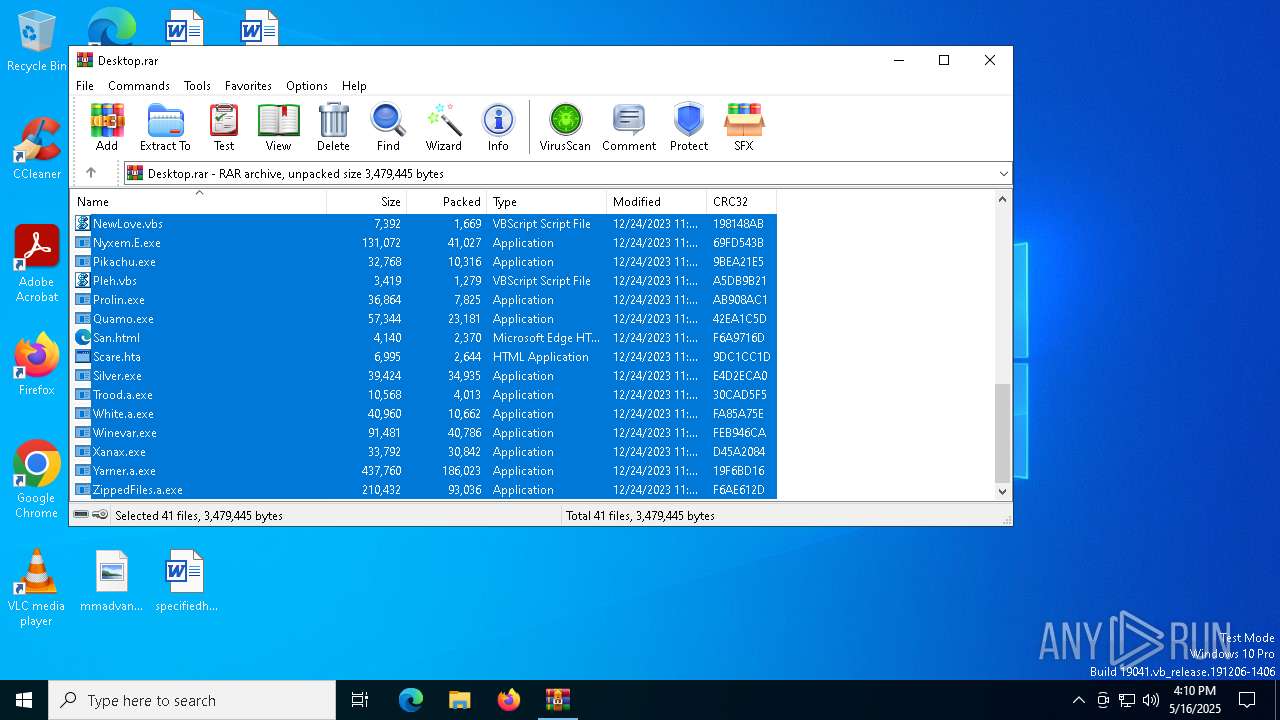
| File name: | Desktop.rar |
| Full analysis: | https://app.any.run/tasks/d5be652a-ff55-4d5a-8a01-a824ca53a3da |
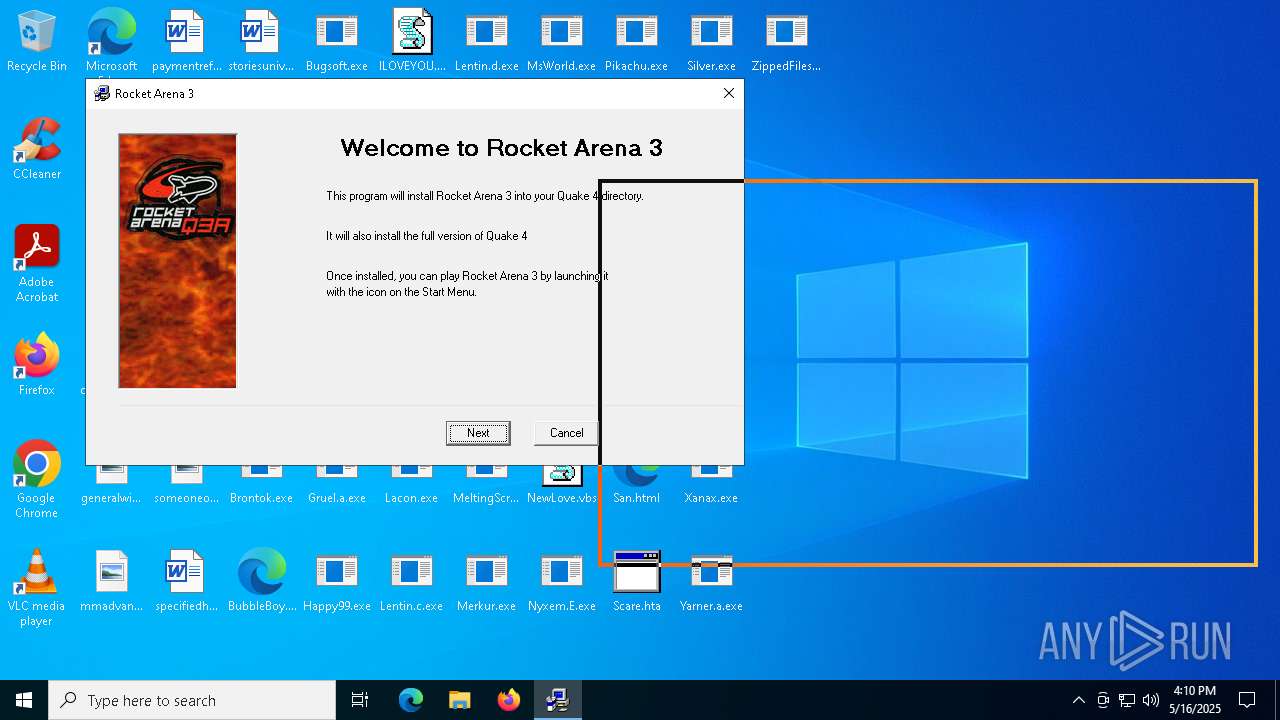
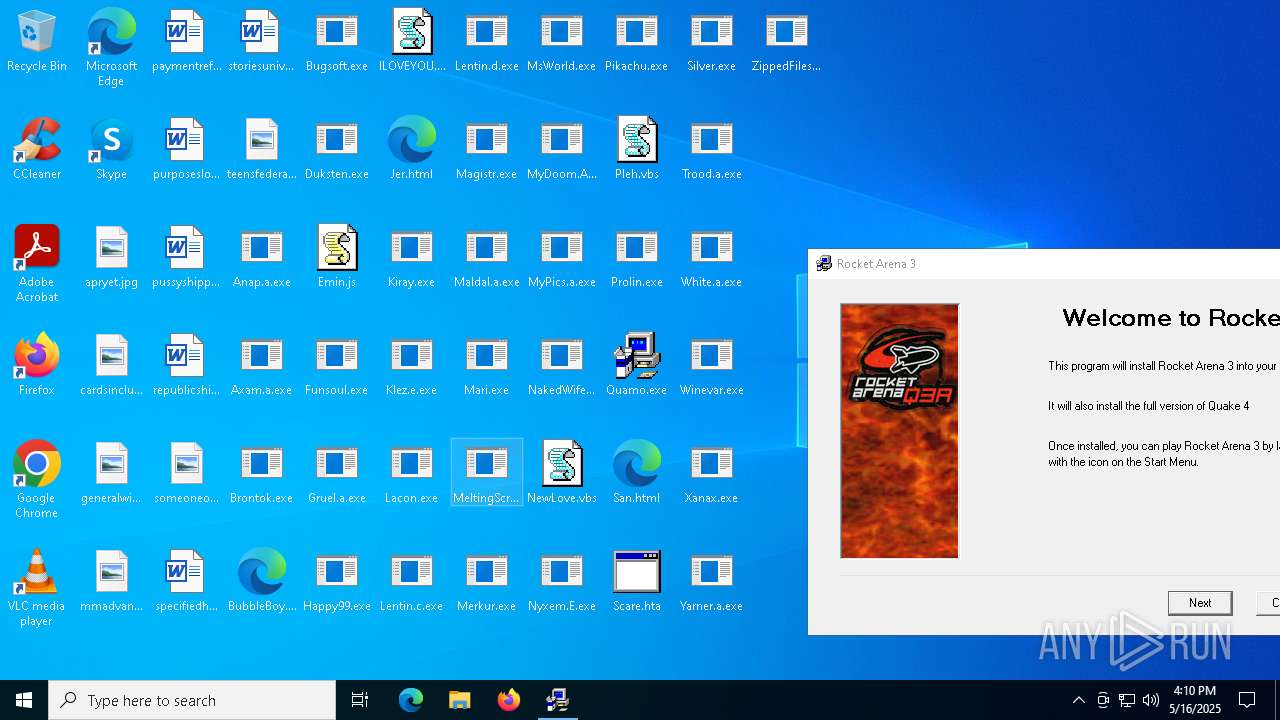
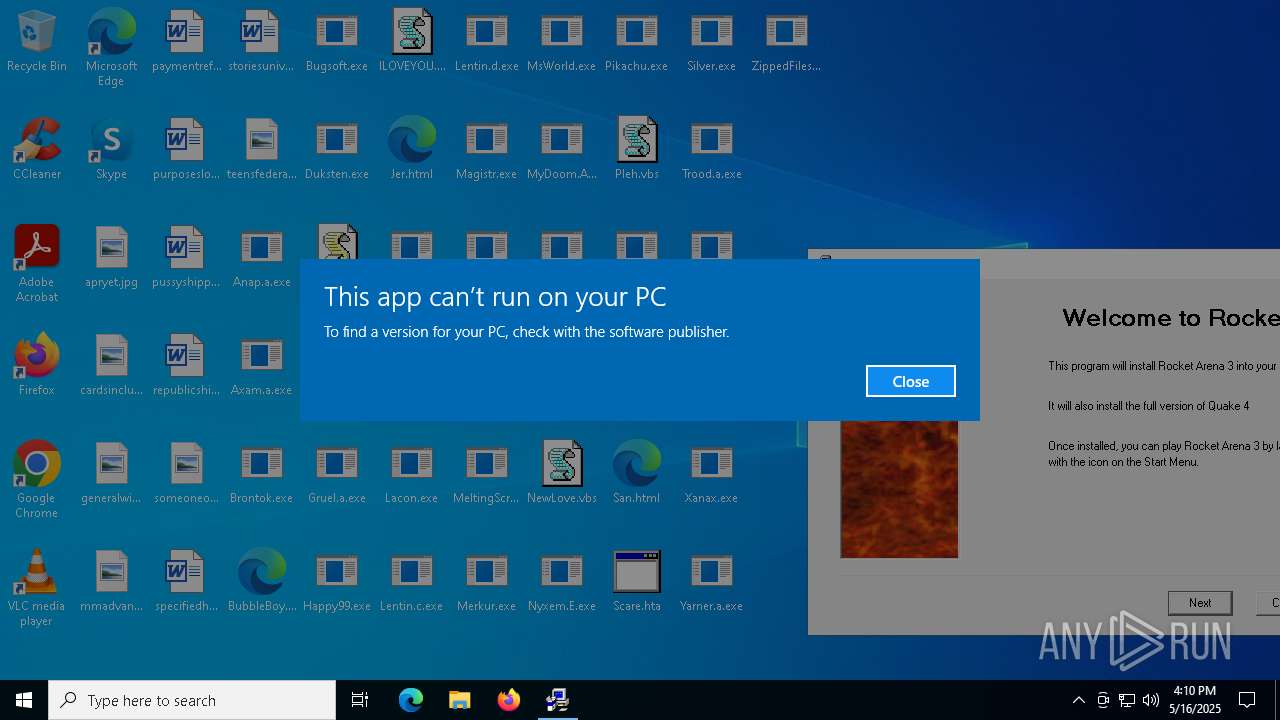
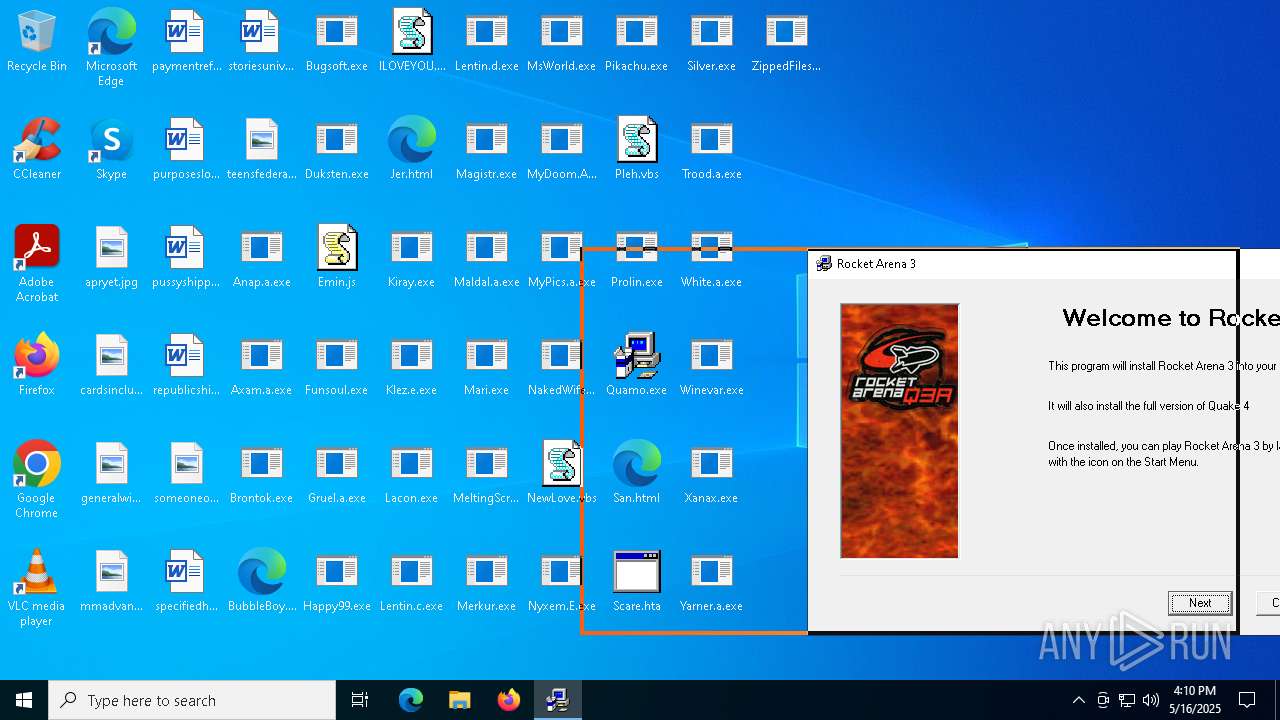
| Verdict: | Malicious activity |
| Analysis date: | May 16, 2025, 16:10:34 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-rar |
| File info: | RAR archive data, v5 |
| MD5: | E7AA9408EE2577D70DEC6B7B8B45B234 |
| SHA1: | D625011A040B62B7C91754344239E274CC2ED935 |
| SHA256: | 7CCFD9B52EA9C8F3FAF6AFAD17BABFF9C052B0B7561B912BCF4030EFB2E9EE78 |
| SSDEEP: | 98304:3Nm+xYOGxxZVEm+PcIPnjSduoiUILbRR9F3vfrgCyMSZdNx0kMmjP5YmTj3alrPK:4URHjy5 |
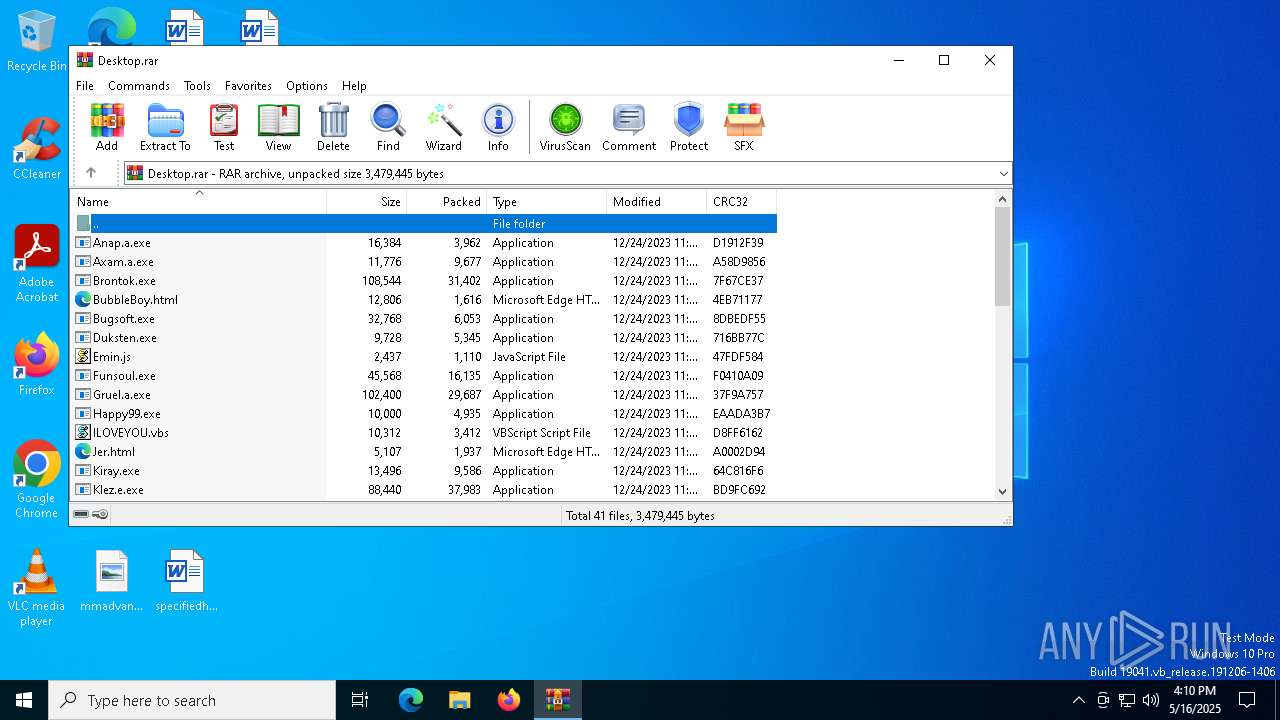
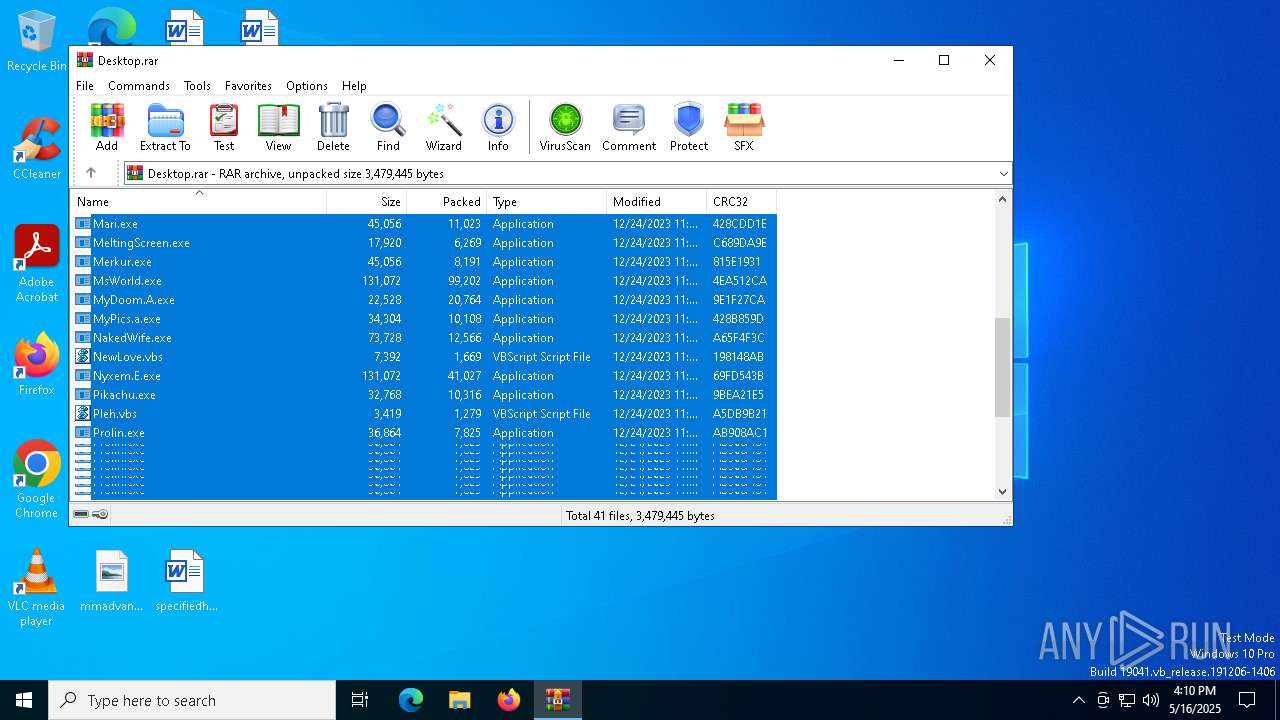
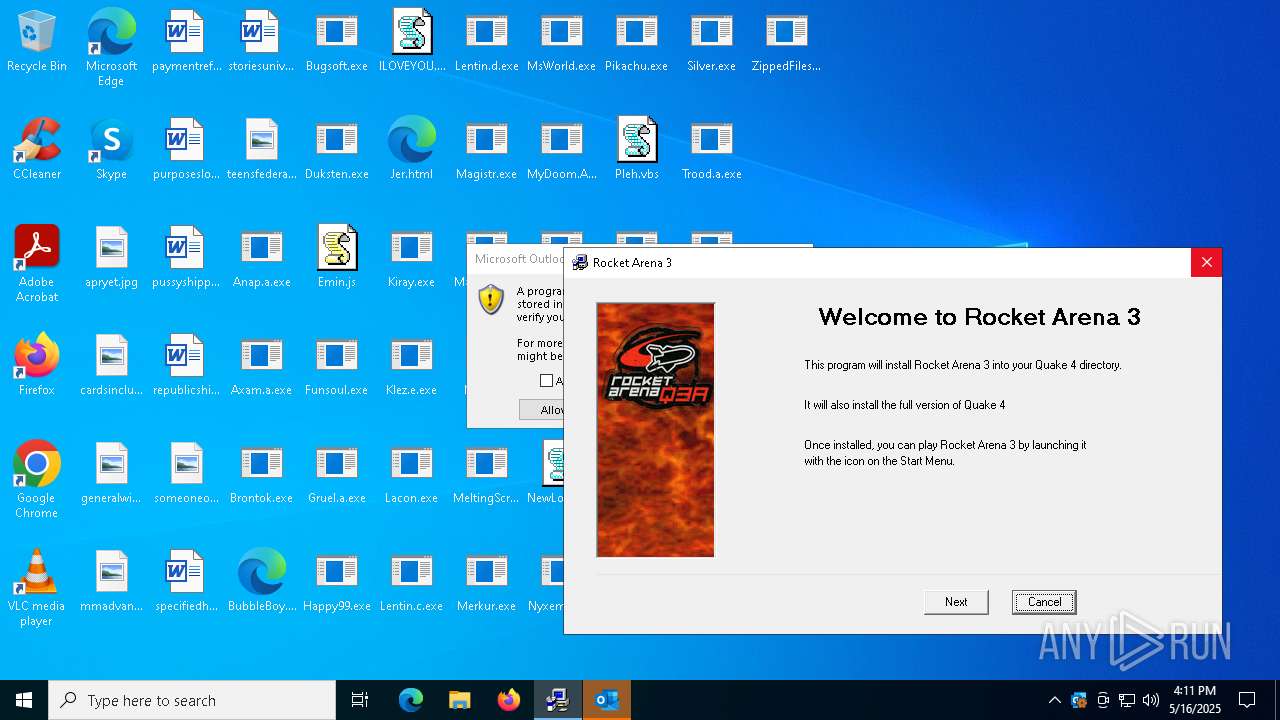
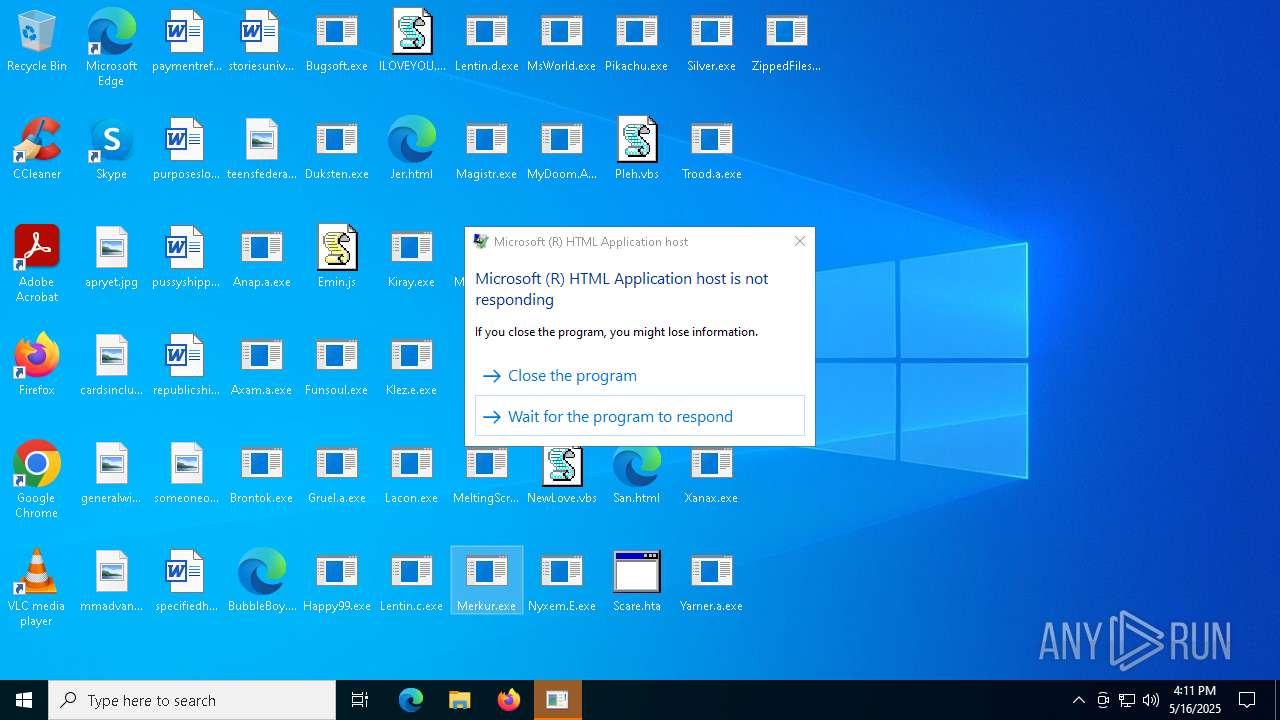
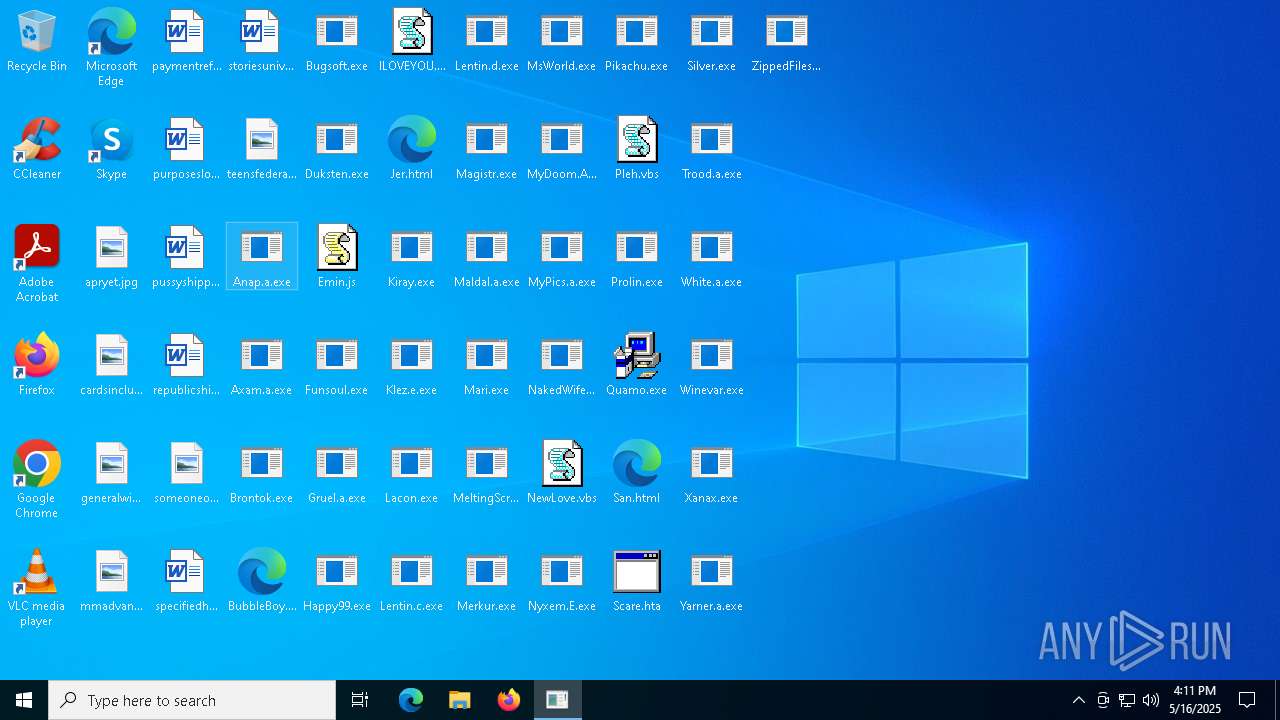
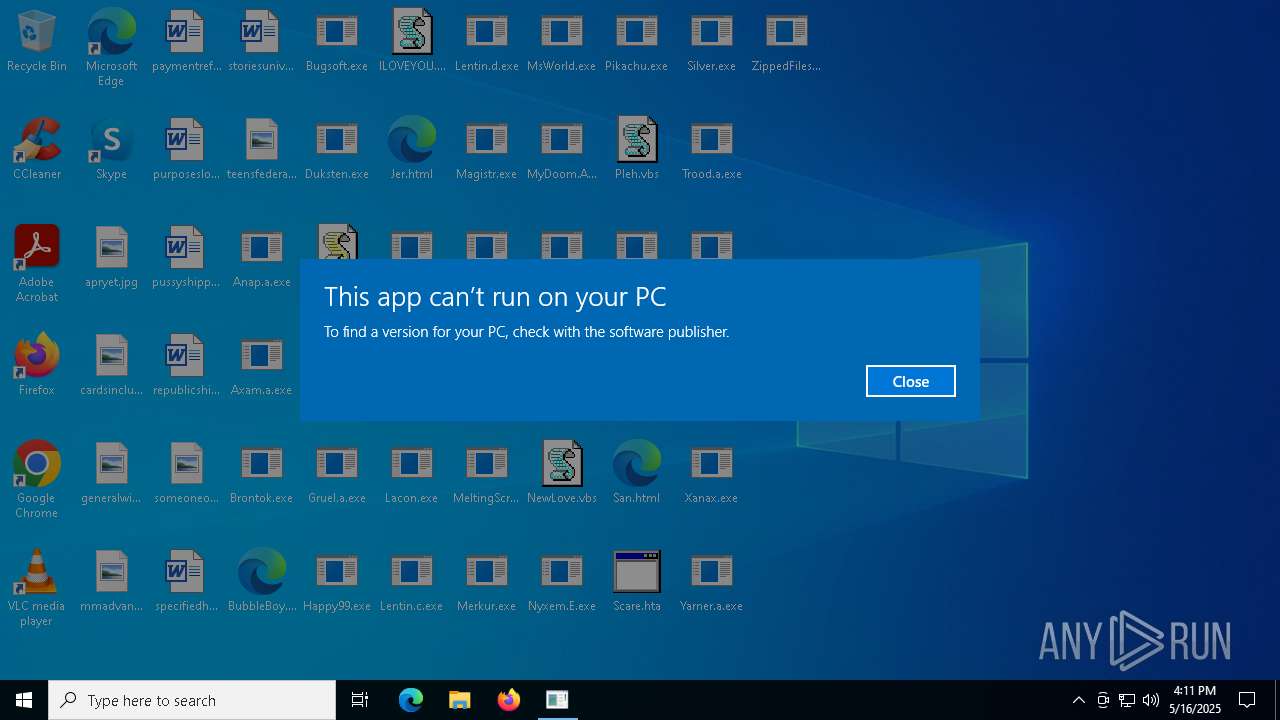
MALICIOUS
MYDOOM has been found (auto)
- WinRAR.exe (PID: 6516)
Changes the autorun value in the registry
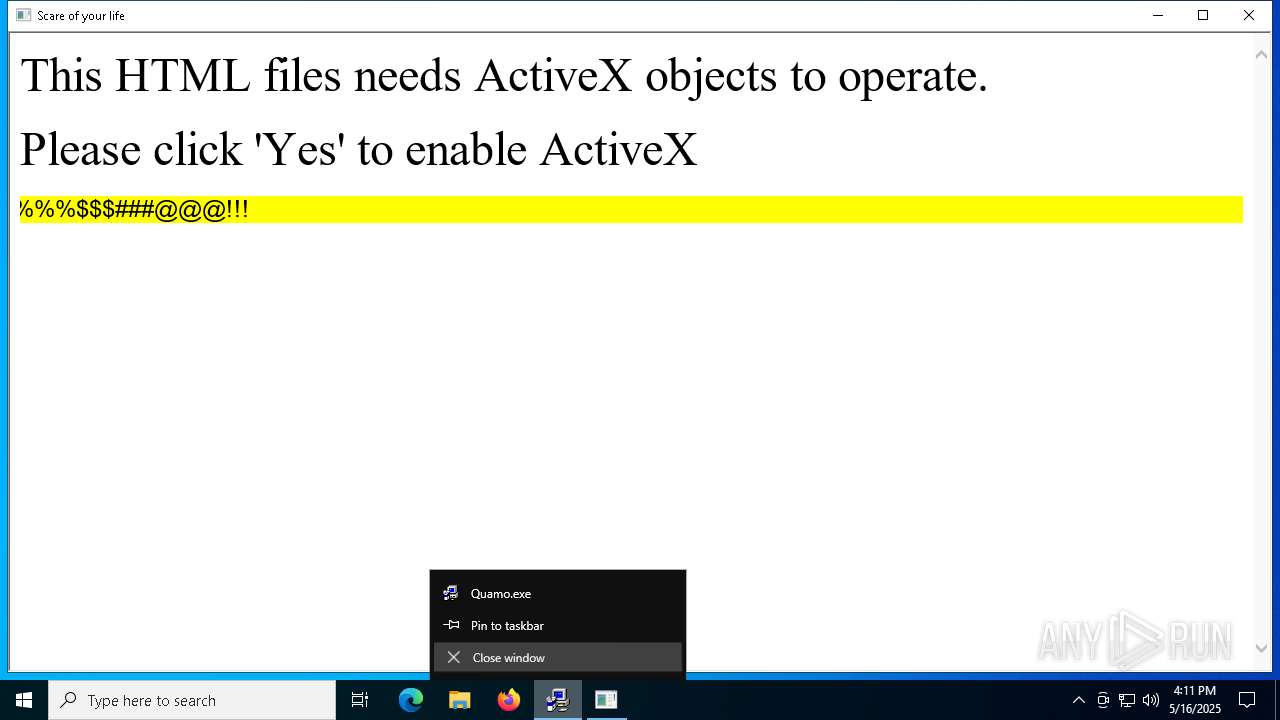
- Quamo.exe (PID: 7020)
- Quamo.exe (PID: 5588)
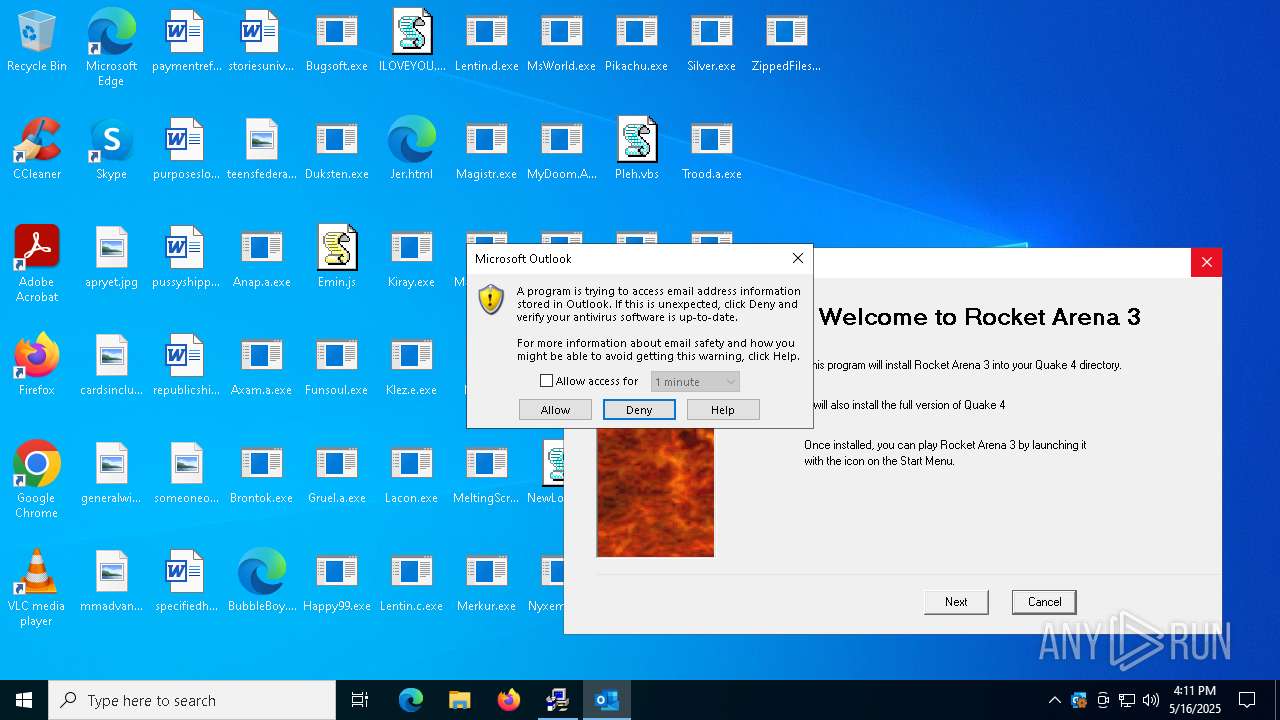
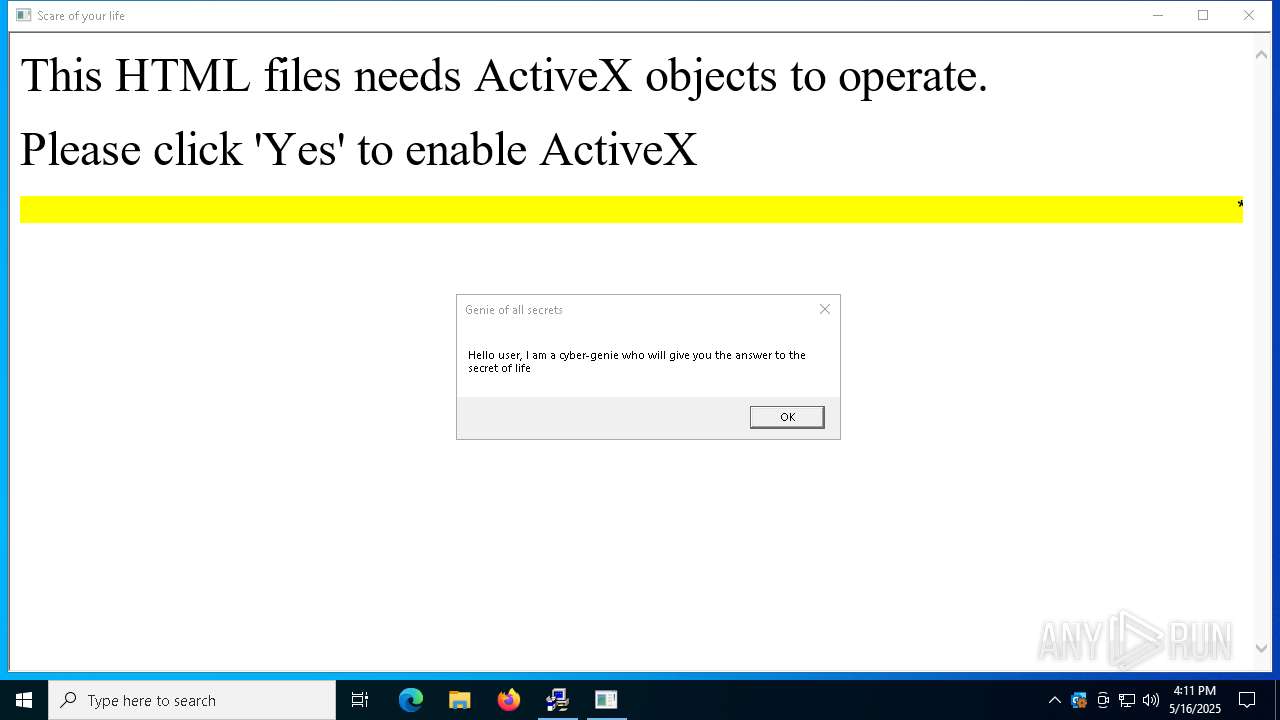
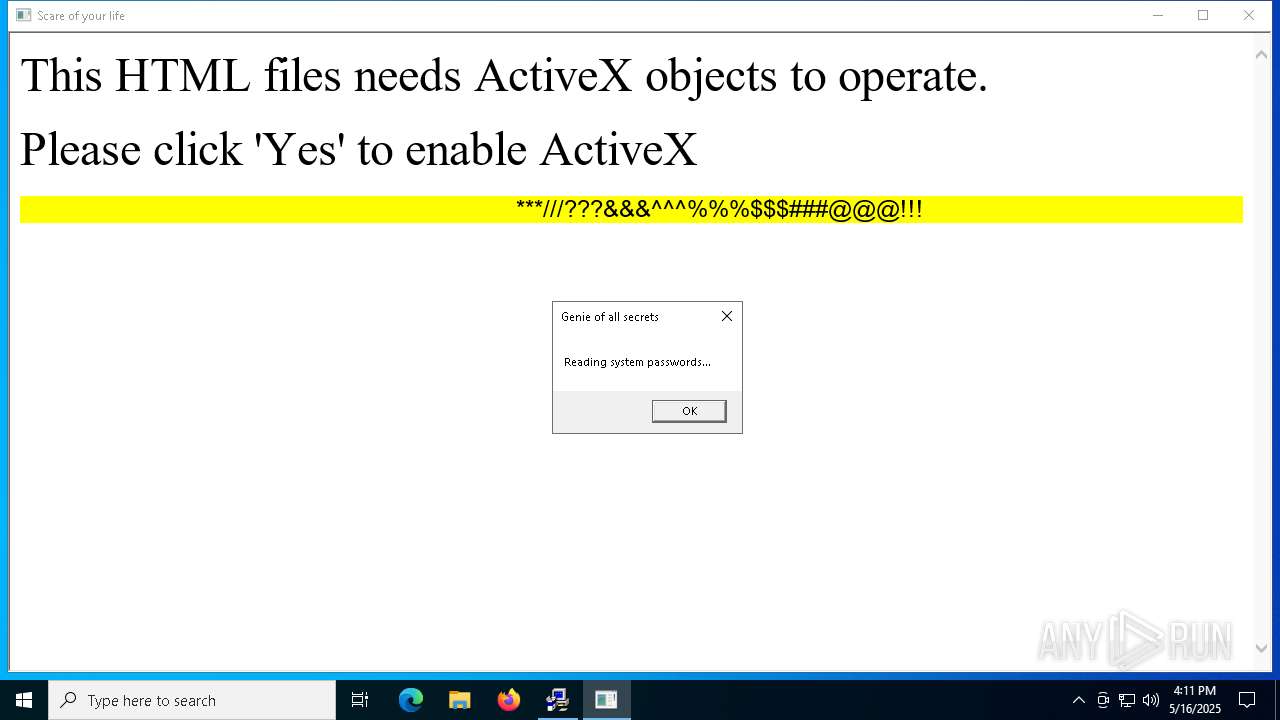
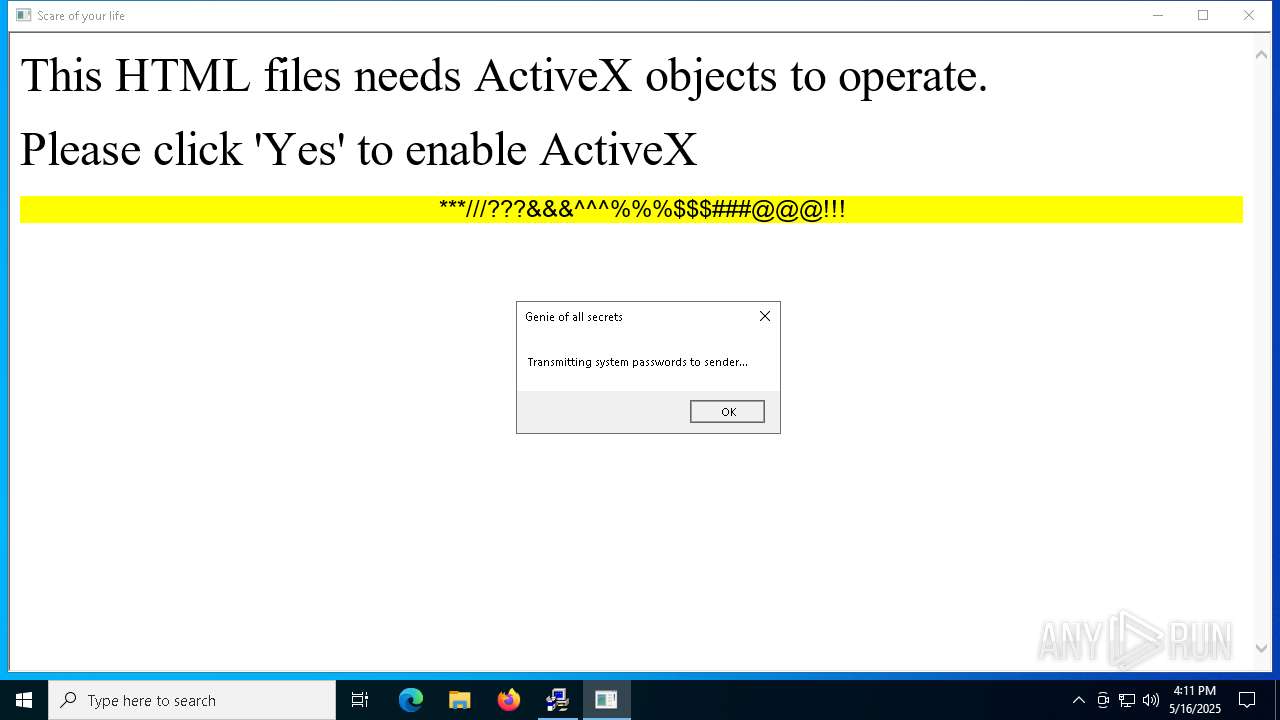
Gets path to any of the special folders (SCRIPT)
- mshta.exe (PID: 4736)
Gets a file object corresponding to the file in a specified path (SCRIPT)
- mshta.exe (PID: 4736)
Opens a text file (SCRIPT)
- mshta.exe (PID: 4736)
SUSPICIOUS
Checks whether a specific file exists (SCRIPT)
- mshta.exe (PID: 4736)
Creates FileSystem object to access computer's file system (SCRIPT)
- mshta.exe (PID: 4736)
Writes binary data to a Stream object (SCRIPT)
- mshta.exe (PID: 4736)
Checks whether the drive is ready (SCRIPT)
- mshta.exe (PID: 4736)
Gets a collection of all available drive names (SCRIPT)
- mshta.exe (PID: 4736)
Reads security settings of Internet Explorer
- ShellExperienceHost.exe (PID: 4112)
Gets the drive type (SCRIPT)
- mshta.exe (PID: 4736)
INFO
Executable content was dropped or overwritten
- WinRAR.exe (PID: 6516)
The sample compiled with german language support
- WinRAR.exe (PID: 6516)
The sample compiled with korean language support
- WinRAR.exe (PID: 6516)
The sample compiled with english language support
- WinRAR.exe (PID: 6516)
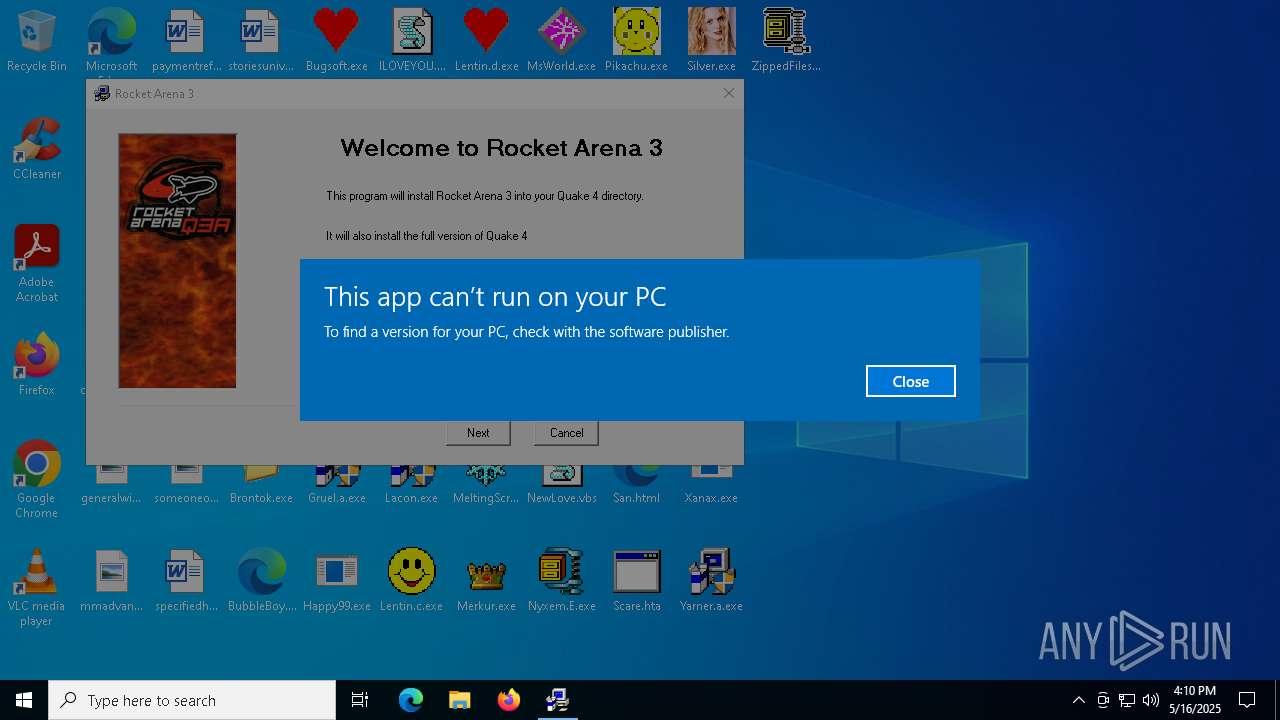
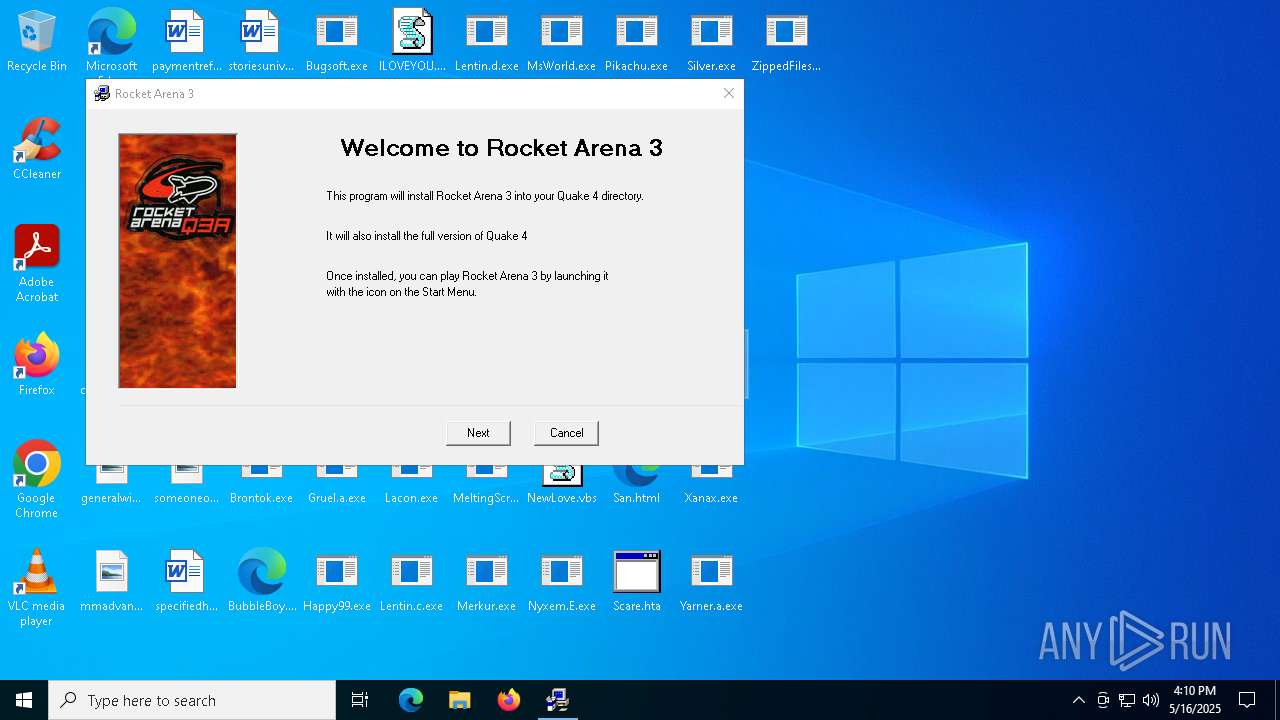
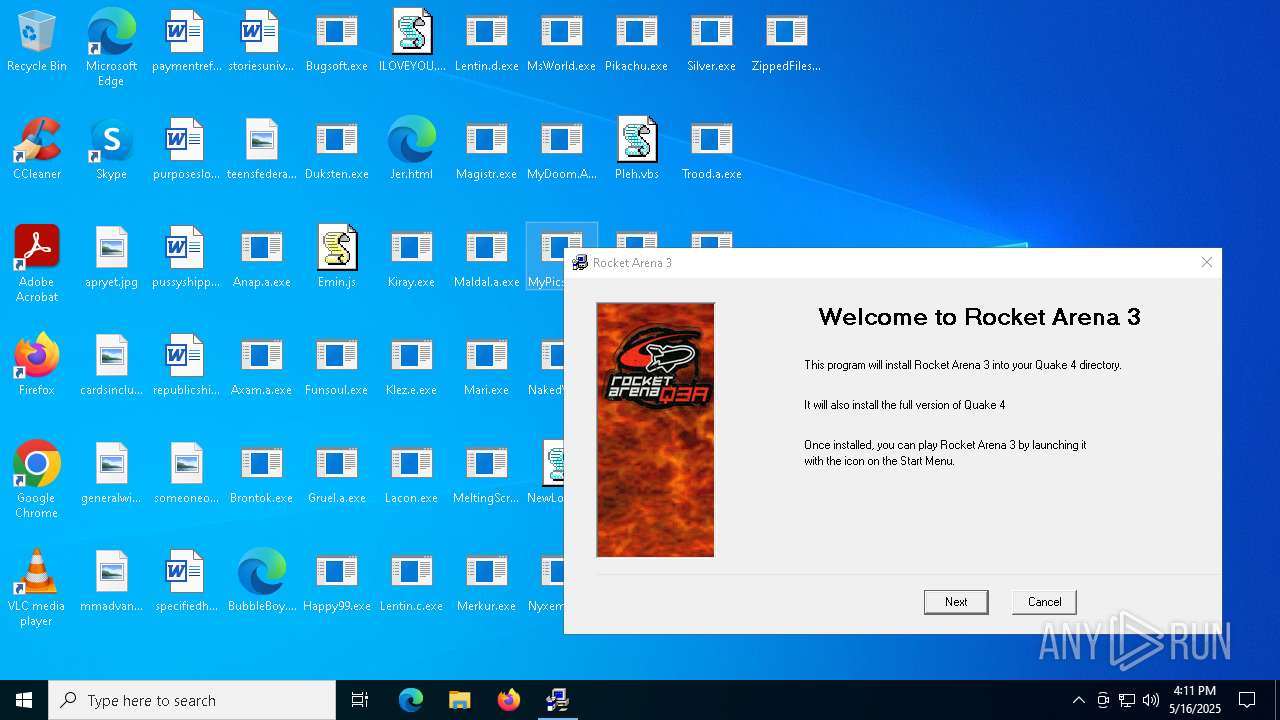
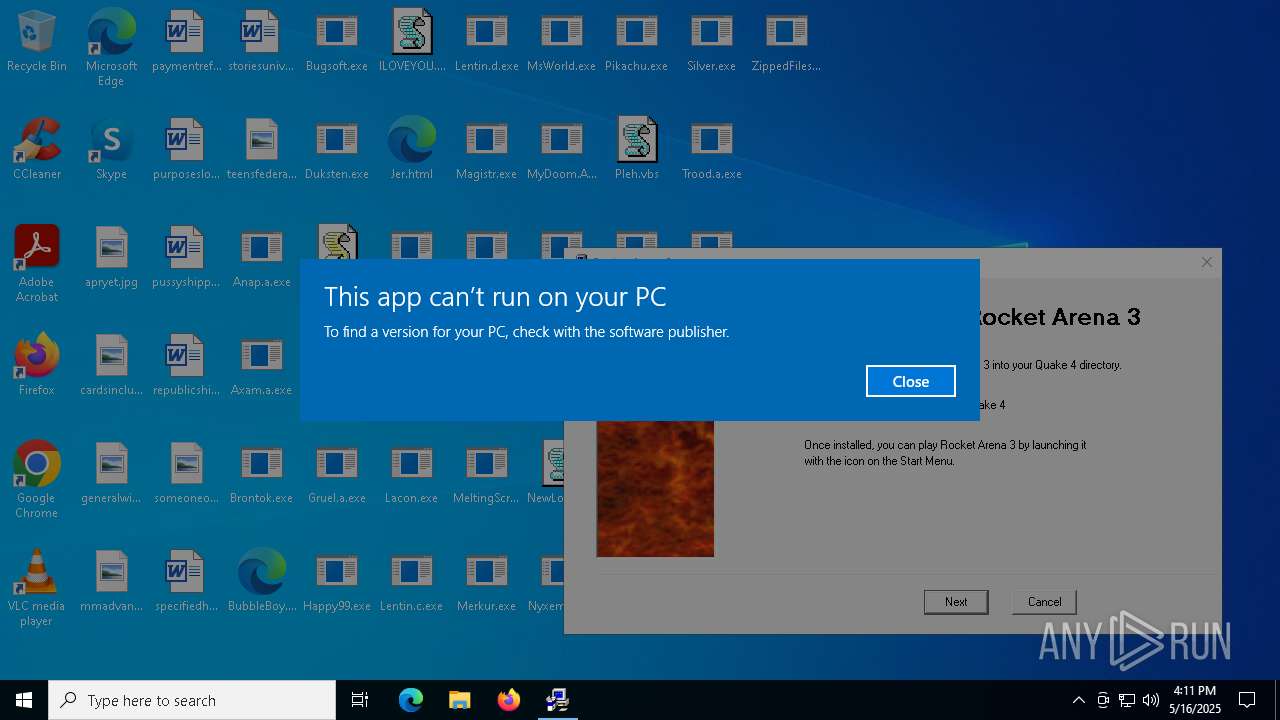
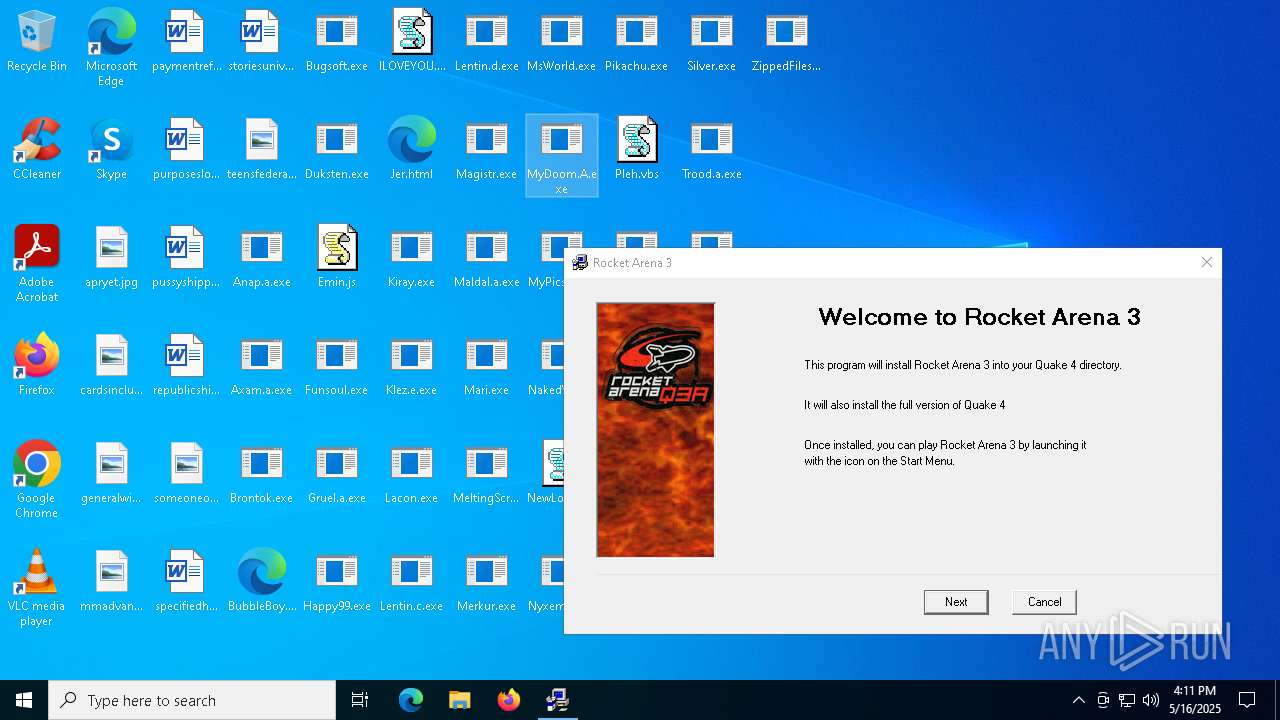
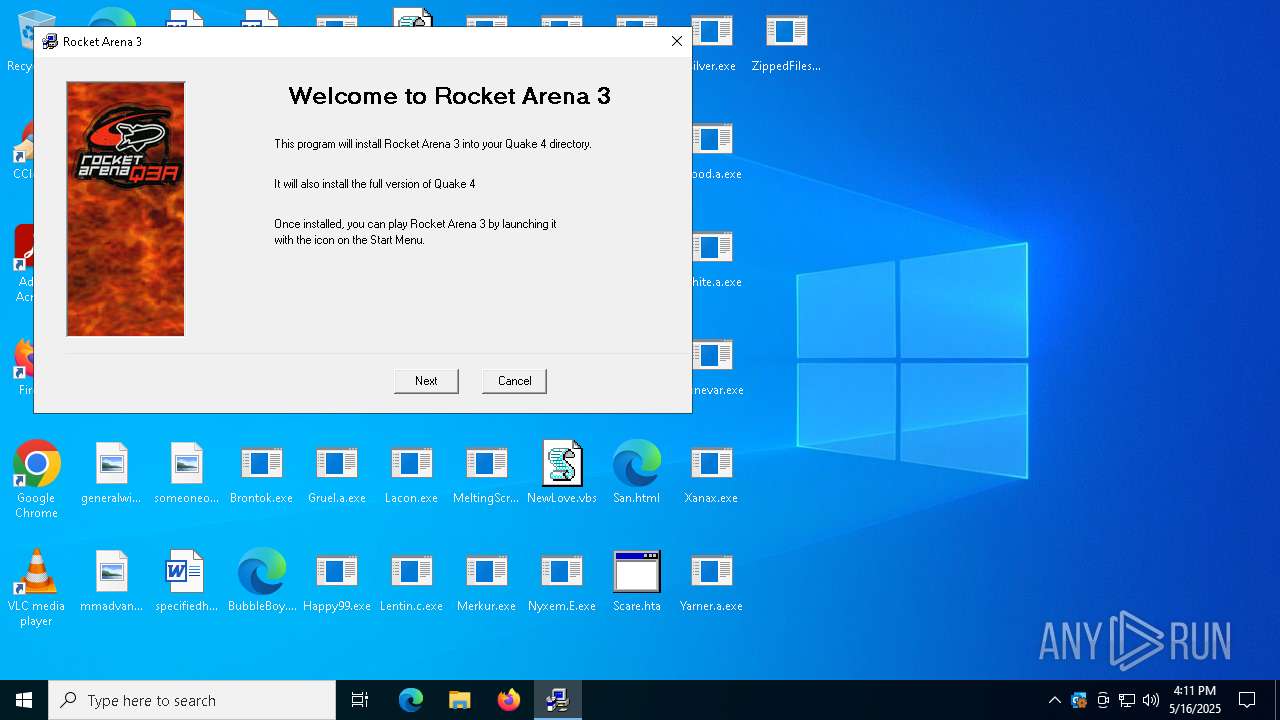
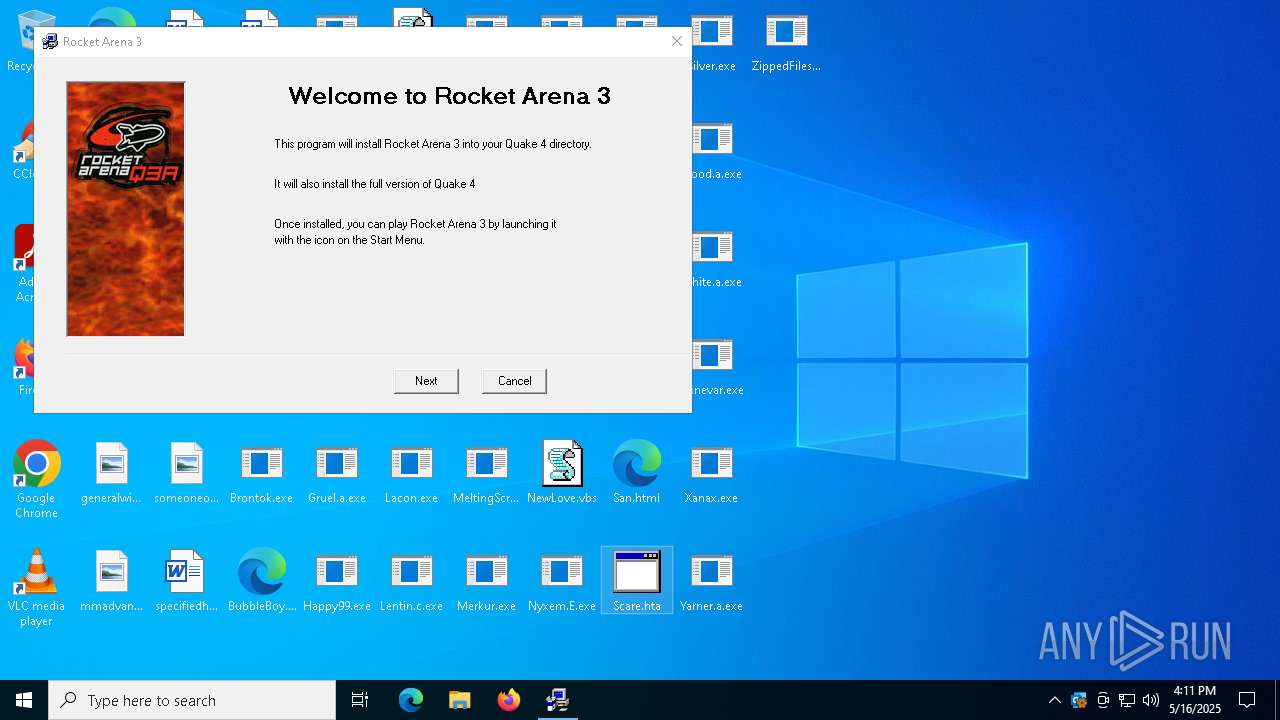
Manual execution by a user
- Quamo.exe (PID: 7020)
- Quamo.exe (PID: 5588)
- mshta.exe (PID: 4736)
Checks supported languages
- Quamo.exe (PID: 7020)
- Quamo.exe (PID: 5588)
- ShellExperienceHost.exe (PID: 4112)
The sample compiled with spanish language support
- WinRAR.exe (PID: 6516)
Create files in a temporary directory
- Quamo.exe (PID: 7020)
- Quamo.exe (PID: 5588)
Reads the computer name
- Quamo.exe (PID: 5588)
- Quamo.exe (PID: 7020)
- ShellExperienceHost.exe (PID: 4112)
Reads Internet Explorer settings
- mshta.exe (PID: 4736)
Reads the software policy settings
- slui.exe (PID: 4980)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .rar | | | RAR compressed archive (v5.0) (61.5) |
|---|---|---|
| .rar | | | RAR compressed archive (gen) (38.4) |
EXIF
ZIP
| FileVersion: | RAR v5 |
|---|---|
| CompressedSize: | 10108 |
| UncompressedSize: | 34304 |
| OperatingSystem: | Win32 |
| ArchivedFileName: | MyPics.a.exe |
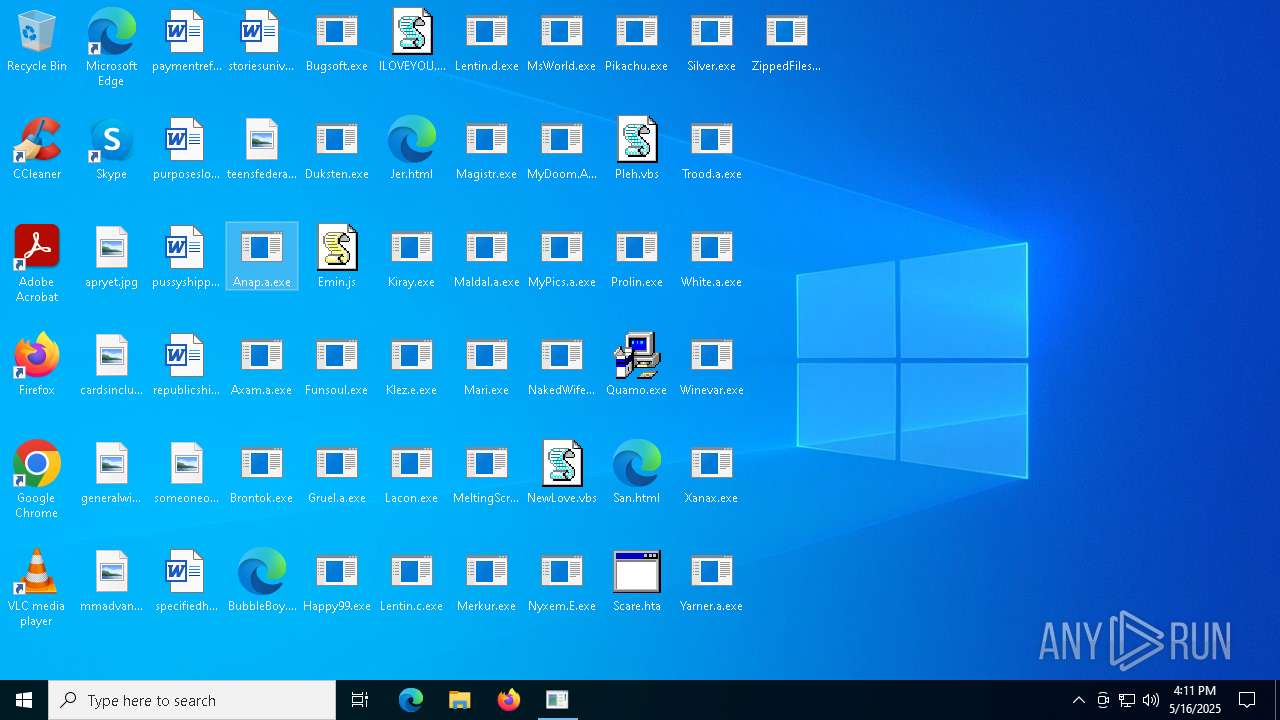
Total processes
140
Monitored processes
9
Malicious processes
4
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1660 | "C:\Program Files\Microsoft Office\Root\Office16\OUTLOOK.EXE" -Embedding | C:\Program Files\Microsoft Office\root\Office16\OUTLOOK.EXE | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Outlook Exit code: 0 Version: 16.0.16026.20146 Modules
| |||||||||||||||
| 4112 | "C:\WINDOWS\SystemApps\ShellExperienceHost_cw5n1h2txyewy\ShellExperienceHost.exe" -ServerName:App.AppXtk181tbxbce2qsex02s8tw7hfxa9xb3t.mca | C:\Windows\SystemApps\ShellExperienceHost_cw5n1h2txyewy\ShellExperienceHost.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Shell Experience Host Version: 10.0.19041.3758 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4300 | C:\WINDOWS\system32\SppExtComObj.exe -Embedding | C:\Windows\System32\SppExtComObj.Exe | — | svchost.exe | |||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: KMS Connection Broker Version: 10.0.19041.3996 (WinBuild.160101.0800) Modules
| |||||||||||||||
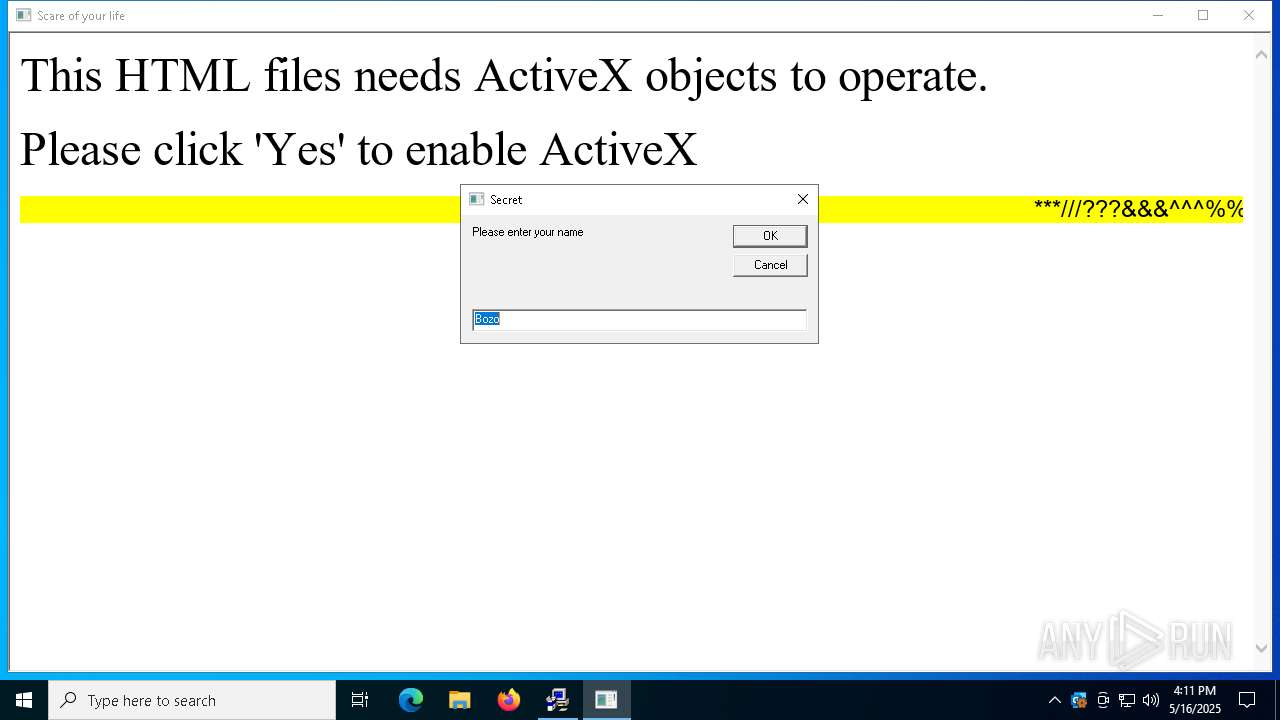
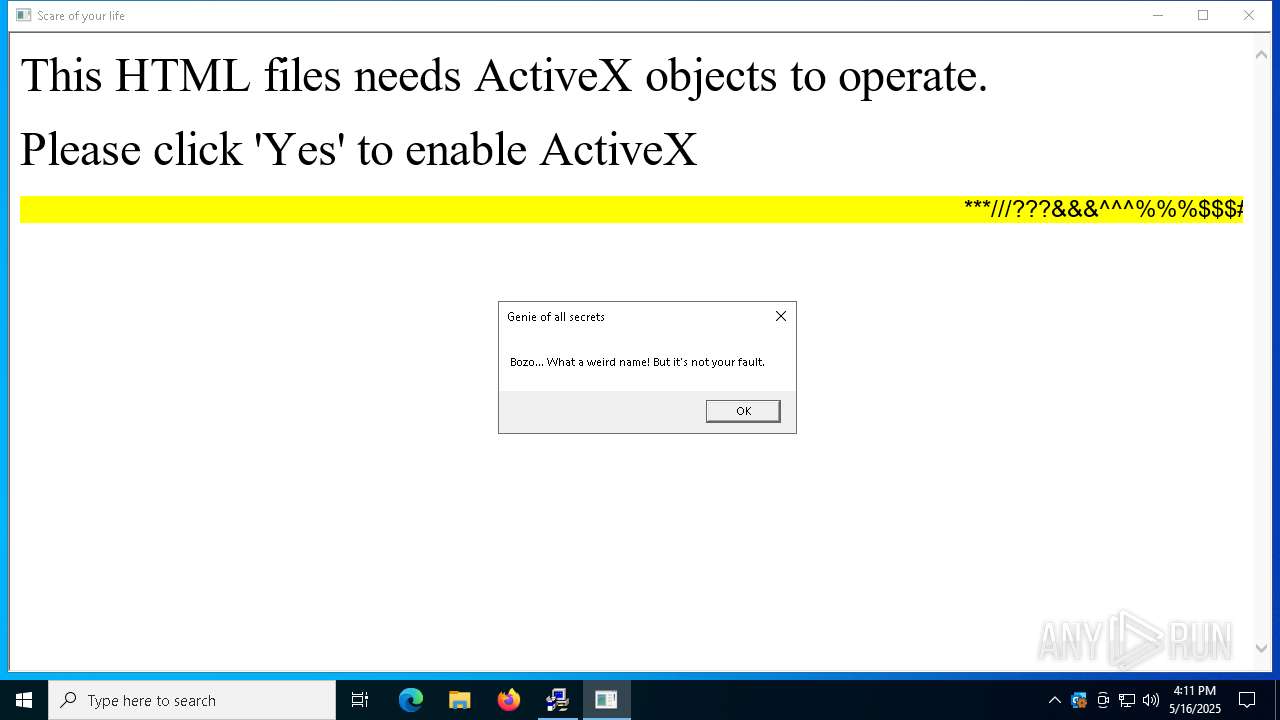
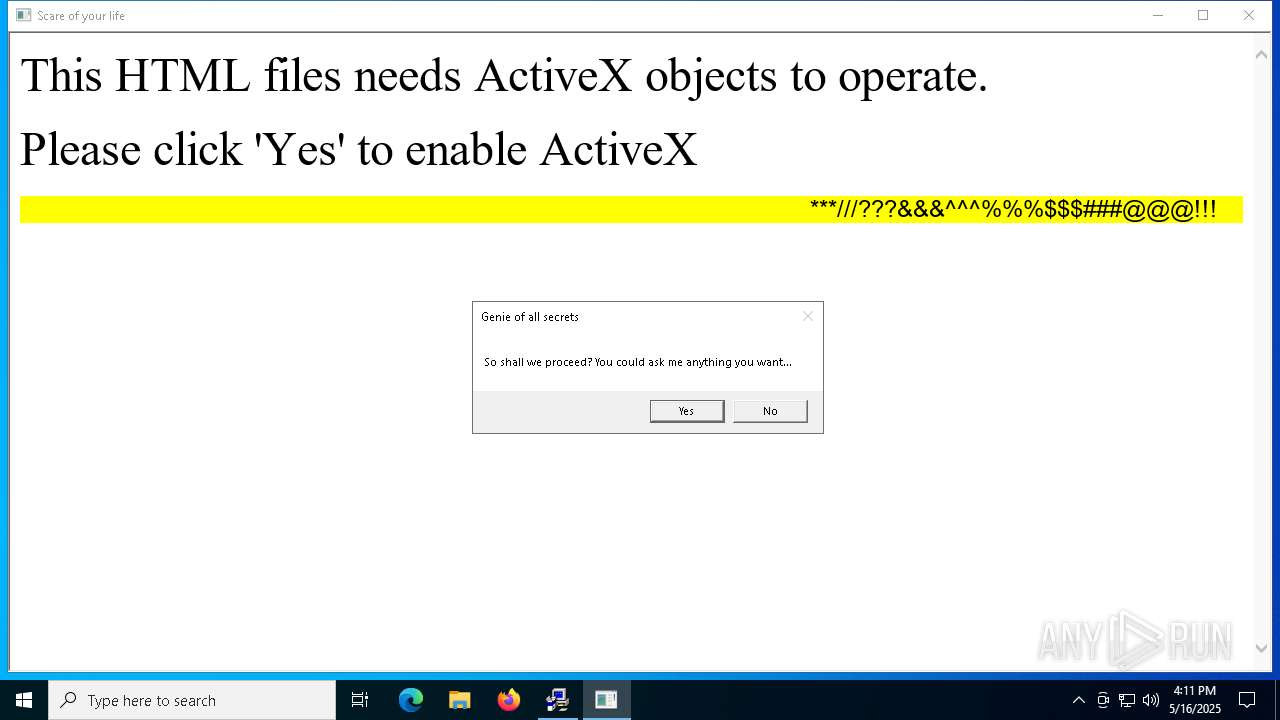
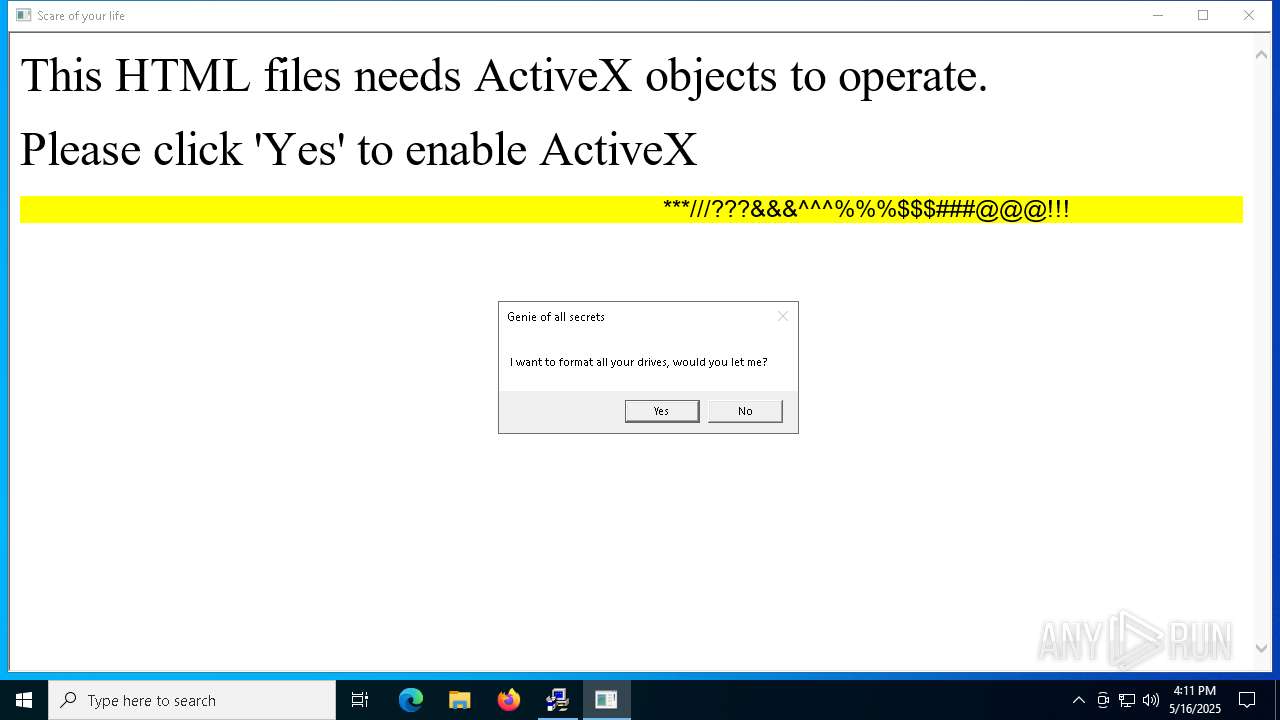
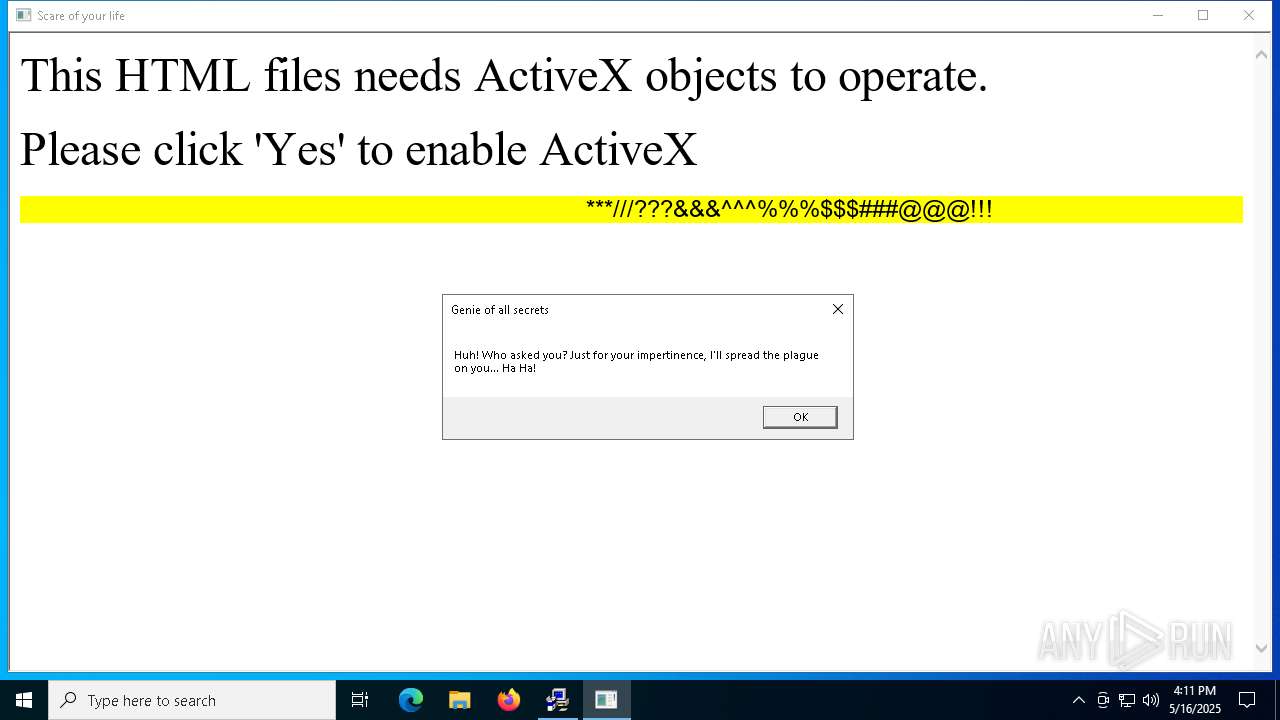
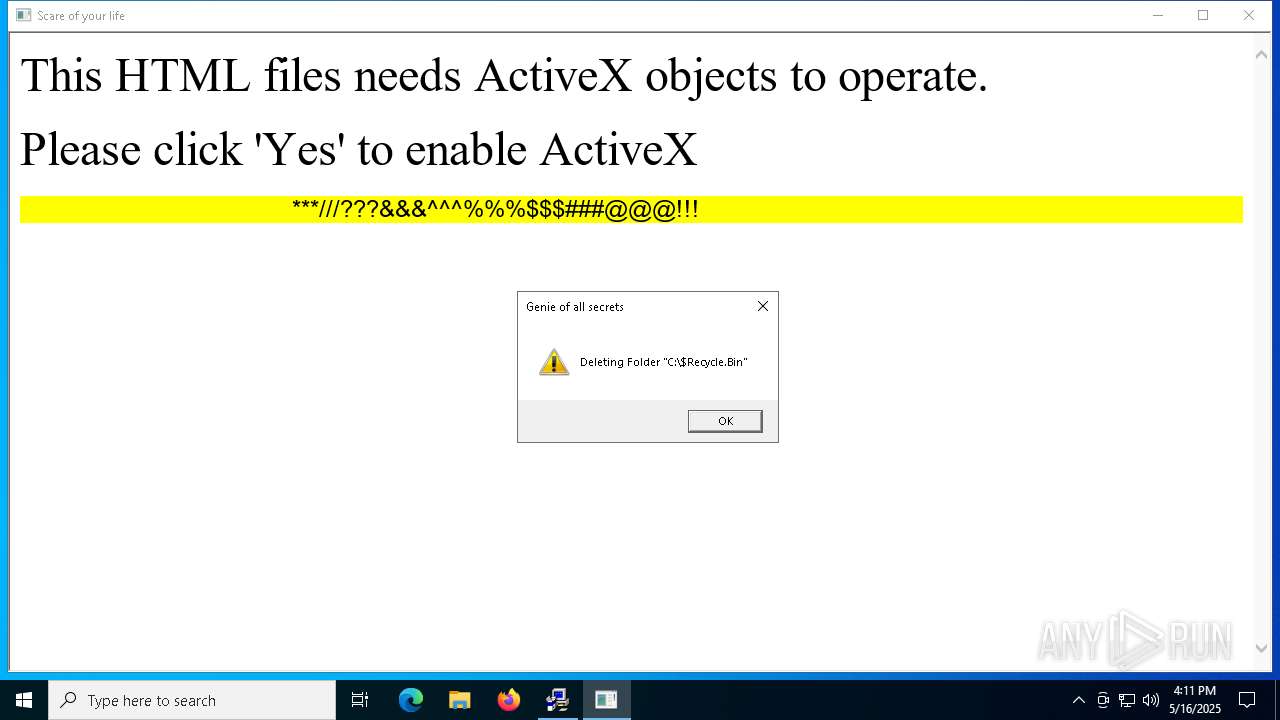
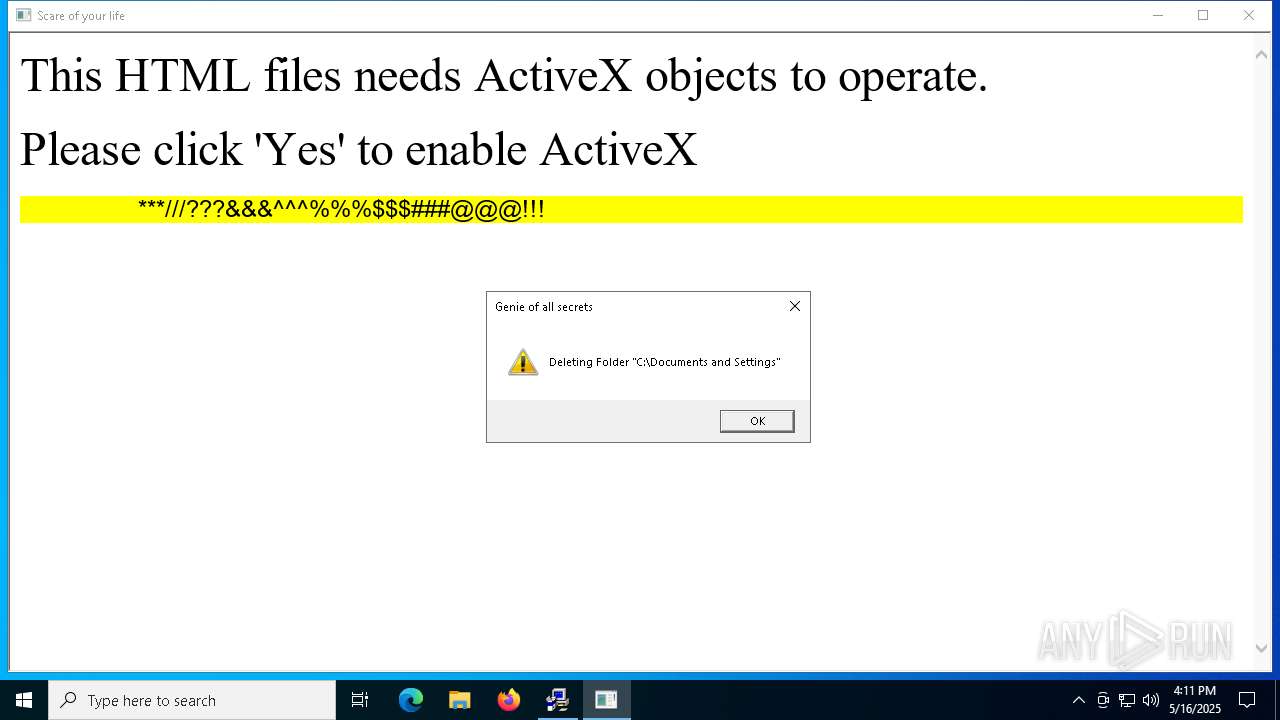
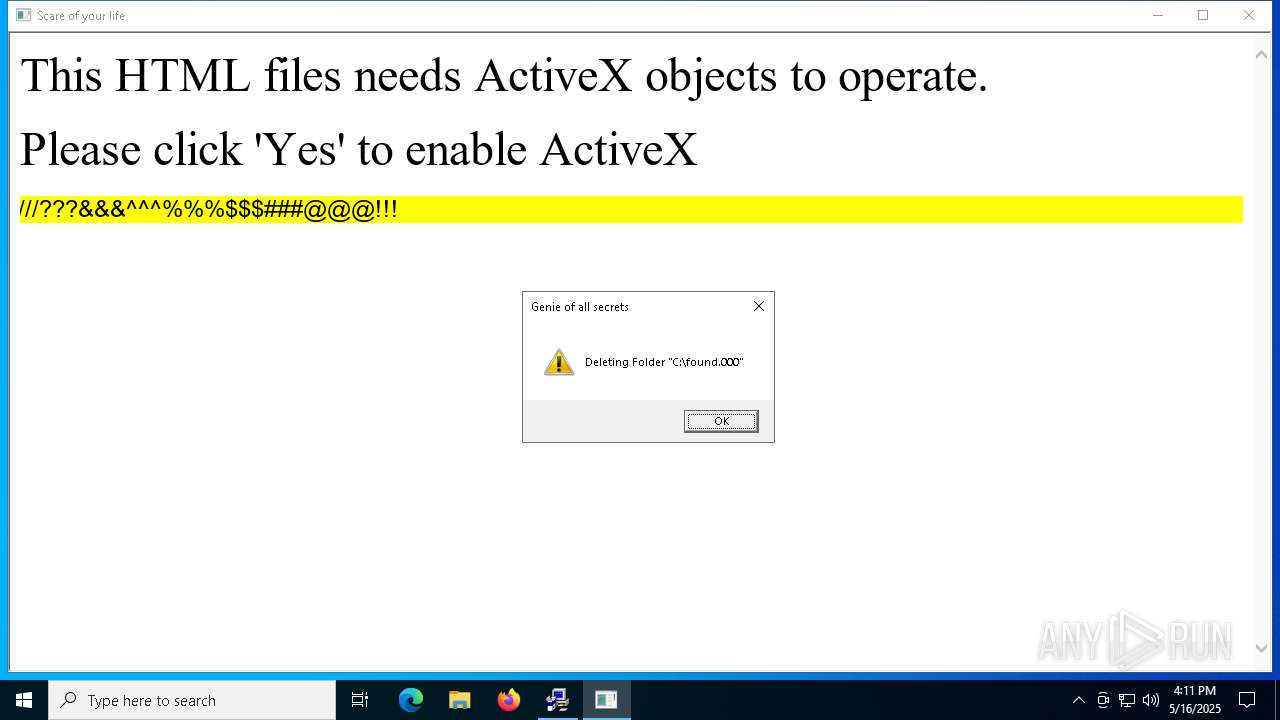
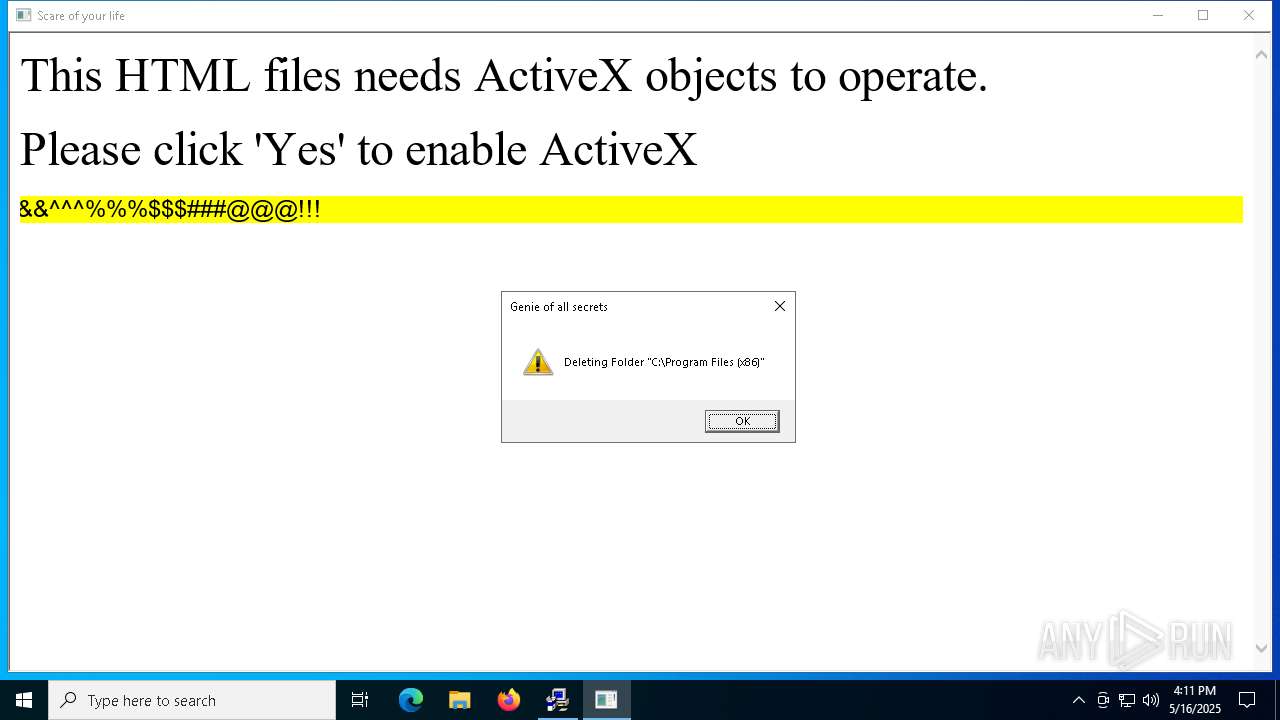
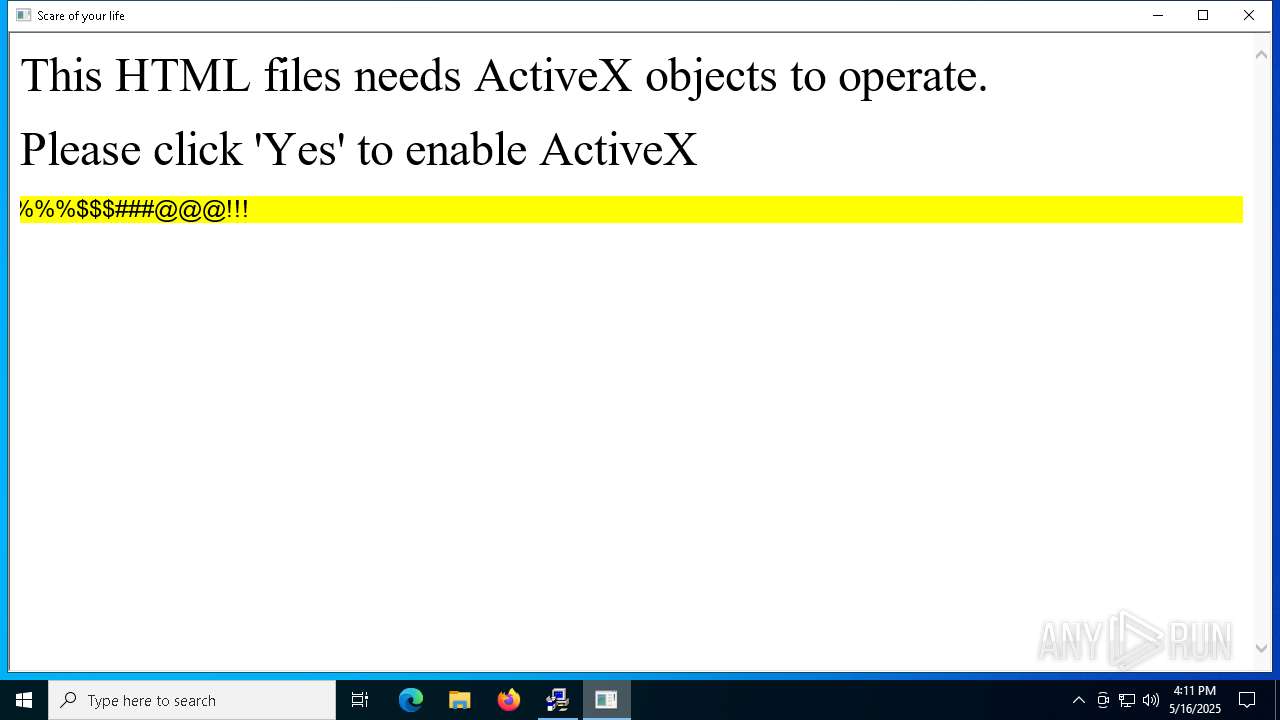
| 4736 | "C:\Windows\SysWOW64\mshta.exe" "C:\Users\admin\Desktop\Scare.hta" {1E460BD7-F1C3-4B2E-88BF-4E770A288AF5}{1E460BD7-F1C3-4B2E-88BF-4E770A288AF5} | C:\Windows\SysWOW64\mshta.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft (R) HTML Application host Version: 11.00.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4980 | "C:\WINDOWS\System32\SLUI.exe" RuleId=3482d82e-ca2c-4e1f-8864-da0267b484b2;Action=AutoActivate;AppId=55c92734-d682-4d71-983e-d6ec3f16059f;SkuId=4de7cb65-cdf1-4de9-8ae8-e3cce27b9f2c;NotificationInterval=1440;Trigger=TimerEvent | C:\Windows\System32\slui.exe | SppExtComObj.Exe | ||||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows Activation Client Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5376 | C:\WINDOWS\System32\slui.exe -Embedding | C:\Windows\System32\slui.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Activation Client Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5588 | "C:\Users\admin\Desktop\Quamo.exe" | C:\Users\admin\Desktop\Quamo.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Version: 1.00 Modules
| |||||||||||||||
| 6516 | "C:\Program Files\WinRAR\WinRAR.exe" C:\Users\admin\AppData\Local\Temp\Desktop.rar | C:\Program Files\WinRAR\WinRAR.exe | explorer.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.91.0 Modules
| |||||||||||||||
| 7020 | "C:\Users\admin\Desktop\Quamo.exe" | C:\Users\admin\Desktop\Quamo.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Version: 1.00 Modules
| |||||||||||||||
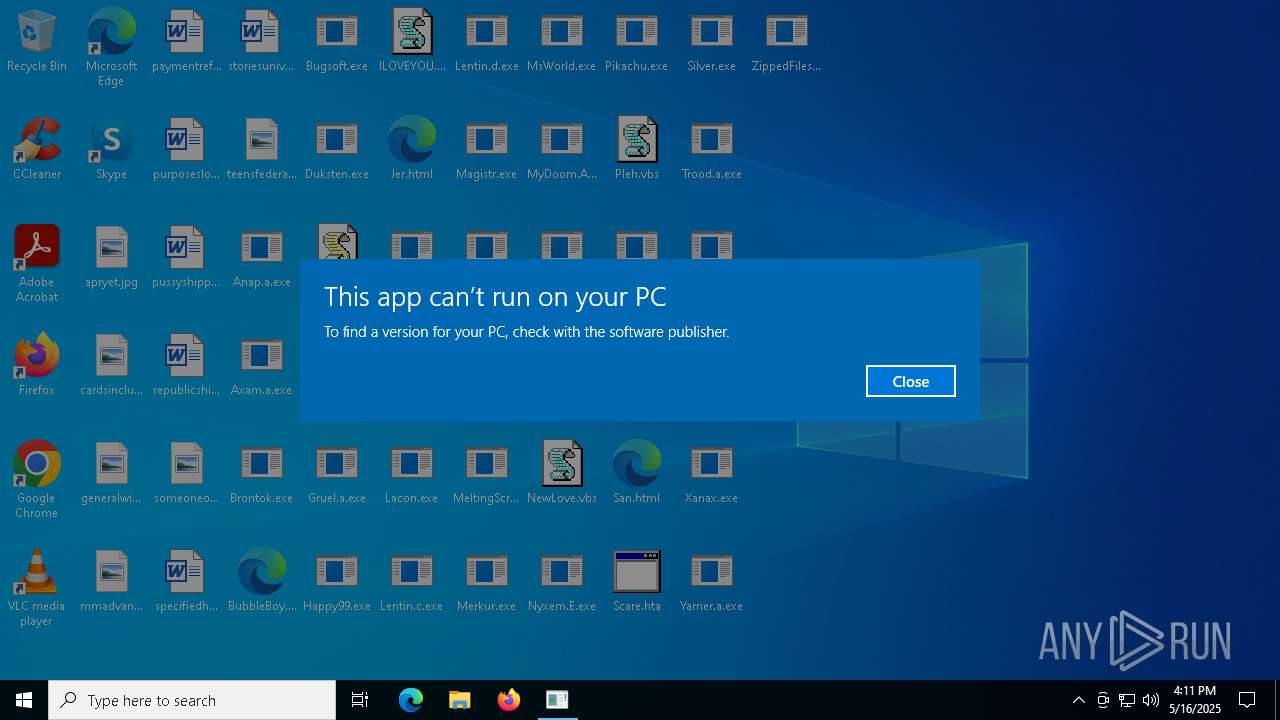
Total events
17 623
Read events
17 442
Write events
154
Delete events
27
Modification events
| (PID) Process: | (6516) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (6516) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (6516) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 3 |
Value: C:\Users\admin\Desktop\preferences.zip | |||
| (PID) Process: | (6516) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\chromium_ext.zip | |||
| (PID) Process: | (6516) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\omni_23_10_2024_.zip | |||
| (PID) Process: | (6516) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\Desktop.rar | |||
| (PID) Process: | (6516) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (6516) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (6516) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (6516) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
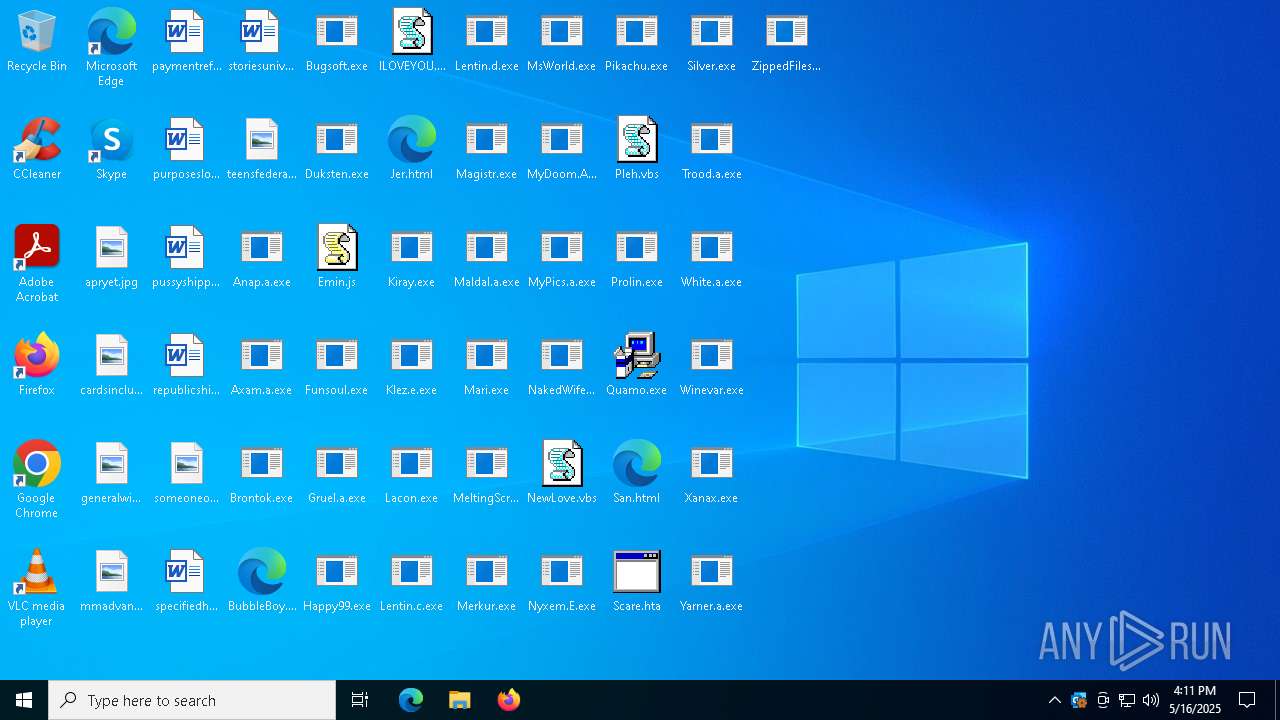
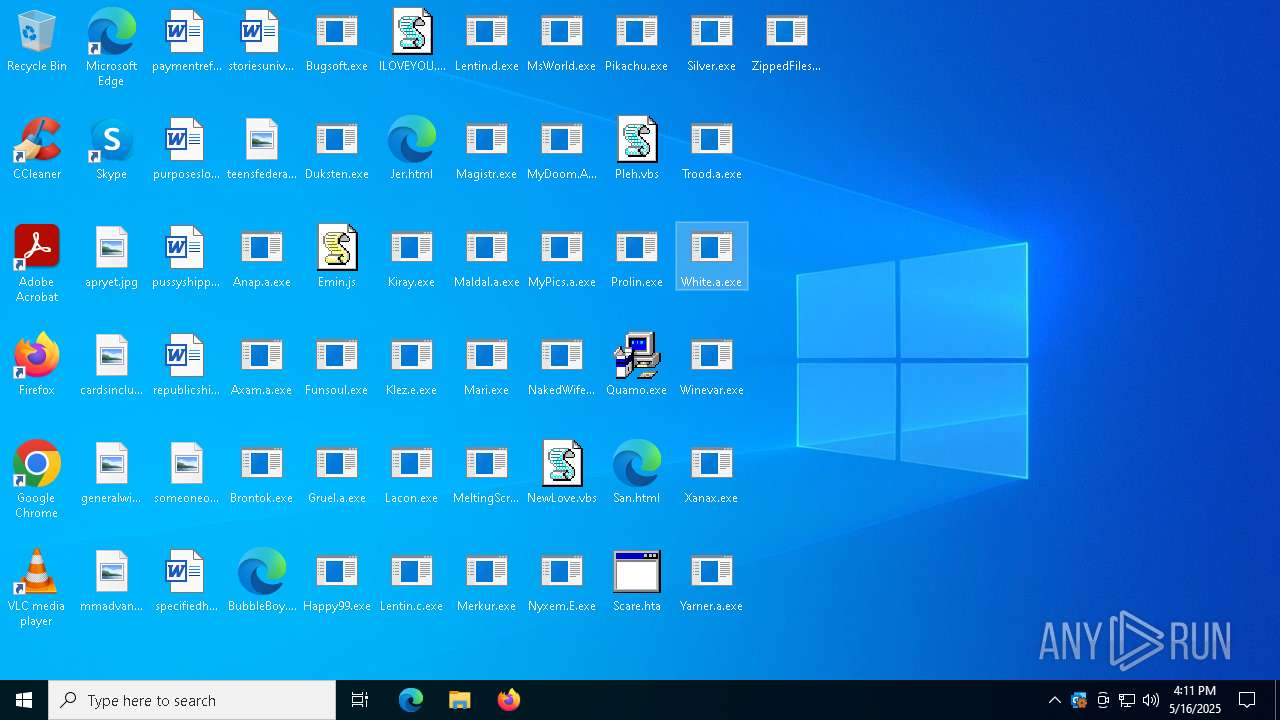
Executable files
33
Suspicious files
9
Text files
9
Unknown types
0
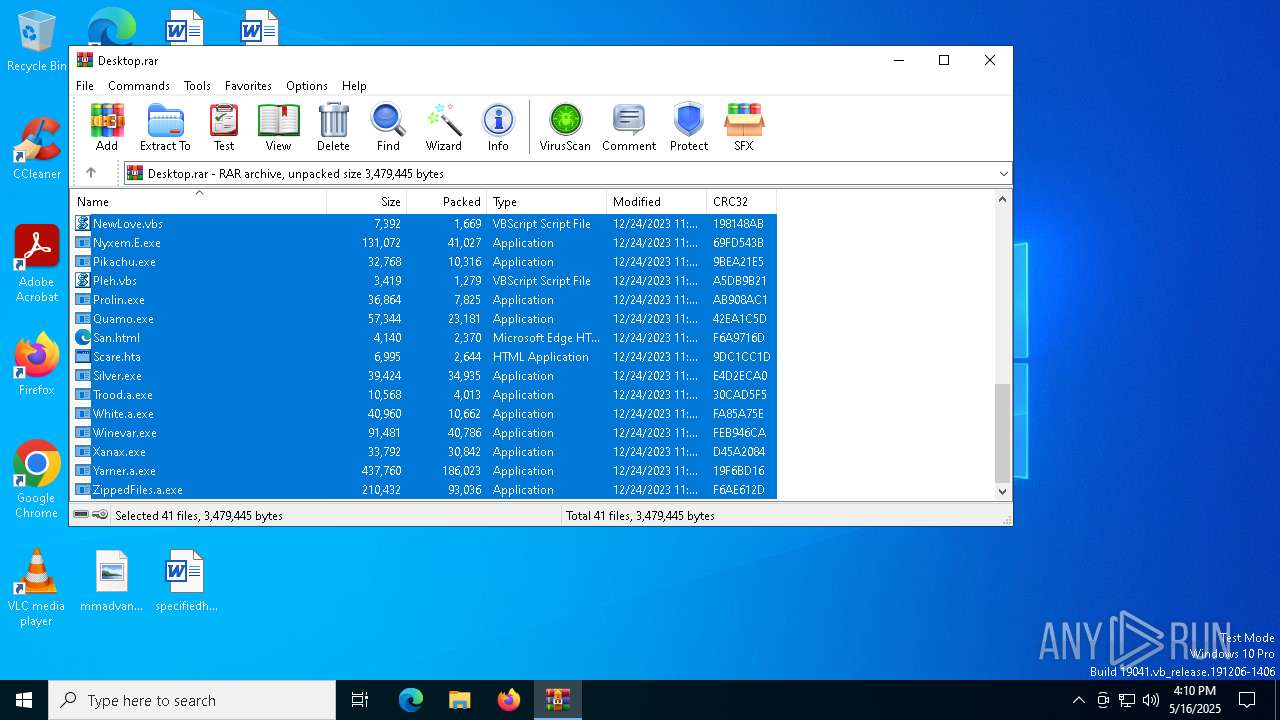
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6516 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa6516.15863\Pikachu.exe | executable | |
MD5:715614E09261B39DFA439FA1326C0CEC | SHA256:E1DFC005D5403FB2F356276F0ABE19DF68249CE10E5035450926D56C2F8D3652 | |||
| 6516 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa6516.15863\Lentin.d.exe | executable | |
MD5:D9CE0273F791DA275ED2A69446413A87 | SHA256:AA2E8D70654E30CF11E2B57E92CEA72A9823A048F75FC9029DA04E1E4D8A9810 | |||
| 6516 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa6516.15863\Nyxem.E.exe | executable | |
MD5:A0BDCE2F937FFBB7BA548845B24749C0 | SHA256:62F8364C46300BCE2E75C4CC65039DE3F060B854764DD90F0FA656EFAF31BEA9 | |||
| 6516 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa6516.15863\Scare.hta | html | |
MD5:B4978D1E7542EAFDC7B3908A5F45B8A6 | SHA256:1A8083787B336B322510F93D930F52AEDEB90D2052501E864BFA5B1906E74D58 | |||
| 6516 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa6516.15863\Lentin.c.exe | executable | |
MD5:04EE0EFF07A7E545F7052031CA0D8133 | SHA256:50D60CD841A18B05E00AB4691FC1E30F6A099A65A58BA51080304205FBB0D666 | |||
| 6516 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa6516.15863\Xanax.exe | executable | |
MD5:DF24E1CCCEB3C75DADA950A1C1ABCA4D | SHA256:910C03D210381F0443BFCEFE682717F28378DCFE5415071DD127A9837A97B0A6 | |||
| 6516 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa6516.15863\Trood.a.exe | executable | |
MD5:47D1F48A127736E63AAD709DDC9D81D0 | SHA256:24DD269B4D5EDEB591AD992DB33553D90F1848F58C06C9DD9FB3CDB4EAF812F5 | |||
| 6516 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa6516.15863\Winevar.exe | executable | |
MD5:E79D0B1A342712EA9B96104086149D65 | SHA256:E68EBECD17BB8E91079BD4FE9BD24059A2BC007B4BAAC477127EDA7C5D5C6706 | |||
| 6516 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa6516.15863\San.html | binary | |
MD5:2E69F2FA1DFCF256549CCA809CC4C9D6 | SHA256:49151419F15B1BF00DC4D5B1D988D9C2669D1E4E46C62CF2B0DB3C89CD0293E7 | |||
| 6516 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa6516.15863\Yarner.a.exe | executable | |
MD5:64218AC85566808EE404A3E2ACED679C | SHA256:C8B59505E578D555976B6176732C1F19FD76860CF465CF1427E1DFA50622E067 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
22
DNS requests
7
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 40.127.240.158:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | IE | unknown |
2104 | svchost.exe | 40.127.240.158:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | IE | unknown |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
2112 | svchost.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
2104 | svchost.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
1660 | OUTLOOK.EXE | 52.123.129.14:443 | ecs.office.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
1660 | OUTLOOK.EXE | 23.50.131.86:443 | omex.cdn.office.net | Akamai International B.V. | DE | whitelisted |
1660 | OUTLOOK.EXE | 20.42.65.84:443 | self.events.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
4980 | slui.exe | 40.91.76.224:443 | activation-v2.sls.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
google.com |
| whitelisted |
settings-win.data.microsoft.com |
| whitelisted |
ecs.office.com |
| whitelisted |
omex.cdn.office.net |
| whitelisted |
self.events.data.microsoft.com |
| whitelisted |
activation-v2.sls.microsoft.com |
| whitelisted |