| File name: | SDClient-Setup.exe |
| Full analysis: | https://app.any.run/tasks/65caba40-8407-4e76-a0ab-eb1be7cdb892 |
| Verdict: | Malicious activity |
| Analysis date: | January 22, 2019, 11:45:37 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | F28BA2C881AF54948C23C14F01F3E46B |
| SHA1: | FDC51E364063DDA572B145DB6EC08CABF0259EE9 |
| SHA256: | 7CF6F593C5E4A264A0C2CC50DC446D77BDE176941D109B3C4D4F3A3D7619D090 |
| SSDEEP: | 98304:MPmY8sjk2m5+0srtjnvuNkf29w2NcjJBY4eaCOB3SZW5IXCGLgkly3nQ:MNjbmETvMkO9Ji04twCGLgz3Q |
MALICIOUS
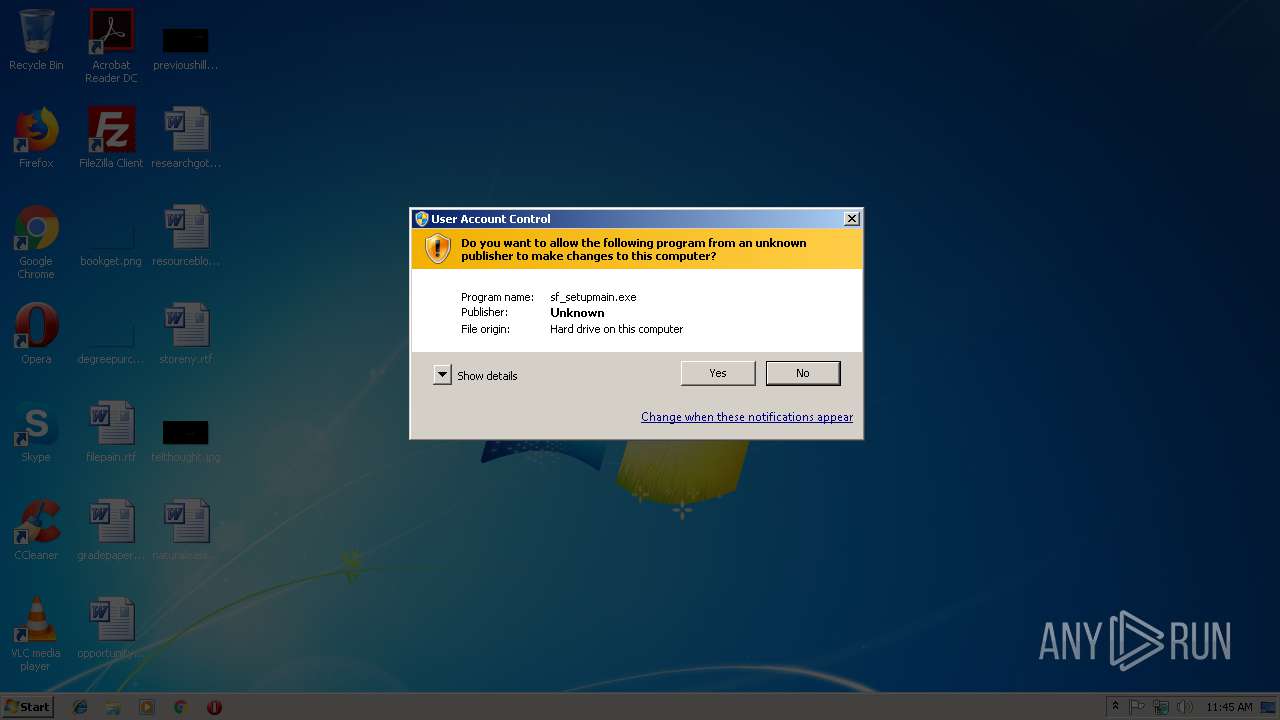
Application was dropped or rewritten from another process
- sf_setupmain.exe (PID: 2800)
- sf_setupmain.exe (PID: 3120)
- suda.exe (PID: 2308)
- EasyPrint.exe (PID: 3960)
- EasyPrint.exe (PID: 3780)
SUSPICIOUS
Executable content was dropped or overwritten
- SDClient-Setup.exe (PID: 3360)
- suda.exe (PID: 2308)
- suda.tmp (PID: 3064)
Changes IE settings (feature browser emulation)
- EasyPrint.exe (PID: 3780)
INFO
Application was dropped or rewritten from another process
- suda.tmp (PID: 3064)
Loads dropped or rewritten executable
- suda.tmp (PID: 3064)
Creates a software uninstall entry
- suda.tmp (PID: 3064)
Creates files in the user directory
- WINWORD.EXE (PID: 2180)
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 2180)
Creates files in the program directory
- suda.tmp (PID: 3064)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win64 Executable (generic) (76.4) |
|---|---|---|
| .exe | | | Win32 Executable (generic) (12.4) |
| .exe | | | Generic Win/DOS Executable (5.5) |
| .exe | | | DOS Executable Generic (5.5) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2016:11:22 03:30:25+01:00 |
| PEType: | PE32 |
| LinkerVersion: | 12 |
| CodeSize: | 283648 |
| InitializedDataSize: | 191488 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x36d87 |
| OSVersion: | 5.1 |
| ImageVersion: | - |
| SubsystemVersion: | 5.1 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 5.9.2.10735 |
| ProductVersionNumber: | 5.9.2.10735 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Windows NT 32-bit |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Chinese (Simplified) |
| CharacterSet: | Unicode |
| FileVersion: | 5.9.2.10735 |
| ProductVersion: | 5.9 |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 22-Nov-2016 02:30:25 |
| Detected languages: |
|
| Debug artifacts: |
|
| FileVersion: | 5.9.2.10735 |
| ProductVersion: | 5.9 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000108 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 5 |
| Time date stamp: | 22-Nov-2016 02:30:25 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x0004527B | 0x00045400 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.64156 |
.rdata | 0x00047000 | 0x00011A60 | 0x00011C00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 4.73902 |
.data | 0x00059000 | 0x0000A180 | 0x00003A00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.67134 |
.rsrc | 0x00064000 | 0x00013FDC | 0x00014000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 6.45203 |
.reloc | 0x00078000 | 0x000055E0 | 0x00005600 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 6.48033 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.3159 | 1217 | Latin 1 / Western European | English - United States | RT_MANIFEST |
2 | 5.48625 | 4264 | Latin 1 / Western European | Chinese - PRC | RT_ICON |
3 | 5.4219 | 1128 | Latin 1 / Western European | Chinese - PRC | RT_ICON |
107 | 2.45849 | 48 | Latin 1 / Western European | Chinese - PRC | RT_GROUP_ICON |
129 | 3.66614 | 476 | Latin 1 / Western European | Chinese - PRC | RT_DIALOG |
131 | 7.16841 | 16478 | Latin 1 / Western European | Chinese - PRC | RT_BITMAP |
132 | 3.59875 | 758 | Latin 1 / Western European | Chinese - PRC | RT_DIALOG |
304 | 3.80658 | 336 | Latin 1 / Western European | Chinese - PRC | RT_DIALOG |
563 | 2.52313 | 82 | Latin 1 / Western European | Chinese - PRC | RT_STRING |
626 | 6.14053 | 436 | Latin 1 / Western European | Chinese - PRC | RT_STRING |
Imports
COMCTL32.dll |
GDI32.dll |
KERNEL32.dll |
SHELL32.dll |
USER32.dll |
ole32.dll |
Total processes
47
Monitored processes
8
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2180 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\Desktop\naturaleasily.rtf" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
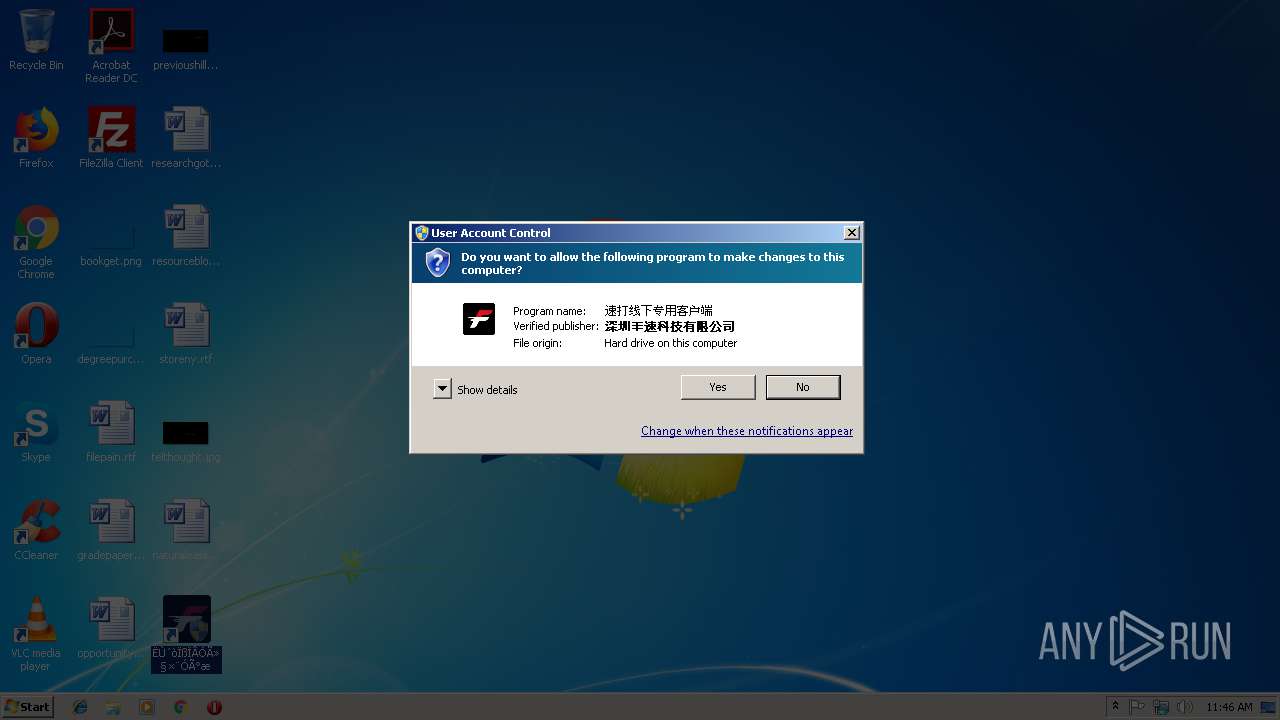
| 2308 | C:\Users\admin\AppData\Local\Temp\suda.exe | C:\Users\admin\AppData\Local\Temp\suda.exe | sf_setupmain.exe | ||||||||||||
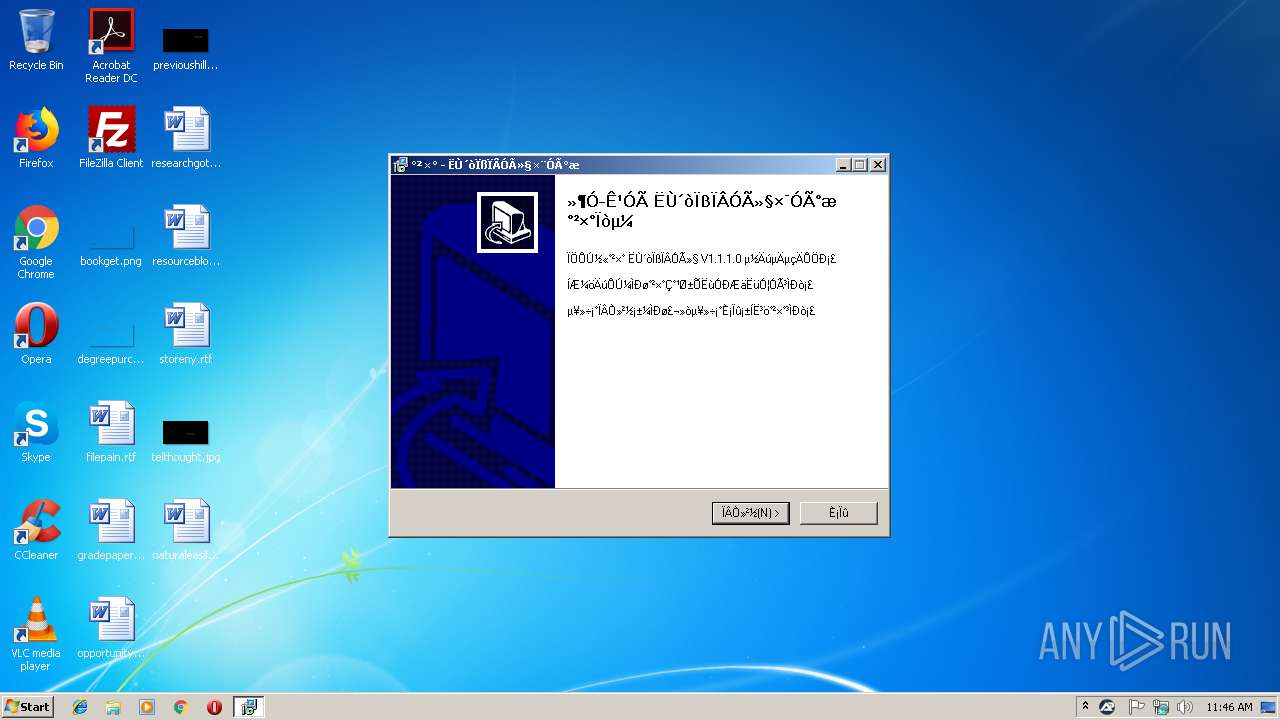
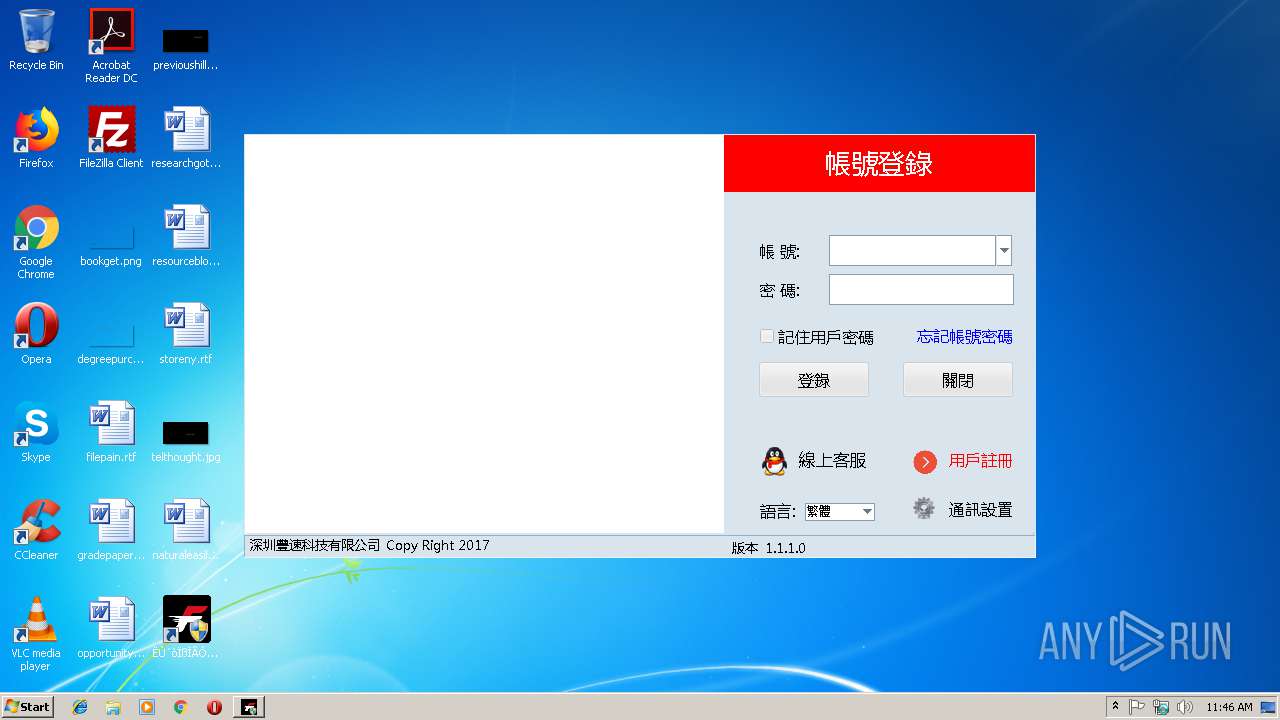
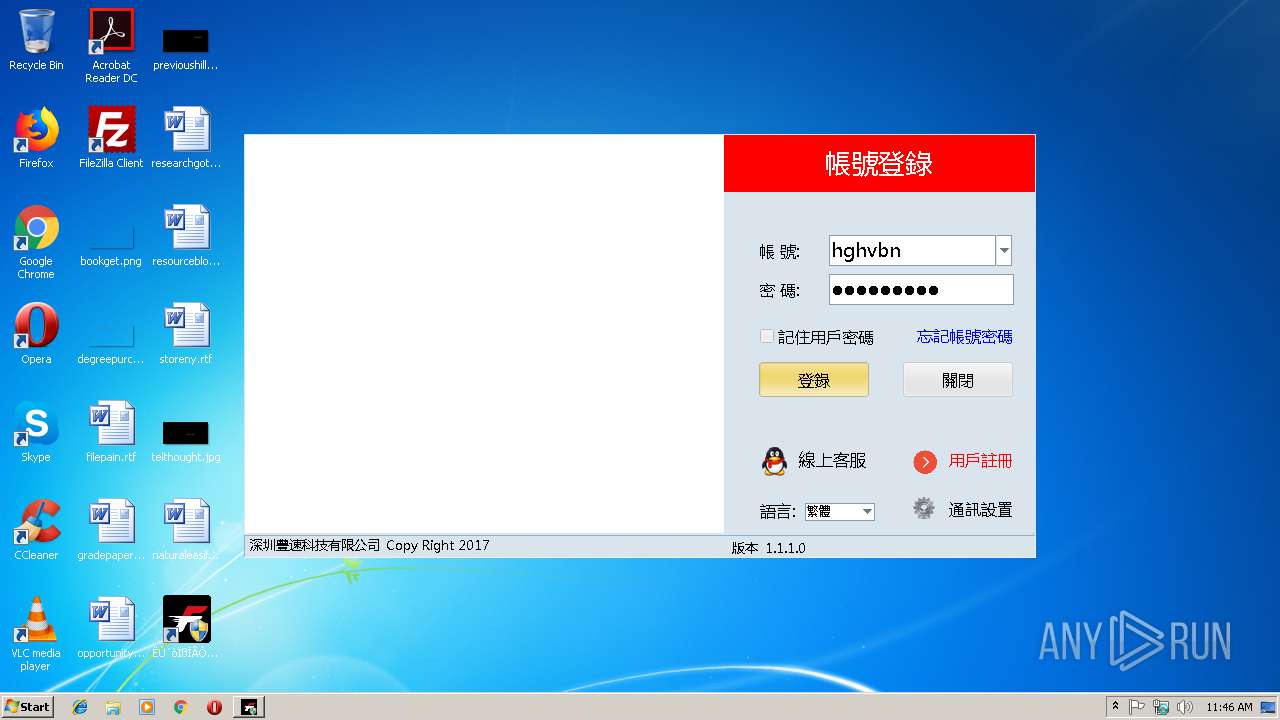
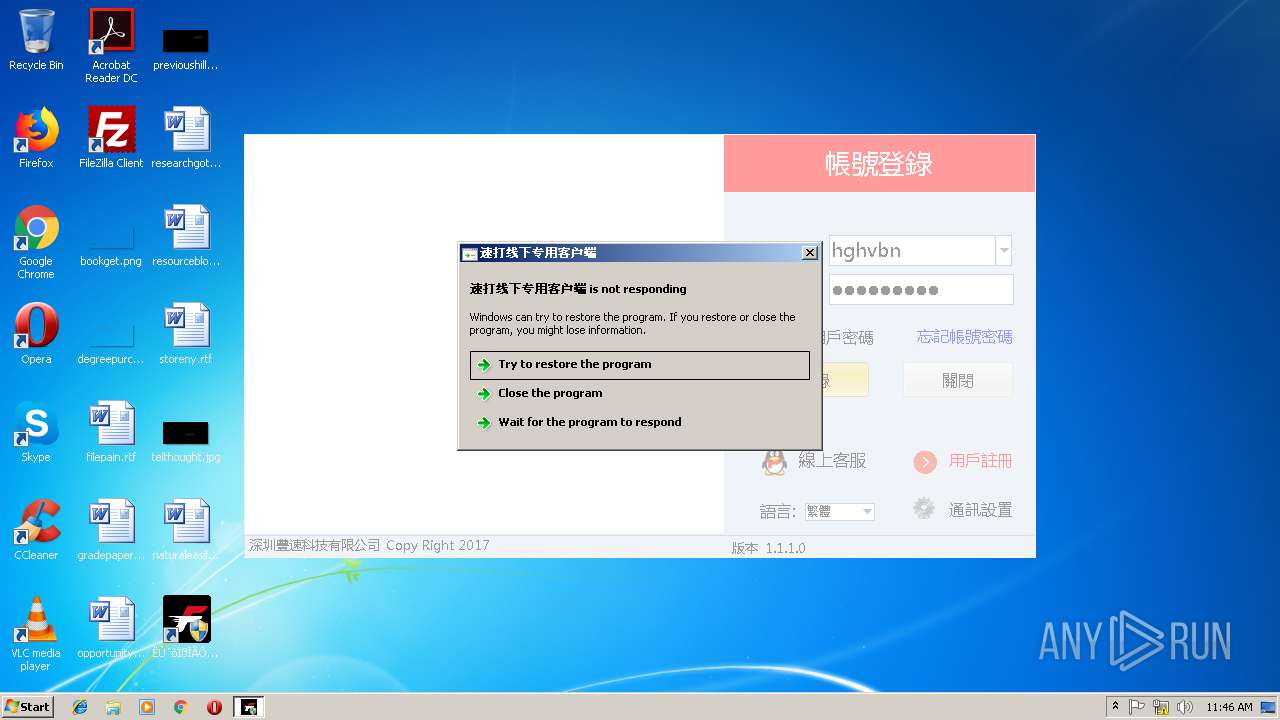
User: admin Company: 深圳丰速科技有限公司 Integrity Level: HIGH Description: 速打线下用户专用版 Setup Exit code: 0 Version: 1.1.1.0 Modules
| |||||||||||||||
| 2800 | "C:\Users\admin\AppData\Local\Temp\sf_setupmain.exe" | C:\Users\admin\AppData\Local\Temp\sf_setupmain.exe | — | SDClient-Setup.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: Aut2Exe Exit code: 3221226540 Version: 3.3.14.2 Modules
| |||||||||||||||
| 3064 | "C:\Users\admin\AppData\Local\Temp\is-2C641.tmp\suda.tmp" /SL5="$20128,5211574,51712,C:\Users\admin\AppData\Local\Temp\suda.exe" | C:\Users\admin\AppData\Local\Temp\is-2C641.tmp\suda.tmp | suda.exe | ||||||||||||
User: admin Integrity Level: HIGH Description: 安装/卸载 Exit code: 0 Version: 51.49.0.0 Modules
| |||||||||||||||
| 3120 | "C:\Users\admin\AppData\Local\Temp\sf_setupmain.exe" | C:\Users\admin\AppData\Local\Temp\sf_setupmain.exe | SDClient-Setup.exe | ||||||||||||
User: admin Integrity Level: HIGH Description: Aut2Exe Exit code: 0 Version: 3.3.14.2 Modules
| |||||||||||||||
| 3360 | "C:\Users\admin\Downloads\SDClient-Setup.exe" | C:\Users\admin\Downloads\SDClient-Setup.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Version: 5.9.2.10735 Modules
| |||||||||||||||
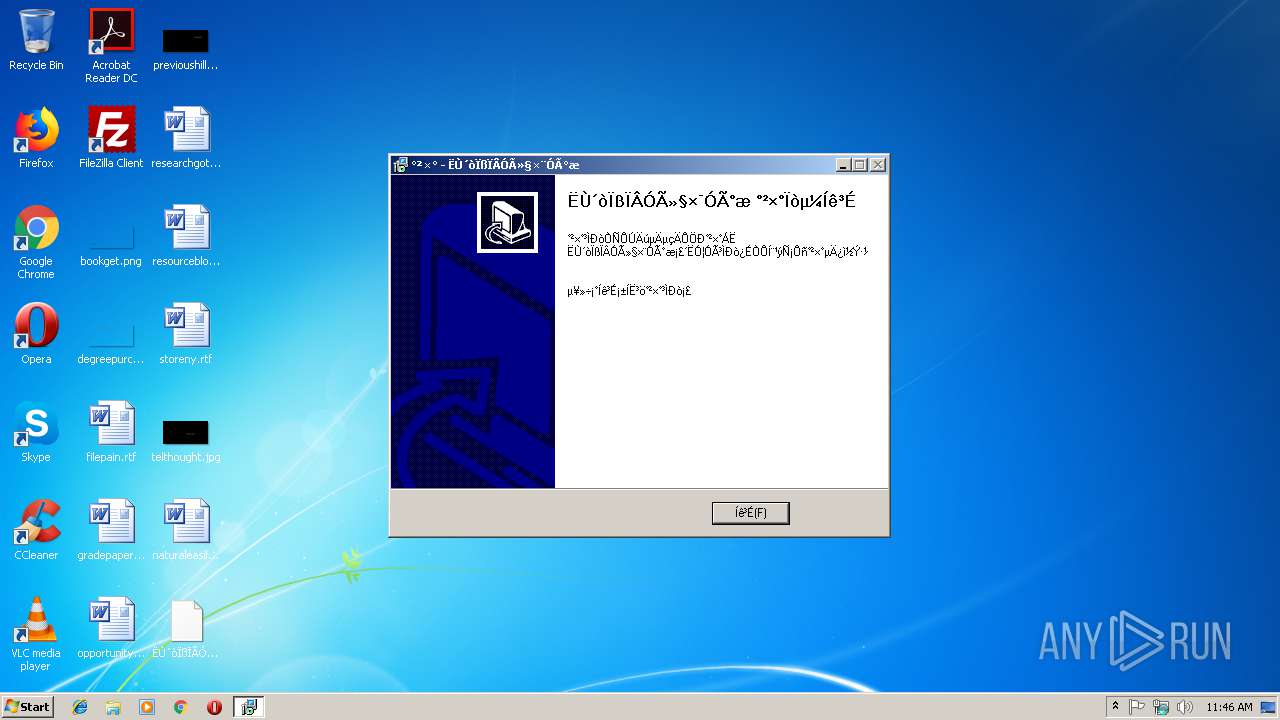
| 3780 | "C:\Program Files\ËÙ´òÏßÏÂÓû§×¨Óðæ\EasyPrint.exe" | C:\Program Files\ËÙ´òÏßÏÂÓû§×¨Óðæ\EasyPrint.exe | explorer.exe | ||||||||||||
User: admin Company: 深圳丰速科技有限公司 Integrity Level: HIGH Description: 速打线下专用客户端 Exit code: 3489660927 Version: 1.1.1.0 Modules
| |||||||||||||||
| 3960 | "C:\Program Files\ËÙ´òÏßÏÂÓû§×¨Óðæ\EasyPrint.exe" | C:\Program Files\ËÙ´òÏßÏÂÓû§×¨Óðæ\EasyPrint.exe | — | explorer.exe | |||||||||||
User: admin Company: 深圳丰速科技有限公司 Integrity Level: MEDIUM Description: 速打线下专用客户端 Exit code: 3221226540 Version: 1.1.1.0 Modules
| |||||||||||||||
Total events
980
Read events
926
Write events
53
Delete events
1
Modification events
| (PID) Process: | (3360) SDClient-Setup.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (3360) SDClient-Setup.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (3064) suda.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\{3a3003ed-2fb1-4546-8b04-5603fe2e0eb8}_is1 |
| Operation: | write | Name: | Inno Setup: Setup Version |
Value: 5.3.5 (a) | |||
| (PID) Process: | (3064) suda.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\{3a3003ed-2fb1-4546-8b04-5603fe2e0eb8}_is1 |
| Operation: | write | Name: | Inno Setup: App Path |
Value: C:\Program Files\ËÙ´òÏßÏÂÓû§×¨Óðæ | |||
| (PID) Process: | (3064) suda.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\{3a3003ed-2fb1-4546-8b04-5603fe2e0eb8}_is1 |
| Operation: | write | Name: | InstallLocation |
Value: C:\Program Files\ËÙ´òÏßÏÂÓû§×¨Óðæ\ | |||
| (PID) Process: | (3064) suda.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\{3a3003ed-2fb1-4546-8b04-5603fe2e0eb8}_is1 |
| Operation: | write | Name: | Inno Setup: Icon Group |
Value: ËÙ´òÏßÏÂÓû§×¨Óðæ | |||
| (PID) Process: | (3064) suda.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\{3a3003ed-2fb1-4546-8b04-5603fe2e0eb8}_is1 |
| Operation: | write | Name: | Inno Setup: User |
Value: admin | |||
| (PID) Process: | (3064) suda.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\{3a3003ed-2fb1-4546-8b04-5603fe2e0eb8}_is1 |
| Operation: | write | Name: | Inno Setup: Selected Tasks |
Value: desktopicon | |||
| (PID) Process: | (3064) suda.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\{3a3003ed-2fb1-4546-8b04-5603fe2e0eb8}_is1 |
| Operation: | write | Name: | Inno Setup: Deselected Tasks |
Value: quicklaunchicon | |||
| (PID) Process: | (3064) suda.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\{3a3003ed-2fb1-4546-8b04-5603fe2e0eb8}_is1 |
| Operation: | write | Name: | DisplayName |
Value: ËÙ´òÏßÏÂÓû§ V1.1.1.0 | |||
Executable files
7
Suspicious files
20
Text files
95
Unknown types
6
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3064 | suda.tmp | C:\Program Files\ËÙ´òÏßÏÂÓû§×¨Óðæ\is-N0BVS.tmp | — | |
MD5:— | SHA256:— | |||
| 3064 | suda.tmp | C:\Program Files\ËÙ´òÏßÏÂÓû§×¨Óðæ\is-4I199.tmp | — | |
MD5:— | SHA256:— | |||
| 3064 | suda.tmp | C:\Program Files\ËÙ´òÏßÏÂÓû§×¨Óðæ\is-UL58J.tmp | — | |
MD5:— | SHA256:— | |||
| 3064 | suda.tmp | C:\Program Files\ËÙ´òÏßÏÂÓû§×¨Óðæ\Images\is-UJ0MF.tmp | — | |
MD5:— | SHA256:— | |||
| 3064 | suda.tmp | C:\Program Files\ËÙ´òÏßÏÂÓû§×¨Óðæ\Images\is-U8NI0.tmp | — | |
MD5:— | SHA256:— | |||
| 3064 | suda.tmp | C:\Program Files\ËÙ´òÏßÏÂÓû§×¨Óðæ\Images\is-4LMAU.tmp | — | |
MD5:— | SHA256:— | |||
| 3064 | suda.tmp | C:\Program Files\ËÙ´òÏßÏÂÓû§×¨Óðæ\Images\is-SFMJT.tmp | — | |
MD5:— | SHA256:— | |||
| 3064 | suda.tmp | C:\Program Files\ËÙ´òÏßÏÂÓû§×¨Óðæ\Images\is-13VTU.tmp | — | |
MD5:— | SHA256:— | |||
| 3064 | suda.tmp | C:\Program Files\ËÙ´òÏßÏÂÓû§×¨Óðæ\Images\is-L9U2D.tmp | — | |
MD5:— | SHA256:— | |||
| 3064 | suda.tmp | C:\Program Files\ËÙ´òÏßÏÂÓû§×¨Óðæ\Images\is-H4AJU.tmp | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
2
TCP/UDP connections
3
DNS requests
3
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3780 | EasyPrint.exe | GET | — | 116.62.97.2:80 | http://sd.1dadan.com/clienthtml/sd/index.html?Tag=38 | CN | — | — | unknown |
3780 | EasyPrint.exe | POST | — | 116.62.97.2:80 | http://sd.1dadan.com/client/security/loginIp?ecstoken=&node= | CN | — | — | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3780 | EasyPrint.exe | 103.235.46.39:80 | www.baidu.com | Beijing Baidu Netcom Science and Technology Co., Ltd. | HK | unknown |
3780 | EasyPrint.exe | 116.62.97.2:80 | sd.1dadan.com | Hangzhou Alibaba Advertising Co.,Ltd. | CN | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.baidu.com |
| whitelisted |
sd.1dadan.com |
| unknown |