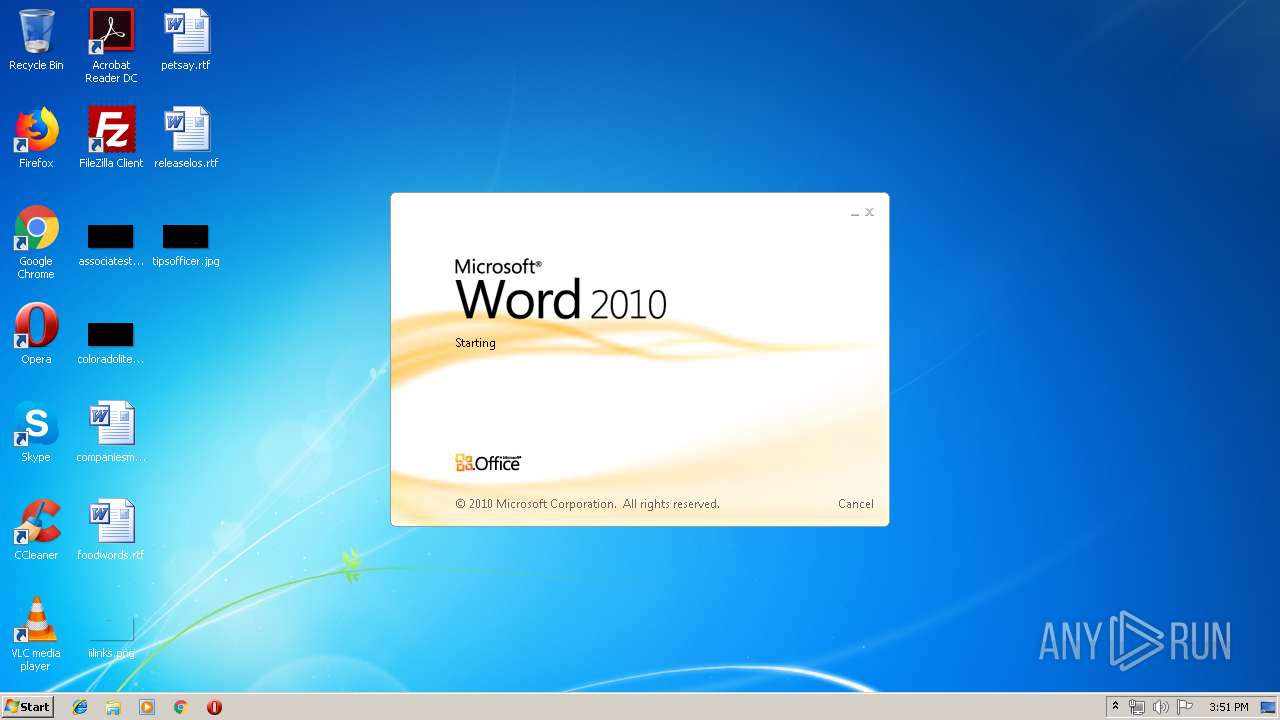
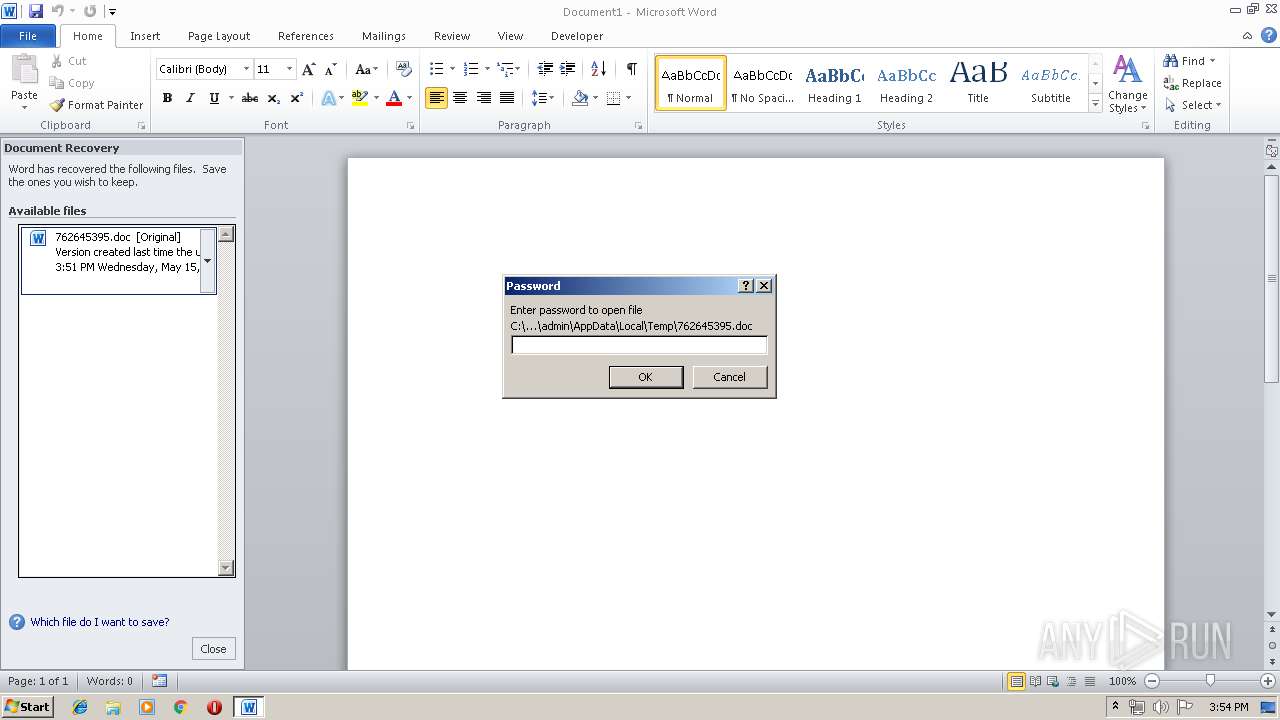
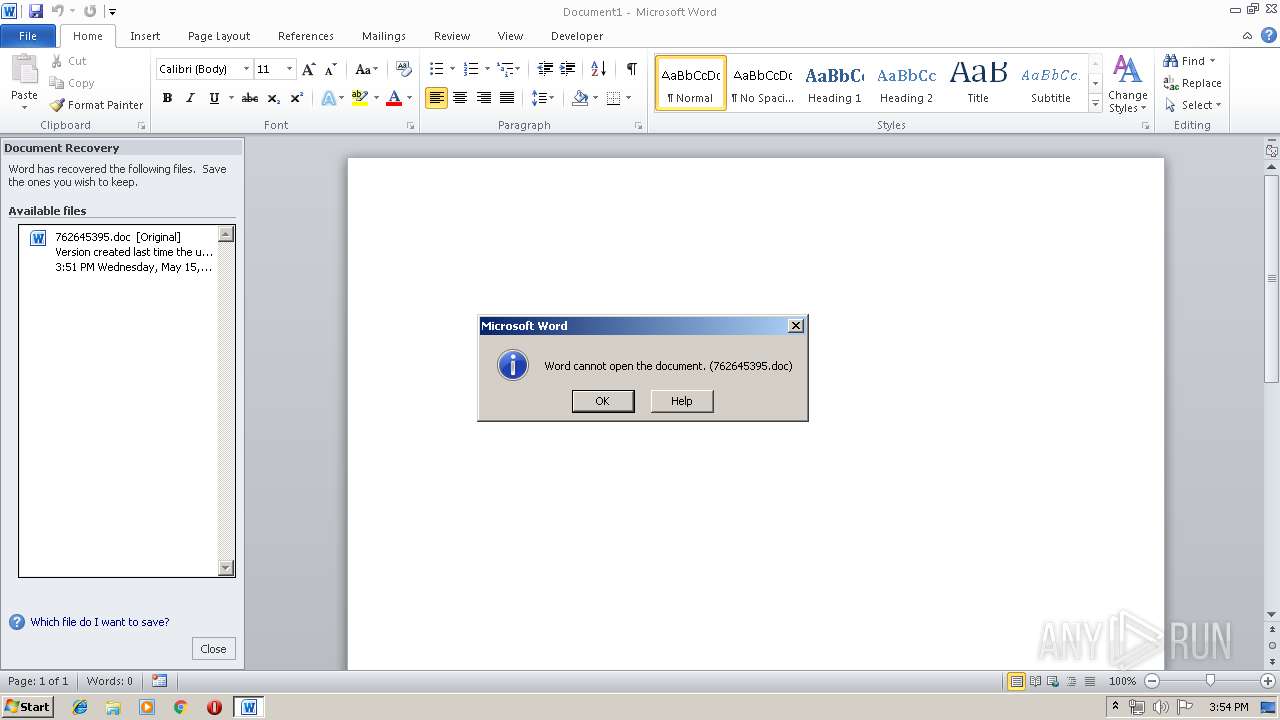
| File name: | 762645395.doc |
| Full analysis: | https://app.any.run/tasks/4c50b80f-c9fb-421e-b5ca-76542d0898a3 |
| Verdict: | Malicious activity |
| Threats: | GandCrab is probably one of the most famous Ransomware. A Ransomware is a malware that asks the victim to pay money in order to restore access to encrypted files. If the user does not cooperate the files are forever lost. |
| Analysis date: | May 15, 2019, 14:51:25 |
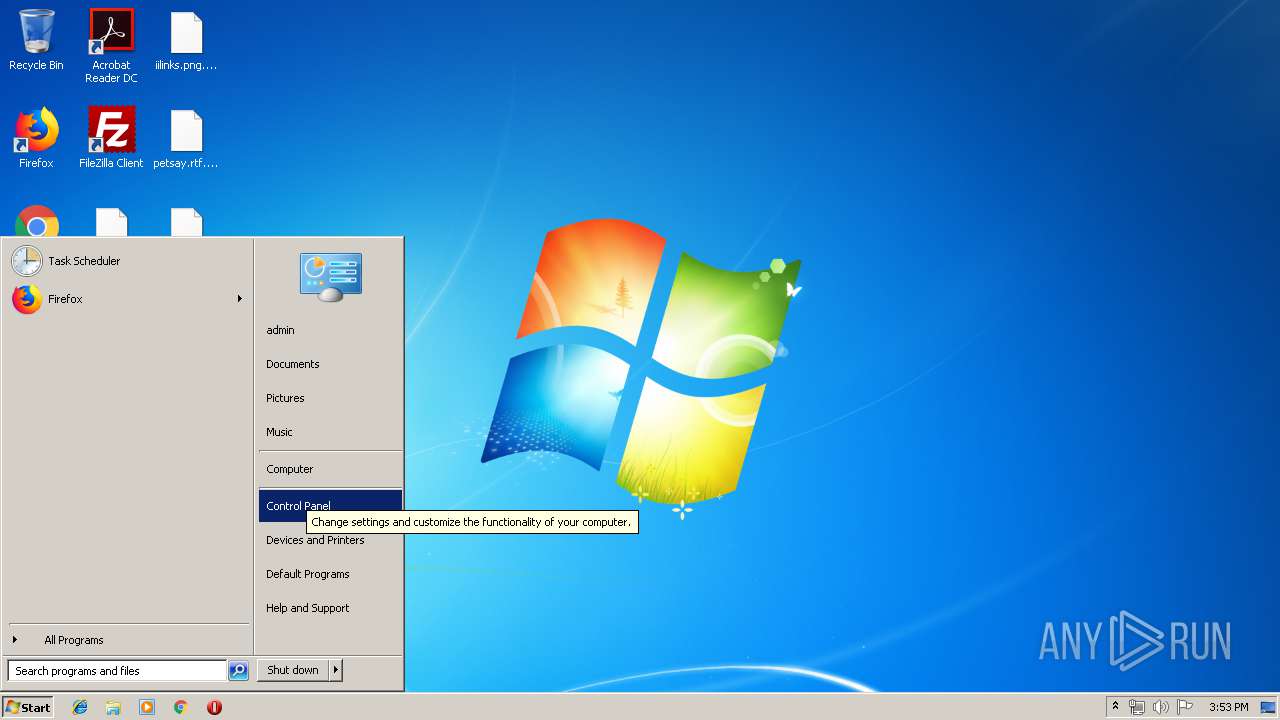
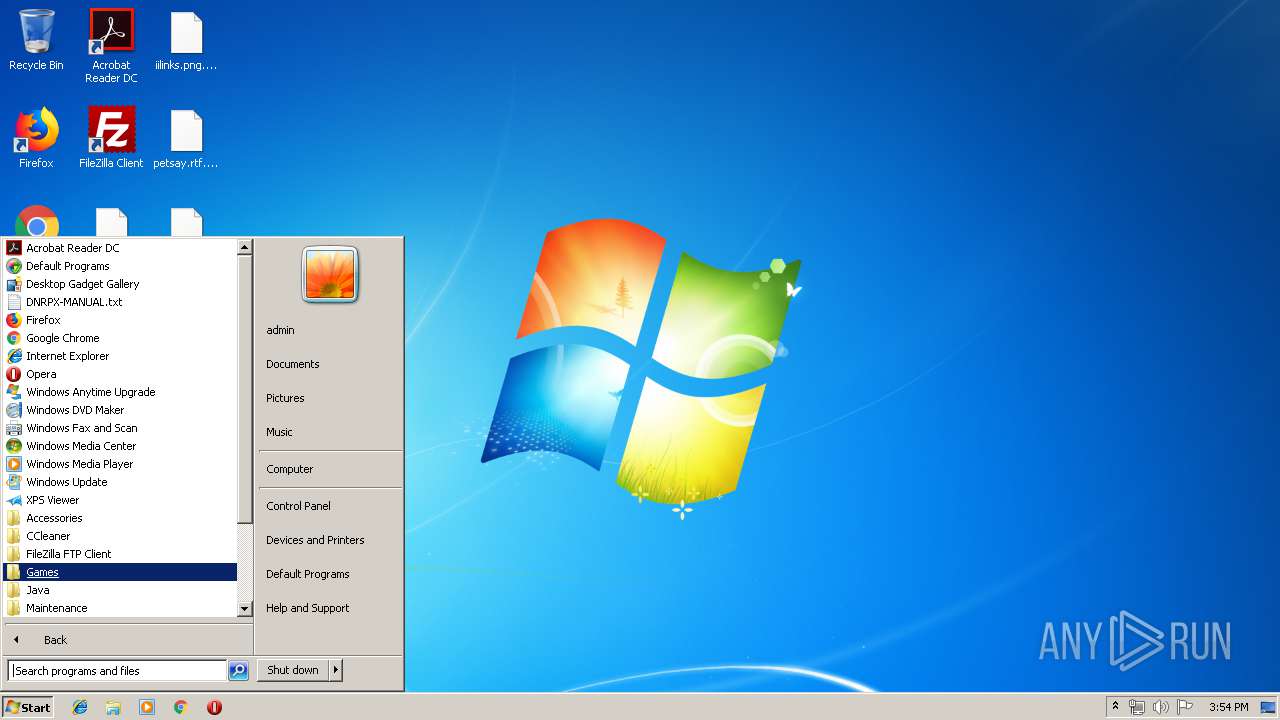
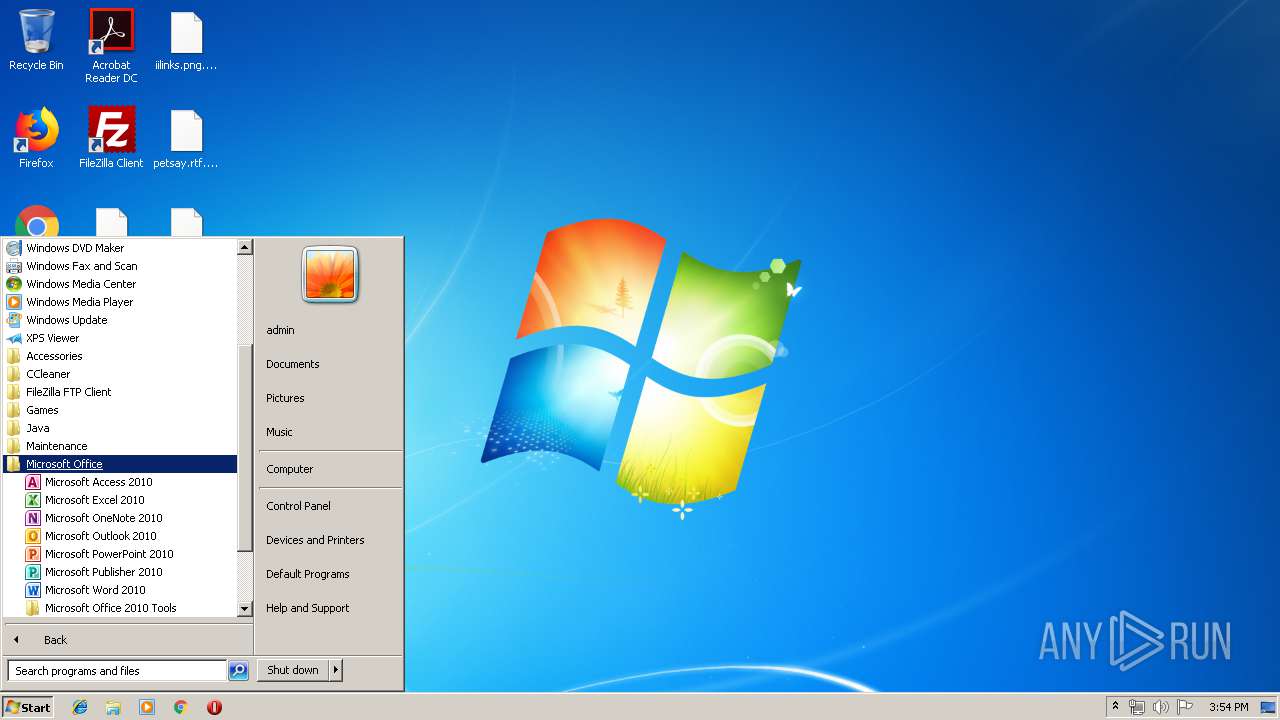
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
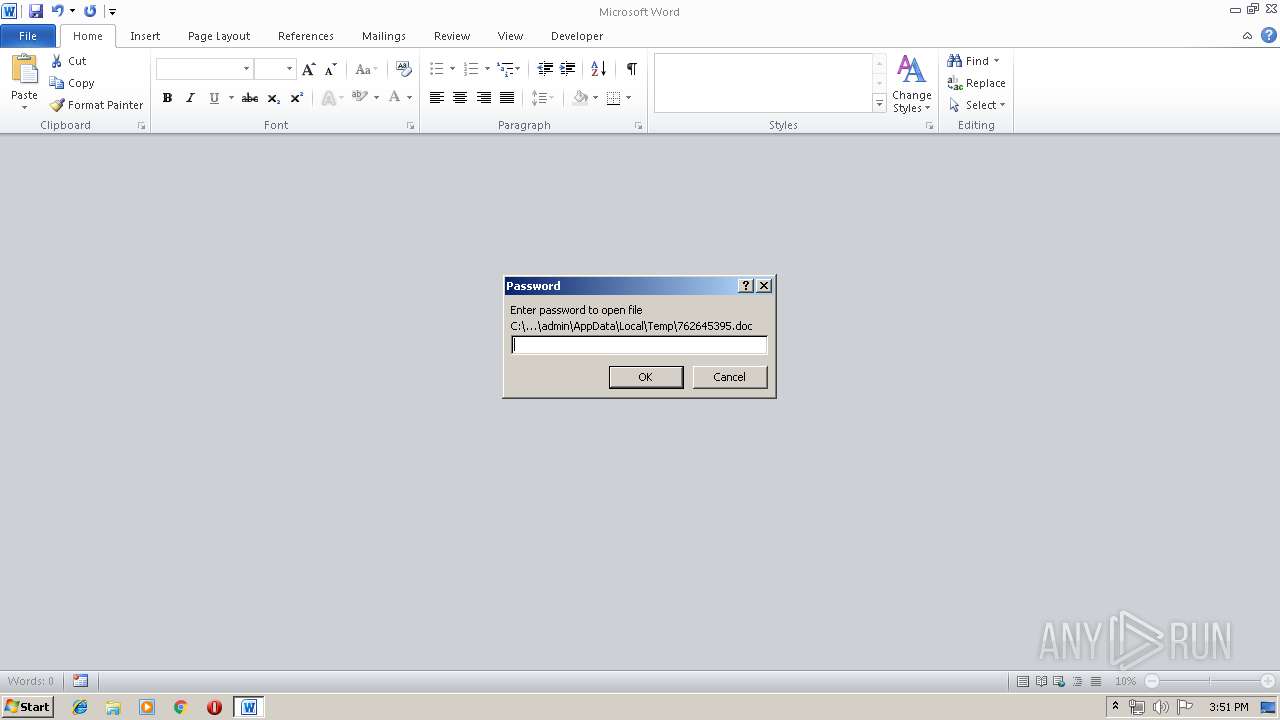
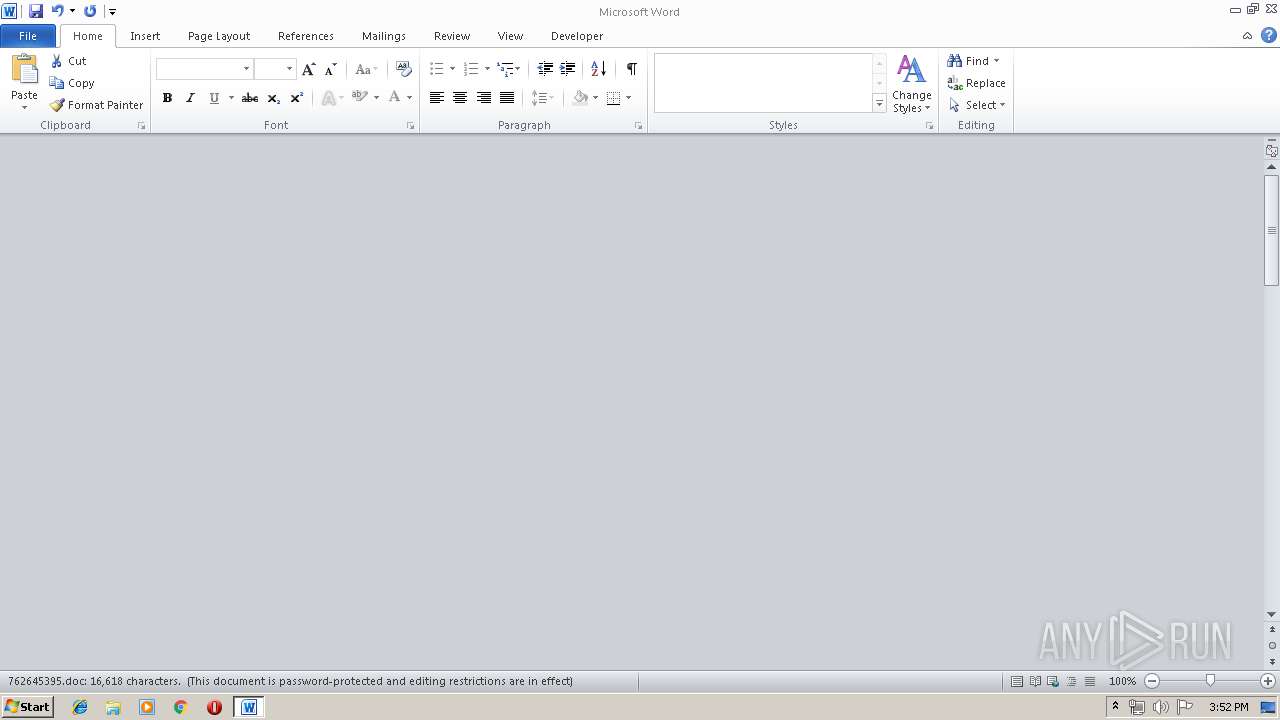
| MIME: | application/encrypted |
| File info: | CDFV2 Encrypted |
| MD5: | FED03CCBD724F44A8AFF1823904AD92E |
| SHA1: | AE789A9A9DE02E9B07BEC4DAF76DF520B9F7C029 |
| SHA256: | 7D4BCC4DD7475F95D82F783A4321A64E74F467C408C4E615E98E21B97E14260C |
| SSDEEP: | 6144:3GT6MxfiESgQawgTarwcIdUQDaaPQGjBg1Y5WZkDNurQh:3GTGEnQavTuZmVPQslNurA |
MALICIOUS
Writes file to Word startup folder
- bbbb1.ccc (PID: 760)
Renames files like Ransomware
- bbbb1.ccc (PID: 760)
Deletes shadow copies
- cmd.exe (PID: 3864)
Unusual execution from Microsoft Office
- WINWORD.EXE (PID: 1824)
Changes settings of System certificates
- bbbb1.ccc (PID: 760)
Connects to CnC server
- bbbb1.ccc (PID: 760)
Dropped file may contain instructions of ransomware
- bbbb1.ccc (PID: 760)
Actions looks like stealing of personal data
- bbbb1.ccc (PID: 760)
Executable content was dropped or overwritten
- WINWORD.EXE (PID: 1824)
Application was dropped or rewritten from another process
- bbbb1.ccc (PID: 760)
GANDCRAB detected
- bbbb1.ccc (PID: 760)
SUSPICIOUS
Creates files in the program directory
- bbbb1.ccc (PID: 760)
Starts CMD.EXE for commands execution
- bbbb1.ccc (PID: 760)
Reads the cookies of Mozilla Firefox
- bbbb1.ccc (PID: 760)
Reads Internet Cache Settings
- bbbb1.ccc (PID: 760)
Creates files in the Windows directory
- WINWORD.EXE (PID: 1824)
Starts application with an unusual extension
- WINWORD.EXE (PID: 1824)
Adds / modifies Windows certificates
- bbbb1.ccc (PID: 760)
Creates files in the user directory
- bbbb1.ccc (PID: 760)
INFO
Creates files in the user directory
- WINWORD.EXE (PID: 1824)
- WINWORD.EXE (PID: 296)
- iexplore.exe (PID: 2792)
Dropped object may contain Bitcoin addresses
- bbbb1.ccc (PID: 760)
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 1824)
- WINWORD.EXE (PID: 296)
Application launched itself
- iexplore.exe (PID: 2572)
Changes internet zones settings
- iexplore.exe (PID: 2572)
Reads Internet Cache Settings
- iexplore.exe (PID: 2792)
Reads internet explorer settings
- iexplore.exe (PID: 2792)
Dropped object may contain TOR URL's
- bbbb1.ccc (PID: 760)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
46
Monitored processes
9
Malicious processes
3
Suspicious processes
0
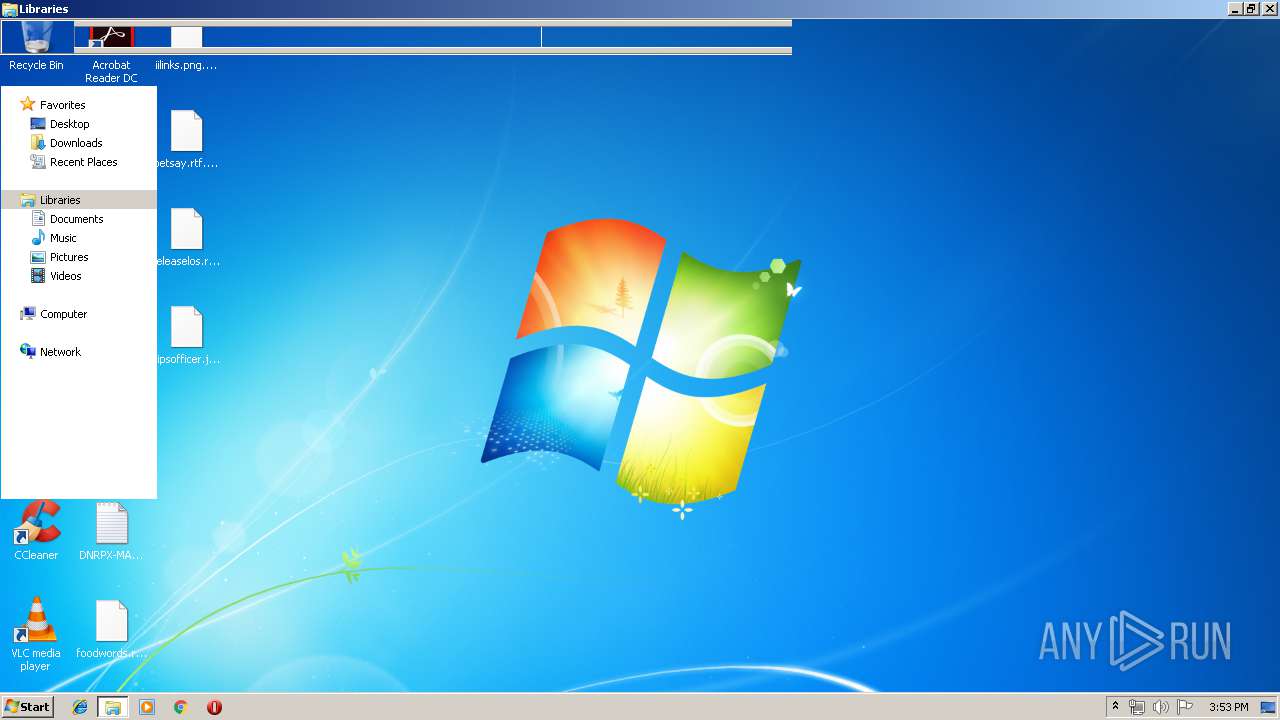
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 296 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 760 | C:\Windows\Temp\bbbb1.ccc | C:\Windows\Temp\bbbb1.ccc | WINWORD.EXE | ||||||||||||
User: admin Company: Hootsuite Integrity Level: MEDIUM Description: Tunnels Mix Attracted Slightly Pen Exit code: 0 Modules
| |||||||||||||||
| 1416 | "C:\Windows\explorer.exe" | C:\Windows\explorer.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1824 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\AppData\Local\Temp\762645395.doc" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 1916 | C:\Windows\system32\vssvc.exe | C:\Windows\system32\vssvc.exe | — | services.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft® Volume Shadow Copy Service Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2572 | "C:\Program Files\Internet Explorer\iexplore.exe" | C:\Program Files\Internet Explorer\iexplore.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 1 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2792 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:2572 CREDAT:71937 | C:\Program Files\Internet Explorer\iexplore.exe | — | iexplore.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2824 | vssadmin delete shadows /all /quiet | C:\Windows\system32\vssadmin.exe | — | cmd.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Command Line Interface for Microsoft® Volume Shadow Copy Service Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3864 | "C:\Windows\system32\cmd.exe" /c vssadmin delete shadows /all /quiet | C:\Windows\system32\cmd.exe | bbbb1.ccc | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
Total events
2 782
Read events
2 320
Write events
448
Delete events
14
Modification events
| (PID) Process: | (1824) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | write | Name: | ~5 |
Value: 7F7E350020070000010000000000000000000000 | |||
| (PID) Process: | (1824) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
| (PID) Process: | (1824) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: On | |||
| (PID) Process: | (1824) WINWORD.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | WORDFiles |
Value: 1320091678 | |||
| (PID) Process: | (1824) WINWORD.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | ProductFiles |
Value: 1320091792 | |||
| (PID) Process: | (1824) WINWORD.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | ProductFiles |
Value: 1320091793 | |||
| (PID) Process: | (1824) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word |
| Operation: | write | Name: | MTTT |
Value: 200700001A624CB42D0BD50100000000 | |||
| (PID) Process: | (1824) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | write | Name: | (5 |
Value: 287F35002007000004000000000000008C00000001000000840000003E0043003A005C00550073006500720073005C00610064006D0069006E005C0041007000700044006100740061005C0052006F0061006D0069006E0067005C004D006900630072006F0073006F00660074005C00540065006D0070006C0061007400650073005C004E006F0072006D0061006C002E0064006F0074006D00000000000000 | |||
| (PID) Process: | (1824) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | delete value | Name: | (5 |
Value: 287F35002007000004000000000000008C00000001000000840000003E0043003A005C00550073006500720073005C00610064006D0069006E005C0041007000700044006100740061005C0052006F0061006D0069006E0067005C004D006900630072006F0073006F00660074005C00540065006D0070006C0061007400650073005C004E006F0072006D0061006C002E0064006F0074006D00000000000000 | |||
| (PID) Process: | (1824) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
Executable files
2
Suspicious files
419
Text files
327
Unknown types
25
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1824 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVRE7F.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 1824 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\~DF8D3D02E3454D68C0.TMP | — | |
MD5:— | SHA256:— | |||
| 1824 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\~DF38BA7F426F564F1D.TMP | — | |
MD5:— | SHA256:— | |||
| 1824 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\~DFFDA63B09F9E62635.TMP | — | |
MD5:— | SHA256:— | |||
| 1824 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\~DF1C9C70C931EB591B.TMP | — | |
MD5:— | SHA256:— | |||
| 1824 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\~DFA6909DF57D96DE17.TMP | — | |
MD5:— | SHA256:— | |||
| 1824 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\~DFFBDAC13D729DA0D0.TMP | — | |
MD5:— | SHA256:— | |||
| 1824 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\4A89E27F.jpg | — | |
MD5:— | SHA256:— | |||
| 1824 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\~DFE11267962CA505B0.TMP | — | |
MD5:— | SHA256:— | |||
| 760 | bbbb1.ccc | C:\Recovery\345b46fe-a9f9-11e7-a83c-e8a4f72b1d33\boot.sdi | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
2
TCP/UDP connections
4
DNS requests
3
Threats
4
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
760 | bbbb1.ccc | GET | 301 | 107.173.49.208:80 | http://www.kakaocorp.link/ | US | html | 162 b | malicious |
2572 | iexplore.exe | GET | 200 | 204.79.197.200:80 | http://www.bing.com/favicon.ico | US | image | 237 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1824 | WINWORD.EXE | 51.77.146.231:443 | zircoilerexelandr.info | — | GB | suspicious |
760 | bbbb1.ccc | 107.173.49.208:80 | www.kakaocorp.link | ColoCrossing | US | malicious |
2572 | iexplore.exe | 204.79.197.200:80 | www.bing.com | Microsoft Corporation | US | whitelisted |
760 | bbbb1.ccc | 107.173.49.208:443 | www.kakaocorp.link | ColoCrossing | US | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
zircoilerexelandr.info |
| suspicious |
www.kakaocorp.link |
| malicious |
www.bing.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
760 | bbbb1.ccc | A Network Trojan was detected | MALWARE [PTsecurity] Blacklisted GandCrab Ransomware C2 Server |
760 | bbbb1.ccc | A Network Trojan was detected | MALWARE [PTsecurity] Blacklisted GandCrab Ransomware C2 Server |
2 ETPRO signatures available at the full report