| File name: | NET-Framework-3.5-Offline-Installer-v2.3.exe |
| Full analysis: | https://app.any.run/tasks/b41864c6-7a04-4c61-9401-0934b4f552f3 |
| Verdict: | Malicious activity |
| Analysis date: | March 22, 2025, 13:13:08 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32 executable (GUI) Intel 80386 Mono/.Net assembly, for MS Windows, 4 sections |
| MD5: | BF910159424F982FA71DE43D86852EF3 |
| SHA1: | AC5606049B48F154A616107E4BD2794C4FDA2B49 |
| SHA256: | 7CD40346E324680B6825381E0B931C5D7297280EE818BB837E64B773103D5A29 |
| SSDEEP: | 12288:X53feMW8ldNPLotBOp+tfoq0IRlTKb553feMW8ldS:X53fE8ldNPLotBw+aq0IfTKl53fE8ldS |
MALICIOUS
No malicious indicators.SUSPICIOUS
Reads security settings of Internet Explorer
- NET-Framework-3.5-Offline-Installer-v2.3.exe (PID: 5960)
Reads the date of Windows installation
- NET-Framework-3.5-Offline-Installer-v2.3.exe (PID: 5960)
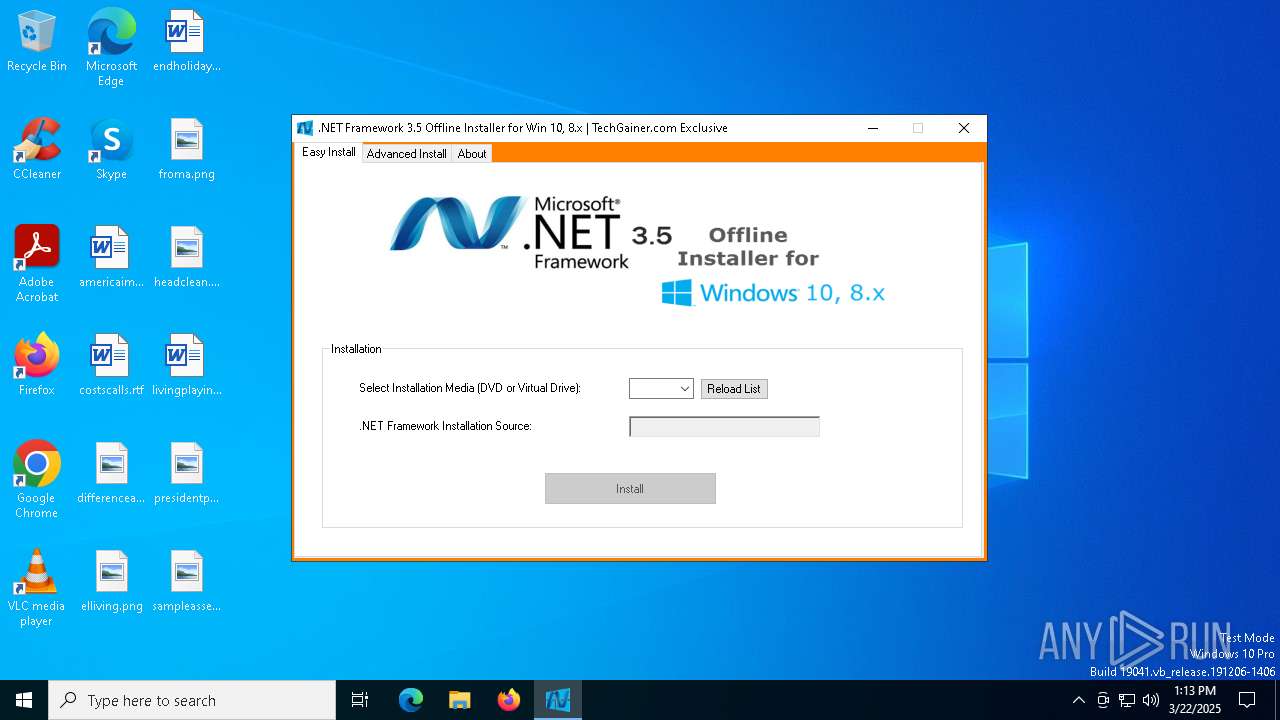
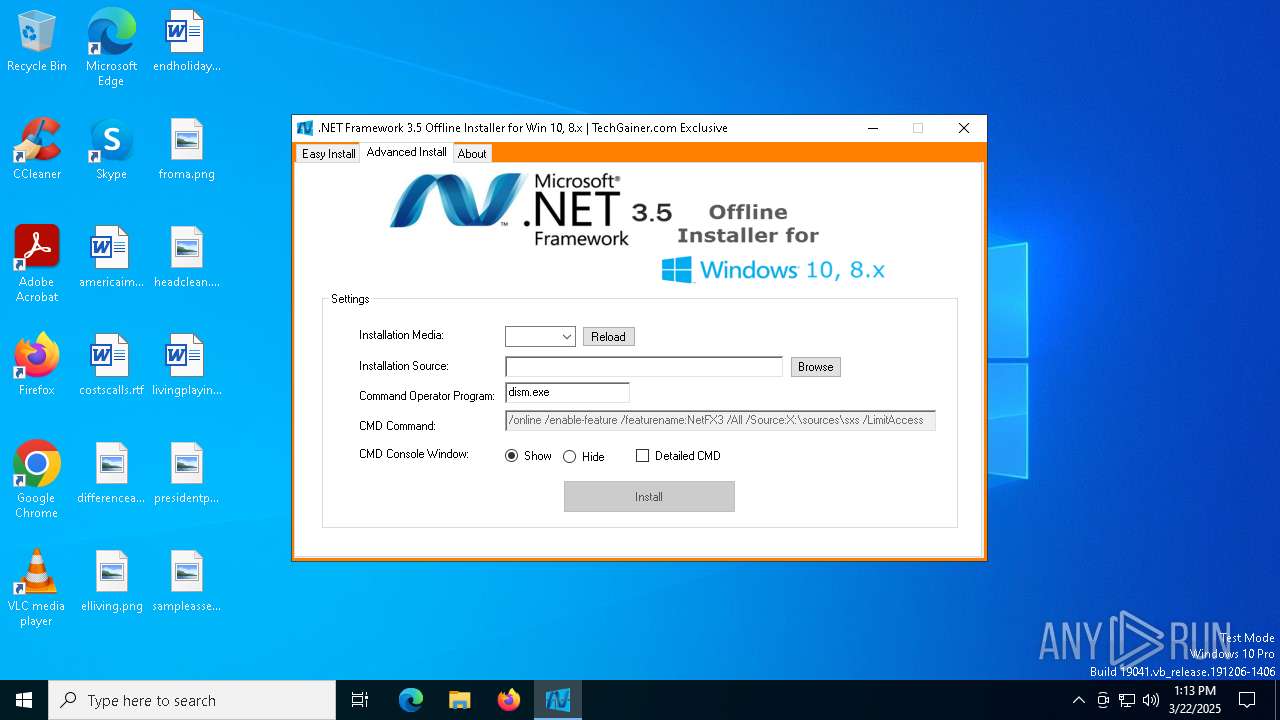
Starts CMD.EXE for commands execution
- NET-Framework-3.5-Offline-Installer-v2.3.exe (PID: 5960)
Executing commands from a ".bat" file
- NET-Framework-3.5-Offline-Installer-v2.3.exe (PID: 5960)
Likely accesses (executes) a file from the Public directory
- cmd.exe (PID: 7000)
The process creates files with name similar to system file names
- Dism.exe (PID: 904)
Executable content was dropped or overwritten
- Dism.exe (PID: 904)
Starts a Microsoft application from unusual location
- DismHost.exe (PID: 5988)
Executes as Windows Service
- VSSVC.exe (PID: 4980)
Searches for installed software
- TiWorker.exe (PID: 896)
INFO
Process checks computer location settings
- NET-Framework-3.5-Offline-Installer-v2.3.exe (PID: 5960)
Checks supported languages
- NET-Framework-3.5-Offline-Installer-v2.3.exe (PID: 5960)
- DismHost.exe (PID: 5988)
Reads the machine GUID from the registry
- NET-Framework-3.5-Offline-Installer-v2.3.exe (PID: 5960)
Reads the computer name
- NET-Framework-3.5-Offline-Installer-v2.3.exe (PID: 5960)
- DismHost.exe (PID: 5988)
The sample compiled with english language support
- Dism.exe (PID: 904)
Create files in a temporary directory
- Dism.exe (PID: 904)
Reads Environment values
- DismHost.exe (PID: 5988)
Manages system restore points
- SrTasks.exe (PID: 4208)
Reads the software policy settings
- TiWorker.exe (PID: 896)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Generic CIL Executable (.NET, Mono, etc.) (55.8) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (21) |
| .scr | | | Windows screen saver (9.9) |
| .dll | | | Win32 Dynamic Link Library (generic) (5) |
| .exe | | | Win32 Executable (generic) (3.4) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2014:12:15 18:25:24+00:00 |
| ImageFileCharacteristics: | Executable, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 11 |
| CodeSize: | 325120 |
| InitializedDataSize: | 89600 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x5141e |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 2.3.0.0 |
| ProductVersionNumber: | 2.3.0.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Unicode |
| FileDescription: | .NET Framework 3.5 Offline Installer |
| FileVersion: | 2.3.0.0 |
| InternalName: | .NET Framework Offline Installer.exe |
| LegalCopyright: | Copyright © 2014 TechGainer |
| OriginalFileName: | .NET Framework Offline Installer.exe |
| ProductName: | .NET Framework 3.5 Offline Installer |
| ProductVersion: | 2.3.0.0 |
| AssemblyVersion: | 2.3.0.0 |
Total processes
139
Monitored processes
12
Malicious processes
1
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 896 | C:\WINDOWS\winsxs\amd64_microsoft-windows-servicingstack_31bf3856ad364e35_10.0.19041.3989_none_7ddb45627cb30e03\TiWorker.exe -Embedding | C:\Windows\WinSxS\amd64_microsoft-windows-servicingstack_31bf3856ad364e35_10.0.19041.3989_none_7ddb45627cb30e03\TiWorker.exe | — | svchost.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows Modules Installer Worker Version: 10.0.19041.3989 (WinBuild.160101.0800) Modules
| |||||||||||||||
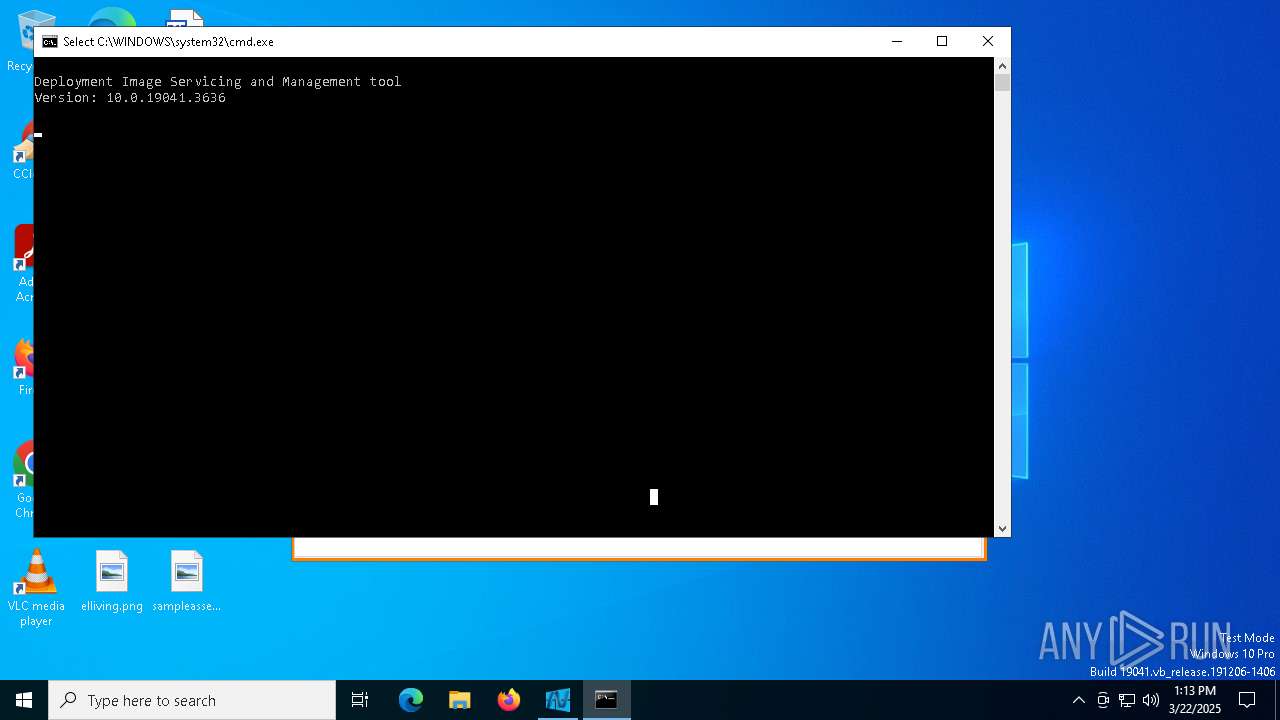
| 904 | dism.exe /online /enable-feature /featurename:NetFX3 /source:C:\sources\sxs /LimitAccess | C:\Windows\System32\Dism.exe | cmd.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Dism Image Servicing Utility Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4008 | C:\WINDOWS\system32\SppExtComObj.exe -Embedding | C:\Windows\System32\SppExtComObj.Exe | — | svchost.exe | |||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: KMS Connection Broker Version: 10.0.19041.3996 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4208 | C:\WINDOWS\system32\srtasks.exe ExecuteScopeRestorePoint /WaitForRestorePoint:11 | C:\Windows\System32\SrTasks.exe | — | TiWorker.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft® Windows System Protection background tasks. Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4980 | C:\WINDOWS\system32\vssvc.exe | C:\Windows\System32\VSSVC.exe | — | services.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft® Volume Shadow Copy Service Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5744 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5960 | "C:\WINDOWS\NET-Framework-3.5-Offline-Installer-v2.3.exe" | C:\Windows\NET-Framework-3.5-Offline-Installer-v2.3.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: HIGH Description: .NET Framework 3.5 Offline Installer Version: 2.3.0.0 Modules
| |||||||||||||||
| 5988 | C:\Users\admin\AppData\Local\Temp\0CBEEC6F-1CD0-4A60-A61F-A10766830ACA\dismhost.exe {691746C8-2FD3-4347-B86A-6FA81195BF2F} | C:\Users\admin\AppData\Local\Temp\0CBEEC6F-1CD0-4A60-A61F-A10766830ACA\DismHost.exe | — | Dism.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Dism Host Servicing Process Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6252 | "C:\WINDOWS\NET-Framework-3.5-Offline-Installer-v2.3.exe" | C:\Windows\NET-Framework-3.5-Offline-Installer-v2.3.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: .NET Framework 3.5 Offline Installer Exit code: 3221226540 Version: 2.3.0.0 Modules
| |||||||||||||||
| 6560 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | SrTasks.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Console Window Host Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
27 407
Read events
27 137
Write events
228
Delete events
42
Modification events
| (PID) Process: | (896) TiWorker.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Component Based Servicing |
| Operation: | write | Name: | SessionIdHigh |
Value: 31169324 | |||
| (PID) Process: | (896) TiWorker.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Component Based Servicing |
| Operation: | write | Name: | SessionIdLow |
Value: | |||
| (PID) Process: | (896) TiWorker.exe | Key: | HKEY_LOCAL_MACHINE\COMPONENTS\ServicingStackVersions |
| Operation: | write | Name: | 10.0.19041.3989 (WinBuild.160101.0800) |
Value: 2025/3/22:13:13:56.24 10.0.19041.3989 (WinBuild.160101.0800) | |||
| (PID) Process: | (896) TiWorker.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Component Based Servicing\SessionsPending\31169324_1113068007 |
| Operation: | write | Name: | 1_Queued |
Value: 2025/03/22/13:13:56 | |||
| (PID) Process: | (896) TiWorker.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Component Based Servicing\SessionsPending\31169324_1113068007 |
| Operation: | write | Name: | 1_QueuedTimeLow |
Value: | |||
| (PID) Process: | (896) TiWorker.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Component Based Servicing\SessionsPending\31169324_1113068007 |
| Operation: | write | Name: | 1_QueuedTimeHigh |
Value: 31169324 | |||
| (PID) Process: | (896) TiWorker.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Component Based Servicing\SessionsPending\31169324_1113068007 |
| Operation: | write | Name: | LastModified |
Value: 2025/03/22/13:13:56 | |||
| (PID) Process: | (896) TiWorker.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SystemRestore |
| Operation: | write | Name: | SrCreateRp (Enter) |
Value: 48000000000000007B5118442C9BDB0180030000901A0000D50700000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (896) TiWorker.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SPP |
| Operation: | write | Name: | SppGetSnapshots (Enter) |
Value: 480000000000000083A21A442C9BDB0180030000901A0000D20700000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (896) TiWorker.exe | Key: | HKEY_LOCAL_MACHINE\COMPONENTS |
| Operation: | delete value | Name: | PendingRequired |
Value: | |||
Executable files
50
Suspicious files
10
Text files
12
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 904 | Dism.exe | C:\Users\admin\AppData\Local\Temp\0CBEEC6F-1CD0-4A60-A61F-A10766830ACA\DismHost.exe | executable | |
MD5:97CB1E2FCAB378421C4B91DF0C9F8310 | SHA256:E36BCF02BC11F560761E943D0FAD37417078F6CBB473F85C72FCBC89E2600C58 | |||
| 904 | Dism.exe | C:\Users\admin\AppData\Local\Temp\0CBEEC6F-1CD0-4A60-A61F-A10766830ACA\en-US\AppxProvider.dll.mui | executable | |
MD5:BD0DD9C5A602CB0AD7EABC16B3C1ABFC | SHA256:8AF0073F8A023F55866E48BF3B902DFA7F41C51B0E8B0FE06F8C496D41F9A7B3 | |||
| 904 | Dism.exe | C:\Users\admin\AppData\Local\Temp\0CBEEC6F-1CD0-4A60-A61F-A10766830ACA\DismCore.dll | executable | |
MD5:681186B5696BA7D46B6681C027A659AD | SHA256:FBB5135DE4F6A5C9422A0B218D676930DB9BC9A2AEA0F7219077862912455914 | |||
| 904 | Dism.exe | C:\Users\admin\AppData\Local\Temp\0CBEEC6F-1CD0-4A60-A61F-A10766830ACA\CbsProvider.dll | executable | |
MD5:14932441A96E254B3D29D452CE1263A0 | SHA256:8FFF21CB7C88A0DD8C8E7B386604001F2974E75D229369A87BEE0BA18DA575F3 | |||
| 904 | Dism.exe | C:\Users\admin\AppData\Local\Temp\0CBEEC6F-1CD0-4A60-A61F-A10766830ACA\DismCorePS.dll | executable | |
MD5:35A07968EC37231249F3F072AE555E3A | SHA256:E5F25E5A170CB3D165C3D143EAE967B96AB80F88FB09176DA8591B0B68C77E00 | |||
| 904 | Dism.exe | C:\Users\admin\AppData\Local\Temp\0CBEEC6F-1CD0-4A60-A61F-A10766830ACA\en-US\AssocProvider.dll.mui | executable | |
MD5:8833761572F0964BDC1BEA6E1667F458 | SHA256:B18C6CE1558C9EF6942A3BCE246A46557C2A7D12AEC6C4A07E4FA84DD5C422F5 | |||
| 904 | Dism.exe | C:\Users\admin\AppData\Local\Temp\0CBEEC6F-1CD0-4A60-A61F-A10766830ACA\DismProv.dll | executable | |
MD5:AB0DBC4F05B33EAAA447E31ACCAB8D21 | SHA256:6A3C3F07BDDBC3079873F8799F2C19ADDDC59F15D6B2DBA6E9314E5626BFD2A0 | |||
| 904 | Dism.exe | C:\Users\admin\AppData\Local\Temp\0CBEEC6F-1CD0-4A60-A61F-A10766830ACA\en-US\DismProv.dll.mui | executable | |
MD5:7D06108999CC83EB3A23EADCEBB547A5 | SHA256:CF8CC85CDD12CF4A02DF5274F8D0CDC625C6409FE80866B3052B7D5A862AC311 | |||
| 904 | Dism.exe | C:\Users\admin\AppData\Local\Temp\0CBEEC6F-1CD0-4A60-A61F-A10766830ACA\en-US\CbsProvider.dll.mui | executable | |
MD5:6C51A3187D2464C48CC8550B141E25C5 | SHA256:D7A0253D6586E7BBFB0ACB6FACD9A326B32BA1642B458F5B5ED27FECCB4FC199 | |||
| 904 | Dism.exe | C:\Users\admin\AppData\Local\Temp\0CBEEC6F-1CD0-4A60-A61F-A10766830ACA\en-US\DismCore.dll.mui | executable | |
MD5:7A15F6E845F0679DE593C5896FE171F9 | SHA256:F91E3C35B472F95D7B1AE3DC83F9D6BFDE33515AA29E8B310F55D9FE66466419 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
19
DNS requests
2
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
5496 | MoUsoCoreWorker.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
2112 | svchost.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
2104 | svchost.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |