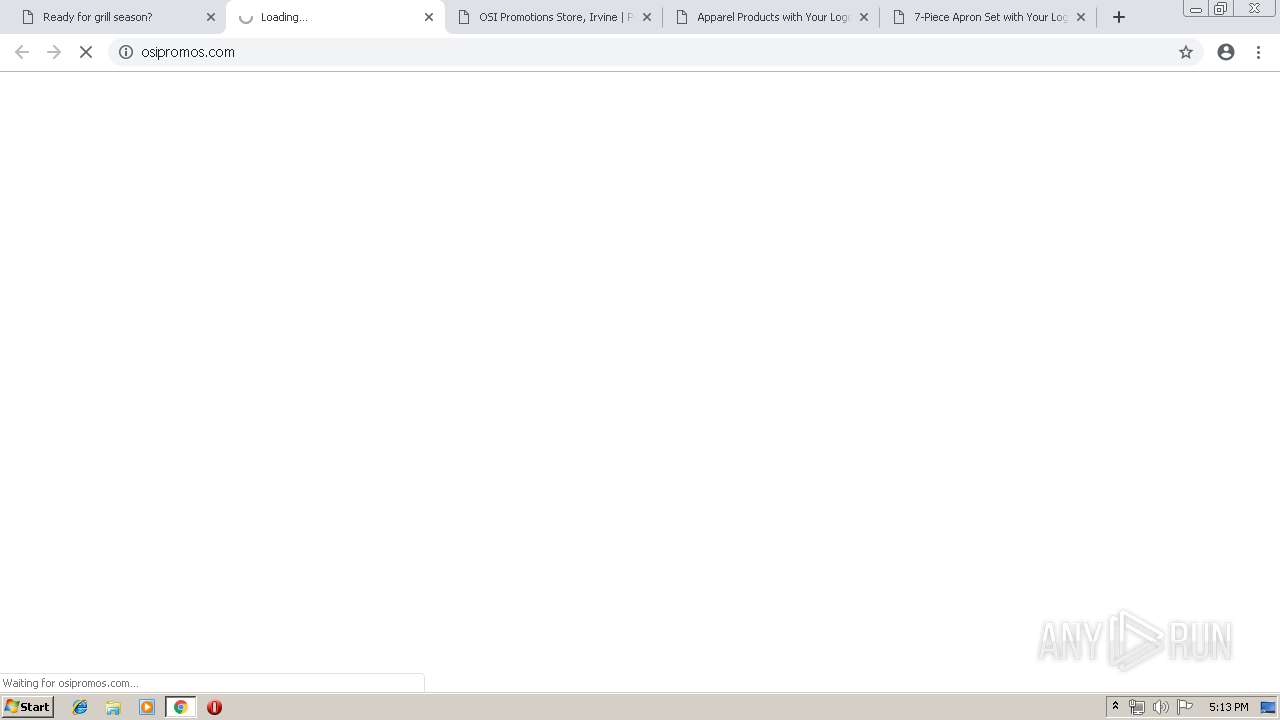
| URL: | https://email.outboundsend.com/wf/click?upn=-2BtMiRk7i5oMZAyT1H87wCXimWT4JRW-2FqI9SrgMsa-2FJTXmpQl11RbMFOynBBULAL8_PiqEyHvoKQzukqkoJGE9R31lujmbeYhptLlRqoHied3m6tbbItigBbvgbJl8pyQE9B3xUdsC9eyx0g4UzzTbxxPDKpKhU1Sz7lQVVUjLlQVw-2FF1x8S6rycEJYgj49ImwDDUcFLkzAw-2FKqe84bBHY1LYmXGss6MbIYbGn5yGc9RPsWat-2BMgam-2BrbEIRJ4WzpSvKmh1fpN3y1rWvNAOMeYLyhjJH04uEzuk4KRO-2FfU1CWWpRTSSBbYrqA6H9aGTmeukScikboO9sWHPjHd0I6ZnVKO4zafQKgo-2FPso8IwfmcVk2SvAWV51vS8qh6X8JD5R7umxfKYtcheNfSUPkaItgr56OlQnmJjWF6Ho3LswyONnE2sdoyhFKgS9KGGE4PreSgO-2FW4DD-2F-2BKo-2BzXNNZujDJBTrqUQg3YeZOt5vTMTvIq3OR-2FEcgRawZEvi-2BTQb5Vt |
| Full analysis: | https://app.any.run/tasks/c4ee72c1-5c30-4323-9e7f-d45ed6eff4b3 |
| Verdict: | Malicious activity |
| Analysis date: | June 19, 2019, 16:10:59 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MD5: | 578BED8E0E3BBA22CA3DBC33D0FCBF92 |
| SHA1: | C304705E8BC2094D128DD4BCD2B8C0644969ECB2 |
| SHA256: | 7D3B7C6AC408FF545074221DB96556B22AF686182451DDDB139EE4978AEF5E37 |
| SSDEEP: | 12:2dL6Spz3LzBgRLMn48yyc6Vroe9oZkFOU+pctwyGENbrptug+:2djb9gRQ4t6JoMoPpeh3v+ |
MALICIOUS
No malicious indicators.SUSPICIOUS
Modifies files in Chrome extension folder
- chrome.exe (PID: 1832)
INFO
Application launched itself
- chrome.exe (PID: 1832)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
58
Monitored processes
27
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 296 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=940,16708445020135051685,17252138367246493940,131072 --enable-features=PasswordImport --disable-gpu-compositing --service-pipe-token=12796160541388891557 --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=12796160541388891557 --renderer-client-id=23 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=4132 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 1084 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=940,16708445020135051685,17252138367246493940,131072 --enable-features=PasswordImport --disable-gpu-compositing --service-pipe-token=9983174423650882554 --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=9983174423650882554 --renderer-client-id=24 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3648 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 1172 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=940,16708445020135051685,17252138367246493940,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=11284258984889125601 --mojo-platform-channel-handle=3712 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 1332 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=940,16708445020135051685,17252138367246493940,131072 --enable-features=PasswordImport --disable-gpu-compositing --service-pipe-token=1623163383384907396 --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=1623163383384907396 --renderer-client-id=22 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=932 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 1448 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=940,16708445020135051685,17252138367246493940,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=7710919829716465880 --mojo-platform-channel-handle=4016 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 1768 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=940,16708445020135051685,17252138367246493940,131072 --enable-features=PasswordImport --service-pipe-token=15681485701852209054 --lang=en-US --extension-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=15681485701852209054 --renderer-client-id=3 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2232 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 1832 | "C:\Program Files\Google\Chrome\Application\chrome.exe" https://email.outboundsend.com/wf/click?upn=-2BtMiRk7i5oMZAyT1H87wCXimWT4JRW-2FqI9SrgMsa-2FJTXmpQl11RbMFOynBBULAL8_PiqEyHvoKQzukqkoJGE9R31lujmbeYhptLlRqoHied3m6tbbItigBbvgbJl8pyQE9B3xUdsC9eyx0g4UzzTbxxPDKpKhU1Sz7lQVVUjLlQVw-2FF1x8S6rycEJYgj49ImwDDUcFLkzAw-2FKqe84bBHY1LYmXGss6MbIYbGn5yGc9RPsWat-2BMgam-2BrbEIRJ4WzpSvKmh1fpN3y1rWvNAOMeYLyhjJH04uEzuk4KRO-2FfU1CWWpRTSSBbYrqA6H9aGTmeukScikboO9sWHPjHd0I6ZnVKO4zafQKgo-2FPso8IwfmcVk2SvAWV51vS8qh6X8JD5R7umxfKYtcheNfSUPkaItgr56OlQnmJjWF6Ho3LswyONnE2sdoyhFKgS9KGGE4PreSgO-2FW4DD-2F-2BKo-2BzXNNZujDJBTrqUQg3YeZOt5vTMTvIq3OR-2FEcgRawZEvi-2BTQb5Vt | C:\Program Files\Google\Chrome\Application\chrome.exe | explorer.exe | ||||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 2128 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=940,16708445020135051685,17252138367246493940,131072 --enable-features=PasswordImport --disable-gpu-compositing --service-pipe-token=17219657908900569519 --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=17219657908900569519 --renderer-client-id=6 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3724 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 2296 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=940,16708445020135051685,17252138367246493940,131072 --enable-features=PasswordImport --gpu-preferences=KAAAAAAAAACAAwAAAQAAAAAAAAAAAGAAAAAAAAEAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --service-request-channel-token=10754223863273789255 --mojo-platform-channel-handle=972 --ignored=" --type=renderer " /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 2528 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=940,16708445020135051685,17252138367246493940,131072 --enable-features=PasswordImport --disable-gpu-compositing --service-pipe-token=4953940402745376833 --lang=en-US --extension-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=4953940402745376833 --renderer-client-id=17 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2652 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
Total events
568
Read events
471
Write events
92
Delete events
5
Modification events
| (PID) Process: | (2828) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 1832-13205434275266875 |
Value: 259 | |||
| (PID) Process: | (1832) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (1832) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (1832) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (1832) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (1832) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (1832) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (1832) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (1832) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 3488-13197474229333984 |
Value: 0 | |||
| (PID) Process: | (1832) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
Executable files
0
Suspicious files
105
Text files
209
Unknown types
8
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1832 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\index | — | |
MD5:— | SHA256:— | |||
| 1832 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_0 | — | |
MD5:— | SHA256:— | |||
| 1832 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_1 | — | |
MD5:— | SHA256:— | |||
| 1832 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_2 | — | |
MD5:— | SHA256:— | |||
| 1832 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_3 | — | |
MD5:— | SHA256:— | |||
| 1832 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\da81ad3d-0ad4-42d4-af9b-1190a0267d60.tmp | — | |
MD5:— | SHA256:— | |||
| 1832 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000018.dbtmp | — | |
MD5:— | SHA256:— | |||
| 1832 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\GPUCache\index | — | |
MD5:— | SHA256:— | |||
| 1832 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\GPUCache\data_0 | — | |
MD5:— | SHA256:— | |||
| 1832 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\GPUCache\data_1 | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
393
TCP/UDP connections
81
DNS requests
44
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
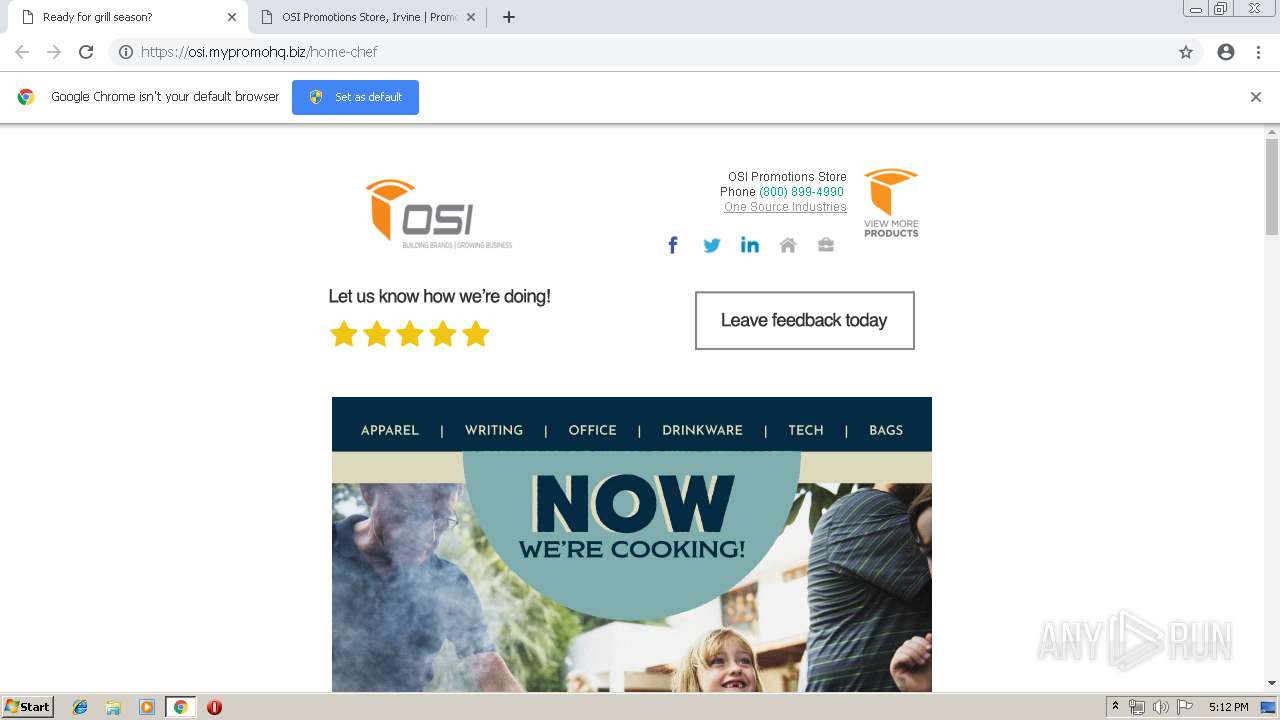
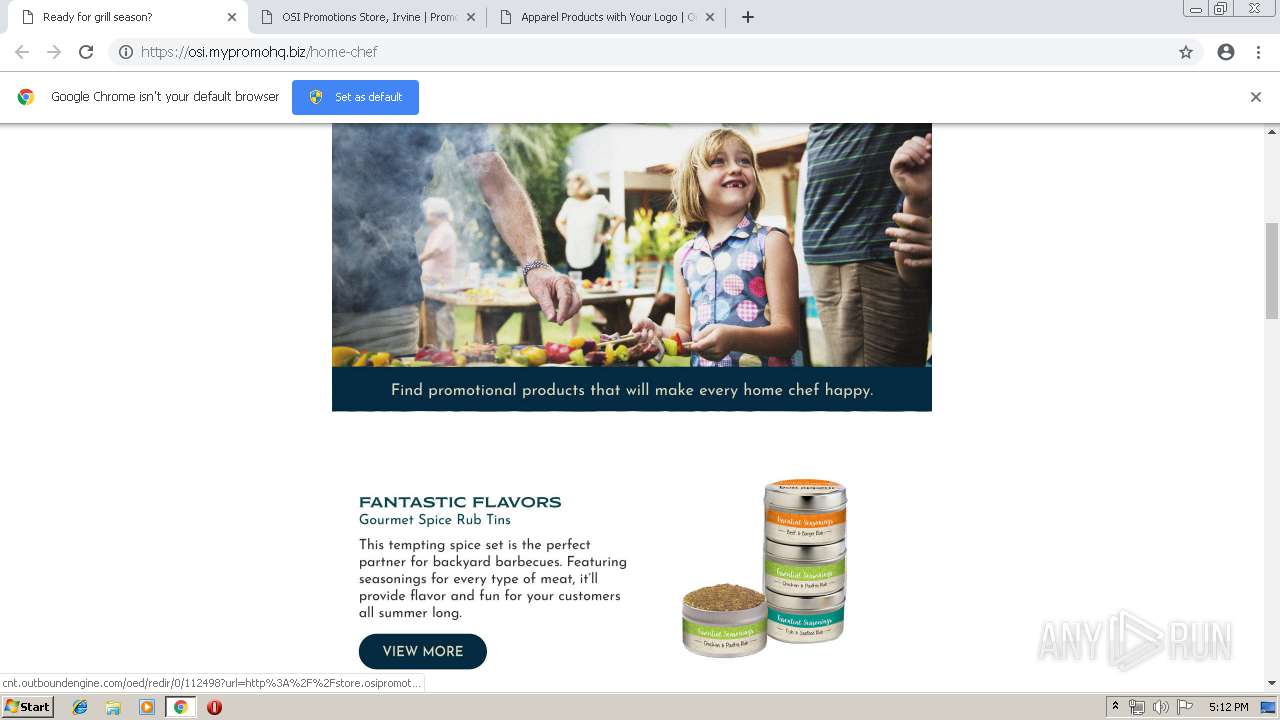
1832 | chrome.exe | GET | 200 | 143.204.214.55:80 | http://email2.promolabslink.com/2019/06.17/HomeChef_Spotlight_06.jpg | US | image | 2.96 Kb | suspicious |
1832 | chrome.exe | GET | 200 | 143.204.214.55:80 | http://email2.promolabslink.com/2019/06.17/HomeChef_Spotlight_02.jpg | US | image | 3.82 Kb | suspicious |
1832 | chrome.exe | GET | 200 | 143.204.214.55:80 | http://email2.promolabslink.com/2019/06.17/HomeChef_Spotlight_08.jpg | US | image | 75.1 Kb | suspicious |
1832 | chrome.exe | GET | 200 | 143.204.214.55:80 | http://email2.promolabslink.com/2019/06.17/HomeChef_Spotlight_11.jpg | US | image | 66.4 Kb | suspicious |
1832 | chrome.exe | GET | 200 | 93.184.221.240:80 | http://www.download.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab | US | compressed | 56.2 Kb | whitelisted |
1832 | chrome.exe | GET | 200 | 143.204.214.55:80 | http://email2.promolabslink.com/2019/06.17/HomeChef_Spotlight_10.jpg | US | image | 74.6 Kb | suspicious |
1832 | chrome.exe | GET | 200 | 143.204.214.55:80 | http://email2.promolabslink.com/2019/06.17/HomeChef_Spotlight_16.jpg | US | image | 16.3 Kb | suspicious |
1832 | chrome.exe | GET | 200 | 143.204.214.55:80 | http://email2.promolabslink.com/2019/06.17/HomeChef_Spotlight_12.jpg | US | image | 23.6 Kb | suspicious |
1832 | chrome.exe | GET | 200 | 143.204.214.55:80 | http://email2.promolabslink.com/2019/06.17/HomeChef_Spotlight_18.jpg | US | image | 19.2 Kb | suspicious |
1832 | chrome.exe | GET | 200 | 143.204.214.55:80 | http://email2.promolabslink.com/2019/06.17/HomeChef_Spotlight_17.jpg | US | image | 10.5 Kb | suspicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
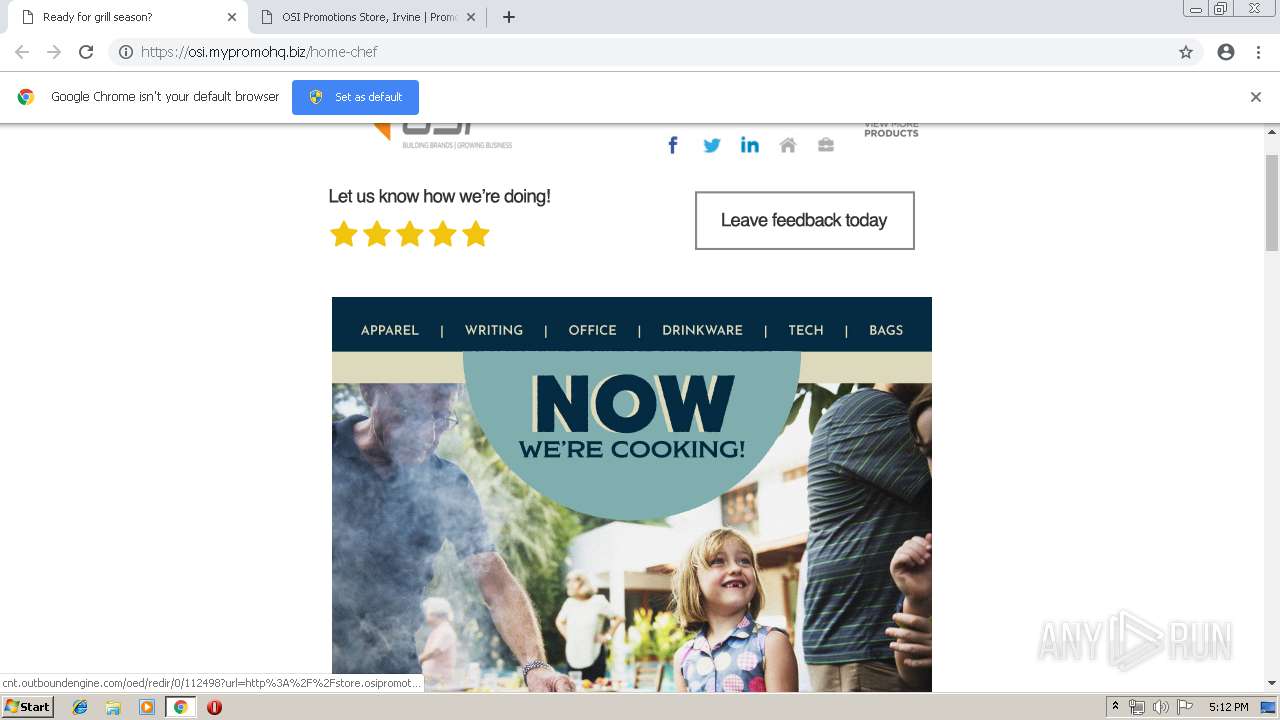
1832 | chrome.exe | 143.204.214.124:443 | email.outboundsend.com | — | US | unknown |
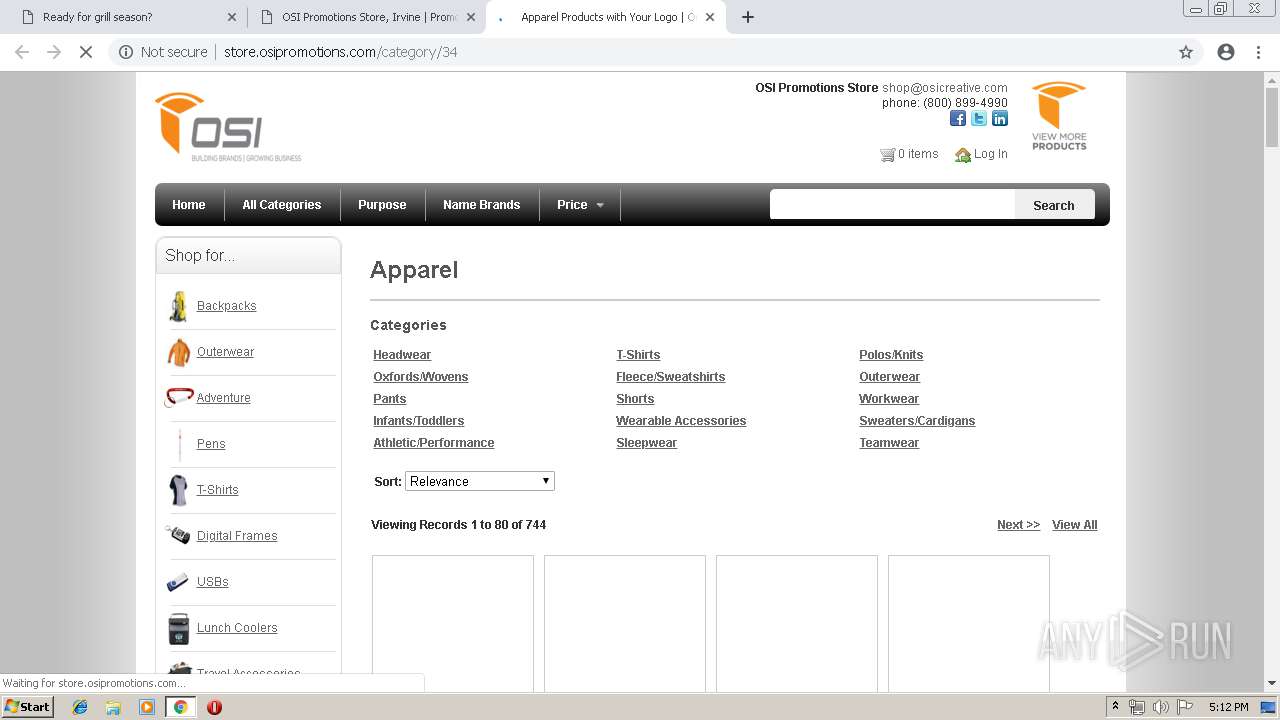
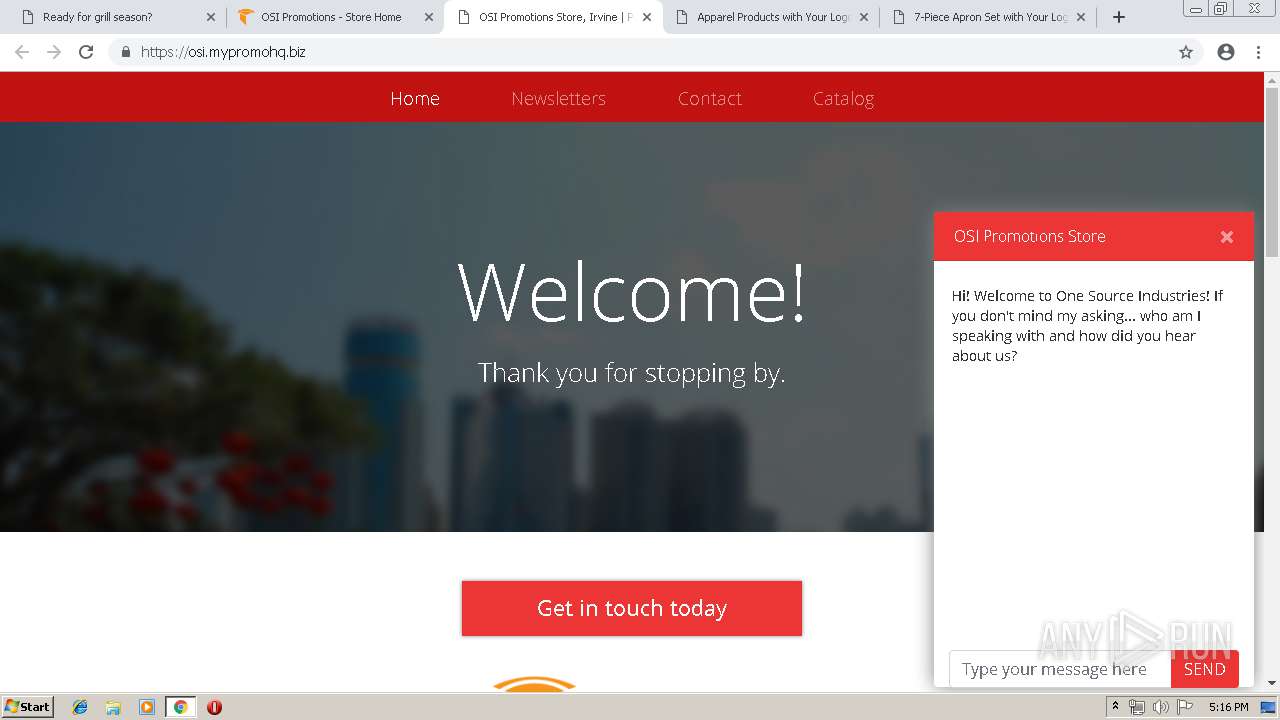
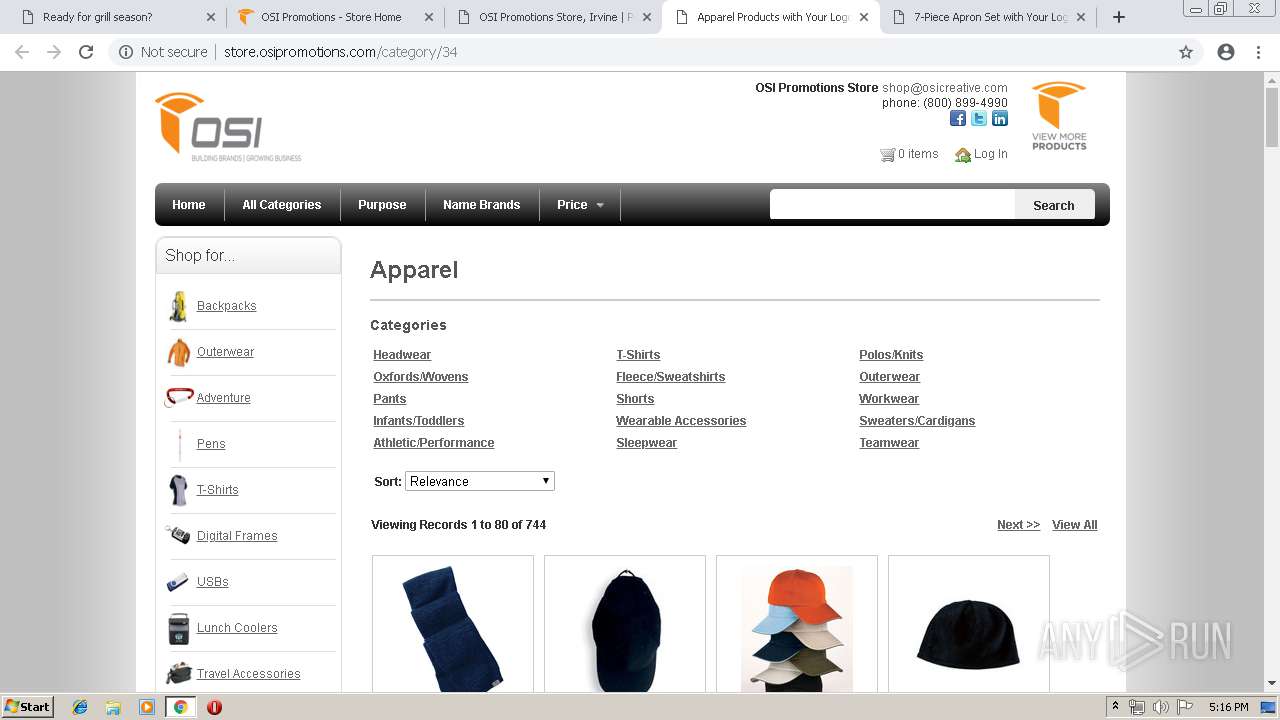
1832 | chrome.exe | 34.210.142.153:443 | osi.mypromohq.biz | Amazon.com, Inc. | US | unknown |
1832 | chrome.exe | 143.204.214.82:443 | content.outboundengine.com | — | US | whitelisted |
1832 | chrome.exe | 143.204.214.28:80 | content.outboundengine.com | — | US | unknown |
— | — | 216.58.208.33:443 | clients2.googleusercontent.com | Google Inc. | US | whitelisted |
1832 | chrome.exe | 143.204.214.55:80 | email2.promolabslink.com | — | US | suspicious |
1832 | chrome.exe | 173.194.5.41:80 | r4---sn-aigzrn7e.gvt1.com | Google Inc. | US | whitelisted |
1832 | chrome.exe | 52.216.160.85:443 | s3.amazonaws.com | Amazon.com, Inc. | US | unknown |
1832 | chrome.exe | 108.177.15.198:80 | redirector.gvt1.com | Google Inc. | US | whitelisted |
1832 | chrome.exe | 172.217.22.35:443 | ssl.gstatic.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
clientservices.googleapis.com |
| whitelisted |
email.outboundsend.com |
| whitelisted |
accounts.google.com |
| shared |
x.ss2.us |
| whitelisted |
www.download.windowsupdate.com |
| whitelisted |
www.google.com |
| malicious |
osi.mypromohq.biz |
| unknown |
s3.amazonaws.com |
| shared |
content.outboundengine.com |
| whitelisted |
d1k3c4xlx29yaw.cloudfront.net |
| whitelisted |