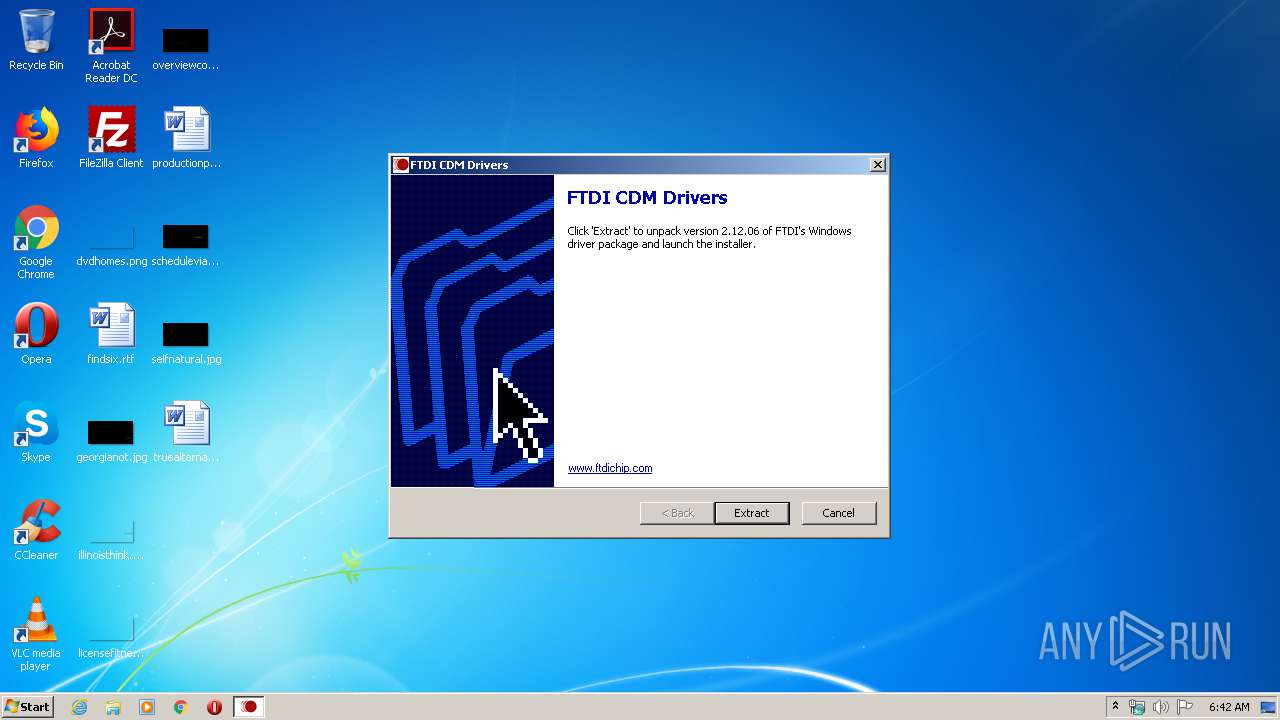
| File name: | CDM v2.12.06 WHQL Certified.exe |
| Full analysis: | https://app.any.run/tasks/3336a2fb-6018-441c-9319-4ff4d884b408 |
| Verdict: | No threats detected |
| Analysis date: | February 05, 2020, 06:42:01 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, UPX compressed |
| MD5: | E0DBE354D8A6CDDE8C1D7E5366D90E43 |
| SHA1: | 8E052A3BF930737FA8E9EE1B6DE1406380474DEB |
| SHA256: | 7D69618B17C6F56C53B539225EB88F715A693E809B7DBB86F35B817FD988DC00 |
| SSDEEP: | 49152:8l1lBmGrRBlkFSeii0Mt9Ic96SXF4EiNNn9xtJB4E58RhyaDmZi:ol1vlPyiM4EiHnDt74E58yaDui |
MALICIOUS
Application was dropped or rewritten from another process
- dpinst-x86.exe (PID: 3456)
- dp-chooser.exe (PID: 3264)
SUSPICIOUS
Executable content was dropped or overwritten
- CDM v2.12.06 WHQL Certified.exe (PID: 3772)
INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | UPX compressed Win32 Executable (39.3) |
|---|---|---|
| .exe | | | Win32 EXE Yoda's Crypter (38.6) |
| .dll | | | Win32 Dynamic Link Library (generic) (9.5) |
| .exe | | | Win32 Executable (generic) (6.5) |
| .exe | | | Generic Win/DOS Executable (2.9) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2001:03:20 07:35:57+01:00 |
| PEType: | PE32 |
| LinkerVersion: | 6 |
| CodeSize: | 24576 |
| InitializedDataSize: | 4096 |
| UninitializedDataSize: | 77824 |
| EntryPoint: | 0x19200 |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 20-Mar-2001 06:35:57 |
| Detected languages: |
|
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x000000E0 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 3 |
| Time date stamp: | 20-Mar-2001 06:35:57 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
UPX0 | 0x00001000 | 0x00013000 | 0x00000000 | IMAGE_SCN_CNT_UNINITIALIZED_DATA, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
UPX1 | 0x00014000 | 0x00006000 | 0x00005400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 7.8552 |
.rsrc | 0x0001A000 | 0x00001000 | 0x00000E00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.69797 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 7.20474 | 308 | UNKNOWN | English - United States | RT_CURSOR |
2 | 5.41113 | 2216 | UNKNOWN | English - United States | RT_ICON |
101 | 1.9815 | 20 | UNKNOWN | English - United States | RT_GROUP_ICON |
102 | 7.40615 | 386 | UNKNOWN | English - United States | RT_DIALOG |
103 | 7.98259 | 26286 | UNKNOWN | English - United States | RT_BITMAP |
104 | 6.7639 | 160 | UNKNOWN | English - United States | RT_DIALOG |
105 | 7.5182 | 476 | UNKNOWN | English - United States | RT_DIALOG |
106 | 7.30898 | 298 | UNKNOWN | English - United States | RT_DIALOG |
113 | 4.8125 | 32 | UNKNOWN | English - United States | RT_MENU |
123 | 4.22193 | 20 | UNKNOWN | English - United States | RT_GROUP_CURSOR |
Imports
ADVAPI32.dll |
GDI32.dll |
KERNEL32.DLL |
SHELL32.dll |
USER32.dll |
ole32.dll |
Total processes
36
Monitored processes
3
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
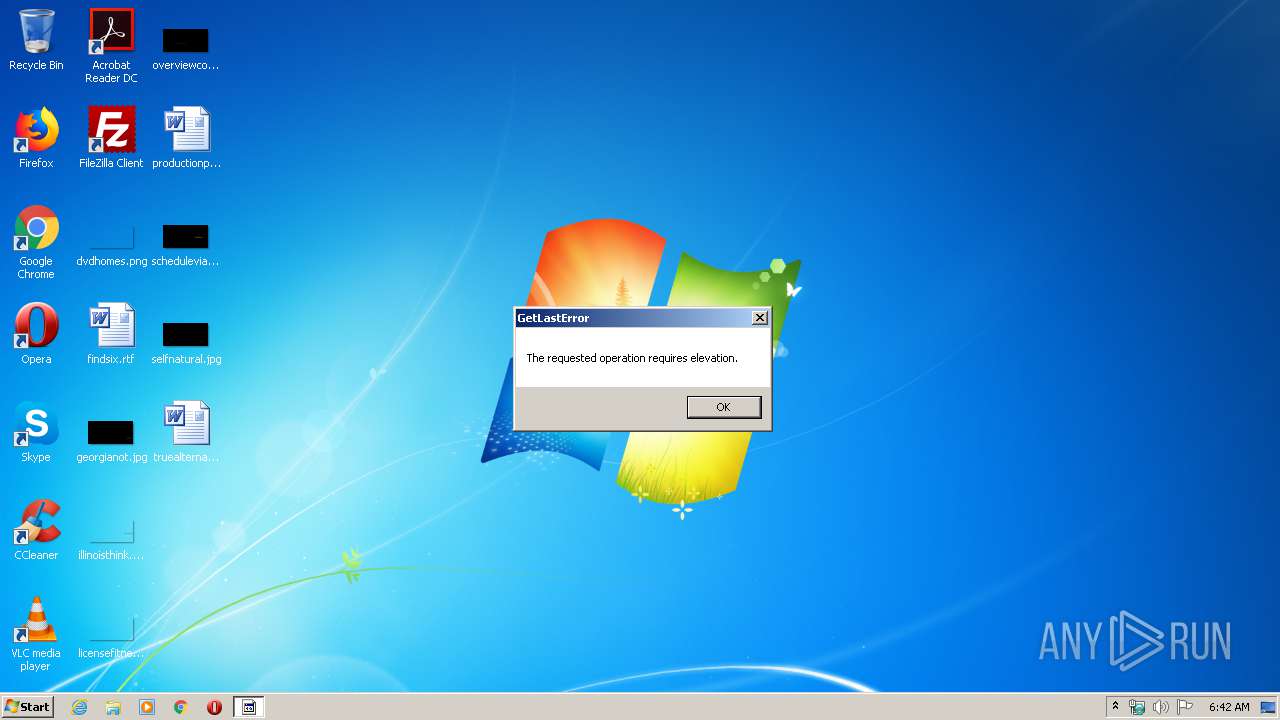
| 3264 | C:\Users\admin\AppData\Local\Temp\FTDI-Driver\dp-chooser.exe | C:\Users\admin\AppData\Local\Temp\FTDI-Driver\dp-chooser.exe | — | CDM v2.12.06 WHQL Certified.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 1 Modules
| |||||||||||||||
| 3456 | C:\Users\admin\AppData\Local\Temp\FTDI-Driver\dpinst-x86.exe /sa | C:\Users\admin\AppData\Local\Temp\FTDI-Driver\dpinst-x86.exe | — | dp-chooser.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Driver Package Installer Exit code: 3221226540 Version: 2.1 Modules
| |||||||||||||||
| 3772 | "C:\Users\admin\AppData\Local\Temp\CDM v2.12.06 WHQL Certified.exe" | C:\Users\admin\AppData\Local\Temp\CDM v2.12.06 WHQL Certified.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 1 Modules
| |||||||||||||||
Total events
0
Read events
0
Write events
0
Delete events
0
Modification events
Executable files
17
Suspicious files
0
Text files
5
Unknown types
6
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3772 | CDM v2.12.06 WHQL Certified.exe | C:\Users\admin\AppData\Local\Temp\FE5F00.tmp | — | |
MD5:— | SHA256:— | |||
| 3772 | CDM v2.12.06 WHQL Certified.exe | C:\Users\admin\AppData\Local\Temp\FTDI-Driver\amd64\ftdibus.sys | executable | |
MD5:A826F9AEEB66F61E3BE813E5E03402A5 | SHA256:DDAAA5F92B8A66A37D9DD3C1AB27292B374663E92105E7D5DC65C0CC29046603 | |||
| 3772 | CDM v2.12.06 WHQL Certified.exe | C:\Users\admin\AppData\Local\Temp\FTDI-Driver\amd64\ftd2xx.lib | obj | |
MD5:3AB9529D9F7C5BF74151B77C92566F91 | SHA256:42D6578B3E5A6B0E4F2ABC98A85A7A1196D96E2C2F6970DEF8AAD249B226040B | |||
| 3772 | CDM v2.12.06 WHQL Certified.exe | C:\Users\admin\AppData\Local\Temp\FTDI-Driver\amd64\ftcserco.dll | executable | |
MD5:5E5094779004A37853EFD508641B6580 | SHA256:45938A9ABBBCC0F2A2D02102DEE2B4EAAD8506B77392F03C9D79CB077828DFCC | |||
| 3772 | CDM v2.12.06 WHQL Certified.exe | C:\Users\admin\AppData\Local\Temp\FTDI-Driver\amd64\ftd2xx64.dll | executable | |
MD5:CCAB91D8A9D470EE989863D9500CE219 | SHA256:D7D5AC47DD0B5D20DC389FBA2608CCD17F37CC08A075555A52AB1FA338A56827 | |||
| 3772 | CDM v2.12.06 WHQL Certified.exe | C:\Users\admin\AppData\Local\Temp\FTDI-Driver\amd64\ftserui2.dll | executable | |
MD5:4F3725428FD109FB94049A263D4A0DE9 | SHA256:DB56C054FB887299E67329ED89C9B778A15BA04CBAEA5666DB4852FB7CE7B549 | |||
| 3772 | CDM v2.12.06 WHQL Certified.exe | C:\Users\admin\AppData\Local\Temp\FTDI-Driver\amd64\ftlang.dll | executable | |
MD5:B98F9CA1232FC048321833D8A8A61671 | SHA256:411C8B4733AC0E6AB81FA27A6323233B7982FDC545B1BB747A94BABD09D5F3B5 | |||
| 3772 | CDM v2.12.06 WHQL Certified.exe | C:\Users\admin\AppData\Local\Temp\FTDI-Driver\amd64\ftser2k.sys | executable | |
MD5:7782755AA5537A5A1F8F13E5E04FD412 | SHA256:7DC9D2B2B543F31F3DDE5A3DEEE25E6B50B38AAAA2117F31BAEEA2AE4D8F0167 | |||
| 3772 | CDM v2.12.06 WHQL Certified.exe | C:\Users\admin\AppData\Local\Temp\FTDI-Driver\dpinst-amd64.exe | executable | |
MD5:051CFC801AEBF138613E2AAC61DD4321 | SHA256:D770482F49E8825F9339DDE01E98BA8085A901D1F56137015BFC159191F43BA3 | |||
| 3772 | CDM v2.12.06 WHQL Certified.exe | C:\Users\admin\AppData\Local\Temp\FTDI-Driver\dp-chooser.exe | executable | |
MD5:568FA9CEA0DA23109ED133086B3F67A1 | SHA256:5C50345FDB03BD663D7BE916327BEEE8FBC91999FE38D482C79B34A4D46F855D | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report