| download: | index.html |
| Full analysis: | https://app.any.run/tasks/d0d1b629-a8ad-4d30-82f5-7f045f9fc9b0 |
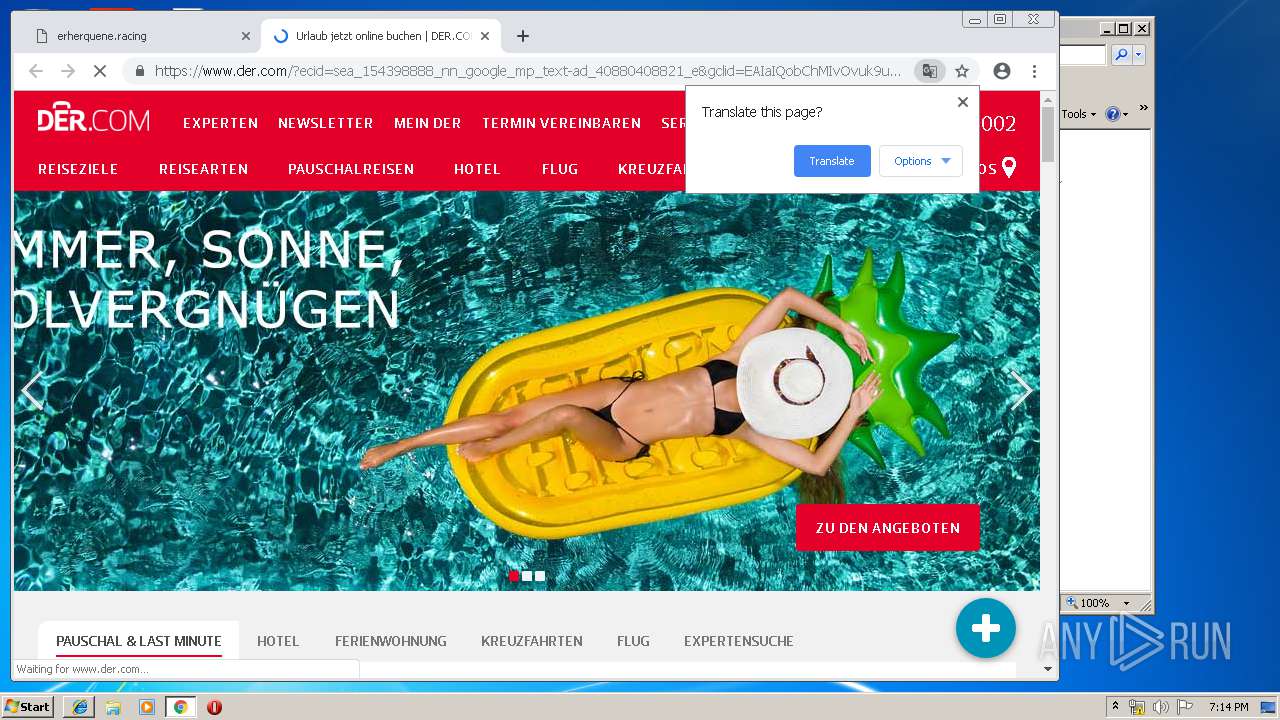
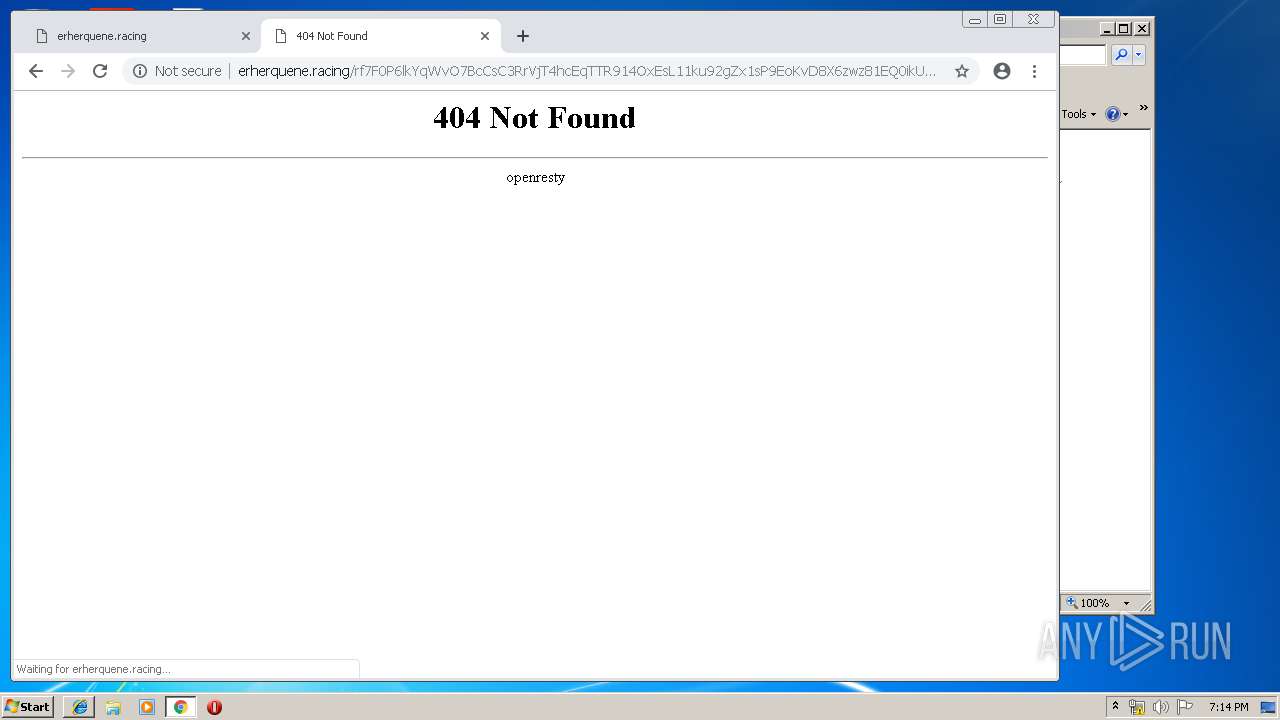
| Verdict: | Malicious activity |
| Analysis date: | May 20, 2019, 18:12:52 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | text/html |
| File info: | HTML document, UTF-8 Unicode text, with CRLF line terminators |
| MD5: | FBDF1A4B4D247CF41F5A11FF95CD77BC |
| SHA1: | 2F1548D692D6C561F14D9B2C2CE78D9A06807942 |
| SHA256: | 7CADF9E07E9126DA651E4EAF23FC984BB54454B69BEEBDBFDB3B74504D5DF698 |
| SSDEEP: | 48:ts9gcE9evZNHnUQyklV6uNuqUSGdZogcZz/tA/VHQn50t4GKX0Q5uOSo1cZmvi/D:u2m/nUnsZcjvqA/lrHBcTi/mD+ifw |
MALICIOUS
No malicious indicators.SUSPICIOUS
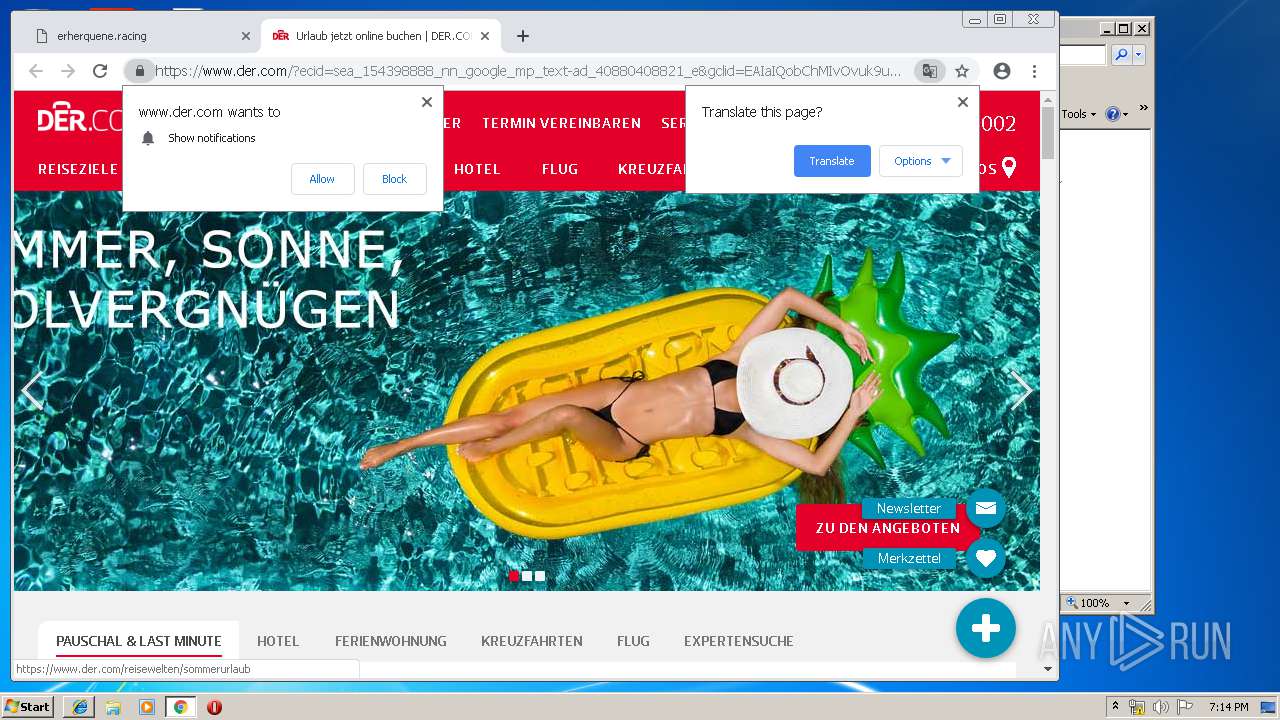
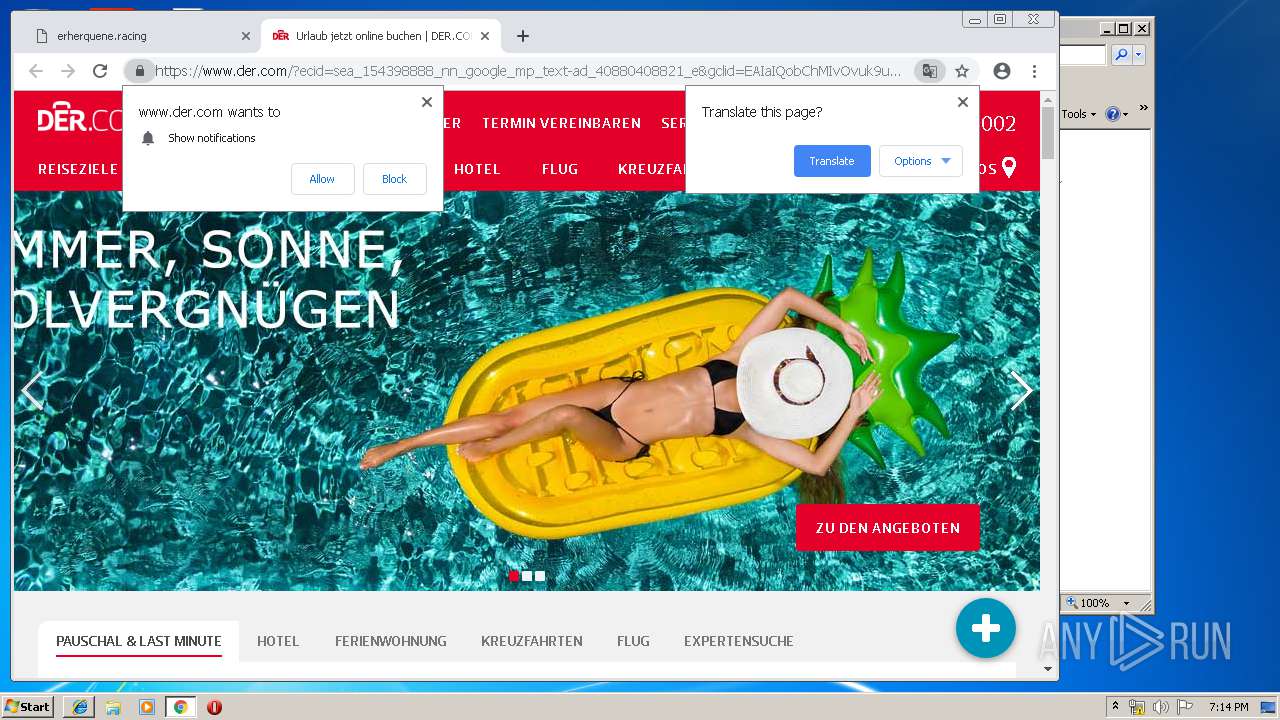
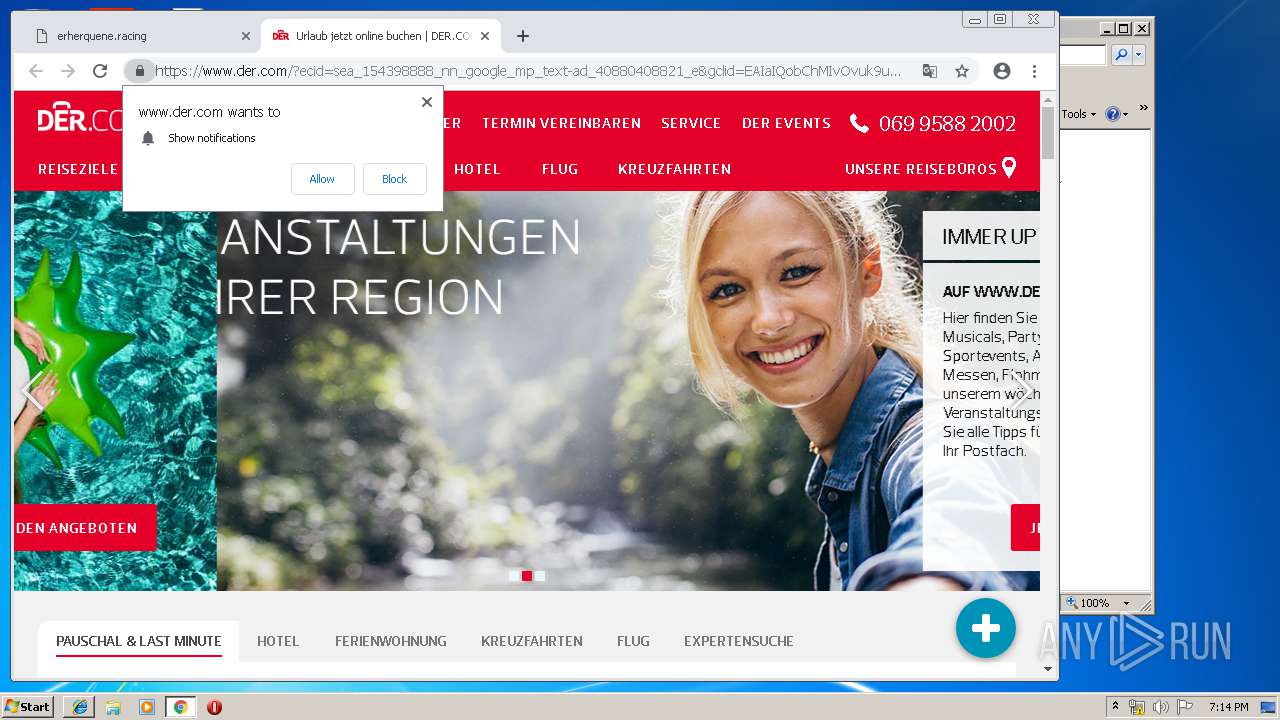
Modifies files in Chrome extension folder
- chrome.exe (PID: 3348)
INFO
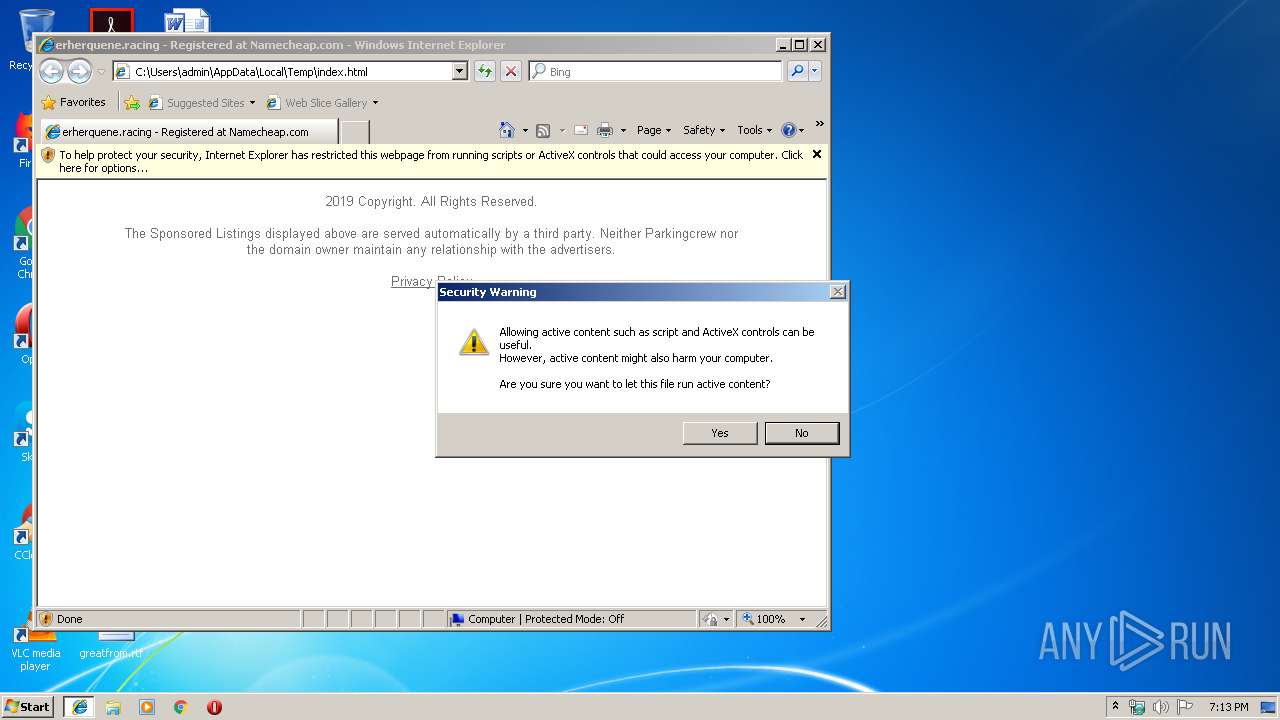
Changes internet zones settings
- iexplore.exe (PID: 456)
Reads internet explorer settings
- iexplore.exe (PID: 3464)
Manual execution by user
- chrome.exe (PID: 3348)
Application launched itself
- chrome.exe (PID: 3348)
Reads Internet Cache Settings
- iexplore.exe (PID: 3464)
- iexplore.exe (PID: 456)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .html | | | HyperText Markup Language (100) |
|---|
EXIF
HTML
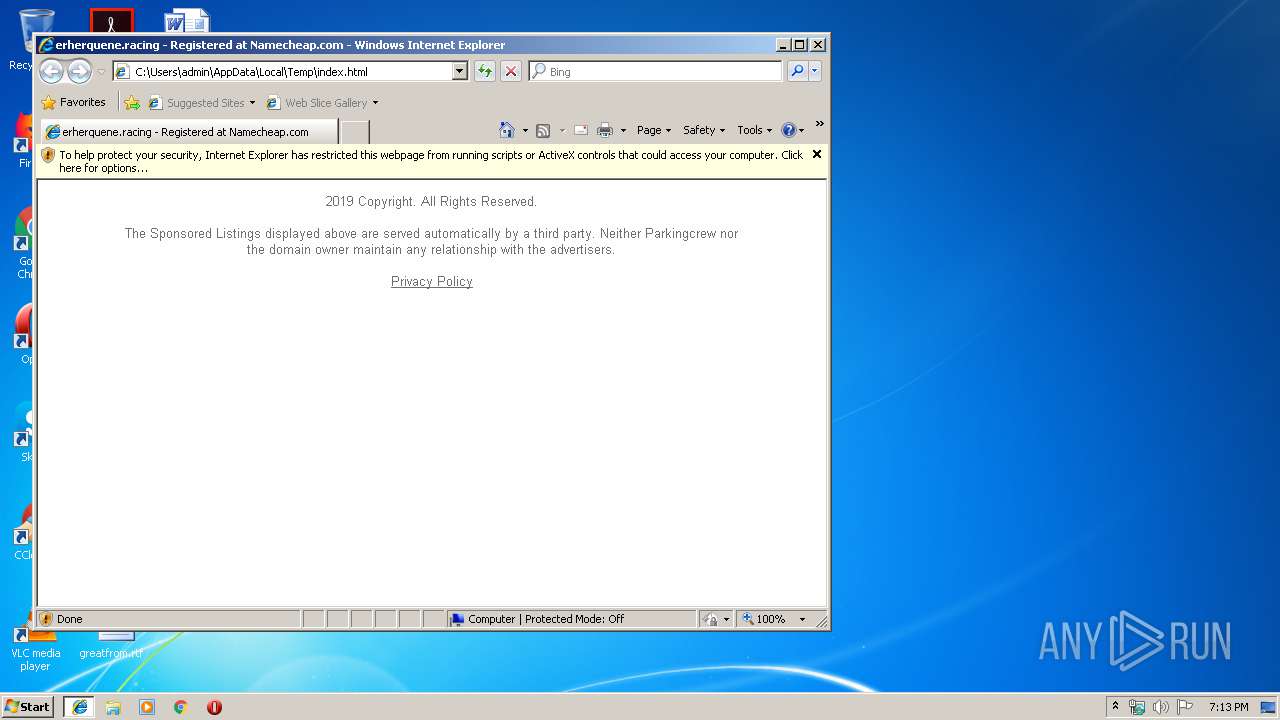
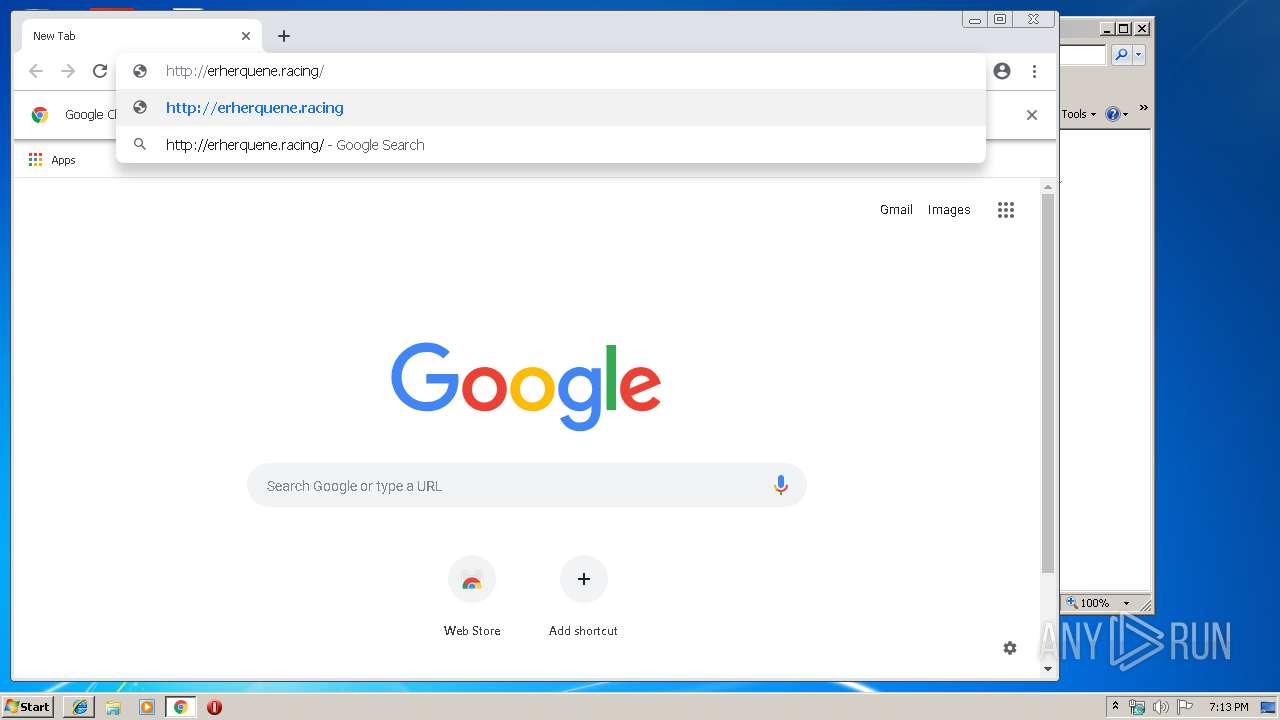
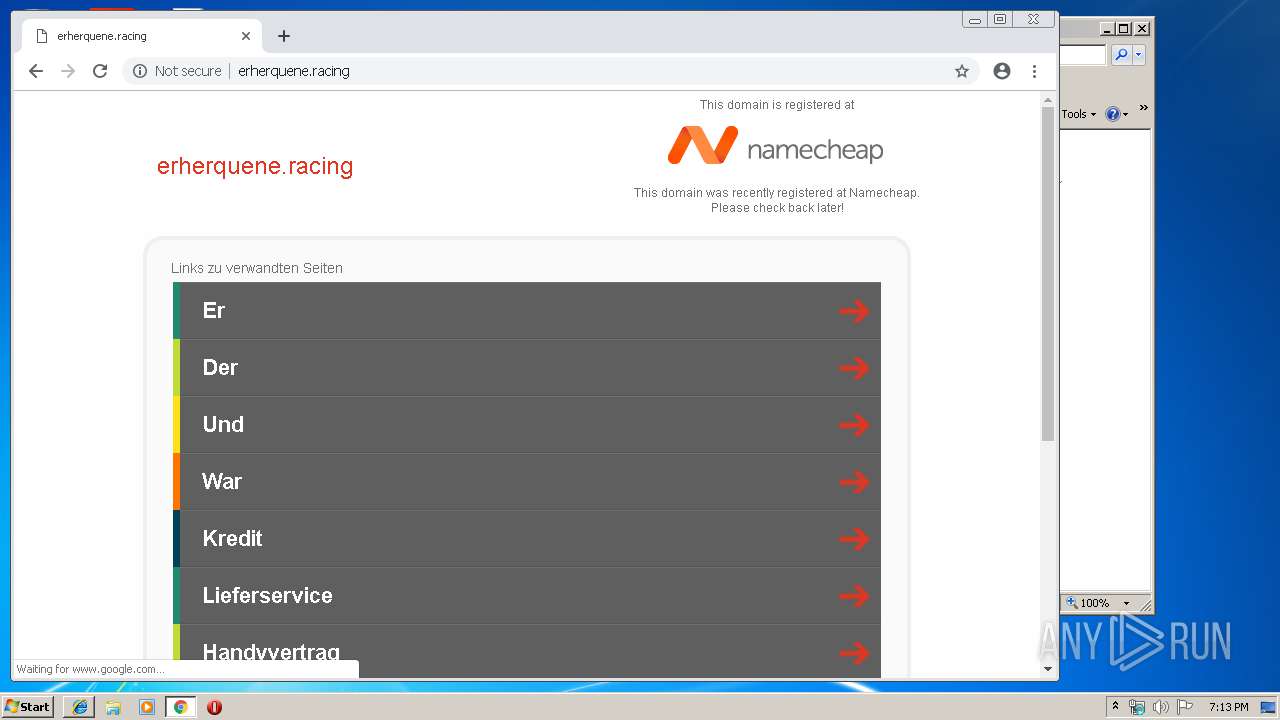
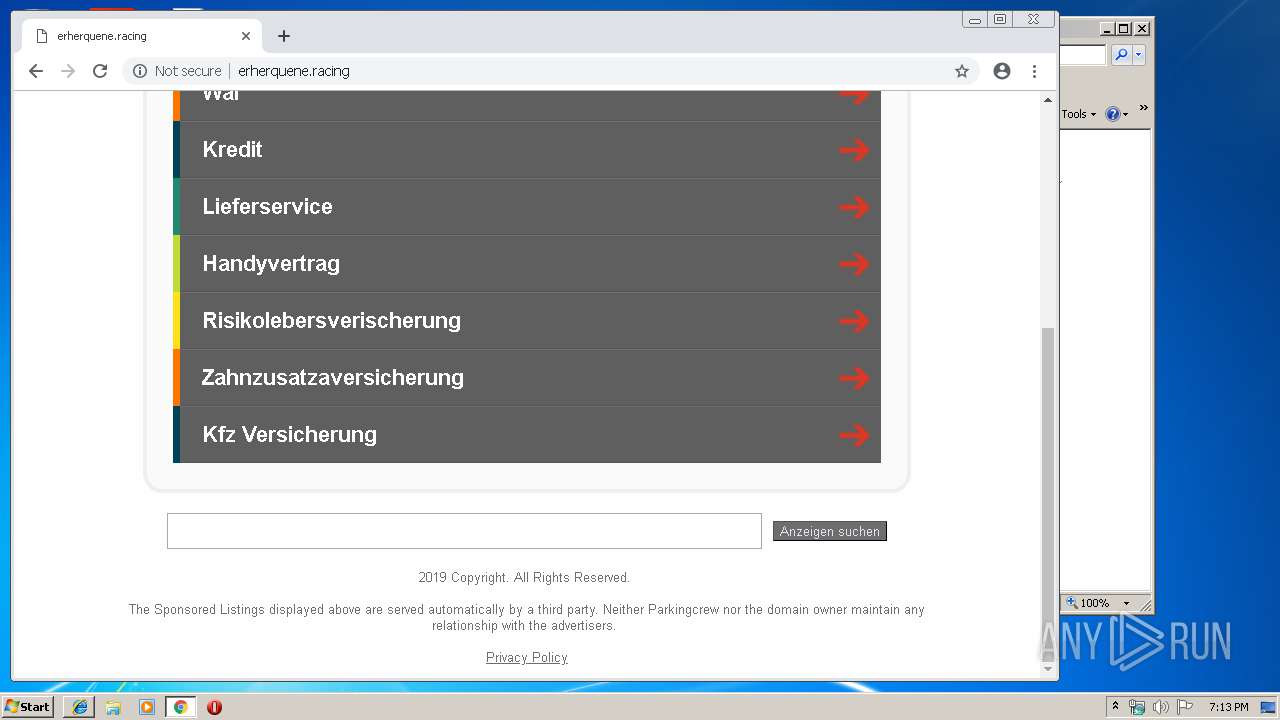
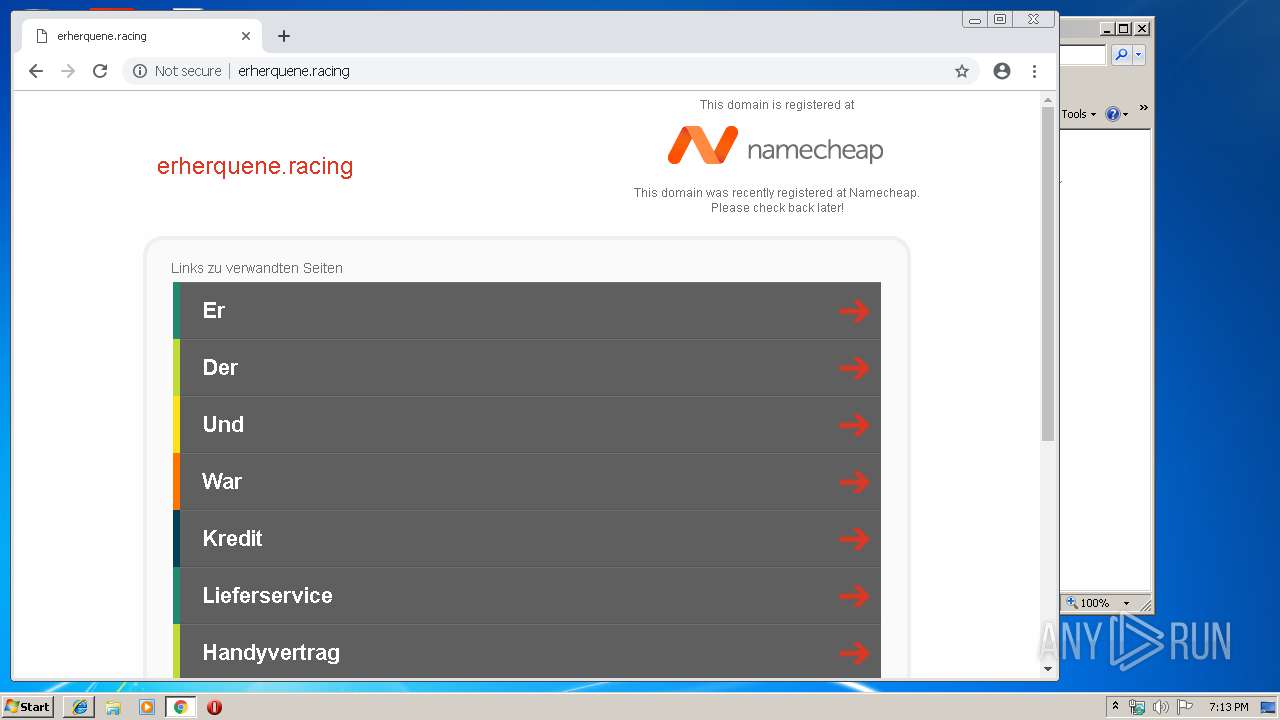
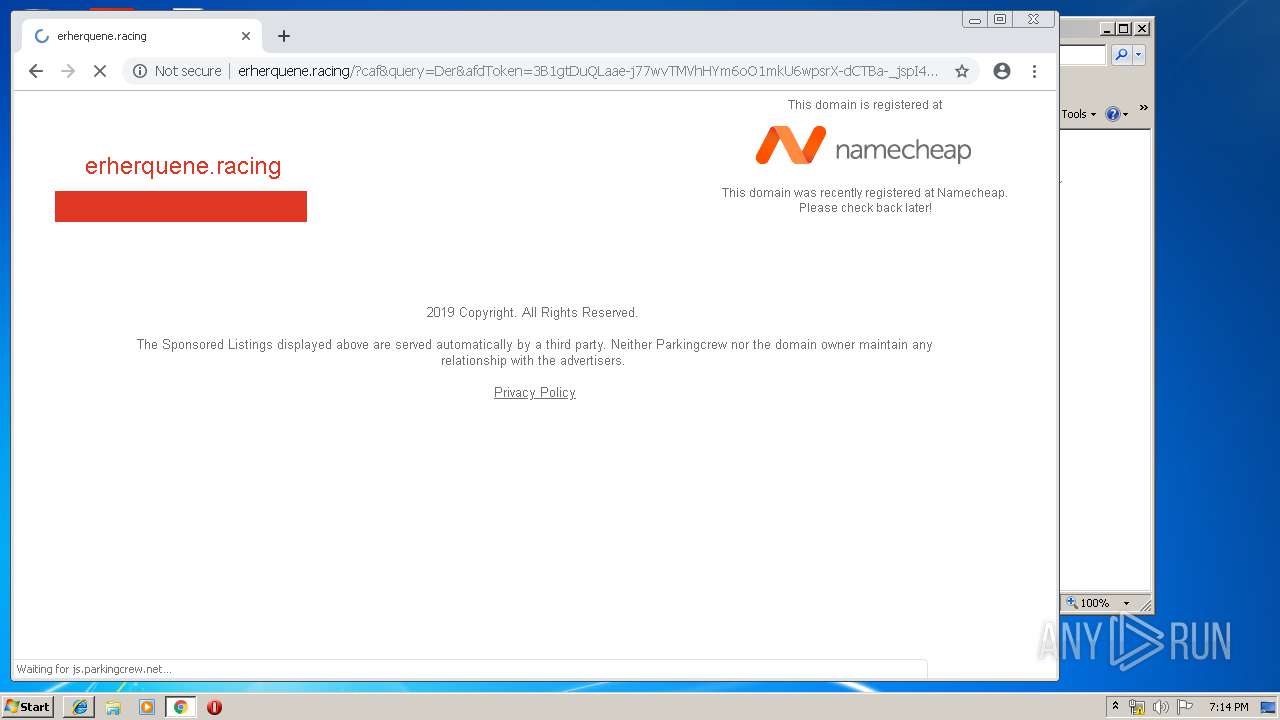
| Title: | erherquene.racing - Registered at Namecheap.com |
|---|---|
| ContentType: | text/html;charset=UTF-8 |
| viewport: | width=device-width, user-scalable=no |
| Generator: | Sitefinity 3.7.2136.240:1 |
Total processes
70
Monitored processes
36
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 272 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=960,16234065677751361604,6067134352988315796,131072 --enable-features=PasswordImport --disable-gpu-compositing --service-pipe-token=14233325971796641288 --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=14233325971796641288 --renderer-client-id=31 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=4264 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 352 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=960,16234065677751361604,6067134352988315796,131072 --enable-features=PasswordImport --gpu-preferences=KAAAAAAAAACAAwAAAQAAAAAAAAAAAGAAAAAAAAEAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --service-request-channel-token=10681582785449058161 --mojo-platform-channel-handle=944 --ignored=" --type=renderer " /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 456 | "C:\Program Files\Internet Explorer\iexplore.exe" C:\Users\admin\AppData\Local\Temp\index.html | C:\Program Files\Internet Explorer\iexplore.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 860 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=960,16234065677751361604,6067134352988315796,131072 --enable-features=PasswordImport --service-pipe-token=1269066306207431782 --lang=en-US --extension-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=1269066306207431782 --renderer-client-id=3 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2192 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 1092 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=960,16234065677751361604,6067134352988315796,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=11501368419625574285 --mojo-platform-channel-handle=4496 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 1240 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=960,16234065677751361604,6067134352988315796,131072 --enable-features=PasswordImport --disable-gpu-compositing --service-pipe-token=9973067272530911350 --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=9973067272530911350 --renderer-client-id=33 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=5160 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 1532 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=960,16234065677751361604,6067134352988315796,131072 --enable-features=PasswordImport --lang=en-US --no-sandbox --service-request-channel-token=9919484800805020730 --mojo-platform-channel-handle=4904 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 1568 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=960,16234065677751361604,6067134352988315796,131072 --enable-features=PasswordImport --disable-gpu-compositing --service-pipe-token=3120850685639540142 --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=3120850685639540142 --renderer-client-id=26 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3768 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 1576 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=960,16234065677751361604,6067134352988315796,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=6941477492114940063 --mojo-platform-channel-handle=4084 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 1700 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=960,16234065677751361604,6067134352988315796,131072 --enable-features=PasswordImport --disable-gpu-sandbox --use-gl=disabled --gpu-preferences=KAAAAAAAAACAAwAAAQAAAAAAAAAAAGAAAAAAAAEAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --service-request-channel-token=7294377148597193087 --mojo-platform-channel-handle=4616 /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
Total events
948
Read events
780
Write events
162
Delete events
6
Modification events
| (PID) Process: | (456) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (456) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (456) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (456) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Zones |
| Operation: | write | Name: | SecuritySafe |
Value: 1 | |||
| (PID) Process: | (456) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (456) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 4600000071000000010000000000000000000000000000000000000000000000C0E333BBEAB1D301000000000000000000000000020000001700000000000000FE800000000000007D6CB050D9C573F70B000000000000006D00330032005C004D00530049004D004700330032002E0064006C000100000004AA400014AA4000040000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000002000000C0A8016400000000000000000000000000000000000000000800000000000000805D3F00983740000008000002000000000000600000002060040000B8A94000020000008802000060040000B8A9400004000000F8010000B284000088B64000B84B400043003A000000000000000000000000000000000000000000 | |||
| (PID) Process: | (456) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Recovery\Active |
| Operation: | write | Name: | {EA7223E7-7B2A-11E9-B63D-5254004A04AF} |
Value: 0 | |||
| (PID) Process: | (456) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Ext\Stats\{2670000A-7350-4F3C-8081-5663EE0C6C49}\iexplore |
| Operation: | write | Name: | Type |
Value: 4 | |||
| (PID) Process: | (456) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Ext\Stats\{2670000A-7350-4F3C-8081-5663EE0C6C49}\iexplore |
| Operation: | write | Name: | Count |
Value: 1 | |||
| (PID) Process: | (456) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Ext\Stats\{2670000A-7350-4F3C-8081-5663EE0C6C49}\iexplore |
| Operation: | write | Name: | Time |
Value: E30705000100140012000D000700D303 | |||
Executable files
0
Suspicious files
184
Text files
265
Unknown types
13
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 456 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\JGRR2OYX\favicon[1].ico | — | |
MD5:— | SHA256:— | |||
| 456 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\Internet Explorer\Services\search_{0633EE93-D776-472f-A0FF-E1416B8B2E3A}.ico | — | |
MD5:— | SHA256:— | |||
| 3348 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\index | — | |
MD5:— | SHA256:— | |||
| 3348 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_0 | — | |
MD5:— | SHA256:— | |||
| 3348 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_1 | — | |
MD5:— | SHA256:— | |||
| 3348 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_2 | — | |
MD5:— | SHA256:— | |||
| 3348 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_3 | — | |
MD5:— | SHA256:— | |||
| 3348 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\ac7f8cab-ea6f-4ca8-8c4a-e336c89d6898.tmp | — | |
MD5:— | SHA256:— | |||
| 3348 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000018.dbtmp | — | |
MD5:— | SHA256:— | |||
| 3348 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\GPUCache\index | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
30
TCP/UDP connections
93
DNS requests
70
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3464 | iexplore.exe | GET | 304 | 13.32.223.2:80 | http://i.cdnpark.com/themes/assets/style.css | US | compressed | 343 b | whitelisted |
3348 | chrome.exe | GET | 302 | 172.217.22.110:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvMjJlQUFXRC12Ny1ldUFnMXF3SDlXZDlFZw/7319.128.0.1_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx | US | html | 503 b | whitelisted |
3464 | iexplore.exe | GET | 200 | 13.32.223.2:80 | http://i.cdnpark.com/themes/assets/style.css | US | text | 343 b | whitelisted |
456 | iexplore.exe | GET | 200 | 204.79.197.200:80 | http://www.bing.com/favicon.ico | US | image | 237 b | whitelisted |
3464 | iexplore.exe | GET | 200 | 13.32.223.2:80 | http://i.cdnpark.com/themes/registrar/images/logo_namecheap.png | US | image | 4.80 Kb | whitelisted |
3464 | iexplore.exe | GET | 200 | 13.32.223.2:80 | http://i.cdnpark.com/themes/registrar/style_namecheap.css | US | text | 1.73 Kb | whitelisted |
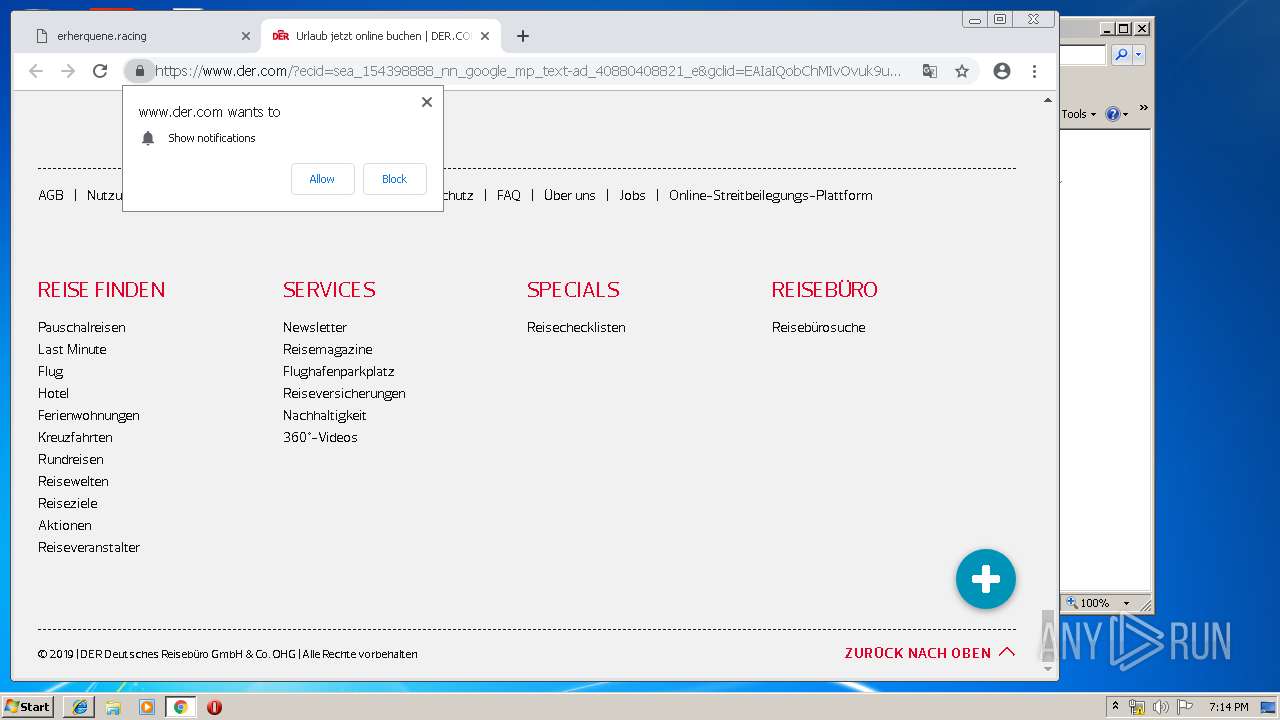
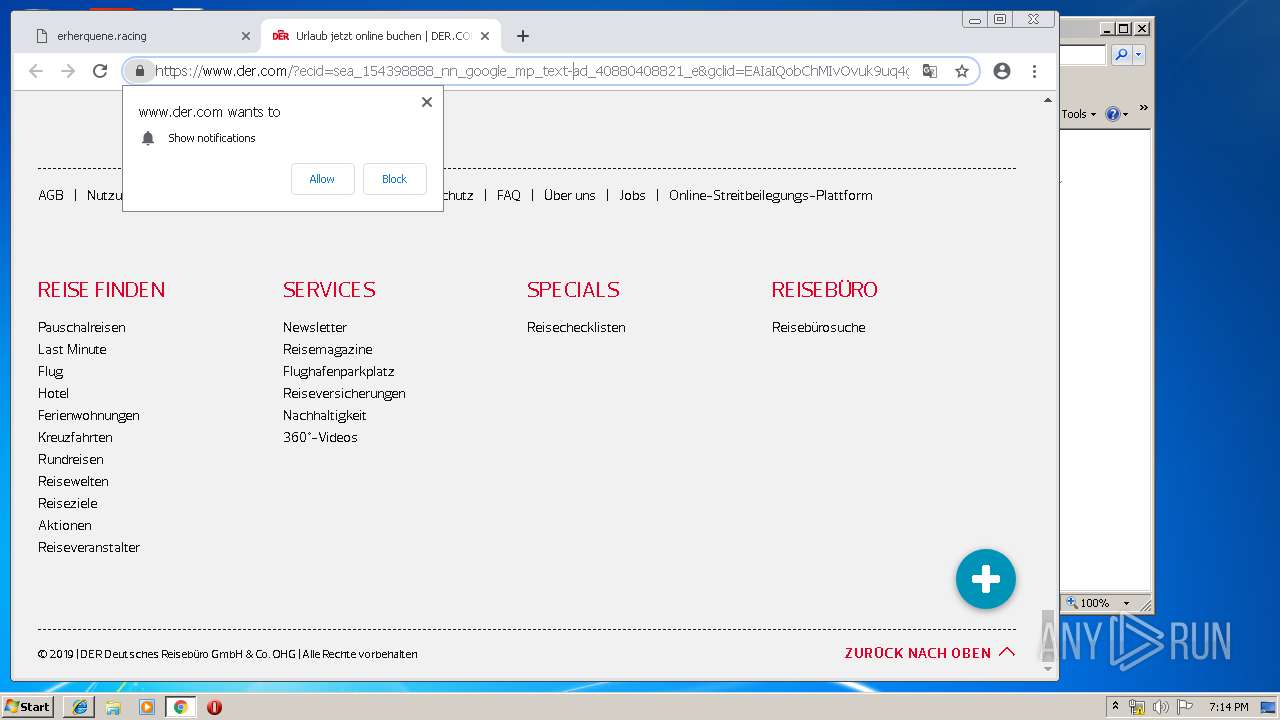
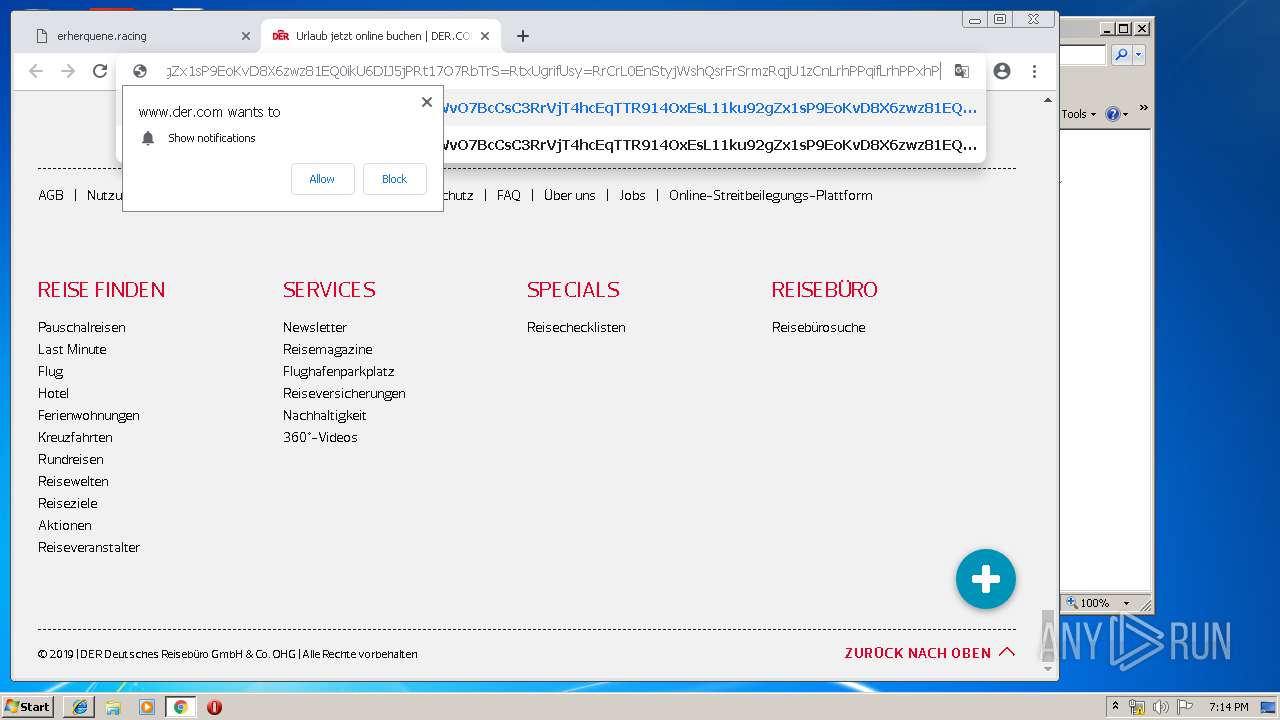
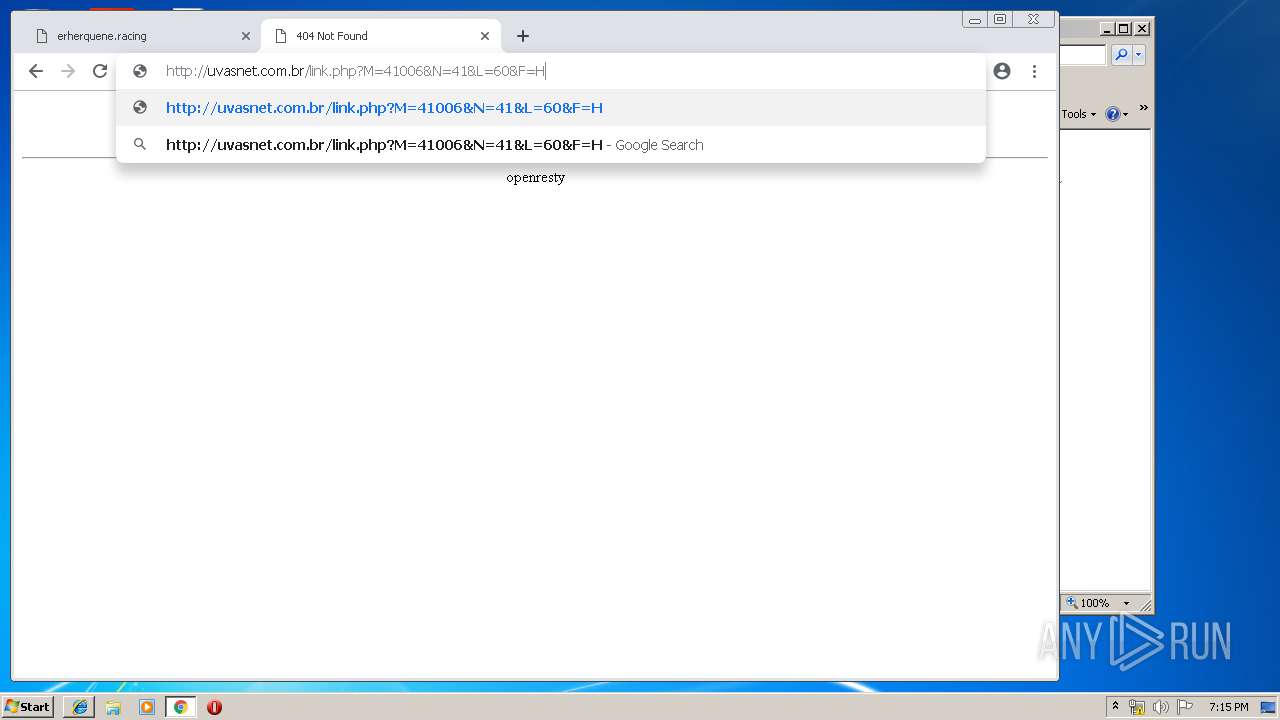
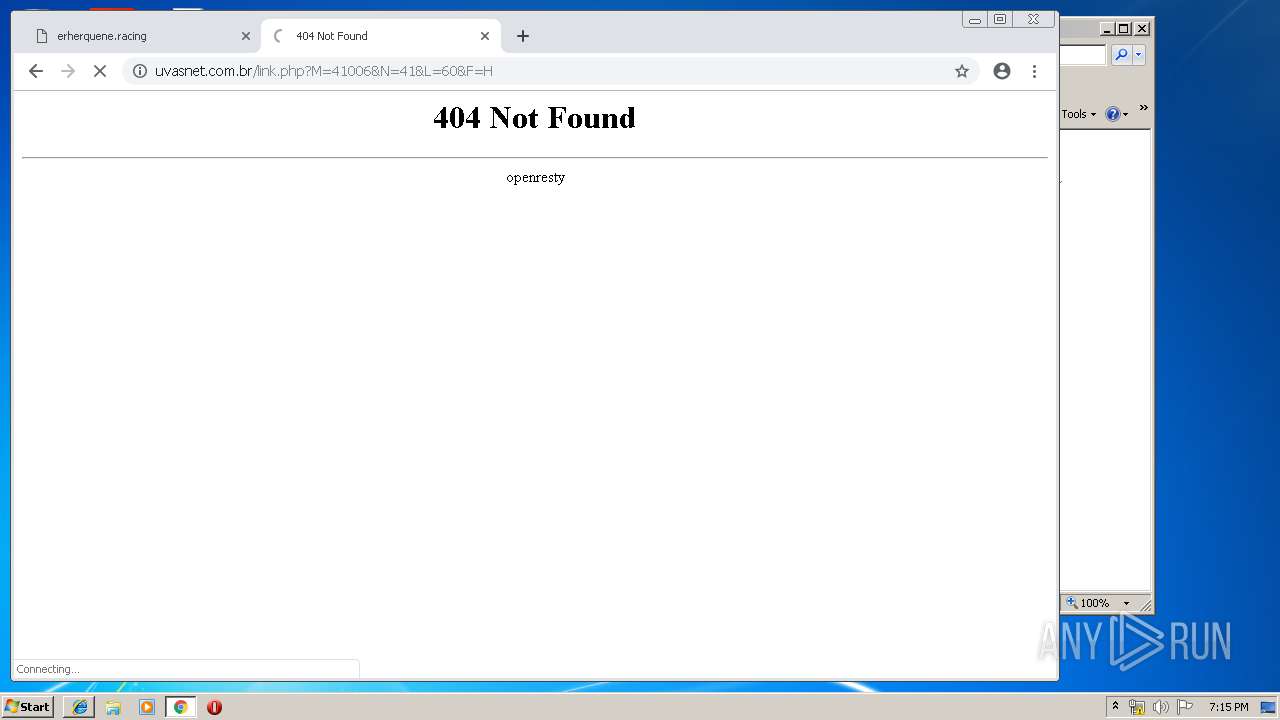
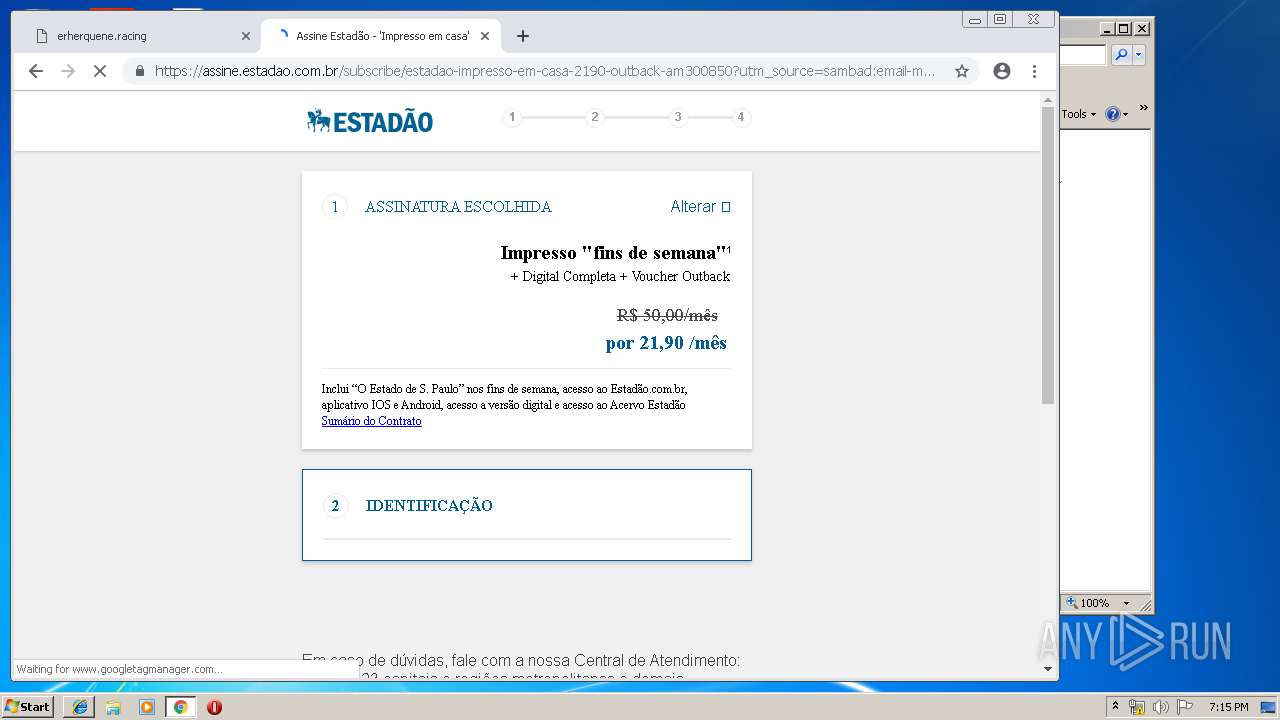
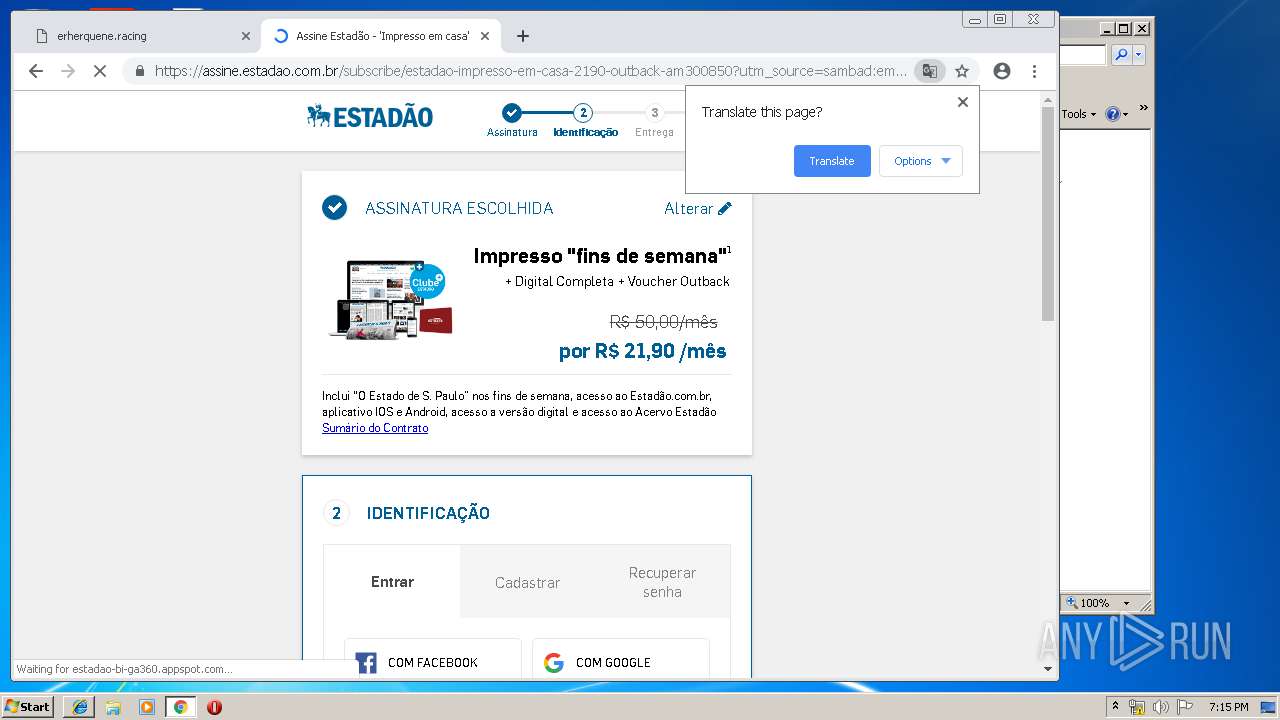
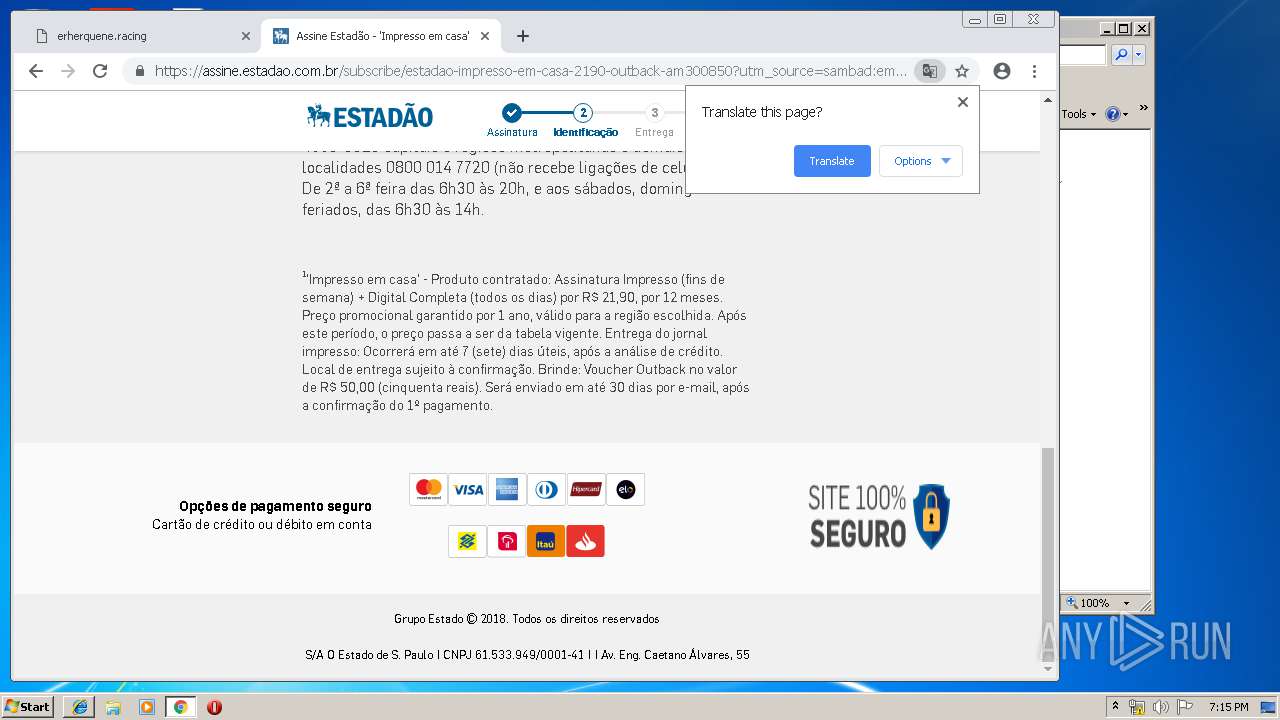
3348 | chrome.exe | GET | 200 | 198.54.117.197:80 | http://erherquene.racing/ | US | html | 1.58 Kb | malicious |
3348 | chrome.exe | GET | 200 | 173.194.5.234:80 | http://r5---sn-aigzrn7l.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvMjJlQUFXRC12Ny1ldUFnMXF3SDlXZDlFZw/7319.128.0.1_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx?cms_redirect=yes&mip=89.249.73.20&mm=28&mn=sn-aigzrn7l&ms=nvh&mt=1558375905&mv=m&pl=25&shardbypass=yes | US | crx | 842 Kb | whitelisted |
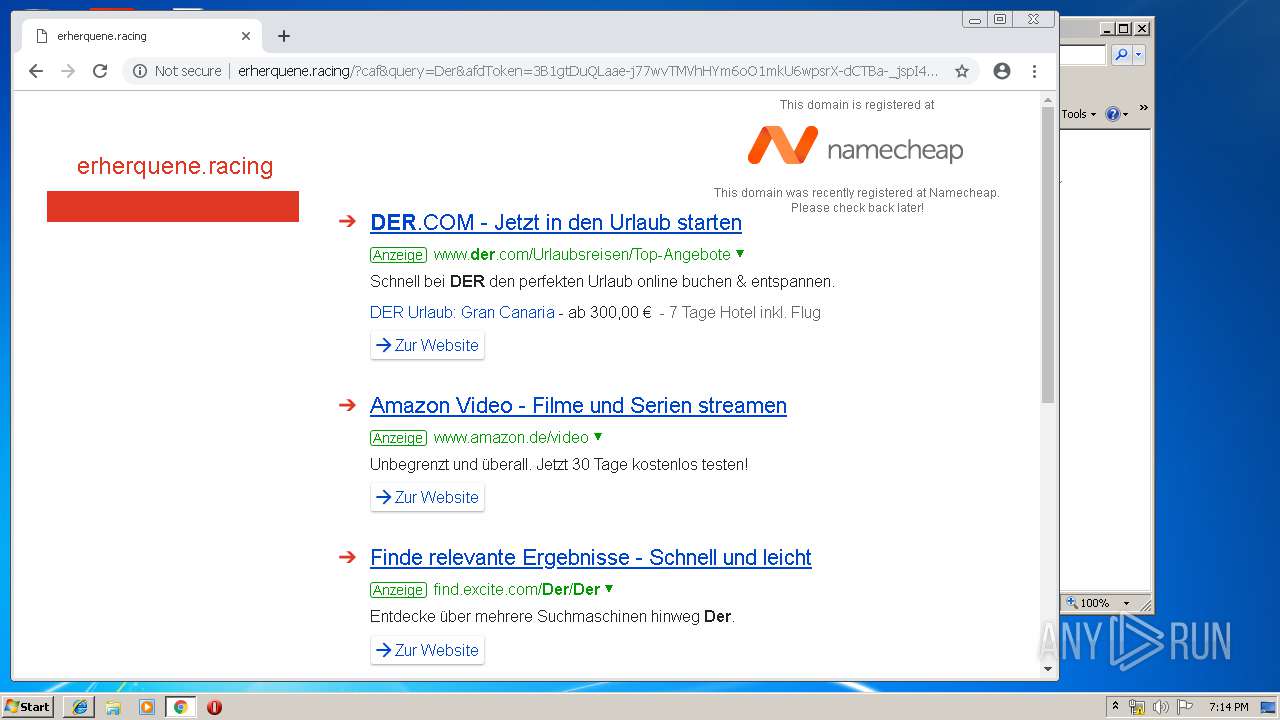
3348 | chrome.exe | GET | 200 | 185.53.179.29:80 | http://parkingcrew.net/jsparkcaf.php?regcn=243142&_v=2&_h=erherquene.racing&_t=1558376032387 | DE | html | 2.54 Kb | whitelisted |
3348 | chrome.exe | GET | 200 | 185.53.178.30:80 | http://js.parkingcrew.net/track.php?domain=erherquene.racing&toggle=browserjs&uid=MTU1ODM3NjAzMi41ODMzOjNlYzIyOGUwN2JiN2E1NDMwNTk3ODEyODJmMDgyMzlkM2Q0MGJkMTNhYzE4M2U0ZGJkODE5ZGI2YWQxMTg3MzU6NWNlMmVlNjA4ZTY5Nw%3D%3D | DE | binary | 20 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
456 | iexplore.exe | 204.79.197.200:80 | bat.bing.com | Microsoft Corporation | US | whitelisted |
3348 | chrome.exe | 216.58.206.3:443 | www.google.com.ua | Google Inc. | US | whitelisted |
3464 | iexplore.exe | 185.53.179.29:80 | parkingcrew.net | Team Internet AG | DE | malicious |
3348 | chrome.exe | 172.217.16.206:443 | clients1.google.com | Google Inc. | US | whitelisted |
3348 | chrome.exe | 172.217.21.227:443 | www.gstatic.com | Google Inc. | US | whitelisted |
3348 | chrome.exe | 172.217.18.163:443 | ssl.gstatic.com | Google Inc. | US | whitelisted |
3348 | chrome.exe | 216.58.210.14:443 | apis.google.com | Google Inc. | US | whitelisted |
3348 | chrome.exe | 172.217.18.100:443 | www.google.com | Google Inc. | US | whitelisted |
3348 | chrome.exe | 172.217.16.131:443 | www.google.de | Google Inc. | US | whitelisted |
— | — | 216.58.206.14:443 | clients2.google.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
i.cdnpark.com |
| whitelisted |
www.bing.com |
| whitelisted |
parkingcrew.net |
| whitelisted |
accounts.google.com |
| shared |
clientservices.googleapis.com |
| whitelisted |
www.google.com.ua |
| whitelisted |
clients1.google.com |
| whitelisted |
ssl.gstatic.com |
| whitelisted |
www.gstatic.com |
| whitelisted |
apis.google.com |
| whitelisted |