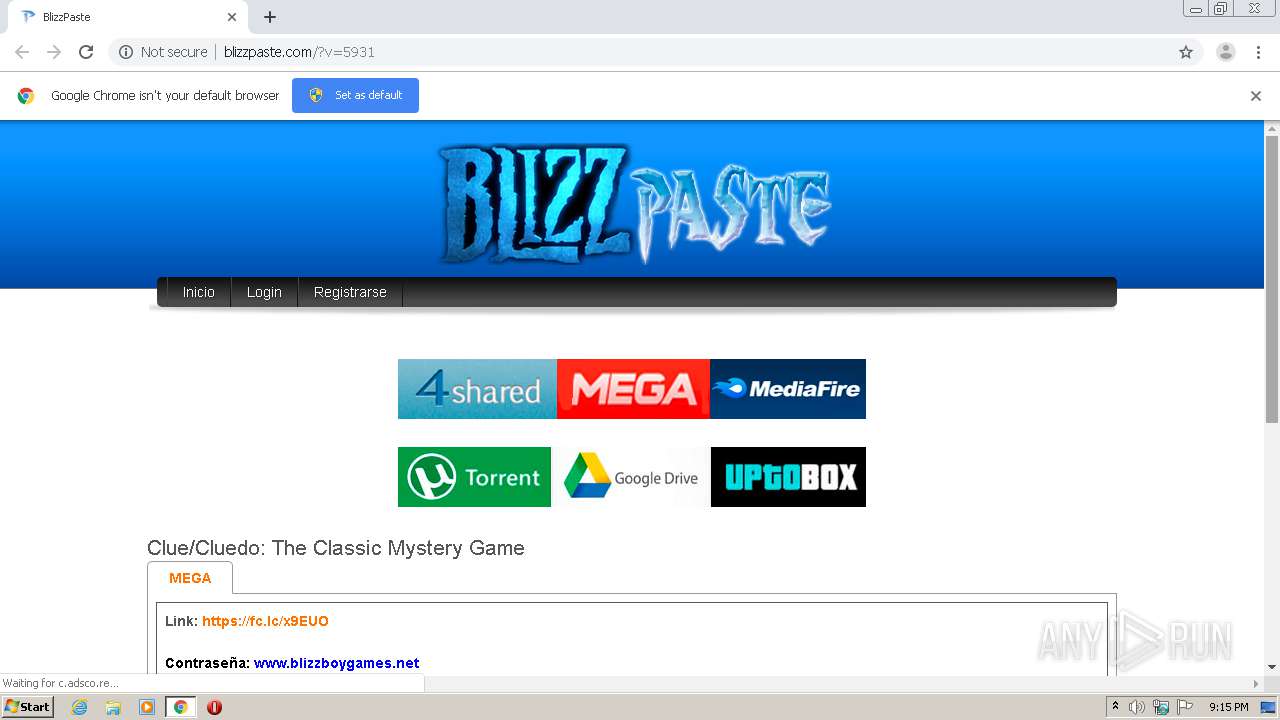
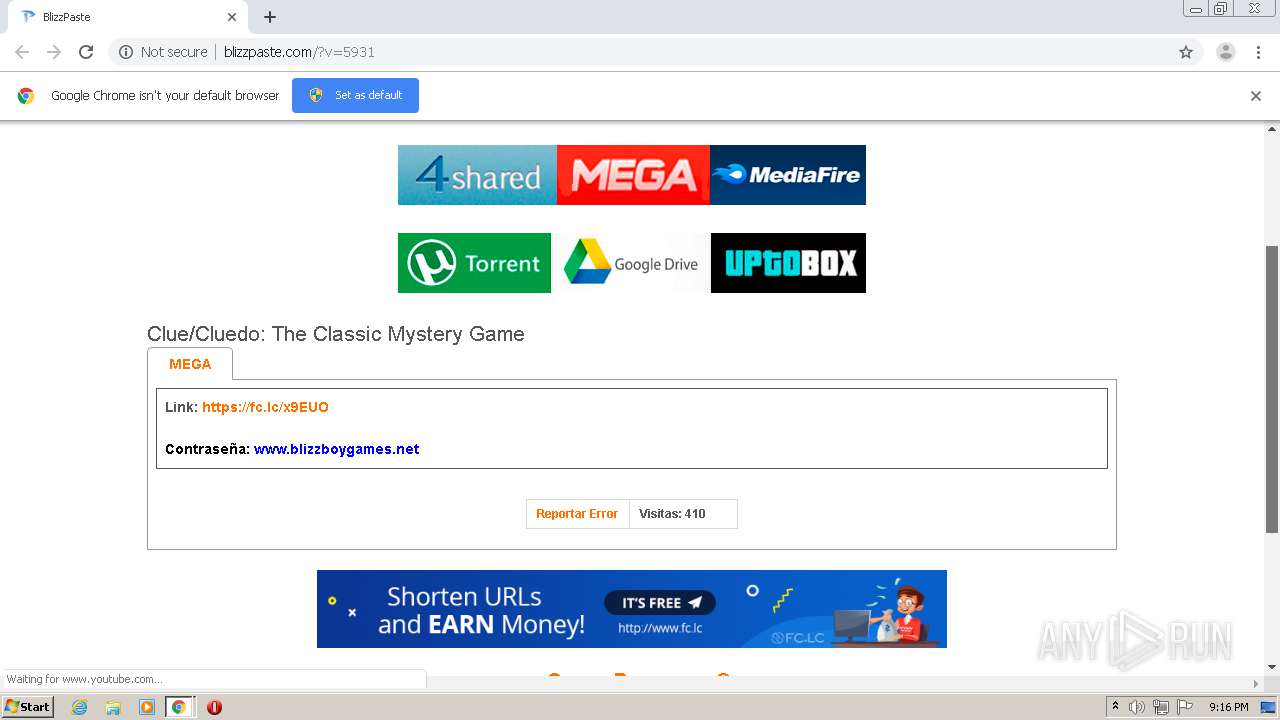
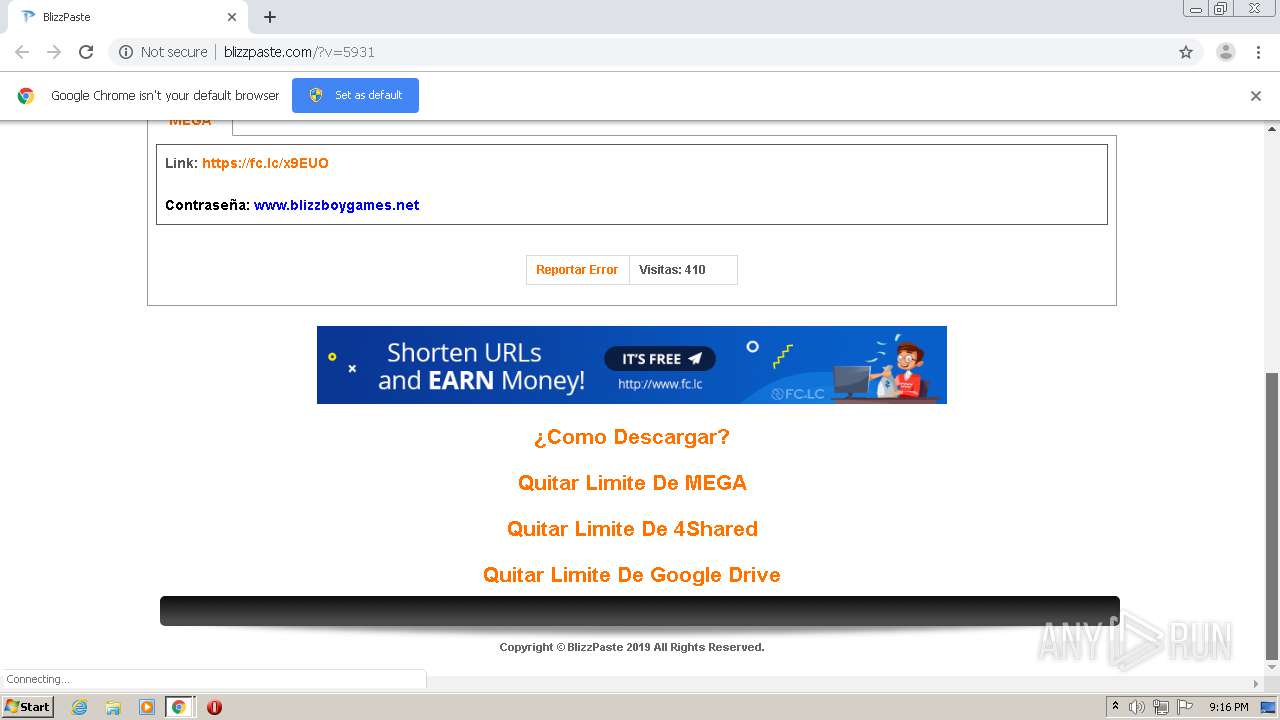
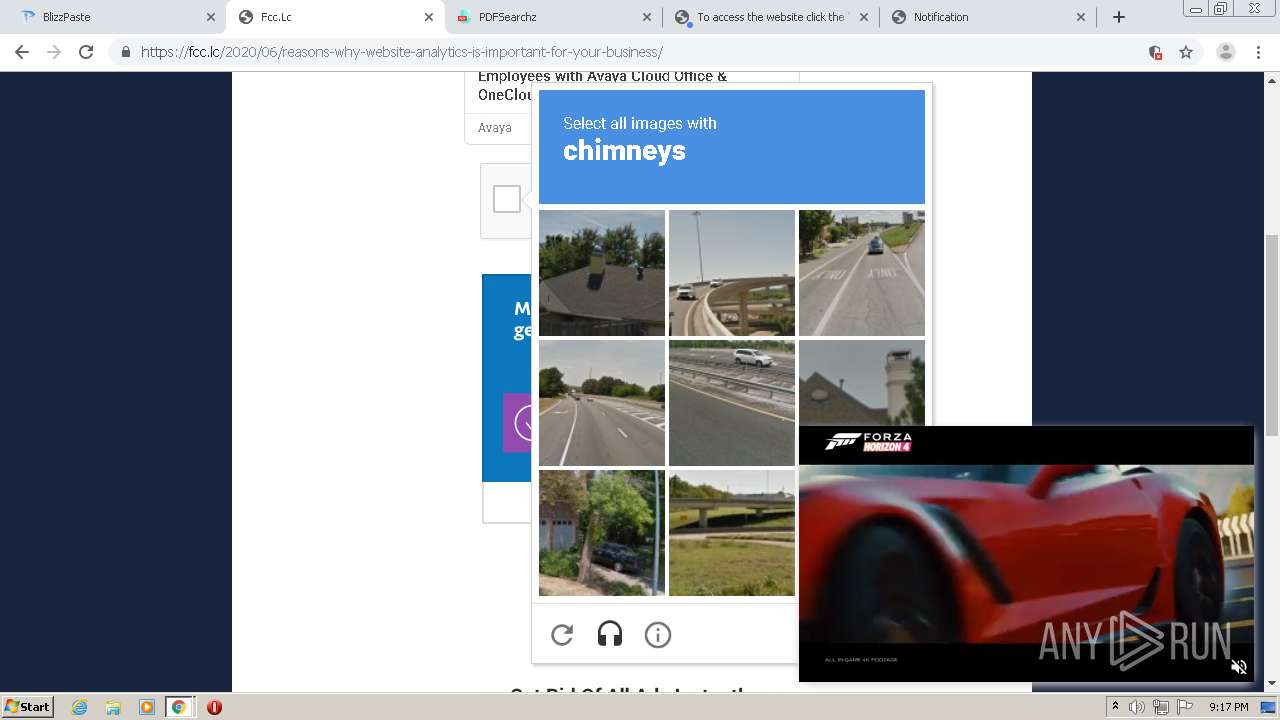
| URL: | http://blizzpaste.com/?v=5931 |
| Full analysis: | https://app.any.run/tasks/8a53c2cf-228f-446e-bf96-814fbdd76181 |
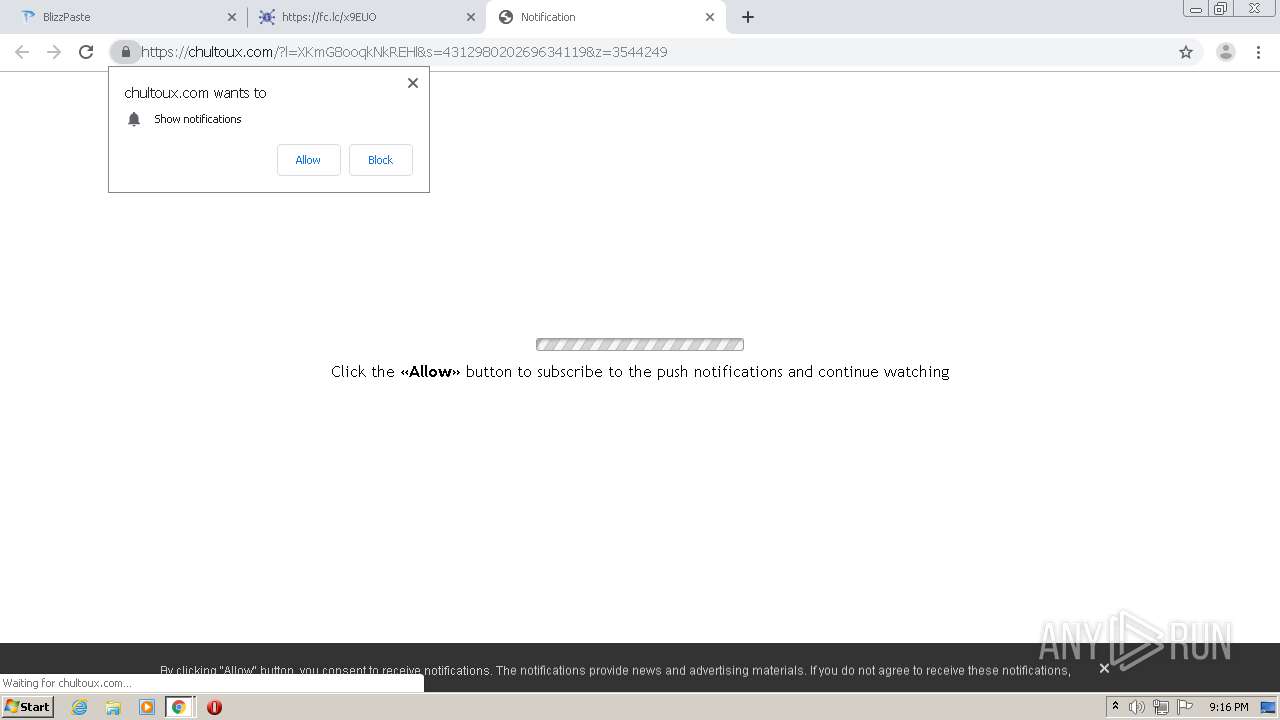
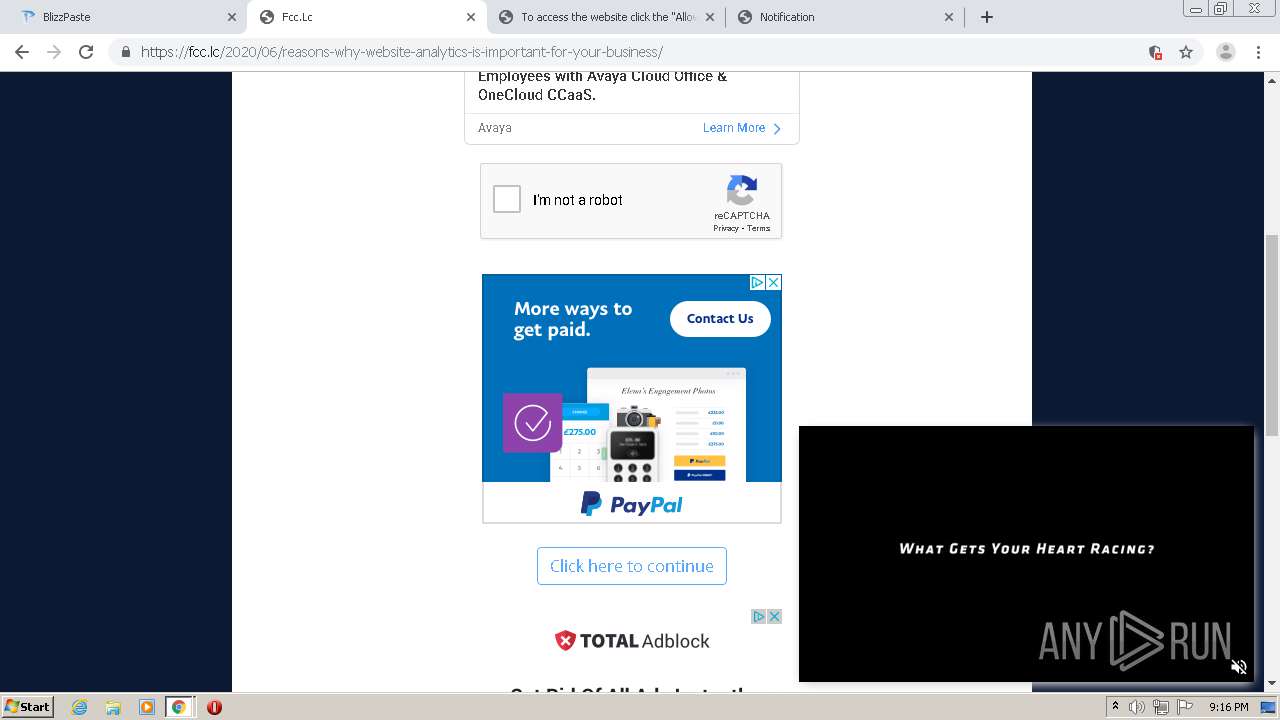
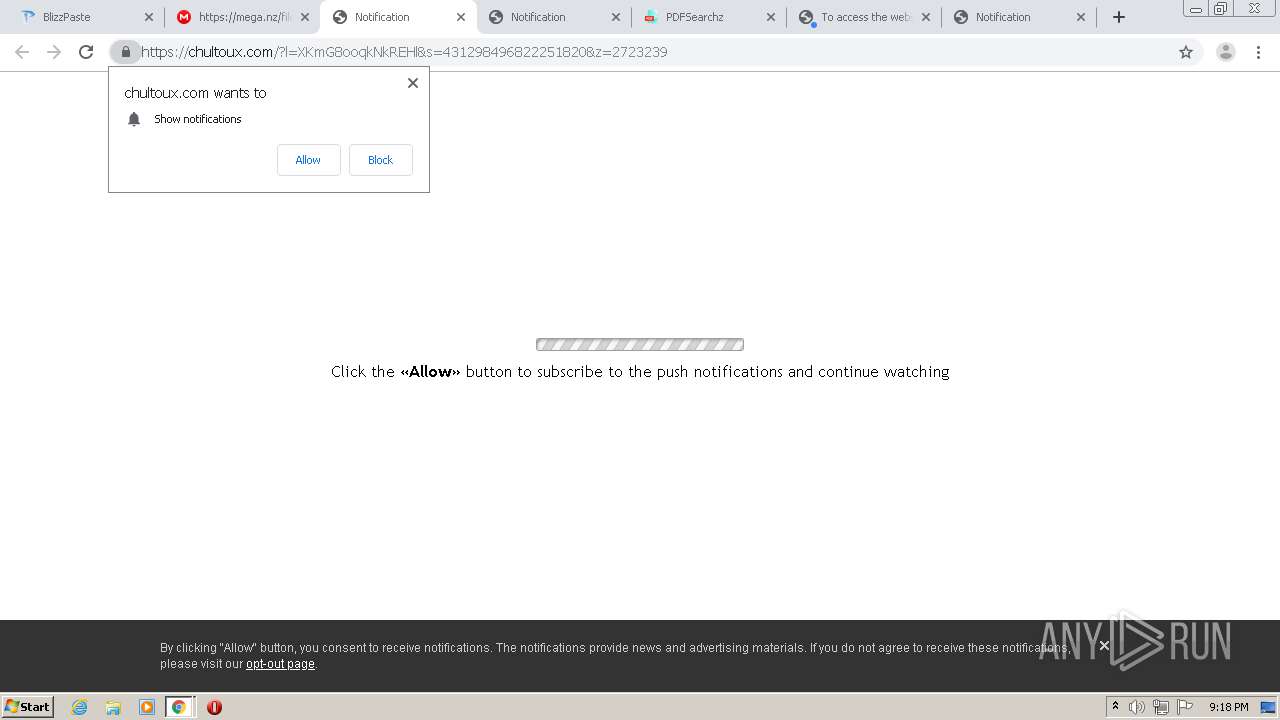
| Verdict: | Malicious activity |
| Analysis date: | June 22, 2021, 20:15:10 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 77915F3580CC48F183A458996BED9C75 |
| SHA1: | 45E8E35EA17291A5D7124C7E947D59CF0D48D081 |
| SHA256: | 7D255077EC5C5D9034879E82153709BBE27955E39089C09089F25E6B92E2CBBB |
| SSDEEP: | 3:N1KcuZXKT:CcuZc |
MALICIOUS
No malicious indicators.SUSPICIOUS
No suspicious indicators.INFO
Application launched itself
- chrome.exe (PID: 2500)
Reads the hosts file
- chrome.exe (PID: 2500)
- chrome.exe (PID: 1940)
Changes settings of System certificates
- chrome.exe (PID: 1940)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
75
Monitored processes
37
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 540 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1004,18334347123548056459,5345543222366670302,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=16685457186571895005 --renderer-client-id=34 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=5472 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 752 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1004,18334347123548056459,5345543222366670302,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=8376476377413427910 --renderer-client-id=21 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=4564 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 928 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1004,18334347123548056459,5345543222366670302,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=7618104488109238742 --renderer-client-id=15 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=728 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 948 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1004,18334347123548056459,5345543222366670302,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=17247435080570962600 --renderer-client-id=32 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=4316 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 956 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1004,18334347123548056459,5345543222366670302,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=17995453451763058388 --renderer-client-id=29 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3912 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1388 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1004,18334347123548056459,5345543222366670302,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=3270024005081157641 --renderer-client-id=23 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=4728 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1396 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1004,18334347123548056459,5345543222366670302,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=96311194301209778 --renderer-client-id=20 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=4008 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1564 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1004,18334347123548056459,5345543222366670302,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=10501215851559795232 --renderer-client-id=28 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=4516 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1628 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1004,18334347123548056459,5345543222366670302,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=18344782566442249507 --renderer-client-id=10 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2676 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1760 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1004,18334347123548056459,5345543222366670302,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=4603648365009110789 --renderer-client-id=33 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2732 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
Total events
700
Read events
605
Write events
92
Delete events
3
Modification events
| (PID) Process: | (2500) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (2500) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (2500) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (2500) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (2500) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (2636) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 2500-13268866529690625 |
Value: 259 | |||
| (PID) Process: | (2500) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (2500) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (2500) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 3252-13245750958665039 |
Value: 0 | |||
| (PID) Process: | (2500) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
Executable files
0
Suspicious files
170
Text files
139
Unknown types
4
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2500 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\BrowserMetrics\BrowserMetrics-60D244E2-9C4.pma | — | |
MD5:— | SHA256:— | |||
| 2500 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\f95b7345-7696-4f17-a212-ddc09f34e9ea.tmp | — | |
MD5:— | SHA256:— | |||
| 2500 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000048.dbtmp | — | |
MD5:— | SHA256:— | |||
| 2500 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old~RF141962.TMP | text | |
MD5:— | SHA256:— | |||
| 2500 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2500 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\BudgetDatabase\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2500 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Feature Engagement Tracker\EventDB\LOG.old~RF141a0e.TMP | text | |
MD5:— | SHA256:— | |||
| 2500 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2500 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2500 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old~RF141cae.TMP | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
13
TCP/UDP connections
174
DNS requests
101
Threats
6
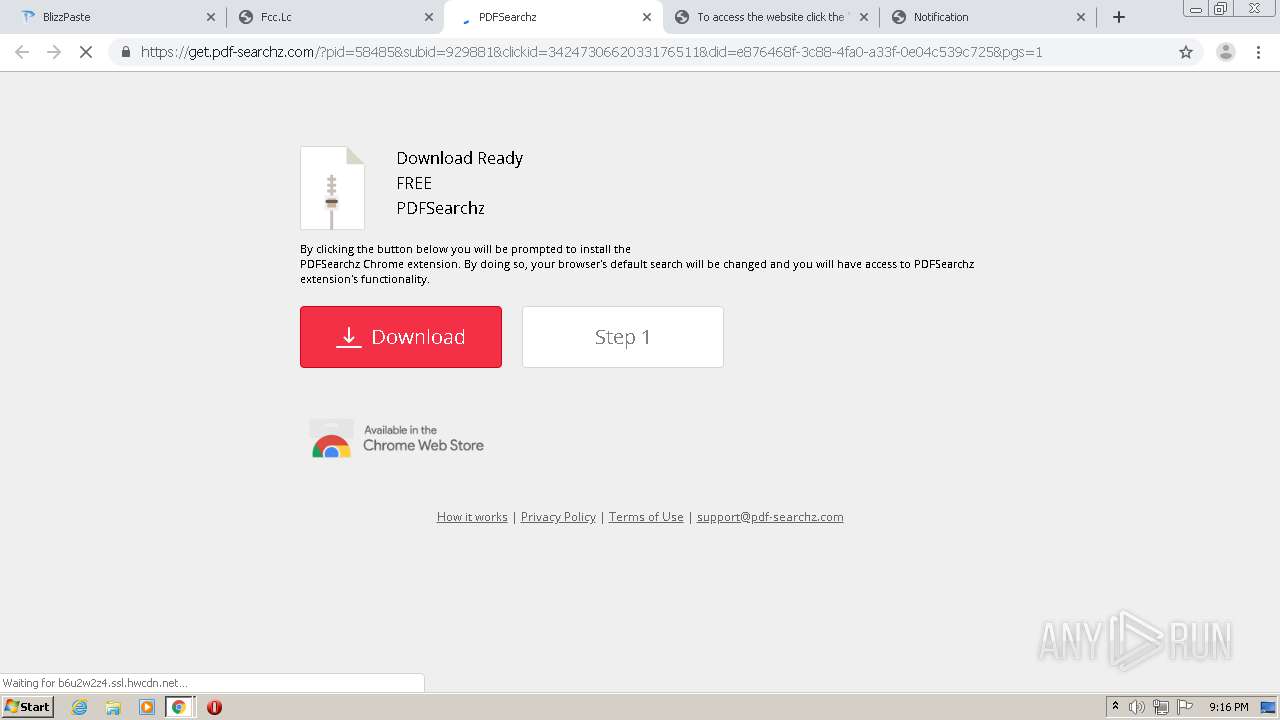
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1940 | chrome.exe | GET | 200 | 104.17.166.186:80 | http://6.adsco.re/ | US | — | — | whitelisted |
1940 | chrome.exe | GET | 200 | 216.21.13.16:80 | http://serve.popads.net/c?_=BAYAYNJE6gFg0kTqgAGBAsAAIEWhx5PLUQgQ24tMsN1hEAjfcn71NpnlGo-h7iN5Zi8UwQBHMEUCIQCzj8unHeGLC-CDVBDhVkhfrleoj9vazk4tIwHNH1rP_QIgOMkxSeYM8JxCL-Vn1Z1CwuPC1IG2tCuTcTwqImkJZOI&v=4&siteId=3894149&minBid=&popundersPerIP=0,0&blockedCountries=&documentRef=&s=1280,720,1,1280,720,0 | US | text | 794 b | whitelisted |
1940 | chrome.exe | POST | 200 | 162.252.214.5:80 | http://adsco.re/p | US | text | 170 b | whitelisted |
1940 | chrome.exe | GET | 200 | 195.181.175.54:80 | http://c1.popads.net/pop.js | DE | html | 9.51 Kb | whitelisted |
1940 | chrome.exe | GET | 200 | 162.252.214.5:80 | http://4.adsco.re/ | US | text | 63 b | whitelisted |
1940 | chrome.exe | GET | 200 | 216.21.13.16:80 | http://serve.popads.net/s?cid=7214915&iuid=1974661260&ts=1624392939&ps=3118036347&pw=409&pl=%21wyoXmwWgmOTjLLaL%2FAV9NhQBrIbDUlwtAcqjCb%2B2vBubGMr4GphR6xVqKYyVZekLhLaqsNV%2B1BTyWf6I6a619dKxY4ovNwQfJajhaDRhC2WxF4idwW3rK1CBtpaJBIJK8lwpE3PtV9v5o46NywczuAtJKZpbuNHrfVkmHu%2BfxZCN1ub1tBjQ%2FHmUUsDGjj4Ap0%2BVkSkwTCM7hFjYQ3aUnucJbMBnDp%2FQWV6OVT3kNq1Zlay1K5o2iiiAHM%2Bldqmysd18j21D%2Bxs9EA3jUjOe1zgzc88PVae1B1EeCQSWk4rLjahA1MOgg6ytmgkPORbW6AwcZmITECxDmEB9Yt%2ByDHOrPRoFPZTLPzXWvJFZW8iX%2FQRaWxt1pLVKP%2BrbyDF0EVkD9G1dUmoLhE8Dipk0Fw%3D%3D&s=1280,720,1,1280,720,0&v=&m= | US | html | 671 b | whitelisted |
1940 | chrome.exe | GET | 200 | 104.17.167.186:80 | http://c.adsco.re/ | US | html | 24.2 Kb | whitelisted |
1940 | chrome.exe | POST | 200 | 162.252.214.5:80 | http://adsco.re/p | US | binary | 20 b | whitelisted |
1940 | chrome.exe | GET | 200 | 142.250.186.138:80 | http://ajax.googleapis.com/ajax/libs/jquery/1.3/jquery.min.js | US | text | 55.9 Kb | whitelisted |
1940 | chrome.exe | GET | 200 | 104.18.21.226:80 | http://secure2.alphassl.com/cacert/gsalphasha2g2r1.crt | US | der | 1.08 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1940 | chrome.exe | 185.66.140.13:80 | blizzpaste.com | NForce Entertainment B.V. | NL | unknown |
1940 | chrome.exe | 172.217.23.45:443 | accounts.google.com | Google Inc. | US | unknown |
1940 | chrome.exe | 142.250.186.138:80 | ajax.googleapis.com | Google Inc. | US | whitelisted |
1940 | chrome.exe | 185.66.140.13:443 | blizzpaste.com | NForce Entertainment B.V. | NL | unknown |
1940 | chrome.exe | 142.250.186.168:443 | www.googletagmanager.com | Google Inc. | US | suspicious |
1940 | chrome.exe | 142.250.185.138:443 | safebrowsing.googleapis.com | Google Inc. | US | whitelisted |
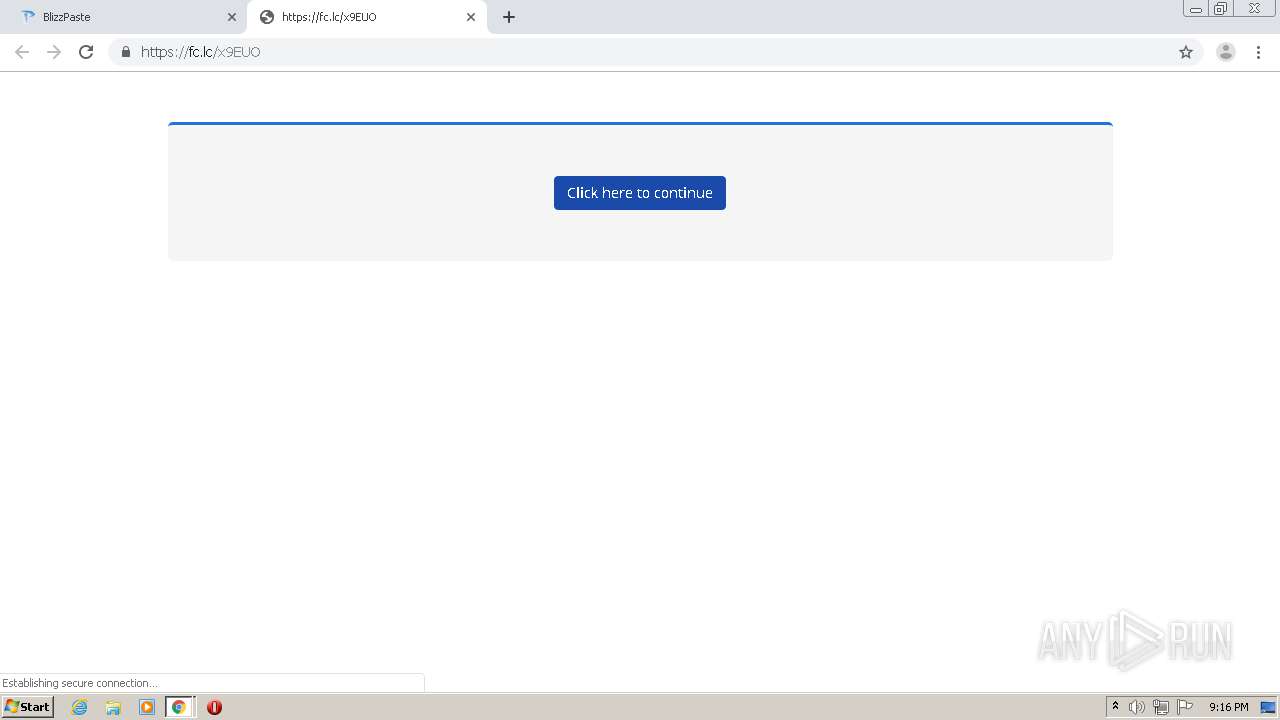
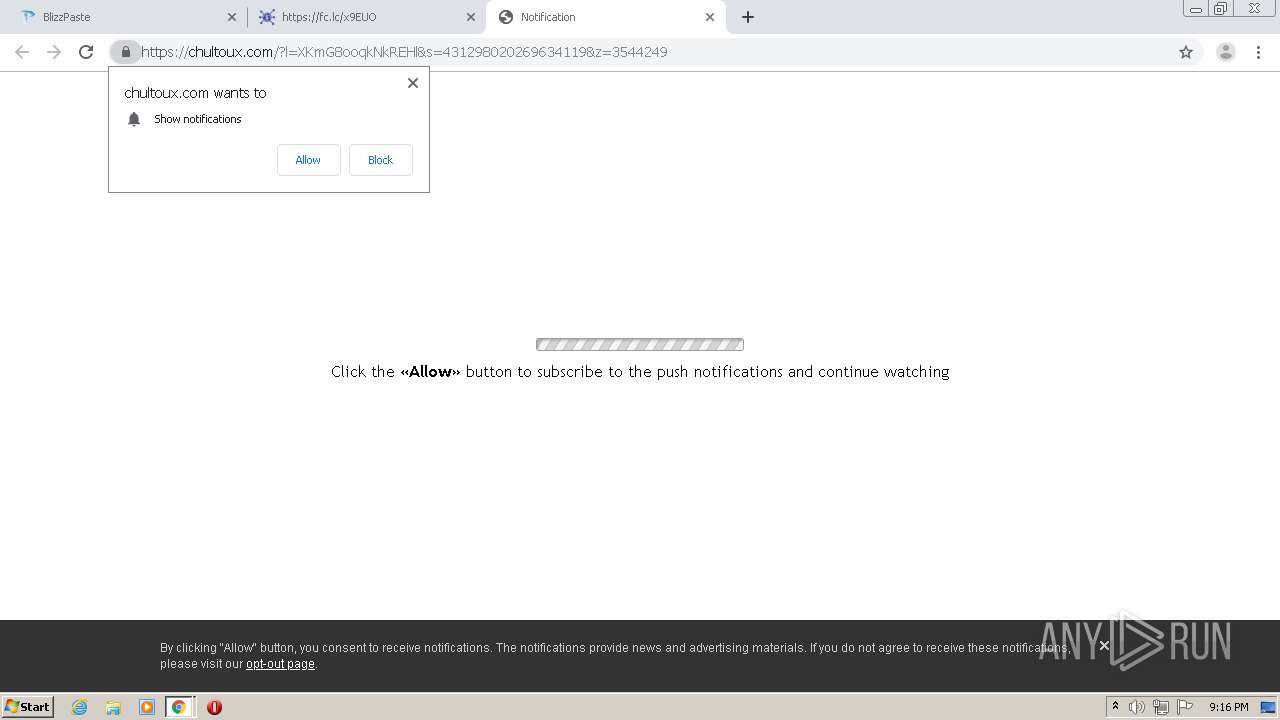
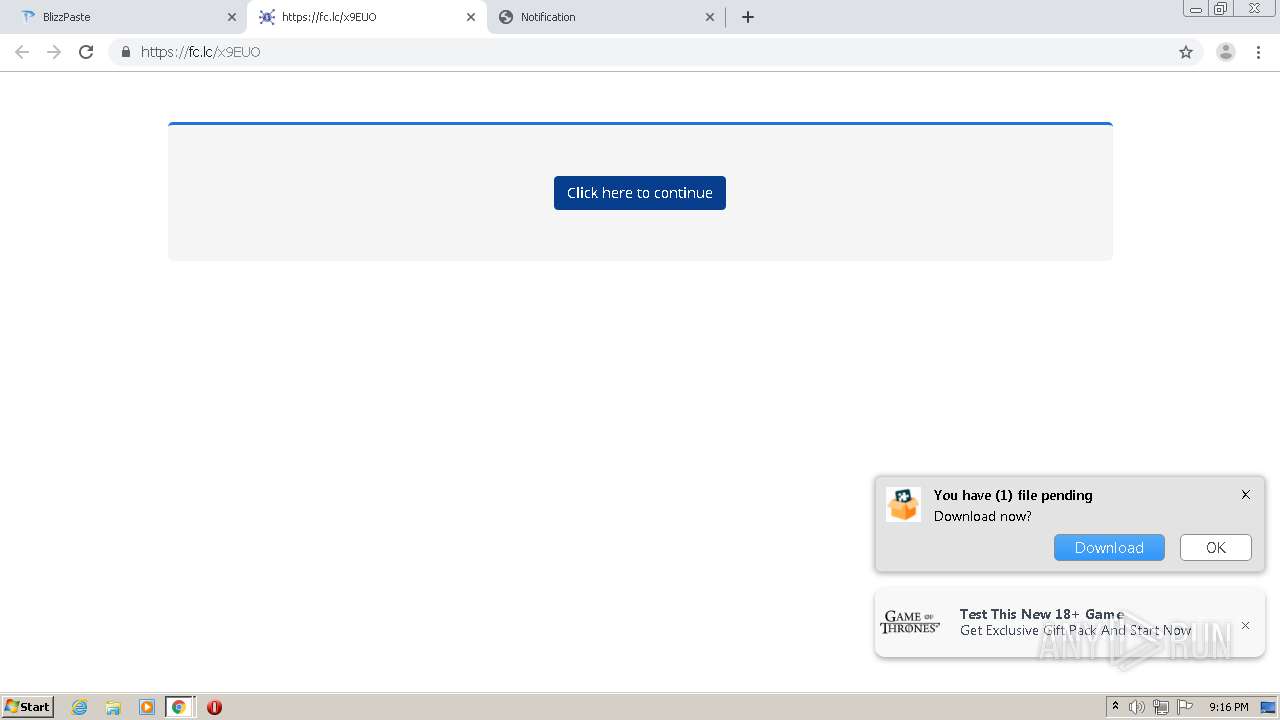
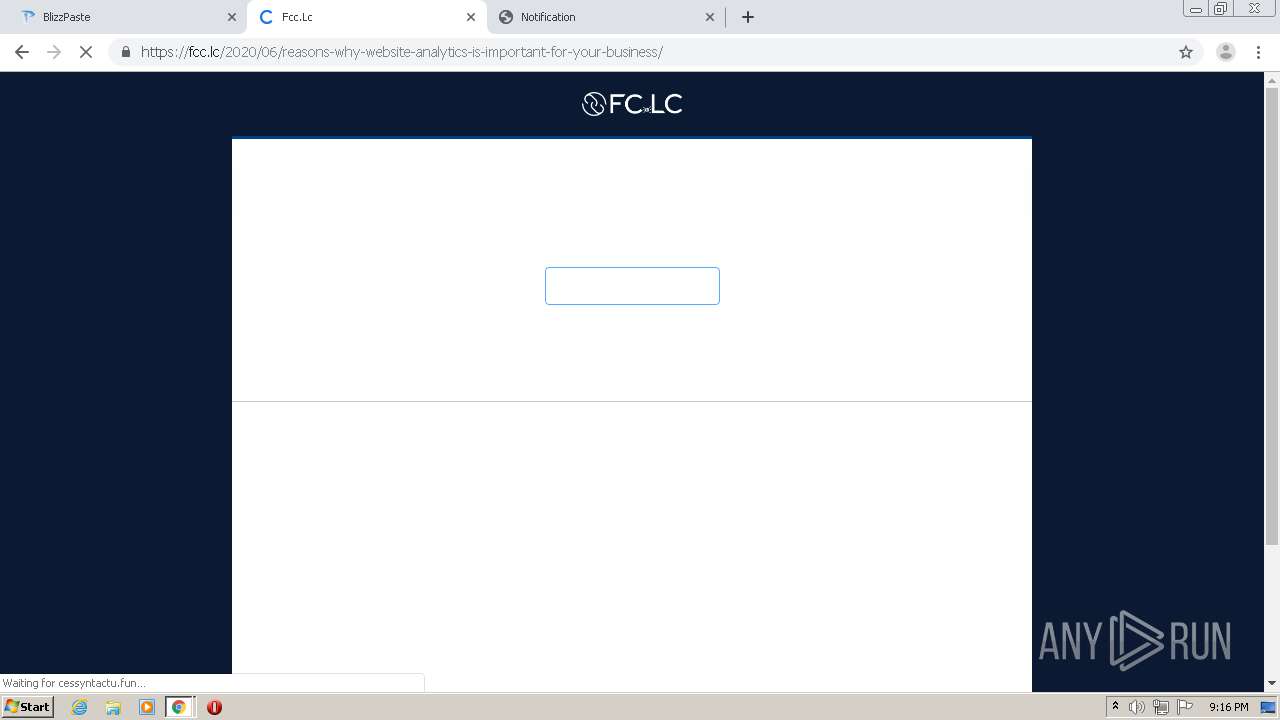
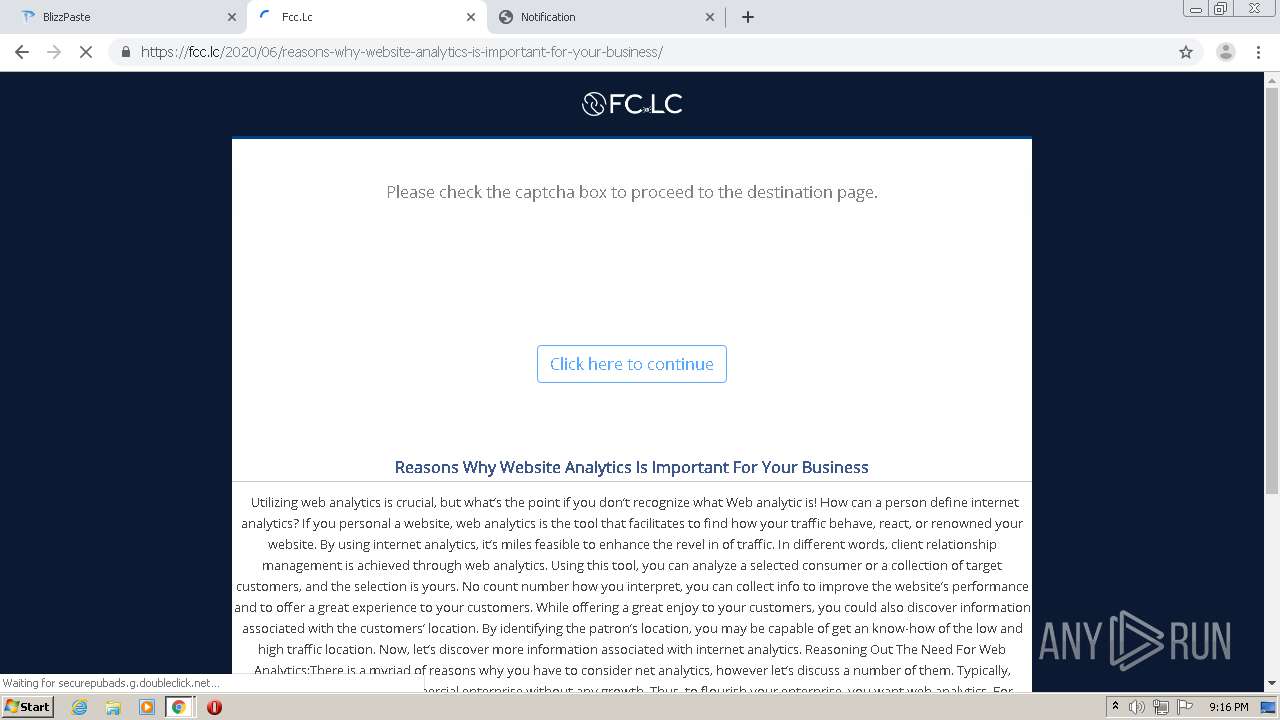
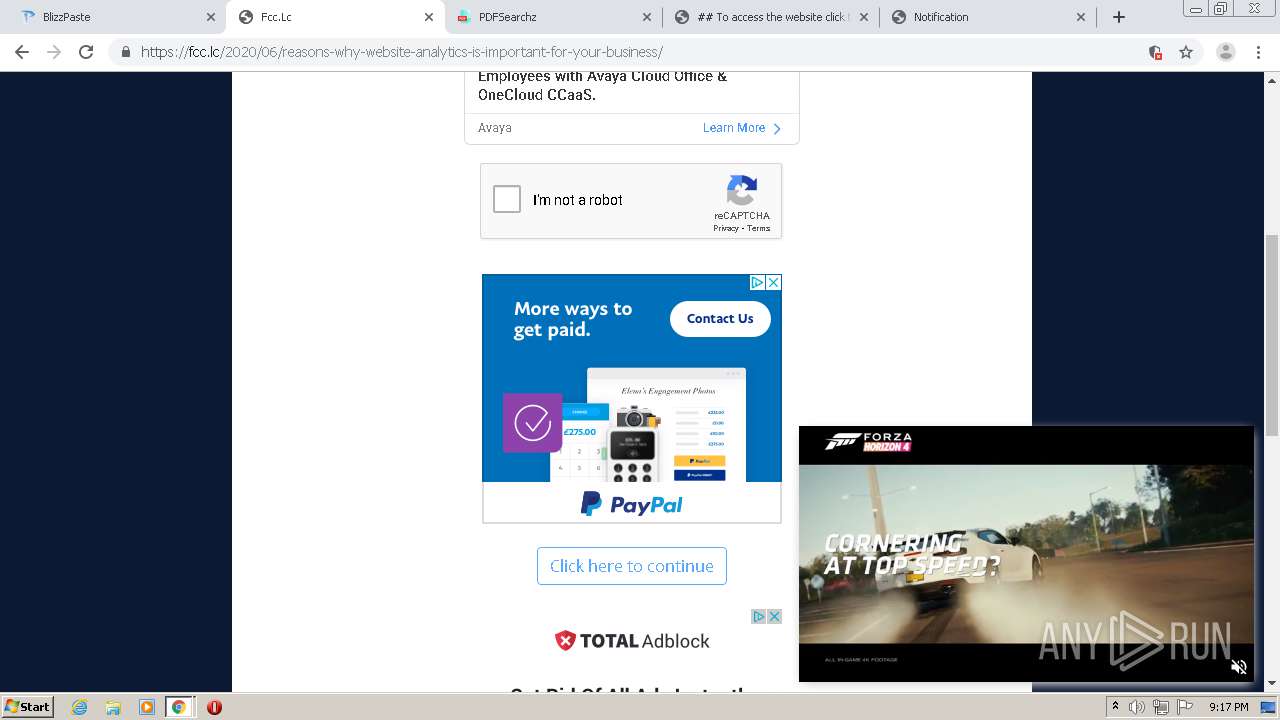
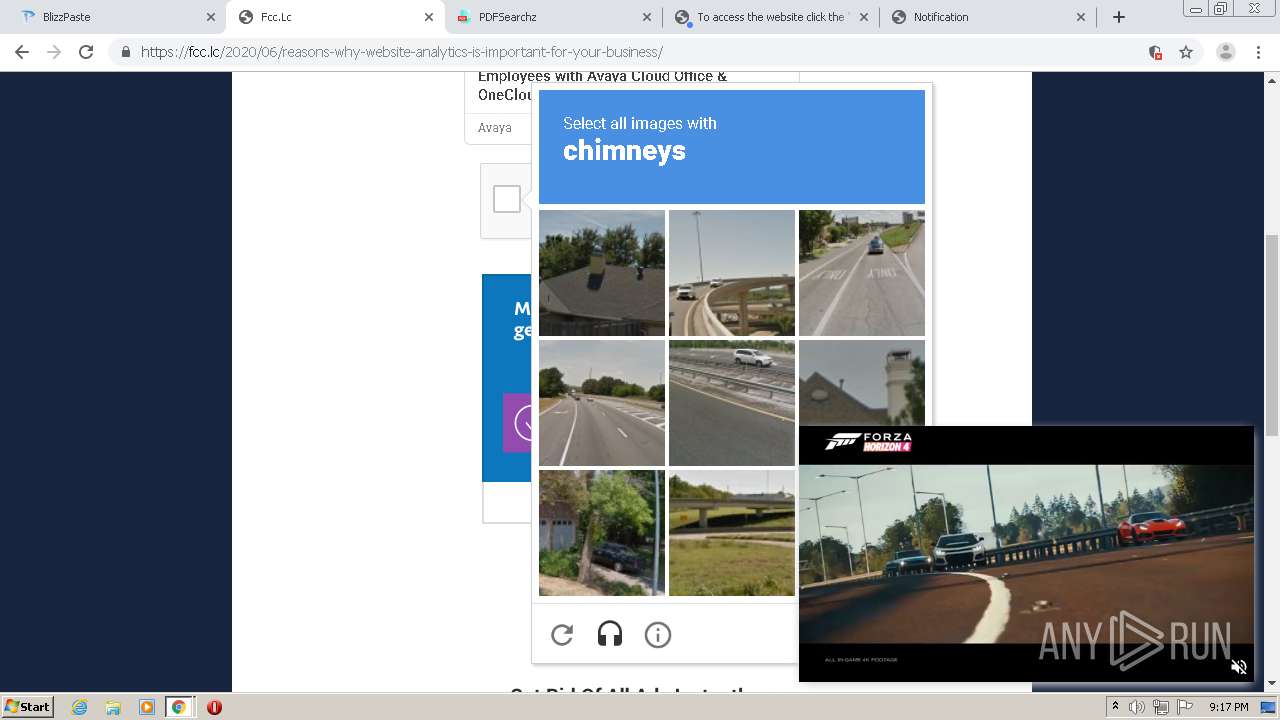
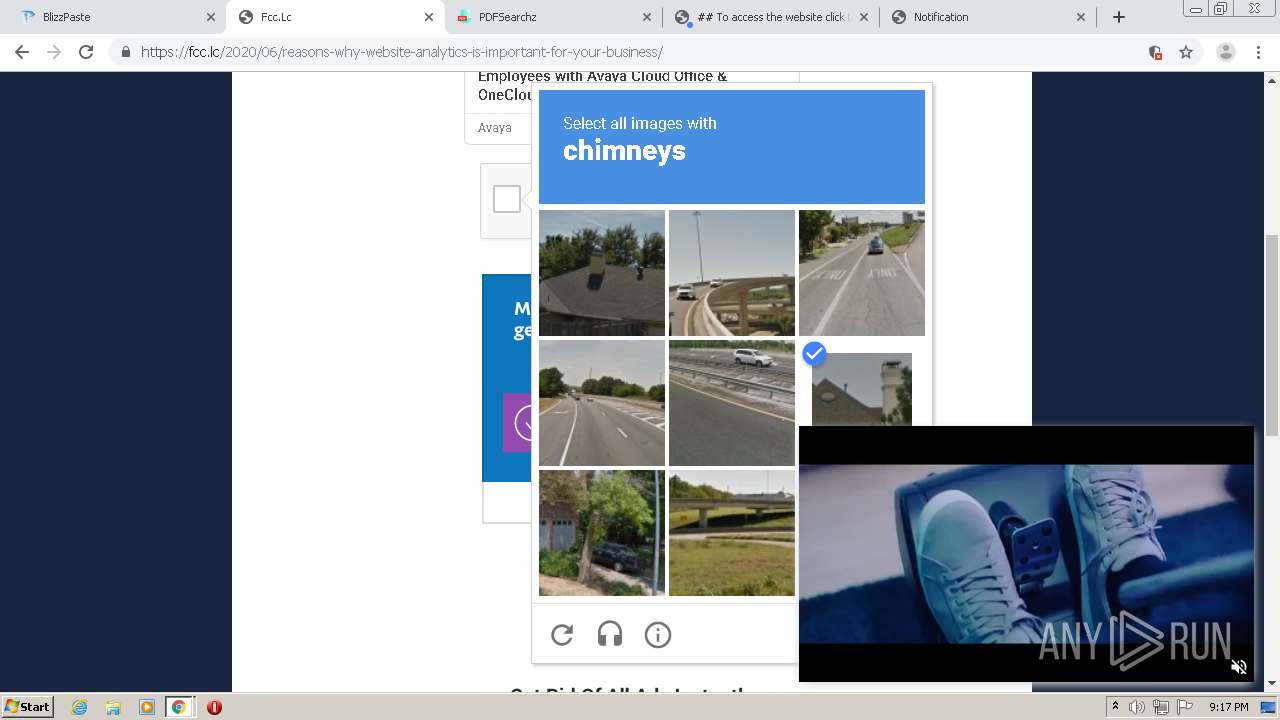
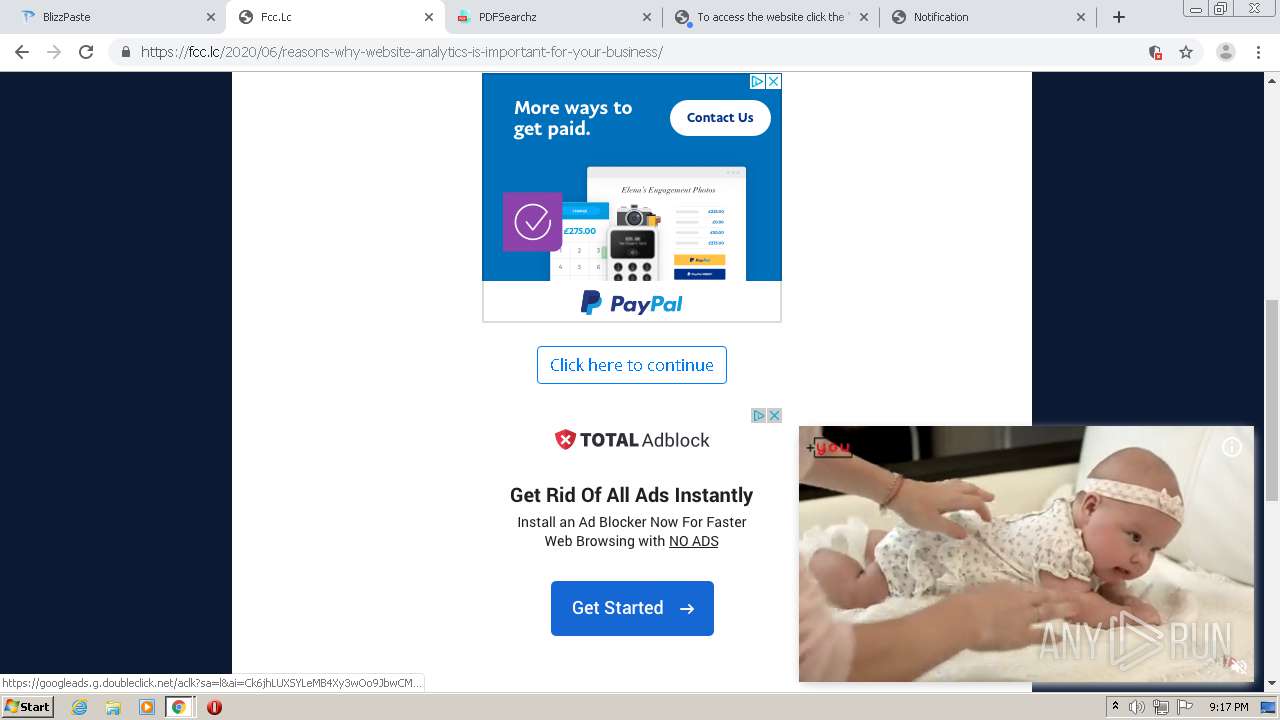
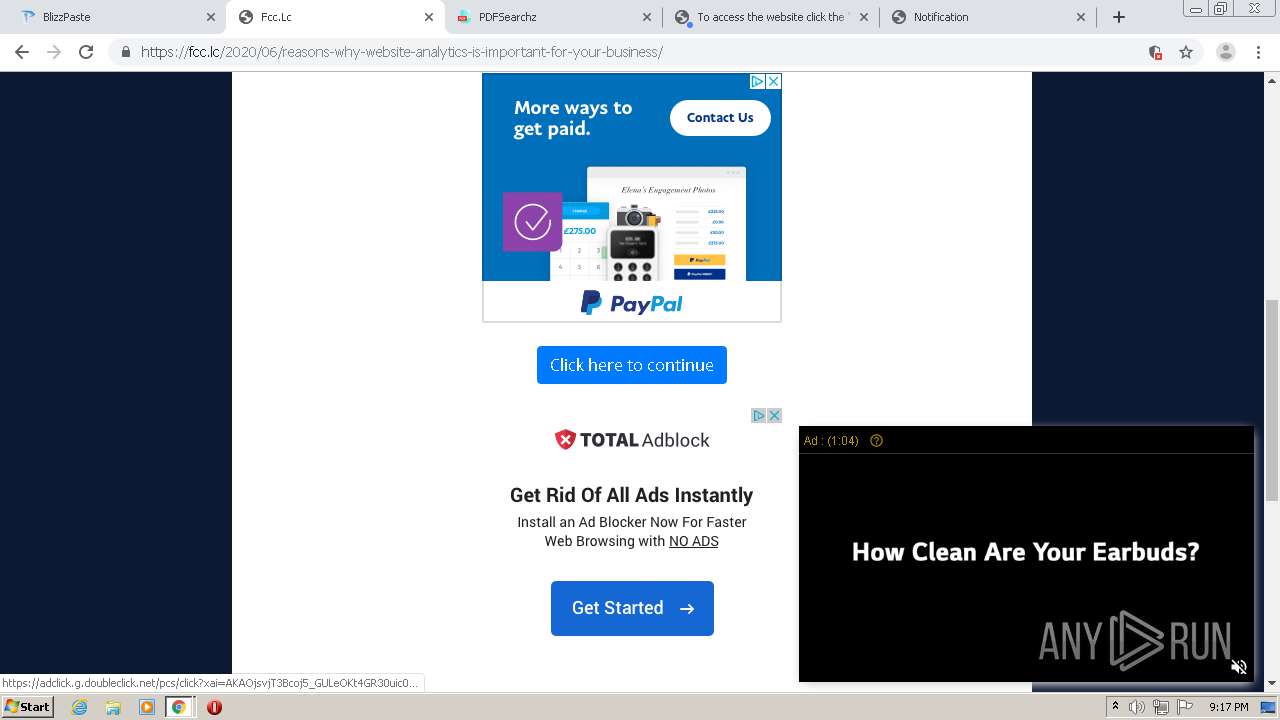
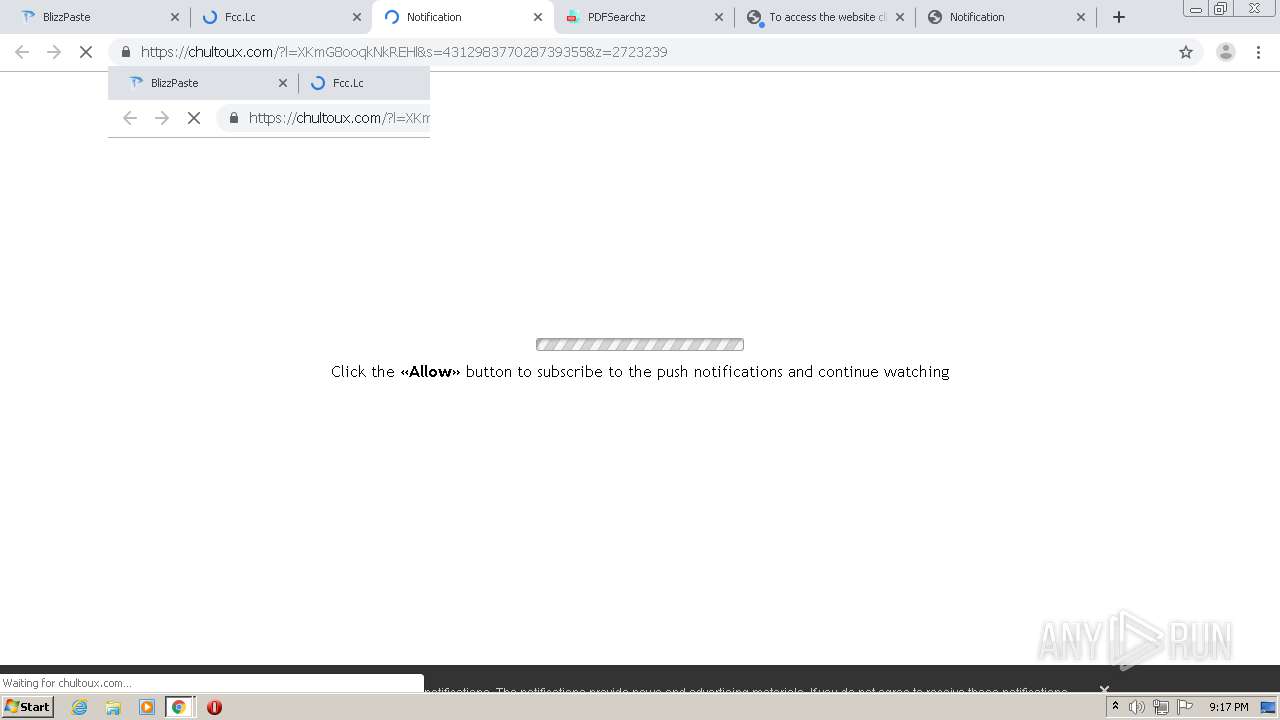
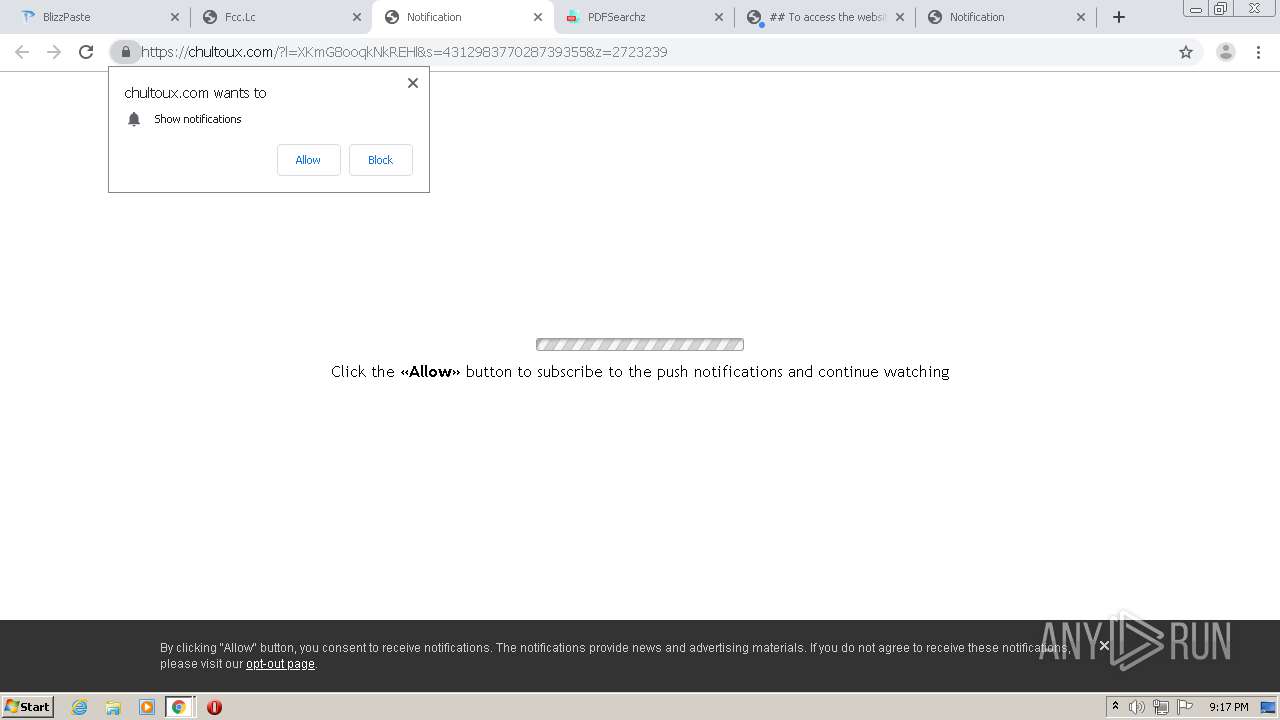
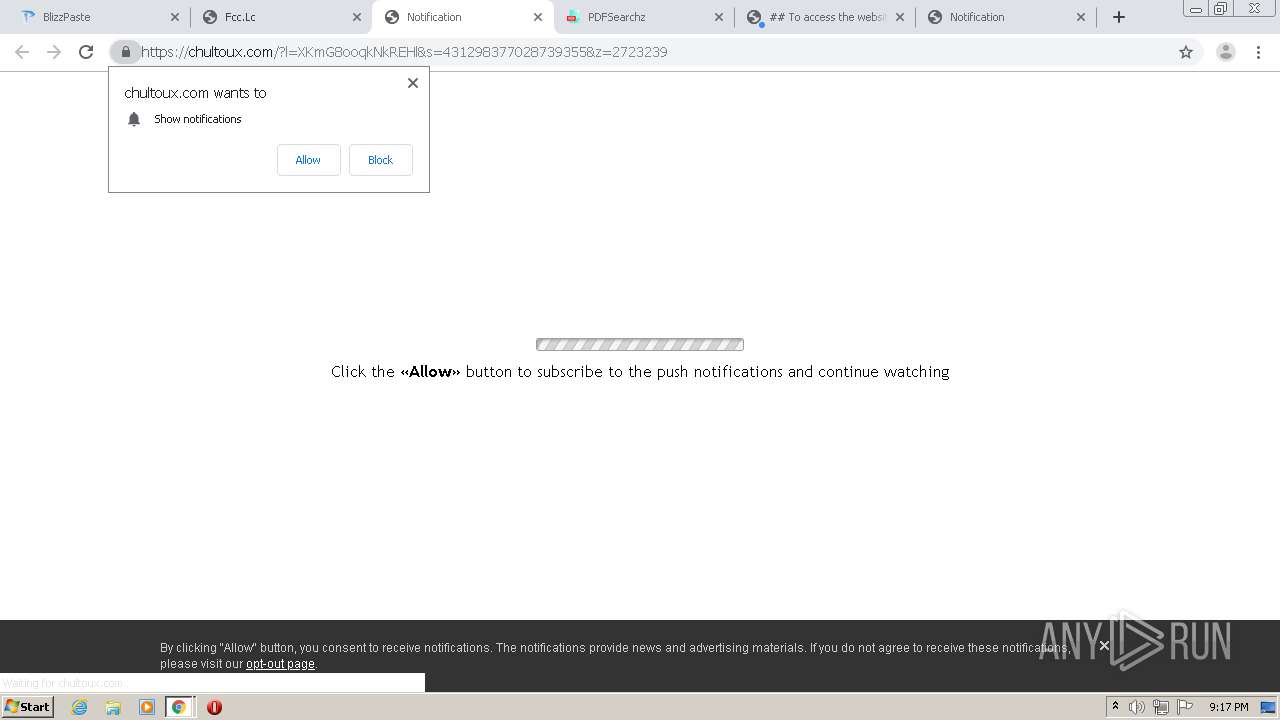
1940 | chrome.exe | 104.21.78.148:443 | fc.lc | Cloudflare Inc | US | malicious |
1940 | chrome.exe | 195.181.175.54:80 | c1.popads.net | Datacamp Limited | DE | suspicious |
1940 | chrome.exe | 104.17.167.186:443 | c.adsco.re | Cloudflare Inc | US | shared |
1940 | chrome.exe | 142.250.185.174:443 | www.google-analytics.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
blizzpaste.com |
| whitelisted |
accounts.google.com |
| shared |
ajax.googleapis.com |
| whitelisted |
www.blizzpaste.com |
| unknown |
fc.lc |
| malicious |
www.googletagmanager.com |
| whitelisted |
c1.popads.net |
| whitelisted |
safebrowsing.googleapis.com |
| whitelisted |
bit.ly |
| shared |
www.google-analytics.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1940 | chrome.exe | Attempted User Privilege Gain | ET INFO Session Traversal Utilities for NAT (STUN Binding Request) |
— | — | Attempted User Privilege Gain | ET INFO Session Traversal Utilities for NAT (STUN Binding Request) |
— | — | Attempted User Privilege Gain | ET INFO Session Traversal Utilities for NAT (STUN Binding Request) |
— | — | Attempted User Privilege Gain | ET INFO Session Traversal Utilities for NAT (STUN Binding Response) |
1940 | chrome.exe | Attempted User Privilege Gain | ET INFO Session Traversal Utilities for NAT (STUN Binding Response) |
— | — | Attempted User Privilege Gain | ET INFO Session Traversal Utilities for NAT (STUN Binding Response) |