| File name: | surgeon.pdf |
| Full analysis: | https://app.any.run/tasks/2b2e19e6-34c2-4854-8130-65a3582412fc |
| Verdict: | Malicious activity |
| Analysis date: | October 19, 2020, 20:36:38 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/pdf |
| File info: | PDF document, version 1.4 |
| MD5: | 1082C3DBEEFF282EC80E94F985269122 |
| SHA1: | 02A0E6635AE024650131F55CAC9A0598CB2B6D69 |
| SHA256: | 7CFF45649C4DC30C62128AC75C299D2351A69C89B26B3B6989B15D31746B090E |
| SSDEEP: | 1536:AdHAOJIYNw20AomRj9y0/pactn7ViHDxcKIHt:OAQIYNb0AtRDam7Vuc3t |
MALICIOUS
No malicious indicators.SUSPICIOUS
Starts Internet Explorer
- AcroRd32.exe (PID: 2064)
Creates files in the program directory
- AdobeARM.exe (PID: 3344)
INFO
Application launched itself
- AcroRd32.exe (PID: 2064)
- RdrCEF.exe (PID: 2512)
- iexplore.exe (PID: 1652)
Changes IE settings (feature browser emulation)
- AcroRd32.exe (PID: 2064)
Reads the hosts file
- RdrCEF.exe (PID: 2512)
Reads Internet Cache Settings
- iexplore.exe (PID: 1652)
- iexplore.exe (PID: 2100)
- AcroRd32.exe (PID: 944)
- AcroRd32.exe (PID: 2064)
- iexplore.exe (PID: 548)
Changes internet zones settings
- iexplore.exe (PID: 1652)
Reads internet explorer settings
- iexplore.exe (PID: 548)
- iexplore.exe (PID: 2100)
Reads settings of System Certificates
- iexplore.exe (PID: 1652)
- iexplore.exe (PID: 548)
- AcroRd32.exe (PID: 2064)
Creates files in the user directory
- iexplore.exe (PID: 2100)
- iexplore.exe (PID: 548)
Adds / modifies Windows certificates
- iexplore.exe (PID: 1652)
Drops Coronavirus (possible) decoy
- iexplore.exe (PID: 2100)
Changes settings of System certificates
- iexplore.exe (PID: 1652)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| | | Adobe Portable Document Format (100) |
EXIF
| PDFVersion: | 1.4 |
|---|---|
| Linearized: | No |
| Title: | - |
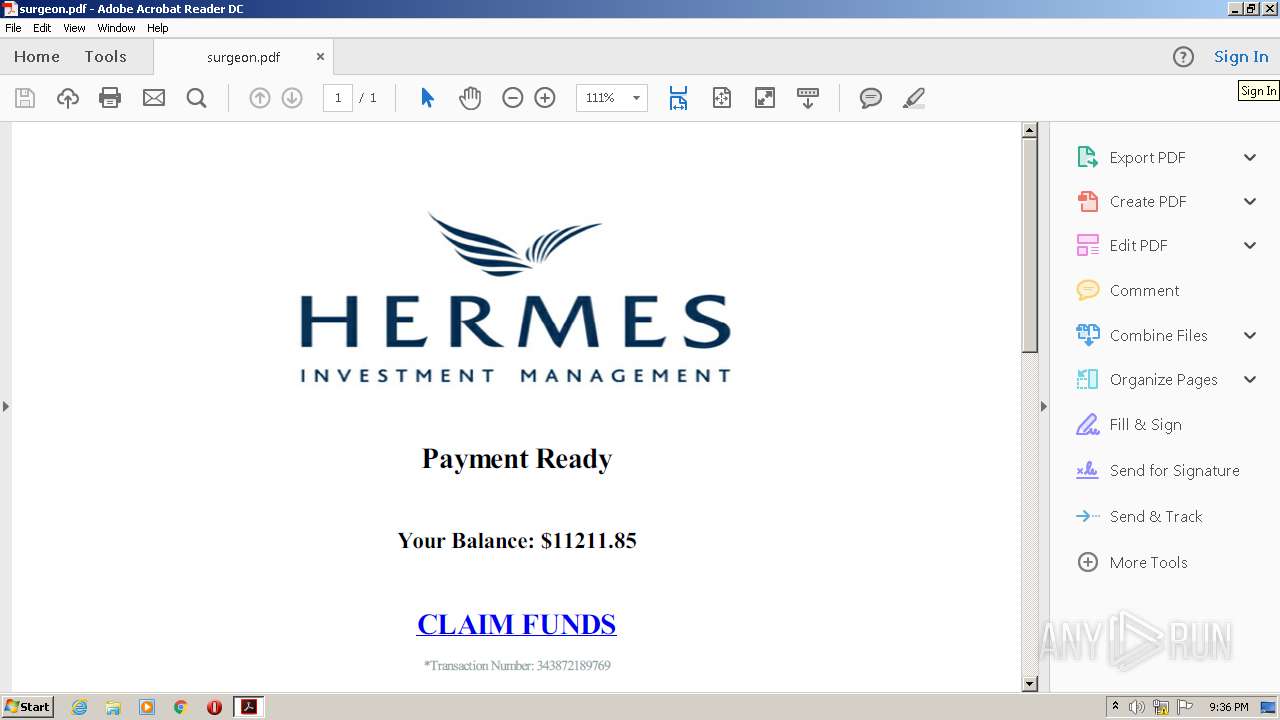
| Creator: | wkhtmltopdf 0.12.5 |
| Producer: | Qt 4.8.7 |
| CreateDate: | 2020:10:15 12:06:02+03:00 |
| PageCount: | 1 |
Total processes
46
Monitored processes
10
Malicious processes
0
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 548 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:1652 CREDAT:3806487 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 944 | "C:\Program Files\Adobe\Acrobat Reader DC\Reader\AcroRd32.exe" --type=renderer "C:\Users\admin\AppData\Local\Temp\surgeon.pdf" | C:\Program Files\Adobe\Acrobat Reader DC\Reader\AcroRd32.exe | — | AcroRd32.exe | |||||||||||
User: admin Company: Adobe Systems Incorporated Integrity Level: LOW Description: Adobe Acrobat Reader DC Exit code: 0 Version: 15.23.20070.215641 Modules
| |||||||||||||||
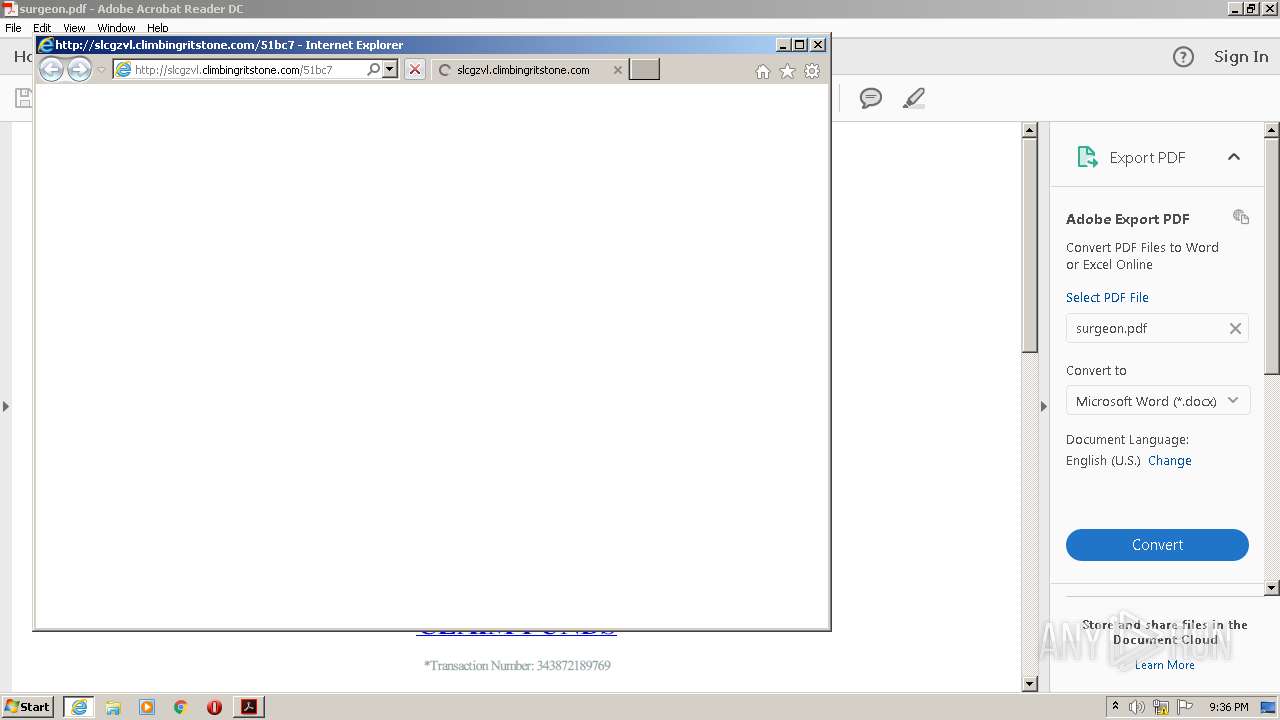
| 1652 | "C:\Program Files\Internet Explorer\iexplore.exe" http://slcgzvl.climbingritstone.com/51bc7 | C:\Program Files\Internet Explorer\iexplore.exe | AcroRd32.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 2064 | "C:\Program Files\Adobe\Acrobat Reader DC\Reader\AcroRd32.exe" "C:\Users\admin\AppData\Local\Temp\surgeon.pdf" | C:\Program Files\Adobe\Acrobat Reader DC\Reader\AcroRd32.exe | explorer.exe | ||||||||||||
User: admin Company: Adobe Systems Incorporated Integrity Level: MEDIUM Description: Adobe Acrobat Reader DC Exit code: 0 Version: 15.23.20070.215641 Modules
| |||||||||||||||
| 2100 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:1652 CREDAT:267521 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 2512 | "C:\Program Files\Adobe\Acrobat Reader DC\Reader\AcroCEF\RdrCEF.exe" --backgroundcolor=16448250 | C:\Program Files\Adobe\Acrobat Reader DC\Reader\AcroCEF\RdrCEF.exe | — | AcroRd32.exe | |||||||||||
User: admin Company: Adobe Systems Incorporated Integrity Level: MEDIUM Description: Adobe RdrCEF Exit code: 0 Version: 15.23.20053.211670 Modules
| |||||||||||||||
| 2604 | "C:\Program Files\Adobe\Acrobat Reader DC\Reader\Reader_sl.exe" | C:\Program Files\Adobe\Acrobat Reader DC\Reader\Reader_sl.exe | — | AdobeARM.exe | |||||||||||
User: admin Company: Adobe Systems Incorporated Integrity Level: MEDIUM Description: Adobe Acrobat SpeedLauncher Exit code: 0 Version: 15.23.20053.211670 Modules
| |||||||||||||||
| 3344 | "C:\Program Files\Common Files\Adobe\ARM\1.0\AdobeARM.exe" /PRODUCT:Reader /VERSION:15.0 /MODE:3 | C:\Program Files\Common Files\Adobe\ARM\1.0\AdobeARM.exe | — | AcroRd32.exe | |||||||||||
User: admin Company: Adobe Systems Incorporated Integrity Level: MEDIUM Description: Adobe Reader and Acrobat Manager Exit code: 0 Version: 1.824.27.2646 Modules
| |||||||||||||||
| 3360 | "C:\Program Files\Adobe\Acrobat Reader DC\Reader\AcroCEF\RdrCEF.exe" --type=renderer --disable-3d-apis --disable-databases --disable-direct-npapi-requests --disable-file-system --disable-notifications --disable-shared-workers --disable-direct-write --lang=en-US --lang=en-US --log-severity=disable --product-version="ReaderServices/15.23.20053 Chrome/45.0.2454.85" --device-scale-factor=1 --enable-delegated-renderer --num-raster-threads=2 --gpu-rasterization-msaa-sample-count=8 --content-image-texture-target=3553 --video-image-texture-target=3553 --disable-accelerated-video-decode --disable-webrtc-hw-encoding --disable-gpu-compositing --channel="2512.1.2095838679\785470737" --allow-no-sandbox-job /prefetch:673131151 | C:\Program Files\Adobe\Acrobat Reader DC\Reader\AcroCEF\RdrCEF.exe | — | RdrCEF.exe | |||||||||||
User: admin Company: Adobe Systems Incorporated Integrity Level: LOW Description: Adobe RdrCEF Exit code: 0 Version: 15.23.20053.211670 Modules
| |||||||||||||||
| 3496 | "C:\Program Files\Adobe\Acrobat Reader DC\Reader\AcroCEF\RdrCEF.exe" --type=renderer --disable-3d-apis --disable-databases --disable-direct-npapi-requests --disable-file-system --disable-notifications --disable-shared-workers --disable-direct-write --lang=en-US --lang=en-US --log-severity=disable --product-version="ReaderServices/15.23.20053 Chrome/45.0.2454.85" --device-scale-factor=1 --enable-delegated-renderer --num-raster-threads=2 --gpu-rasterization-msaa-sample-count=8 --content-image-texture-target=3553 --video-image-texture-target=3553 --disable-accelerated-video-decode --disable-webrtc-hw-encoding --disable-gpu-compositing --channel="2512.0.839346498\293396837" --allow-no-sandbox-job /prefetch:673131151 | C:\Program Files\Adobe\Acrobat Reader DC\Reader\AcroCEF\RdrCEF.exe | — | RdrCEF.exe | |||||||||||
User: admin Company: Adobe Systems Incorporated Integrity Level: LOW Description: Adobe RdrCEF Exit code: 0 Version: 15.23.20053.211670 Modules
| |||||||||||||||
Total events
1 028
Read events
886
Write events
138
Delete events
4
Modification events
| (PID) Process: | (944) AcroRd32.exe | Key: | HKEY_CURRENT_USER\Software\Adobe\Acrobat Reader\DC\ExitSection |
| Operation: | write | Name: | bLastExitNormal |
Value: 0 | |||
| (PID) Process: | (944) AcroRd32.exe | Key: | HKEY_CURRENT_USER\Software\Adobe\Acrobat Reader\DC\AVGeneral |
| Operation: | write | Name: | bExpandRHPInViewer |
Value: 1 | |||
| (PID) Process: | (944) AcroRd32.exe | Key: | HKEY_CURRENT_USER\Software\Adobe\Acrobat Reader\DC\NoTimeOut |
| Operation: | write | Name: | smailto |
Value: 5900 | |||
| (PID) Process: | (2064) AcroRd32.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main\FeatureControl\FEATURE_BROWSER_EMULATION |
| Operation: | write | Name: | AcroRd32.exe |
Value: 10001 | |||
| (PID) Process: | (1652) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateLowDateTime |
Value: 2839150643 | |||
| (PID) Process: | (1652) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateHighDateTime |
Value: 30844503 | |||
| (PID) Process: | (1652) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (1652) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (1652) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (2064) AcroRd32.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Shell Extensions\Cached |
| Operation: | write | Name: | {17FE9752-0B5A-4665-84CD-569794602F5C} {7F9185B0-CB92-43C5-80A9-92277A4F7B54} 0xFFFF |
Value: 0100000000000000B77F3C9757A6D601 | |||
Executable files
0
Suspicious files
75
Text files
121
Unknown types
104
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 944 | AcroRd32.exe | C:\Users\admin\AppData\LocalLow\Adobe\Acrobat\DC\ReaderMessages-journal | — | |
MD5:— | SHA256:— | |||
| 1652 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\Internet Explorer\Services\search_{0633EE93-D776-472f-A0FF-E1416B8B2E3A}.ico | — | |
MD5:— | SHA256:— | |||
| 2100 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Low\Cab70B0.tmp | — | |
MD5:— | SHA256:— | |||
| 2100 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Low\Tar70B1.tmp | — | |
MD5:— | SHA256:— | |||
| 944 | AcroRd32.exe | C:\Users\admin\AppData\Local\Temp\acrord32_sbx\A9R10k6dm5_jsehrf_q8.tmp | — | |
MD5:— | SHA256:— | |||
| 944 | AcroRd32.exe | C:\Users\admin\AppData\Local\Temp\acrord32_sbx\A9R7ja8k1_jsehrg_q8.tmp | — | |
MD5:— | SHA256:— | |||
| 944 | AcroRd32.exe | C:\Users\admin\AppData\Local\Temp\acrord32_sbx\A9R1c4ti6b_jsehri_q8.tmp | — | |
MD5:— | SHA256:— | |||
| 944 | AcroRd32.exe | C:\Users\admin\AppData\Local\Temp\acrord32_sbx\A9Ro3dwwn_jsehrh_q8.tmp | — | |
MD5:— | SHA256:— | |||
| 2100 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\6BADA8974A10C4BD62CC921D13E43B18_28DEA62A0AE77228DD387E155AD0BA27 | der | |
MD5:— | SHA256:— | |||
| 944 | AcroRd32.exe | C:\Users\admin\AppData\LocalLow\Adobe\Acrobat\DC\ReaderMessages | sqlite | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
163
TCP/UDP connections
199
DNS requests
41
Threats
5
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1652 | iexplore.exe | GET | 404 | 162.0.229.126:80 | http://slcgzvl.climbingritstone.com/favicon.ico | CA | — | — | suspicious |
2064 | AcroRd32.exe | GET | 304 | 2.16.107.24:80 | http://acroipm2.adobe.com/15/rdr/ENU/win/nooem/none/consumer/278_15_23_20070.zip | unknown | — | — | whitelisted |
2064 | AcroRd32.exe | GET | 304 | 2.16.107.24:80 | http://acroipm2.adobe.com/15/rdr/ENU/win/nooem/none/consumer/280_15_23_20070.zip | unknown | — | — | whitelisted |
2064 | AcroRd32.exe | GET | 304 | 2.16.107.24:80 | http://acroipm2.adobe.com/15/rdr/ENU/win/nooem/none/consumer/277_15_23_20070.zip | unknown | — | — | whitelisted |
2100 | iexplore.exe | GET | 200 | 74.208.236.74:80 | http://coinsblog.ws/ | US | html | 42.0 Kb | suspicious |
2100 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEAo3h2ReX7SMIk79G%2B0UDDw%3D | US | der | 1.47 Kb | whitelisted |
2100 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQS14tALDViBvqCf47YkiQRtKz1BAQUpc436uuwdQ6UZ4i0RfrZJBCHlh8CEAwIDjn%2FFrMf7wXyIDkQENw%3D | US | der | 280 b | whitelisted |
2100 | iexplore.exe | GET | 200 | 162.0.229.126:80 | http://slcgzvl.climbingritstone.com/51bc7 | CA | html | 3.20 Kb | suspicious |
2100 | iexplore.exe | GET | 200 | 216.58.208.42:80 | http://fonts.googleapis.com/css?family=Comfortaa:300,regular,700|Merriweather:300,300italic,regular,italic,700,700italic,900,900italic&subset=latin-ext,greek,vietnamese,cyrillic,latin,cyrillic-ext&display=swap | US | text | 436 b | whitelisted |
2100 | iexplore.exe | GET | 200 | 54.230.183.71:80 | http://a.impactradius-go.com/display-ad/2029-76930 | US | image | 6.83 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1652 | iexplore.exe | 204.79.197.200:80 | www.bing.com | Microsoft Corporation | US | whitelisted |
2064 | AcroRd32.exe | 2.16.107.24:80 | acroipm2.adobe.com | Akamai International B.V. | — | malicious |
2064 | AcroRd32.exe | 2.18.233.74:443 | armmf.adobe.com | Akamai International B.V. | — | whitelisted |
2100 | iexplore.exe | 74.208.236.74:80 | coinsblog.ws | 1&1 Internet SE | US | malicious |
2100 | iexplore.exe | 192.0.77.2:443 | i2.wp.com | Automattic, Inc | US | suspicious |
2100 | iexplore.exe | 216.58.208.42:80 | fonts.googleapis.com | Google Inc. | US | whitelisted |
2100 | iexplore.exe | 151.101.12.84:80 | assets.pinterest.com | Fastly | US | unknown |
2100 | iexplore.exe | 216.58.208.42:443 | fonts.googleapis.com | Google Inc. | US | whitelisted |
2064 | AcroRd32.exe | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
2100 | iexplore.exe | 192.0.77.37:443 | c0.wp.com | Automattic, Inc | US | suspicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
slcgzvl.climbingritstone.com |
| suspicious |
adropcolink.club |
| suspicious |
ocsp.digicert.com |
| whitelisted |
api.bing.com |
| whitelisted |
www.bing.com |
| whitelisted |
coinsblog.ws |
| suspicious |
acroipm2.adobe.com |
| whitelisted |
armmf.adobe.com |
| whitelisted |
c0.wp.com |
| whitelisted |
fonts.googleapis.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1052 | svchost.exe | Potentially Bad Traffic | ET INFO Suspicious Domain Request for Possible COVID-19 Domain M2 |
2100 | iexplore.exe | Potentially Bad Traffic | ET INFO Suspicious GET Request with Possible COVID-19 Domain M2 |
2100 | iexplore.exe | Potentially Bad Traffic | ET INFO Suspicious GET Request with Possible COVID-19 URI M2 |
548 | iexplore.exe | Potentially Bad Traffic | ET INFO Suspicious GET Request with Possible COVID-19 Domain M2 |
548 | iexplore.exe | Potentially Bad Traffic | ET INFO Suspicious GET Request with Possible COVID-19 URI M2 |