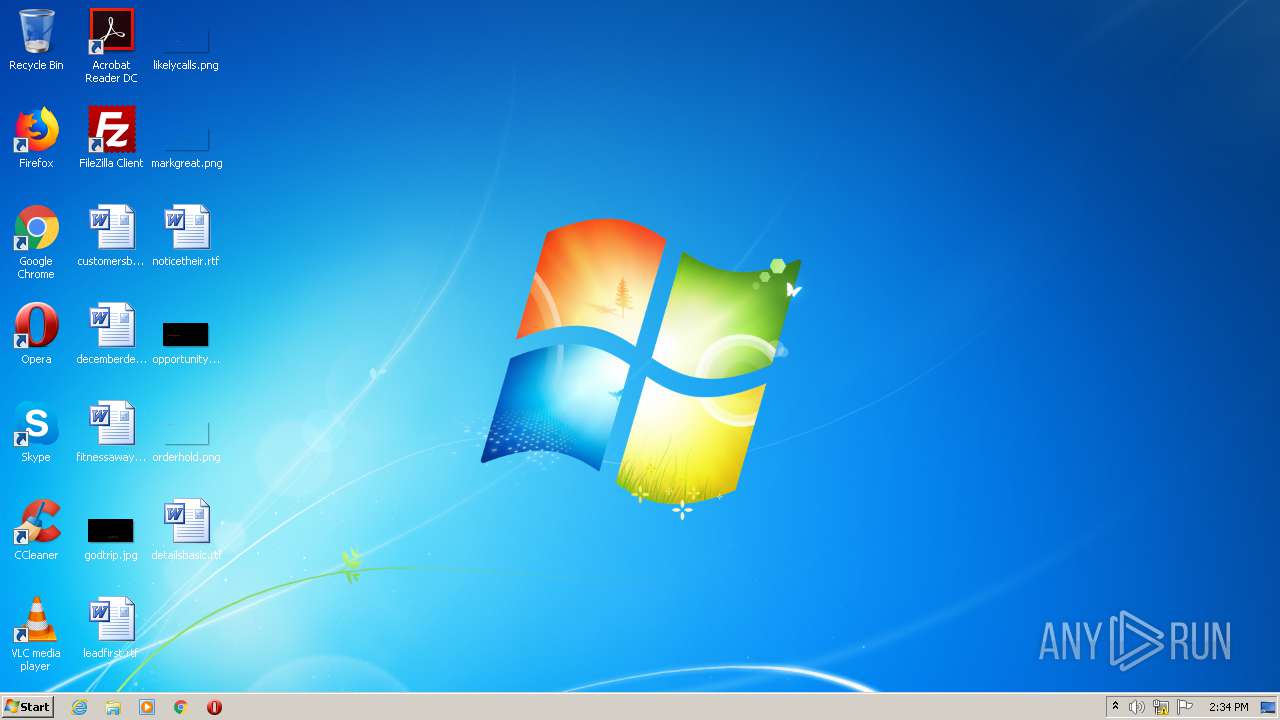
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 7531FA698F5A2BF7CDB3100BBFD87D9C |
| SHA1: | 0F9D94F6145DDCF3B60FB0B66181337A9B5345AC |
| SHA256: | 7D9C9781F2A9D4E20DE53AE51804112CF7DF4EB7489D56904BBAFAB79E6B89C8 |
| SSDEEP: | 3:N8X/iP/D8iGttf3CywWAkXrDYVs:2M/D8lttf3xTPB |
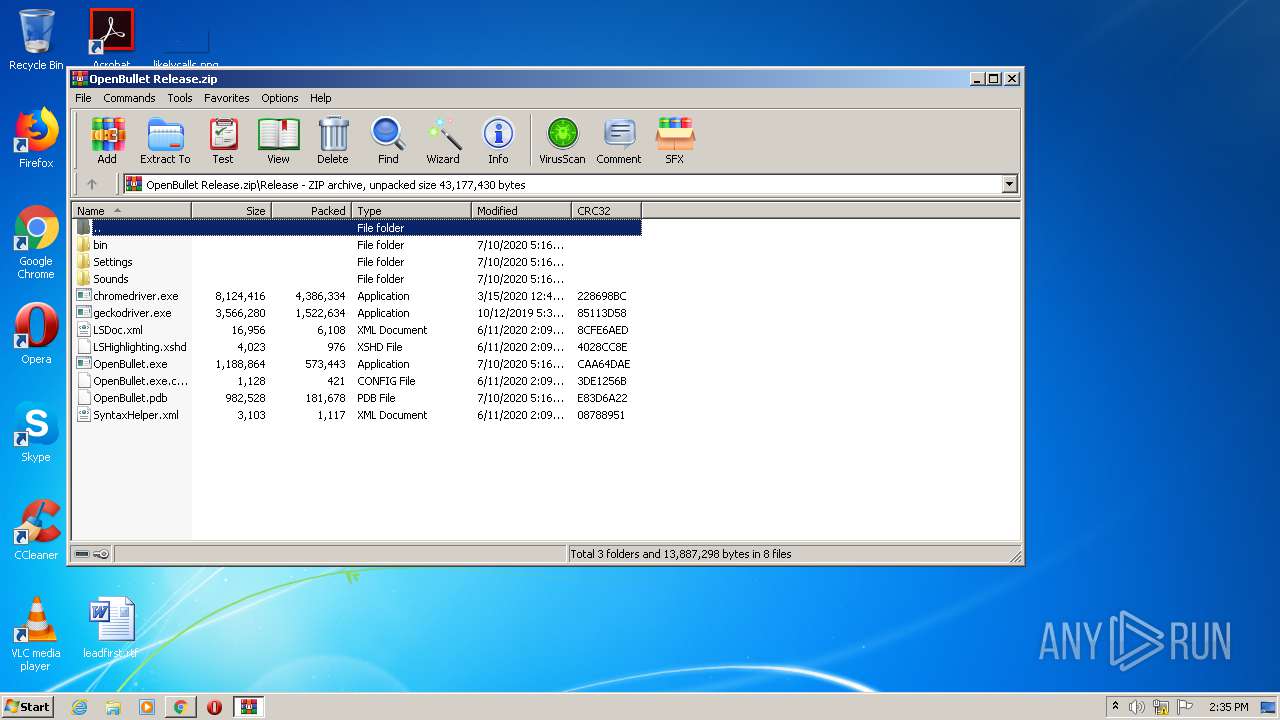
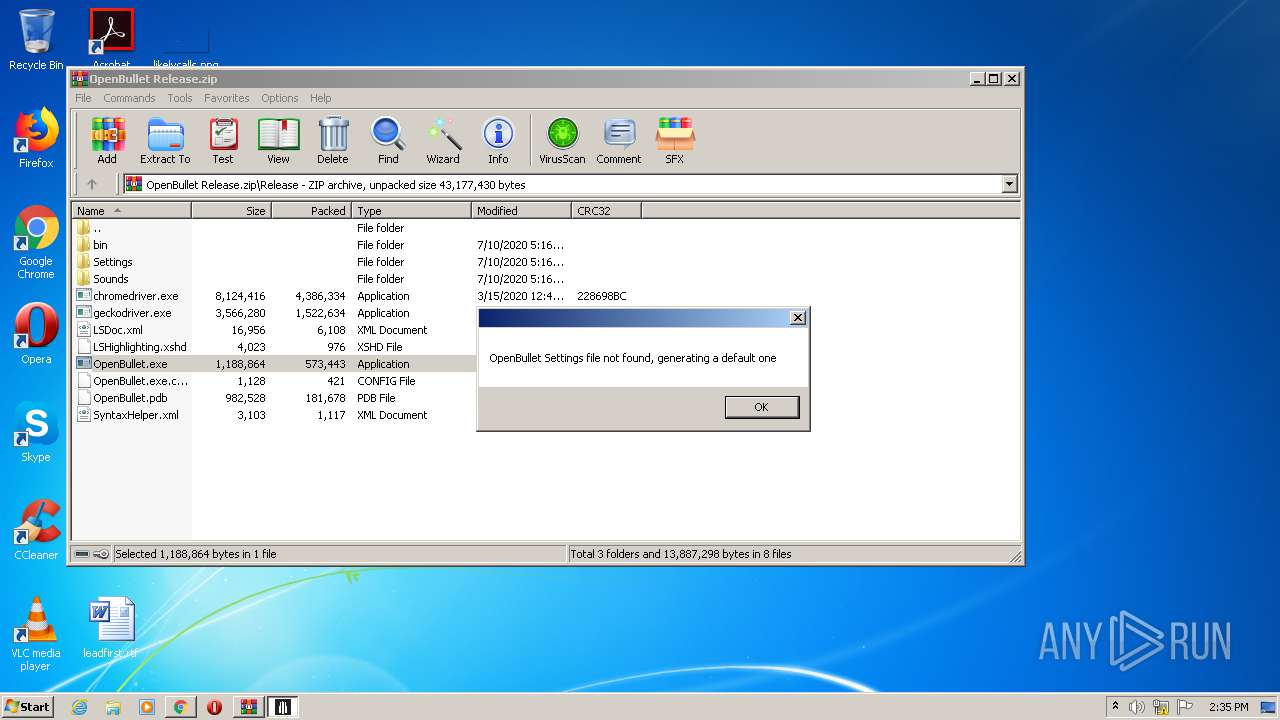
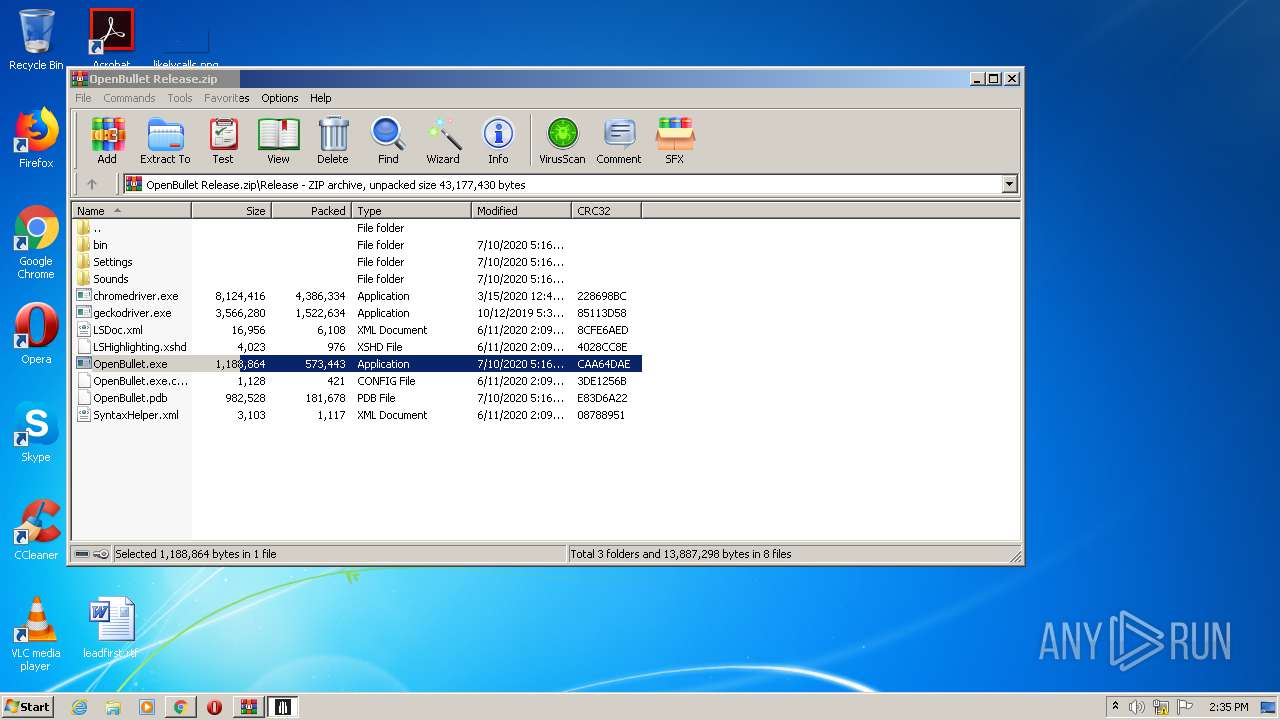
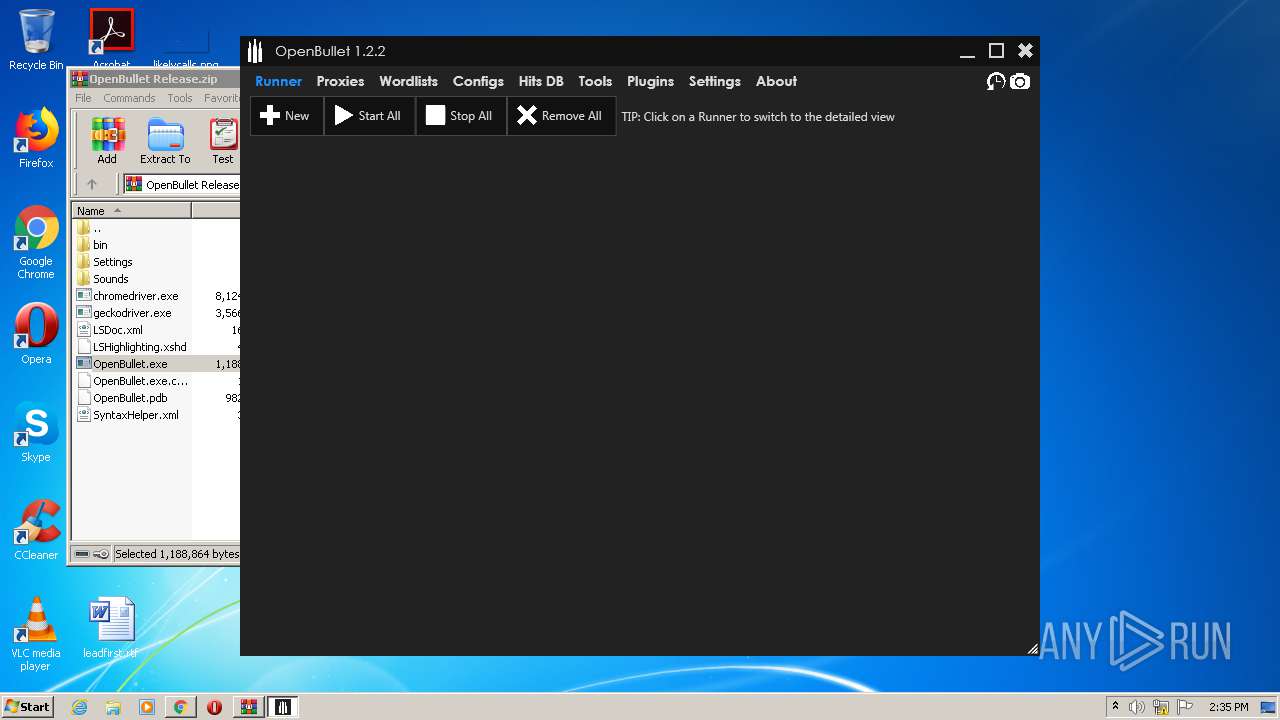
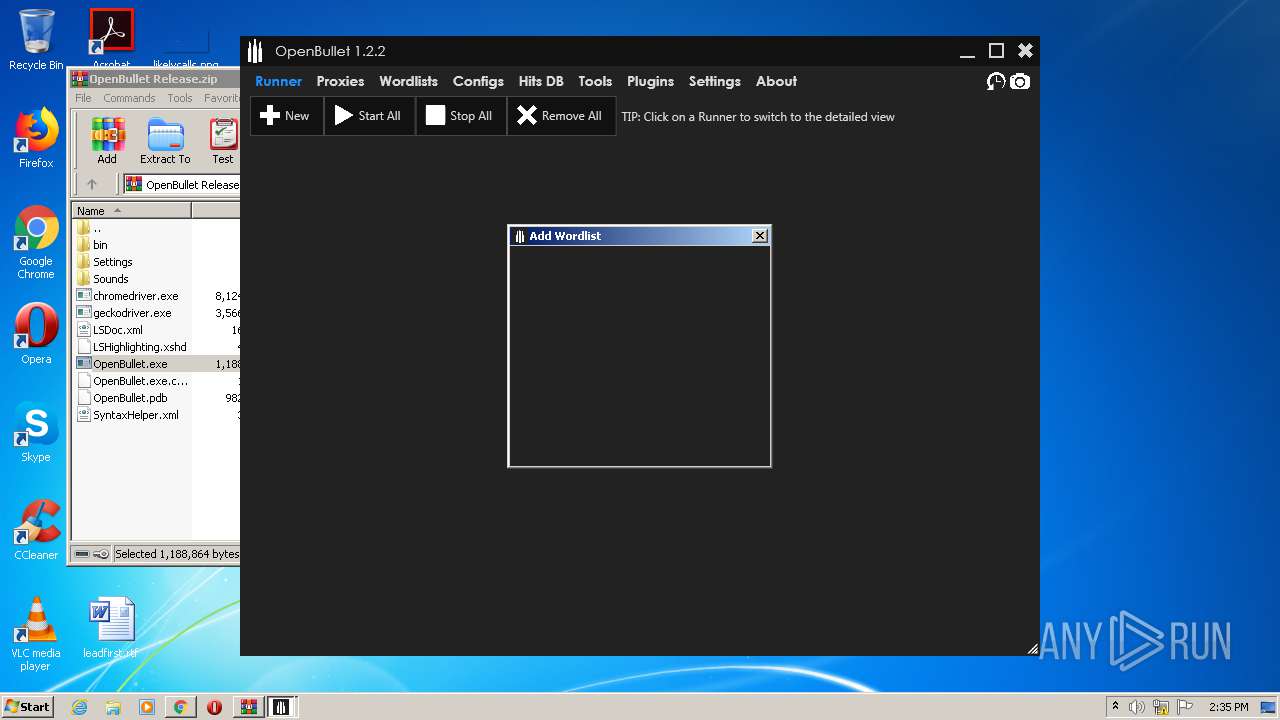
MALICIOUS
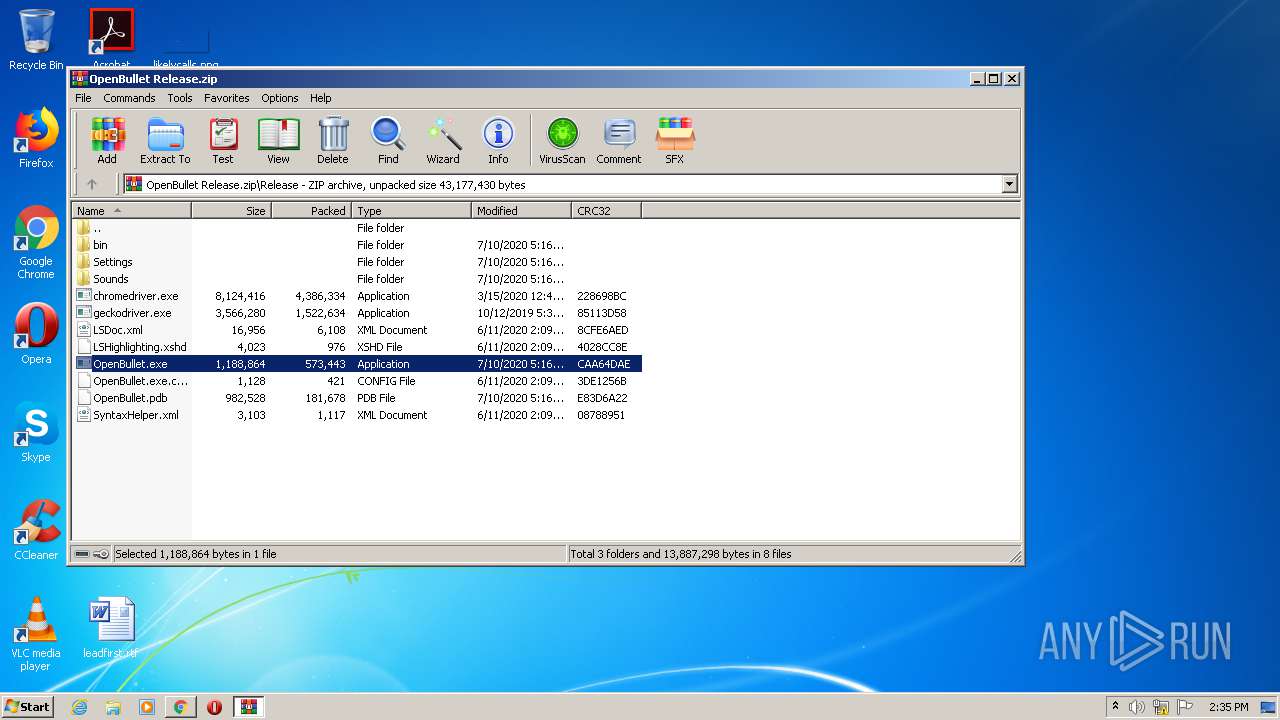
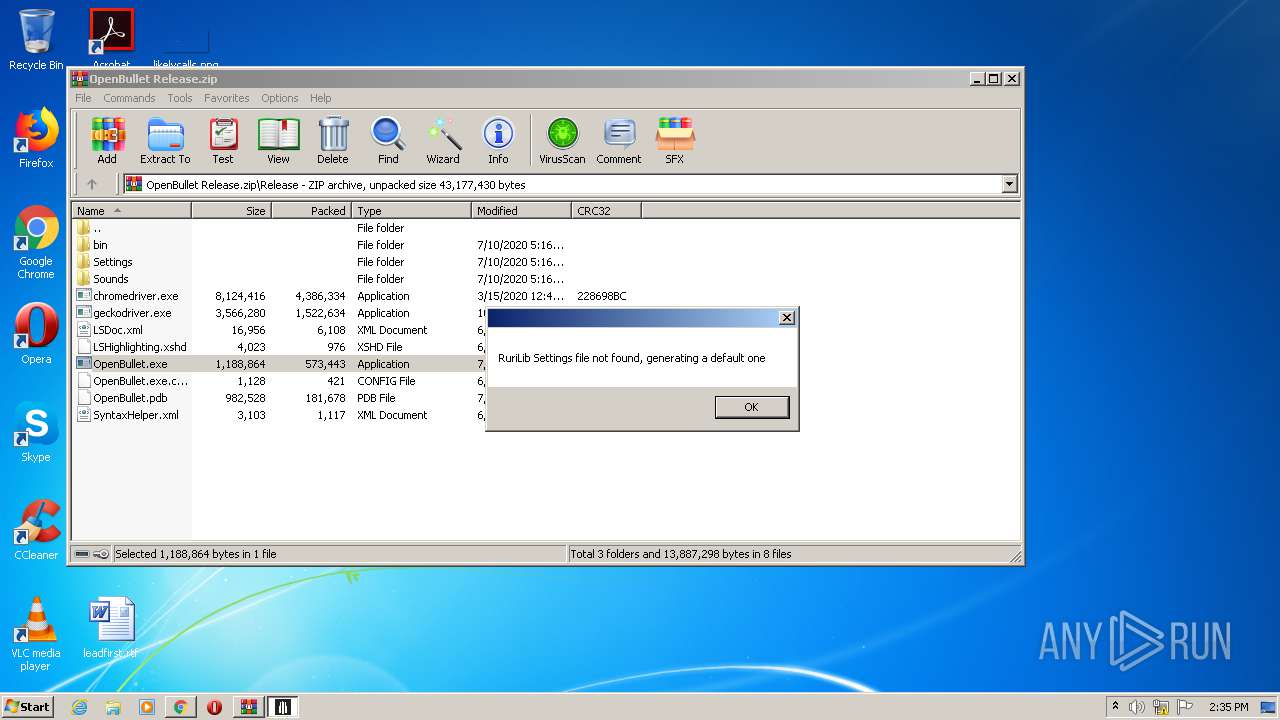
Application was dropped or rewritten from another process
- OpenBullet.exe (PID: 2808)
Loads dropped or rewritten executable
- OpenBullet.exe (PID: 2808)
SUSPICIOUS
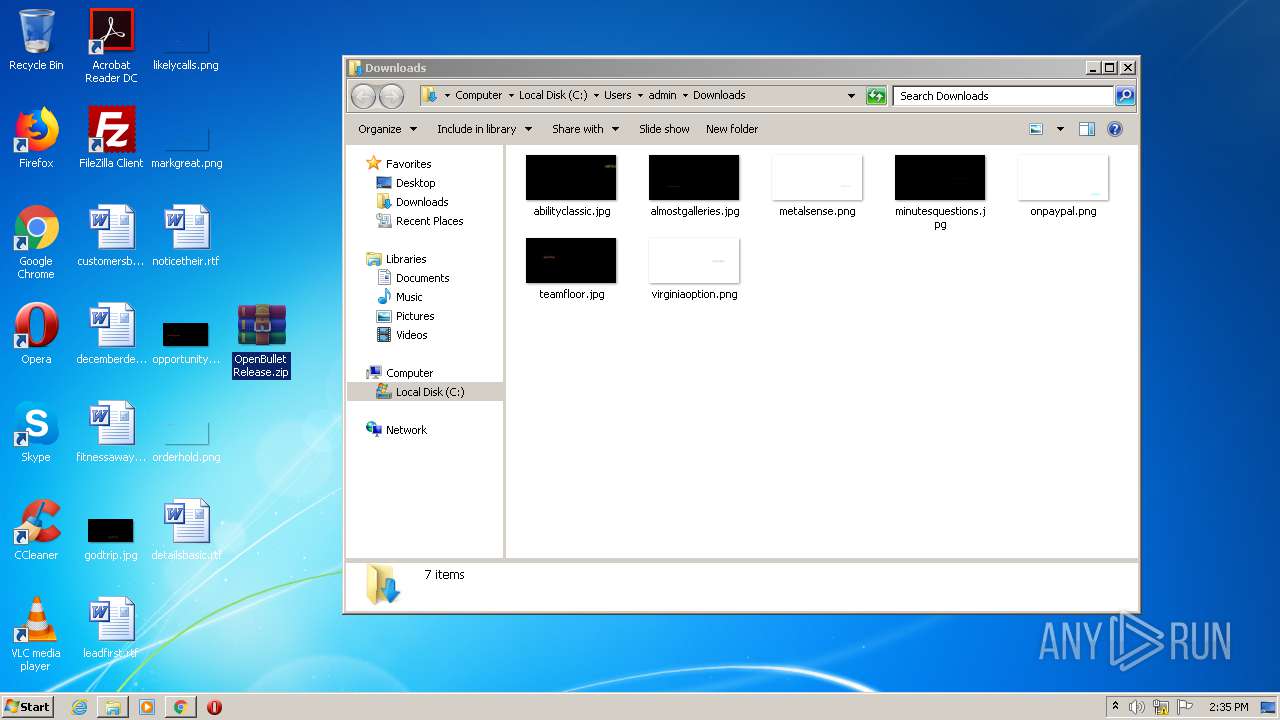
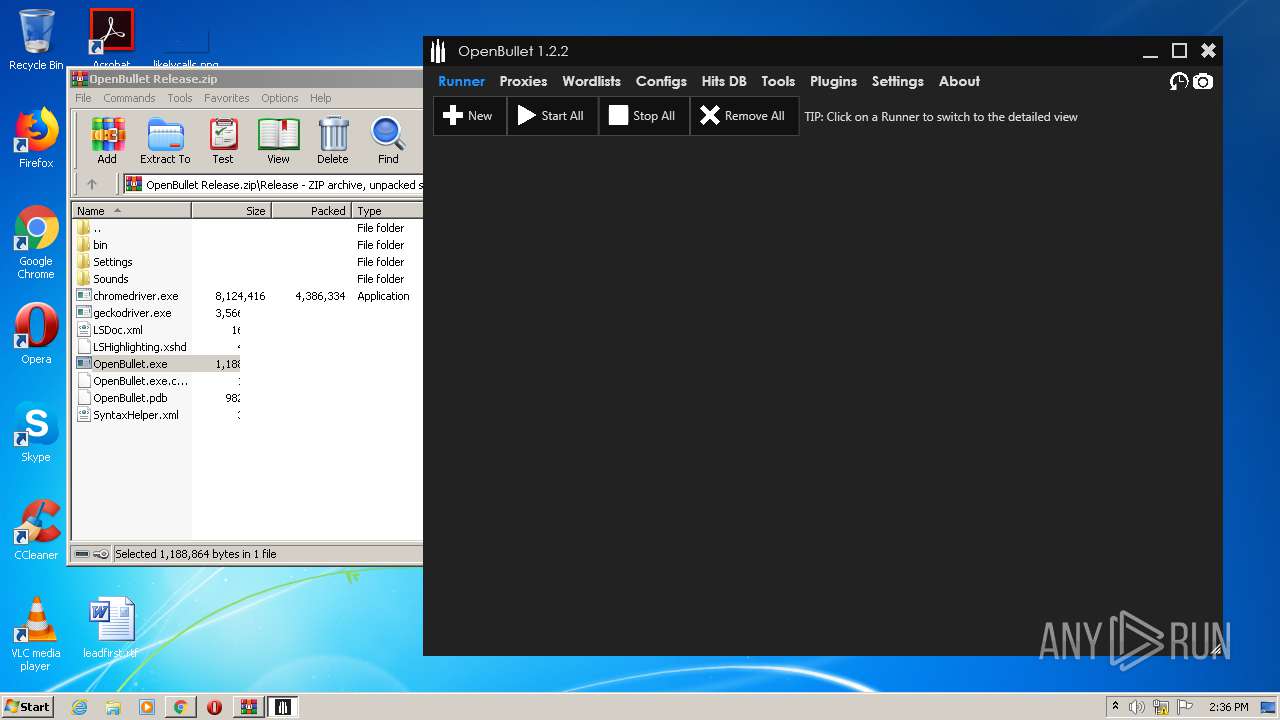
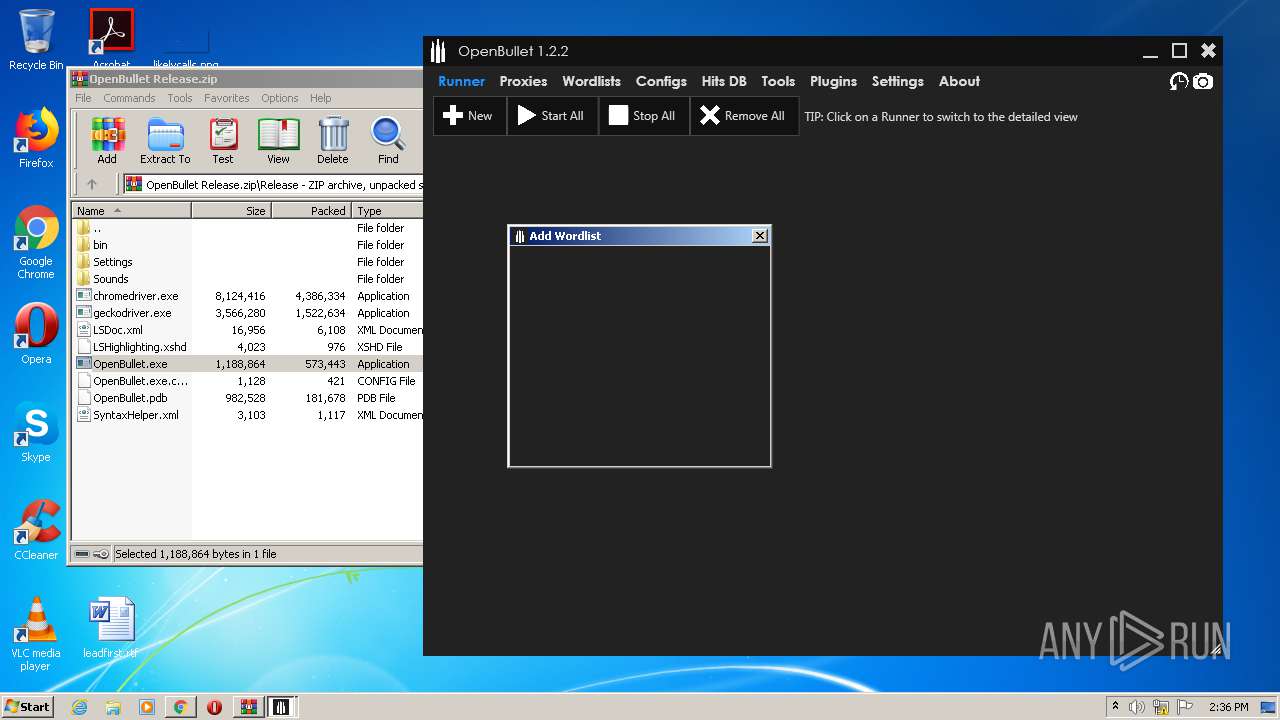
Executable content was dropped or overwritten
- WinRAR.exe (PID: 2580)
Drops a file with too old compile date
- WinRAR.exe (PID: 2580)
Drops a file that was compiled in debug mode
- WinRAR.exe (PID: 2580)
INFO
Reads the hosts file
- chrome.exe (PID: 1548)
- chrome.exe (PID: 2540)
Application launched itself
- chrome.exe (PID: 2540)
Reads settings of System Certificates
- chrome.exe (PID: 1548)
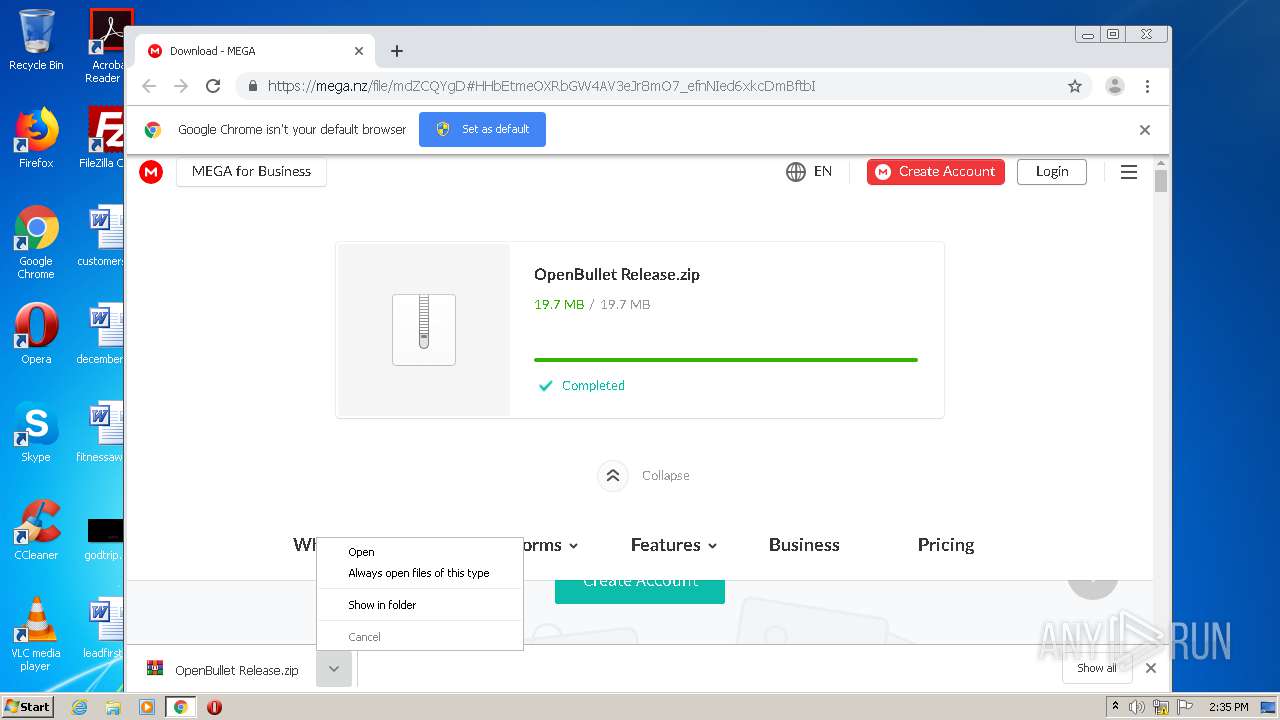
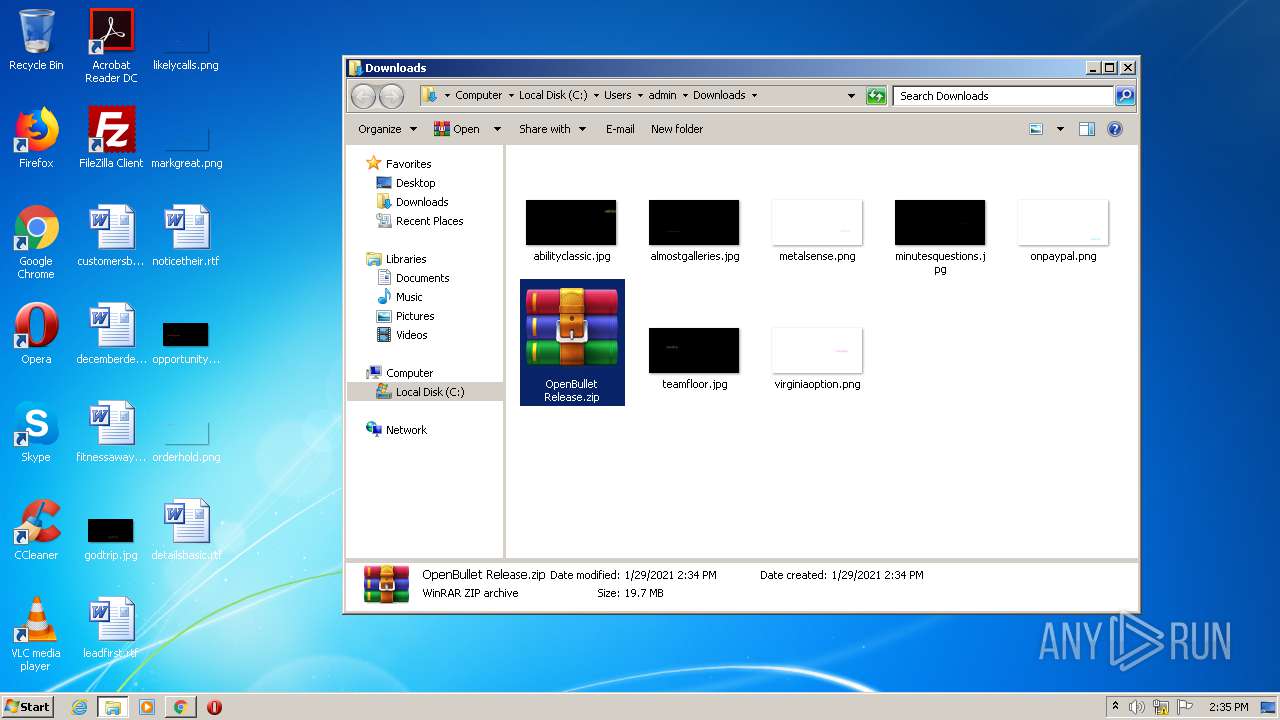
Manual execution by user
- WinRAR.exe (PID: 2580)
Dropped object may contain Bitcoin addresses
- WinRAR.exe (PID: 2580)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
50
Monitored processes
13
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1528 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1032,16710984831838150874,8504211905127791359,131072 --enable-features=PasswordImport --lang=en-US --extension-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=4578716805457760104 --renderer-client-id=4 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2436 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1532 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1032,16710984831838150874,8504211905127791359,131072 --enable-features=PasswordImport --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=1539029693661447647 --renderer-client-id=6 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2164 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1548 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1032,16710984831838150874,8504211905127791359,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=network --service-request-channel-token=5147911927359537869 --mojo-platform-channel-handle=1460 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | chrome.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1812 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=1032,16710984831838150874,8504211905127791359,131072 --enable-features=PasswordImport --gpu-preferences=KAAAAAAAAADgACAgAQAAAAAAAAAAAGAAAAAAAAAAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --service-request-channel-token=234328573984376539 --mojo-platform-channel-handle=1040 --ignored=" --type=renderer " /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2176 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=watcher --main-thread-id=2792 --on-initialized-event-handle=316 --parent-handle=320 /prefetch:6 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2400 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1032,16710984831838150874,8504211905127791359,131072 --enable-features=PasswordImport --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=4456709646107344894 --renderer-client-id=5 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2180 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2540 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --disk-cache-dir=null --disk-cache-size=1 --media-cache-size=1 --disable-gpu-shader-disk-cache --disable-background-networking "https://mega.nz/file/mdZCQYgD#HHbEtmeOXRbGW4AV3eJr8mO7_efnNIed6xkcDmBftbI" | C:\Program Files\Google\Chrome\Application\chrome.exe | explorer.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
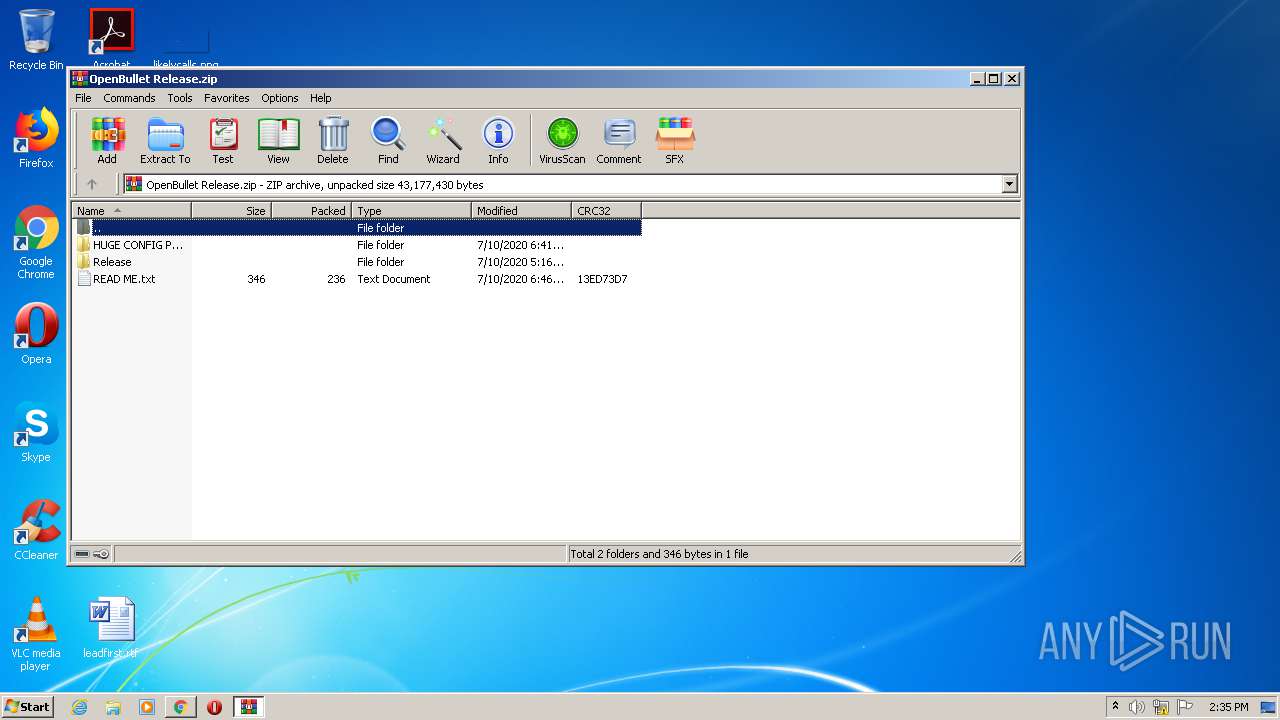
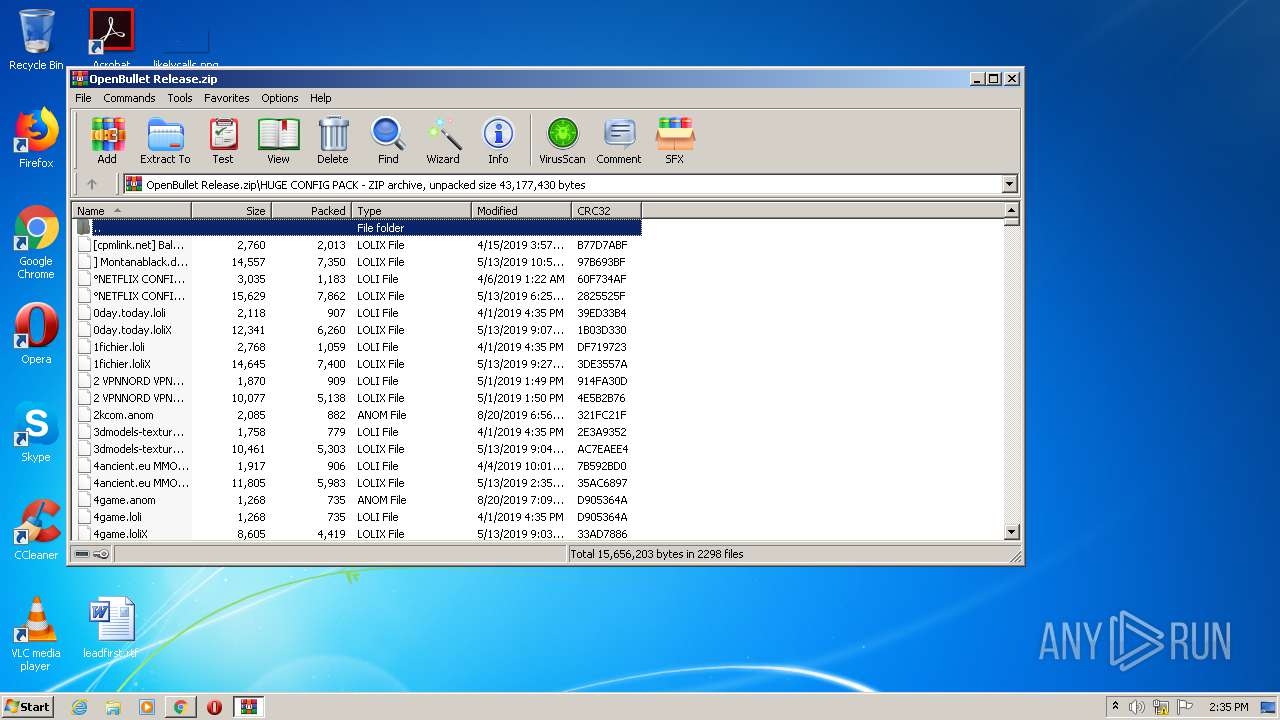
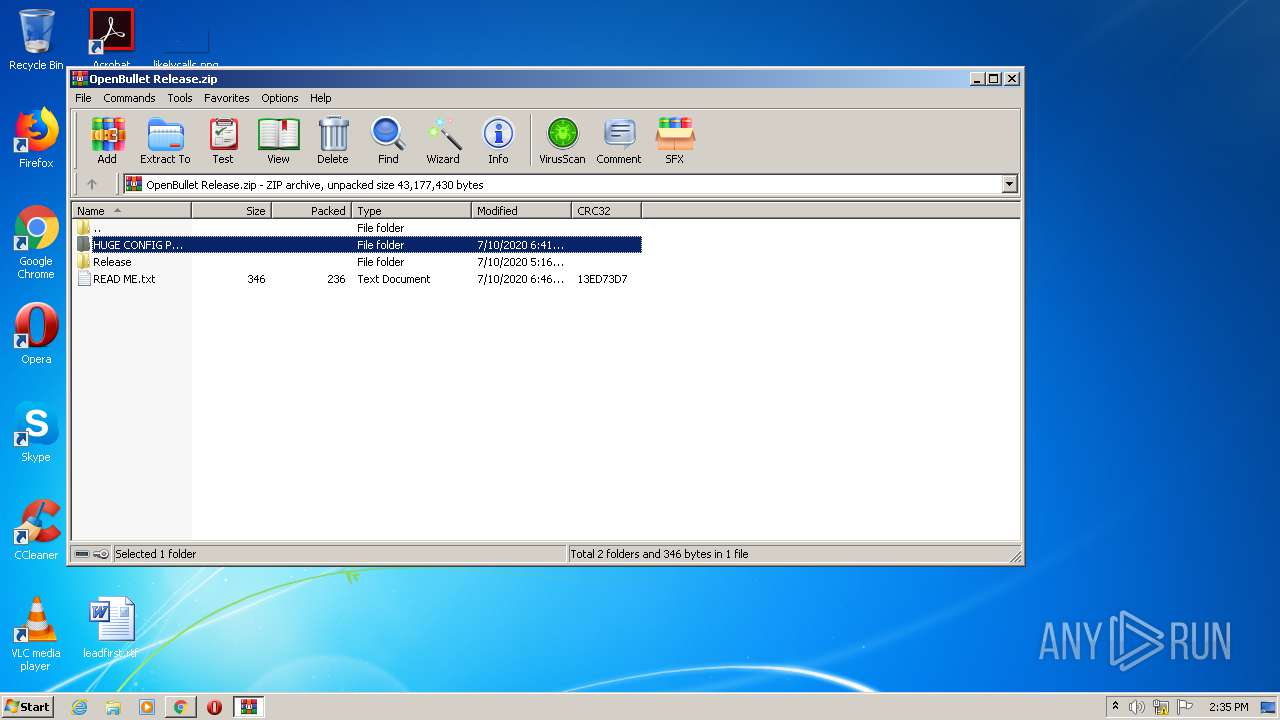
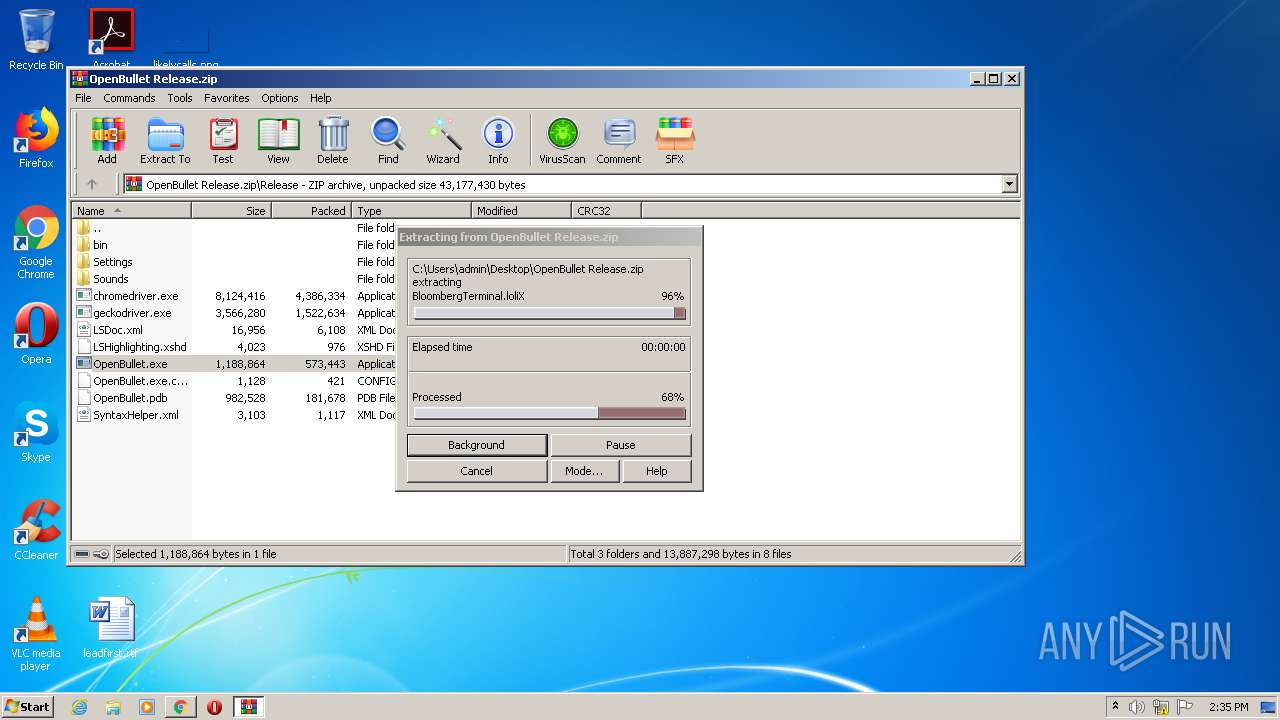
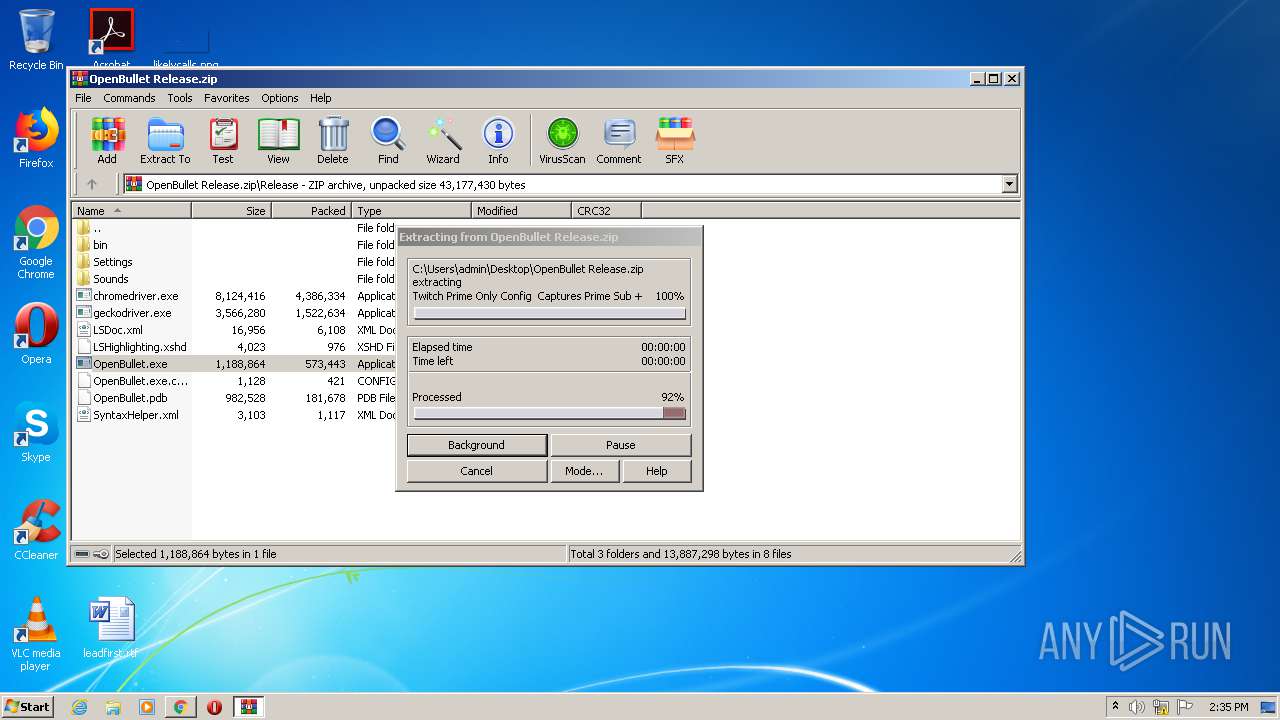
| 2580 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\Desktop\OpenBullet Release.zip" | C:\Program Files\WinRAR\WinRAR.exe | explorer.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
| 2596 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=1032,16710984831838150874,8504211905127791359,131072 --enable-features=PasswordImport --disable-gpu-sandbox --use-gl=disabled --gpu-preferences=KAAAAAAAAADgACAgAQAAAAAAAAAAAGAAAAAAAAAAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --service-request-channel-token=12845983328400755991 --mojo-platform-channel-handle=3500 /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2648 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1032,16710984831838150874,8504211905127791359,131072 --enable-features=PasswordImport --lang=en-US --no-sandbox --service-request-channel-token=6290247753901947157 --mojo-platform-channel-handle=1164 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
Total events
1 418
Read events
1 343
Write events
72
Delete events
3
Modification events
| (PID) Process: | (2176) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 2540-13256404463353750 |
Value: 259 | |||
| (PID) Process: | (2540) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (2540) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (2540) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (2540) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (2540) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (2540) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (2540) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (2540) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 3252-13245750958665039 |
Value: 0 | |||
| (PID) Process: | (2540) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
Executable files
34
Suspicious files
18
Text files
2 384
Unknown types
3
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2540 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\BrowserMetrics\BrowserMetrics-60141CEF-9EC.pma | — | |
MD5:— | SHA256:— | |||
| 2540 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\3eed9b42-25e8-4453-8a45-3b16adcdbd6a.tmp | — | |
MD5:— | SHA256:— | |||
| 2540 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000048.dbtmp | — | |
MD5:— | SHA256:— | |||
| 2540 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Feature Engagement Tracker\EventDB\LOG.old~RF154511.TMP | text | |
MD5:— | SHA256:— | |||
| 2540 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\CURRENT~RF154550.TMP | text | |
MD5:— | SHA256:— | |||
| 2540 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Feature Engagement Tracker\AvailabilityDB\LOG.old~RF15456f.TMP | text | |
MD5:— | SHA256:— | |||
| 2540 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\CURRENT | text | |
MD5:— | SHA256:— | |||
| 2540 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Session Storage\LOG.old~RF1545cd.TMP | text | |
MD5:— | SHA256:— | |||
| 2540 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2540 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old~RF154698.TMP | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
27
DNS requests
15
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1548 | chrome.exe | 89.44.169.135:443 | mega.nz | Datacenter Luxembourg S.A. | LU | suspicious |
1548 | chrome.exe | 142.250.186.106:443 | safebrowsing.googleapis.com | Google Inc. | US | whitelisted |
1548 | chrome.exe | 172.217.212.138:443 | clients1.google.com | Google Inc. | US | whitelisted |
1548 | chrome.exe | 66.203.124.37:443 | eu.static.mega.co.nz | RealNetworks, Inc. | US | suspicious |
1548 | chrome.exe | 142.250.186.35:443 | ssl.gstatic.com | Google Inc. | US | whitelisted |
1548 | chrome.exe | 89.44.168.167:443 | gfs270n212.userstorage.mega.co.nz | Datacenter Luxembourg S.A. | LU | unknown |
1548 | chrome.exe | 94.24.36.42:443 | gfs262n332.userstorage.mega.co.nz | — | RO | unknown |
1548 | chrome.exe | 185.206.26.48:443 | gfs208n138.userstorage.mega.co.nz | — | DE | unknown |
— | — | 94.24.37.47:443 | gfs206n137.userstorage.mega.co.nz | — | RO | unknown |
1548 | chrome.exe | 185.206.24.73:443 | gfs204n145.userstorage.mega.co.nz | MEGA Limited | — | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
mega.nz |
| whitelisted |
accounts.google.com |
| shared |
safebrowsing.googleapis.com |
| whitelisted |
clients1.google.com |
| whitelisted |
eu.static.mega.co.nz |
| shared |
g.api.mega.co.nz |
| shared |
ssl.gstatic.com |
| whitelisted |
gfs270n212.userstorage.mega.co.nz |
| unknown |
gfs206n137.userstorage.mega.co.nz |
| unknown |
gfs214n138.userstorage.mega.co.nz |
| unknown |