| File name: | bat2exe.exe |
| Full analysis: | https://app.any.run/tasks/f8d0ebef-d6a6-4ec7-84d4-aeb834acaa56 |
| Verdict: | Malicious activity |
| Analysis date: | November 12, 2024, 01:10:55 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, 4 sections |
| MD5: | 915F2CA3FD04CC86E7912FE3ADE1024A |
| SHA1: | 985C048AF406923C1970028FE7EA2AD7356BA81B |
| SHA256: | 7CF70E58E783FC9AC42C4F9E5135AF827EF66AF709F37D6E7A871B4CE941BCF1 |
| SSDEEP: | 49152:3wmFLmPOMNOruPBXhihZE8/zoiiMLuYt3KmheanenxpLxwiQawDe7AKV+VkNNsjP:37LmPORu5X8jEEE/MSeLh7enxbwt67At |
MALICIOUS
No malicious indicators.SUSPICIOUS
The process executes VB scripts
- cmd.exe (PID: 5624)
Executable content was dropped or overwritten
- bat2exe.exe (PID: 4072)
Drops 7-zip archiver for unpacking
- bat2exe.exe (PID: 4072)
Starts CMD.EXE for commands execution
- cmd.exe (PID: 6628)
- bat2exe.exe (PID: 4072)
Executing commands from a ".bat" file
- cmd.exe (PID: 6628)
Application launched itself
- cmd.exe (PID: 6628)
Executing commands from ".cmd" file
- bat2exe.exe (PID: 4072)
- cmd.exe (PID: 6628)
Reads security settings of Internet Explorer
- bat2exe.exe (PID: 4072)
INFO
Reads security settings of Internet Explorer
- cscript.exe (PID: 1112)
Reads the computer name
- bat2exe.exe (PID: 4072)
Create files in a temporary directory
- bat2exe.exe (PID: 4072)
Process checks computer location settings
- bat2exe.exe (PID: 4072)
Starts MODE.COM to configure console settings
- mode.com (PID: 3828)
The process uses the downloaded file
- bat2exe.exe (PID: 4072)
Checks supported languages
- mode.com (PID: 3828)
- bat2exe.exe (PID: 4072)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .dll | | | Win32 Dynamic Link Library (generic) (43.5) |
|---|---|---|
| .exe | | | Win32 Executable (generic) (29.8) |
| .exe | | | Generic Win/DOS Executable (13.2) |
| .exe | | | DOS Executable Generic (13.2) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2010:11:18 18:41:55+00:00 |
| ImageFileCharacteristics: | No relocs, Executable, No line numbers, No symbols, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 6 |
| CodeSize: | 22016 |
| InitializedDataSize: | 19456 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x643f |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 2.1.0.0 |
| ProductVersionNumber: | 2.1.0.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Windows NT 32-bit |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Unicode |
| CompanyName: | Igor Pavlov |
| FileDescription: | Created by BAT2EXE.net |
| FileVersion: | 2.1 |
| InternalName: | 7zS2.sfx |
| LegalCopyright: | - |
| OriginalFileName: | 7zS2.sfx.exe |
| ProductName: | 7-Zip |
| ProductVersion: | 2.1 |
Total processes
129
Monitored processes
7
Malicious processes
1
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1112 | cscript //nologo bin\browse.vbs | C:\Windows\SysWOW64\cscript.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft ® Console Based Script Host Exit code: 0 Version: 5.812.10240.16384 Modules
| |||||||||||||||
| 3828 | MODE 90,50 | C:\Windows\SysWOW64\mode.com | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: DOS Device MODE Utility Exit code: 0 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
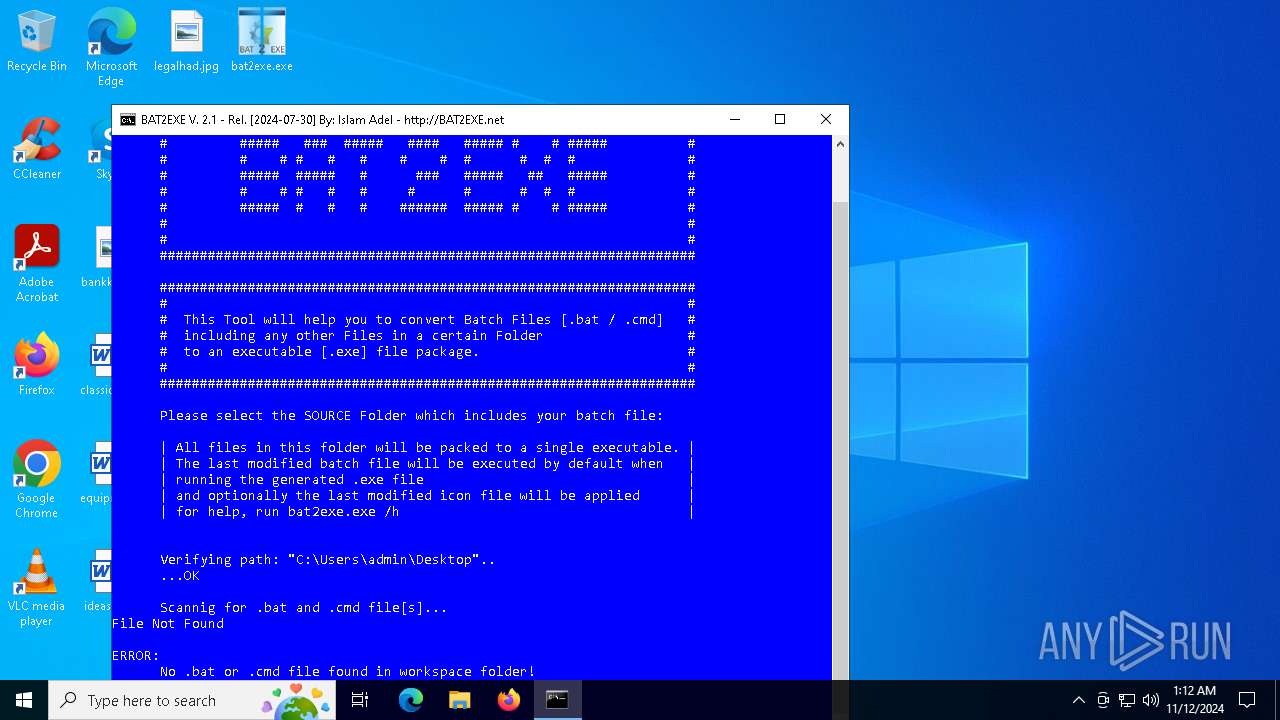
| 4032 | C:\WINDOWS\system32\cmd.exe /c dir /b /OD "C:\Users\admin\Desktop\*.bat" "C:\Users\admin\Desktop\*.cmd" | C:\Windows\SysWOW64\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 1 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4072 | "C:\Users\admin\Desktop\bat2exe.exe" | C:\Users\admin\Desktop\bat2exe.exe | explorer.exe | ||||||||||||
User: admin Company: Igor Pavlov Integrity Level: MEDIUM Description: Created by BAT2EXE.net Version: 2.1 Modules
| |||||||||||||||
| 5624 | C:\WINDOWS\system32\cmd.exe /c cscript //nologo bin\browse.vbs | C:\Windows\SysWOW64\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6564 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6628 | C:\WINDOWS\system32\cmd.exe /c ""C:\Users\admin\AppData\Local\Temp\7z897BCFE8\bat2exe.cmd" " | C:\Windows\SysWOW64\cmd.exe | — | bat2exe.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
1 165
Read events
1 162
Write events
3
Delete events
0
Modification events
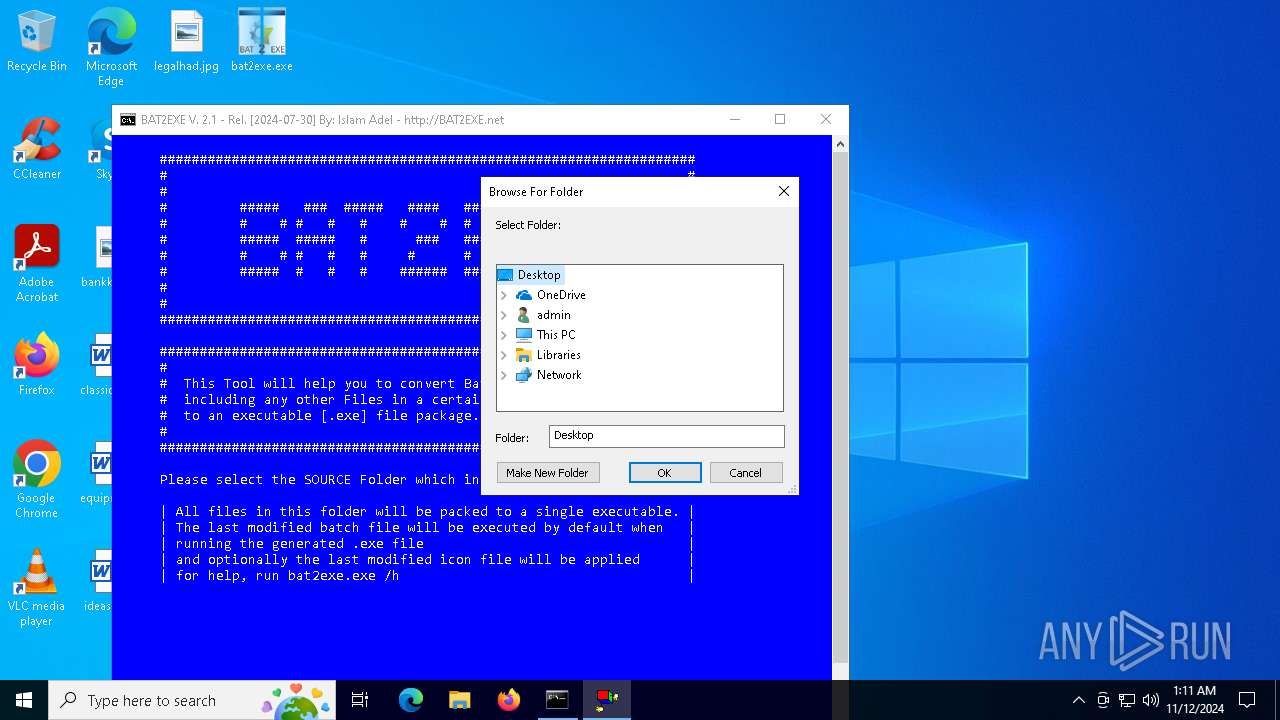
| (PID) Process: | (1112) cscript.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer |
| Operation: | write | Name: | GlobalAssocChangedCounter |
Value: 96 | |||
| (PID) Process: | (1112) cscript.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer |
| Operation: | write | Name: | Browse For Folder Width |
Value: 318 | |||
| (PID) Process: | (1112) cscript.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer |
| Operation: | write | Name: | Browse For Folder Height |
Value: 288 | |||
Executable files
5
Suspicious files
0
Text files
3
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 4072 | bat2exe.exe | C:\Users\admin\AppData\Local\Temp\7z897BCFE8\bat2exe.cmd | text | |
MD5:A00863A11227E1E9DD8045E293009C33 | SHA256:A08DC568B77D7A1673319282B3CA4128898A70FCC827C9B7DDEFD180AEB64B9C | |||
| 4072 | bat2exe.exe | C:\Users\admin\AppData\Local\Temp\7z897BCFE8\bin\browse.vbs | text | |
MD5:8580D8CAB38506F200F4D935EDCC19BE | SHA256:CBAF396FF11D723E0FFF497C6B7AFEDABE6975BCB32B7512058732911111AB15 | |||
| 4072 | bat2exe.exe | C:\Users\admin\AppData\Local\Temp\7z897BCFE8\bin\rcedit-x64.exe | executable | |
MD5:E0CB28BF051D6311C1DCA32F392C7D5E | SHA256:3E7801DB1A5EDBEC91B49A24A094AAD776CB4515488EA5A4CA2289C400EADE2A | |||
| 4072 | bat2exe.exe | C:\Users\admin\AppData\Local\Temp\7z897BCFE8\bin\7z.dll | executable | |
MD5:0009BD5E13766D11A23289734B383CBE | SHA256:3691ADCEFC6DA67EEDD02A1B1FC7A21894AFD83ECF1B6216D303ED55A5F8D129 | |||
| 4072 | bat2exe.exe | C:\Users\admin\AppData\Local\Temp\7z897BCFE8\bin\7zS2.sfx | executable | |
MD5:AD7ABF981C951F530496BAD48D8FB74D | SHA256:668A0C24AB22CACE37A36DB58990B74F5090F5CE9DCE6A71CAA896457AC7F9D5 | |||
| 4072 | bat2exe.exe | C:\Users\admin\AppData\Local\Temp\7z897BCFE8\bin\choice.exe | executable | |
MD5:E8F8B1058775103AC8BA6381345A4A57 | SHA256:4A1B84960EBB5E98F945A1935952633CD805A86B199D2DBCD140D75033636EC7 | |||
| 4072 | bat2exe.exe | C:\Users\admin\AppData\Local\Temp\7z897BCFE8\bin\7z.exe | executable | |
MD5:1D1B0349F970C8DE7FAE7A94520E21F7 | SHA256:F63A2D492D7A20E7AE6ACE725DA0320B05A6250794C9B449E1BC48D3F63CEF56 | |||
| 6628 | cmd.exe | C:\Users\admin\AppData\Local\Temp\BAT2EXE_WS.ini | text | |
MD5:2D2C01F9D1CD3A1403382F1BBF0DE908 | SHA256:BD4AAD1756B35D84673AD5247E93CEA58309D8A6A3A16B788CF4E6BC7FAC1792 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
6
TCP/UDP connections
25
DNS requests
9
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
6944 | svchost.exe | GET | 200 | 23.48.23.143:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
5488 | MoUsoCoreWorker.exe | GET | 200 | 23.48.23.143:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
1764 | RUXIMICS.exe | GET | 200 | 23.48.23.143:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
6944 | svchost.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
1764 | RUXIMICS.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
5488 | MoUsoCoreWorker.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
6944 | svchost.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
1764 | RUXIMICS.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
5488 | MoUsoCoreWorker.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 104.126.37.145:443 | www.bing.com | Akamai International B.V. | DE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
6944 | svchost.exe | 23.48.23.143:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
5488 | MoUsoCoreWorker.exe | 23.48.23.143:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
1764 | RUXIMICS.exe | 23.48.23.143:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
6944 | svchost.exe | 184.30.21.171:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
www.bing.com |
| whitelisted |
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
self.events.data.microsoft.com |
| whitelisted |