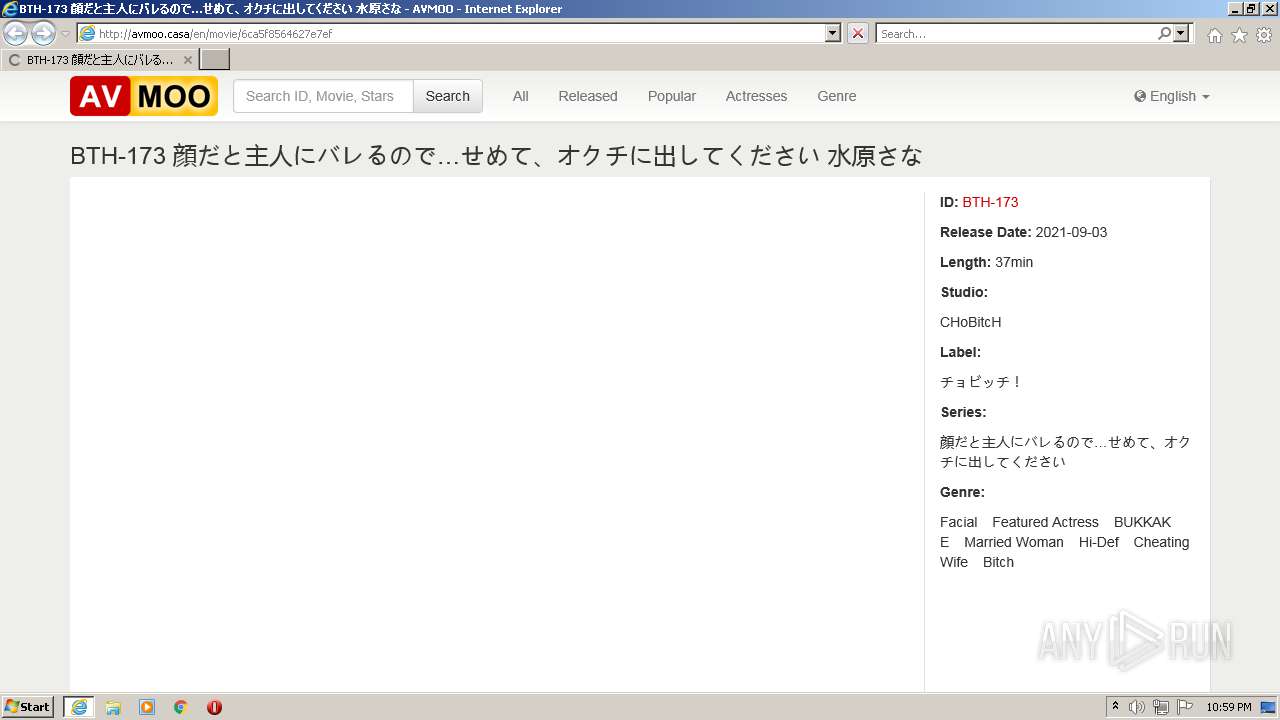
| URL: | http://avmoo.casa/en/movie/6ca5f8564627e7ef |
| Full analysis: | https://app.any.run/tasks/2426ee40-284e-4a3e-85e6-15ebd3a5dae2 |
| Verdict: | Malicious activity |
| Analysis date: | August 31, 2021, 21:59:17 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 421F5CF6C21659092E928769153B8E8A |
| SHA1: | 6B944C270C6EF37364B5BAB555828E5E5300F54C |
| SHA256: | 7CC663268BA200A82589E4BF2C22B4E5FDA00E101D31638E4D2BBD2C3CF3CFFA |
| SSDEEP: | 3:N1KfEtPS6RC2:C0q6Rb |
MALICIOUS
No malicious indicators.SUSPICIOUS
Reads Microsoft Outlook installation path
- iexplore.exe (PID: 2204)
INFO
Checks supported languages
- iexplore.exe (PID: 888)
- iexplore.exe (PID: 2204)
Reads the computer name
- iexplore.exe (PID: 888)
- iexplore.exe (PID: 2204)
Changes internet zones settings
- iexplore.exe (PID: 888)
Application launched itself
- iexplore.exe (PID: 888)
Checks Windows Trust Settings
- iexplore.exe (PID: 2204)
- iexplore.exe (PID: 888)
Reads internet explorer settings
- iexplore.exe (PID: 2204)
Reads settings of System Certificates
- iexplore.exe (PID: 888)
- iexplore.exe (PID: 2204)
Creates files in the user directory
- iexplore.exe (PID: 2204)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
38
Monitored processes
2
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 888 | "C:\Program Files\Internet Explorer\iexplore.exe" "http://avmoo.casa/en/movie/6ca5f8564627e7ef" | C:\Program Files\Internet Explorer\iexplore.exe | Explorer.EXE | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 2204 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:888 CREDAT:267521 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
Total events
10 440
Read events
10 325
Write events
115
Delete events
0
Modification events
| (PID) Process: | (888) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPDaysSinceLastAutoMigration |
Value: 1 | |||
| (PID) Process: | (888) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchLowDateTime |
Value: | |||
| (PID) Process: | (888) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchHighDateTime |
Value: 30908083 | |||
| (PID) Process: | (888) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateLowDateTime |
Value: | |||
| (PID) Process: | (888) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateHighDateTime |
Value: 30908083 | |||
| (PID) Process: | (888) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (888) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (888) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (888) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (888) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
Executable files
0
Suspicious files
16
Text files
46
Unknown types
14
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2204 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\Low\DHXZAM99.txt | text | |
MD5:— | SHA256:— | |||
| 2204 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\DY534W2X\app.min[1].css | text | |
MD5:— | SHA256:— | |||
| 2204 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\5IWPIAR9\download[1].png | image | |
MD5:— | SHA256:— | |||
| 2204 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\YTOWV792\app.min[1].js | text | |
MD5:— | SHA256:— | |||
| 2204 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\Low\SCOIA77S.txt | text | |
MD5:— | SHA256:— | |||
| 2204 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\Low\EQBL9JJL.txt | text | |
MD5:— | SHA256:— | |||
| 2204 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\Low\70VZCMDM.txt | text | |
MD5:— | SHA256:— | |||
| 2204 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\57C8EDB95DF3F0AD4EE2DC2B8CFD4157 | binary | |
MD5:— | SHA256:— | |||
| 2204 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\MFAQUS6V\6ca5f8564627e7ef[1].htm | html | |
MD5:— | SHA256:— | |||
| 2204 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\Low\BKI43VTP.txt | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
26
TCP/UDP connections
82
DNS requests
26
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2204 | iexplore.exe | GET | 200 | 185.112.156.147:80 | http://avmoo.casa/en/movie/6ca5f8564627e7ef | HU | html | 7.92 Kb | suspicious |
2204 | iexplore.exe | GET | 200 | 185.112.156.147:80 | http://avmoo.casa/app/jav/View/img/download.png | HU | image | 2.78 Kb | suspicious |
2204 | iexplore.exe | GET | 200 | 151.139.128.14:80 | http://ocsp.usertrust.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTNMNJMNDqCqx8FcBWK16EHdimS6QQUU3m%2FWqorSs9UgOHYm8Cd8rIDZssCEH1bUSa0droR23QWC7xTDac%3D | US | der | 727 b | whitelisted |
2204 | iexplore.exe | GET | 200 | 185.112.156.147:80 | http://avmoo.casa/app/jav/View/css/app.min.css?v=1476953808 | HU | text | 40.0 Kb | suspicious |
2204 | iexplore.exe | GET | 200 | 142.250.181.227:80 | http://ocsp.pki.goog/gts1c3/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTHLnmK3f9hNLO67UdCuLvGwCQHYwQUinR%2Fr4XN7pXNPZzQ4kYU83E1HScCEAJakFrb94kMCgAAAAD6Yis%3D | US | der | 471 b | whitelisted |
2204 | iexplore.exe | GET | 200 | 185.112.156.147:80 | http://avmoo.casa/app/jav/View/js/app.min.js?v=1476953808 | HU | text | 119 Kb | suspicious |
2204 | iexplore.exe | GET | 200 | 142.250.181.227:80 | http://ocsp.pki.goog/gtsr1/ME4wTDBKMEgwRjAJBgUrDgMCGgUABBQwkcLWD4LqGJ7bE7B1XZsEbmfwUAQU5K8rJnEaK0gnhS9SZizv8IkTcT4CDQIDvFNZazTHGPUBUGY%3D | US | der | 724 b | whitelisted |
2204 | iexplore.exe | GET | 200 | 151.139.128.14:80 | http://ocsp.comodoca.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBRTtU9uFqgVGHhJwXZyWCNXmVR5ngQUoBEKIz6W8Qfs4q8p74Klf9AwpLQCEDlyRDr5IrdR19NsEN0xNZU%3D | US | der | 471 b | whitelisted |
2204 | iexplore.exe | GET | 200 | 192.124.249.36:80 | http://ocsp.godaddy.com//MEIwQDA%2BMDwwOjAJBgUrDgMCGgUABBQdI2%2BOBkuXH93foRUj4a7lAr4rGwQUOpqFBxBnKLbv9r0FQW4gwZTaD94CAQc%3D | US | der | 1.69 Kb | whitelisted |
2204 | iexplore.exe | GET | 200 | 185.94.237.102:80 | http://poweredby.jads.co/adshow.php?adzone=371708 | NL | html | 1.51 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2204 | iexplore.exe | 185.112.156.147:80 | avmoo.casa | DoclerWeb Kft. | HU | suspicious |
2204 | iexplore.exe | 104.26.8.86:443 | jp.netcdn.space | Cloudflare Inc | US | unknown |
— | — | 205.185.216.10:443 | ads.exoclick.com | Highwinds Network Group, Inc. | US | whitelisted |
— | — | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
2204 | iexplore.exe | 205.185.216.10:443 | ads.exoclick.com | Highwinds Network Group, Inc. | US | whitelisted |
2204 | iexplore.exe | 192.124.249.36:80 | ocsp.godaddy.com | Sucuri | US | suspicious |
888 | iexplore.exe | 204.79.197.200:443 | www.bing.com | Microsoft Corporation | US | whitelisted |
2204 | iexplore.exe | 74.125.206.155:443 | stats.g.doubleclick.net | Google Inc. | US | whitelisted |
— | — | 192.124.249.36:80 | ocsp.godaddy.com | Sucuri | US | suspicious |
2204 | iexplore.exe | 142.250.181.227:80 | ocsp.pki.goog | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
avmoo.casa |
| suspicious |
jp.netcdn.space |
| suspicious |
us.netcdn.space |
| suspicious |
ads.exoclick.com |
| suspicious |
syndication.exoclick.com |
| suspicious |
adserver.juicyads.com |
| suspicious |
j.traffichunt.com |
| unknown |
www.google-analytics.com |
| whitelisted |
ctldl.windowsupdate.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |