| download: | index.html |
| Full analysis: | https://app.any.run/tasks/40ca8b26-ef31-40c1-bc49-699d65090066 |
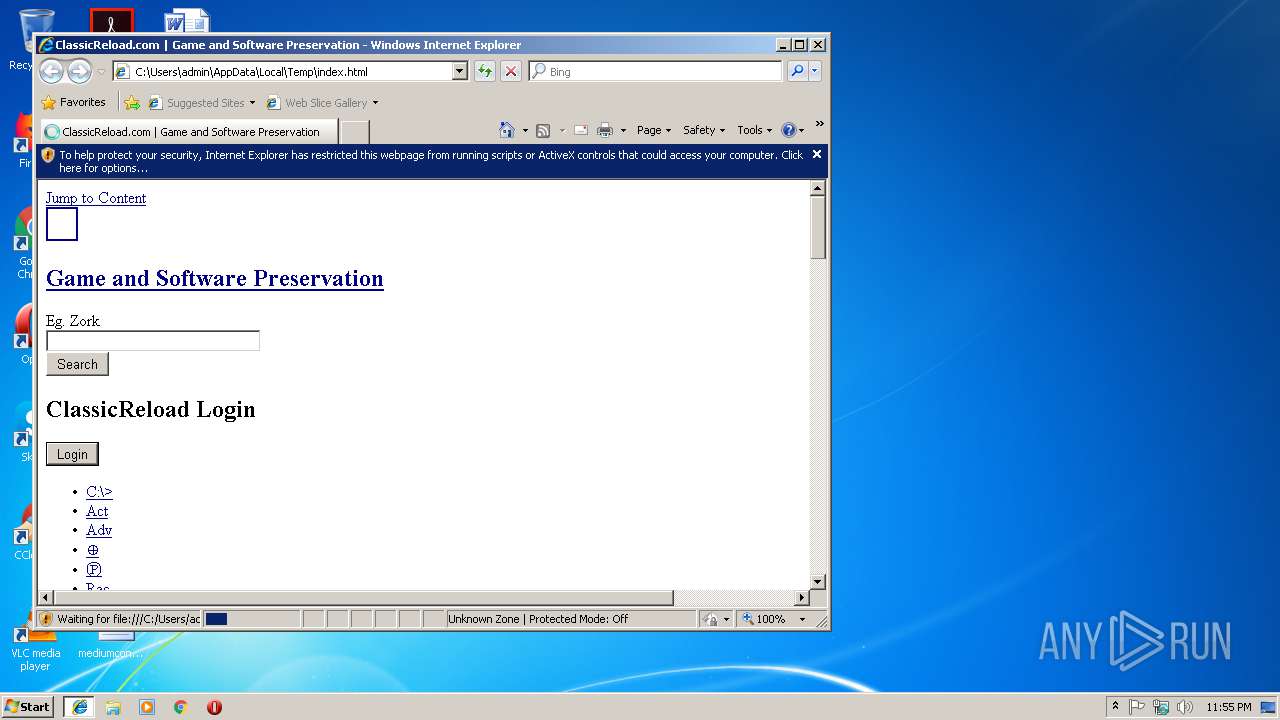
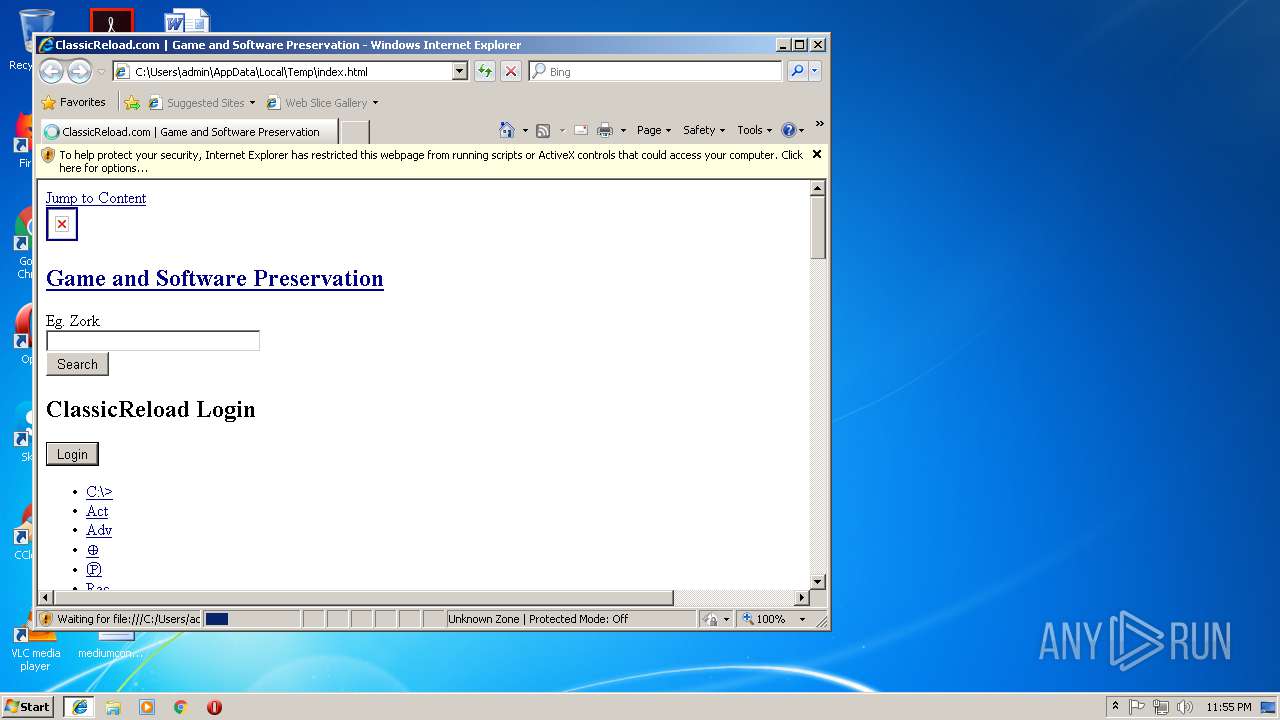
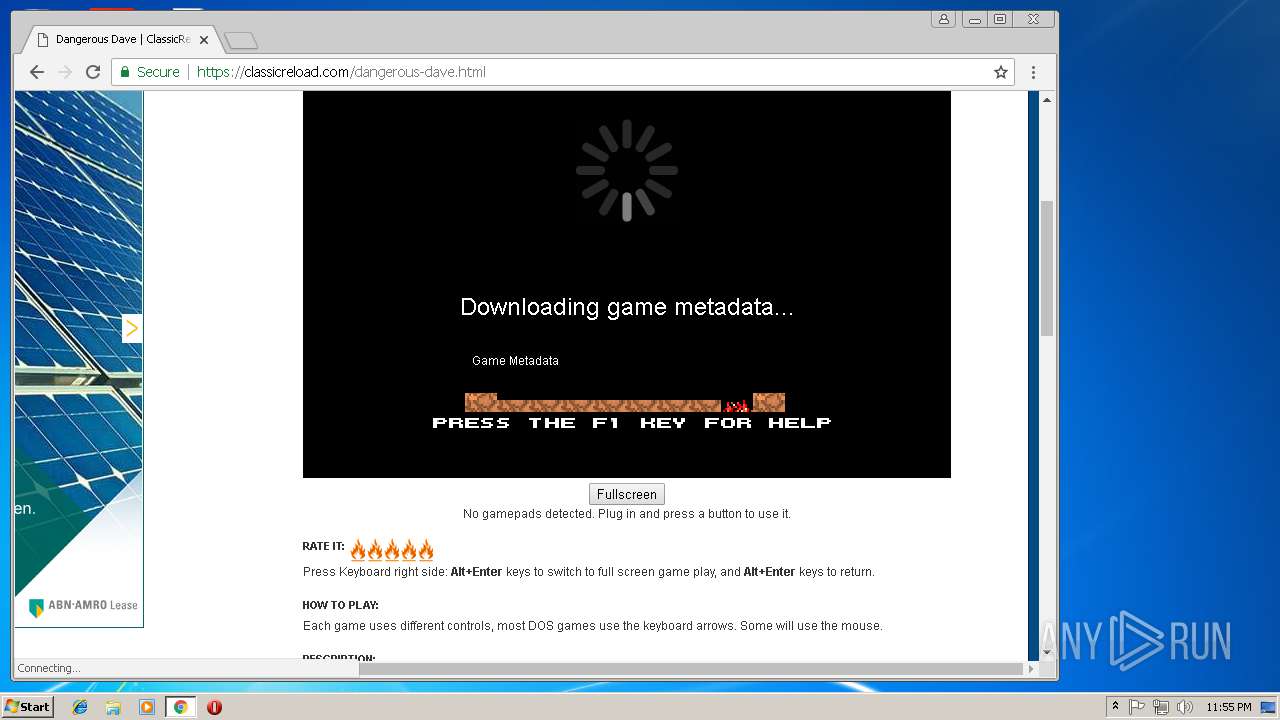
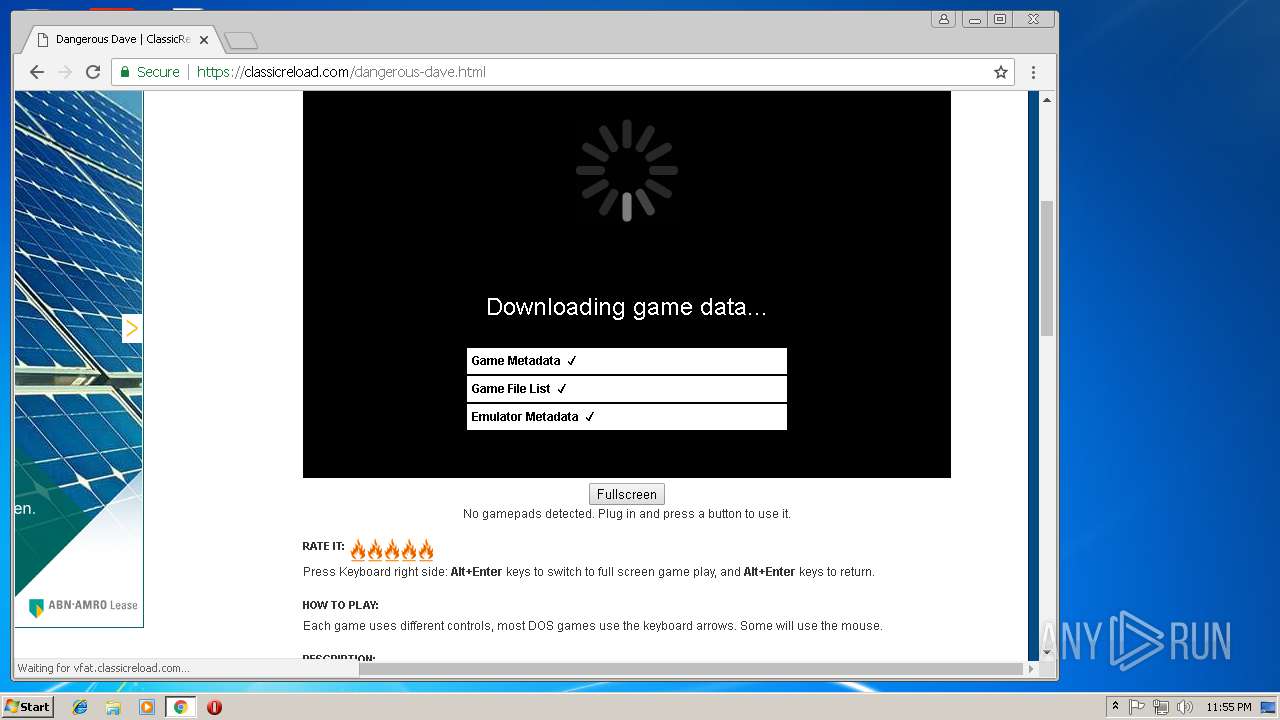
| Verdict: | Malicious activity |
| Analysis date: | January 22, 2019, 23:54:22 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | text/html |
| File info: | HTML document, UTF-8 Unicode text, with very long lines, with CRLF, LF line terminators |
| MD5: | 8721959D71A1387C951244C9CCBA2006 |
| SHA1: | DDFC6460AD3A0B9633BBB0CA8FC7AC868B5D0CAF |
| SHA256: | 7CF8BA7A247A86EA7DDFD550C8689BD82062C2885439A031993BE34E10AAA22A |
| SSDEEP: | 1536:ad3TL/URo8cOMRY0SRZ4aPJtV9zWVPWx3Hh81FaYR4g4VX8WuTL/URo8cOMRY0S9:ad3TL/URo8cOMRY0SRZ4aPJtkPABAFax |
MALICIOUS
No malicious indicators.SUSPICIOUS
No suspicious indicators.INFO
Changes internet zones settings
- iexplore.exe (PID: 2984)
Application launched itself
- iexplore.exe (PID: 2984)
- chrome.exe (PID: 3148)
Reads internet explorer settings
- iexplore.exe (PID: 3416)
Creates files in the user directory
- iexplore.exe (PID: 3416)
Reads settings of System Certificates
- iexplore.exe (PID: 3416)
- chrome.exe (PID: 3148)
Adds / modifies Windows certificates
- iexplore.exe (PID: 3416)
Changes settings of System certificates
- iexplore.exe (PID: 3416)
- chrome.exe (PID: 3148)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .htm/html | | | HyperText Markup Language with DOCTYPE (80.6) |
|---|---|---|
| .html | | | HyperText Markup Language (19.3) |
EXIF
HTML
| googleSiteVerification: | OhA1UzC41PVVNTeZ5t9pzmgG2Ifkxcbd-GtgRkc_Srk |
|---|---|
| Generator: | Drupal 7 (https://www.drupal.org) |
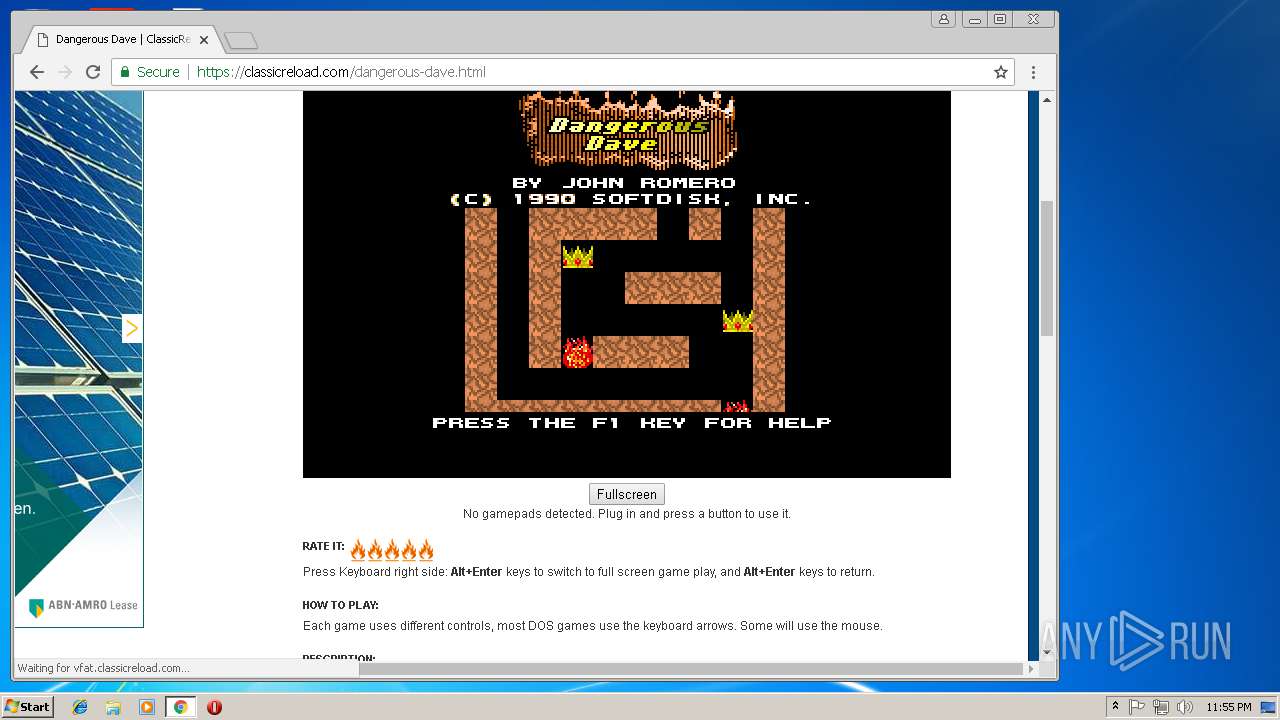
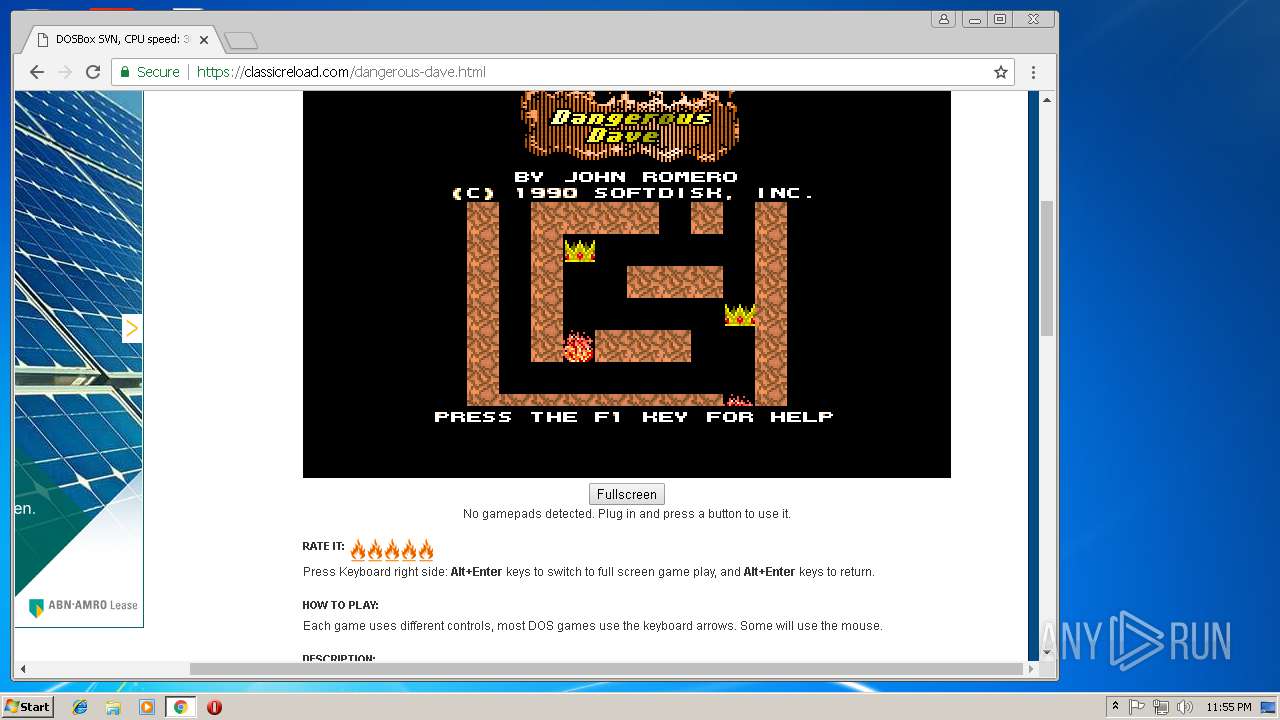
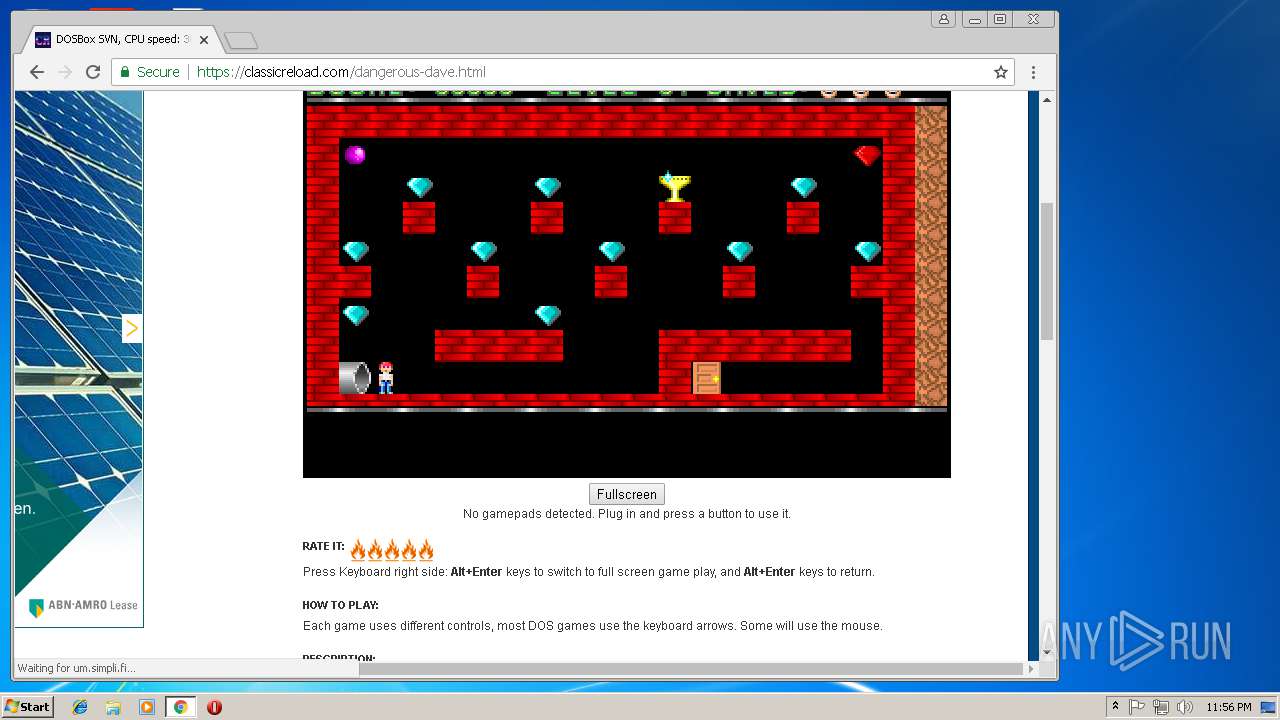
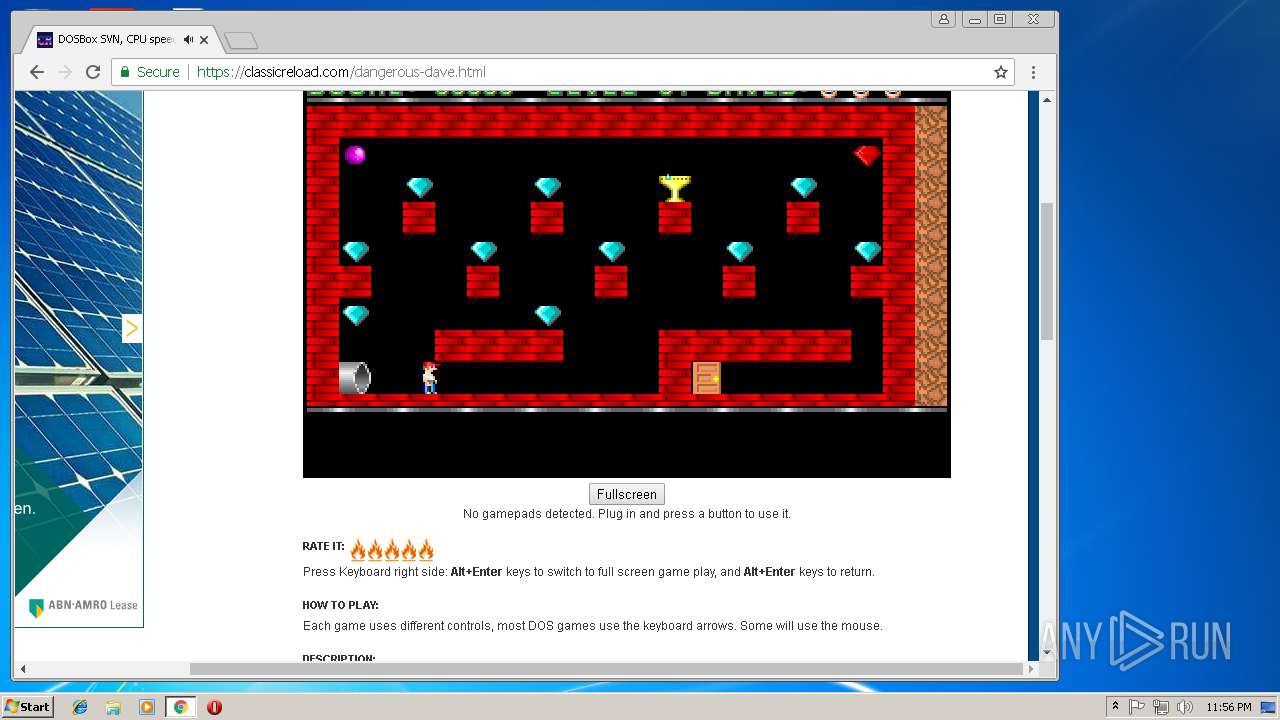
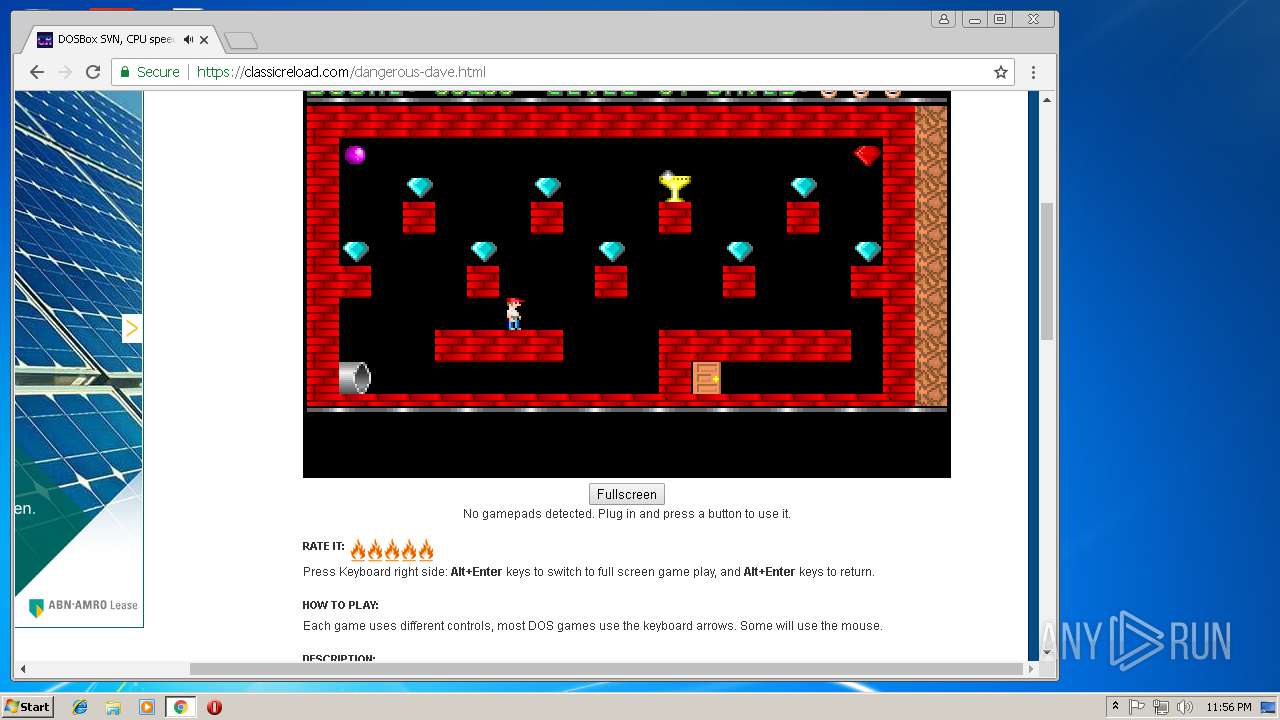
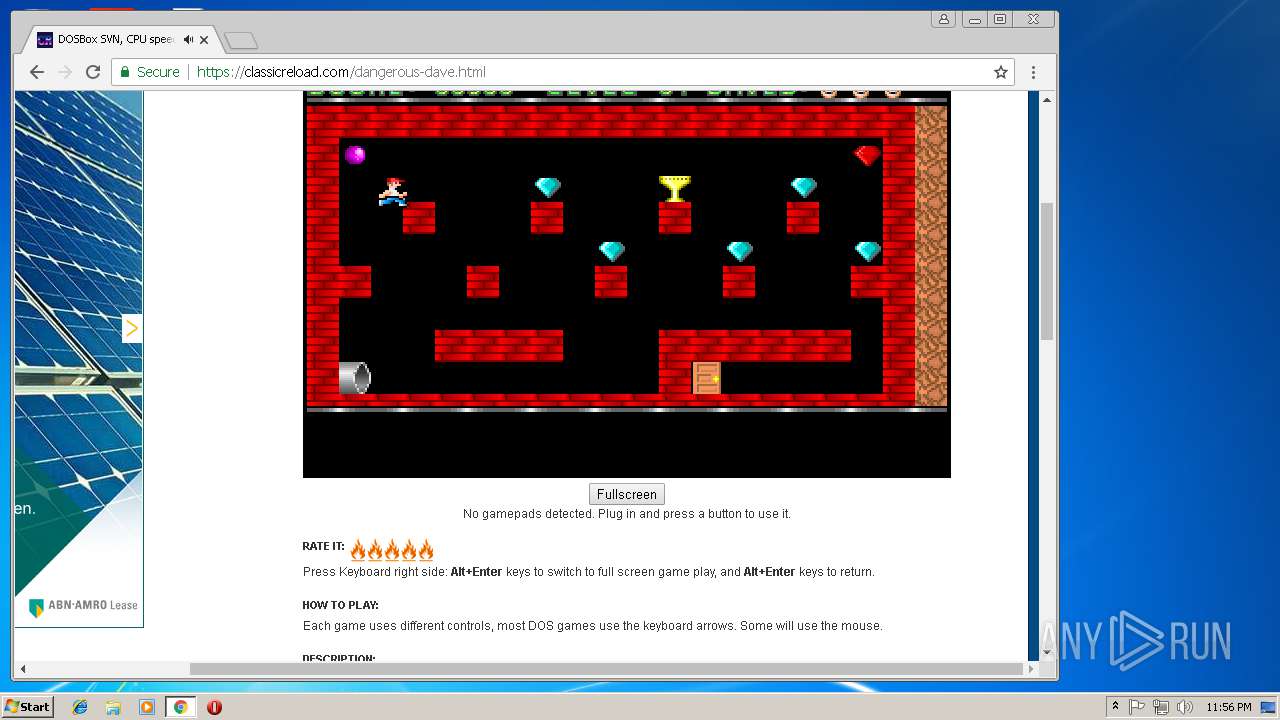
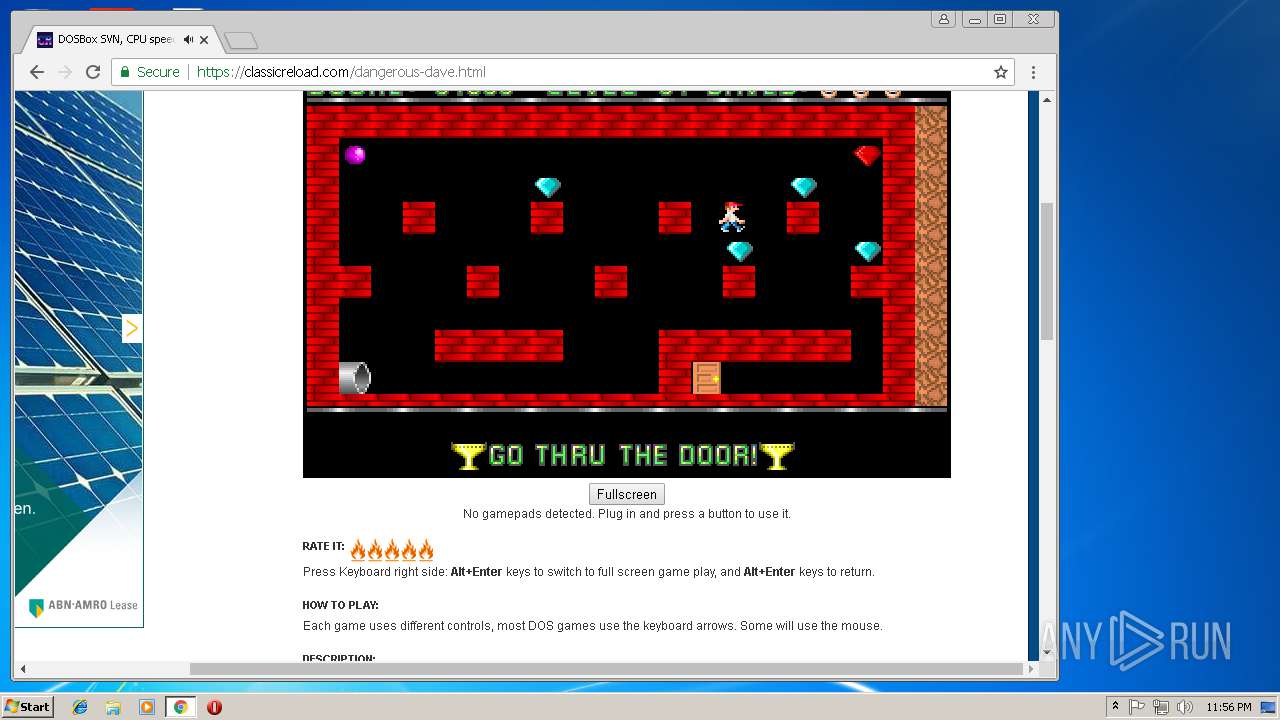
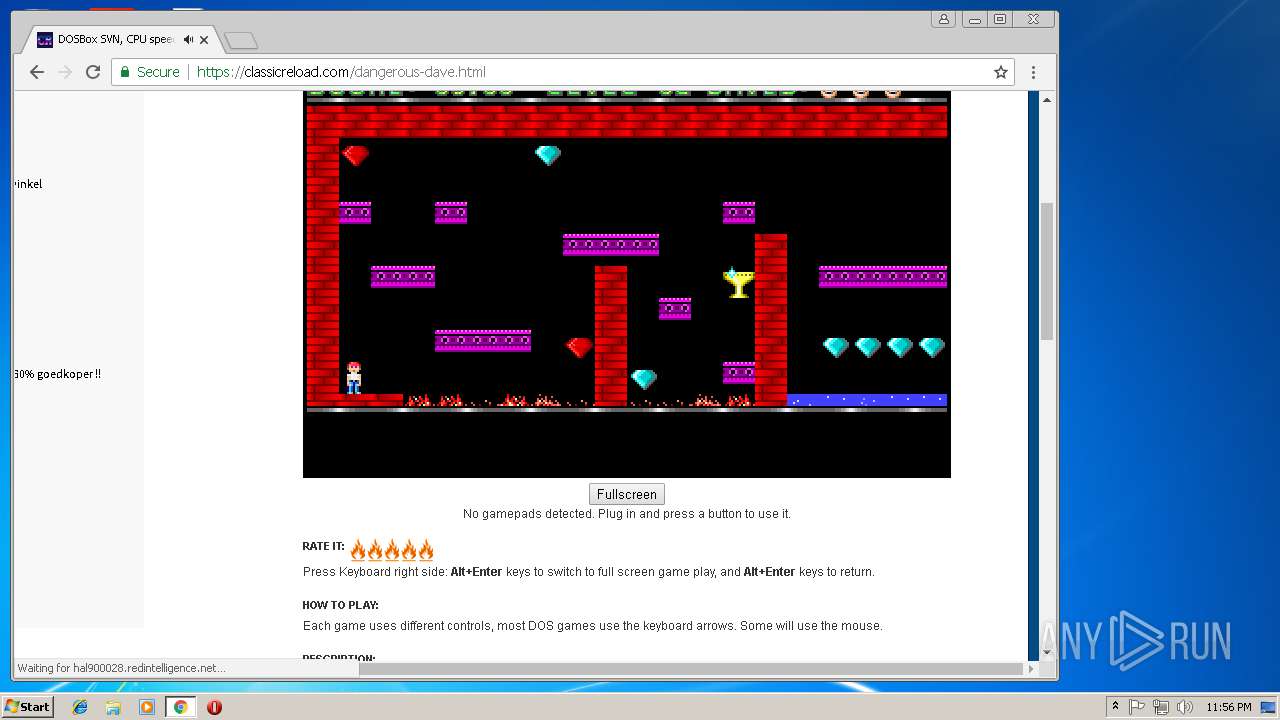
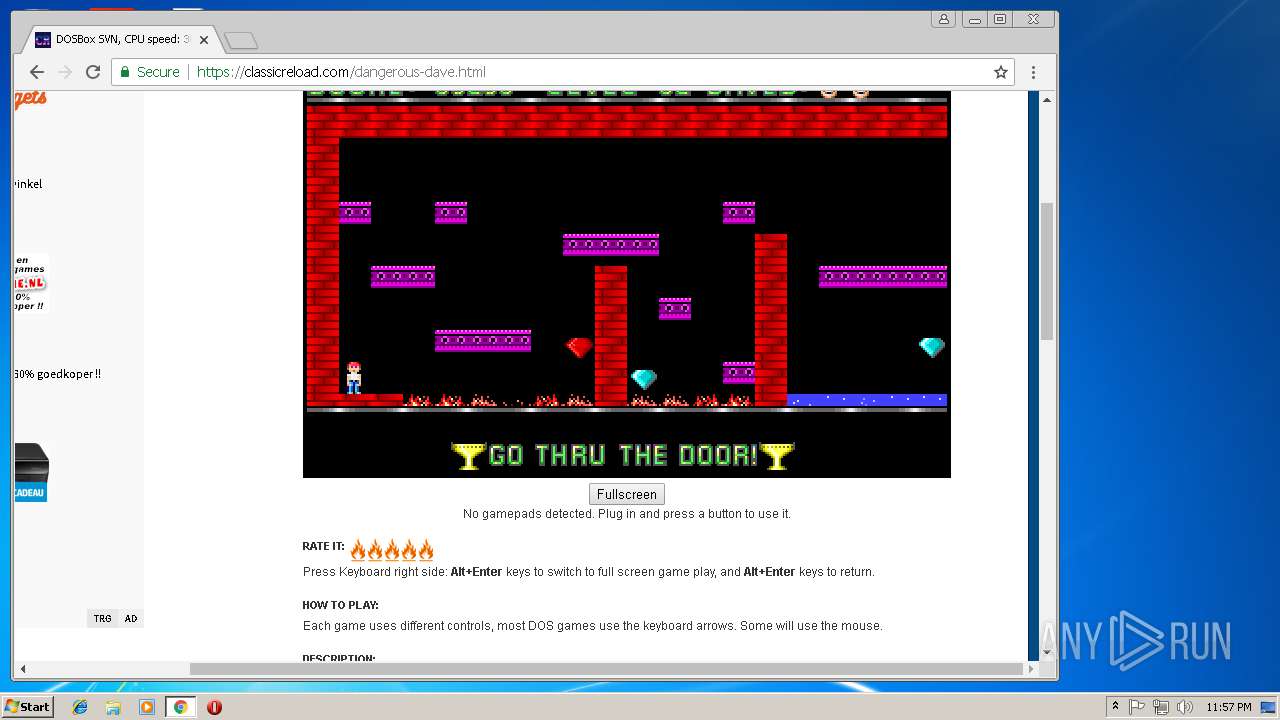
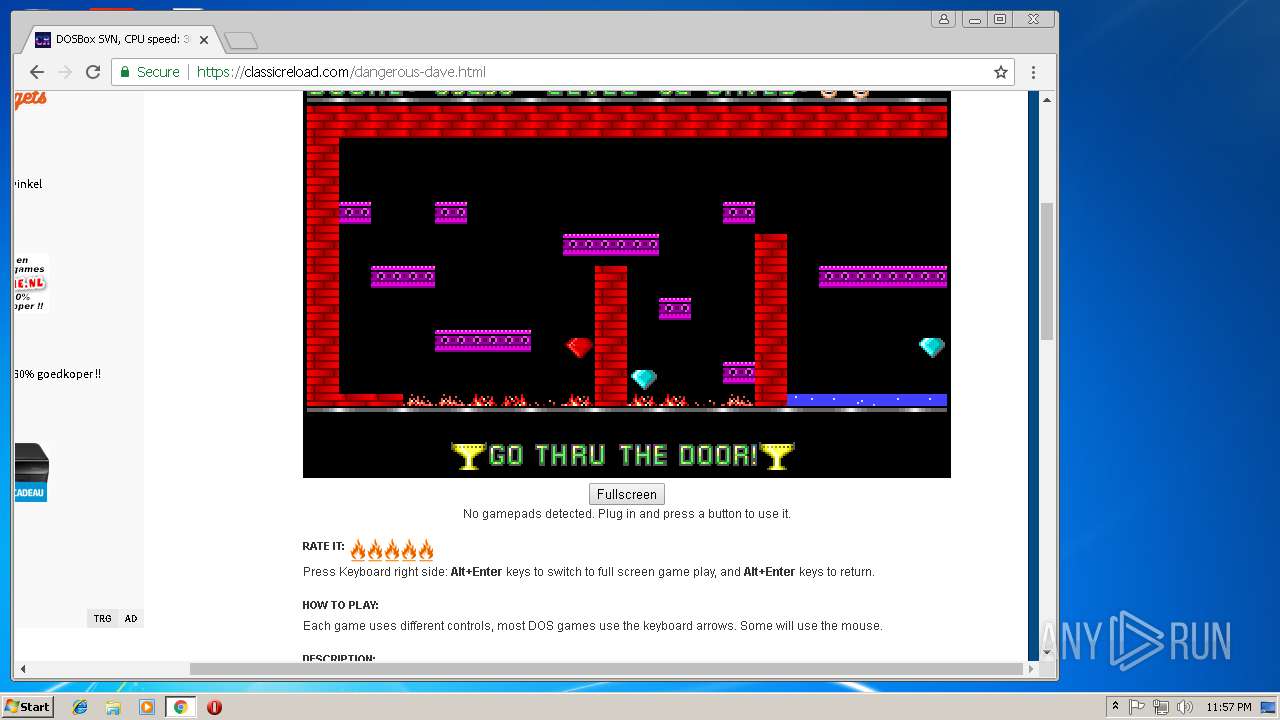
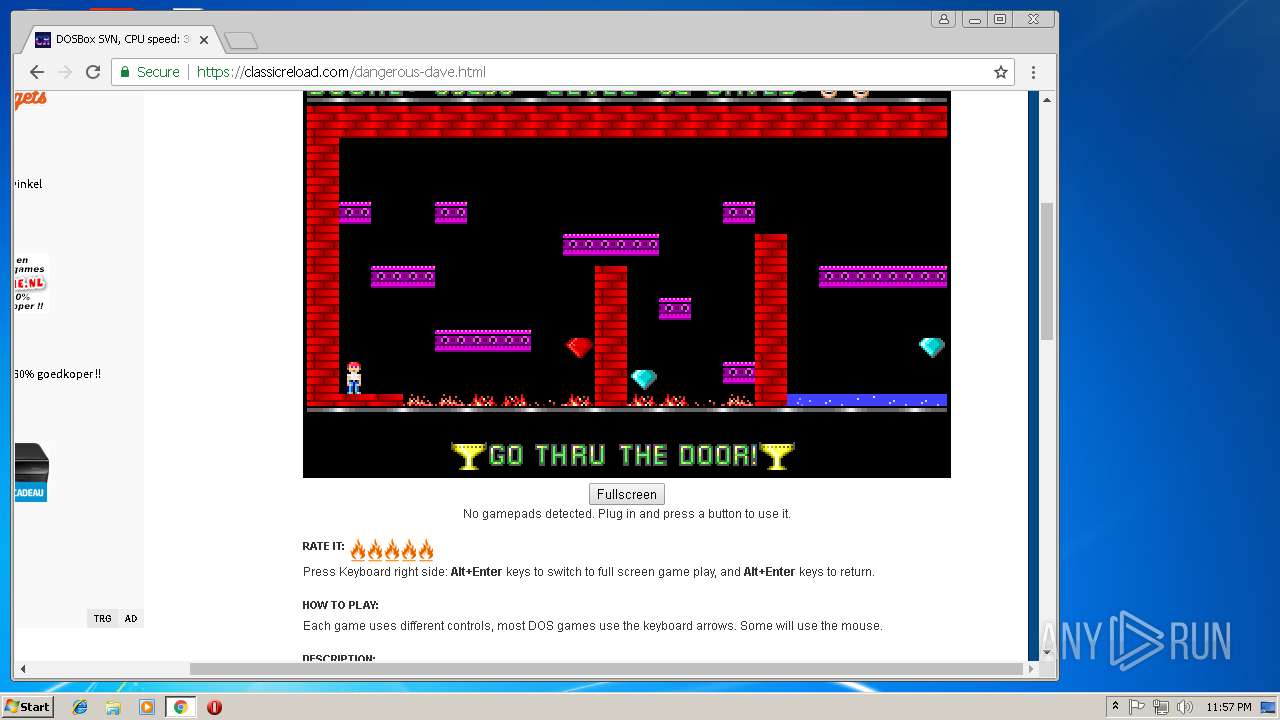
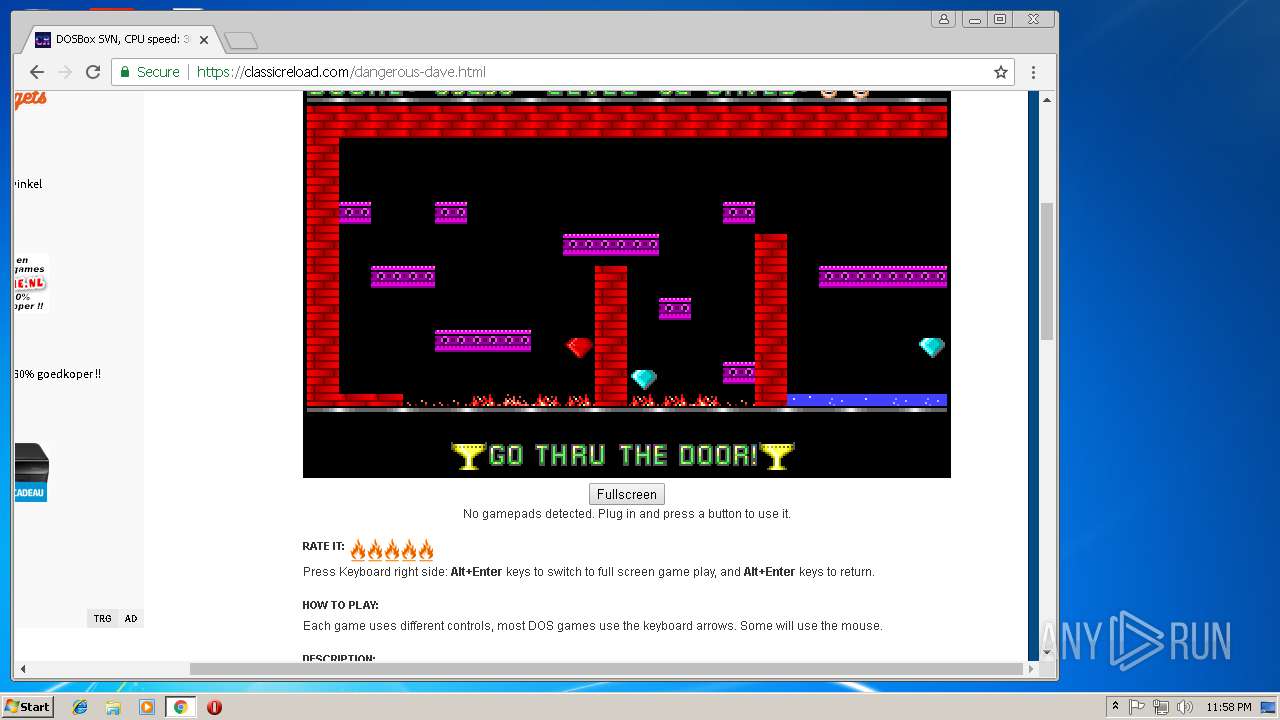
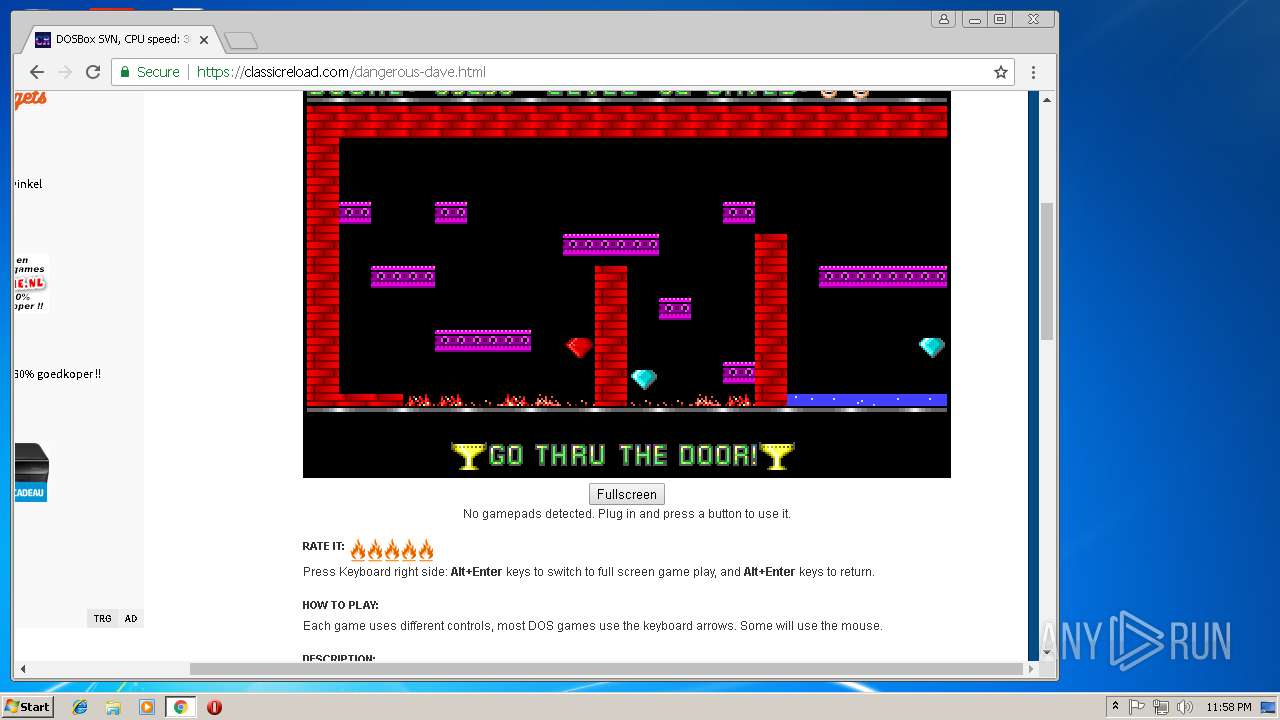
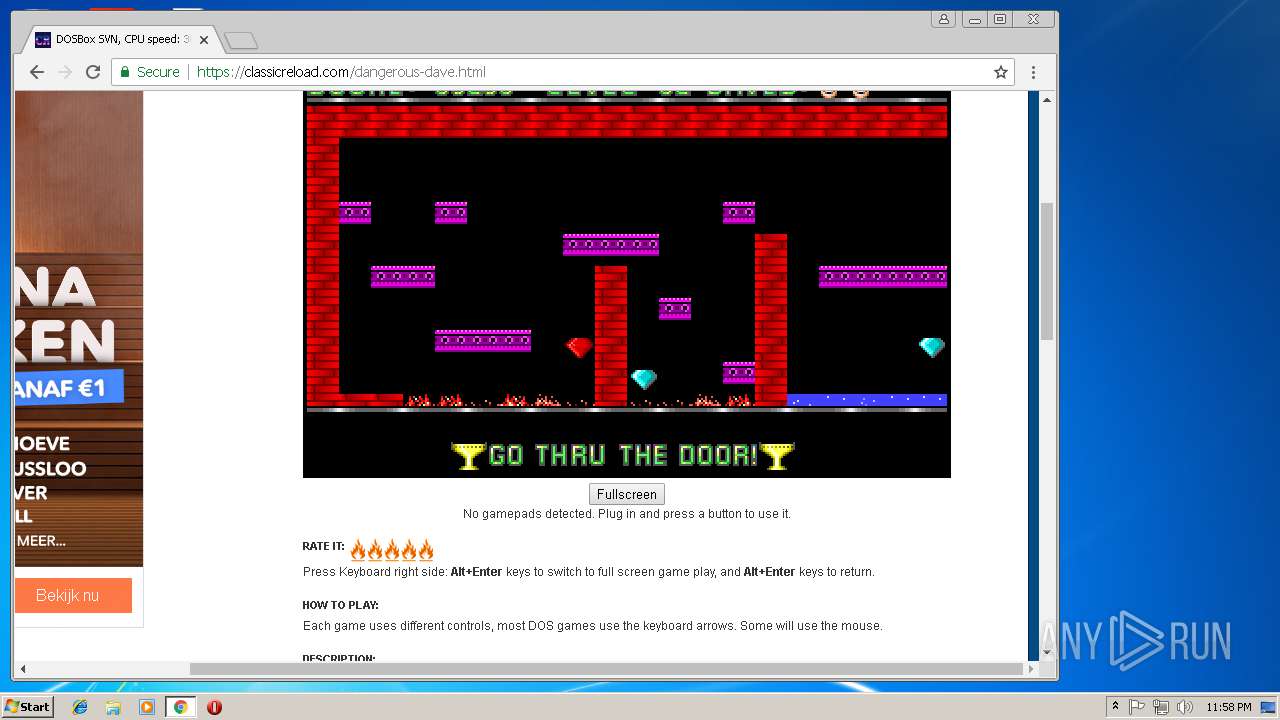
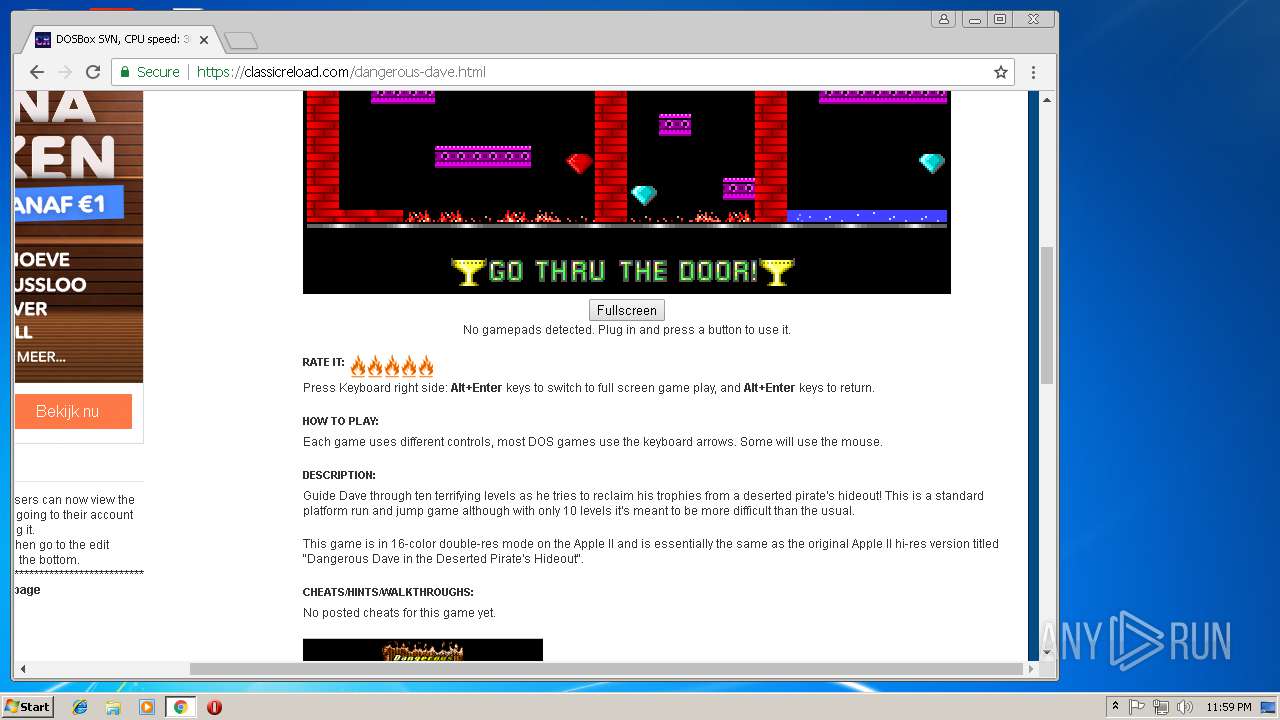
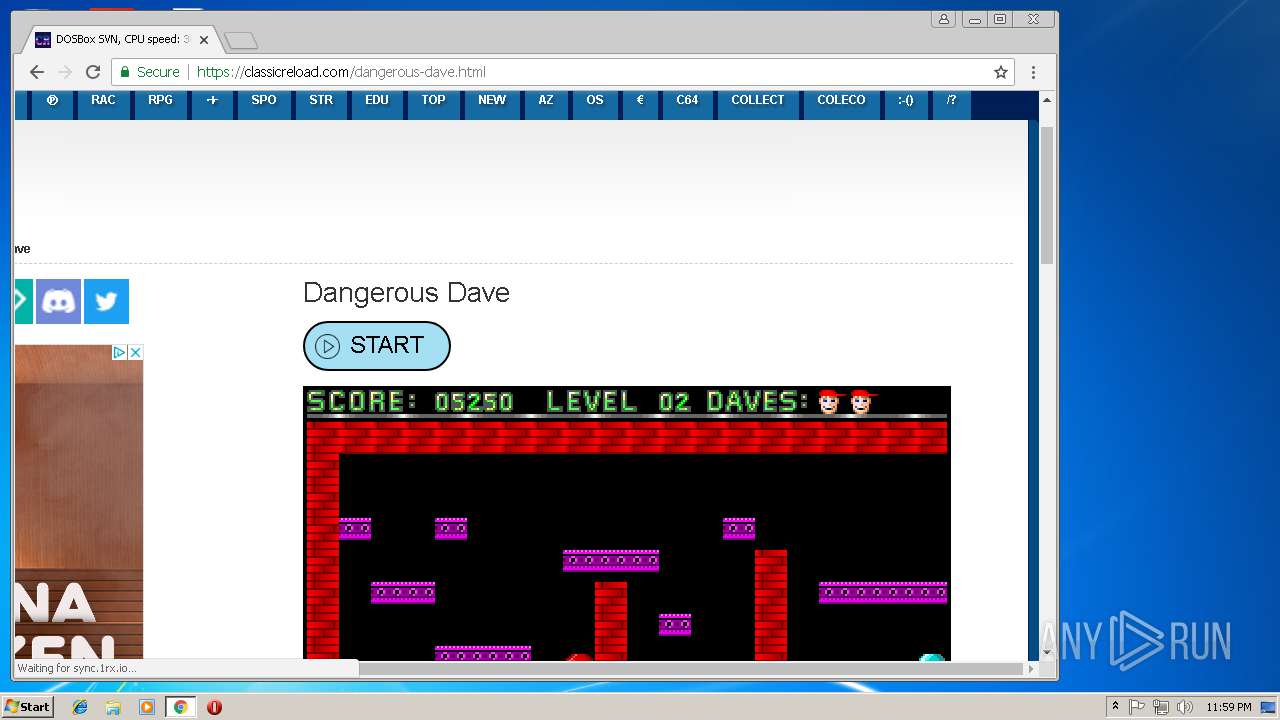
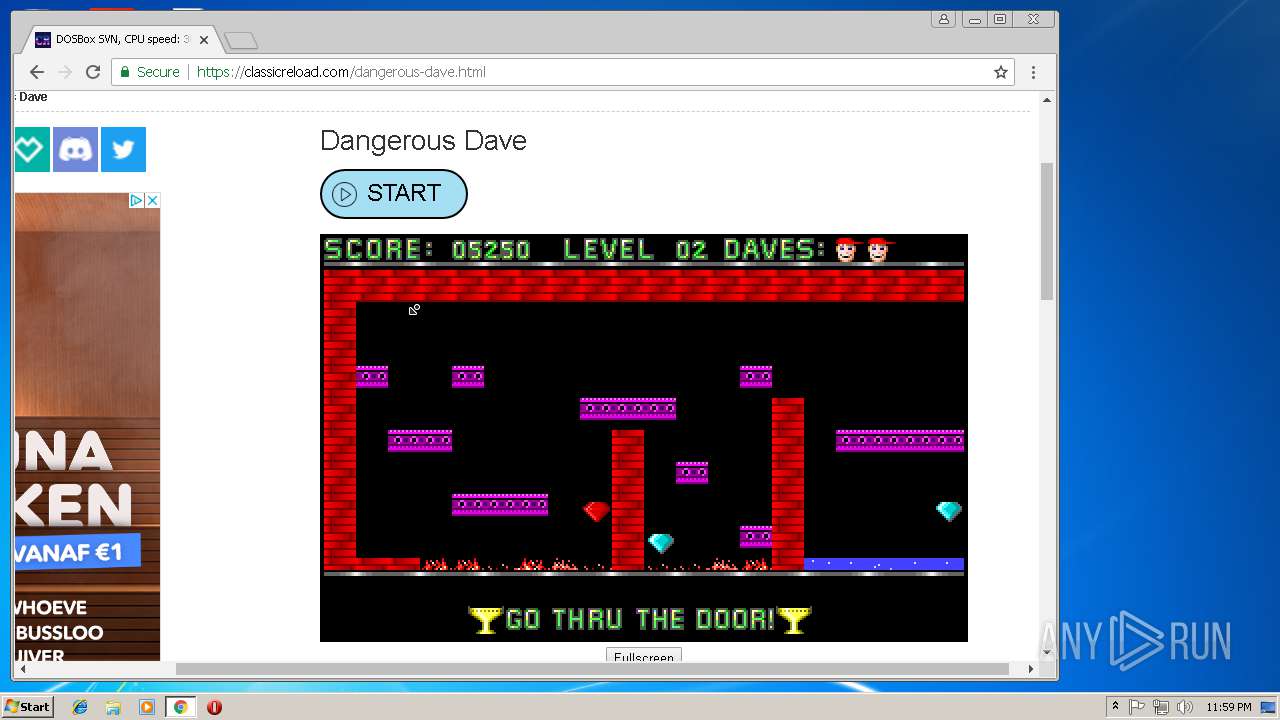
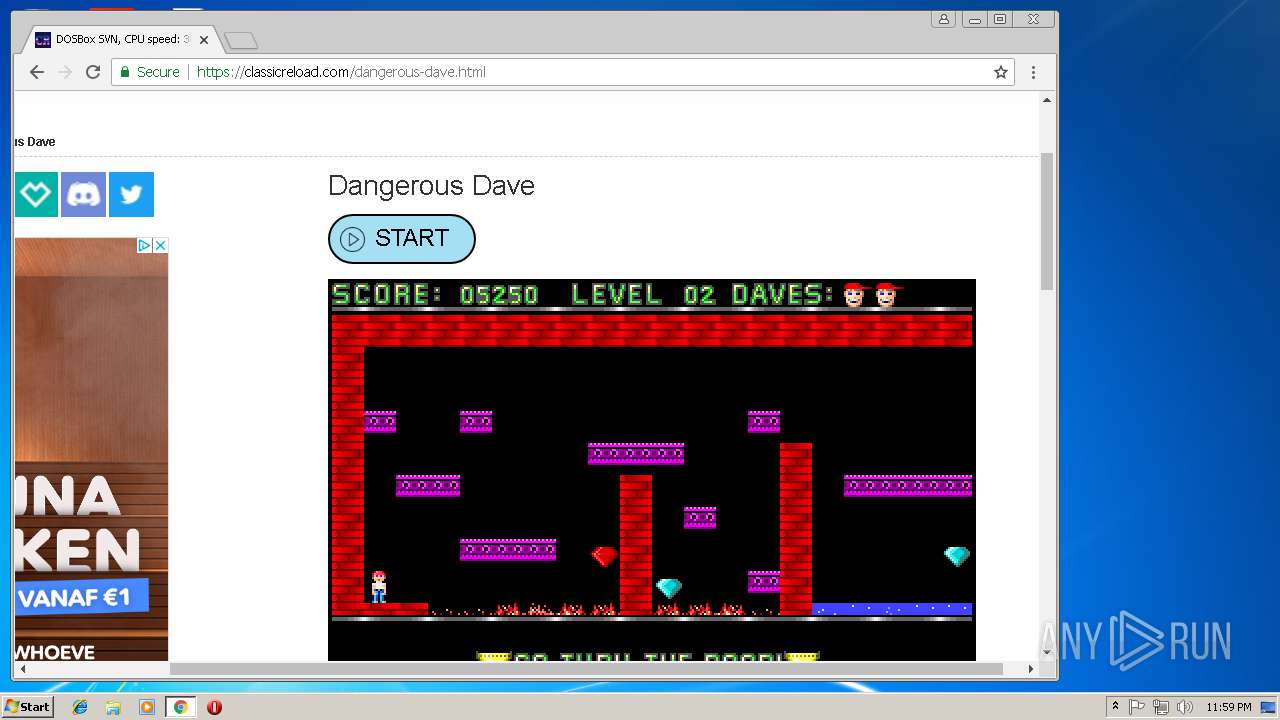
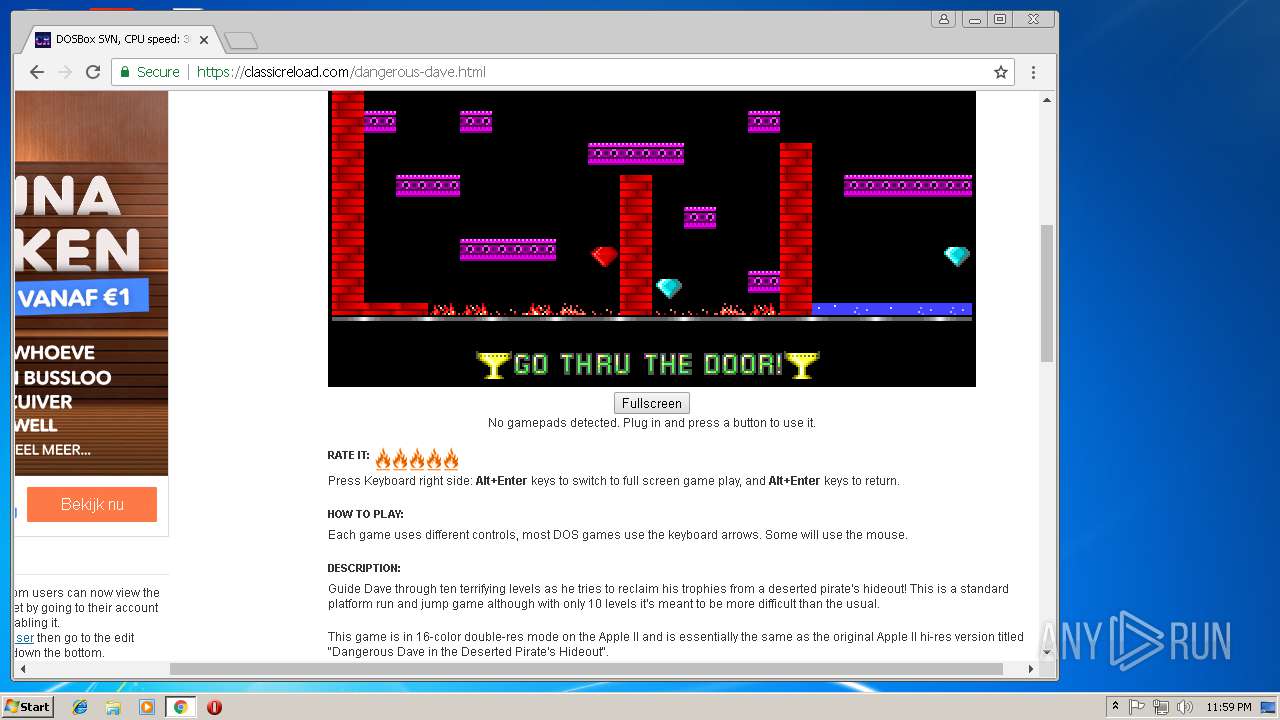
| Title: | ClassicReload.com | Game and Software Preservation |
| ContentType: | text/html; charset=utf-8 |
| themeColor: | #054b81 |
Total processes
48
Monitored processes
18
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1028 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=880,8169839878223957078,9913503104520661592,131072 --enable-features=PasswordImport --lang=en-US --no-sandbox --service-request-channel-token=BE8148308F31DD9B5527B2C3821DED55 --mojo-platform-channel-handle=3460 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 1208 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=880,8169839878223957078,9913503104520661592,131072 --enable-features=PasswordImport --disable-gpu-compositing --service-pipe-token=6415F8E8B7AB4B3D8A0EA4AEC69C0D32 --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=6415F8E8B7AB4B3D8A0EA4AEC69C0D32 --renderer-client-id=14 --mojo-platform-channel-handle=2064 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 1528 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=880,8169839878223957078,9913503104520661592,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=44DF4F941EADF8A80E3A1053B4C99156 --mojo-platform-channel-handle=2676 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 1836 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=880,8169839878223957078,9913503104520661592,131072 --enable-features=PasswordImport --disable-gpu-compositing --service-pipe-token=D7D31F09A833DEC0C1B05DEA86F1909E --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=D7D31F09A833DEC0C1B05DEA86F1909E --renderer-client-id=8 --mojo-platform-channel-handle=3948 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 2248 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=880,8169839878223957078,9913503104520661592,131072 --enable-features=PasswordImport --service-pipe-token=E0DF9733EFE85F5FBCC889196F269FAB --lang=en-US --instant-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=E0DF9733EFE85F5FBCC889196F269FAB --renderer-client-id=5 --mojo-platform-channel-handle=1924 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 2320 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=880,8169839878223957078,9913503104520661592,131072 --enable-features=PasswordImport --disable-gpu-compositing --service-pipe-token=775A2660E200ECEA0E749D1501CDD5D9 --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=775A2660E200ECEA0E749D1501CDD5D9 --renderer-client-id=10 --mojo-platform-channel-handle=5156 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 2796 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=880,8169839878223957078,9913503104520661592,131072 --enable-features=PasswordImport --disable-gpu-sandbox --gpu-preferences=KAAAAAAAAACAAwBAAQAAAAAAAAAAAGAAEAAAAAAAAAAAAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAKAAAAEAAAAAAAAAAAAAAACwAAABAAAAAAAAAAAQAAAAoAAAAQAAAAAAAAAAEAAAALAAAA --service-request-channel-token=3069A7AC7D6B758C4EB47D5AF1B4A87D --mojo-platform-channel-handle=5936 /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 2984 | "C:\Program Files\Internet Explorer\iexplore.exe" C:\Users\admin\AppData\Local\Temp\index.html | C:\Program Files\Internet Explorer\iexplore.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 1 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3144 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=880,8169839878223957078,9913503104520661592,131072 --enable-features=PasswordImport --gpu-preferences=KAAAAAAAAACAAwBAAQAAAAAAAAAAAGAAEAAAAAAAAAAAAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAKAAAAEAAAAAAAAAAAAAAACwAAABAAAAAAAAAAAQAAAAoAAAAQAAAAAAAAAAEAAAALAAAA --service-request-channel-token=AD0779E35A5243314FCFAC47C31A5B10 --mojo-platform-channel-handle=856 --ignored=" --type=renderer " /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 3148 | "C:\Program Files\Google\Chrome\Application\chrome.exe" | C:\Program Files\Google\Chrome\Application\chrome.exe | explorer.exe | ||||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
Total events
965
Read events
818
Write events
141
Delete events
6
Modification events
| (PID) Process: | (3416) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Ext\Stats\{761497BB-D6F0-462C-B6EB-D4DAF1D92D43}\iexplore |
| Operation: | write | Name: | Type |
Value: 3 | |||
| (PID) Process: | (3416) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Ext\Stats\{761497BB-D6F0-462C-B6EB-D4DAF1D92D43}\iexplore |
| Operation: | write | Name: | Count |
Value: 3 | |||
| (PID) Process: | (3416) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Ext\Stats\{761497BB-D6F0-462C-B6EB-D4DAF1D92D43}\iexplore |
| Operation: | write | Name: | Time |
Value: E3070100020016001700360029007703 | |||
| (PID) Process: | (3416) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Ext\Stats\{761497BB-D6F0-462C-B6EB-D4DAF1D92D43}\iexplore |
| Operation: | write | Name: | LoadTime |
Value: 12 | |||
| (PID) Process: | (3416) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Ext\Stats\{B4F3A835-0E21-4959-BA22-42B3008E02FF}\iexplore |
| Operation: | write | Name: | Type |
Value: 3 | |||
| (PID) Process: | (3416) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Ext\Stats\{B4F3A835-0E21-4959-BA22-42B3008E02FF}\iexplore |
| Operation: | write | Name: | Count |
Value: 3 | |||
| (PID) Process: | (3416) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Ext\Stats\{B4F3A835-0E21-4959-BA22-42B3008E02FF}\iexplore |
| Operation: | write | Name: | Time |
Value: E3070100020016001700360029008703 | |||
| (PID) Process: | (2984) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (2984) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (2984) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
Executable files
0
Suspicious files
144
Text files
151
Unknown types
9
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2984 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\RB73MZ6Y\favicon[1].ico | — | |
MD5:— | SHA256:— | |||
| 2984 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\Internet Explorer\Services\search_{0633EE93-D776-472f-A0FF-E1416B8B2E3A}.ico | — | |
MD5:— | SHA256:— | |||
| 2984 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\~DF8EFA3714D44CEA42.TMP | — | |
MD5:— | SHA256:— | |||
| 2984 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\~DF7E33559E12787147.TMP | — | |
MD5:— | SHA256:— | |||
| 2984 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\~DFA5FAFF0EE969D2D0.TMP | — | |
MD5:— | SHA256:— | |||
| 3148 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\9da00ba0-ce6b-4193-be79-9de2d624d87d.tmp | — | |
MD5:— | SHA256:— | |||
| 3148 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Download Service\EntryDB\000016.dbtmp | — | |
MD5:— | SHA256:— | |||
| 3416 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\0UU90R59\js[1] | text | |
MD5:— | SHA256:— | |||
| 3148 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000016.dbtmp | — | |
MD5:— | SHA256:— | |||
| 3148 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Last Version | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
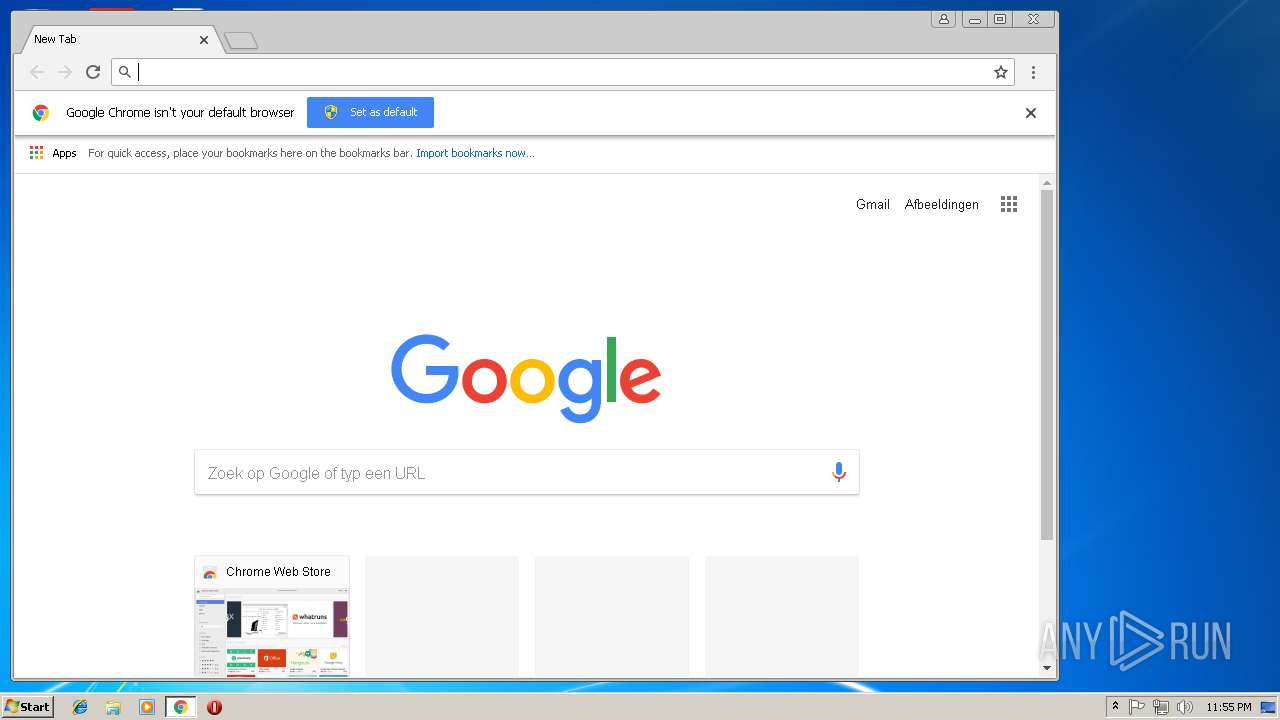
HTTP(S) requests
11
TCP/UDP connections
900
DNS requests
332
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
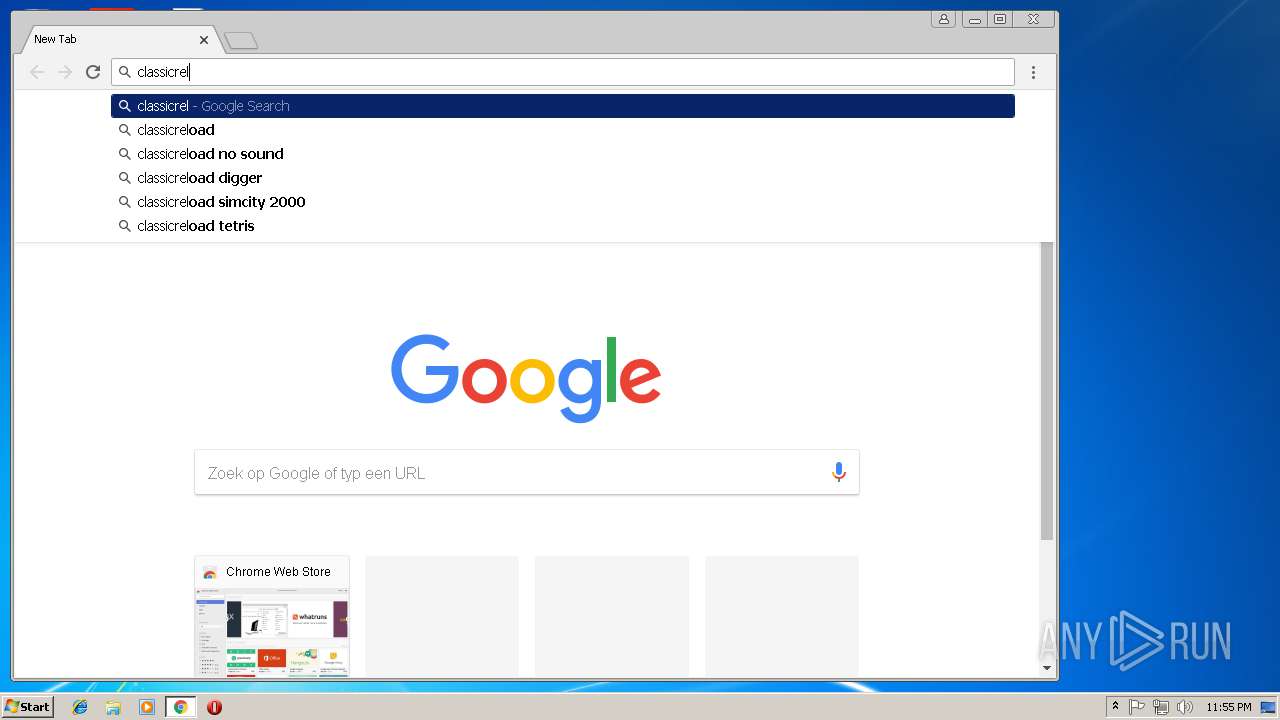
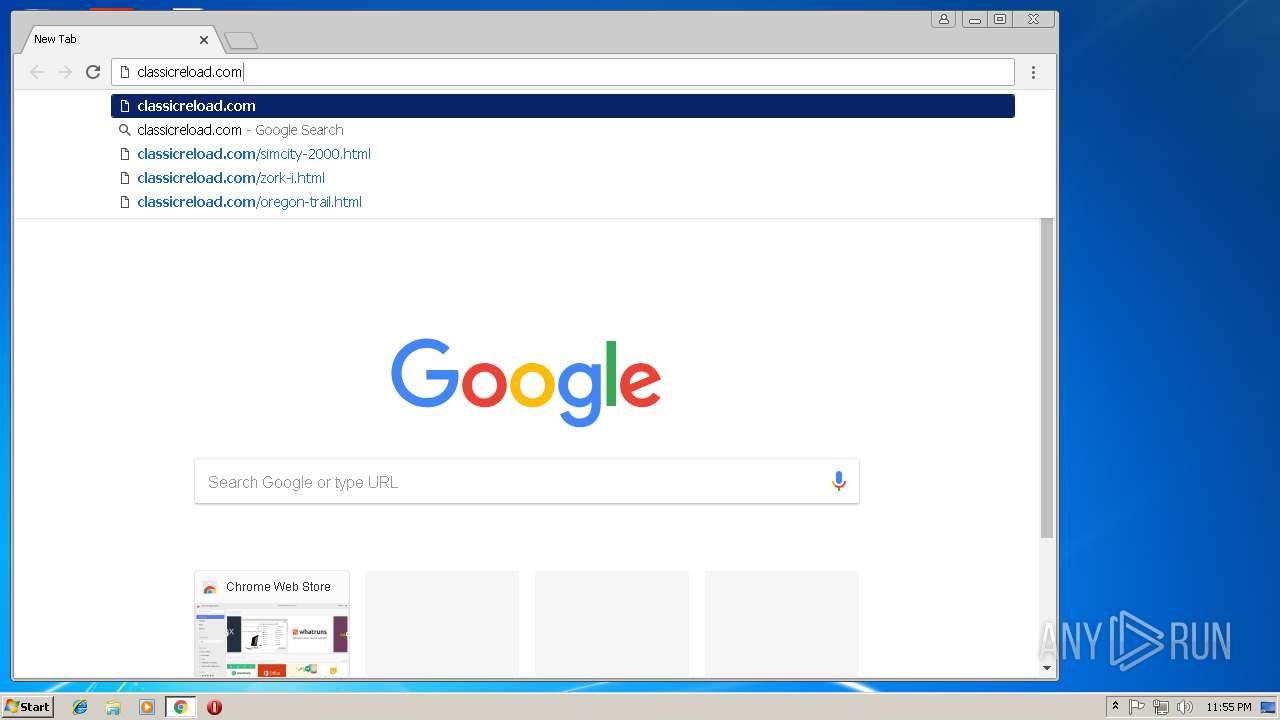
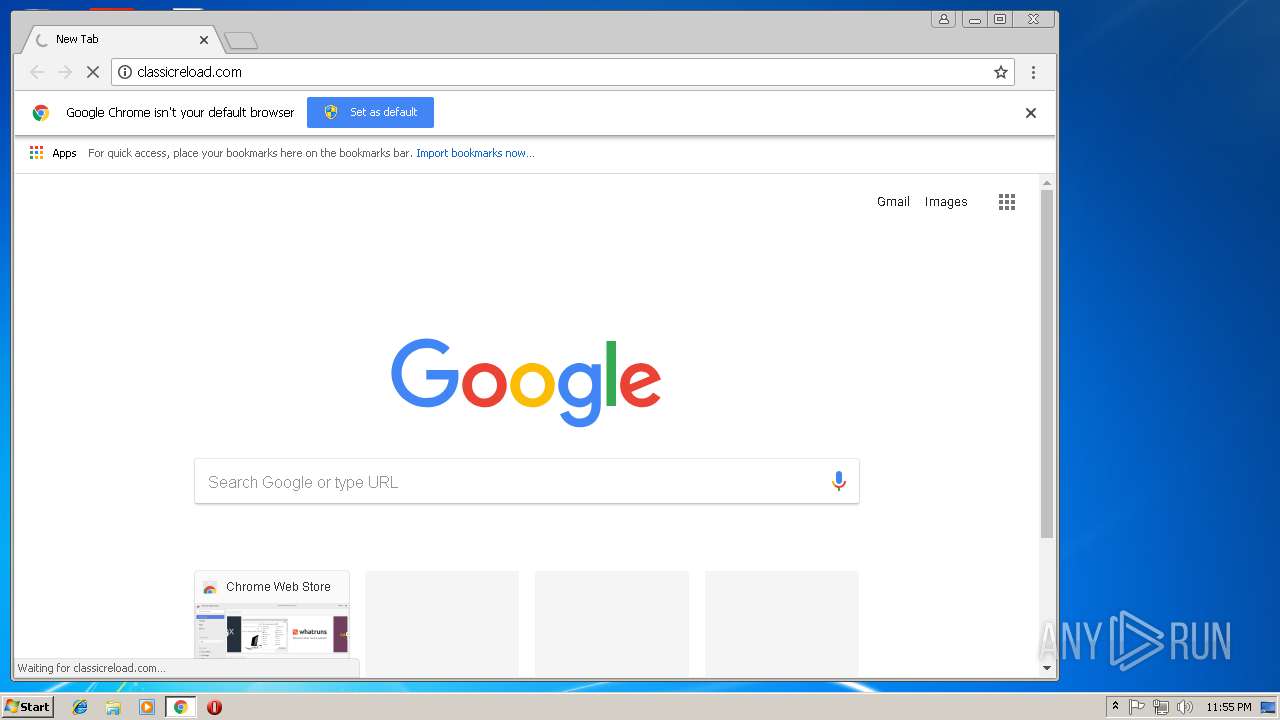
3148 | chrome.exe | GET | 301 | 104.31.64.36:80 | http://classicreload.com/ | US | — | — | whitelisted |
3148 | chrome.exe | GET | 200 | 91.199.212.52:80 | http://crt.comodoca.com/COMODOECCAddTrustCA.crt | GB | der | 980 b | whitelisted |
3148 | chrome.exe | GET | 200 | 23.0.34.190:80 | http://ssl.trustwave.com/issuers/STCA.crt | NL | der | 956 b | whitelisted |
3148 | chrome.exe | GET | 200 | 205.185.216.10:80 | http://www.download.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab | US | compressed | 55.2 Kb | whitelisted |
3148 | chrome.exe | GET | 200 | 91.199.212.52:80 | http://crt.comodoca.com/COMODORSAAddTrustCA.crt | GB | der | 1.37 Kb | whitelisted |
3148 | chrome.exe | GET | 200 | 188.121.36.237:80 | http://certificates.godaddy.com/repository/gdig2.crt | NL | der | 1.21 Kb | whitelisted |
3148 | chrome.exe | GET | 200 | 23.111.11.204:80 | http://repository.certum.pl/ctnca.cer | US | der | 959 b | whitelisted |
3148 | chrome.exe | GET | 200 | 104.16.240.184:80 | http://cacerts.digicert.com/DigiCertSHA2SecureServerCA.crt | US | der | 1.15 Kb | whitelisted |
3148 | chrome.exe | GET | 200 | 52.85.188.165:80 | http://x.ss2.us/x.cer | US | der | 1.27 Kb | whitelisted |
3148 | chrome.exe | GET | 200 | 205.185.216.10:80 | http://www.download.windowsupdate.com/msdownload/update/v3/static/trustedr/en/47BEABC922EAE80E78783462A79F45C254FDE68B.crt | US | der | 969 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3416 | iexplore.exe | 104.31.65.36:443 | classicreload.com | Cloudflare Inc | US | shared |
2984 | iexplore.exe | 13.107.21.200:80 | www.bing.com | Microsoft Corporation | US | whitelisted |
3148 | chrome.exe | 172.217.18.163:443 | www.google.nl | Google Inc. | US | whitelisted |
3148 | chrome.exe | 216.58.205.234:443 | ajax.googleapis.com | Google Inc. | US | whitelisted |
3148 | chrome.exe | 104.31.64.36:443 | classicreload.com | Cloudflare Inc | US | shared |
3148 | chrome.exe | 104.31.64.36:80 | classicreload.com | Cloudflare Inc | US | shared |
— | — | 104.31.65.36:443 | classicreload.com | Cloudflare Inc | US | shared |
3416 | iexplore.exe | 172.217.16.170:443 | ajax.googleapis.com | Google Inc. | US | whitelisted |
4 | System | 104.28.27.231:445 | cdn.adapex.io | Cloudflare Inc | US | shared |
4 | System | 104.28.26.231:445 | cdn.adapex.io | Cloudflare Inc | US | shared |
DNS requests
Domain | IP | Reputation |
|---|---|---|
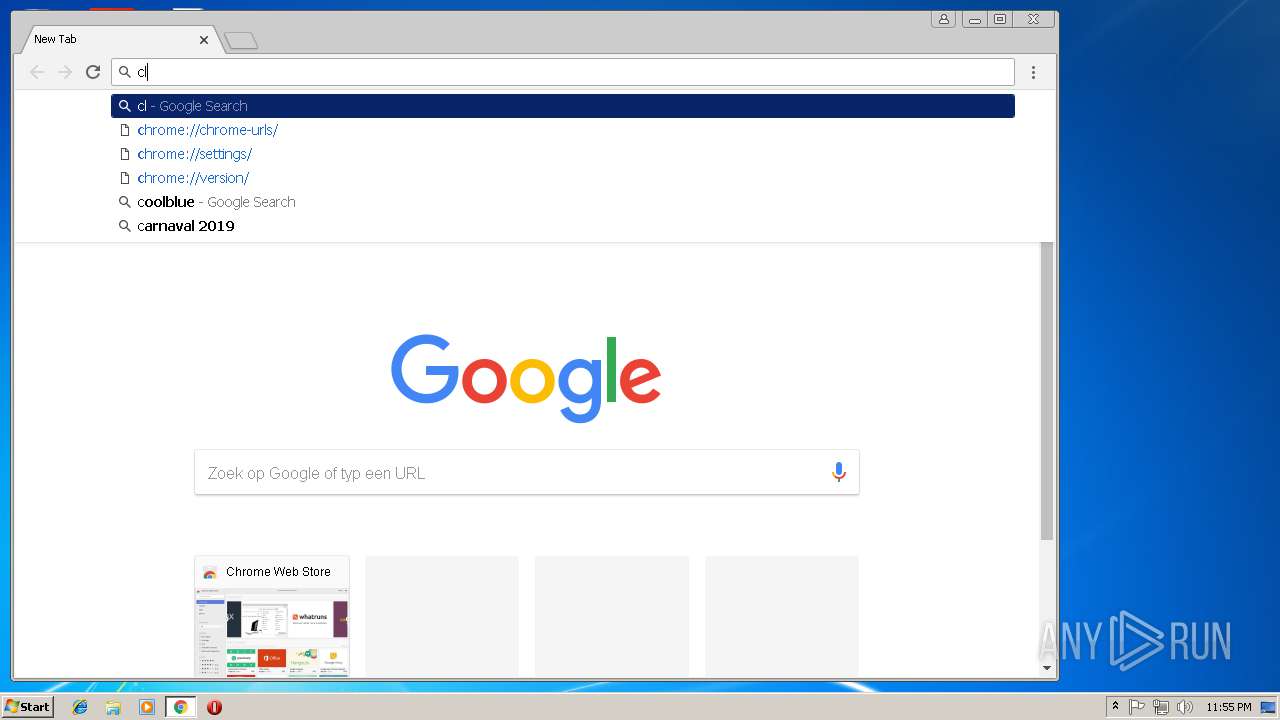
classicreload.com |
| whitelisted |
www.bing.com |
| whitelisted |
ajax.googleapis.com |
| whitelisted |
cdn.adapex.io |
| malicious |
www.googletagmanager.com |
| whitelisted |
imasdk.googleapis.com |
| whitelisted |
clientservices.googleapis.com |
| whitelisted |
www.google.de |
| whitelisted |
www.gstatic.com |
| whitelisted |
safebrowsing.googleapis.com |
| whitelisted |