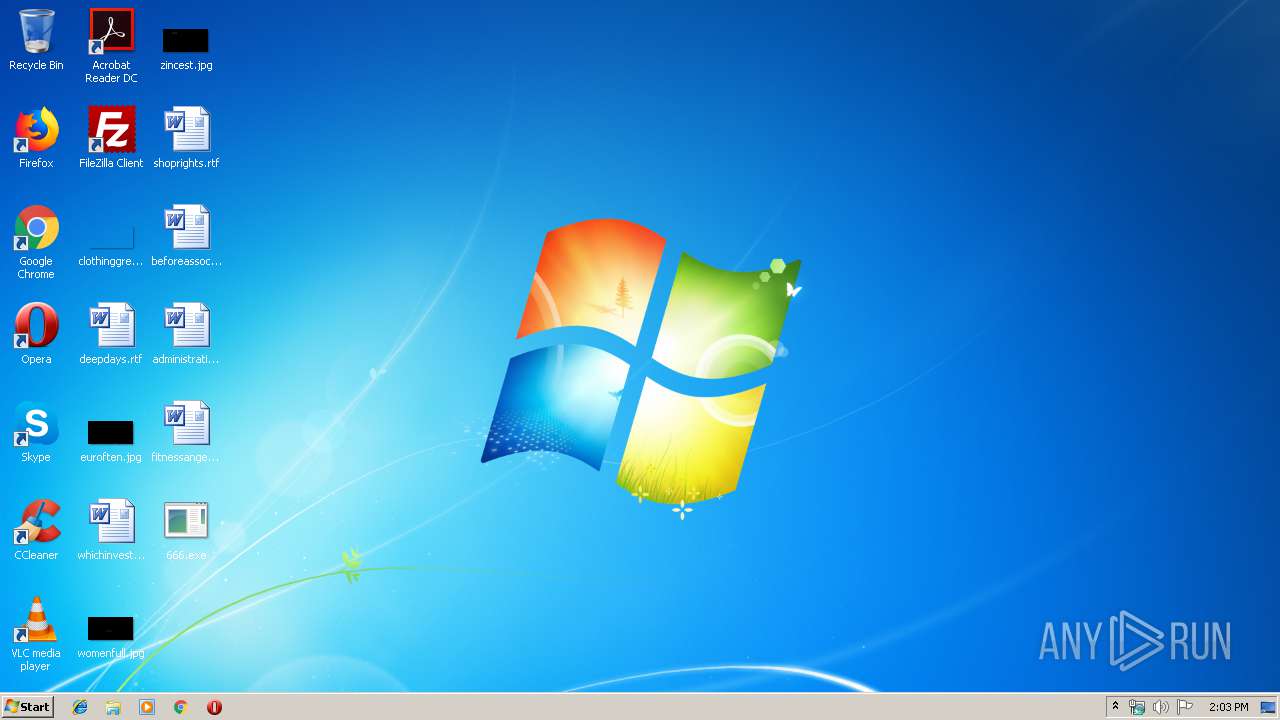
| File name: | 666.exe |
| Full analysis: | https://app.any.run/tasks/3e9301f8-4ff9-4610-a075-4480a63ed993 |
| Verdict: | No threats detected |
| Analysis date: | November 17, 2019, 14:03:24 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 5CA68C39B1EBC199458F6CC46F746EED |
| SHA1: | 7E381F658478E3B06FD0764ECFC6DCF211E0D8C3 |
| SHA256: | 7D31660F2B93077A0A8CF17F6C2B6F71A424A25E6BFFC1DAA52EDC3638EB16D4 |
| SSDEEP: | 98304:aBydzBg18kuwx3vFmBlnDJnhyQGIR/kco:aBydiuwx2DJnUQGI+N |
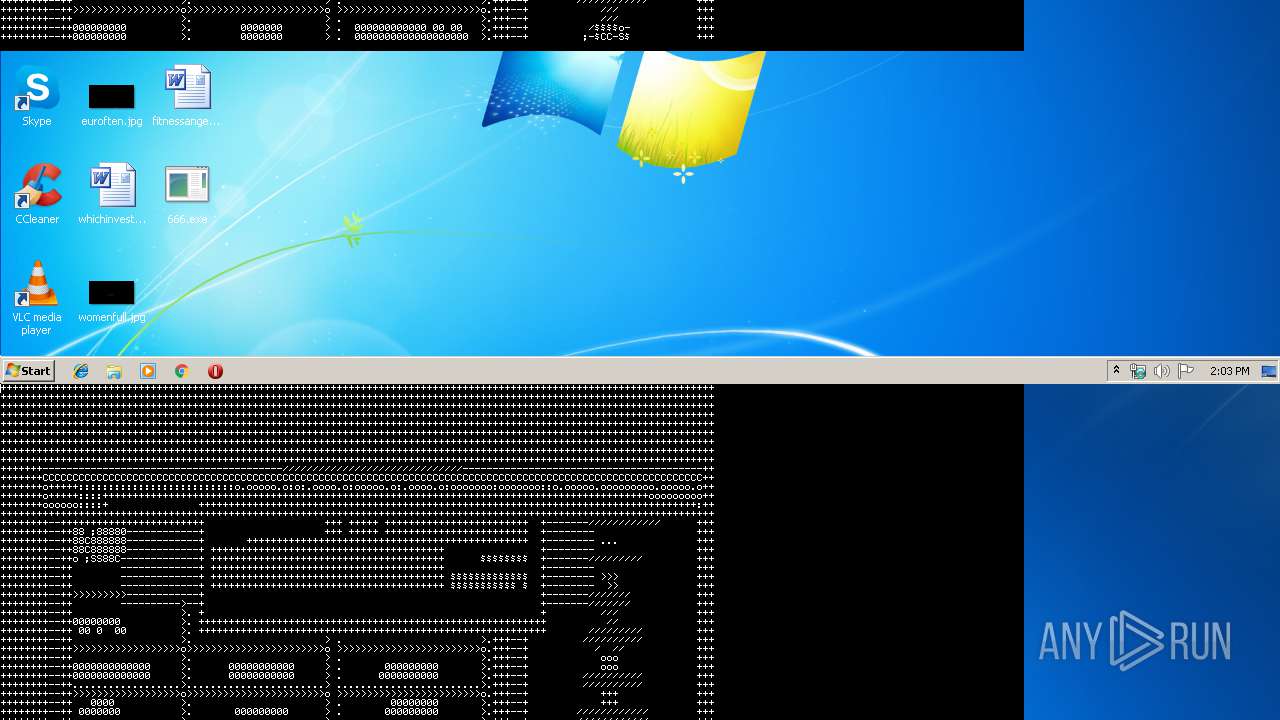
MALICIOUS
Loads dropped or rewritten executable
- 666.exe (PID: 3936)
SUSPICIOUS
Executable content was dropped or overwritten
- 666.exe (PID: 3936)
INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 EXE PECompact compressed (generic) (16.9) |
|---|---|---|
| .exe | | | Win32 Executable MS Visual C++ (generic) (12.7) |
| .exe | | | Win64 Executable (generic) (11.2) |
| .scr | | | Windows screen saver (5.3) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2004:09:09 08:46:18+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 6 |
| CodeSize: | 28672 |
| InitializedDataSize: | 57344 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x3705 |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 10.1.0.11 |
| ProductVersionNumber: | 10.1.0.11 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Windows NT 32-bit |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Unicode |
| CompanyName: | Macromedia, Inc. |
| FileDescription: | Macromedia Projector |
| FileVersion: | 10.1r11 |
| InternalName: | Projector |
| LegalCopyright: | Copyright © 1985-2004 Macromedia, Inc. |
| LegalTrademarks: | Director® is a registered trademark and Shockwave(tm) is a trademark of Macromedia, Inc. |
| OriginalFileName: | Projector.exe |
| ProductName: | Director MX 2004 |
| ProductVersion: | 10.1 |
| Tag040904E4: | - |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 09-Sep-2004 06:46:18 |
| Detected languages: |
|
| CompanyName: | Macromedia, Inc. |
| FileDescription: | Macromedia Projector |
| FileVersion: | 10.1r11 |
| InternalName: | Projector |
| LegalCopyright: | Copyright © 1985-2004 Macromedia, Inc. |
| LegalTrademarks: | Director® is a registered trademark and Shockwave(tm) is a trademark of Macromedia, Inc. |
| OriginalFilename: | Projector.exe |
| ProductName: | Director MX 2004 |
| ProductVersion: | 10.1 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x000000E8 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 4 |
| Time date stamp: | 09-Sep-2004 06:46:18 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x0000681A | 0x00007000 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.31296 |
.rdata | 0x00008000 | 0x0000120A | 0x00002000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 3.60374 |
.data | 0x0000A000 | 0x0000453C | 0x00003000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0.948219 |
.rsrc | 0x0000F000 | 0x00006EE8 | 0x00007000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 2.28629 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 3.41439 | 1788 | UNKNOWN | English - United States | RT_VERSION |
2 | 1.47418 | 744 | UNKNOWN | English - United States | RT_ICON |
3 | 2.1912 | 296 | UNKNOWN | English - United States | RT_ICON |
4 | 2.0958 | 3752 | UNKNOWN | English - United States | RT_ICON |
5 | 2.44001 | 2216 | UNKNOWN | English - United States | RT_ICON |
6 | 3.05258 | 1384 | UNKNOWN | English - United States | RT_ICON |
7 | 1.11222 | 9640 | UNKNOWN | English - United States | RT_ICON |
8 | 1.22378 | 4264 | UNKNOWN | English - United States | RT_ICON |
9 | 1.58437 | 1128 | UNKNOWN | English - United States | RT_ICON |
63 | 3.17905 | 680 | UNKNOWN | English - United States | RT_STRING |
Imports
ADVAPI32.dll |
GDI32.dll |
KERNEL32.dll |
USER32.dll |
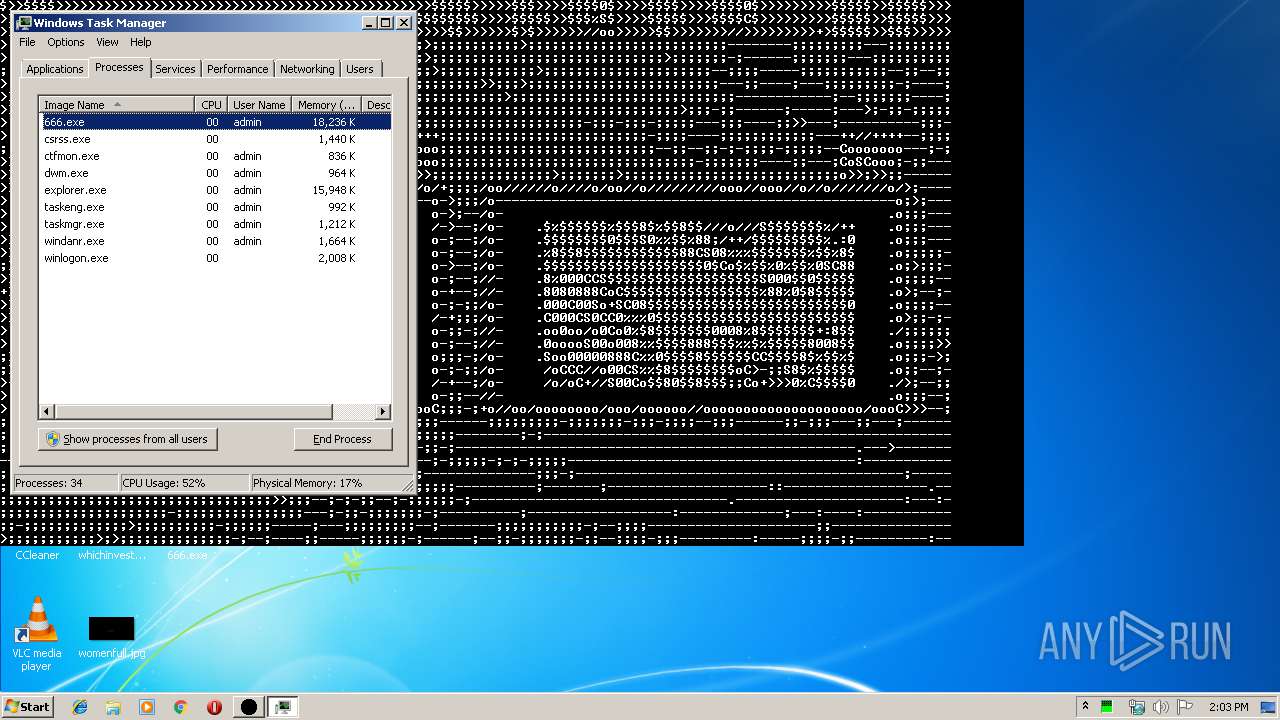
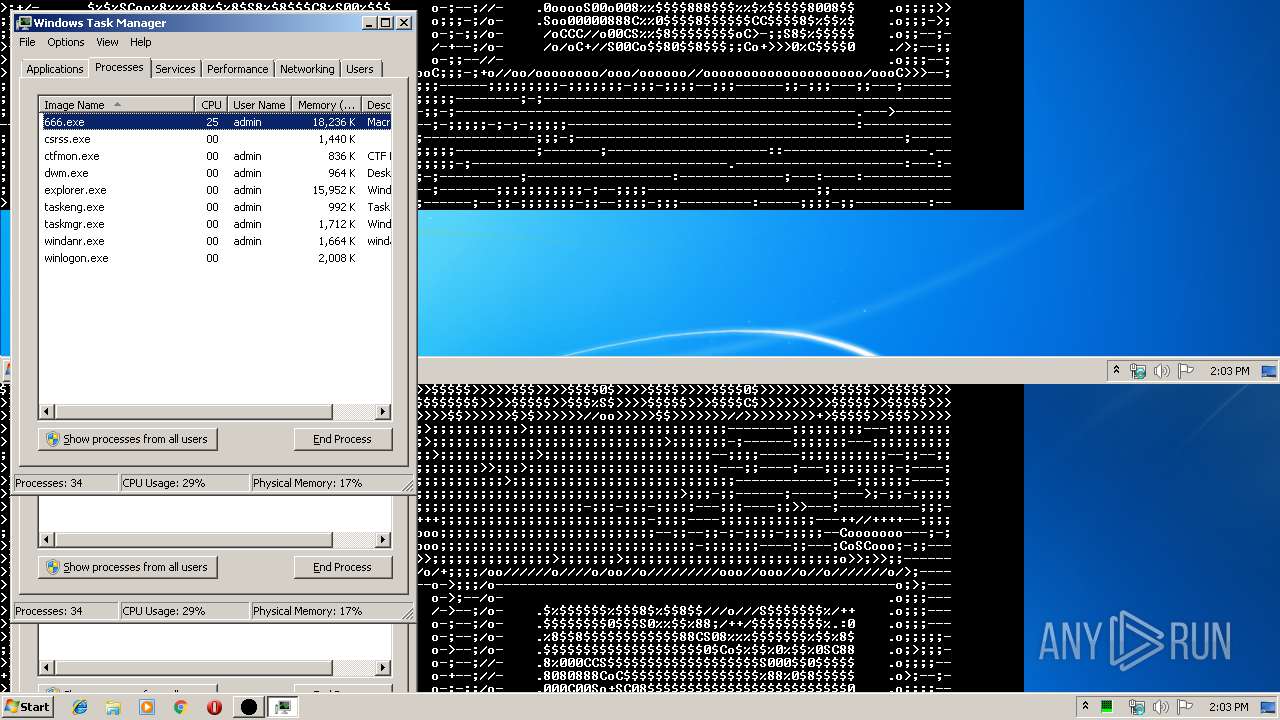
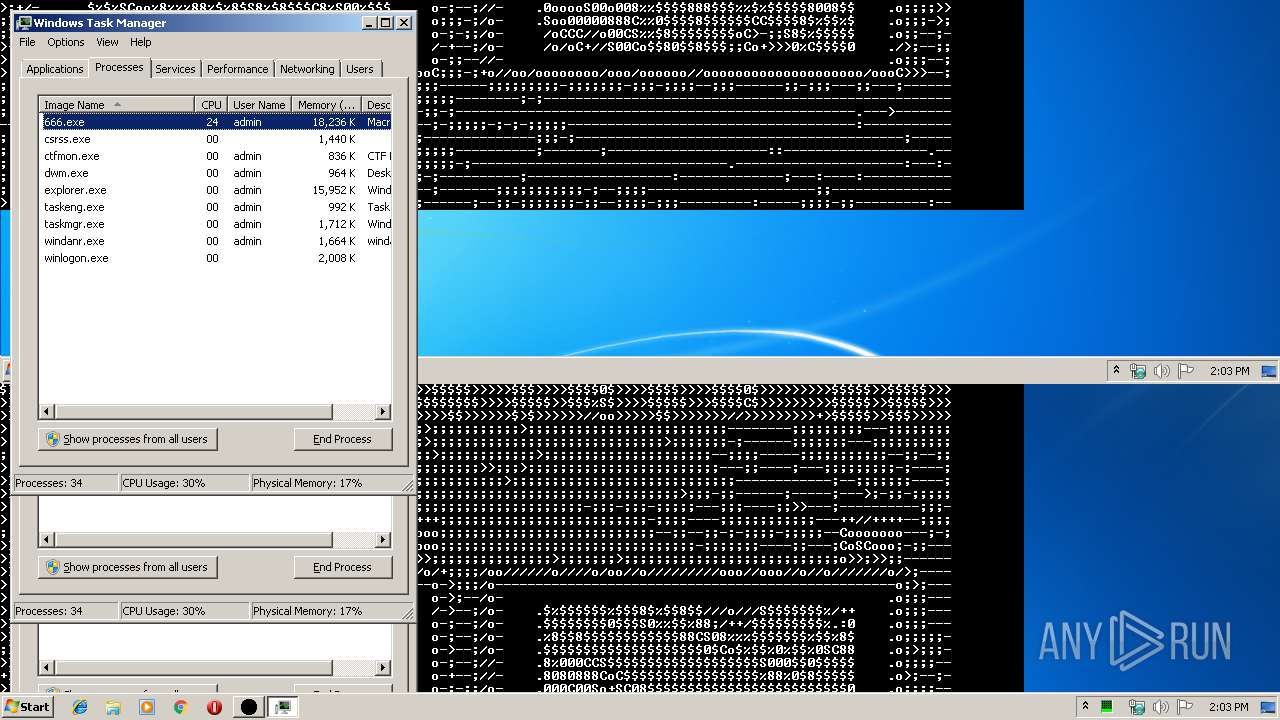
Total processes
36
Monitored processes
1
Malicious processes
0
Suspicious processes
1
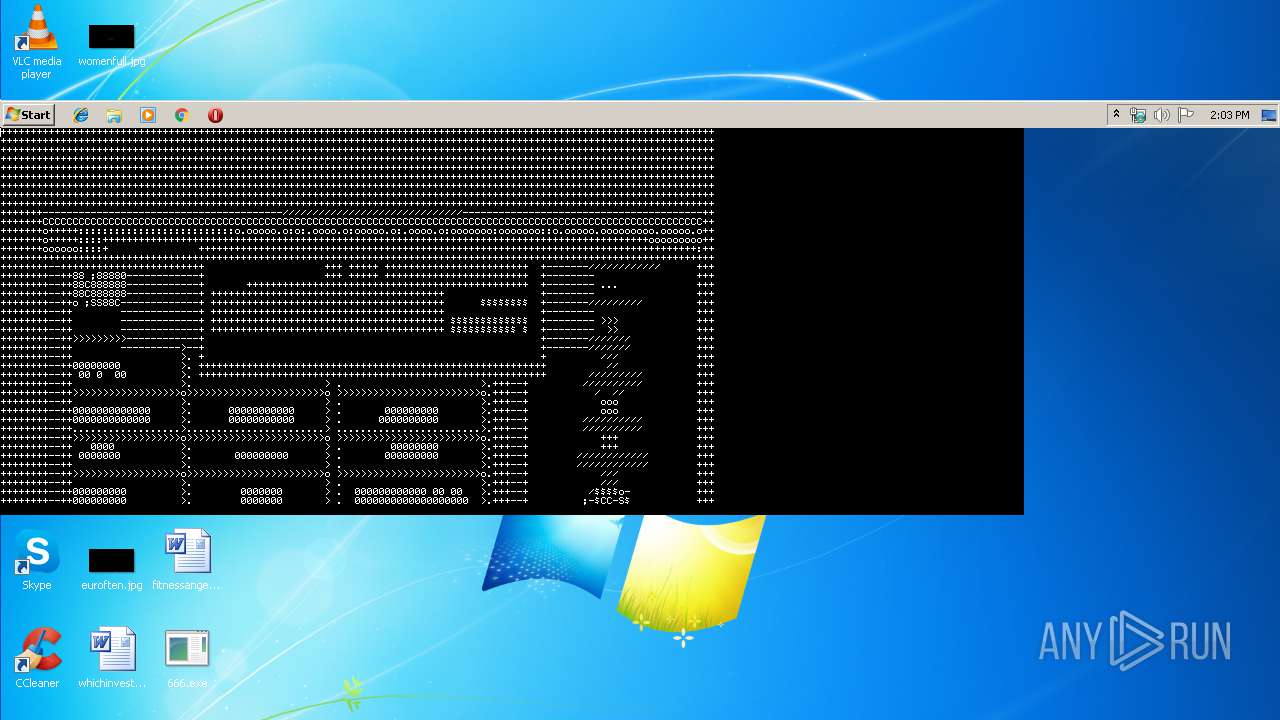
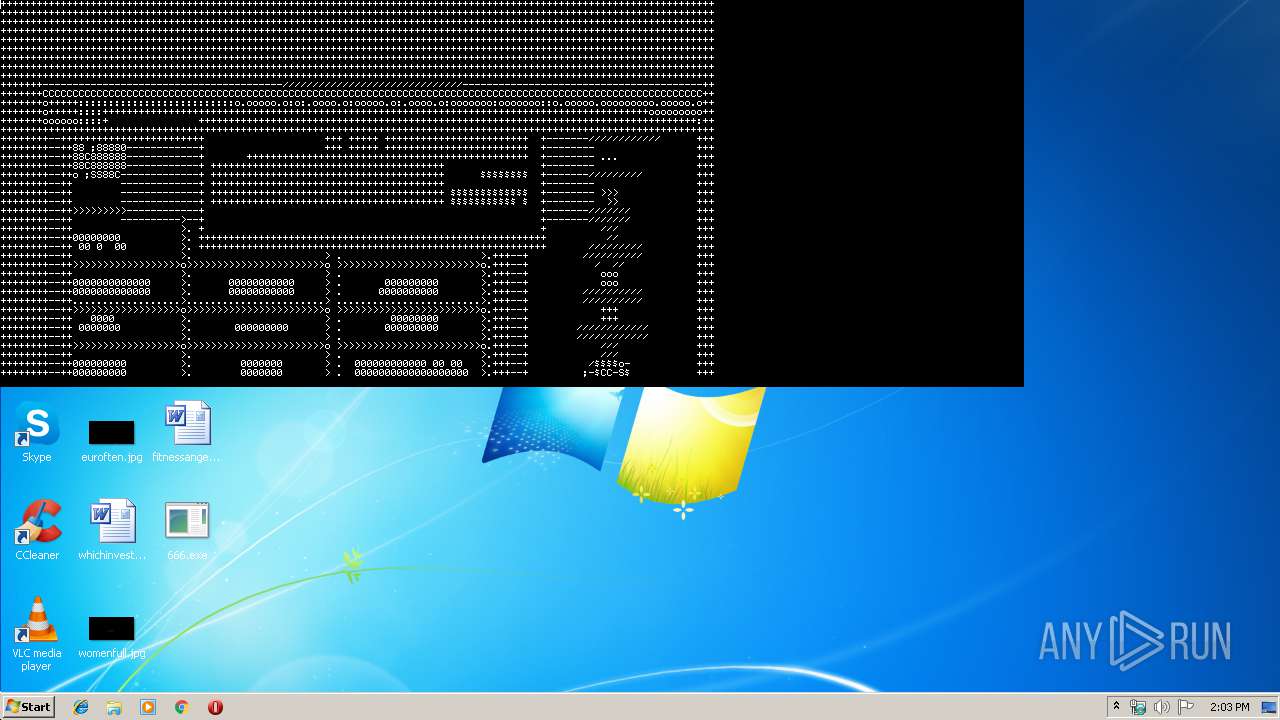
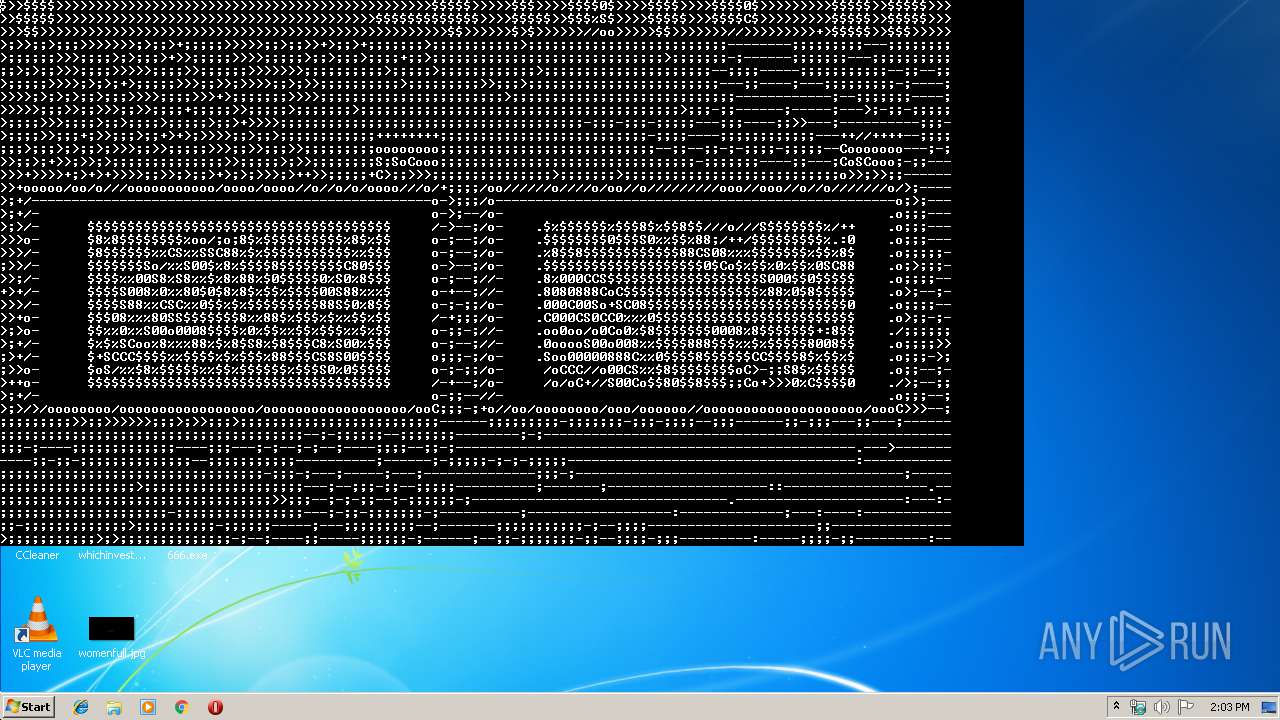
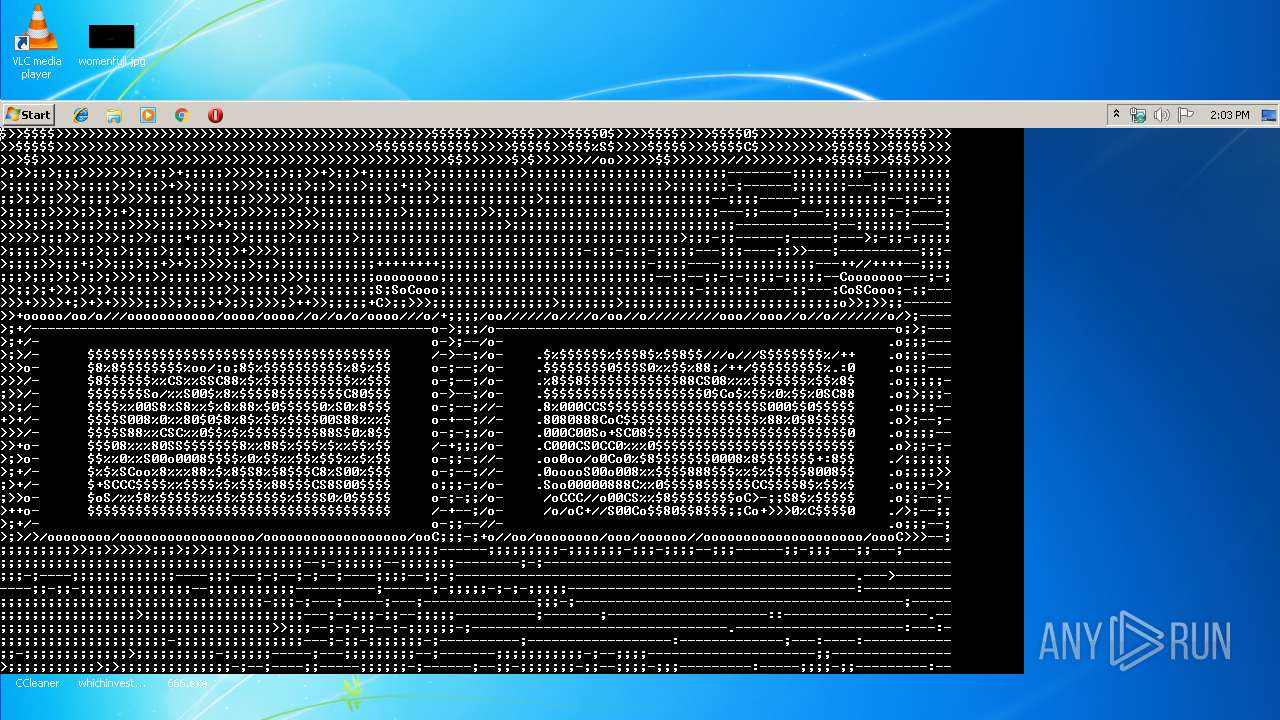
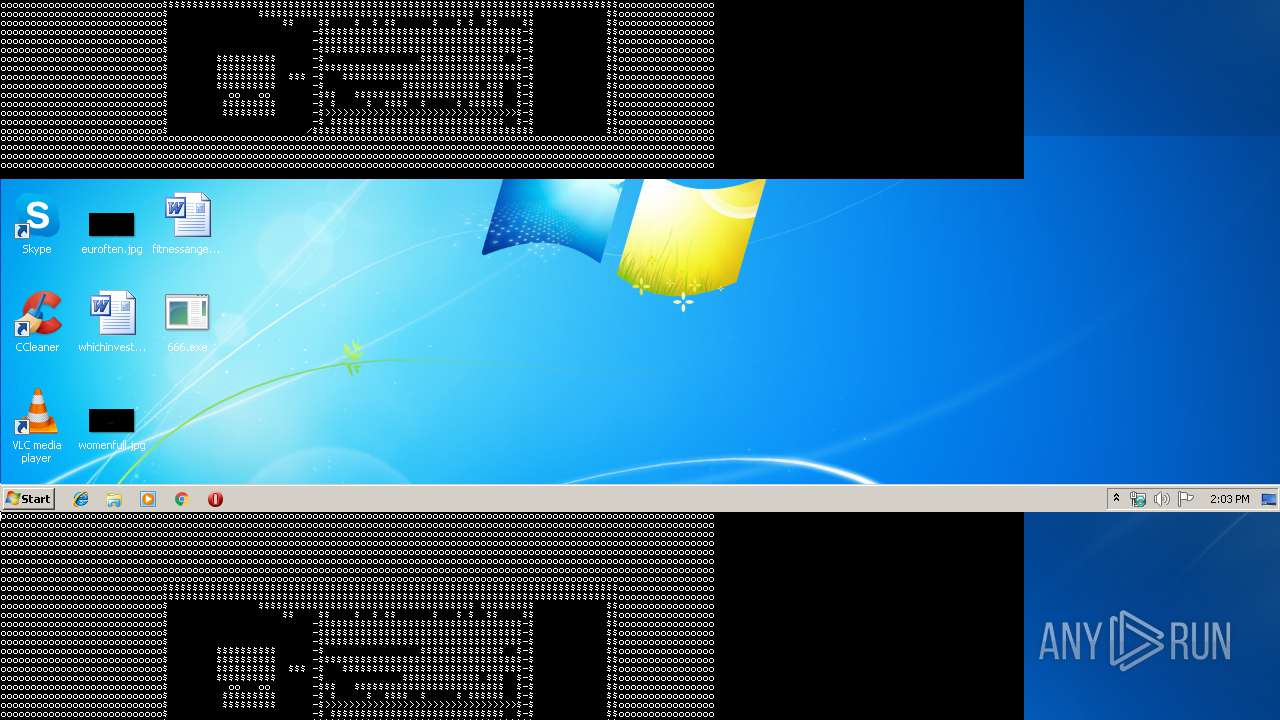
Behavior graph
Click at the process to see the details
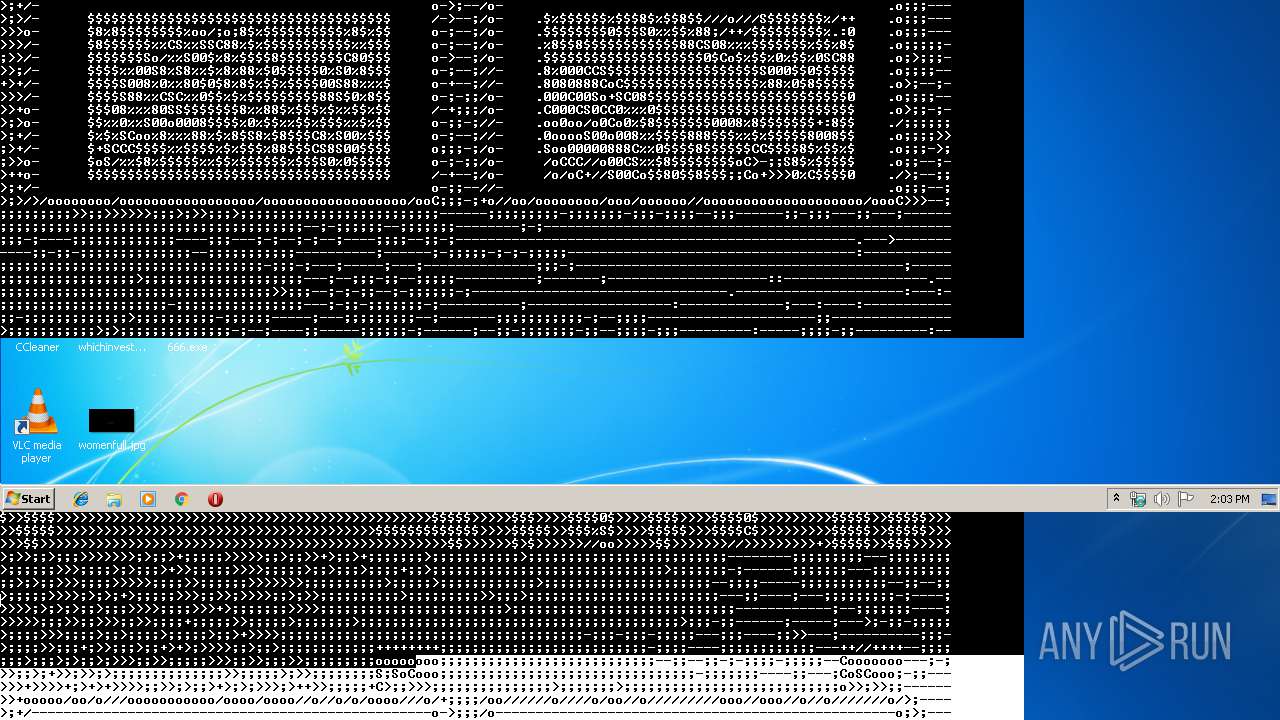
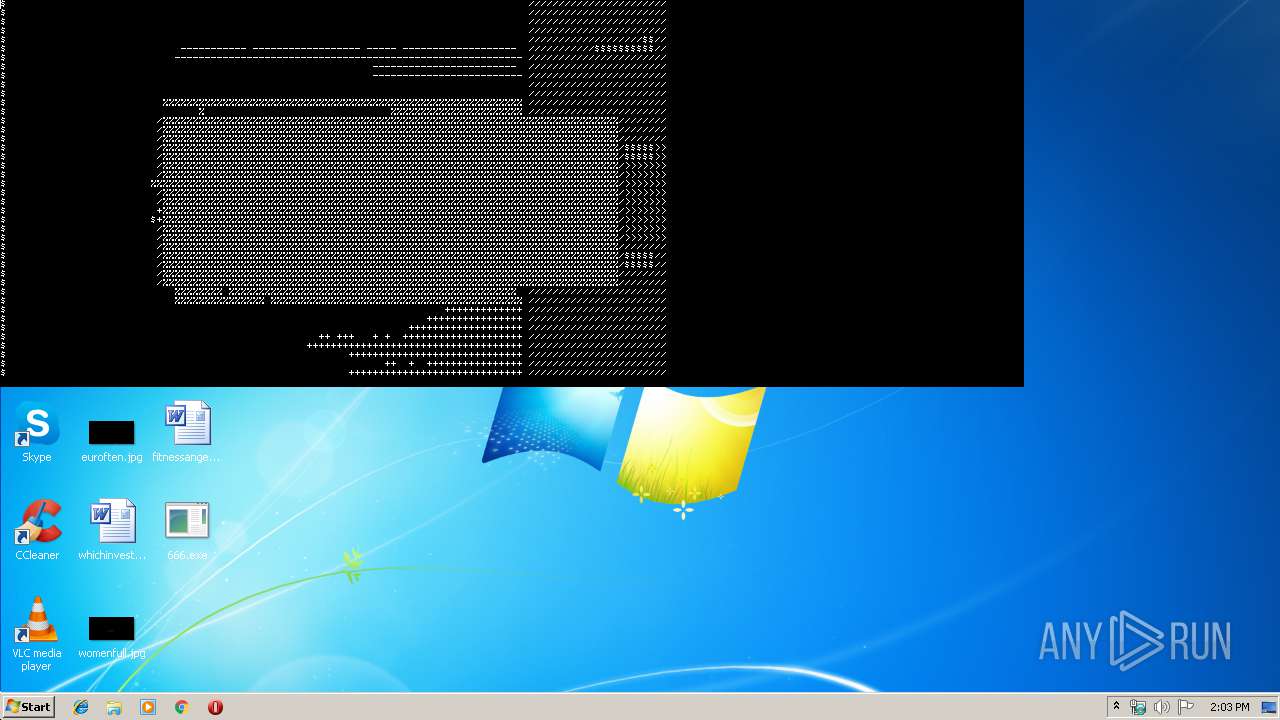
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 3936 | "C:\Users\admin\Desktop\666.exe" | C:\Users\admin\Desktop\666.exe | explorer.exe | ||||||||||||
User: admin Company: Macromedia, Inc. Integrity Level: MEDIUM Description: Macromedia Projector Exit code: 0 Version: 10.1r11 Modules
| |||||||||||||||
Total events
7
Read events
5
Write events
2
Delete events
0
Modification events
| (PID) Process: | (3936) 666.exe | Key: | HKEY_CURRENT_USER\Software\Macromedia\Shockwave 10\uicontrol\sw3dbaddriverlist1 |
| Operation: | write | Name: | |
Value: *2k*savage/ix!^5.12.01.7012$79x=stbnvidiatnt16mb!=4.10.01.9131$o2k=diamondstealthiiis530!=5.12.01.8007-8.30.24$72k=m!=5.00.2180.3711$***=atigraphicsproturbopci(atim64-gx)!^9999.0.0.0$ont=nvidiageforce256!=4.00.1381.0327$****virge!^9999.0.0.0$*9x=ibmthinkpad(cyber9397dvd)!=4.10.01.2173$79x=mach64:ragepro!=4.11.2560$*2k=m!^5.12.01.1200$o9x=intel(r)82810graphicscontroller!=4.12.01.2656$o**=m!^5.12.01.1509$o2k=3dfxvoodooseries!=5.00.2195.0197$ont=3dfxvoodooseries!=4.00.1381.0229$o2k=diamondstealthiiis540!=5.12.01.8007-8.30.24$*9x*permedia2!^4.10.01.2359$****mystique!^9999.0.0.0$*9x*g400!^4.12.1.1710$***=2164w!^9999.0.0.0$*9x=mach64:ragepro!^4.10.1720$ont*3dblasterriva!^4.03.00.2100$ont*nvidia!^4.00.1381.0508$79x*nvidia!^4.12.01.0513$o9x*diamondviperv770!^4.11.01.0402$****g100!^9999.0.0.0$59x*nvidiariva128!=4.10.1713$ont*radeon!^4.3.3109$o2k*voodoobanshee!=5.00.2195.2b$o***permedia3!^4.12.01.2107$o***ragefury!^4.3.139$o***rage128glagp!=4.00$ont*voodoo4!=4.00.1381.0229$o2k*s3inc.savage/mx!^5.12.1.7026$ont*3dfxvoodoo3!^4.00.1381.0391$ont=voodoo55500pci!^4.00.1381.0229$*9x=mach64:ragepro!^4.11.2611$*9x=2064w!^4.10.1682$79x=diamondviperv330!=4.10.01.0014$ont*nvidiarivatnt2!^4.00.1381.0631$*9x*g450!^4.12.1.1709$o***g450!^4.12.01.1799$*9x*xpert@play!^4.10.2237$****trio!^9999.0.0.0$79x*voodooo3!^4.11.01.1204$o9x*voodoo3!^4.11.01.7160$*2k*voodooseries!^5.00.2195.0232$79x*voodoo3!^4.12.01.1225$72k*voodoo3!^5.00.2180.58$o2k=elsagloriasynergy!=5.00.2180.1$72k=elsagloriasynergy!=5.00.2180.1$79x=glintdelta+glintmx!^4.10.0106$79x*rageii!=4.10.2165$59x*rageii!=4.10.2165$*9x=3dlabsoxygengvx1!^4.12.01.2107-0828$59x*cyber9397dvd!^4.11.01.2177$79x=mach64lt!^4.11.2022$79x=mach64gt!^4.11.2474$o9x*atirage128glsdagp!^4.12.6269$o9x*nvidia!=4.12.01.0618$ont*nvidia!=4.00.1381.0618$o2k*nvidia!=5.12.01.0618$***=unknown!=unknown$o9x*nvidia!=4.12.01.0650$59x=mach64gt!^4.03.00.2030$59x=mach64gt!^4.03.00.2030$59x*810chipset!^4.11.01.2506$ | |||
| (PID) Process: | (3936) 666.exe | Key: | HKEY_CURRENT_USER\Software\Macromedia\Shockwave 10\uicontrol\sw3dbaddriverlist2 |
| Operation: | write | Name: | |
Value: *9x*g200!^4.11.01.2519$o9x*g200!=4.12.01.2730$o9x=glintr3.!^4.12.01.2107-0829R$omc=.display_rage128!1.0.1f14/opengl1.1.2$59x=magnum/xpert128/x99/xpert2000(english)!=4.12.6292$59x=magnum/xpert128/x99/xpert2000!=4.13.7078$52k=atiragemobility-pagp(english)!=5.00.2195.4045$52k*ragexl!=5.00.2180.1$52k=neomagicmagicmedia256xl+!^5.38.00$o9x*g400!^4.12.01.1799$ont*g400!^9999.0.0.0$o2k*g400!^9999.0.0.0$ont*nvidia!=4.00.1381.0650$ont*rage128gl!=4.3.40$*2k=s3inc.savage4!^5.12.01.8011$79x*trio3d/2x!^4.11.01.5001$72k*savage/ixdisplaydriver!=5.12.01.7028-7.31.06$ont*prosavagepm133!^4.1024.1010.0010$o2k*prosavagepm133!^5.12.01.1002$59x*3dimage9!=4.10.01.2161$79x*3dimage9!=4.10.01.2161$72k=diamondmultimediafiregl1000pro!=5.00.2180.1$72k=s3graphicsprosavage+utilities!^5.13.01.1010-11.80.20$ | |||
Executable files
11
Suspicious files
0
Text files
0
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3936 | 666.exe | C:\Users\admin\AppData\Local\Temp\TempFolder.aaa\iml32.dll | executable | |
MD5:D89C95B66AC5A34B0E8673E7CBAD7600 | SHA256:10543304C9C908AFB4D365C0C377A285353619171C68569C30692DD32DB252DD | |||
| 3936 | 666.exe | C:\Users\admin\AppData\Local\Temp\TempFolder.aaa\msvcrt.dll | executable | |
MD5:63DA4613383EC70E047B4CD5C48F0B05 | SHA256:D4287AB5E4988DFE99BD54243D50DBE8744094F11FE5F9809A1A6FB9728C2124 | |||
| 3936 | 666.exe | C:\Users\admin\AppData\Local\Temp\TempFolder.aaa\proj.dll | executable | |
MD5:4ABED6167CDA7DCF638903F744B620A5 | SHA256:43DD597EFCFAD738BFAF1275ADF8C41480118910CC88F78B5E857C8B39D4B655 | |||
| 3936 | 666.exe | C:\Users\admin\AppData\Local\Temp\TempFolder.aaa\xtras\DirectImage.x32 | executable | |
MD5:707DA95B26715D8F13218B1BB4A1BEA5 | SHA256:ED64EDA88D300D71A02BCDCB1097DDEDF99F045544C43F800CE792A6818E41EB | |||
| 3936 | 666.exe | C:\Users\admin\AppData\Local\Temp\TempFolder.aaa\xtras\FileIo.x32 | executable | |
MD5:73F5B7572E6D901F3EE3871BFB307FC1 | SHA256:0F0A616518642F786974024866830A6902CCDAC8223E9DCC4A555066FA608659 | |||
| 3936 | 666.exe | C:\Users\admin\AppData\Local\Temp\TempFolder.aaa\xtras\DirectSound.x32 | executable | |
MD5:A79EEF28BCAE9FF5713ACA00AEF71B74 | SHA256:D8CA89C97177464C00323F9AD3E5FD95353CE093706C559DFB63A8A535AB3DAD | |||
| 3936 | 666.exe | C:\Users\admin\AppData\Local\Temp\TempFolder.aaa\xtras\MacroMix.x32 | executable | |
MD5:512604EE1606ED14479BB25E7026AA6F | SHA256:76FCAC0C9CC5B904FBC3C190D6F9D9F14948A4E1C7C9FA1EF535E437D656D41F | |||
| 3936 | 666.exe | C:\Users\admin\AppData\Local\Temp\TempFolder.aaa\xtras\SWADCmpr.x32 | executable | |
MD5:1CCB3ABD1364CCCB67A5C61FC142EB72 | SHA256:DD75853F47A8930B523A19842E1391E10A81AABB4BAA56ECE6FC0E476B2D9AEA | |||
| 3936 | 666.exe | C:\Users\admin\AppData\Local\Temp\TempFolder.aaa\xtras\Mui Dialog.x32 | executable | |
MD5:7C12951D83EAB73A39BA47DA36B56481 | SHA256:67DAFBDE8966B6DA4EB894608CACDEB276788148D03609611536078B766638C0 | |||
| 3936 | 666.exe | C:\Users\admin\AppData\Local\Temp\TempFolder.aaa\dirapi.dll | executable | |
MD5:5A1E0F5938AD41E3AE6BFC118FC57A1E | SHA256:D111EFEA8D3387D8332339C937FC9D2E6992787149A04392C2F77E78561570A9 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report