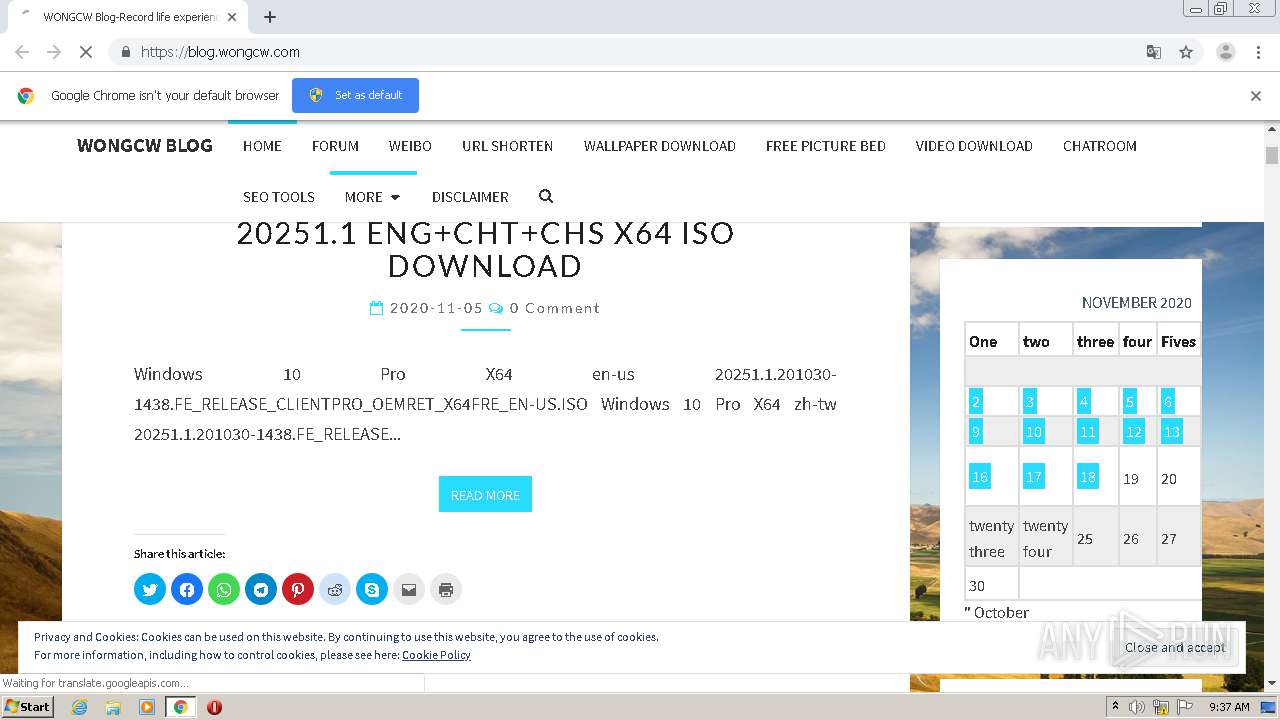
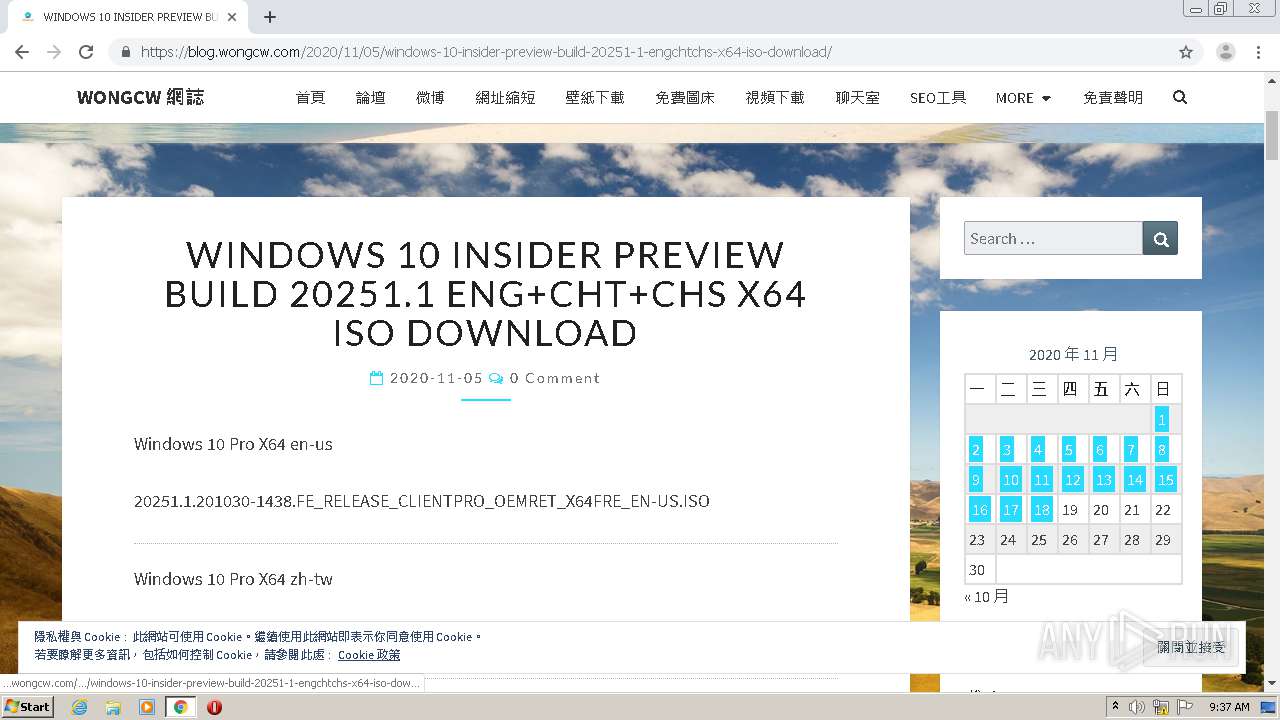
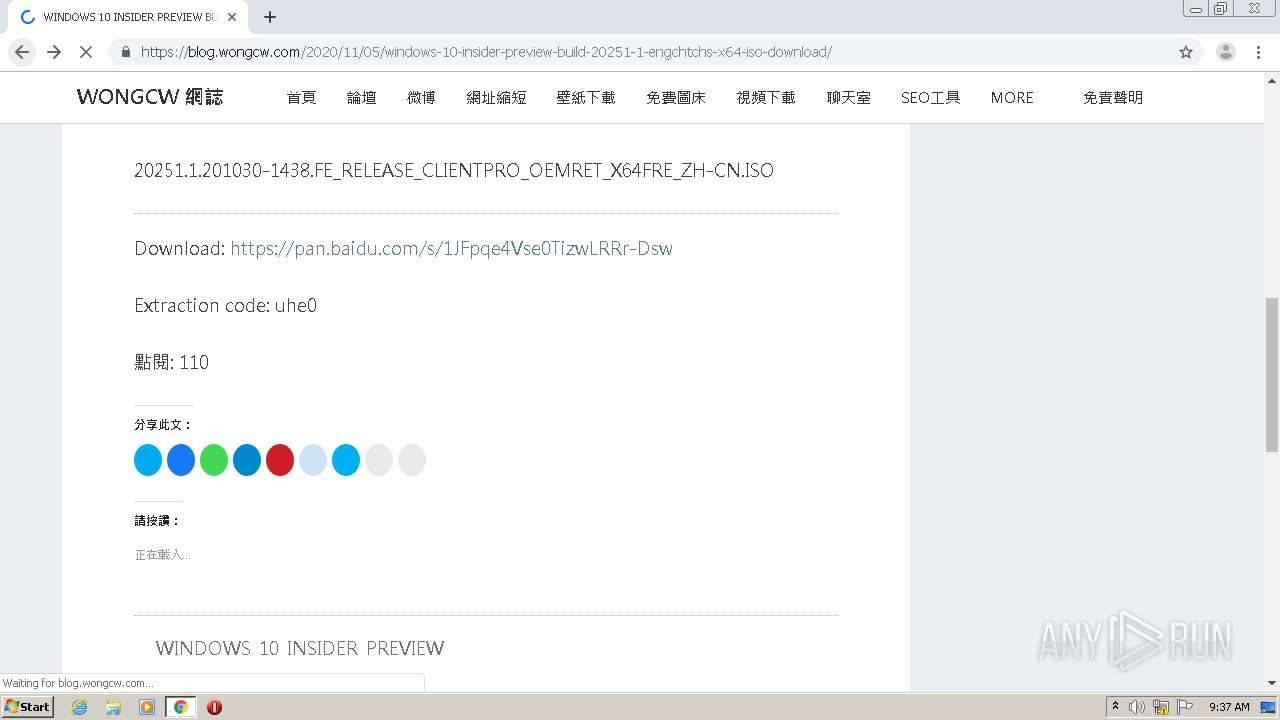
| URL: | http://blog.wongcw.com |
| Full analysis: | https://app.any.run/tasks/85040951-88d9-4c72-983f-4c4c0d969f6e |
| Verdict: | Malicious activity |
| Analysis date: | November 18, 2020, 09:36:25 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
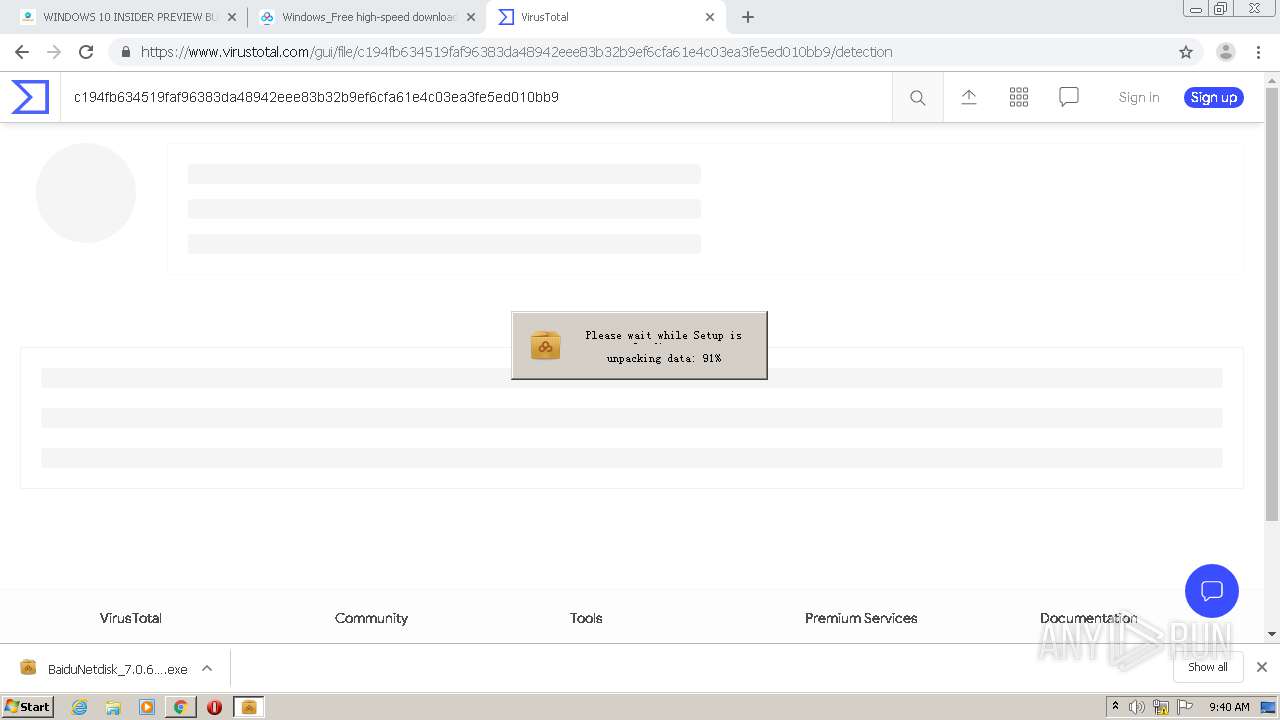
| MD5: | 0BBE851CAEFA7D1D5ABB3F1D2E32FBB1 |
| SHA1: | 606CE9C4C0B39744B2E1D006B96AA67CA0E3C88C |
| SHA256: | 7D29054793FF7DDD8B1971FAFBCABC8D0CF23CA7577C10521357A3A486C518B6 |
| SSDEEP: | 3:N1KcrL52GSyKI:Ccr92GS2 |
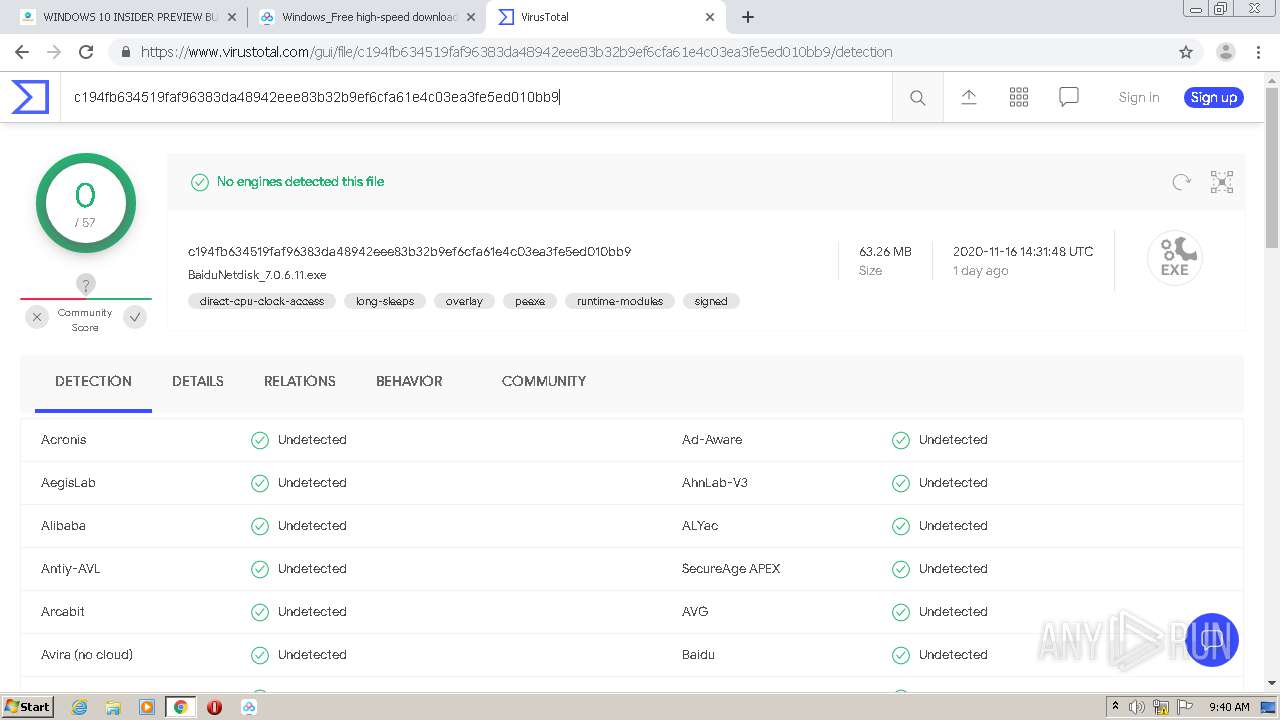
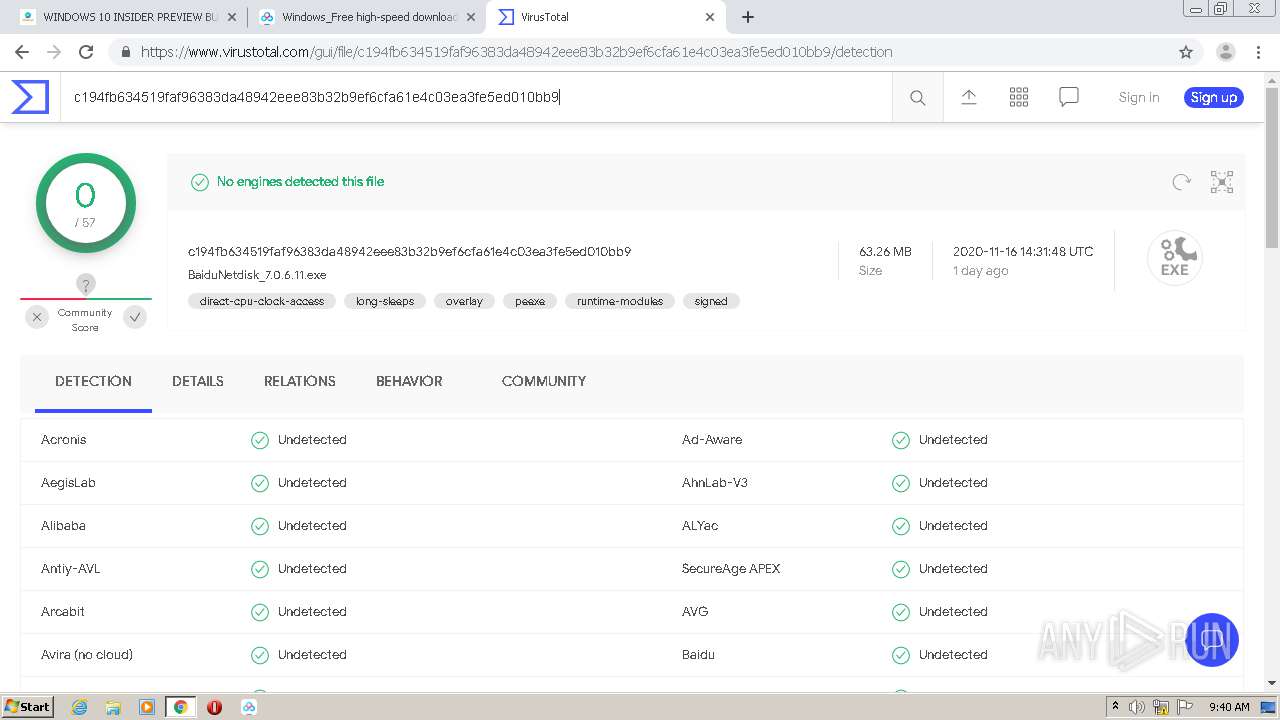
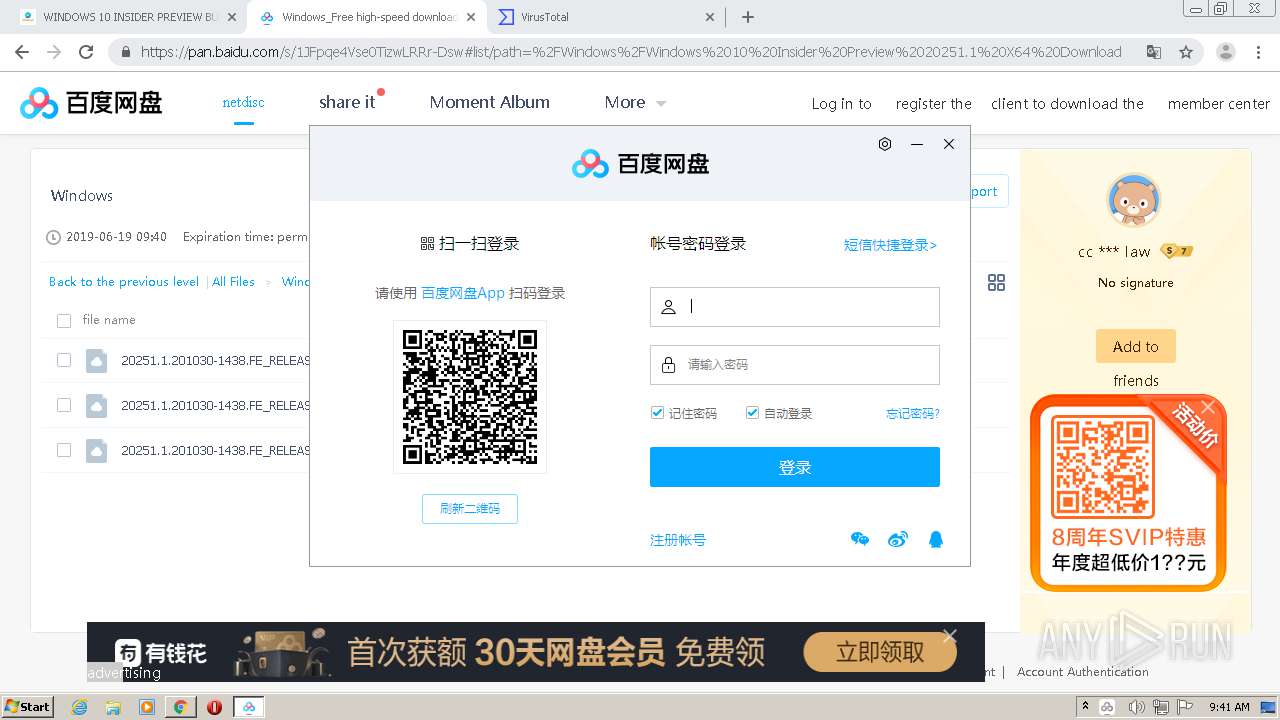
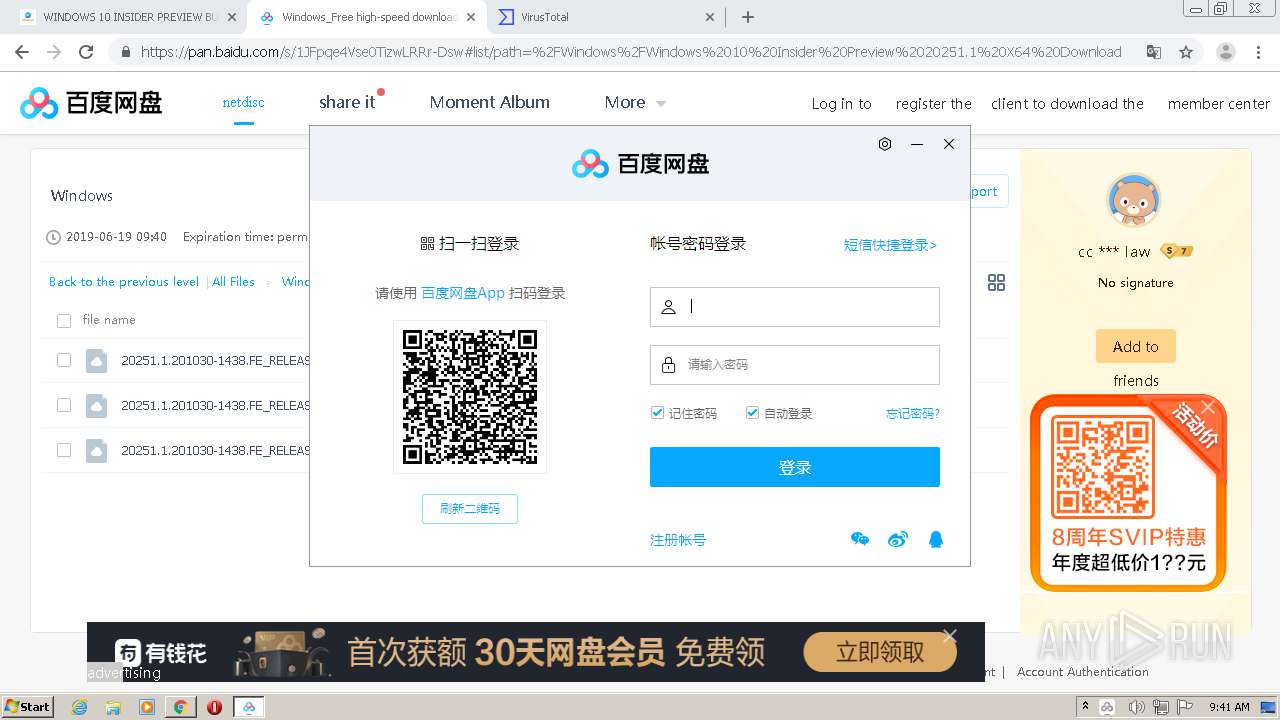
MALICIOUS
Application was dropped or rewritten from another process
- BaiduNetdisk_7.0.6.11.exe (PID: 788)
- BaiduNetdisk_7.0.6.11.exe (PID: 2992)
- BaiduNetdisk.exe (PID: 3952)
- BaiduNetdisk.exe (PID: 3348)
- YunUtilityService.exe (PID: 568)
- YunDetectService.exe (PID: 2800)
- YunDetectService.exe (PID: 1776)
- BaiduNetdiskHost.exe (PID: 3276)
- BaiduNetdisk.exe (PID: 2620)
- BaiduNetdiskHost.exe (PID: 3156)
- YunDetectService.exe (PID: 3272)
- BaiduNetdiskHost.exe (PID: 1852)
- BaiduNetdiskHost.exe (PID: 2812)
- bugReport.exe (PID: 2336)
- bugReport.exe (PID: 1884)
- BaiduNetdiskHost.exe (PID: 3048)
- BaiduNetdiskRender.exe (PID: 1508)
- AutoUpdate.exe (PID: 3376)
Registers / Runs the DLL via REGSVR32.EXE
- BaiduNetdisk_7.0.6.11.exe (PID: 2992)
Loads dropped or rewritten executable
- BaiduNetdisk_7.0.6.11.exe (PID: 2992)
- BaiduNetdisk.exe (PID: 3952)
- YunDetectService.exe (PID: 1776)
- regsvr32.exe (PID: 1940)
- BaiduNetdisk.exe (PID: 3348)
- regsvr32.exe (PID: 3476)
- regsvr32.exe (PID: 1592)
- YunDetectService.exe (PID: 2800)
- BaiduNetdiskHost.exe (PID: 3276)
- BaiduNetdisk.exe (PID: 2620)
- BaiduNetdiskHost.exe (PID: 3156)
- BaiduNetdiskHost.exe (PID: 1852)
- BaiduNetdiskHost.exe (PID: 2812)
- YunDetectService.exe (PID: 3272)
- YunUtilityService.exe (PID: 568)
- bugReport.exe (PID: 2336)
- bugReport.exe (PID: 1884)
- BaiduNetdiskHost.exe (PID: 3048)
- BaiduNetdiskRender.exe (PID: 1508)
Changes the autorun value in the registry
- BaiduNetdisk.exe (PID: 3952)
SUSPICIOUS
Executable content was dropped or overwritten
- chrome.exe (PID: 2568)
- BaiduNetdisk_7.0.6.11.exe (PID: 2992)
Creates files in the user directory
- BaiduNetdisk.exe (PID: 3952)
- BaiduNetdisk_7.0.6.11.exe (PID: 2992)
- BaiduNetdisk.exe (PID: 3348)
- YunDetectService.exe (PID: 2800)
- BaiduNetdisk.exe (PID: 2620)
- BaiduNetdiskHost.exe (PID: 3276)
- BaiduNetdiskHost.exe (PID: 1852)
- BaiduNetdiskHost.exe (PID: 3048)
- BaiduNetdiskRender.exe (PID: 1508)
- AutoUpdate.exe (PID: 3376)
Modifies the open verb of a shell class
- BaiduNetdisk.exe (PID: 3952)
- YunDetectService.exe (PID: 1776)
Creates a software uninstall entry
- BaiduNetdisk_7.0.6.11.exe (PID: 2992)
Creates COM task schedule object
- regsvr32.exe (PID: 3476)
- regsvr32.exe (PID: 1592)
- regsvr32.exe (PID: 1940)
Reads Internet Cache Settings
- YunDetectService.exe (PID: 2800)
- BaiduNetdisk.exe (PID: 3348)
- BaiduNetdisk.exe (PID: 2620)
- AutoUpdate.exe (PID: 3376)
Reads internet explorer settings
- BaiduNetdisk.exe (PID: 3348)
Application launched itself
- bugReport.exe (PID: 1884)
Starts Internet Explorer
- BaiduNetdisk.exe (PID: 3348)
INFO
Application launched itself
- chrome.exe (PID: 2568)
- iexplore.exe (PID: 2724)
Dropped object may contain Bitcoin addresses
- BaiduNetdisk_7.0.6.11.exe (PID: 2992)
- iexplore.exe (PID: 3000)
- AutoUpdate.exe (PID: 3376)
Reads the hosts file
- chrome.exe (PID: 1680)
- chrome.exe (PID: 2568)
- BaiduNetdisk.exe (PID: 3348)
- BaiduNetdisk.exe (PID: 2620)
Reads Internet Cache Settings
- chrome.exe (PID: 2568)
- iexplore.exe (PID: 3000)
- iexplore.exe (PID: 2724)
Reads settings of System Certificates
- chrome.exe (PID: 2568)
- iexplore.exe (PID: 2724)
Manual execution by user
- BaiduNetdisk.exe (PID: 2620)
Changes internet zones settings
- iexplore.exe (PID: 2724)
Creates files in the user directory
- iexplore.exe (PID: 3000)
Reads internet explorer settings
- iexplore.exe (PID: 3000)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
103
Monitored processes
60
Malicious processes
17
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 272 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1040,17007929876243019062,5875373582369945927,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=17714525130414844498 --renderer-client-id=34 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3996 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 544 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1040,17007929876243019062,5875373582369945927,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=5843777788848303634 --renderer-client-id=20 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2916 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 568 | "C:\Users\admin\AppData\Roaming\baidu\BaiduNetdisk\YunUtilityService.exe" --uninstall | C:\Users\admin\AppData\Roaming\baidu\BaiduNetdisk\YunUtilityService.exe | — | BaiduNetdisk_7.0.6.11.exe | |||||||||||
User: admin Integrity Level: HIGH Description: YunUtilityService Exit code: 5 Version: 7.0.6.11 Modules
| |||||||||||||||
| 788 | "C:\Users\admin\Downloads\BaiduNetdisk_7.0.6.11.exe" | C:\Users\admin\Downloads\BaiduNetdisk_7.0.6.11.exe | — | chrome.exe | |||||||||||
User: admin Company: Baidu Integrity Level: MEDIUM Description: BaiduYunguanjia Installer Exit code: 3221226540 Version: 7.0.6.11 Modules
| |||||||||||||||
| 944 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=1040,17007929876243019062,5875373582369945927,131072 --enable-features=PasswordImport --gpu-preferences=KAAAAAAAAADgACAgAQAAAAAAAAAAAGAAAAAAAAAAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --service-request-channel-token=9356896797002071128 --mojo-platform-channel-handle=1000 --ignored=" --type=renderer " /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1012 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1040,17007929876243019062,5875373582369945927,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --instant-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=7910509379894378585 --renderer-client-id=25 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=1608 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1204 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1040,17007929876243019062,5875373582369945927,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=9231319047397441392 --mojo-platform-channel-handle=4080 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1232 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1040,17007929876243019062,5875373582369945927,131072 --enable-features=PasswordImport --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=8789804738069956218 --renderer-client-id=5 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2160 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1252 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1040,17007929876243019062,5875373582369945927,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=1576525968668963059 --renderer-client-id=16 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3276 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1304 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=1040,17007929876243019062,5875373582369945927,131072 --enable-features=PasswordImport --disable-gpu-sandbox --use-gl=disabled --gpu-preferences=KAAAAAAAAADgACAgAQAAAAAAAAAAAGAAAAAAAAAAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --service-request-channel-token=16555113493780077785 --mojo-platform-channel-handle=3888 /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
Total events
4 519
Read events
3 907
Write events
592
Delete events
20
Modification events
| (PID) Process: | (2568) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (2568) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (2568) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (2568) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (2540) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 2568-13250165806605250 |
Value: 259 | |||
| (PID) Process: | (2568) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (2568) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (2568) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (2568) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 3252-13245750958665039 |
Value: 0 | |||
| (PID) Process: | (2568) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
Executable files
92
Suspicious files
227
Text files
228
Unknown types
18
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2568 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\BrowserMetrics\BrowserMetrics-5FB4EB2F-A08.pma | — | |
MD5:— | SHA256:— | |||
| 2568 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\77f938c9-ab3f-42e5-b1c0-1f3769b1a6dd.tmp | — | |
MD5:— | SHA256:— | |||
| 2568 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000048.dbtmp | — | |
MD5:— | SHA256:— | |||
| 2568 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2568 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old~RF127a1a.TMP | text | |
MD5:— | SHA256:— | |||
| 2568 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\BudgetDatabase\LOG.old~RF127a58.TMP | text | |
MD5:— | SHA256:— | |||
| 2568 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\CURRENT | text | |
MD5:— | SHA256:— | |||
| 2568 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\CURRENT~RF127ae5.TMP | text | |
MD5:— | SHA256:— | |||
| 2568 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2568 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old~RF127cd9.TMP | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
17
TCP/UDP connections
169
DNS requests
92
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
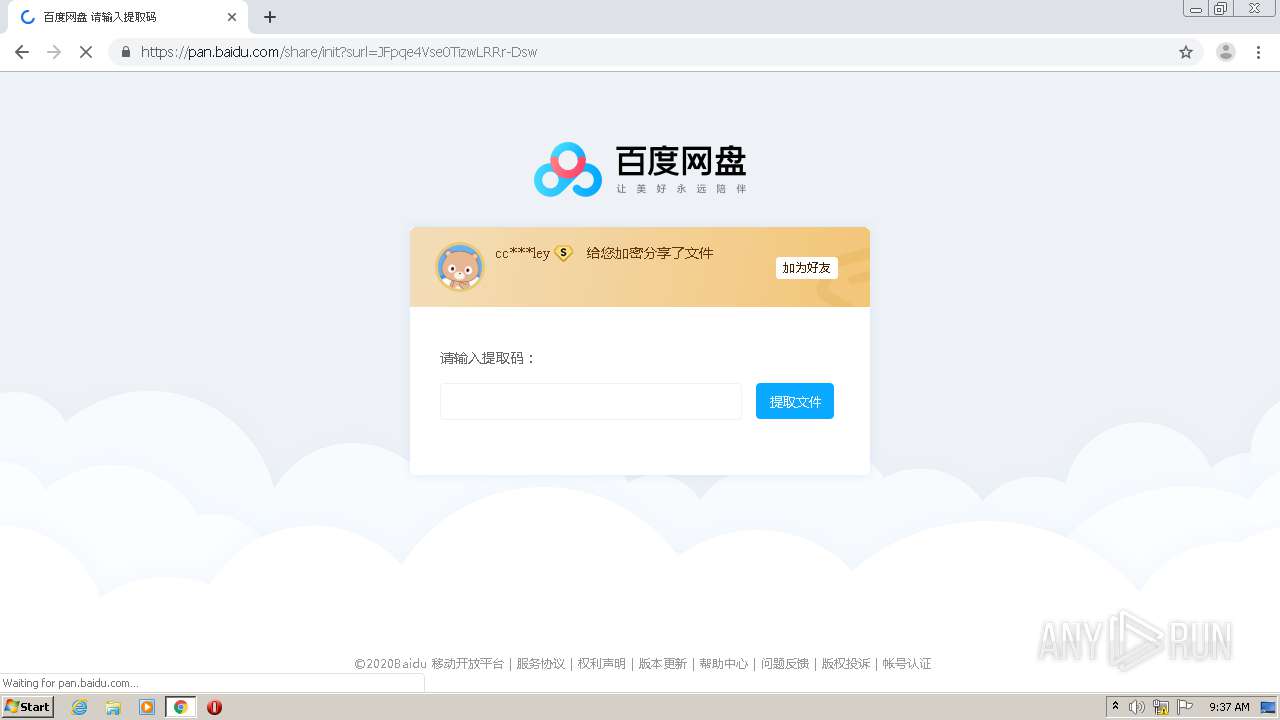
3348 | BaiduNetdisk.exe | GET | 200 | 116.114.98.35:80 | http://issuecdn.baidupcs.com/issue/netdisk/guanggao/ewm-180822.png | CN | image | 10.8 Kb | malicious |
3000 | iexplore.exe | GET | 200 | 104.18.20.226:80 | http://ocsp2.globalsign.com/gsorganizationvalsha2g2/ME0wSzBJMEcwRTAJBgUrDgMCGgUABBQMnk2cPe3vhNiR6XLHz4QGvBl7BwQUlt5h8b0cFilTHMDMfTuDAEDmGnwCDHJYeDZun1boHUGISA%3D%3D | US | der | 1.54 Kb | whitelisted |
— | — | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEA9bw6F2y3ieICDHiTyBZ7Q%3D | US | der | 1.47 Kb | whitelisted |
3348 | BaiduNetdisk.exe | GET | 200 | 104.18.21.226:80 | http://ocsp.globalsign.com/rootr1/MEwwSjBIMEYwRDAJBgUrDgMCGgUABBS3V7W2nAf4FiMTjpDJKg6%2BMgGqMQQUYHtmGkUNl8qJUC99BM00qP%2F8%2FUsCCwQAAAAAAURO8EJH | US | der | 1.49 Kb | whitelisted |
3048 | BaiduNetdiskHost.exe | POST | 200 | 112.80.255.122:80 | http://nj.t.bcsp2p.baidu.com/seed | CN | binary | 96 b | whitelisted |
3000 | iexplore.exe | GET | 200 | 104.18.20.226:80 | http://ocsp2.globalsign.com/gsorganizationvalsha2g2/ME0wSzBJMEcwRTAJBgUrDgMCGgUABBQMnk2cPe3vhNiR6XLHz4QGvBl7BwQUlt5h8b0cFilTHMDMfTuDAEDmGnwCDHJYeDZun1boHUGISA%3D%3D | US | der | 1.54 Kb | whitelisted |
3348 | BaiduNetdisk.exe | GET | 200 | 104.18.20.226:80 | http://ocsp2.globalsign.com/gsorganizationvalsha2g2/ME0wSzBJMEcwRTAJBgUrDgMCGgUABBQMnk2cPe3vhNiR6XLHz4QGvBl7BwQUlt5h8b0cFilTHMDMfTuDAEDmGnwCDBhyuElvTh7HbtMMiw%3D%3D | US | der | 1.54 Kb | whitelisted |
3000 | iexplore.exe | GET | 200 | 104.18.20.226:80 | http://ocsp2.globalsign.com/gsorganizationvalsha2g2/ME0wSzBJMEcwRTAJBgUrDgMCGgUABBQMnk2cPe3vhNiR6XLHz4QGvBl7BwQUlt5h8b0cFilTHMDMfTuDAEDmGnwCDHJYeDZun1boHUGISA%3D%3D | US | der | 1.54 Kb | whitelisted |
1680 | chrome.exe | GET | 301 | 213.246.39.116:80 | http://blog.wongcw.com/ | FR | html | 297 b | unknown |
3000 | iexplore.exe | GET | 200 | 104.18.20.226:80 | http://ocsp2.globalsign.com/gsorganizationvalsha2g2/ME0wSzBJMEcwRTAJBgUrDgMCGgUABBQMnk2cPe3vhNiR6XLHz4QGvBl7BwQUlt5h8b0cFilTHMDMfTuDAEDmGnwCDHJYeDZun1boHUGISA%3D%3D | US | der | 1.54 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1680 | chrome.exe | 213.246.39.116:80 | blog.wongcw.com | Ikoula Net SAS | FR | unknown |
1680 | chrome.exe | 213.246.39.116:443 | blog.wongcw.com | Ikoula Net SAS | FR | unknown |
1680 | chrome.exe | 192.0.77.37:443 | c0.wp.com | Automattic, Inc | US | suspicious |
1680 | chrome.exe | 172.217.18.173:443 | accounts.google.com | Google Inc. | US | whitelisted |
1680 | chrome.exe | 172.217.21.195:443 | fonts.gstatic.com | Google Inc. | US | whitelisted |
1680 | chrome.exe | 192.0.76.3:443 | stats.wp.com | Automattic, Inc | US | suspicious |
1680 | chrome.exe | 107.173.168.19:443 | matomo.wongcw.com | ColoCrossing | US | unknown |
1680 | chrome.exe | 192.0.77.32:443 | s0.wp.com | Automattic, Inc | US | suspicious |
— | — | 104.75.88.209:443 | api.pinterest.com | Akamai Technologies, Inc. | NL | malicious |
1680 | chrome.exe | 104.75.88.209:443 | api.pinterest.com | Akamai Technologies, Inc. | NL | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
blog.wongcw.com |
| unknown |
accounts.google.com |
| shared |
c0.wp.com |
| whitelisted |
fonts.gstatic.com |
| whitelisted |
images.dmca.com |
| whitelisted |
0.gravatar.com |
| whitelisted |
2.gravatar.com |
| whitelisted |
1.gravatar.com |
| whitelisted |
fonts.googleapis.com |
| whitelisted |
i0.wp.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1680 | chrome.exe | Generic Protocol Command Decode | SURICATA STREAM CLOSEWAIT FIN out of window |