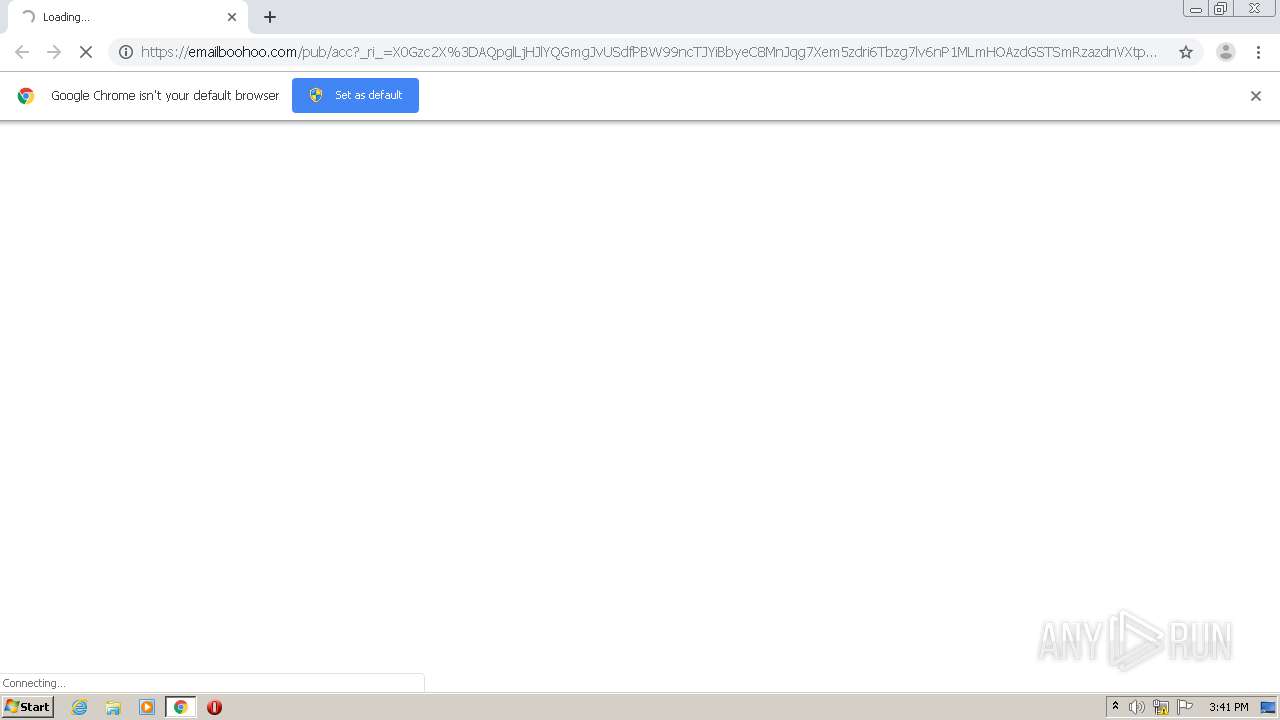
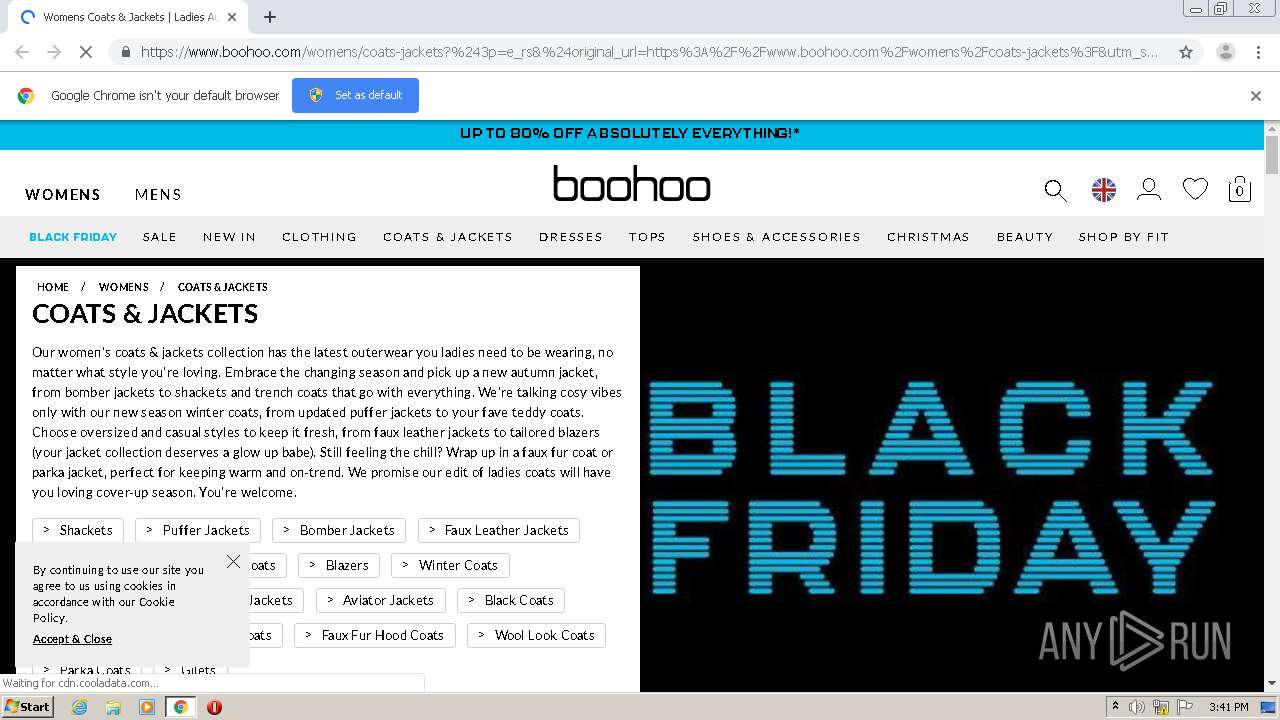
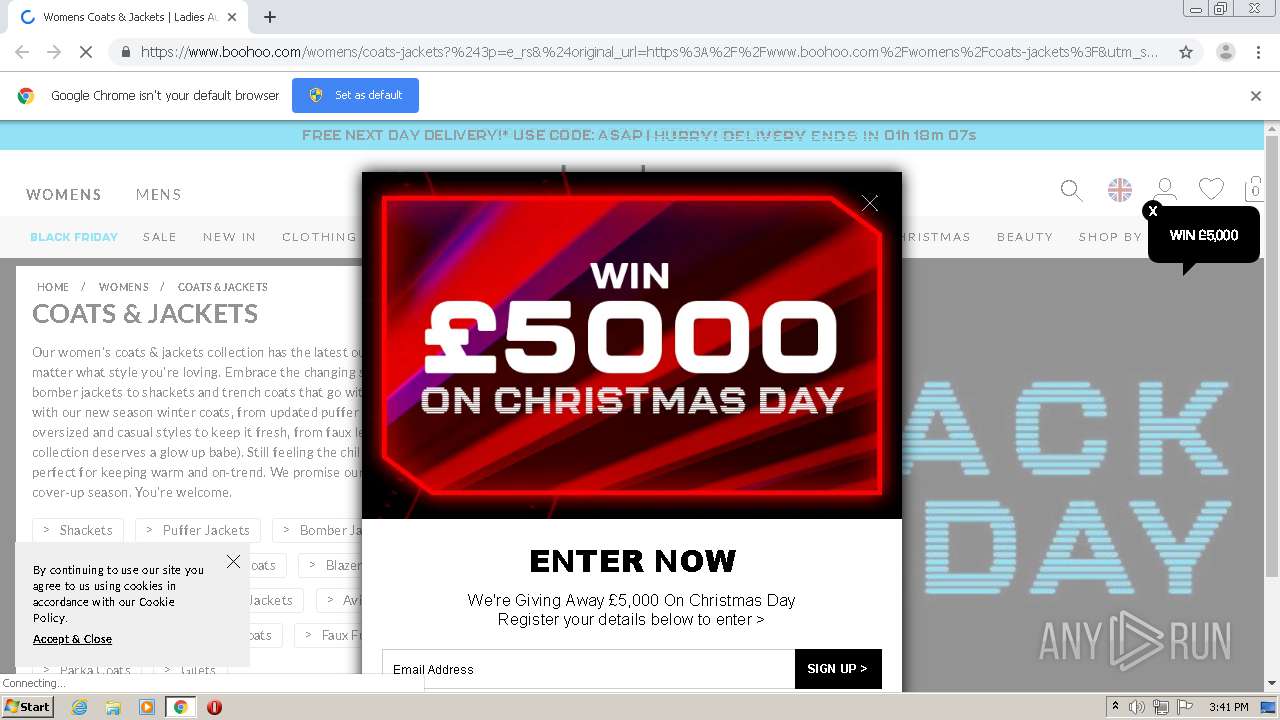
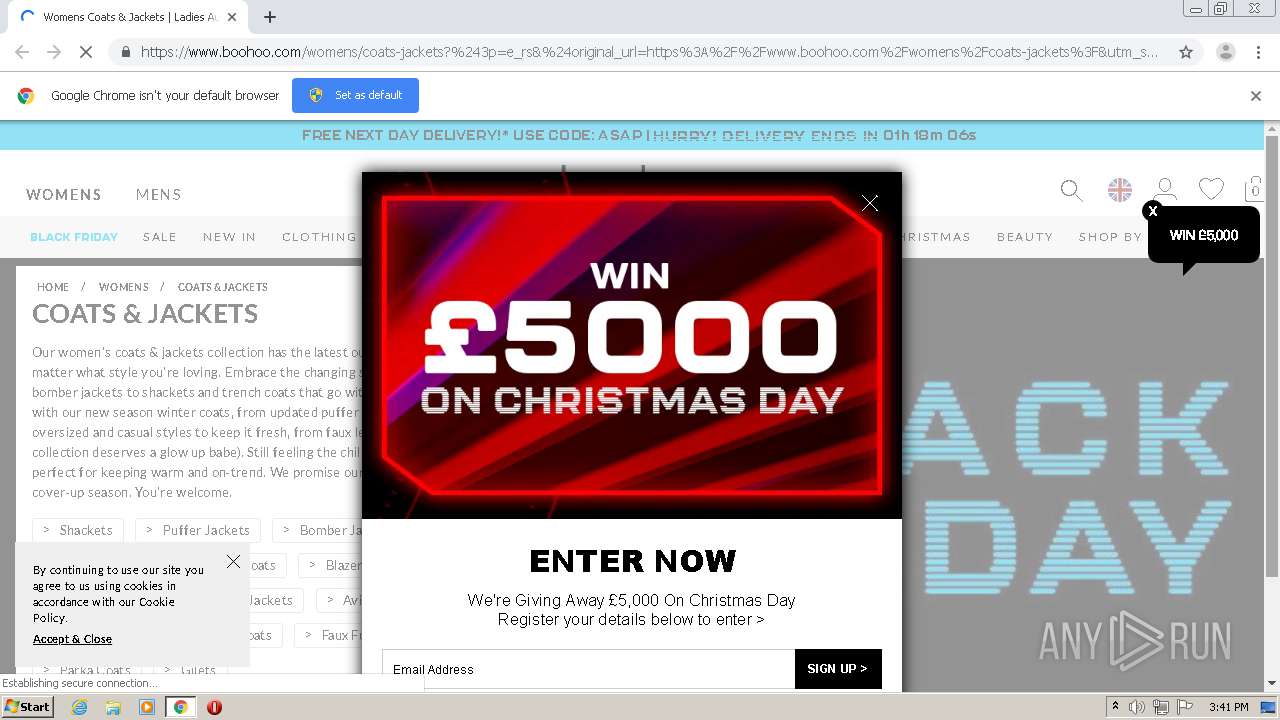
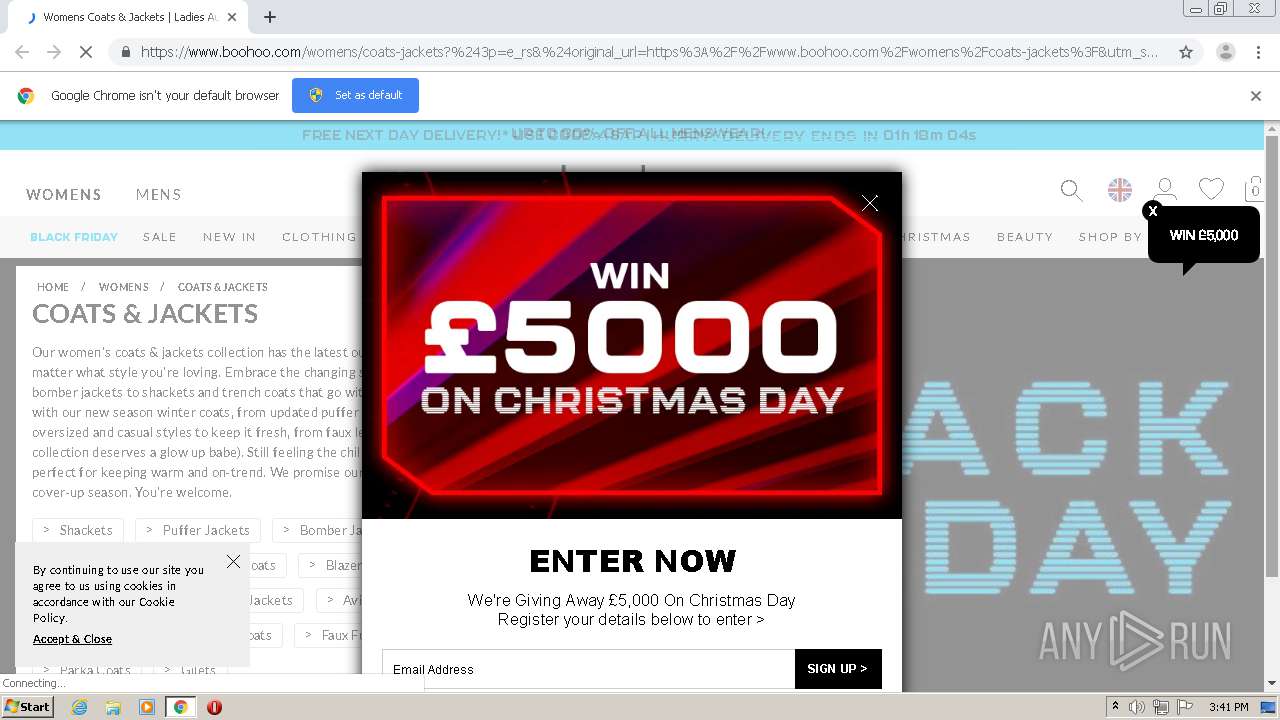
| URL: | https://emailboohoo.com/pub/acc?_ri_=X0Gzc2X%3DAQpglLjHJlYQGmgJvUSdfPBW99ncTJYiBbyeC8MnJqg7Xem5zdri6Tbzg7lv6nP1MLmHOAzdGSTSmRzazdnVXtpKX%3DYUDWUTWY&_ei_=Eq2tf9zs59idfPO1Sc_9Bbnm2qCPahUI4YtIbhkEmLft7EkgeI5crx-x0r2vRHkBfFz0oeZrz1oHgVyI6u5hHbZItFSA86dOi1zCd5vwUgH_EYMBMgjBCfEYZugcdSezG0j6PENFq2cBkadrVCxza2IFg6seBUKyxdmgTU22Wrz-vW1hFn6N98_5qDqcYaQQDUFCr6UwpahWaBbIZstG7G9dYGWhCClzt6z53zwtYzKvzbBwuX620kf9ln313R1-Emnj2PSbWwCkrg.&_di_=1kicmaldfjovg8rc2kh26v9par0htdamjm1fqn86fdfr21vtjlsgnq8aauql9ac662pbgf3f3lr2935ug |
| Full analysis: | https://app.any.run/tasks/442504e6-e72e-4206-8fbd-f5a97ab83a04 |
| Verdict: | Malicious activity |
| Analysis date: | November 29, 2020, 15:41:29 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 25DF7346512FE528974CDD5AE1C2D126 |
| SHA1: | 2875477D37F5371D14BCA9F9E57611A2957C16A7 |
| SHA256: | 7D798E4699322AC8593A660D5C9909B3750262686B8433418DFA7E1C317099C4 |
| SSDEEP: | 12:2YX/EL3vstOrzH/onmw7EfgOKsBKccV7x:2Yv2ff+ROqcW9 |
MALICIOUS
No malicious indicators.SUSPICIOUS
No suspicious indicators.INFO
Reads the hosts file
- chrome.exe (PID: 1144)
- chrome.exe (PID: 2584)
Application launched itself
- chrome.exe (PID: 2584)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
52
Monitored processes
17
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 820 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1004,13831804917766943249,11480517521767826089,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=8488574514556083429 --renderer-client-id=9 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3084 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 936 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1004,13831804917766943249,11480517521767826089,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=15183736805448435951 --renderer-client-id=14 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=4124 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1144 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1004,13831804917766943249,11480517521767826089,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=network --service-request-channel-token=2240121037905003435 --mojo-platform-channel-handle=1500 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | chrome.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1236 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1004,13831804917766943249,11480517521767826089,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=7572555694632856036 --renderer-client-id=12 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3848 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1700 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=watcher --main-thread-id=2580 --on-initialized-event-handle=316 --parent-handle=320 /prefetch:6 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1736 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1004,13831804917766943249,11480517521767826089,131072 --enable-features=PasswordImport --lang=en-US --no-sandbox --service-request-channel-token=7045197848619512867 --mojo-platform-channel-handle=3072 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1860 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1004,13831804917766943249,11480517521767826089,131072 --enable-features=PasswordImport --lang=en-US --extension-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=4021825018750905700 --renderer-client-id=4 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2448 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2328 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1004,13831804917766943249,11480517521767826089,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=16919942731249870391 --renderer-client-id=11 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3564 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2504 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1004,13831804917766943249,11480517521767826089,131072 --enable-features=PasswordImport --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=12843212087299970949 --renderer-client-id=5 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2188 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2584 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --disk-cache-dir=null --disk-cache-size=1 --media-cache-size=1 --disable-gpu-shader-disk-cache --disable-background-networking "https://emailboohoo.com/pub/acc?_ri_=X0Gzc2X%3DAQpglLjHJlYQGmgJvUSdfPBW99ncTJYiBbyeC8MnJqg7Xem5zdri6Tbzg7lv6nP1MLmHOAzdGSTSmRzazdnVXtpKX%3DYUDWUTWY&_ei_=Eq2tf9zs59idfPO1Sc_9Bbnm2qCPahUI4YtIbhkEmLft7EkgeI5crx-x0r2vRHkBfFz0oeZrz1oHgVyI6u5hHbZItFSA86dOi1zCd5vwUgH_EYMBMgjBCfEYZugcdSezG0j6PENFq2cBkadrVCxza2IFg6seBUKyxdmgTU22Wrz-vW1hFn6N98_5qDqcYaQQDUFCr6UwpahWaBbIZstG7G9dYGWhCClzt6z53zwtYzKvzbBwuX620kf9ln313R1-Emnj2PSbWwCkrg.&_di_=1kicmaldfjovg8rc2kh26v9par0htdamjm1fqn86fdfr21vtjlsgnq8aauql9ac662pbgf3f3lr2935ug" | C:\Program Files\Google\Chrome\Application\chrome.exe | explorer.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
Total events
198
Read events
158
Write events
37
Delete events
3
Modification events
| (PID) Process: | (2584) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (2584) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (2584) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (2584) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (2584) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (2584) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (2584) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (2584) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 3252-13245750958665039 |
Value: 0 | |||
| (PID) Process: | (2584) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 2584-13251138104275125 |
Value: 259 | |||
| (PID) Process: | (2584) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
Executable files
0
Suspicious files
63
Text files
52
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2584 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\BrowserMetrics\BrowserMetrics-5FC3C138-A18.pma | — | |
MD5:— | SHA256:— | |||
| 2584 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\bf9de836-9ef8-46fe-a685-2c749b3bb2d3.tmp | — | |
MD5:— | SHA256:— | |||
| 2584 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000048.dbtmp | — | |
MD5:— | SHA256:— | |||
| 2584 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Session Storage\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2584 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2584 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old~RF13fea7.TMP | text | |
MD5:— | SHA256:— | |||
| 2584 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old~RF13fe97.TMP | text | |
MD5:— | SHA256:— | |||
| 2584 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2584 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2584 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old~RF13fffe.TMP | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
74
DNS requests
57
Threats
2
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
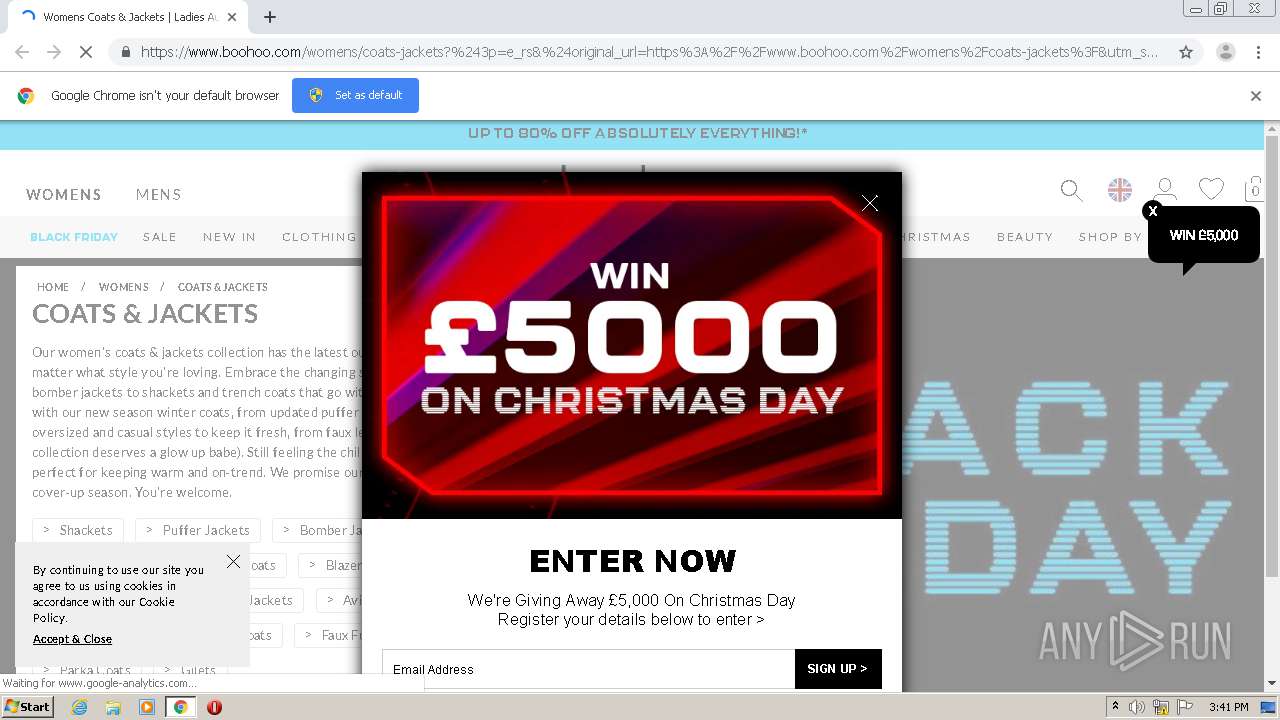
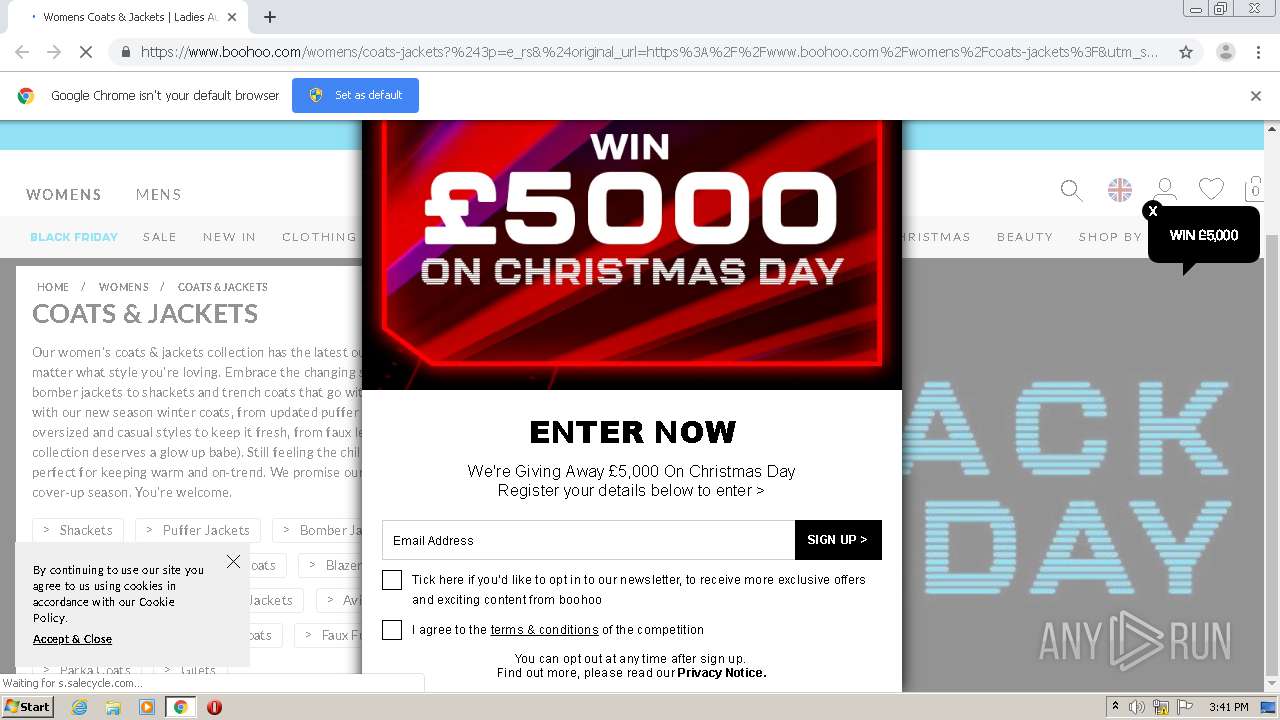
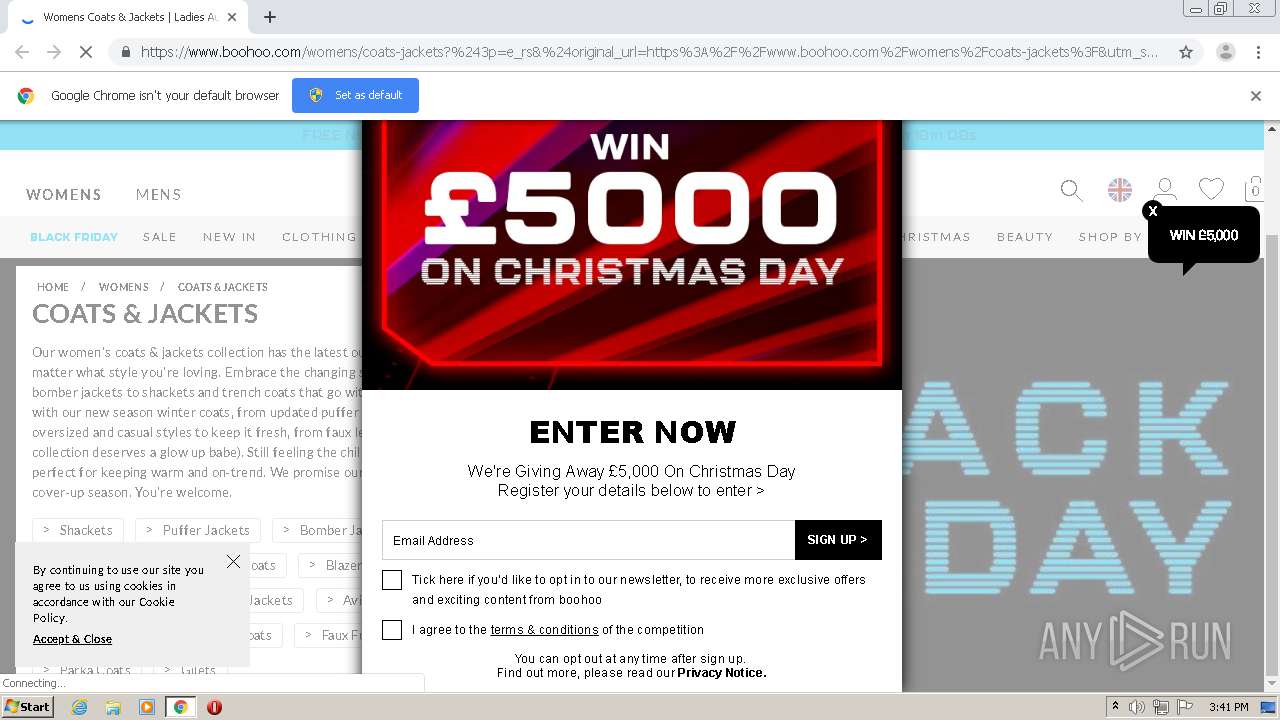
1144 | chrome.exe | 162.223.232.89:443 | emailboohoo.com | RagingWire Data Centers, Inc. | US | unknown |
1144 | chrome.exe | 172.217.22.109:443 | accounts.google.com | Google Inc. | US | whitelisted |
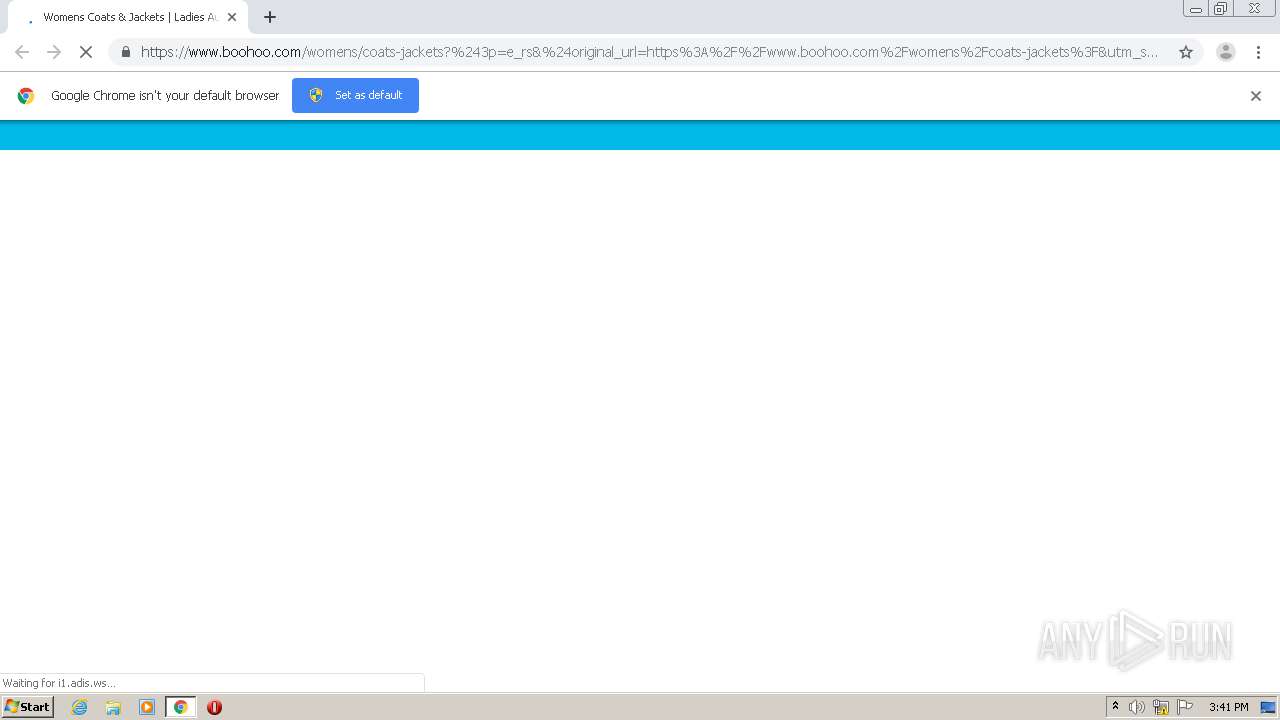
1144 | chrome.exe | 65.9.68.51:443 | boohoo.app.link | AT&T Services, Inc. | US | suspicious |
1144 | chrome.exe | 104.16.32.60:443 | www.boohoo.com | Cloudflare Inc | US | shared |
1144 | chrome.exe | 184.24.4.167:443 | se.monetate.net | Bharti Airtel Ltd., Telemedia Services | US | unknown |
1144 | chrome.exe | 199.7.200.252:443 | wrs.adrsp.net | RagingWire Data Centers, Inc. | US | unknown |
1144 | chrome.exe | 199.7.201.187:443 | custom-wrs.api.responsys.net | RagingWire Data Centers, Inc. | US | unknown |
1144 | chrome.exe | 54.91.31.243:443 | cdn0.forter.com | Amazon.com, Inc. | US | unknown |
1144 | chrome.exe | 23.46.252.132:443 | s.adroll.com | Akamai Technologies, Inc. | US | unknown |
1144 | chrome.exe | 157.240.20.35:443 | www.facebook.com | Facebook, Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
emailboohoo.com |
| unknown |
accounts.google.com |
| shared |
boohoo.app.link |
| suspicious |
www.boohoo.com |
| unknown |
se.monetate.net |
| whitelisted |
wrs.adrsp.net |
| unknown |
custom-wrs.api.responsys.net |
| unknown |
use.typekit.net |
| whitelisted |
cdn0.forter.com |
| whitelisted |
media.boohoo.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1144 | chrome.exe | Attempted User Privilege Gain | ET INFO Session Traversal Utilities for NAT (STUN Binding Request) |
1144 | chrome.exe | Attempted User Privilege Gain | ET INFO Session Traversal Utilities for NAT (STUN Binding Response) |