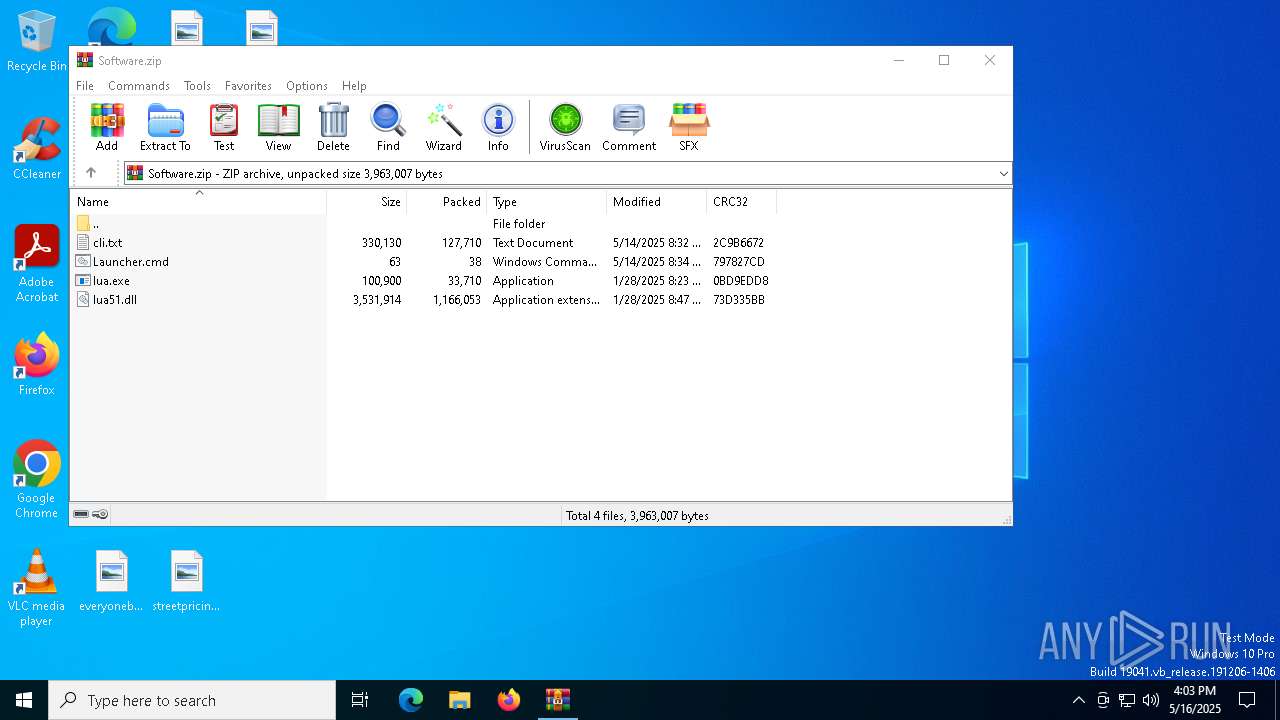
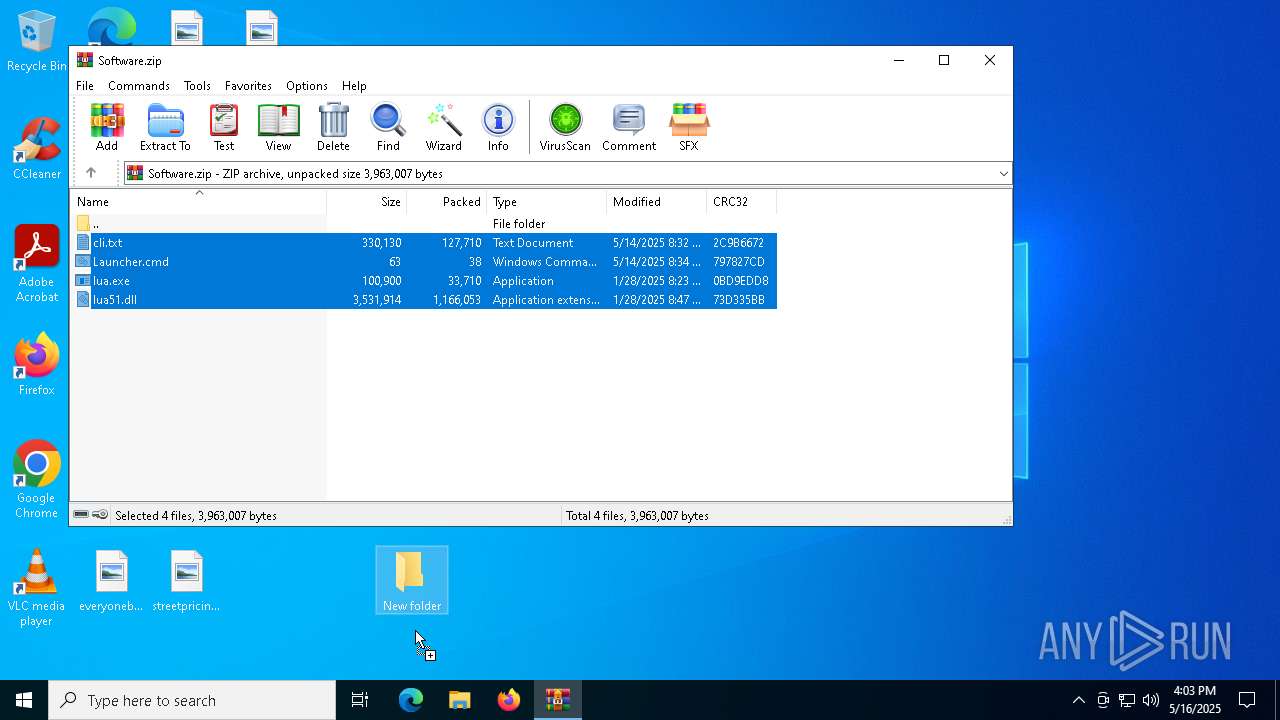
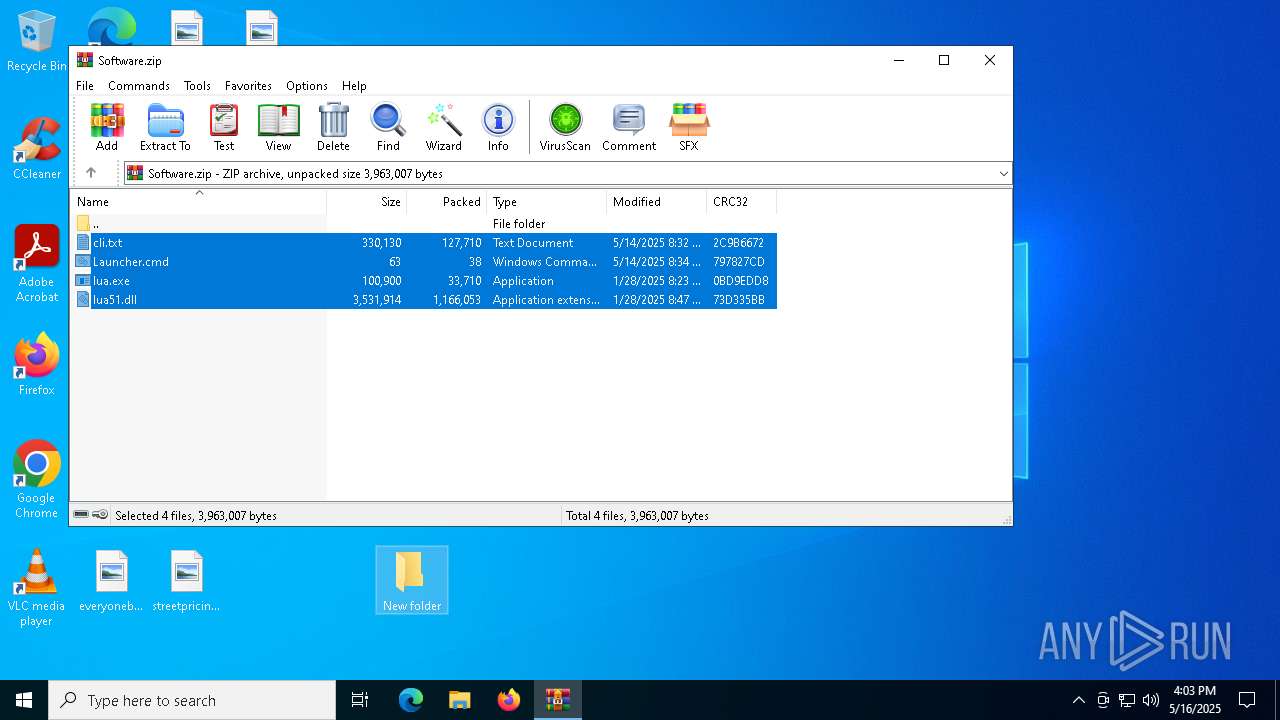
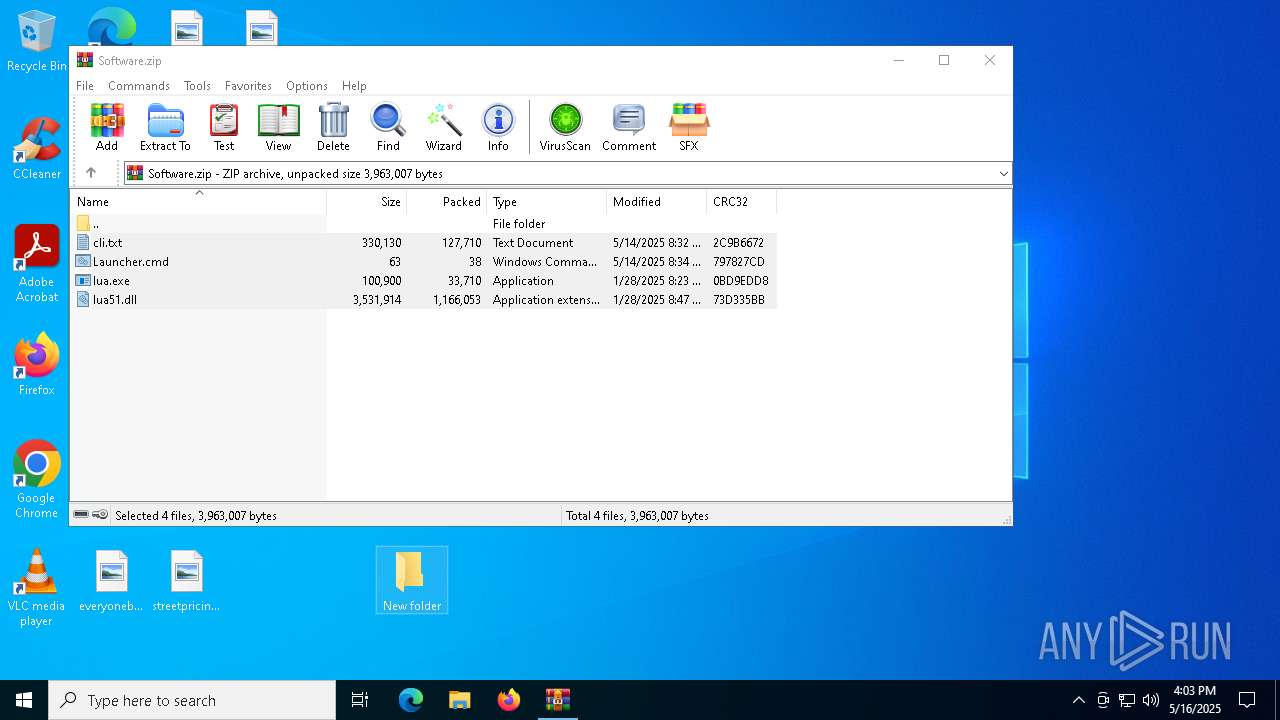
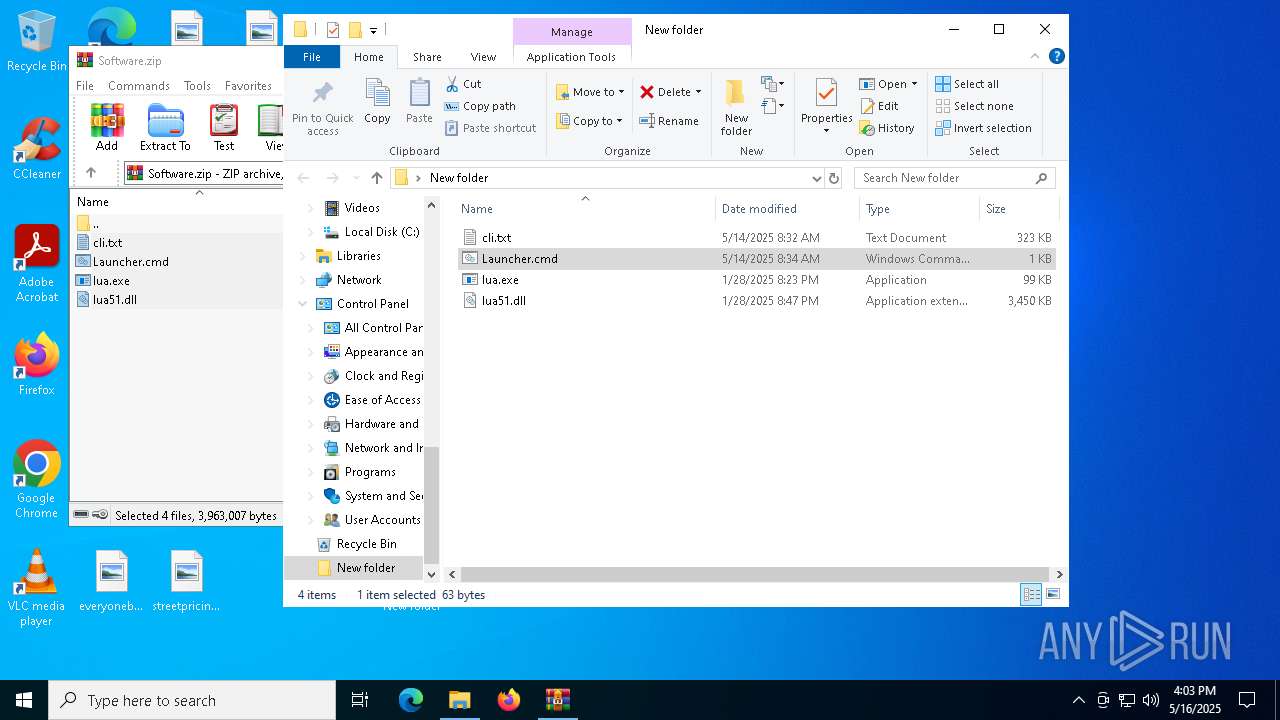
| File name: | Software.zip |
| Full analysis: | https://app.any.run/tasks/dcce2604-427c-49c7-bd5f-e771a8e8d3fa |
| Verdict: | Malicious activity |
| Analysis date: | May 16, 2025, 16:03:19 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v2.0 to extract, compression method=deflate |
| MD5: | 2178B253383176A6AA4E74E9B8532BF4 |
| SHA1: | E036C505F14534C34A0E83D978CCB38A37EE7331 |
| SHA256: | 7D6EA18EBEABAE11D20BB48160A8DE39EFB4A32869506F0D3F2E0ED62BABB27E |
| SSDEEP: | 49152:ECf2BB+czxoyEA52VHYlg+p0YepFOB+3KR5X+GafFArkvuNeNCe6Vgp7lwJrAwjF:ECO+czxoyE42VHWg+pdoABrOvArENCeG |
MALICIOUS
Generic archive extractor
- WinRAR.exe (PID: 4172)
SUSPICIOUS
Reads security settings of Internet Explorer
- lua.exe (PID: 6644)
Connects to the server without a host name
- lua.exe (PID: 6644)
Checks for external IP
- svchost.exe (PID: 2196)
- lua.exe (PID: 6644)
INFO
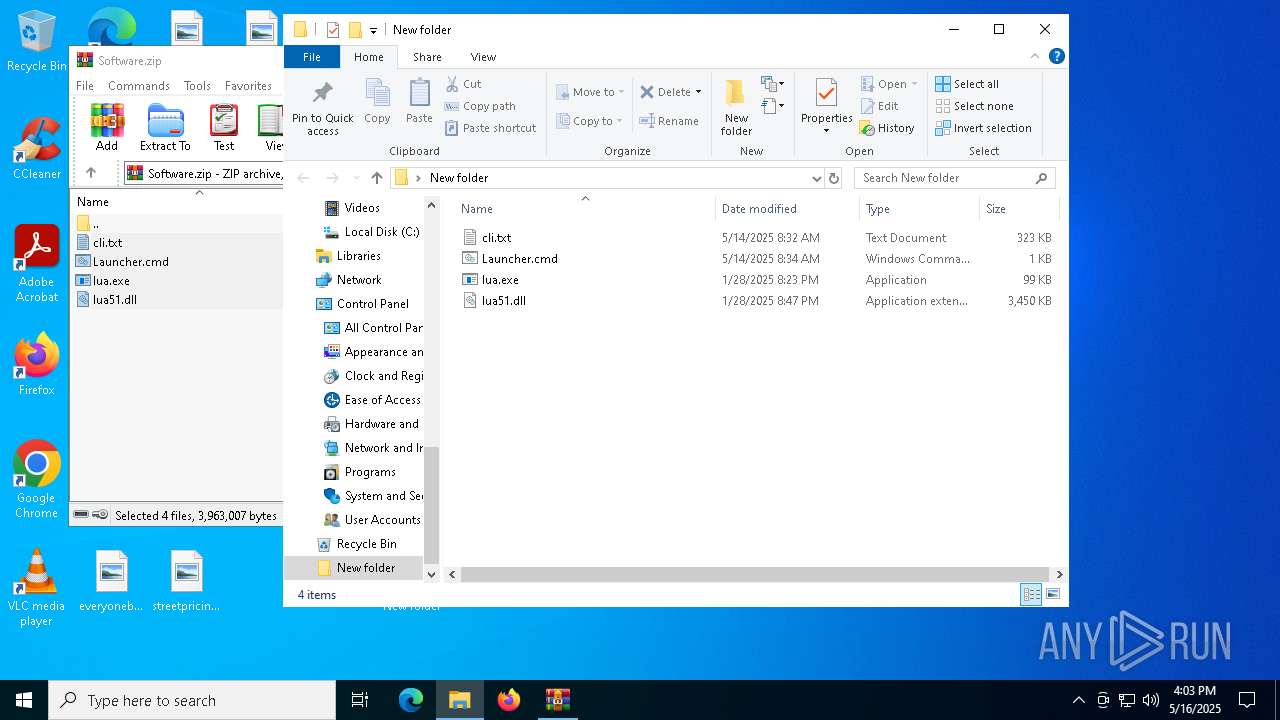
Executable content was dropped or overwritten
- WinRAR.exe (PID: 4172)
Checks proxy server information
- lua.exe (PID: 6644)
Reads the computer name
- lua.exe (PID: 6644)
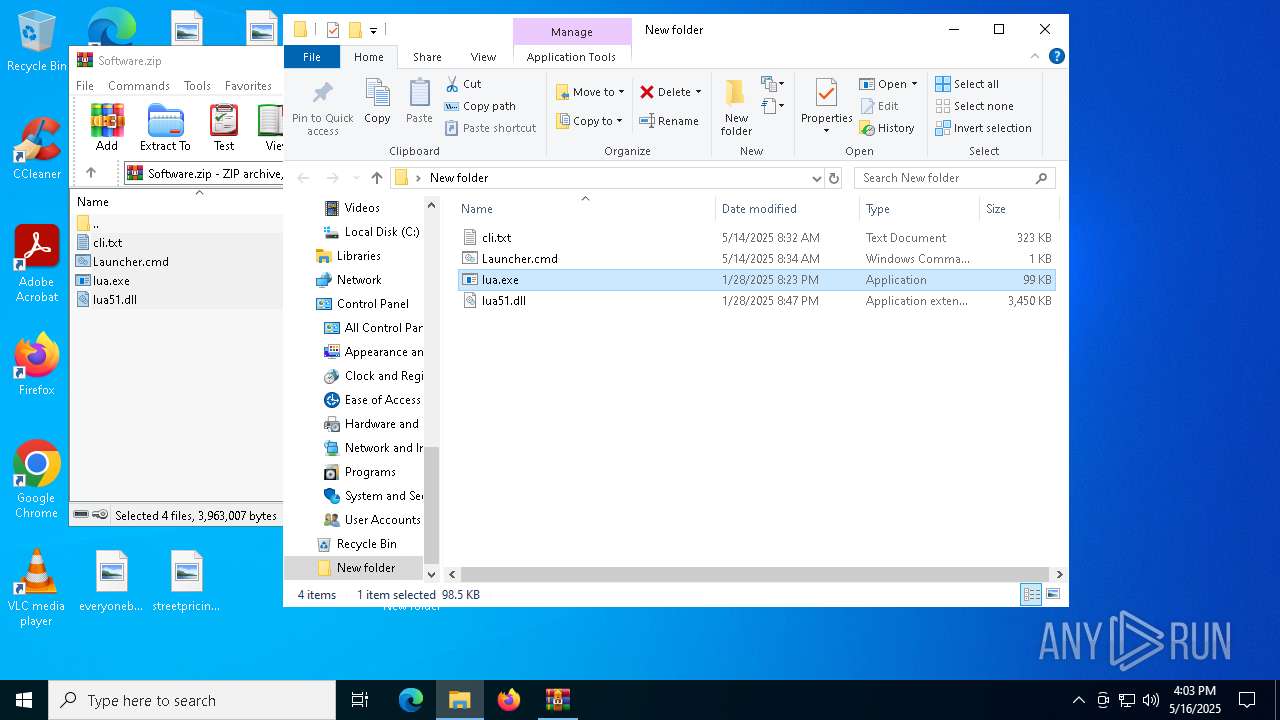
Manual execution by a user
- cmd.exe (PID: 720)
- lua.exe (PID: 3300)
Checks supported languages
- lua.exe (PID: 6644)
- lua.exe (PID: 3300)
Creates files or folders in the user directory
- lua.exe (PID: 6644)
Reads the software policy settings
- lua.exe (PID: 6644)
Reads the machine GUID from the registry
- lua.exe (PID: 6644)
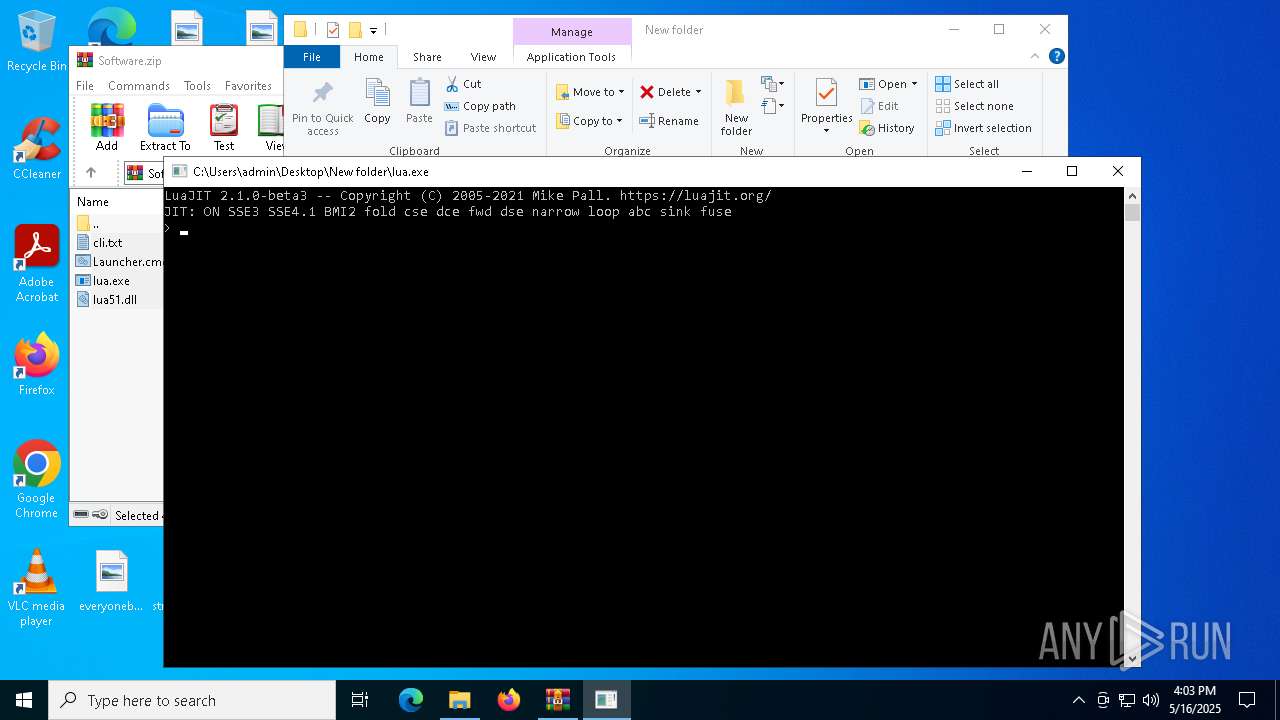
The process uses Lua
- lua.exe (PID: 6644)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 20 |
|---|---|
| ZipBitFlag: | - |
| ZipCompression: | Deflated |
| ZipModifyDate: | 2025:05:14 01:32:06 |
| ZipCRC: | 0x2c9b6672 |
| ZipCompressedSize: | 127710 |
| ZipUncompressedSize: | 330130 |
| ZipFileName: | cli.txt |
Total processes
137
Monitored processes
11
Malicious processes
0
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 720 | C:\WINDOWS\system32\cmd.exe /c ""C:\Users\admin\Desktop\New folder\Launcher.cmd" " | C:\Windows\System32\cmd.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1196 | "C:\WINDOWS\System32\SLUI.exe" RuleId=3482d82e-ca2c-4e1f-8864-da0267b484b2;Action=AutoActivate;AppId=55c92734-d682-4d71-983e-d6ec3f16059f;SkuId=4de7cb65-cdf1-4de9-8ae8-e3cce27b9f2c;NotificationInterval=1440;Trigger=TimerEvent | C:\Windows\System32\slui.exe | — | SppExtComObj.Exe | |||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows Activation Client Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2108 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | lua.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2196 | C:\WINDOWS\system32\svchost.exe -k NetworkService -p -s Dnscache | C:\Windows\System32\svchost.exe | services.exe | ||||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2600 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3300 | "C:\Users\admin\Desktop\New folder\lua.exe" | C:\Users\admin\Desktop\New folder\lua.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Modules
| |||||||||||||||
| 4172 | "C:\Program Files\WinRAR\WinRAR.exe" C:\Users\admin\AppData\Local\Temp\Software.zip | C:\Program Files\WinRAR\WinRAR.exe | explorer.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Version: 5.91.0 Modules
| |||||||||||||||
| 6032 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | lua.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6372 | C:\WINDOWS\System32\rundll32.exe C:\WINDOWS\System32\shell32.dll,SHCreateLocalServerRunDll {9aa46009-3ce0-458a-a354-715610a075e6} -Embedding | C:\Windows\System32\rundll32.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6392 | C:\WINDOWS\system32\SppExtComObj.exe -Embedding | C:\Windows\System32\SppExtComObj.Exe | — | svchost.exe | |||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: KMS Connection Broker Version: 10.0.19041.3996 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
2 800
Read events
2 789
Write events
11
Delete events
0
Modification events
| (PID) Process: | (4172) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 3 |
Value: C:\Users\admin\Desktop\preferences.zip | |||
| (PID) Process: | (4172) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\chromium_ext.zip | |||
| (PID) Process: | (4172) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\omni_23_10_2024_.zip | |||
| (PID) Process: | (4172) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\Software.zip | |||
| (PID) Process: | (4172) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (4172) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (4172) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (4172) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (6644) lua.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (6644) lua.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
Executable files
2
Suspicious files
9
Text files
2
Unknown types
0
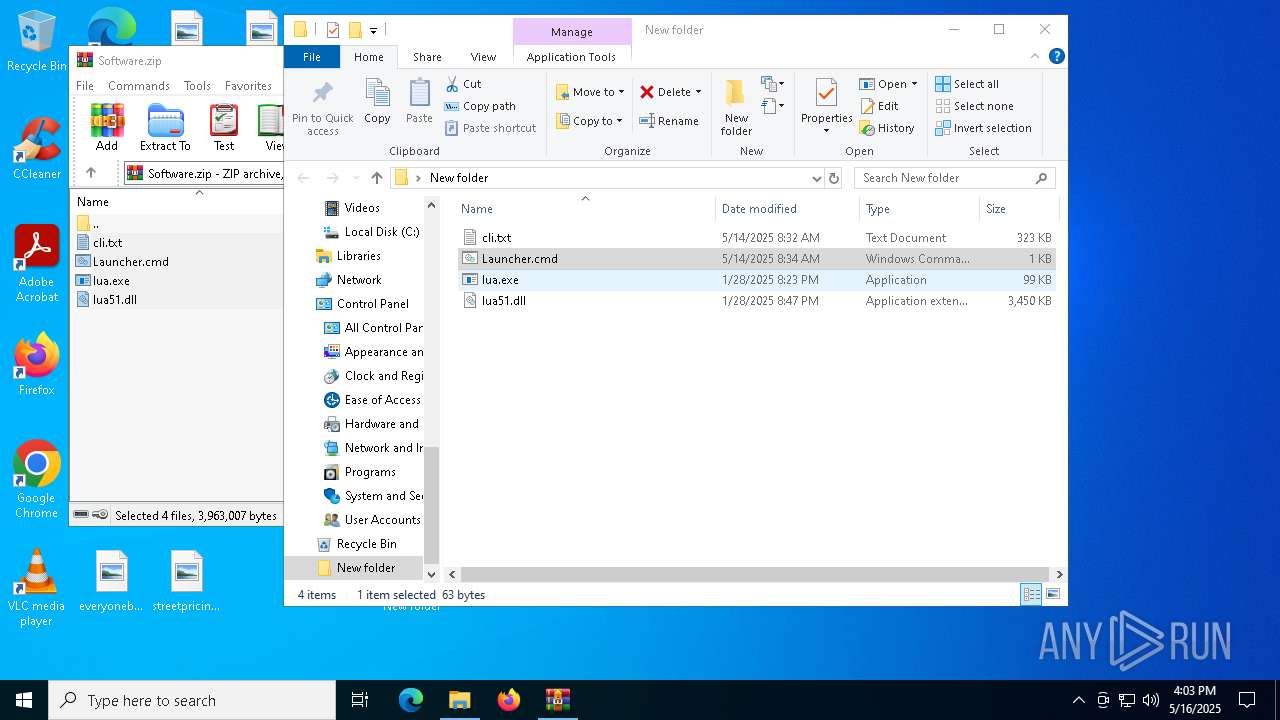
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 4172 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa4172.22773\cli.txt | text | |
MD5:AD688C76AB7B86366B67F985FBBF88E4 | SHA256:43F124233E015E96FF1DEE097B89226E0A1357ED51DEC95DB71899F48DC48ADC | |||
| 4172 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa4172.22773\Launcher.cmd | text | |
MD5:0E4D6BFDB031DEE34F25A104F280C7B6 | SHA256:3A02136C101A0AF9851DEA1DDD04B0C880801D0CA041DE8AA15A6E6B1669B02C | |||
| 4172 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa4172.22773\lua51.dll | executable | |
MD5:4EBD617A3AD9A9619172BD14A902A400 | SHA256:C7A657AF5455812FB215A8888B7E3FD8FA1BA27672A3ED9021EB6004EFF271AC | |||
| 6644 | lua.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\24BD96D5497F70B3F510A6B53CD43F3E_3A89246FB90C5EE6620004F1AE0EB0EA | binary | |
MD5:DCCD7A683348F31985E12625D4A41A0D | SHA256:1C3B0B067A4311D8C3719E1AF5A7C9B33FE6C0457BB11A2AD54C0AB474088F07 | |||
| 4172 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa4172.22773\lua.exe | executable | |
MD5:00F60EE3FF2DEE681B5D7D442009B2C2 | SHA256:5343326FB0B4F79C32276F08FFCC36BD88CDE23AA19962BD1E8D8B80F5D33953 | |||
| 6644 | lua.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\05DDC6AA91765AACACDB0A5F96DF8199 | binary | |
MD5:C22301B5245B697AA0D960E7D3A2D560 | SHA256:8E63BB9D833DDFF90DB225799A6B20821540B2A10AB3764EE07767259765DA0E | |||
| 6644 | lua.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\INetCache\IE\RR3E01RZ\json[1].json | binary | |
MD5:6ACC732B2F640EABFA496AF3EE78A396 | SHA256:016D60A62FC5CB276532855A40DF15EA98E909D1B284C4EB0BDBA594CFE47551 | |||
| 6644 | lua.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\24BD96D5497F70B3F510A6B53CD43F3E_3A89246FB90C5EE6620004F1AE0EB0EA | binary | |
MD5:03A2A723B0946489A8F22ADF9AE51CCB | SHA256:F0A498DB0442200F27692A3904C4CFE6DE3243B872C5826101A1F3AC4E8D8BD3 | |||
| 6644 | lua.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\705B0777CCF2F18A185AAE301FA49062_954F3E08FAABC801B947ABA07C5160D0 | binary | |
MD5:EBEE8490EE346B8F210B3C4FF3D84B4A | SHA256:2B005575F2CCAA903BF1273AE3CEDD809DF83C15F94CACCB041794939B6BDF65 | |||
| 6644 | lua.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\705B0777CCF2F18A185AAE301FA49062_954F3E08FAABC801B947ABA07C5160D0 | binary | |
MD5:2F3CAAF4E6201DCBE850828281EEF643 | SHA256:2EBD5798D227E06AB7648E2DC0CA2A6FEC6D4CC3BCC9509870EBE88CE2AD53FF | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
11
TCP/UDP connections
28
DNS requests
18
Threats
3
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
5304 | SIHClient.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
6644 | lua.exe | POST | 200 | 91.196.32.114:80 | http://91.196.32.114/api/YTAsODYsODIsOWQsYTEsODgsOTAsOTUsNjUsN2Qs | unknown | — | — | unknown |
5304 | SIHClient.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 2.16.168.124:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
6644 | lua.exe | GET | 200 | 142.250.185.99:80 | http://ocsp.pki.goog/gsr1/MFEwTzBNMEswSTAJBgUrDgMCGgUABBS3V7W2nAf4FiMTjpDJKg6%2BMgGqMQQUYHtmGkUNl8qJUC99BM00qP%2F8%2FUsCEHe9DWzbNvka6iEPxPBY0w0%3D | unknown | — | — | whitelisted |
6544 | svchost.exe | GET | 200 | 2.23.77.188:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
— | — | GET | 200 | 23.219.150.101:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
6644 | lua.exe | GET | 200 | 172.217.16.195:80 | http://c.pki.goog/r/r1.crl | unknown | — | — | whitelisted |
6644 | lua.exe | GET | 200 | 2.23.77.188:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | unknown | — | — | whitelisted |
6644 | lua.exe | GET | 200 | 172.217.16.195:80 | http://o.pki.goog/s/wr1/zy8/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBQwHTUyHgfAxFi3r4z8dPC7p%2BvIYAQUZmlJ1N4qnJEDz4kOJLgOMANuiC4CEQDPL8pm0Nh6CRH27hXEzSCh | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 4.231.128.59:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 2.16.168.124:80 | crl.microsoft.com | Akamai International B.V. | RU | whitelisted |
— | — | 23.219.150.101:80 | www.microsoft.com | AKAMAI-AS | CL | whitelisted |
2104 | svchost.exe | 4.231.128.59:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
5496 | MoUsoCoreWorker.exe | 4.231.128.59:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
3216 | svchost.exe | 172.211.123.249:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | FR | whitelisted |
6544 | svchost.exe | 40.126.32.68:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
6544 | svchost.exe | 2.23.77.188:80 | ocsp.digicert.com | AKAMAI-AS | DE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
settings-win.data.microsoft.com |
| whitelisted |
ip-api.com |
| whitelisted |
polygon-rpc.com |
| unknown |
ocsp.pki.goog |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2196 | svchost.exe | Device Retrieving External IP Address Detected | INFO [ANY.RUN] External IP Check (ip-api .com) |
6644 | lua.exe | Device Retrieving External IP Address Detected | ET INFO External IP Lookup ip-api.com |
2196 | svchost.exe | Device Retrieving External IP Address Detected | ET INFO External IP Lookup Domain in DNS Lookup (ip-api .com) |