| File name: | default_.exe |
| Full analysis: | https://app.any.run/tasks/e940a849-a492-4c40-94af-1bd0dfc99084 |
| Verdict: | Malicious activity |
| Threats: | GandCrab is probably one of the most famous Ransomware. A Ransomware is a malware that asks the victim to pay money in order to restore access to encrypted files. If the user does not cooperate the files are forever lost. |
| Analysis date: | October 14, 2019, 17:00:39 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, UPX compressed |
| MD5: | D424A90E8CCBBA7CECFEF646781CF93C |
| SHA1: | 616F74CA274FDB89B28FB26B2261B02E276FF81B |
| SHA256: | 7CE0835682F4C82B7E044C9D9DBB59DA5C5EAA07D3C60CDE0FFBAC58E85BE47D |
| SSDEEP: | 3072:5Ez0Ex4k7eQyX7HAWnY4MVZ0zAwU2GYOuXsnEKUyrAhF4YUWl1:5wx7MVnYRVZ0BU2Ze3MH4YB1 |
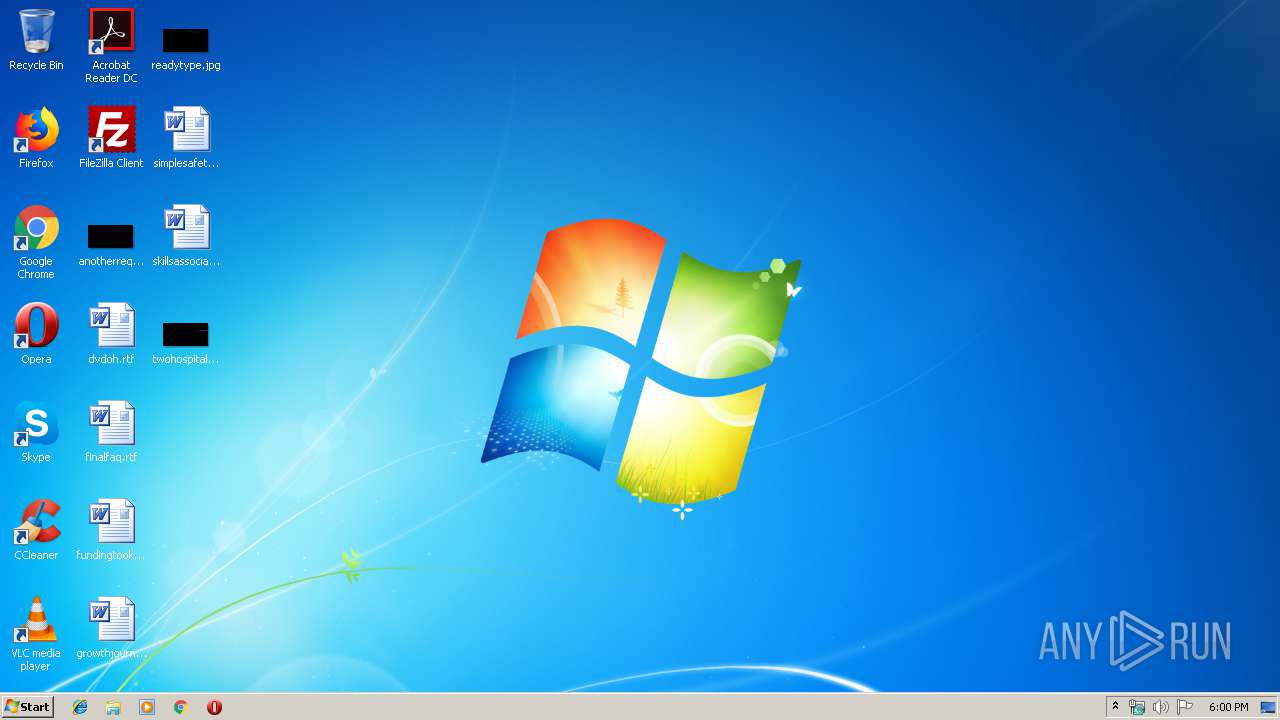
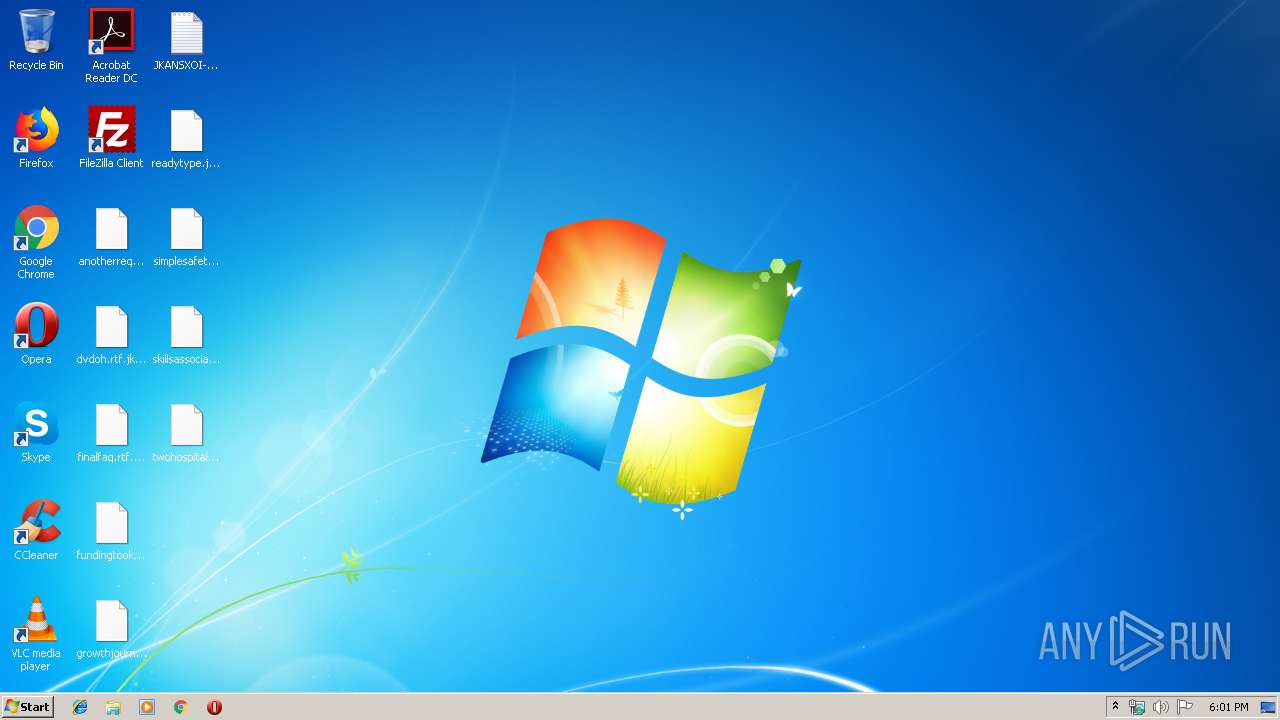
MALICIOUS
GandCrab keys found
- default_.exe (PID: 2176)
Actions looks like stealing of personal data
- default_.exe (PID: 2176)
Writes file to Word startup folder
- default_.exe (PID: 2176)
Renames files like Ransomware
- default_.exe (PID: 2176)
Deletes shadow copies
- default_.exe (PID: 2176)
Dropped file may contain instructions of ransomware
- default_.exe (PID: 2176)
GANDCRAB detected
- default_.exe (PID: 2176)
SUSPICIOUS
Creates files in the program directory
- default_.exe (PID: 2176)
Reads the cookies of Mozilla Firefox
- default_.exe (PID: 2176)
Creates files like Ransomware instruction
- default_.exe (PID: 2176)
Reads Internet Cache Settings
- default_.exe (PID: 2176)
Executed as Windows Service
- vssvc.exe (PID: 3140)
Creates files in the user directory
- default_.exe (PID: 2176)
INFO
Dropped object may contain Bitcoin addresses
- default_.exe (PID: 2176)
Dropped object may contain TOR URL's
- default_.exe (PID: 2176)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | UPX compressed Win32 Executable (64.2) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (15.6) |
| .exe | | | Win32 Executable (generic) (10.6) |
| .exe | | | Generic Win/DOS Executable (4.7) |
| .exe | | | DOS Executable Generic (4.7) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2018:06:25 16:21:47+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 10 |
| CodeSize: | 131072 |
| InitializedDataSize: | 8192 |
| UninitializedDataSize: | 172032 |
| EntryPoint: | 0x4ad20 |
| OSVersion: | 5.1 |
| ImageVersion: | - |
| SubsystemVersion: | 5.1 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 1.0.0.0 |
| ProductVersionNumber: | 1.0.0.0 |
| FileFlagsMask: | 0x004f |
| FileFlags: | (none) |
| FileOS: | Unknown (0x40534) |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Unknown (457A) |
| CharacterSet: | Unknown (A56B) |
| InternalName: | zebeba.exe |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 25-Jun-2018 14:21:47 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x000000E8 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 3 |
| Time date stamp: | 25-Jun-2018 14:21:47 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
UPX0 | 0x00001000 | 0x0002A000 | 0x00000000 | IMAGE_SCN_CNT_UNINITIALIZED_DATA, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
UPX1 | 0x0002B000 | 0x00020000 | 0x00020000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 7.69823 |
.rsrc | 0x0004B000 | 0x00002000 | 0x00001A00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 3.50091 |
Imports
ADVAPI32.dll |
GDI32.dll |
KERNEL32.DLL |
MSIMG32.dll |
SHELL32.dll |
USER32.dll |
WINHTTP.dll |
Total processes
41
Monitored processes
3
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1748 | "C:\Windows\system32\wbem\wmic.exe" shadowcopy delete | C:\Windows\system32\wbem\wmic.exe | default_.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: WMI Commandline Utility Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2176 | "C:\Windows\default_.exe" | C:\Windows\default_.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 3140 | C:\Windows\system32\vssvc.exe | C:\Windows\system32\vssvc.exe | — | services.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft® Volume Shadow Copy Service Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
118
Read events
91
Write events
27
Delete events
0
Modification events
| (PID) Process: | (2176) default_.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\ex_data\data |
| Operation: | write | Name: | ext |
Value: 2E006A006B0061006E00730078006F0069000000 | |||
| (PID) Process: | (2176) default_.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\keys_data\data |
| Operation: | write | Name: | public |
Value: 0602000000A400005253413100080000010001004F8237EA23A62D4367A87AB789D9D3AEB02E5172A77EE43AF9836D9C4624254DB4B929C583B626676C2BB64EA0494C39B29EA72C373B27216EBC202F6B9965FB0E76197EBE30CBD222ABC68D76963B780F447418D3B65740DADE5FF943EE704E3F94A88A158FBEC576F9263360A08395AA0D6351808E3B8A17719142E75C238C543FB3D0B997562C87CED70C980C2E0B43E48ED094E9B583C7507BA74E1D784C1EAD2EDEEC506D4F793ABD9C9475A7F0772327A326EF704319DA575BAA45486165BFE5FFB0374CC4A2DDFE183CEFDCE3273B78BCAF82E8D5438A47404B5D9C41CA1DAA7000E64E0A751C78F69CBB3E66C4153D6FAB3400F23E872C7FB06586BF | |||
| (PID) Process: | (2176) default_.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\keys_data\data |
| Operation: | write | Name: | private |
Value: 94040000334D9ED0B2FFE09AD29AF401D82AC50E54D27D1F3591FBF081B47939F6CD73E661E31BD84118E8968000FE9E5F6B2DF24FE79657D7DC774E13E149F7606B2C9636DC7CE8CBE61F9929338CE126D8F79FF7CE15047CEEDAB978286AEE61FF184D66E134F6A9E2103DF7ACD3AD0408EF6ABE6A76C0E94B813CD68AAD0B4202C2339622830442551C73729E117D80CC44A14EBFDA68F4E7DD9CB5F687F35D390679211AACBDE3D663B38B932F54AF98E20C14EA2113181075FD573C6EBFBC1405B57F4ECDA41A8D64F2E14BE72231D2ACB4DE0E4C0092C1D06AF8BA43DEEBD12F797FEE972E01511702D62E86E75EDCFA94B0724131F9FADEDE64C805DD9096A19031808F8DB55FCF74B67F77050E59453A80CECC943D592F8A8173BA49F90D7EE3F9AB1262E7FF96C58907C453C0FDD931E62F424076167E0803B3E68C6F865D672724FD9029C46D21FB22215EBE26462B1441F929193A783C4D798B934D9776BF8542614BB3194975DA7D251270638279E46F77EC1CF98D8B030F3DA806BED76DC9B94B67CC0E416BA06F2AD16D540CB39738441157E6C50AD35D4A72349BD3BD68B0EE2D8429DECC209628B10A9959F4808C60E555B39210DFBE4061E56720365C1B729BD96F293F6A37FEA08CC9285266878B8A1CAEDC3FC5C87DF426FF213F4FE4436D6628129F7BC64FCA873C4A44D6D677EF2C3341416165A55E0C9AFA38173D50D3BFF82D058A5985A0C5673E2975E44F489730F718A557097E7C79BCF0419EA8B95224581AF62383C7E7EFCACC2A98B7E86D153D0725DB418D5176294E2B1646A76B78109190D50712259D3F3A750325CBCD50BB5D88839406567D206112C597A6543930C94E6A06949B1BF63028462A94C4E3D58C21732E6F3A12E908EFCC5721A5C5E07CE11E97E4826A1EF48D1E3522902C9676EABCB17FADD757DD23EB224EA67CEEBE7ED4B302E9898E7028C2B8EA76FCF9BD492FC91CB00BE812093B47B058B0AFD046AA48D6DB27EC4C9B8A46DD5240D6F9B20CA8BB544AF9EC8DFB11117F22713970DA81DE5DF3B8D2B9BFF892BBA8C9B3533333A09DEB943A7AB550409B4E9EB3EADF1DECD87F1FC28A84D22BE461FB57E536BE55AB54B1FCB4198F39152746FABF757E27E183E3C5DD72484FBC68102B0D31FFAE1952637F192F8001B0464CD7C85089124D7ECE9E2FC69B17E5D2D9D1D1045A59D4283D4DF743D96B6D355A5F06642B4210FBA691CD595908A6E021202107AA0FC1E9C045F152109C1C989D3416362A78827953F29E415AA70A7463C47D8B0795CBE48922EFEE04F6AB51E4A6F42D264F2638C16D5BDB653CEA588DDC5E30529CF504D10A64D6858B7EB171EA00CA6778AB32BD5CE78E4909085411AADAA5DCD5FDD56FBFB1A9E71ED2D5836A7105D34DBF979A5DB1612D4D7F21488F1421A9EEA105026076E478BA3DFE7A5635748FF013513AEF414CFB777A285E208650E40F5CDC72670EB6EE222B011BE8451D3FE3C4DB7770BBF22239B5F188875AA850DCEB658FC74502E9023558BD64E863846842647908043415B264C9A493DA782D4BE98BC41DC04AF1A2CB2A097A734EB35C37BA7D299601FA6483852304AED3BFFD9CDFB5211BAF75394A99E78480F3542FE9811283ADC57990B622097C587197E68DBA4B9D880E663BA6905CC05EC9ED9CD711507FE7D27CE5CF2F06211EDF39C5B1A7AAC28F36D445352CF0E84879E933A9EFFA34EFE43BB6AEC168EC24E8C0628EDCDCDE4099BC7DC57A11A119CD68B10A26D693A5DD73C5ED43568C93DB55DD380FE320F49A552428D123CB6CB6FAF3AD27C3A5BE50C0DD1A05CDEC2F4A995719F91C92EFBA693B61131AAB8C23919F3F94F5FFA7B093E7D5B47A8CA20DB4A6BED019465CE895239372E11F0E049621A258CA3361ED917128A743EA7D48A623703C86EA6252559A4CDAB7FB9BAB654A068629B197C89642F948A3103F586C675F9C48D6E5F0E28AD1714EAD3A8D325BDD5934F310CB58FAE8E21C673385F8B57CA863967FB5D5D9968C99E43DEF3B4B34A555E3DB9857D2CFA1E637853B58FC7F90913A42A11E65C749549051B14FDBA24AA5C41E8FBFDE2E03782F3F0D8871BD882AE22283D84A4691A01917AE24CE49B8C48A008564571242C94877DE0CF1868E43178BAAD6351F8E7711F26738E0DF84C45BBC02316A8E372892E1D3A13643D2D6BB3CE754BE9AAB74672BE874FE3D7ACA9F5DDC0174BB60D8E010023DADEA1DC0EFC244053FBF5E7AE34AAD3261FA72E6FF9317F372FCFA3F6626CDEB03A62C9A22A76334A6EDBB0014F1BBA7A340A4E4349E09D714310F5674D2204D989DB5E0BB303058459C16EE9DD3C421E8887F29133854C779 | |||
| (PID) Process: | (2176) default_.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (2176) default_.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (2176) default_.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\default__RASAPI32 |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (2176) default_.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\default__RASAPI32 |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
| (PID) Process: | (2176) default_.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\default__RASAPI32 |
| Operation: | write | Name: | FileTracingMask |
Value: 4294901760 | |||
| (PID) Process: | (2176) default_.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\default__RASAPI32 |
| Operation: | write | Name: | ConsoleTracingMask |
Value: 4294901760 | |||
| (PID) Process: | (2176) default_.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\default__RASAPI32 |
| Operation: | write | Name: | MaxFileSize |
Value: 1048576 | |||
Executable files
0
Suspicious files
460
Text files
325
Unknown types
18
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2176 | default_.exe | C:\Recovery\345b46fe-a9f9-11e7-a83c-e8a4f72b1d33\boot.sdi | — | |
MD5:— | SHA256:— | |||
| 2176 | default_.exe | C:\Recovery\345b46fe-a9f9-11e7-a83c-e8a4f72b1d33\Winre.wim.jkansxoi | — | |
MD5:— | SHA256:— | |||
| 2176 | default_.exe | C:\Recovery\345b46fe-a9f9-11e7-a83c-e8a4f72b1d33\Winre.wim | — | |
MD5:— | SHA256:— | |||
| 2176 | default_.exe | C:\System Volume Information\SPP\OnlineMetadataCache\{02b4b32f-3d9a-4f0c-90b3-b3f695ffdbdb}_OnDiskSnapshotProp | — | |
MD5:— | SHA256:— | |||
| 2176 | default_.exe | C:\System Volume Information\SPP\OnlineMetadataCache\{05ed3515-06b3-48f6-8cf2-bf24b1bf0727}_OnDiskSnapshotProp | — | |
MD5:— | SHA256:— | |||
| 2176 | default_.exe | C:\System Volume Information\SPP\OnlineMetadataCache\{0e2a6214-ab14-4acd-9944-51dcd3caf902}_OnDiskSnapshotProp | — | |
MD5:— | SHA256:— | |||
| 2176 | default_.exe | C:\System Volume Information\SPP\OnlineMetadataCache\{14e6e058-39ee-43ce-ac15-7acb7d834dae}_OnDiskSnapshotProp | — | |
MD5:— | SHA256:— | |||
| 2176 | default_.exe | C:\System Volume Information\SPP\OnlineMetadataCache\{16d74681-6bc3-4c44-97f0-8b8dfefe2355}_OnDiskSnapshotProp | — | |
MD5:— | SHA256:— | |||
| 2176 | default_.exe | C:\$Recycle.Bin\JKANSXOI-DECRYPT.txt | text | |
MD5:— | SHA256:— | |||
| 2176 | default_.exe | C:\System Volume Information\SPP\OnlineMetadataCache\{31c64f4e-4eef-4f67-acde-eb3f4d02f051}_OnDiskSnapshotProp | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
3
Threats
2
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.kakaocorp.link |
| malicious |
Threats
2 ETPRO signatures available at the full report