| File name: | filename.dll |
| Full analysis: | https://app.any.run/tasks/349d8872-fe5d-4470-bbc8-8046bb2d56b1 |
| Verdict: | Malicious activity |
| Analysis date: | March 19, 2020, 23:33:04 |
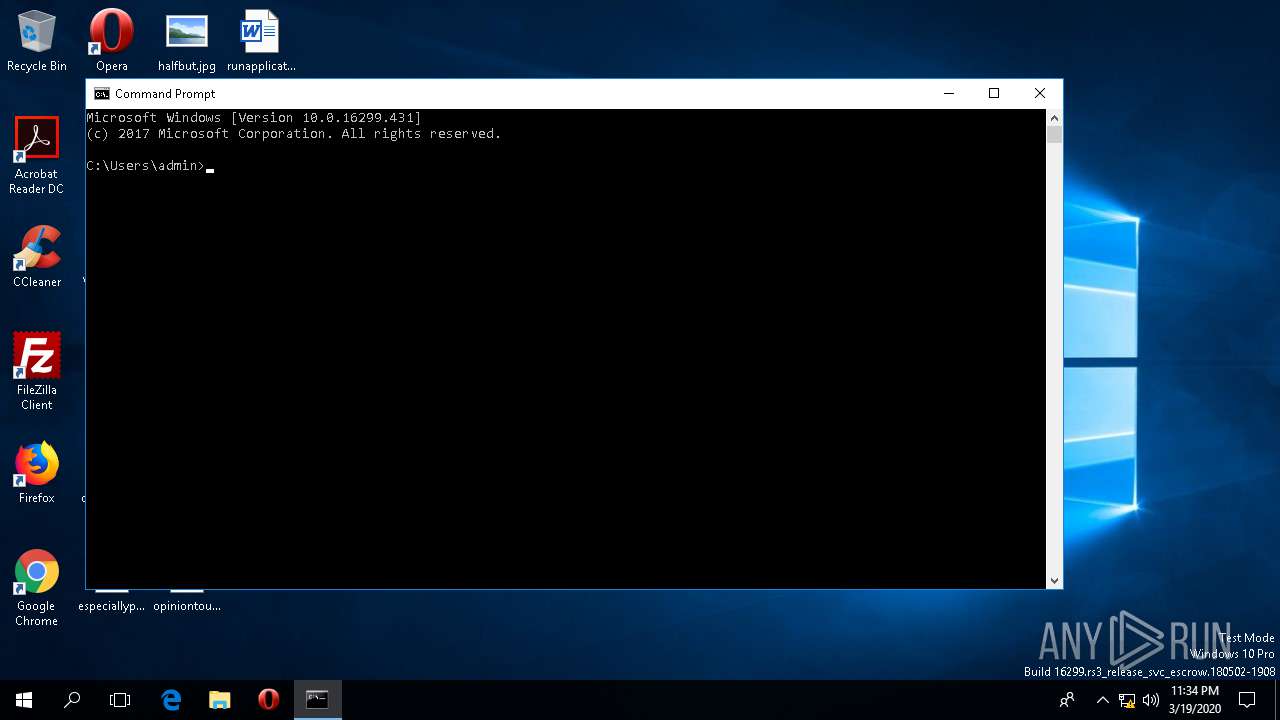
| OS: | Windows 10 Professional (build: 16299, 64 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (DLL) (GUI) Intel 80386, for MS Windows |
| MD5: | F409BD7446B30BF46B835B65096671D0 |
| SHA1: | A1765CE94C6F585A99363F36F6C5EDDF39BFAAE3 |
| SHA256: | 7CD50985B4B718F72B77A807F00FE8A6F2A44A6B6EAED0A4919F8E6C11E63FF0 |
| SSDEEP: | 6144:KCpX94vk88bwlRUNRZ63QVgOrvUuBojDopJ23y5R:KCpXMlRMZ63Q1r8xjsX2Cn |
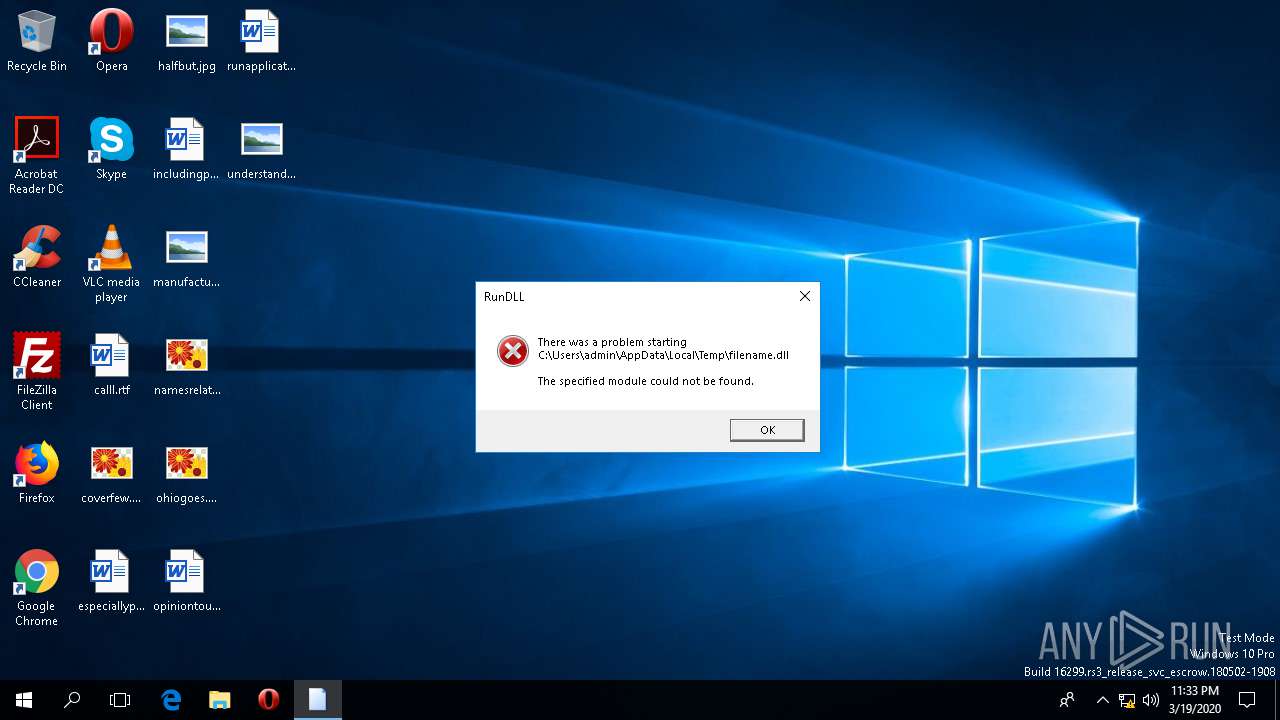
MALICIOUS
Loads dropped or rewritten executable
- rundll32.exe (PID: 720)
SUSPICIOUS
Executed via COM
- RuntimeBroker.exe (PID: 972)
- IEXPLORE.EXE (PID: 3620)
- ielowutil.exe (PID: 2292)
Checks supported languages
- RuntimeBroker.exe (PID: 972)
Uses RUNDLL32.EXE to load library
- rundll32.exe (PID: 1436)
- cmd.exe (PID: 3152)
INFO
Reads the machine GUID from the registry
- IEXPLORE.EXE (PID: 5852)
- IEXPLORE.EXE (PID: 3620)
Changes internet zones settings
- IEXPLORE.EXE (PID: 3620)
Reads internet explorer settings
- IEXPLORE.EXE (PID: 5852)
Manual execution by user
- cmd.exe (PID: 3152)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (42.2) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (37.3) |
| .dll | | | Win32 Dynamic Link Library (generic) (8.8) |
| .exe | | | Win32 Executable (generic) (6) |
| .exe | | | Generic Win/DOS Executable (2.7) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2020:03:19 11:57:14+01:00 |
| PEType: | PE32 |
| LinkerVersion: | 12 |
| CodeSize: | 212992 |
| InitializedDataSize: | 133120 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x206fc |
| OSVersion: | 6 |
| ImageVersion: | - |
| SubsystemVersion: | 6 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 7.3.3043.5321 |
| ProductVersionNumber: | 7.3.3043.5321 |
| FileFlagsMask: | 0x0000 |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Dynamic link library |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Unicode |
| CompanyName: | Example Onewhose |
| FileDescription: | Callran triangle |
| FileVersion: | 7.3.3043.5321 |
| InternalName: | Rop.dll |
| LegalCopyright: | © 1999-2014 Example Onewhose heart Corporation. All rights reserved. |
| OriginalFileName: | Rop.dll |
| ProductName: | Example Onewhose Callran triangle |
| ProductVersion: | 7.3.3043.5321 |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 19-Mar-2020 10:57:14 |
| Detected languages: |
|
| Debug artifacts: |
|
| CompanyName: | Example Onewhose |
| FileDescription: | Callran triangle |
| FileVersion: | 7.3.3043.5321 |
| InternalName: | Rop.dll |
| LegalCopyright: | © 1999-2014 Example Onewhose heart Corporation. All rights reserved. |
| OriginalFilename: | Rop.dll |
| ProductName: | Example Onewhose Callran triangle |
| ProductVersion: | 7.3.3043.5321 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x000000F8 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 5 |
| Time date stamp: | 19-Mar-2020 10:57:14 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x00033EFF | 0x00034000 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.496 |
.rdata | 0x00035000 | 0x0000BC9A | 0x0000BE00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.01082 |
.data | 0x00041000 | 0x0001E98C | 0x00009400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 5.84802 |
.rsrc | 0x00060000 | 0x00008D64 | 0x00008E00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 4.17374 |
.reloc | 0x00069000 | 0x000026E8 | 0x00002800 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 6.60966 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 3.50615 | 868 | Latin 1 / Western European | English - United States | RT_VERSION |
2 | 4.79597 | 346 | Latin 1 / Western European | English - United States | RT_MANIFEST |
3 | 4.41341 | 4264 | Latin 1 / Western European | English - United States | RT_ICON |
4 | 4.80631 | 2440 | Latin 1 / Western European | English - United States | RT_ICON |
5 | 5.18495 | 1128 | Latin 1 / Western European | English - United States | RT_ICON |
101 | 2.79808 | 76 | Latin 1 / Western European | English - United States | RT_GROUP_ICON |
Imports
KERNEL32.dll |
Exports
Title | Ordinal | Address |
|---|---|---|
DllRegisterServer | 1 | 0x00012EA0 |
DllUnregisterServer | 2 | 0x00012BA0 |
Skinelement | 3 | 0x000159E0 |
Total processes
89
Monitored processes
9
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 720 | rundll32.exe C:\Users\admin\AppData\Local\Temp\filename.dll.exe DllRegisterServer | C:\WINDOWS\SysWOW64\rundll32.exe | — | rundll32.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 10.0.16299.15 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 864 | "C:\Windows\System32\rundll32.exe" C:\Users\admin\AppData\Local\Temp\filename.dll,DllRegisterServer | C:\Windows\System32\rundll32.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 10.0.16299.15 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 972 | C:\Windows\System32\RuntimeBroker.exe -Embedding | C:\Windows\System32\RuntimeBroker.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Runtime Broker Exit code: 0 Version: 10.0.16299.15 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1436 | rundll32.exe C:\Users\admin\AppData\Local\Temp\filename.dll.exe DllRegisterServer | C:\WINDOWS\system32\rundll32.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 10.0.16299.15 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2292 | "C:\Program Files (x86)\Internet Explorer\ielowutil.exe" -CLSID:{0002DF01-0000-0000-C000-000000000046} -Embedding | C:\Program Files (x86)\Internet Explorer\ielowutil.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Low-Mic Utility Tool Exit code: 0 Version: 11.00.16299.371 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3152 | "C:\WINDOWS\system32\cmd.exe" | C:\WINDOWS\system32\cmd.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 3221225786 Version: 10.0.16299.15 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3620 | "C:\Program Files\Internet Explorer\IEXPLORE.EXE" -Embedding | C:\Program Files\Internet Explorer\IEXPLORE.EXE | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 11.00.16299.15 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3824 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\WINDOWS\system32\conhost.exe | cmd.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.16299.15 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5852 | "C:\Program Files (x86)\Internet Explorer\IEXPLORE.EXE" SCODEF:3620 CREDAT:9474 /prefetch:2 | C:\Program Files (x86)\Internet Explorer\IEXPLORE.EXE | — | IEXPLORE.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.16299.15 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
1 520
Read events
1 468
Write events
52
Delete events
0
Modification events
| (PID) Process: | (972) RuntimeBroker.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (972) RuntimeBroker.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (972) RuntimeBroker.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (972) RuntimeBroker.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
| (PID) Process: | (3620) IEXPLORE.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlock |
| Operation: | write | Name: | L1WatermarkLowPart |
Value: 0 | |||
| (PID) Process: | (3620) IEXPLORE.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlock |
| Operation: | write | Name: | L1WatermarkHighPart |
Value: 0 | |||
| (PID) Process: | (3620) IEXPLORE.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlock |
| Operation: | write | Name: | NextCheckForUpdateLowDateTime |
Value: 0 | |||
| (PID) Process: | (3620) IEXPLORE.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlock |
| Operation: | write | Name: | NextCheckForUpdateHighDateTime |
Value: 0 | |||
| (PID) Process: | (3620) IEXPLORE.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlock |
| Operation: | write | Name: | NextCheckForUpdateLowDateTime |
Value: 739084312 | |||
| (PID) Process: | (3620) IEXPLORE.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlock |
| Operation: | write | Name: | NextCheckForUpdateHighDateTime |
Value: 30801479 | |||
Executable files
0
Suspicious files
1
Text files
5
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3620 | IEXPLORE.EXE | C:\Users\admin\AppData\Local\Temp\~DF70575DCB29D4E4D1.TMP | — | |
MD5:— | SHA256:— | |||
| 3620 | IEXPLORE.EXE | C:\Users\admin\AppData\Local\Microsoft\Internet Explorer\Recovery\Active\{57B4AEC6-6A3A-11EA-B467-5254004AAD11}.dat | binary | |
MD5:— | SHA256:— | |||
| 5852 | IEXPLORE.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\INetCache\Low\IE\2I6MPL32\errorPageStrings[1] | text | |
MD5:D65EC06F21C379C87040B83CC1ABAC6B | SHA256:A1270E90CEA31B46432EC44731BF4400D22B38EB2855326BF934FE8F1B169A4F | |||
| 5852 | IEXPLORE.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\INetCache\Low\IE\LD57I5PR\dnserror[1] | html | |
MD5:2DC61EB461DA1436F5D22BCE51425660 | SHA256:ACDEB4966289B6CE46ECC879531F85E9C6F94B718AAB521D38E2E00F7F7F7993 | |||
| 5852 | IEXPLORE.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\INetCache\Low\IE\FZ4P8RAN\down[1] | image | |
MD5:C4F558C4C8B56858F15C09037CD6625A | SHA256:39E7DE847C9F731EAA72338AD9053217B957859DE27B50B6474EC42971530781 | |||
| 5852 | IEXPLORE.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\INetCache\Low\IE\FZ4P8RAN\NewErrorPageTemplate[1] | text | |
MD5:DFEABDE84792228093A5A270352395B6 | SHA256:77B138AB5D0A90FF04648C26ADDD5E414CC178165E3B54A4CB3739DA0F58E075 | |||
| 5852 | IEXPLORE.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\INetCache\Low\IE\LD57I5PR\httpErrorPagesScripts[1] | text | |
MD5:9234071287E637F85D721463C488704C | SHA256:65CC039890C7CEB927CE40F6F199D74E49B8058C3F8A6E22E8F916AD90EA8649 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
1
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
DNS requests
Domain | IP | Reputation |
|---|---|---|
self.events.data.microsoft.com |
| whitelisted |
Threats
Process | Message |
|---|---|
conhost.exe | InitSideBySide failed create an activation context. Error: 1814 |