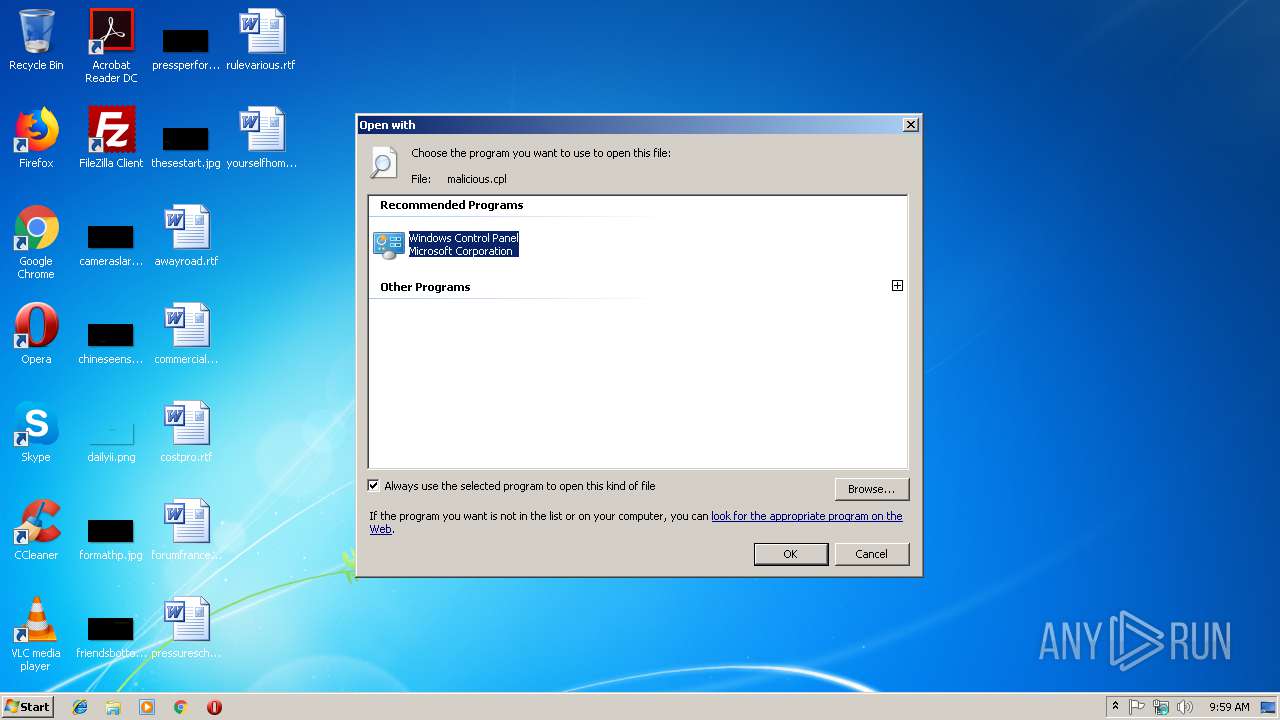
| File name: | malicious.cpl |
| Full analysis: | https://app.any.run/tasks/1d6fecab-bd29-482b-b48d-96babcd32383 |
| Verdict: | Malicious activity |
| Analysis date: | January 11, 2019, 09:59:20 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (DLL) (GUI) Intel 80386, for MS Windows |
| MD5: | 66939236633E772D2E839D91B2357771 |
| SHA1: | 58A77C56C6387CBCCD8CF1B494231BE070261C69 |
| SHA256: | 7D1D5D1723C486E070F0CBE28B1F09F9EB3E9A2E6652B20A068557676B9562FF |
| SSDEEP: | 3072:JzqfbmDB89oUDhwZi8n2bojF6t2UhtAuHJCfV+tc8WCFSDy:kfb01JZTRUvA7kRWC |
MALICIOUS
Loads dropped or rewritten executable
- rundll32.exe (PID: 3404)
- svchost.exe (PID: 844)
SUSPICIOUS
Uses RUNDLL32.EXE to load library
- control.exe (PID: 3212)
INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win64 Executable (generic) (47.4) |
|---|---|---|
| .cpl | | | Win 9x/ME Control Panel applet (26.6) |
| .dll | | | Win32 Dynamic Link Library (generic) (11.2) |
| .exe | | | Win32 Executable (generic) (7.7) |
| .exe | | | Generic Win/DOS Executable (3.4) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2018:12:25 06:44:36+01:00 |
| PEType: | PE32 |
| LinkerVersion: | 10 |
| CodeSize: | 21504 |
| InitializedDataSize: | 135168 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x1c9a |
| OSVersion: | 5.1 |
| ImageVersion: | - |
| SubsystemVersion: | 5.1 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 1.0.0.1 |
| ProductVersionNumber: | 1.0.0.1 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Windows NT 32-bit |
| ObjectFileType: | Dynamic link library |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Unicode |
| CompanyName: | TODO: <Company name> |
| FileDescription: | TODO: <File description> |
| FileVersion: | 1.0.0.1 |
| InternalName: | MS Word.cpl |
| LegalCopyright: | TODO: (c) <Company name>. All rights reserved. |
| OriginalFileName: | MS Word.cpl |
| ProductName: | TODO: <Product name> |
| ProductVersion: | 1.0.0.1 |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 25-Dec-2018 05:44:36 |
| Detected languages: |
|
| CompanyName: | TODO: <Company name> |
| FileDescription: | TODO: <File description> |
| FileVersion: | 1.0.0.1 |
| InternalName: | MS Word.cpl |
| LegalCopyright: | TODO: (c) <Company name>. All rights reserved. |
| OriginalFilename: | MS Word.cpl |
| ProductName: | TODO: <Product name> |
| ProductVersion: | 1.0.0.1 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000100 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 5 |
| Time date stamp: | 25-Dec-2018 05:44:36 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x000052E4 | 0x00005400 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.48131 |
.rdata | 0x00007000 | 0x00002D2E | 0x00002E00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 4.8881 |
.data | 0x0000A000 | 0x0001885C | 0x00017C00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 7.60964 |
.rsrc | 0x00023000 | 0x00005220 | 0x00005400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 4.34156 |
.reloc | 0x00029000 | 0x00001170 | 0x00001200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 3.62508 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 3.42668 | 816 | Latin 1 / Western European | English - United States | RT_VERSION |
2 | 4.79597 | 346 | Latin 1 / Western European | English - United States | RT_MANIFEST |
3 | 2.74274 | 180 | Latin 1 / Western European | English - United States | RT_CURSOR |
4 | 2.34038 | 308 | Latin 1 / Western European | English - United States | RT_CURSOR |
5 | 2.34004 | 308 | Latin 1 / Western European | English - United States | RT_CURSOR |
6 | 2.51649 | 308 | Latin 1 / Western European | English - United States | RT_CURSOR |
7 | 2.45401 | 308 | Latin 1 / Western European | English - United States | RT_CURSOR |
8 | 2.34864 | 308 | Latin 1 / Western European | English - United States | RT_CURSOR |
9 | 2.34505 | 308 | Latin 1 / Western European | English - United States | RT_CURSOR |
10 | 2.34864 | 308 | Latin 1 / Western European | English - United States | RT_CURSOR |
Imports
KERNEL32.dll |
OLEAUT32.dll |
ole32.dll |
Exports
Title | Ordinal | Address |
|---|---|---|
CPlApplet | 1 | 0x00001730 |
Total processes
33
Monitored processes
4
Malicious processes
3
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 844 | C:\Windows\system32\svchost.exe -k netsvcs | C:\Windows\System32\svchost.exe | services.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2988 | "C:\Windows\system32\rundll32.exe" C:\Windows\system32\shell32.dll,OpenAs_RunDLL C:\Users\admin\AppData\Local\Temp\malicious.cpl | C:\Windows\system32\rundll32.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3212 | "C:\Windows\System32\control.exe" "C:\Users\admin\AppData\Local\Temp\malicious.cpl", | C:\Windows\System32\control.exe | — | rundll32.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Control Panel Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3404 | "C:\Windows\system32\rundll32.exe" Shell32.dll,Control_RunDLL "C:\Users\admin\AppData\Local\Temp\malicious.cpl", | C:\Windows\system32\rundll32.exe | — | control.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
549
Read events
469
Write events
80
Delete events
0
Modification events
| (PID) Process: | (2988) rundll32.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\FileExts\.cpl\OpenWithProgids |
| Operation: | write | Name: | cplfile |
Value: | |||
| (PID) Process: | (2988) rundll32.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\MuiCache |
| Operation: | write | Name: | C:\Windows\System32\control.exe |
Value: Windows Control Panel | |||
| (PID) Process: | (2988) rundll32.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\MuiCache |
| Operation: | write | Name: | C:\Program Files\Adobe\Acrobat Reader DC\Reader\AcroRd32.exe |
Value: Adobe Acrobat Reader DC | |||
| (PID) Process: | (2988) rundll32.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\MuiCache |
| Operation: | write | Name: | C:\Windows\eHome\ehshell.exe |
Value: Windows Media Center | |||
| (PID) Process: | (2988) rundll32.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\MuiCache |
| Operation: | write | Name: | C:\Windows\system32\mspaint.exe |
Value: Paint | |||
| (PID) Process: | (2988) rundll32.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\MuiCache |
| Operation: | write | Name: | C:\Windows\system32\NOTEPAD.EXE |
Value: Notepad | |||
| (PID) Process: | (2988) rundll32.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\MuiCache |
| Operation: | write | Name: | C:\PROGRA~1\MICROS~1\Office14\OIS.EXE |
Value: Microsoft Office 2010 | |||
| (PID) Process: | (2988) rundll32.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\MuiCache |
| Operation: | write | Name: | C:\Program Files\Opera\Opera.exe |
Value: Opera Internet Browser | |||
| (PID) Process: | (2988) rundll32.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\MuiCache |
| Operation: | write | Name: | C:\Program Files\Windows Photo Viewer\PhotoViewer.dll |
Value: Windows Photo Viewer | |||
| (PID) Process: | (2988) rundll32.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\MuiCache |
| Operation: | write | Name: | C:\Program Files\VideoLAN\VLC\vlc.exe |
Value: VLC media player | |||
Executable files
0
Suspicious files
4
Text files
0
Unknown types
1
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 844 | svchost.exe | C:\Windows\SoftwareDistribution\DataStore\DataStore.edb | — | |
MD5:— | SHA256:— | |||
| 844 | svchost.exe | C:\Windows\appcompat\programs\RecentFileCache.bcf | txt | |
MD5:— | SHA256:— | |||
| 844 | svchost.exe | C:\Windows\SoftwareDistribution\DataStore\Logs\edb.chk | binary | |
MD5:— | SHA256:— | |||
| 844 | svchost.exe | C:\Windows\SoftwareDistribution\DataStore\Logs\edb.log | binary | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report