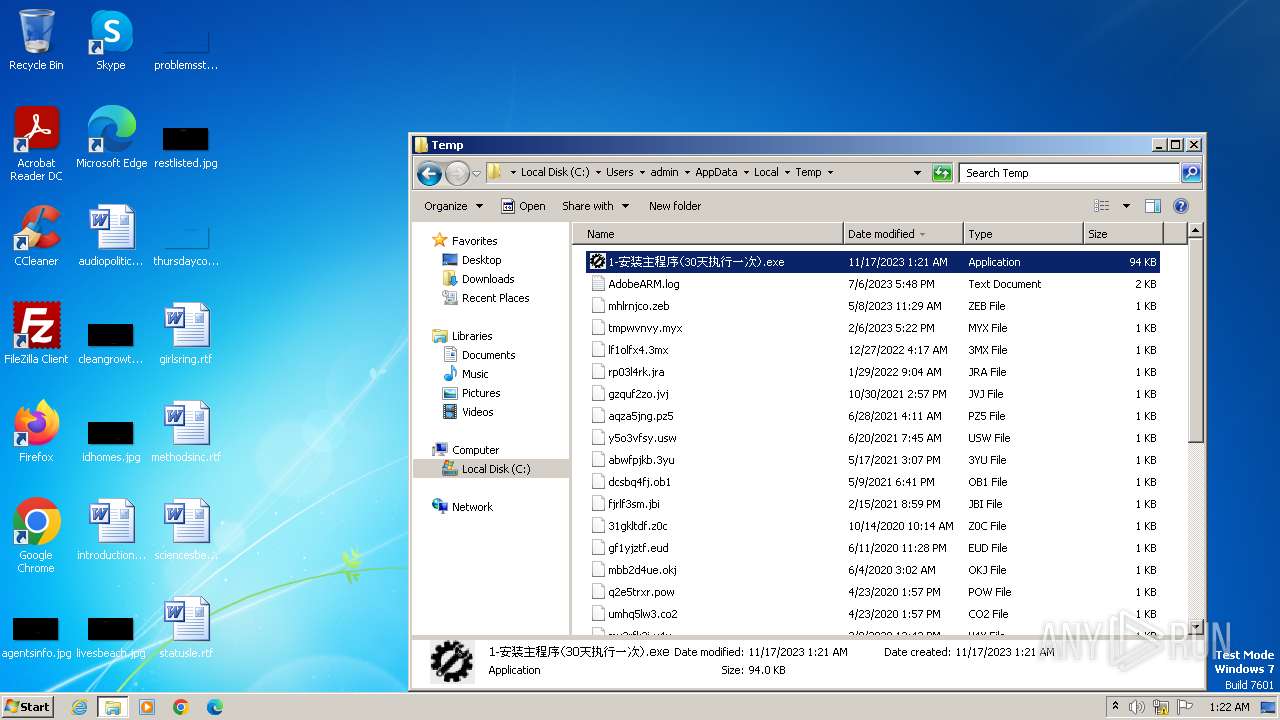
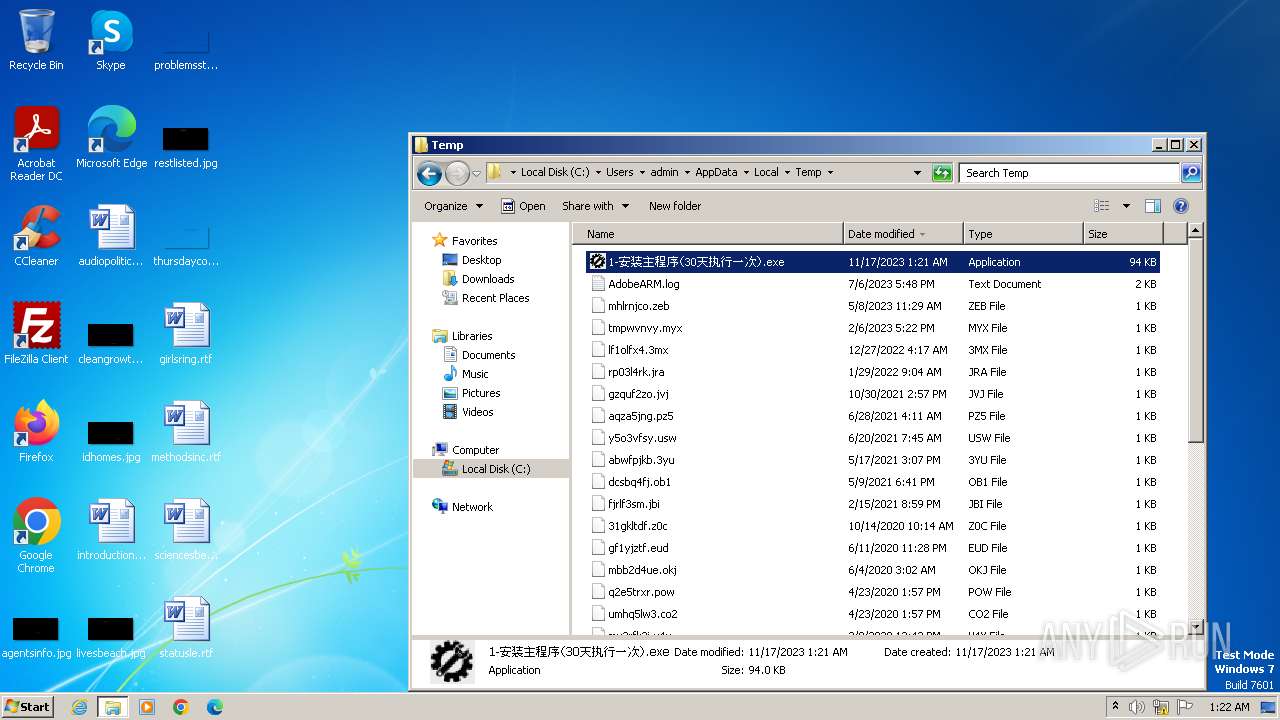
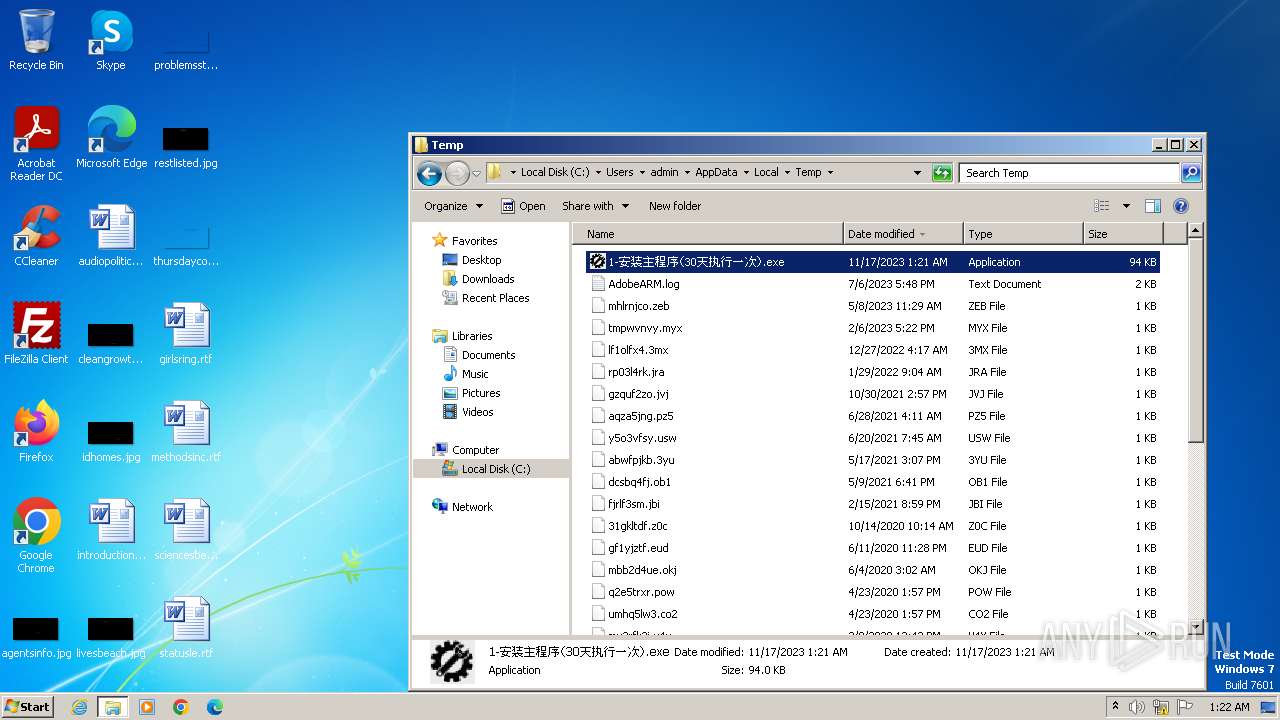
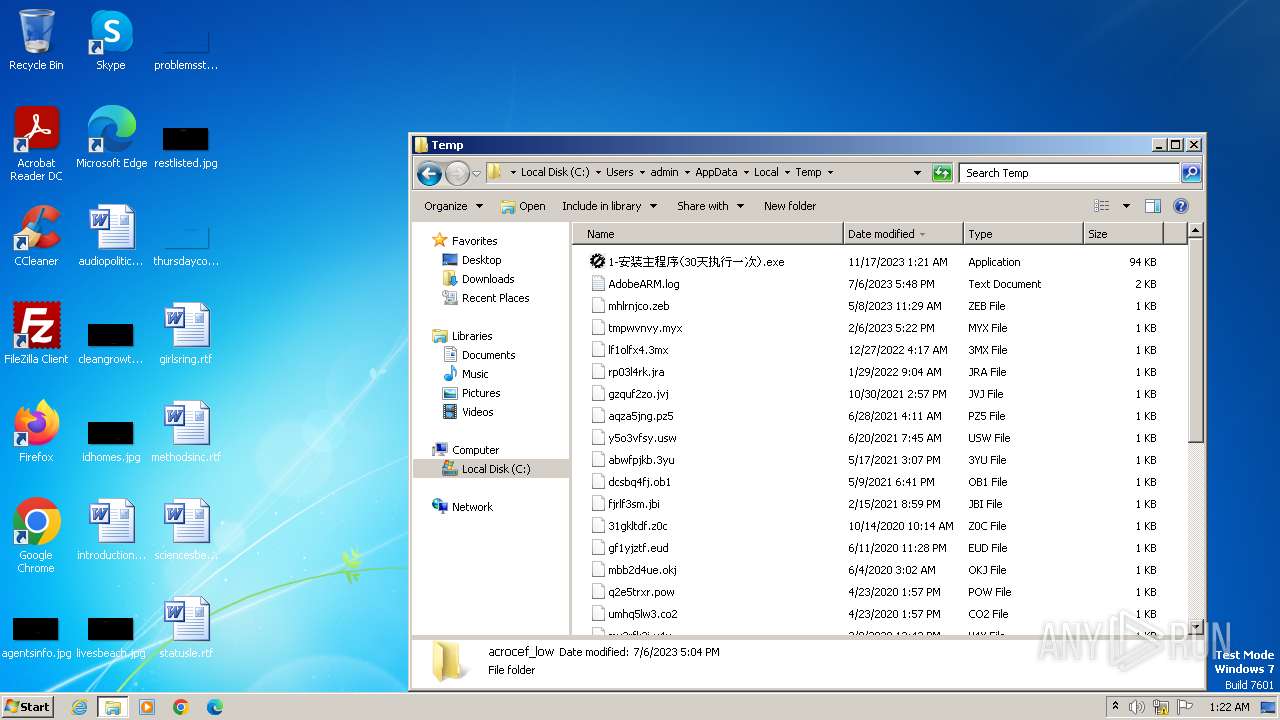
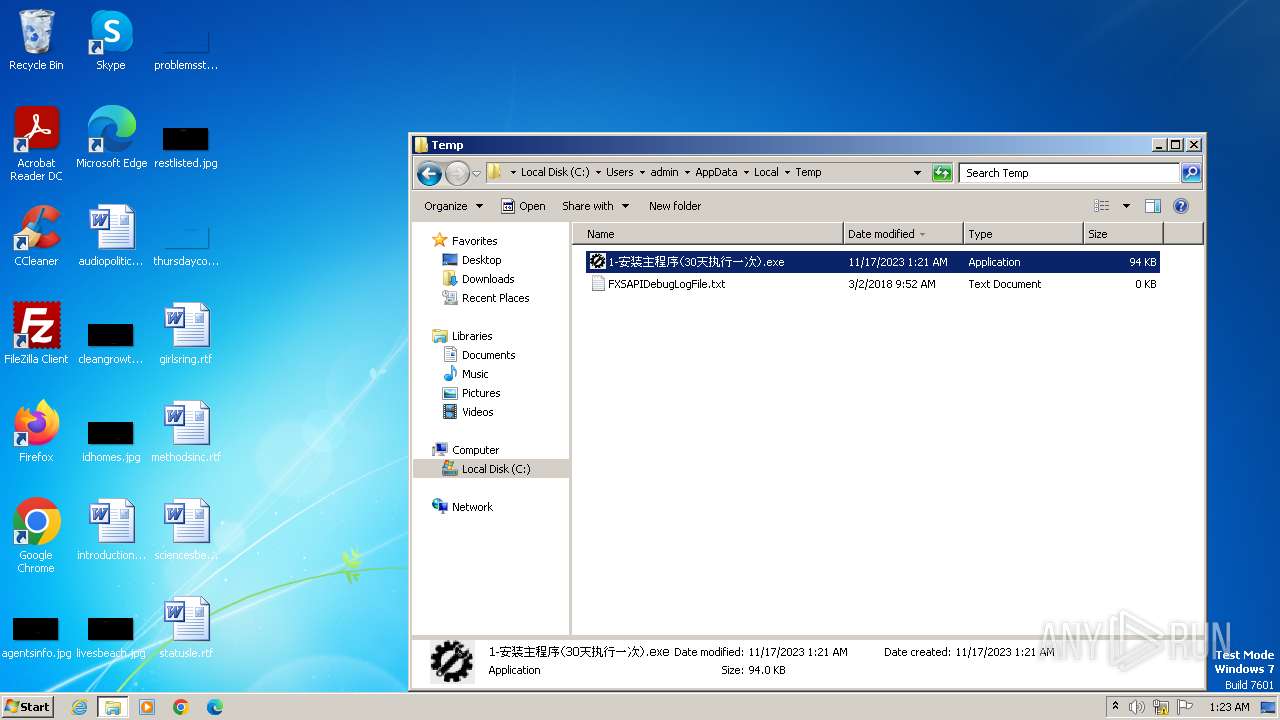
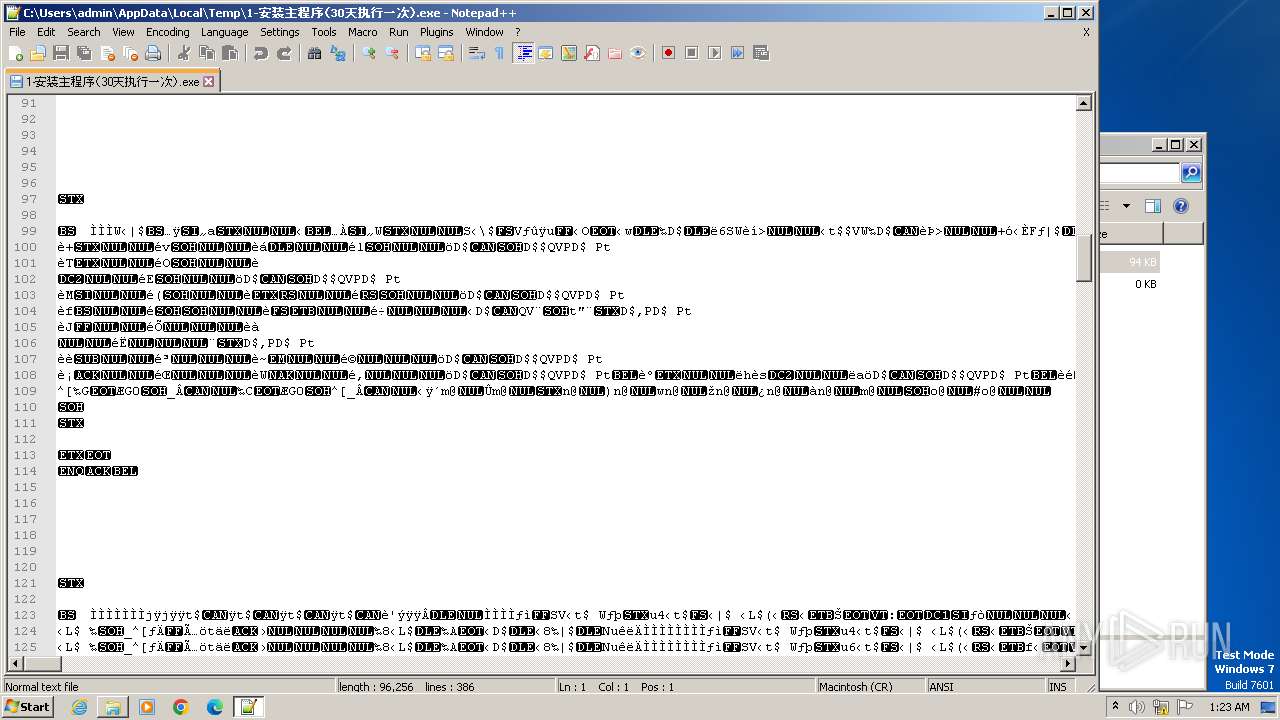
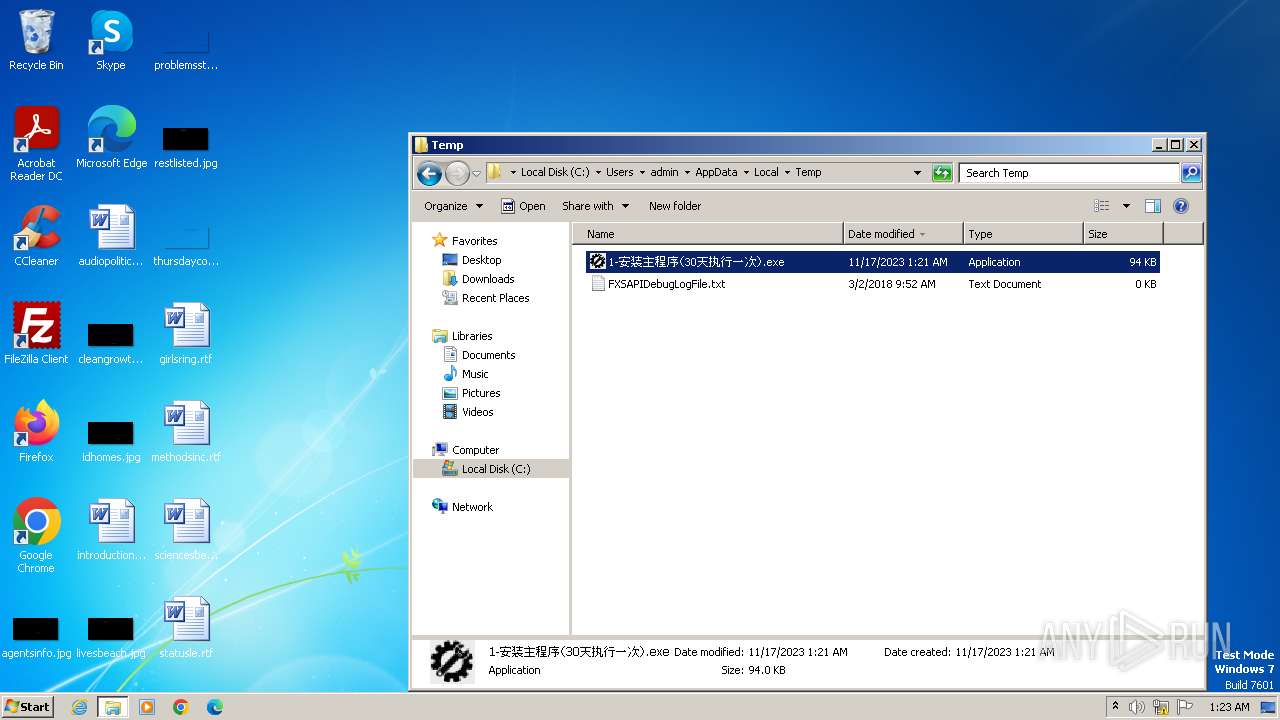
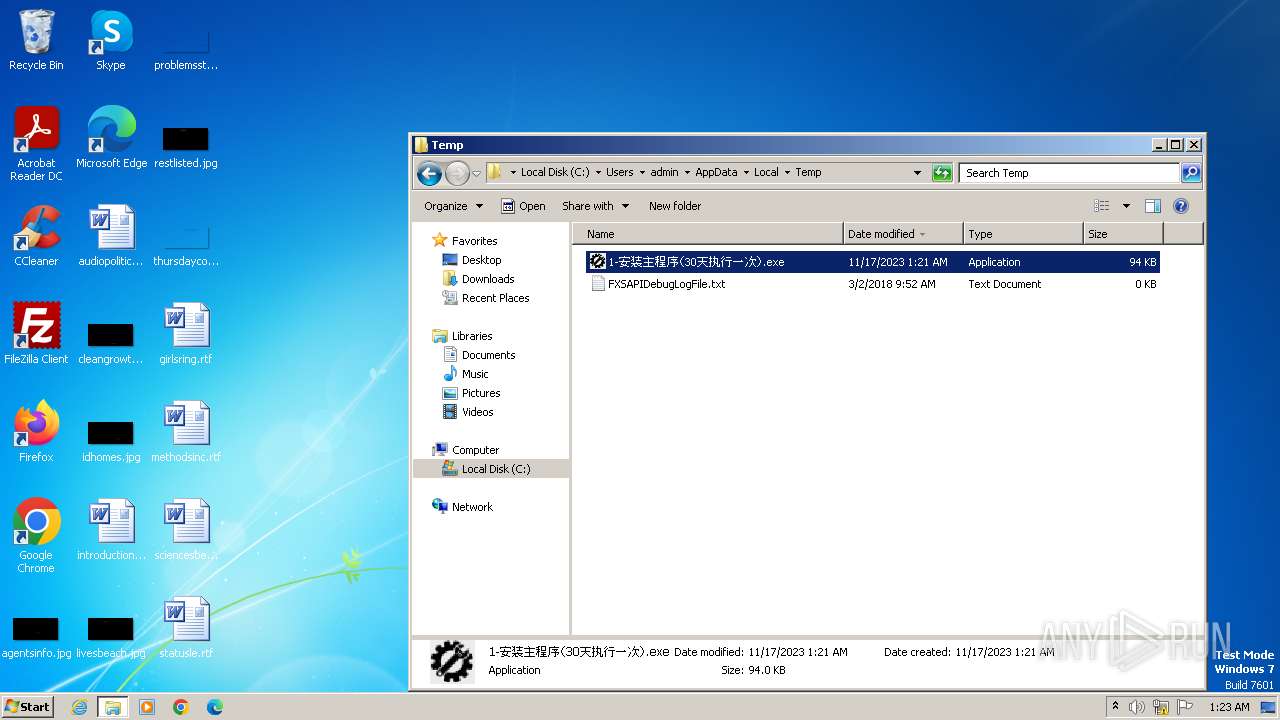
| File name: | 1-安装主程序(30天执行一次).exe |
| Full analysis: | https://app.any.run/tasks/1dbc98c3-8aea-4996-aec3-5083e95e6f9c |
| Verdict: | Malicious activity |
| Analysis date: | November 17, 2023, 01:21:11 |
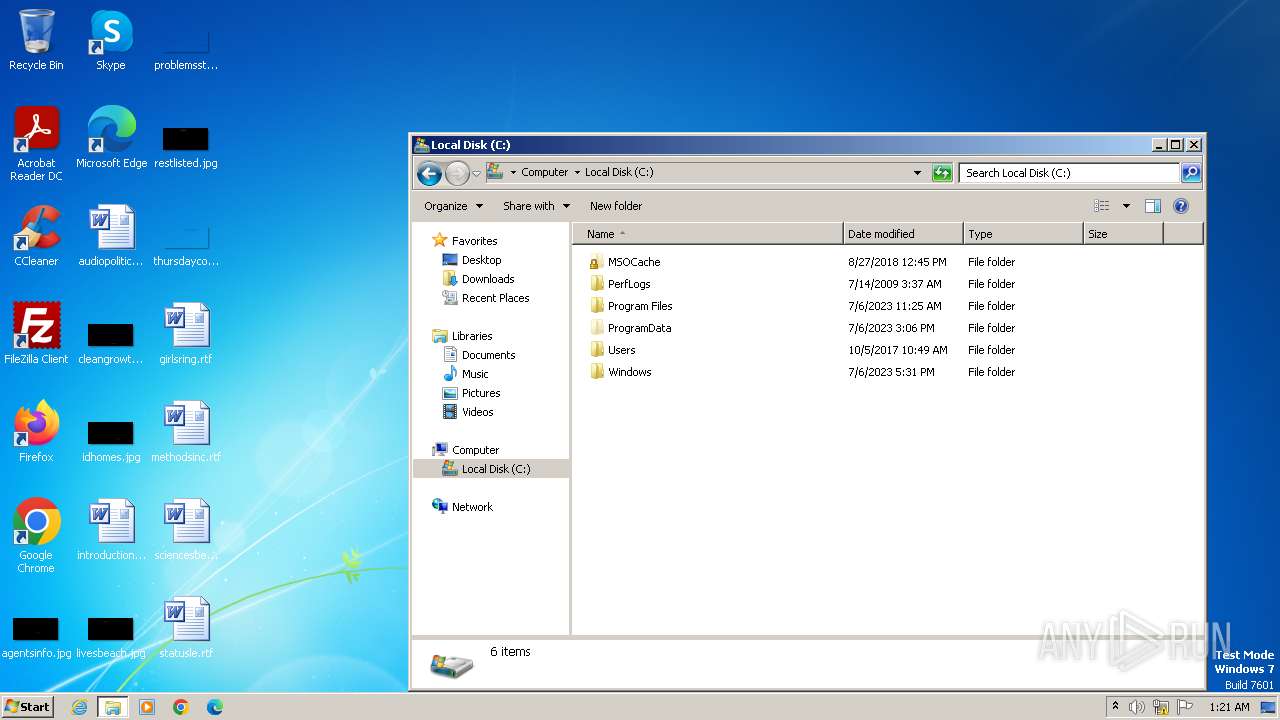
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
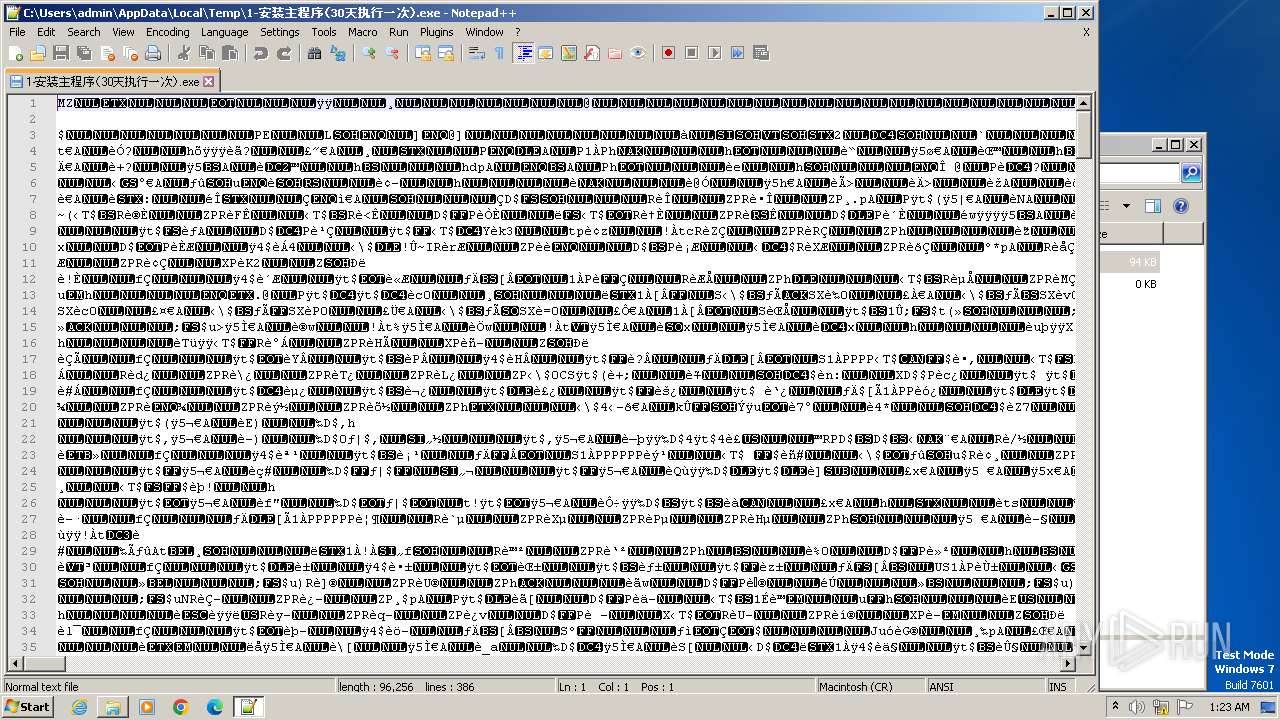
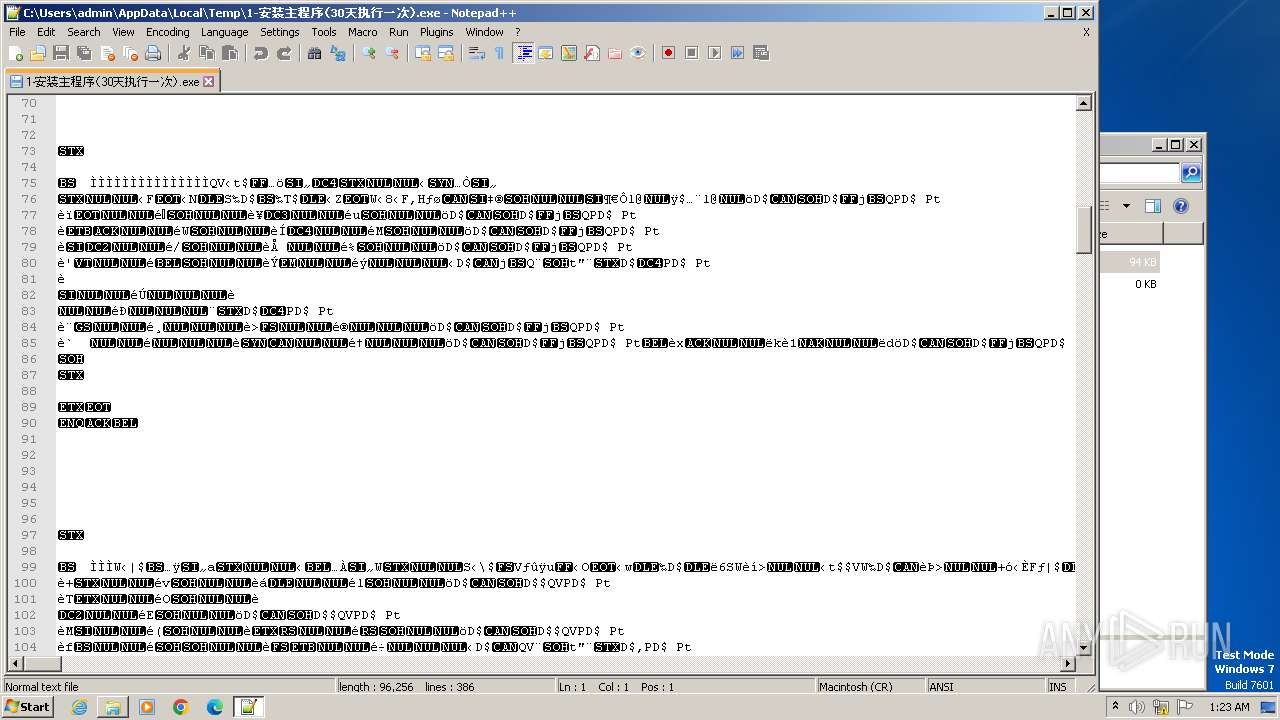
| MIME: | application/x-dosexec |
| File info: | PE32 executable (console) Intel 80386, for MS Windows |
| MD5: | 56C52DF4884464316E0CC03E614DB34D |
| SHA1: | 38C2C278E7ED4198270C9F5DAE41F3C4BA718192 |
| SHA256: | 7D7C670160A92BBDC200B892FC963076E4A2F290B621E464F7AE2E8B59830A9B |
| SSDEEP: | 1536:rCYa+ihNuNMv2blAyHQ5MaAt7JmyxCV7tBKhilgVcRdMK/HOU:rCYa+0Nu6vQAkQ5S7JmyxCbBKhiTbMKL |
MALICIOUS
No malicious indicators.SUSPICIOUS
Starts CMD.EXE for commands execution
- 1-安装主程序(30天执行一次).exe (PID: 3436)
- 1-安装主程序(30天执行一次).exe (PID: 148)
- 1-安装主程序(30天执行一次).exe (PID: 2296)
- 1-安装主程序(30天执行一次).exe (PID: 1592)
- 1-安装主程序(30天执行一次).exe (PID: 1876)
- 1-安装主程序(30天执行一次).exe (PID: 2432)
- 1-安装主程序(30天执行一次).exe (PID: 3832)
- 1-安装主程序(30天执行一次).exe (PID: 3548)
Executing commands from a ".bat" file
- 1-安装主程序(30天执行一次).exe (PID: 3436)
- 1-安装主程序(30天执行一次).exe (PID: 148)
- 1-安装主程序(30天执行一次).exe (PID: 2296)
- 1-安装主程序(30天执行一次).exe (PID: 1592)
- 1-安装主程序(30天执行一次).exe (PID: 1876)
- 1-安装主程序(30天执行一次).exe (PID: 2432)
- 1-安装主程序(30天执行一次).exe (PID: 3832)
- 1-安装主程序(30天执行一次).exe (PID: 3548)
INFO
Checks supported languages
- 1-安装主程序(30天执行一次).exe (PID: 3436)
- 1-安装主程序(30天执行一次).exe (PID: 148)
- 1-安装主程序(30天执行一次).exe (PID: 2296)
- 1-安装主程序(30天执行一次).exe (PID: 1592)
- 1-安装主程序(30天执行一次).exe (PID: 2432)
- 1-安装主程序(30天执行一次).exe (PID: 3832)
- 1-安装主程序(30天执行一次).exe (PID: 3548)
- 1-安装主程序(30天执行一次).exe (PID: 1876)
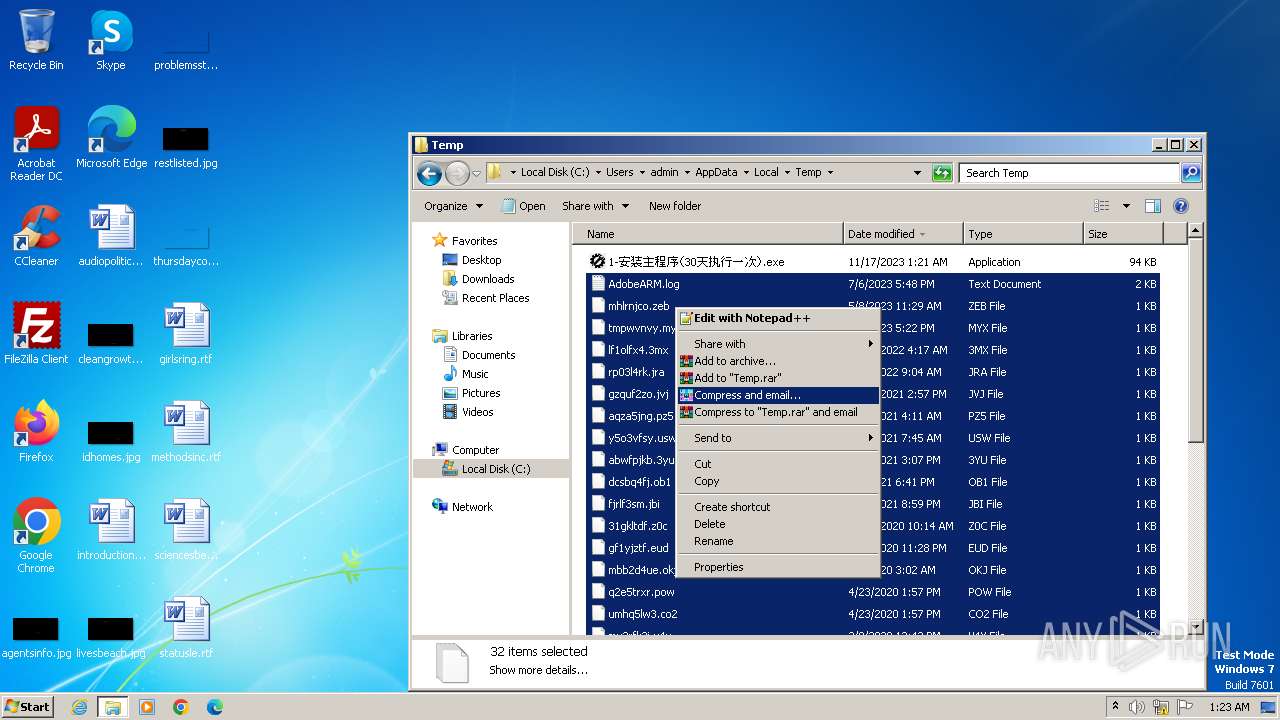
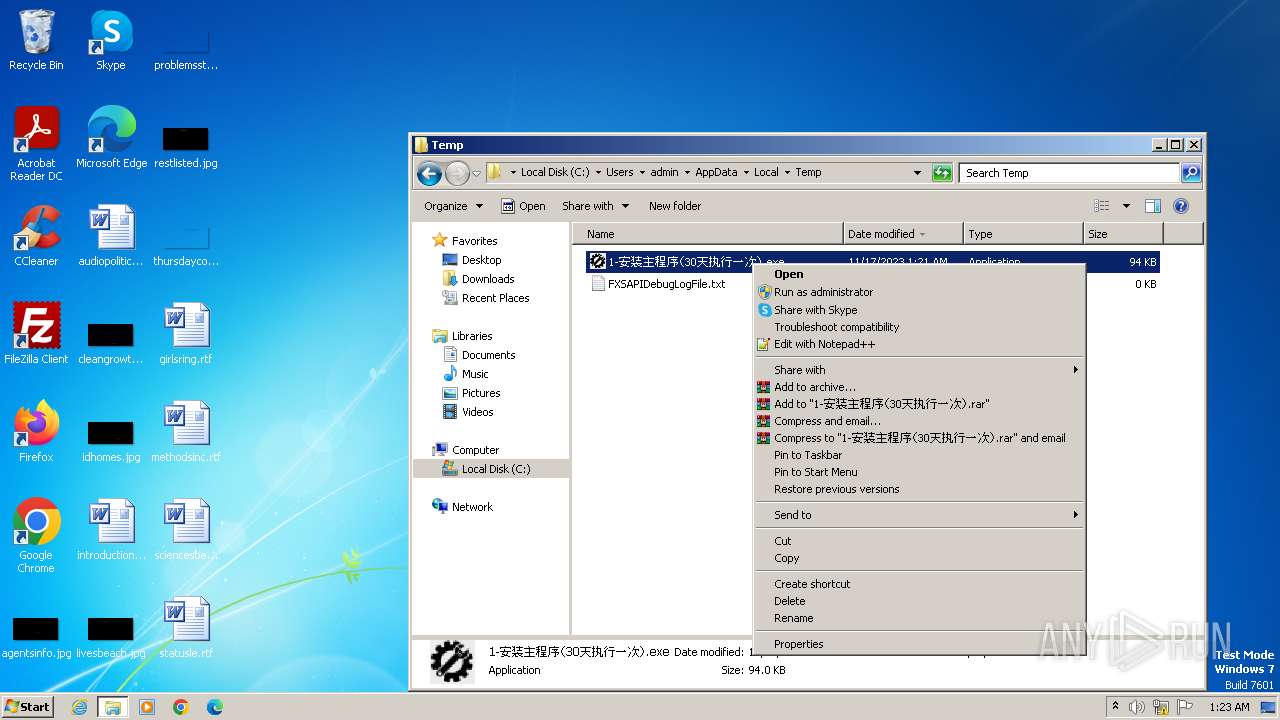
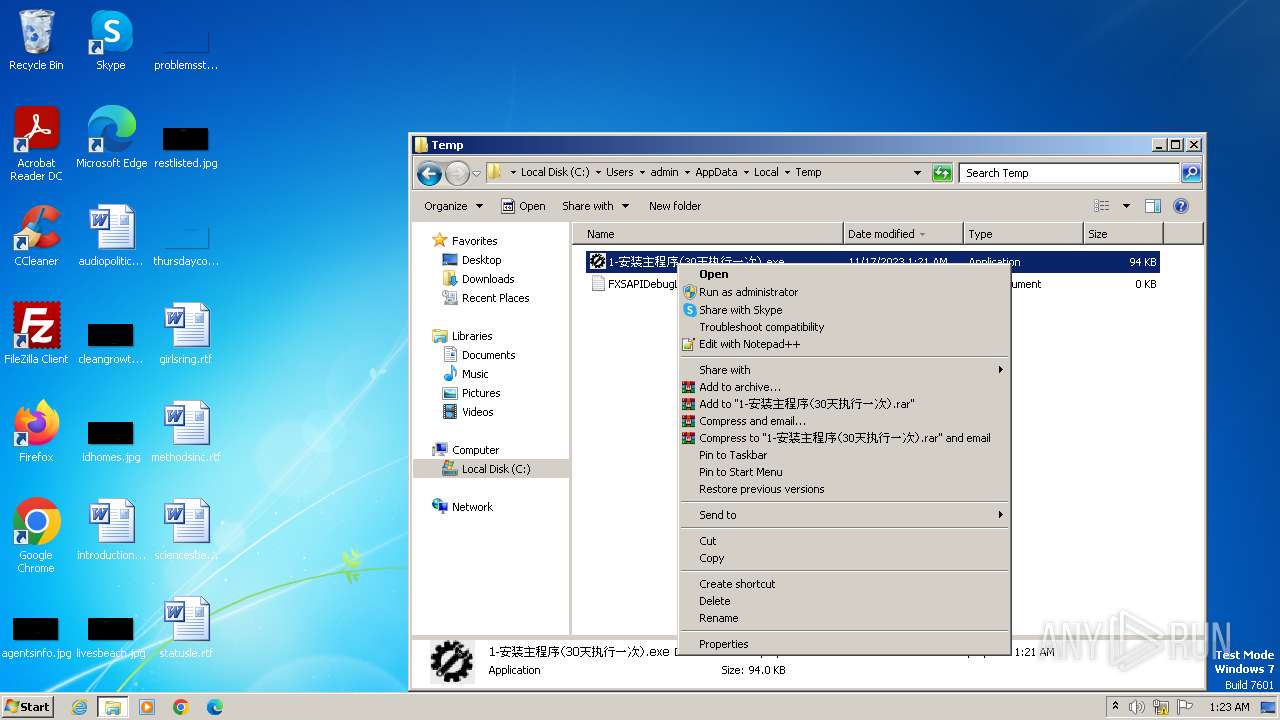
Manual execution by a user
- 1-安装主程序(30天执行一次).exe (PID: 148)
- 1-安装主程序(30天执行一次).exe (PID: 2296)
- 1-安装主程序(30天执行一次).exe (PID: 1592)
- 1-安装主程序(30天执行一次).exe (PID: 1876)
- 1-安装主程序(30天执行一次).exe (PID: 2432)
- 1-安装主程序(30天执行一次).exe (PID: 3832)
- notepad++.exe (PID: 3984)
- 1-安装主程序(30天执行一次).exe (PID: 3548)
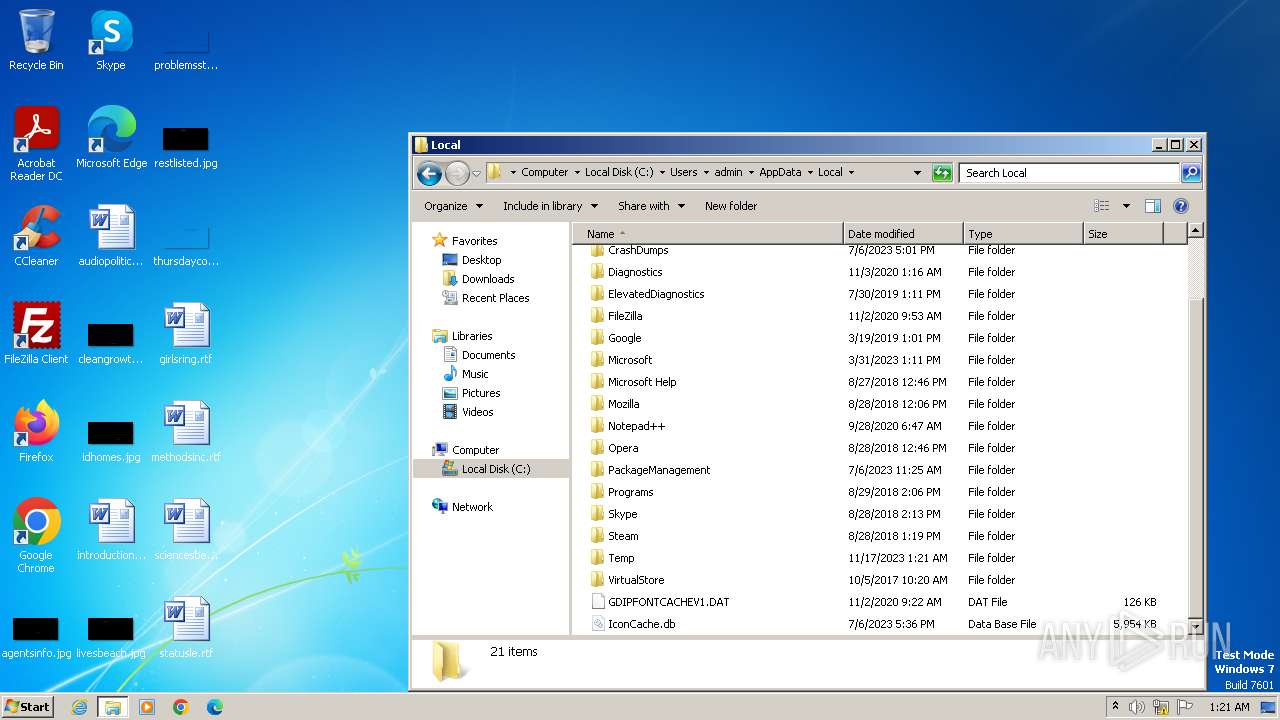
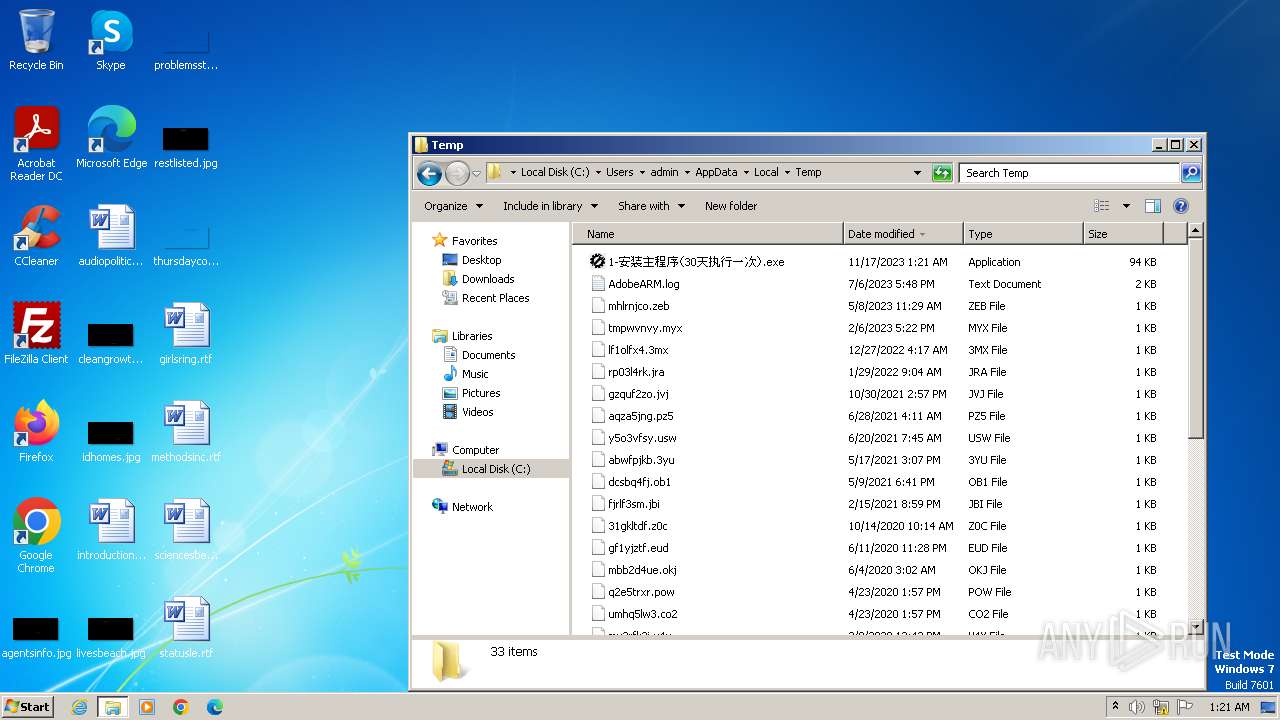
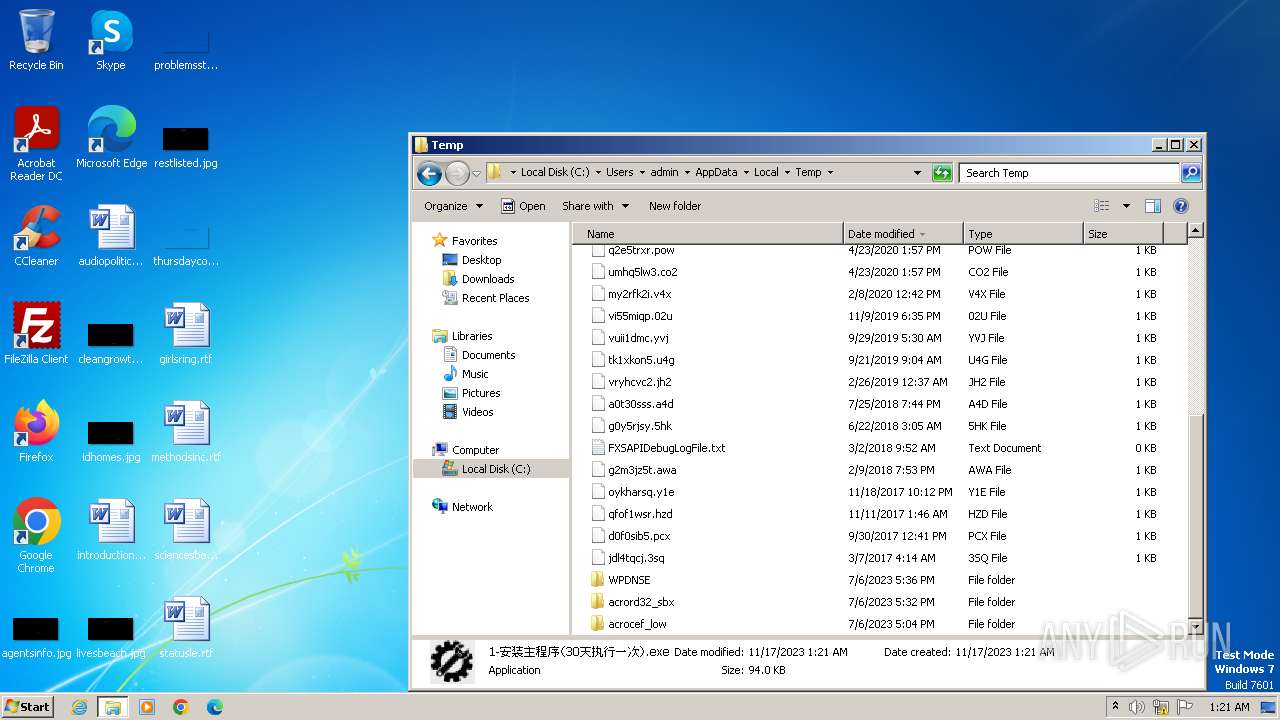
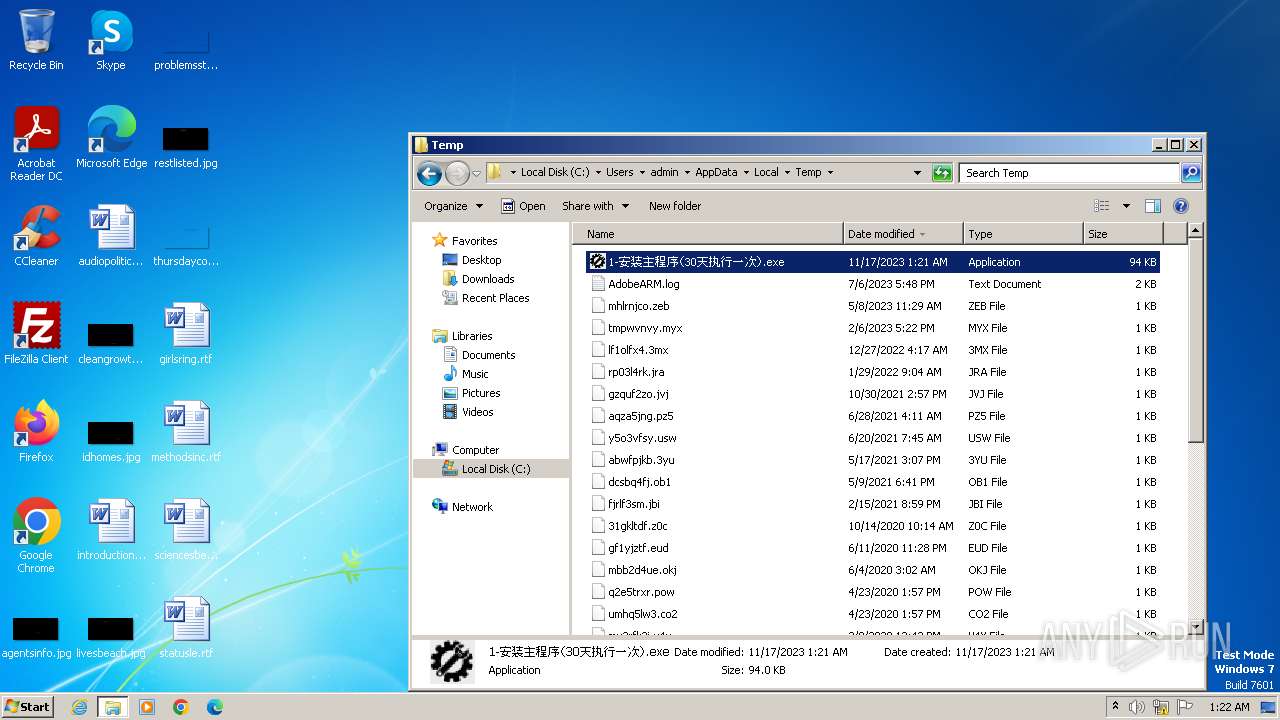
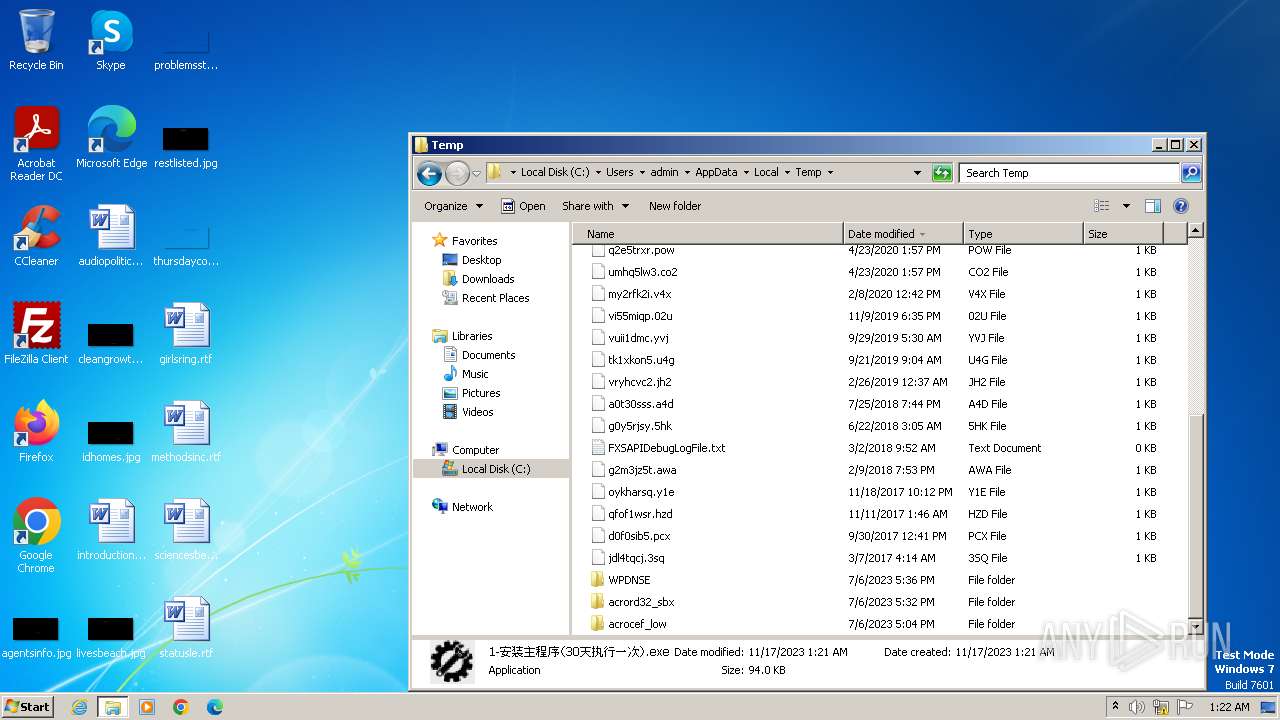
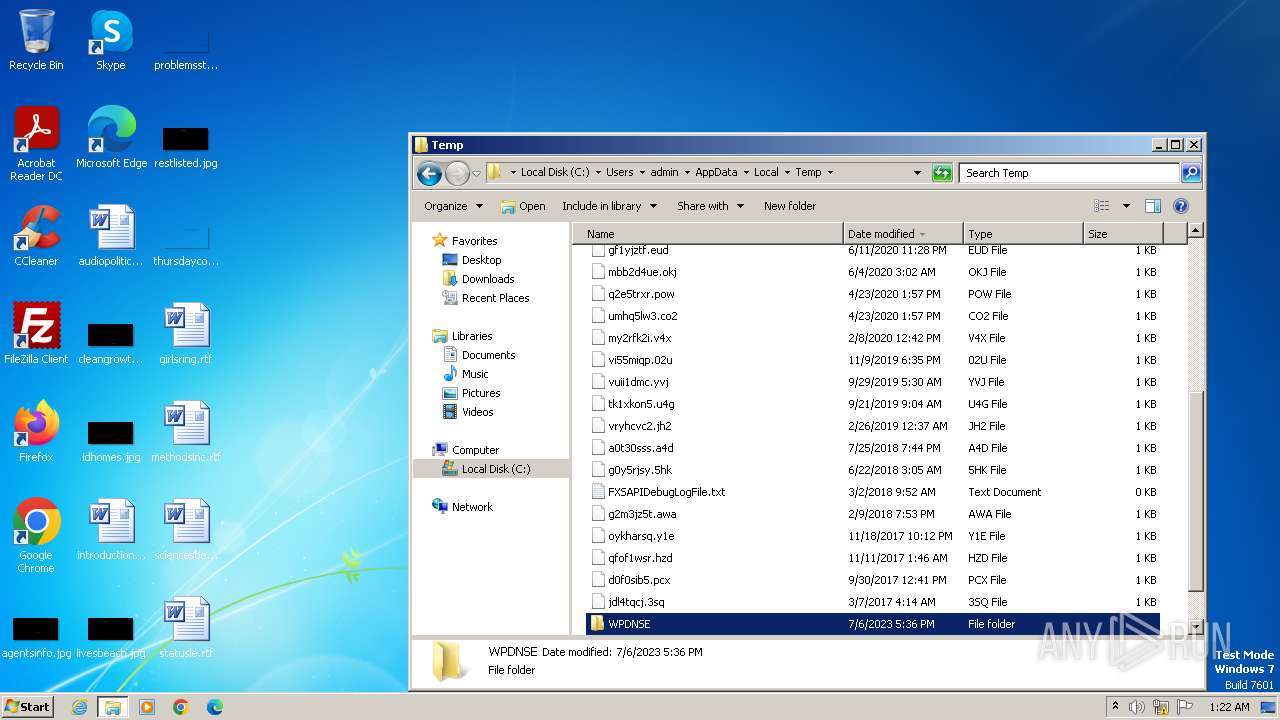
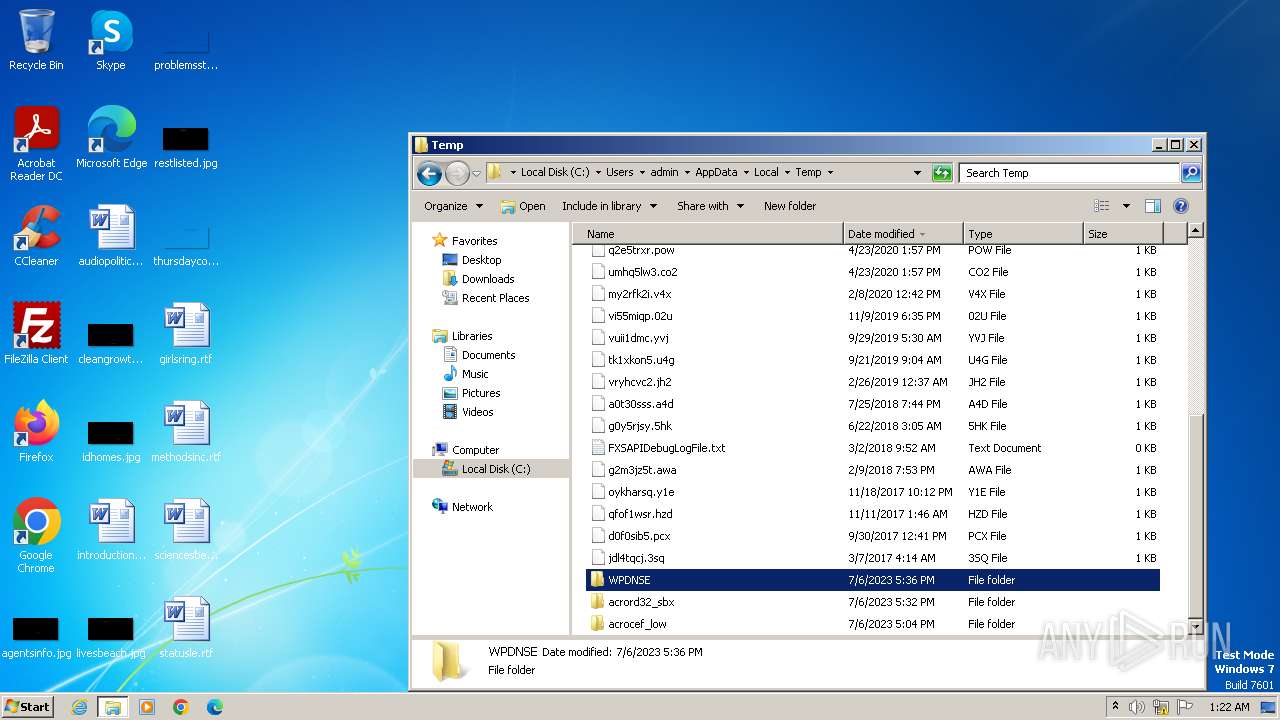
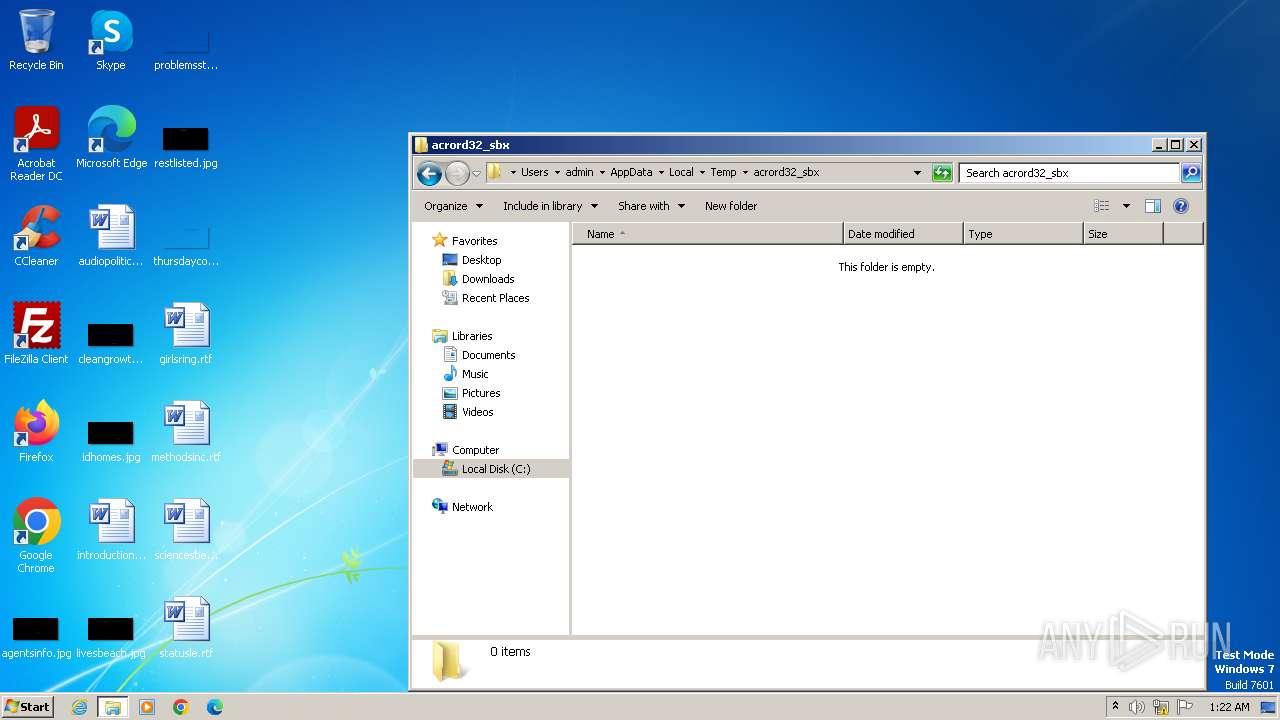
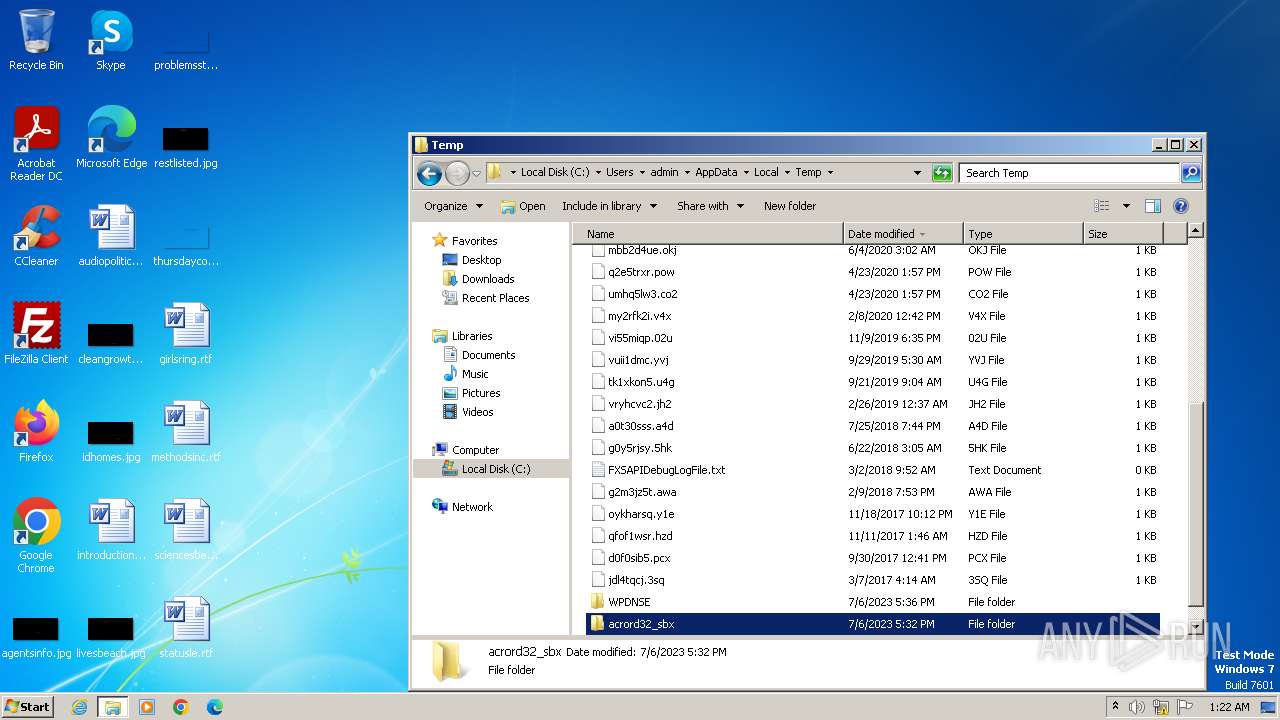
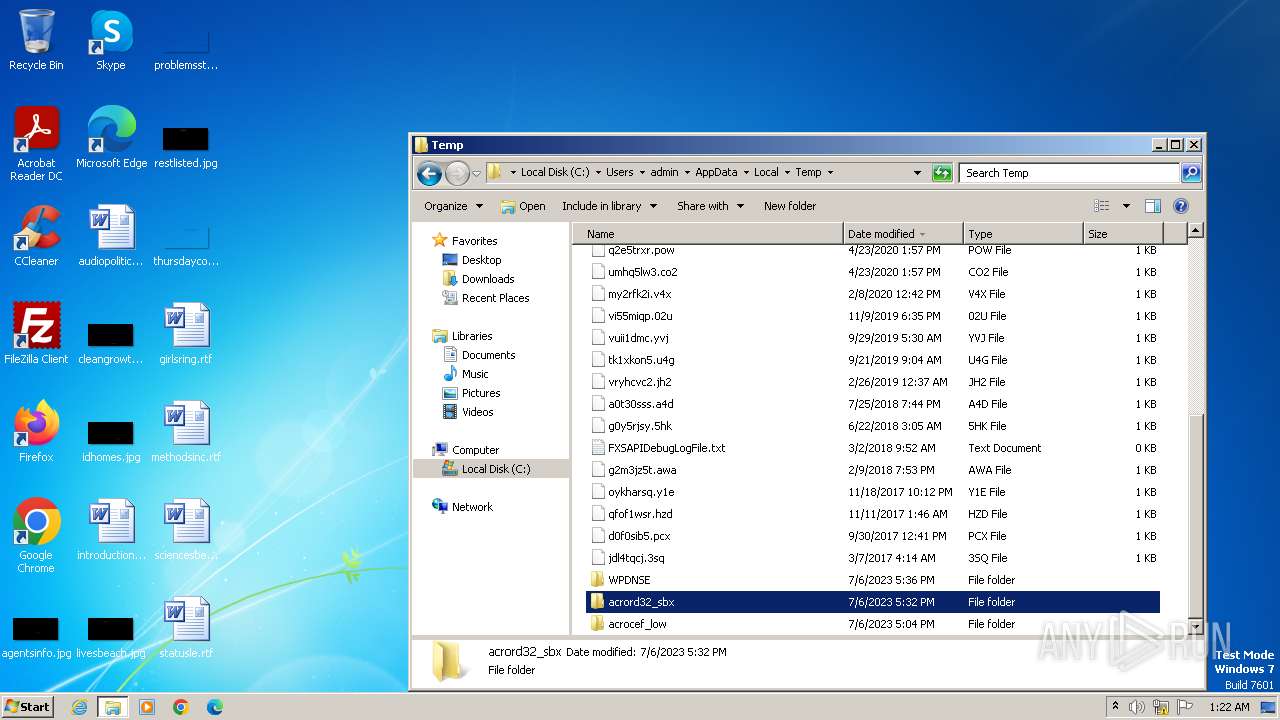
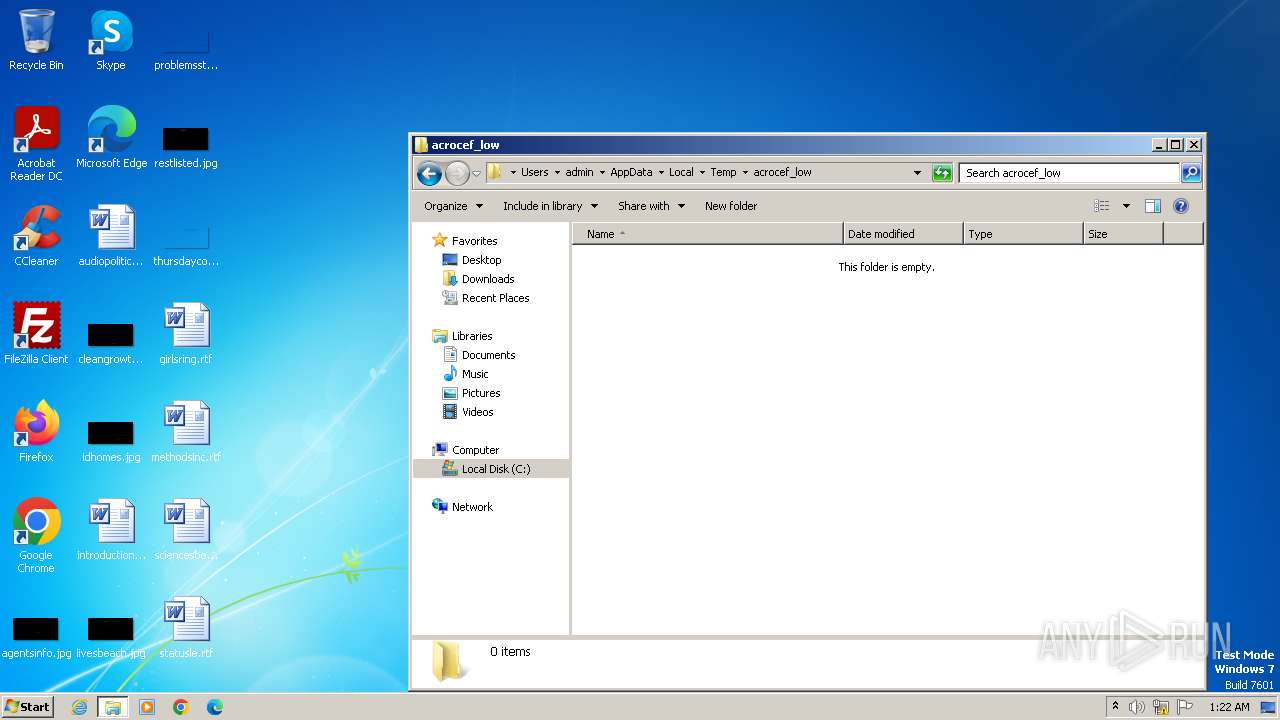
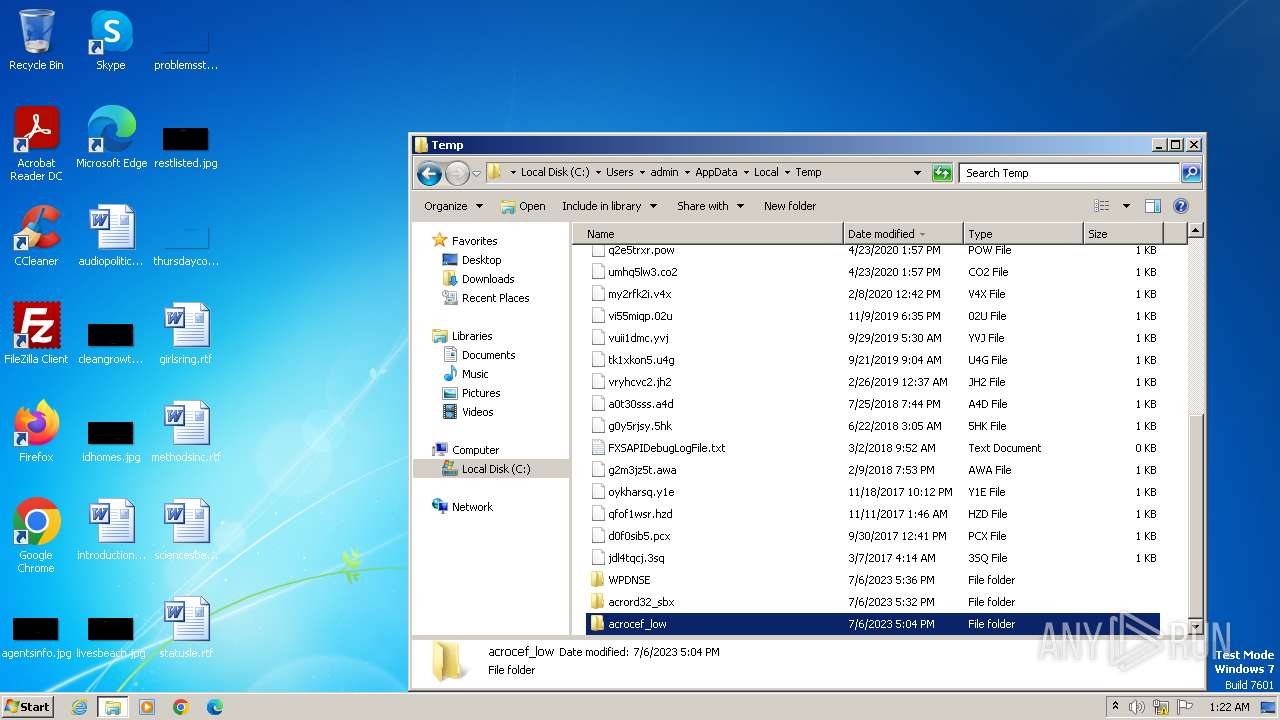
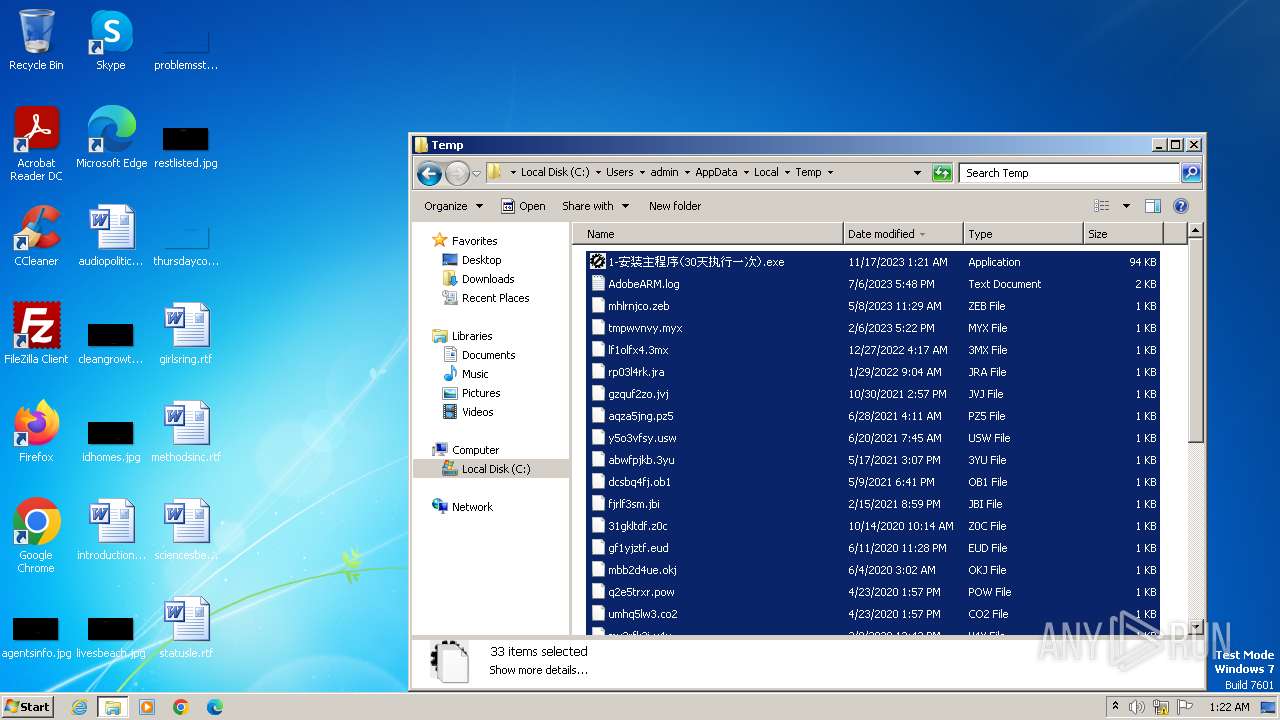
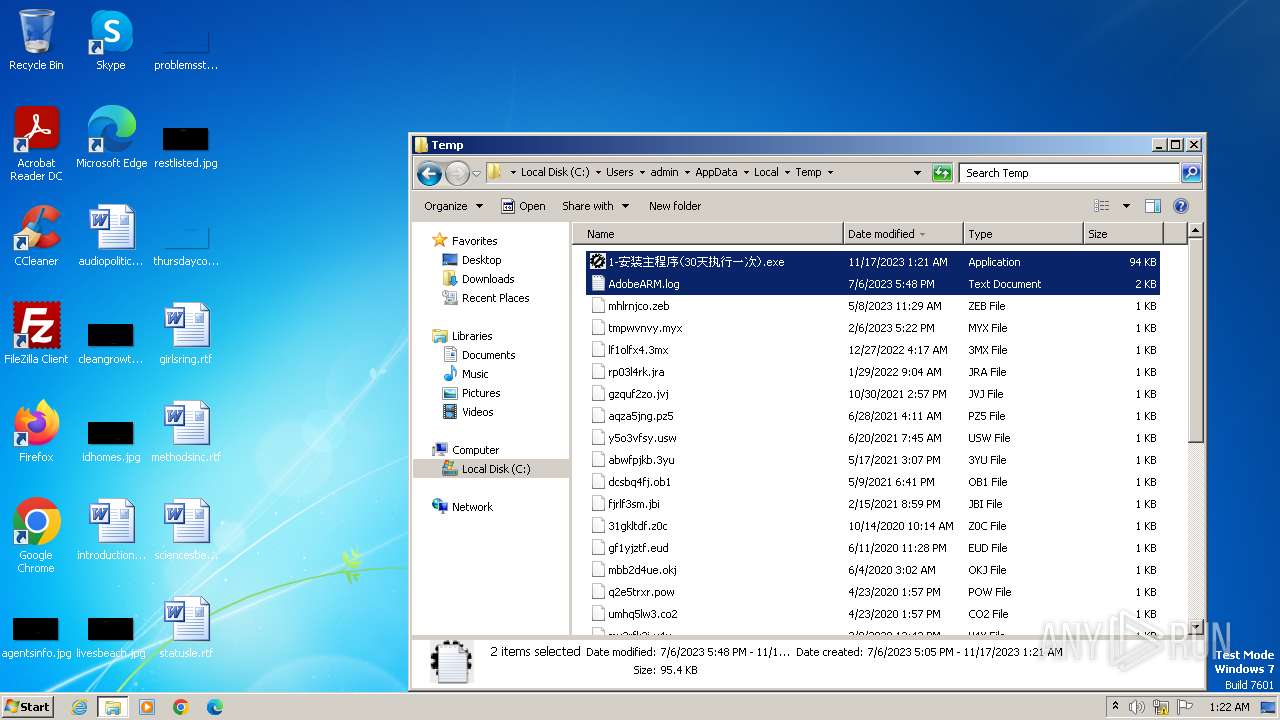
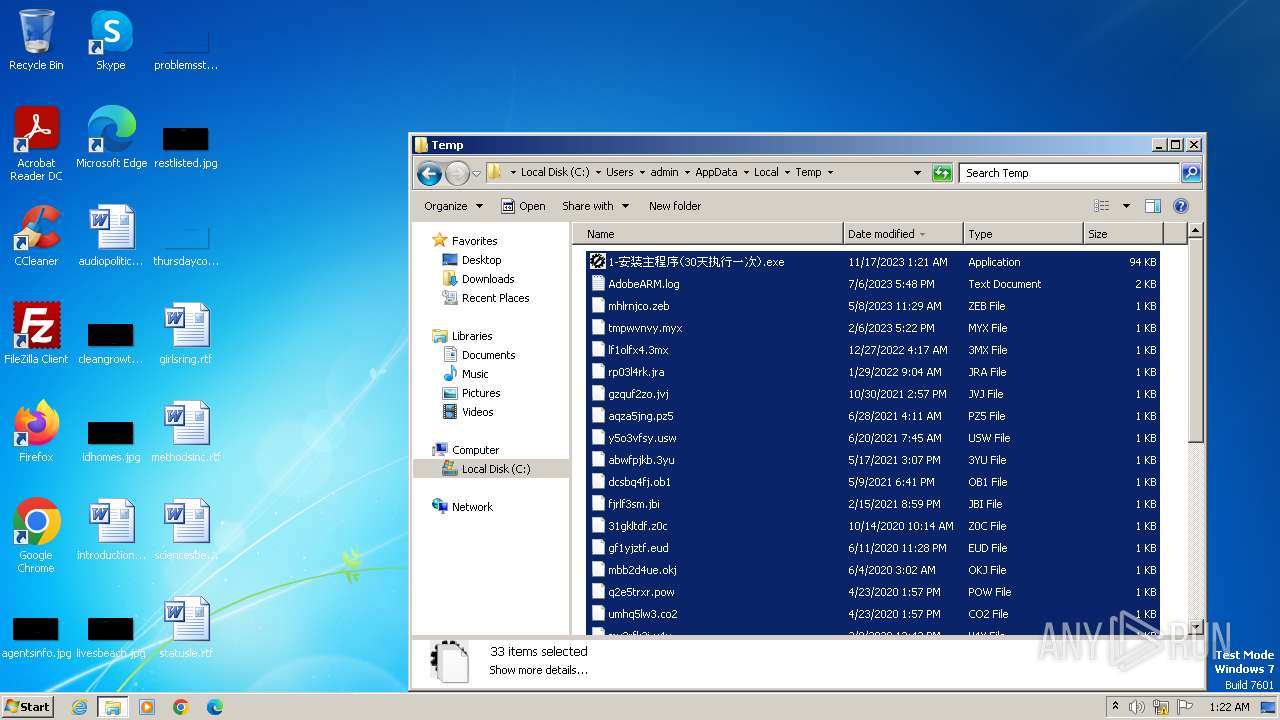
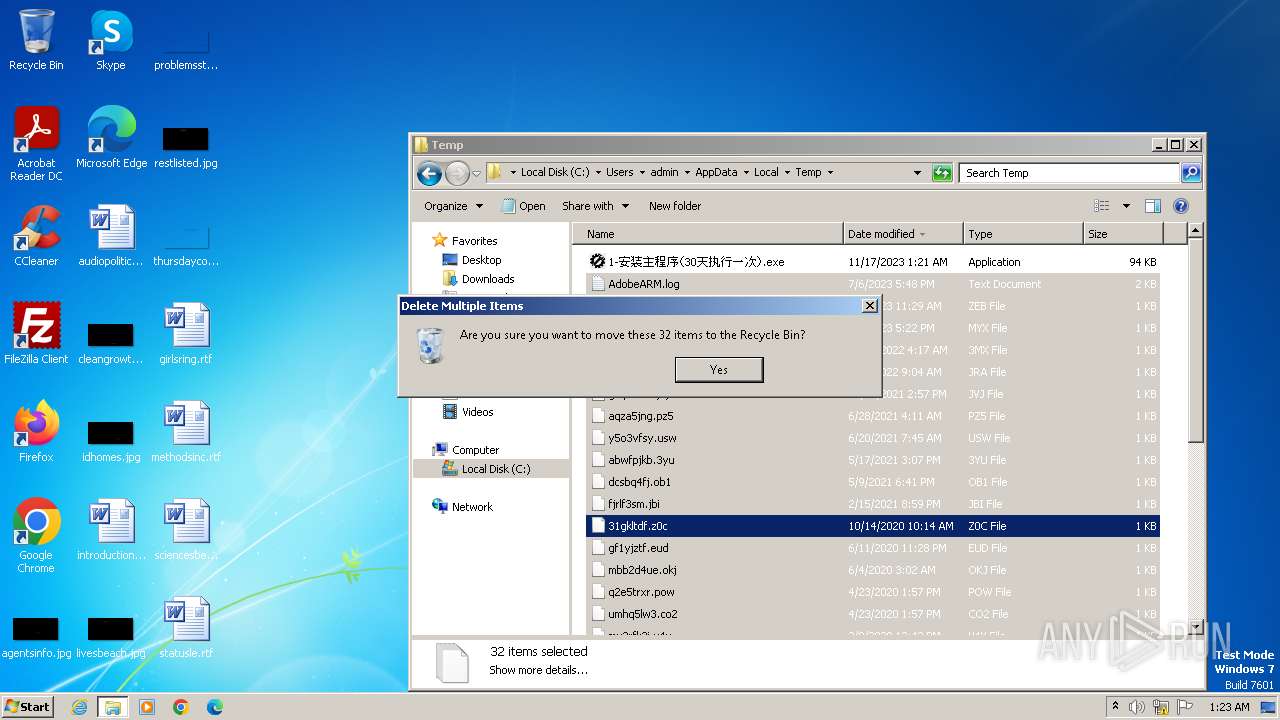
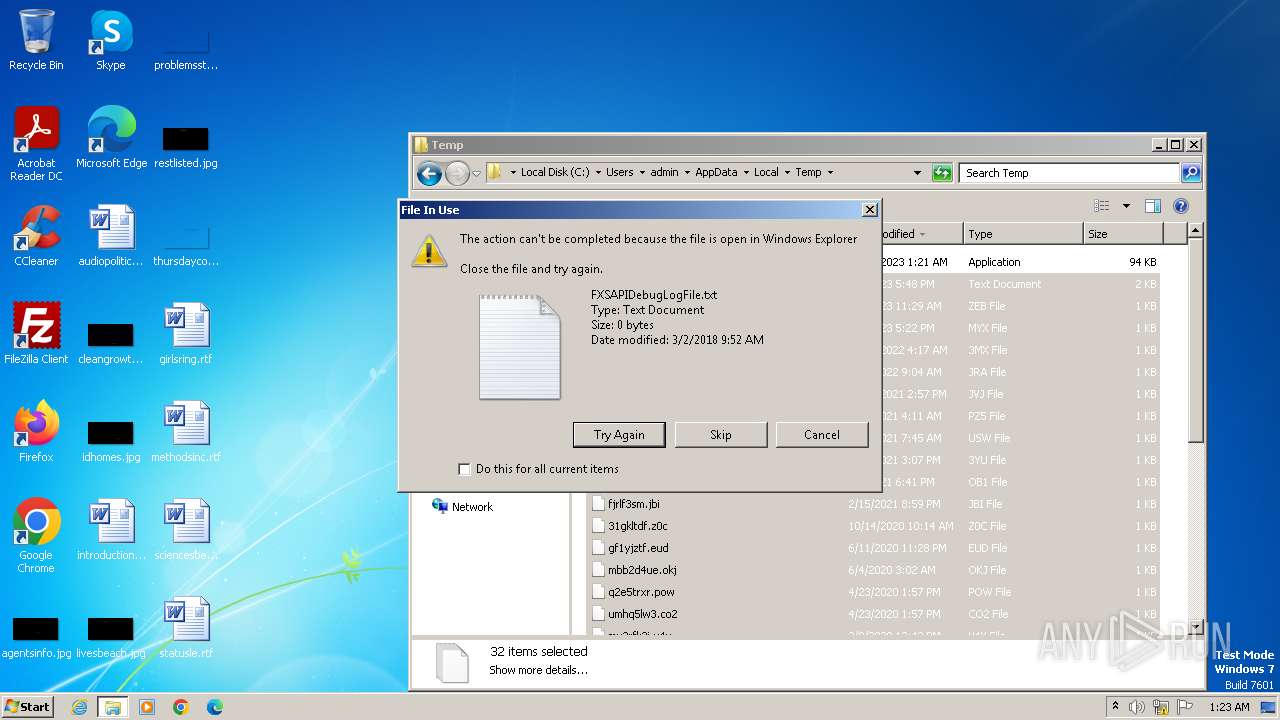
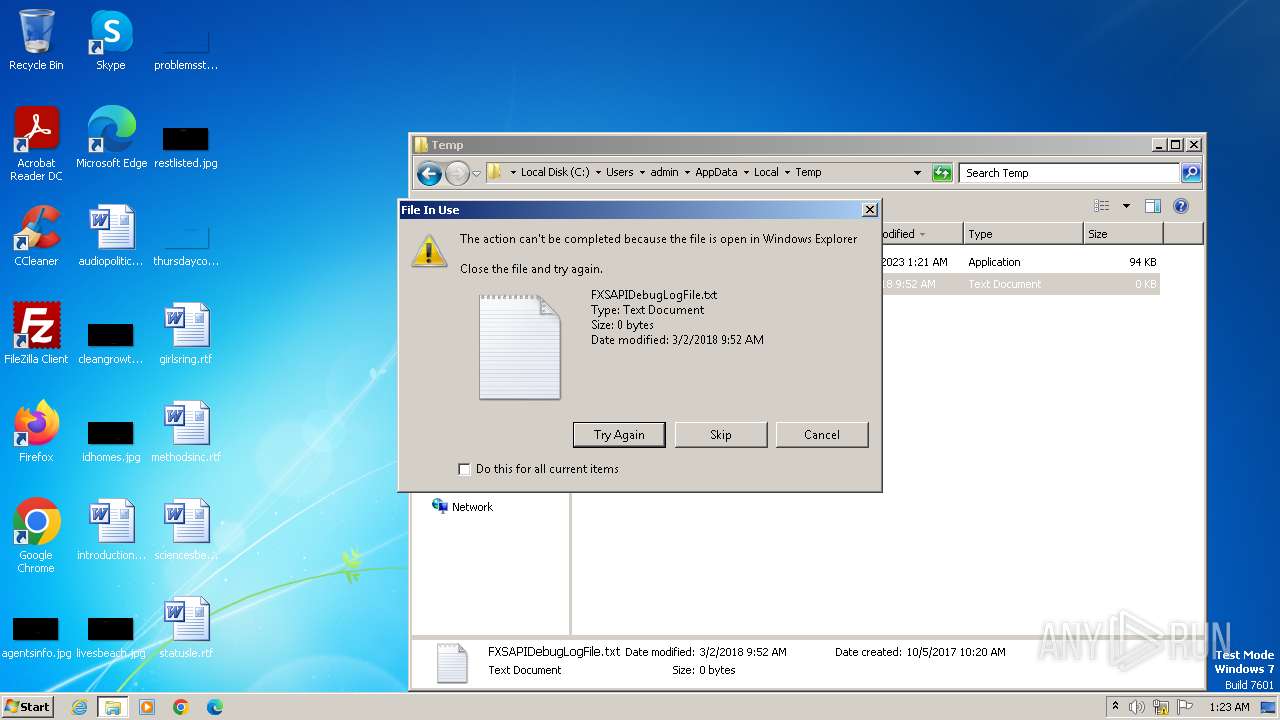
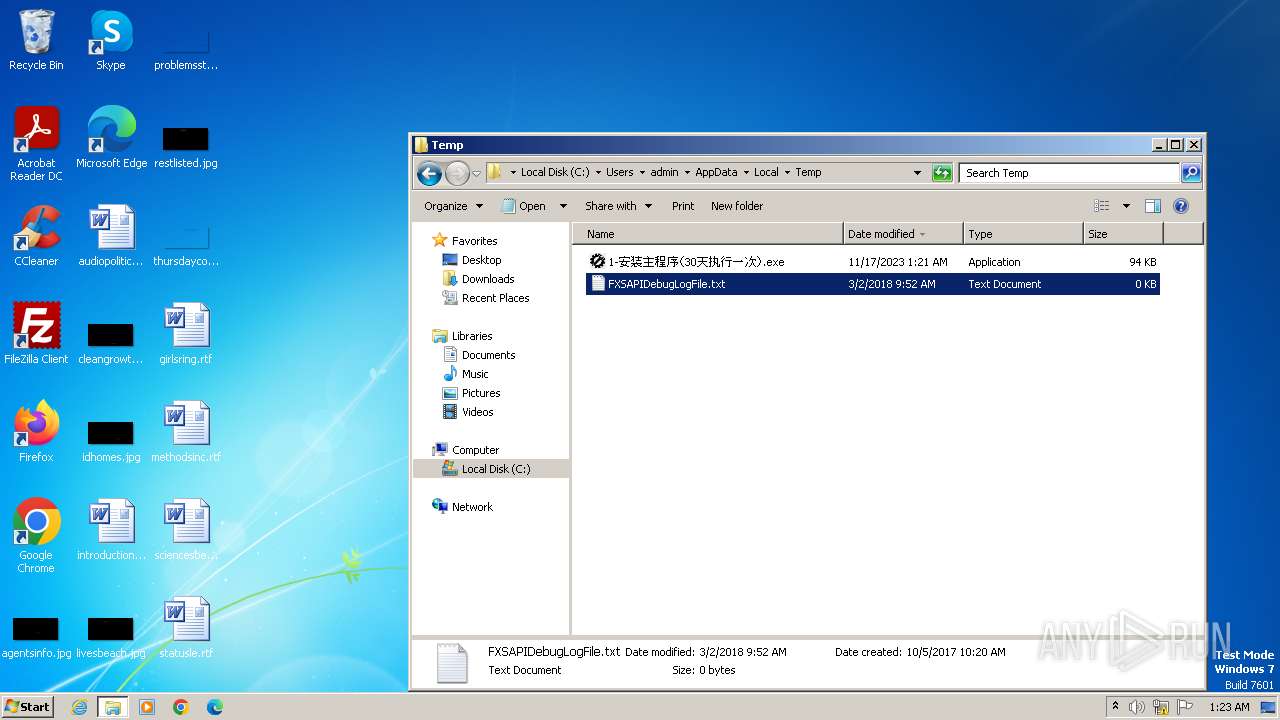
Create files in a temporary directory
- 1-安装主程序(30天执行一次).exe (PID: 148)
- 1-安装主程序(30天执行一次).exe (PID: 3436)
- 1-安装主程序(30天执行一次).exe (PID: 2296)
- 1-安装主程序(30天执行一次).exe (PID: 1592)
- 1-安装主程序(30天执行一次).exe (PID: 1876)
- 1-安装主程序(30天执行一次).exe (PID: 2432)
- 1-安装主程序(30天执行一次).exe (PID: 3832)
- 1-安装主程序(30天执行一次).exe (PID: 3548)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (41) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (36.3) |
| .dll | | | Win32 Dynamic Link Library (generic) (8.6) |
| .exe | | | Win32 Executable (generic) (5.9) |
| .exe | | | Win16/32 Executable Delphi generic (2.7) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2019:07:30 10:52:45+02:00 |
| ImageFileCharacteristics: | No relocs, Executable, No line numbers, No symbols, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 2.5 |
| CodeSize: | 70656 |
| InitializedDataSize: | 24576 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x1000 |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows command line |
Total processes
101
Monitored processes
49
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
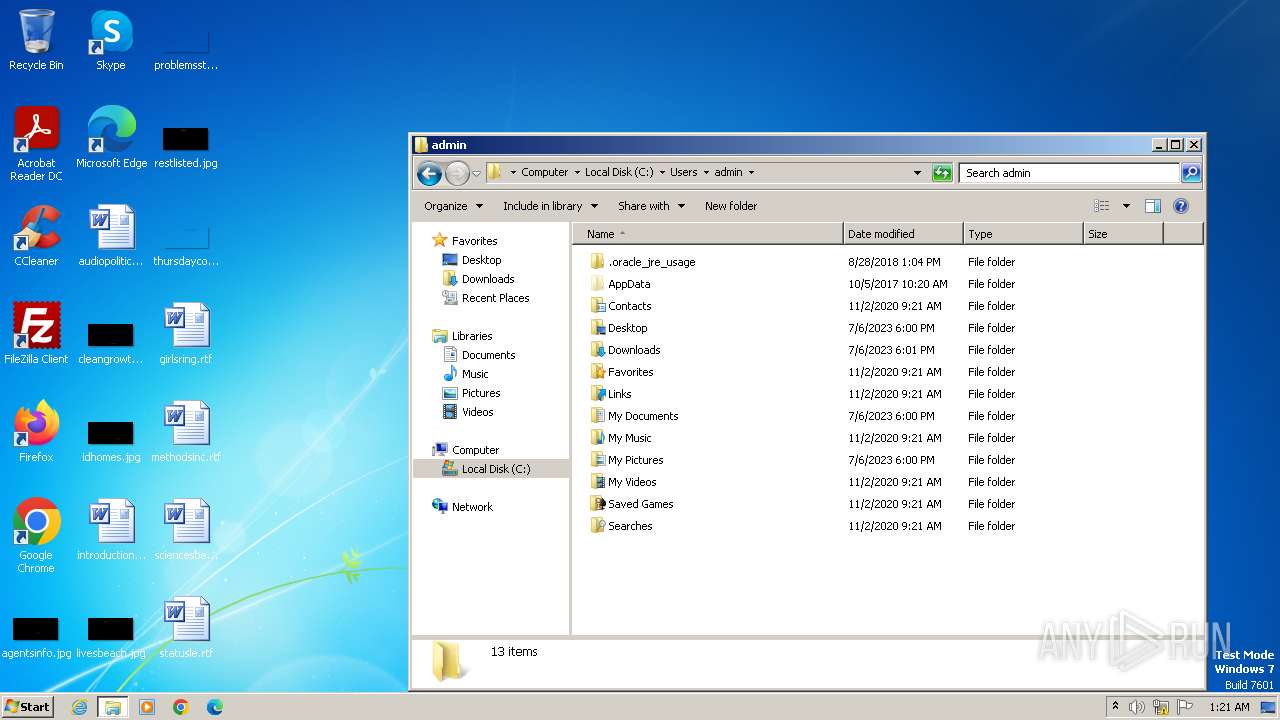
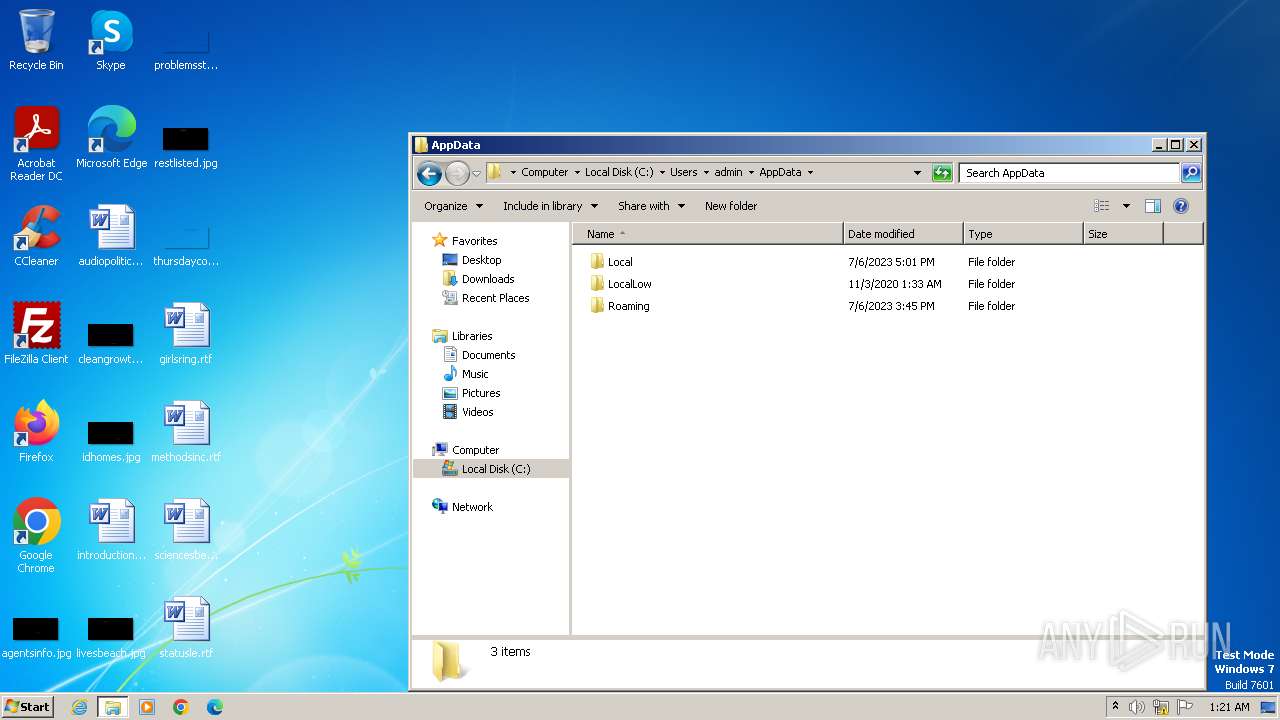
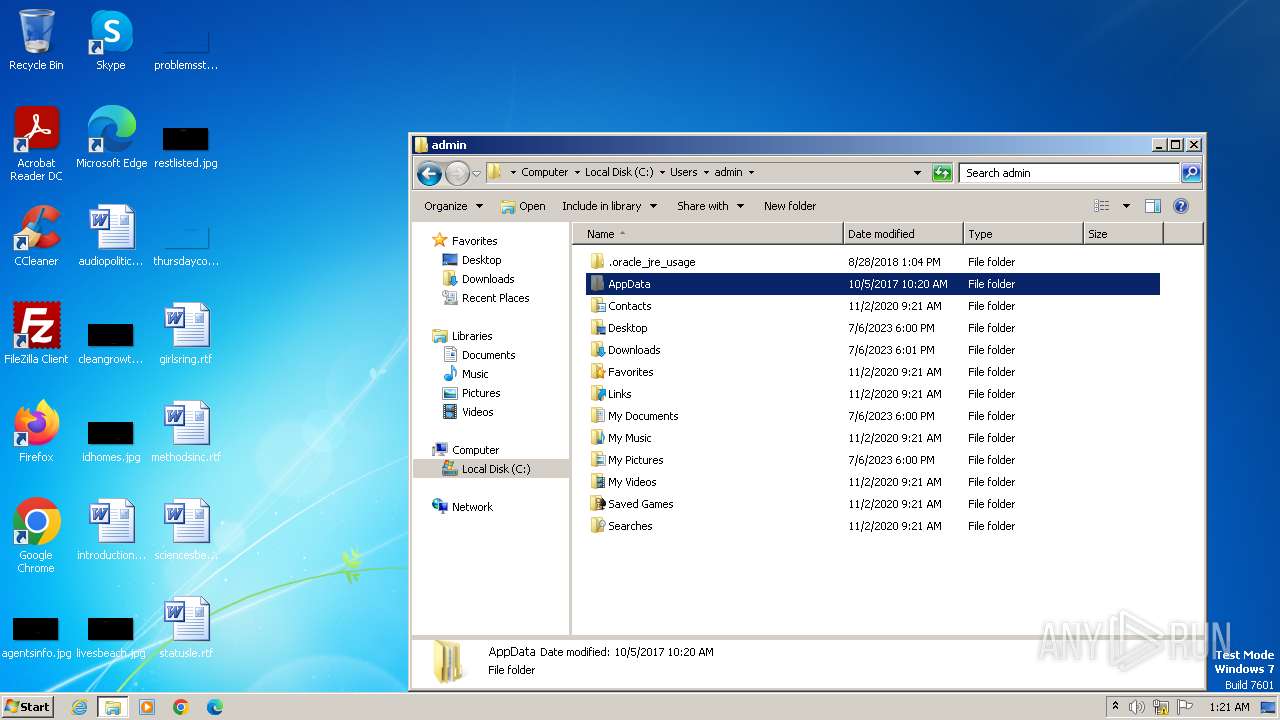
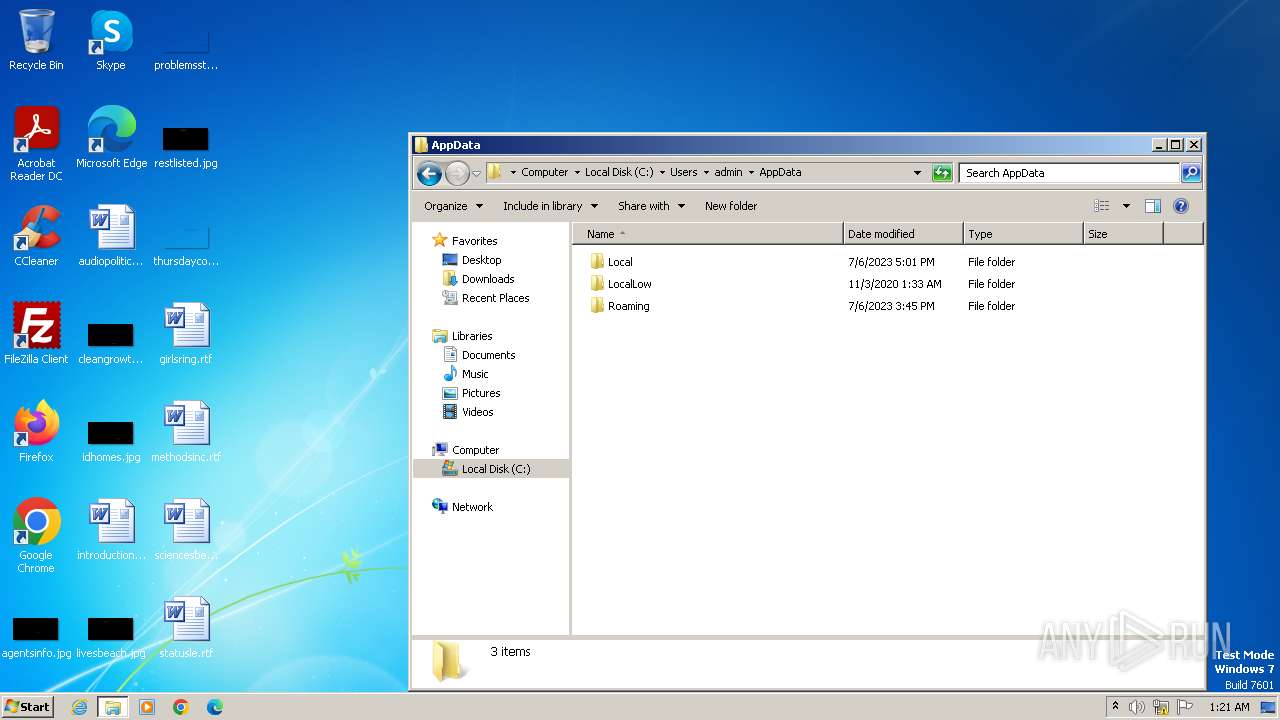
| 120 | xcopy ".\APP\source-1.3.33\App" "C:\Users\admin\AppData\Local" /s /e | C:\Windows\System32\xcopy.exe | — | cmd.exe | |||||||||||
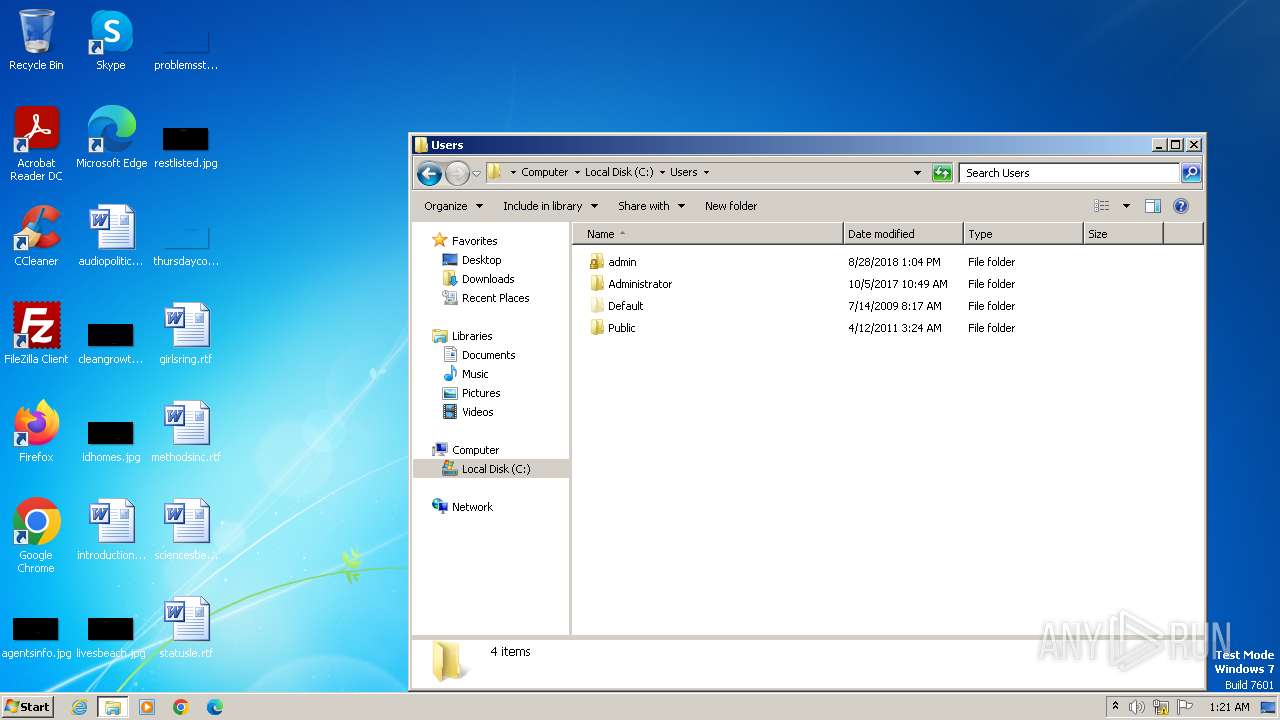
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Extended Copy Utility Exit code: 4 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 148 | "C:\Users\admin\AppData\Local\Temp\1-安装主程序(30天执行一次).exe" | C:\Users\admin\AppData\Local\Temp\1-安装主程序(30天执行一次).exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 276 | xcopy ".\APP\source\License" "C:\Users\admin" /s /e | C:\Windows\System32\xcopy.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Extended Copy Utility Exit code: 4 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 292 | xcopy ".\APP\source-1.3.33\App" "C:\Users\admin\AppData\Local" /s /e | C:\Windows\System32\xcopy.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Extended Copy Utility Exit code: 4 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 448 | xcopy "C:\Users\admin\AppData\Local\plasticity-beta\plasticity-beta.lnk" "C:\Users\admin\Desktop" /y | C:\Windows\System32\xcopy.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Extended Copy Utility Exit code: 4 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 684 | xcopy "C:\Users\admin\AppData\Local\plasticity-beta\plasticity-beta.lnk" "C:\Users\admin\Desktop" /y | C:\Windows\System32\xcopy.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Extended Copy Utility Exit code: 4 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 712 | xcopy ".\APP\source\License" "C:\Users\admin" /s /e | C:\Windows\System32\xcopy.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Extended Copy Utility Exit code: 4 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 732 | xcopy ".\APP\source\App" "C:\Users\admin\AppData\Local" /s /e | C:\Windows\System32\xcopy.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Extended Copy Utility Exit code: 4 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1432 | "C:\Windows\system32\cmd" /c "C:\Users\admin\AppData\Local\Temp\3F3B.tmp\3F3C.tmp\3F3D.bat C:\Users\admin\AppData\Local\Temp\1-安装主程序(30天执行一次).exe" | C:\Windows\System32\cmd.exe | — | 1-安装主程序(30天执行一次).exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 1592 | "C:\Users\admin\AppData\Local\Temp\1-安装主程序(30天执行一次).exe" | C:\Users\admin\AppData\Local\Temp\1-安装主程序(30天执行一次).exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
Total events
660
Read events
648
Write events
12
Delete events
0
Modification events
| (PID) Process: | (3984) notepad++.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\17A\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
Executable files
0
Suspicious files
0
Text files
10
Unknown types
0
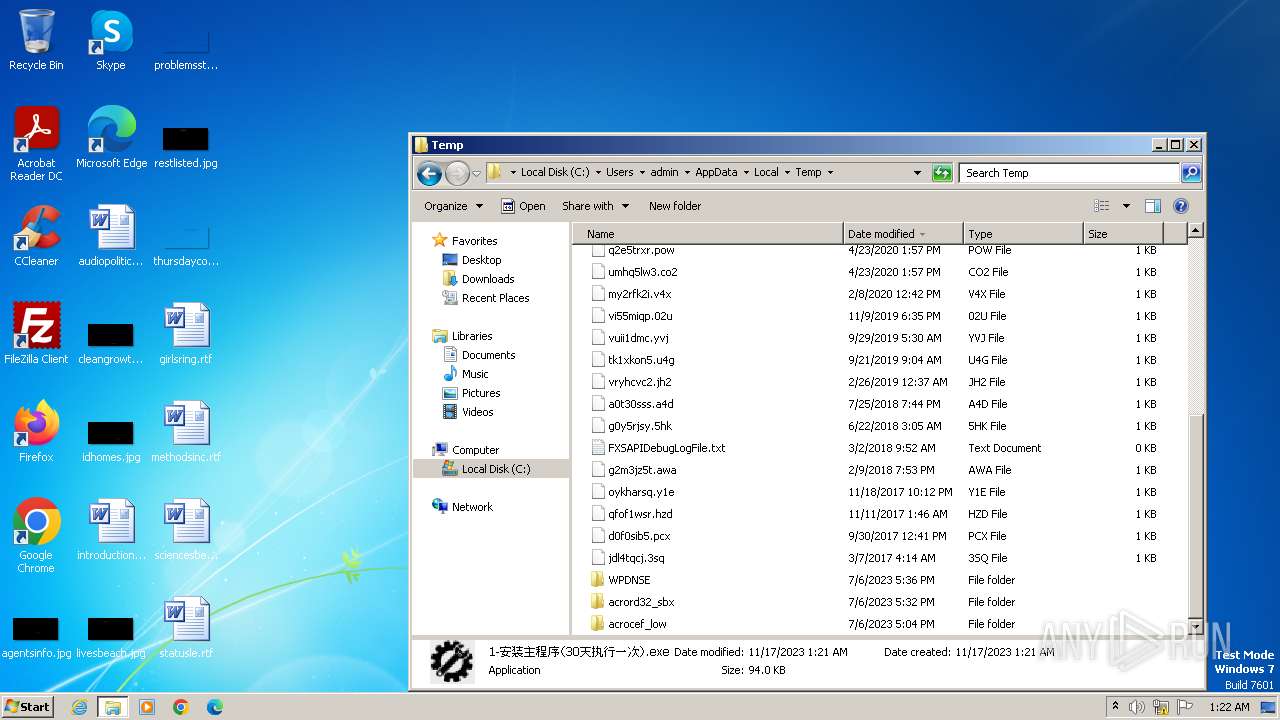
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1876 | 1-安装主程序(30天执行一次).exe | C:\Users\admin\AppData\Local\Temp\3B53.tmp\3B54.tmp\3B55.bat | text | |
MD5:39BC83A36A999B53F92FAD18EB29C973 | SHA256:10C2CF385FE3C4B132AB89231F2BD5D90C3F1B51B0E2FDBF1F382E7F35D534C1 | |||
| 3436 | 1-安装主程序(30天执行一次).exe | C:\Users\admin\AppData\Local\Temp\6F68.tmp\6F69.tmp\6F6A.bat | text | |
MD5:39BC83A36A999B53F92FAD18EB29C973 | SHA256:10C2CF385FE3C4B132AB89231F2BD5D90C3F1B51B0E2FDBF1F382E7F35D534C1 | |||
| 1592 | 1-安装主程序(30天执行一次).exe | C:\Users\admin\AppData\Local\Temp\372D.tmp\372E.tmp\372F.bat | text | |
MD5:39BC83A36A999B53F92FAD18EB29C973 | SHA256:10C2CF385FE3C4B132AB89231F2BD5D90C3F1B51B0E2FDBF1F382E7F35D534C1 | |||
| 2296 | 1-安装主程序(30天执行一次).exe | C:\Users\admin\AppData\Local\Temp\32F7.tmp\32F8.tmp\3308.bat | text | |
MD5:39BC83A36A999B53F92FAD18EB29C973 | SHA256:10C2CF385FE3C4B132AB89231F2BD5D90C3F1B51B0E2FDBF1F382E7F35D534C1 | |||
| 2432 | 1-安装主程序(30天执行一次).exe | C:\Users\admin\AppData\Local\Temp\3F3B.tmp\3F3C.tmp\3F3D.bat | text | |
MD5:39BC83A36A999B53F92FAD18EB29C973 | SHA256:10C2CF385FE3C4B132AB89231F2BD5D90C3F1B51B0E2FDBF1F382E7F35D534C1 | |||
| 148 | 1-安装主程序(30天执行一次).exe | C:\Users\admin\AppData\Local\Temp\1E65.tmp\1E66.tmp\1E67.bat | text | |
MD5:39BC83A36A999B53F92FAD18EB29C973 | SHA256:10C2CF385FE3C4B132AB89231F2BD5D90C3F1B51B0E2FDBF1F382E7F35D534C1 | |||
| 3548 | 1-安装主程序(30天执行一次).exe | C:\Users\admin\AppData\Local\Temp\849C.tmp\84AD.tmp\84AE.bat | text | |
MD5:39BC83A36A999B53F92FAD18EB29C973 | SHA256:10C2CF385FE3C4B132AB89231F2BD5D90C3F1B51B0E2FDBF1F382E7F35D534C1 | |||
| 3832 | 1-安装主程序(30天执行一次).exe | C:\Users\admin\AppData\Local\Temp\1B43.tmp\1B54.tmp\1B55.bat | text | |
MD5:39BC83A36A999B53F92FAD18EB29C973 | SHA256:10C2CF385FE3C4B132AB89231F2BD5D90C3F1B51B0E2FDBF1F382E7F35D534C1 | |||
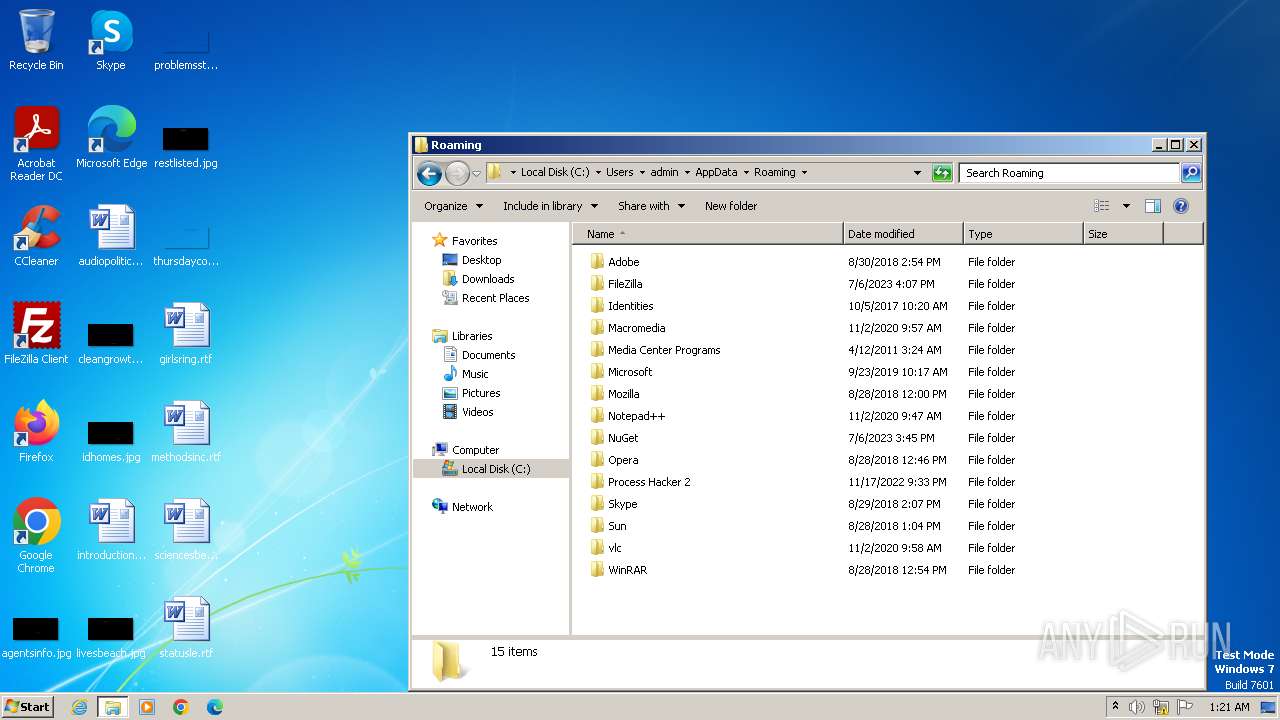
| 3984 | notepad++.exe | C:\Users\admin\AppData\Roaming\Notepad++\config.xml | xml | |
MD5:75DAF0C838CA0F9DAA89D4074A504E1B | SHA256:97901B6DEF410AA997B0E91A0FD0947EB3A26B7D5C83FD7228FDE04F981AC53C | |||
| 3984 | notepad++.exe | C:\Users\admin\AppData\Roaming\Notepad++\session.xml | text | |
MD5:84BD2D7E0E3D3FA743DA36CF49E5DFFE | SHA256:297A697A754A4EFC6214B89EF5E3F797928F7444DB45D7E692B880348F858529 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
4
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
2588 | svchost.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
1080 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |
DNS requests
Threats
Process | Message |
|---|---|
notepad++.exe | VerifyLibrary: C:\Program Files\Notepad++\SciLexer.dll
|
notepad++.exe | VerifyLibrary: certificate revocation checking is disabled
|
notepad++.exe | ED255D9151912E40DF048A56288E969A8D0DAFA3
|
notepad++.exe | VerifyLibrary: C:\Program Files\Notepad++\updater\gup.exe
|
notepad++.exe | ED255D9151912E40DF048A56288E969A8D0DAFA3
|
notepad++.exe | VerifyLibrary: certificate revocation checking is disabled
|
notepad++.exe | VerifyLibrary: certificate revocation checking is disabled
|
notepad++.exe | VerifyLibrary: C:\Program Files\Notepad++\plugins\Config\nppPluginList.dll
|
notepad++.exe | VerifyLibrary: C:\Program Files\Notepad++\updater\gup.exe
|
notepad++.exe | VerifyLibrary: certificate revocation checking is disabled
|