| File name: | 7c9f3607e7ded8209a0d73274834dc35cc0b0300ffb882f0dd4d4114959e9ece.bin |
| Full analysis: | https://app.any.run/tasks/83d929dc-2694-44d9-8e13-6716af04684b |
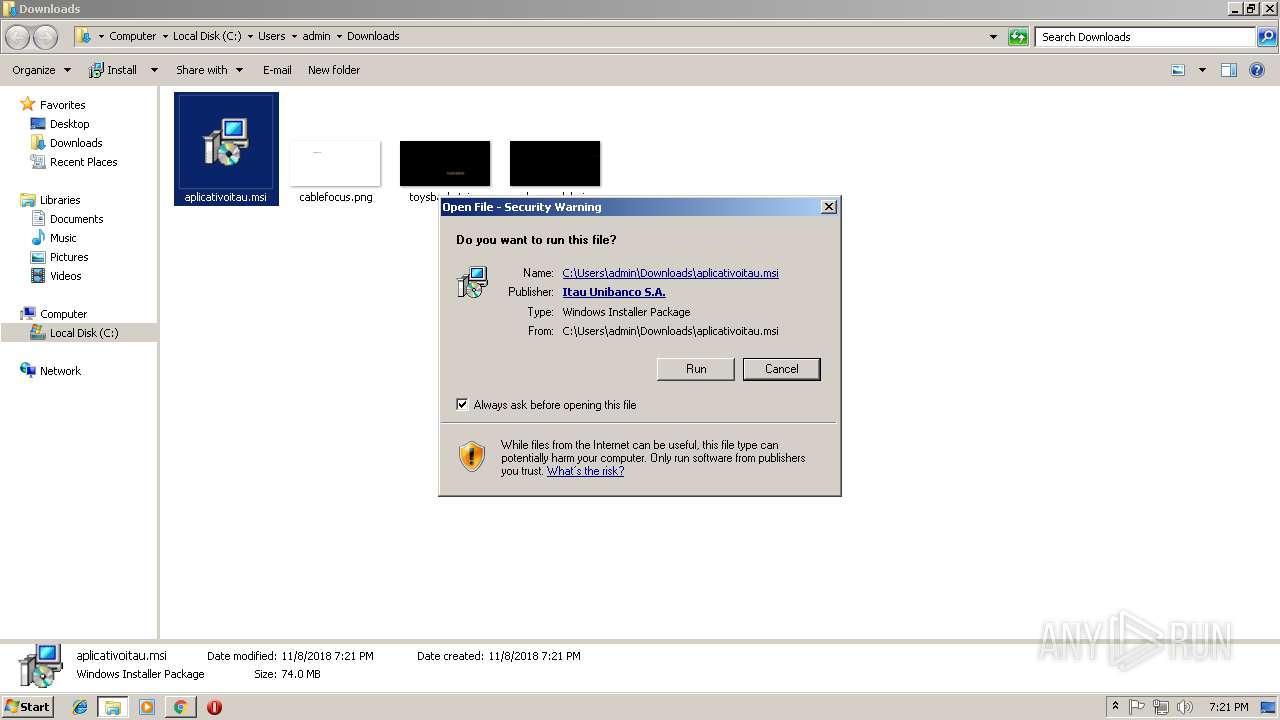
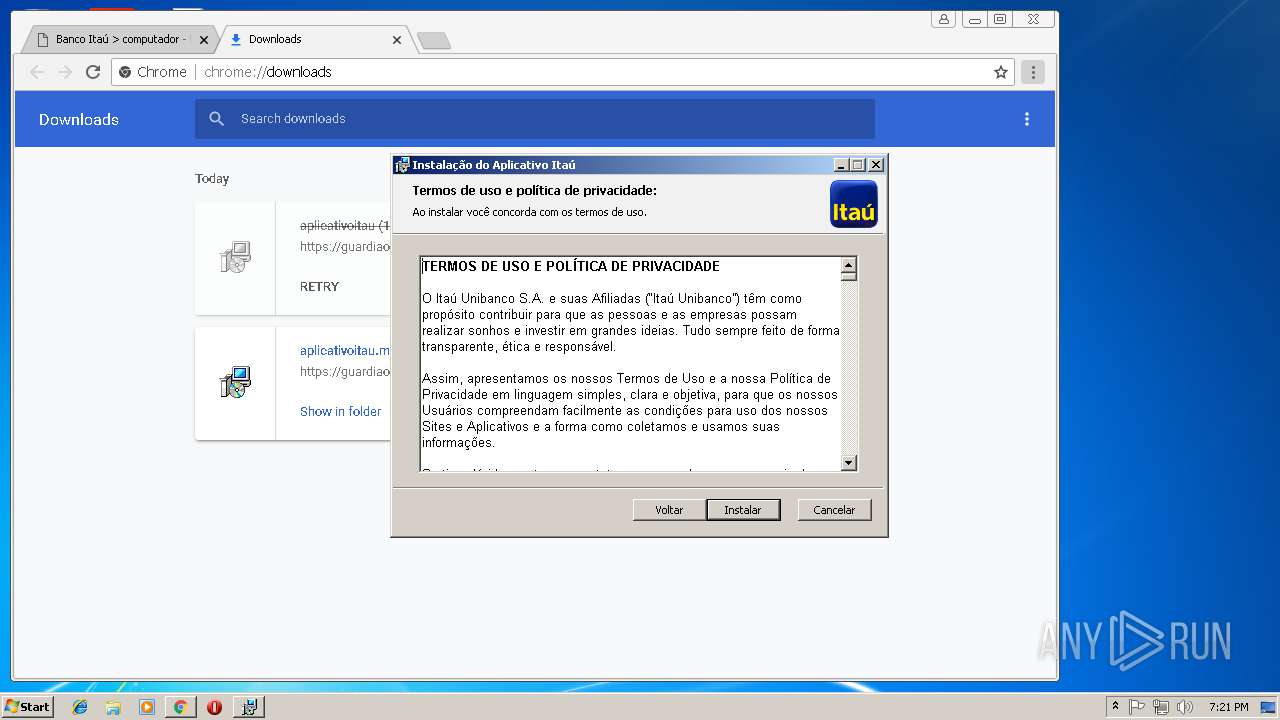
| Verdict: | Malicious activity |
| Analysis date: | November 08, 2018, 19:19:53 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | F43ADFE423DC03E3AA5CA355553706A3 |
| SHA1: | 49803073DD274C8740E0163FC30300CBAE8F2CC9 |
| SHA256: | 7C9F3607E7DED8209A0D73274834DC35CC0B0300FFB882F0DD4D4114959E9ECE |
| SSDEEP: | 12288:5V18cvDNpMkee5PtFw98fP9PBRZJuU0owFq3LtFDKVL74uq7o8BM6B7iW:HvDl5PtPZJ/l9tFW6uYoIBAW |
MALICIOUS
Uses SVCHOST.EXE for hidden code execution
- svchost.exe (PID: 2748)
- 7c9f3607e7ded8209a0d73274834dc35cc0b0300ffb882f0dd4d4114959e9ece.bin.exe (PID: 184)
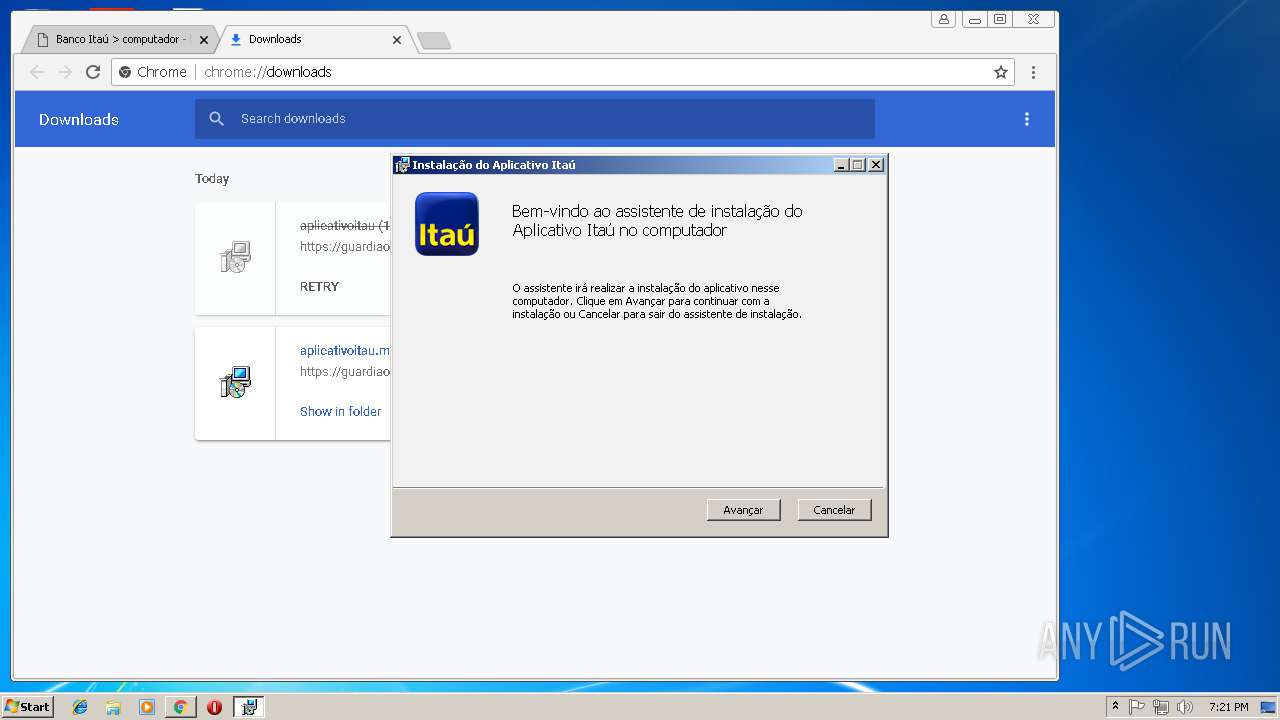
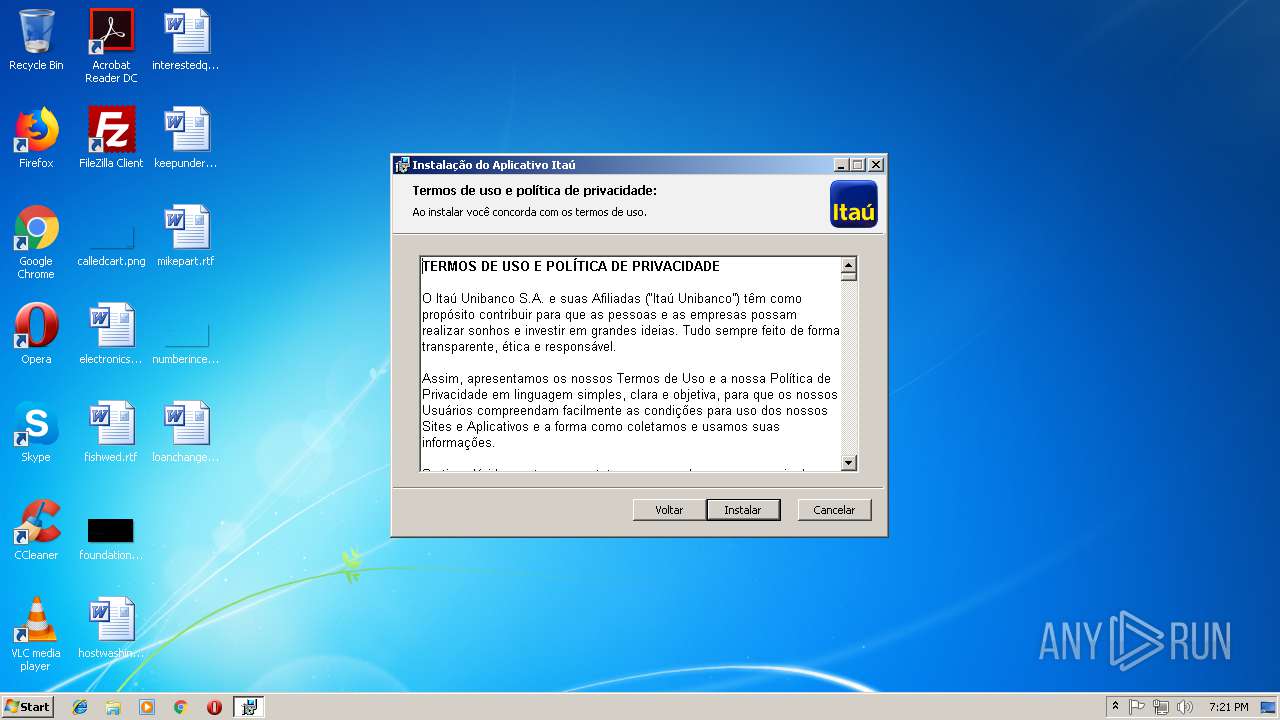
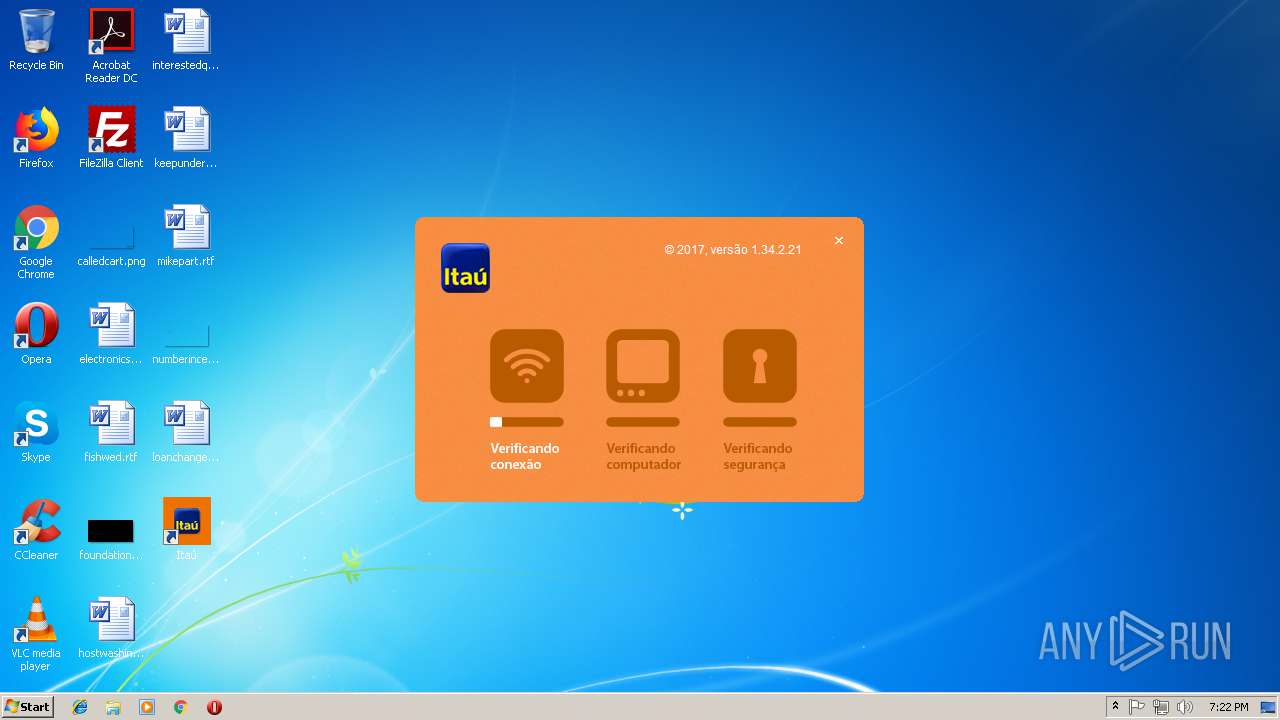
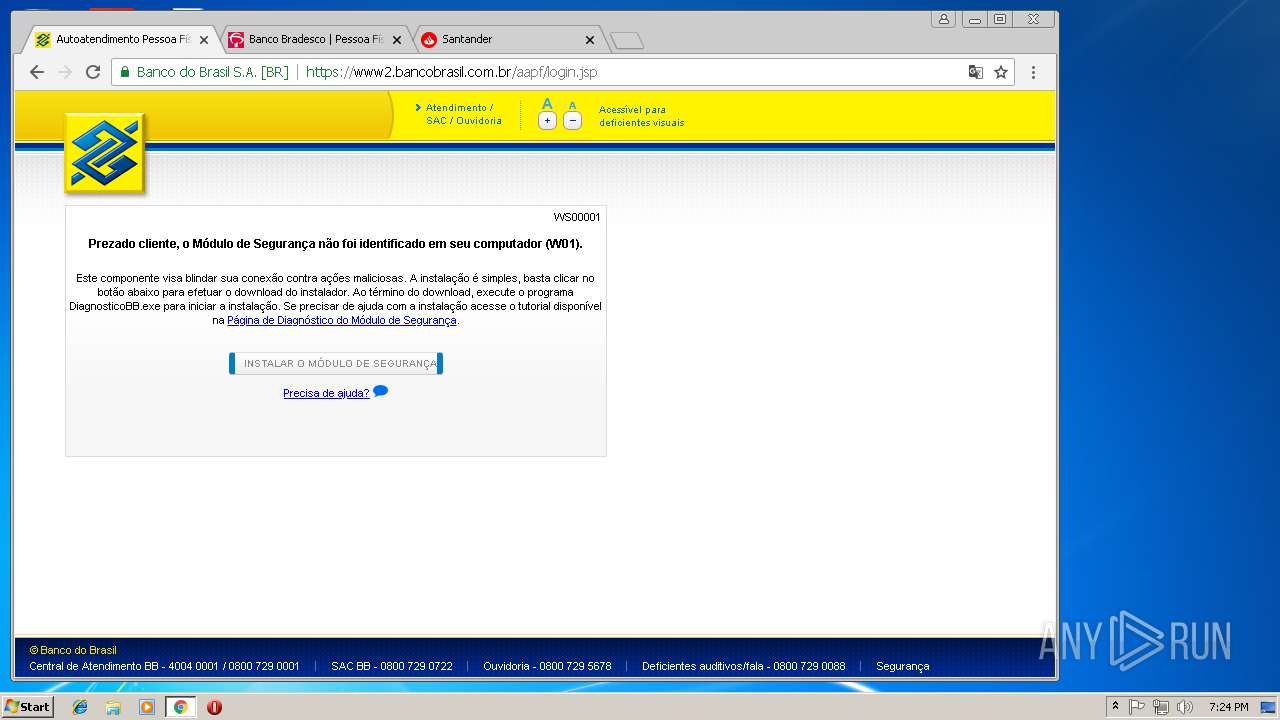
Application was dropped or rewritten from another process
- itauaplicativo.exe (PID: 800)
- itauaplicativo.exe (PID: 1408)
- itauaplicativo.exe (PID: 1112)
- itauaplicativo.exe (PID: 3492)
- itauaplicativo.exe (PID: 3720)
- itauaplicativo.exe (PID: 3916)
Loads dropped or rewritten executable
- itauaplicativo.exe (PID: 1408)
- itauaplicativo.exe (PID: 800)
- itauaplicativo.exe (PID: 1112)
- itauaplicativo.exe (PID: 3492)
- itauaplicativo.exe (PID: 3720)
- itauaplicativo.exe (PID: 3916)
SUSPICIOUS
Application launched itself
- svchost.exe (PID: 2748)
- itauaplicativo.exe (PID: 800)
- itauaplicativo.exe (PID: 1408)
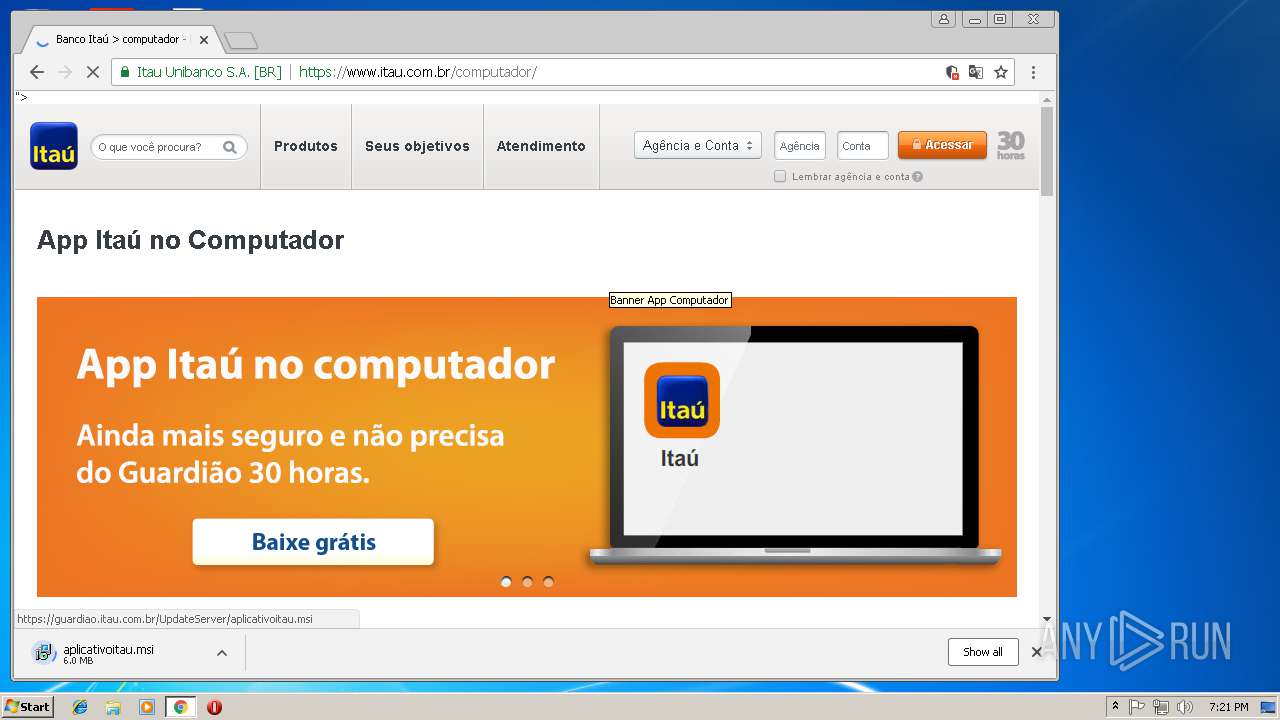
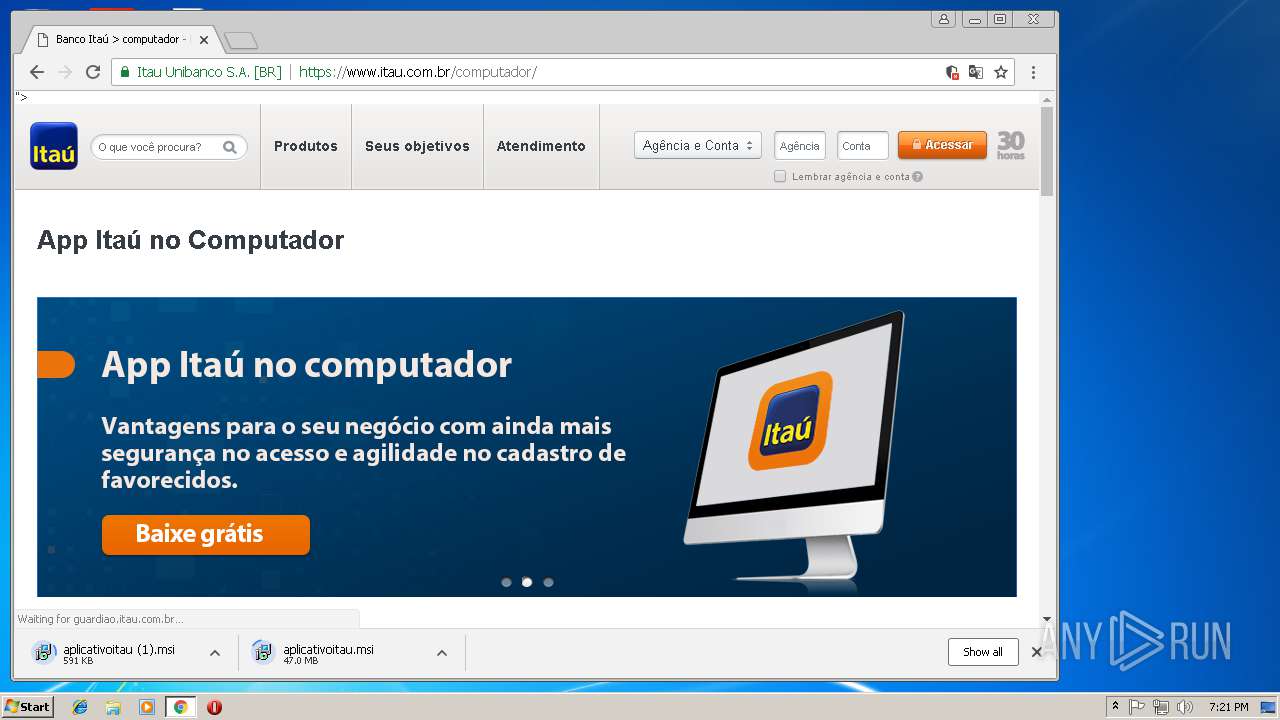
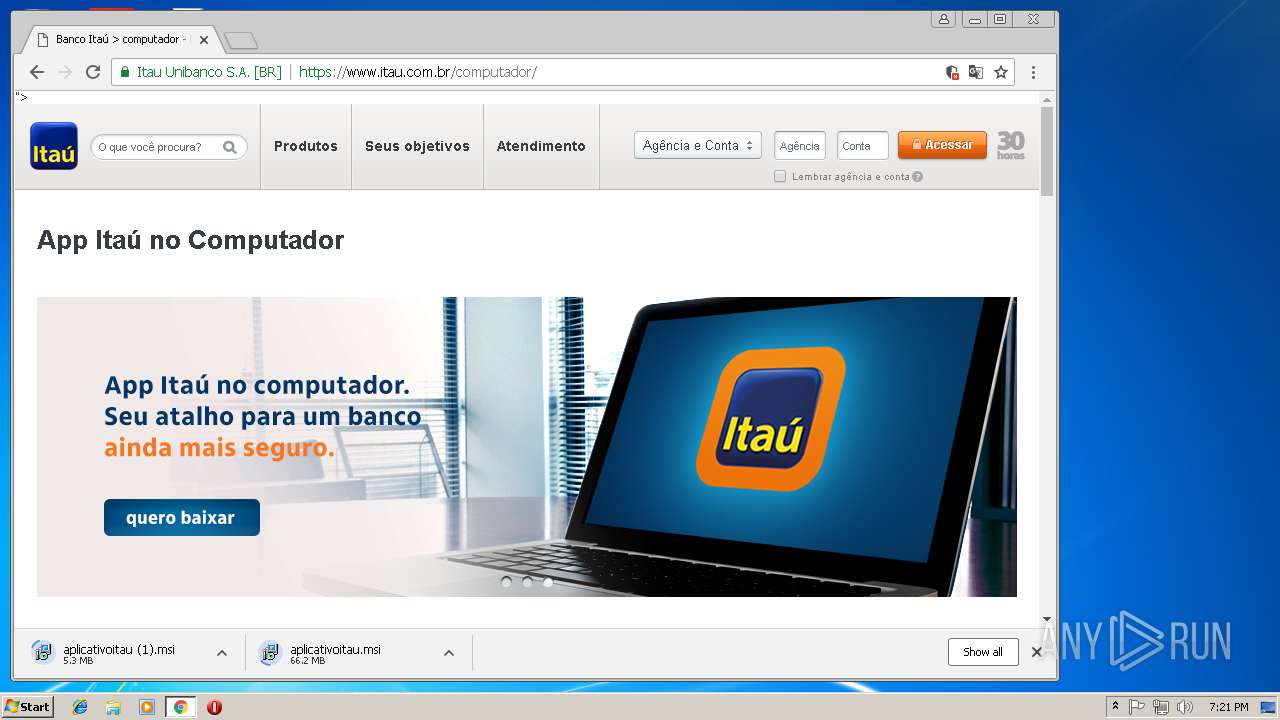
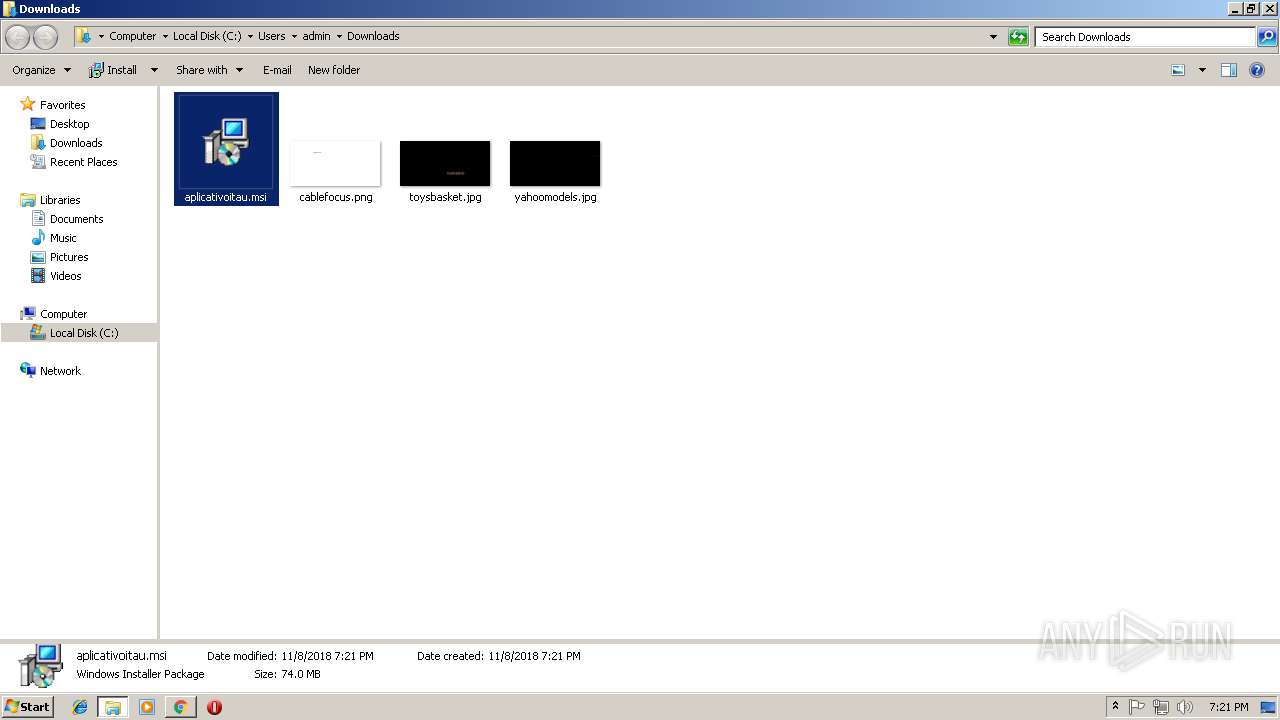
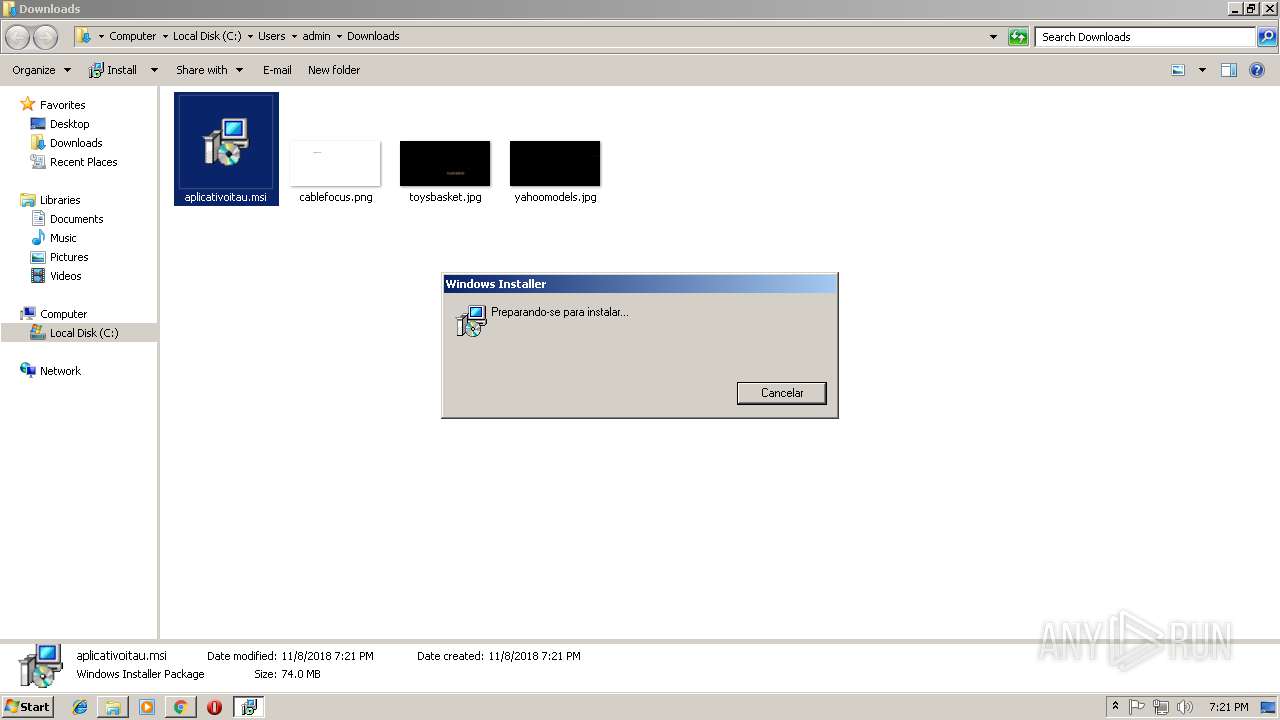
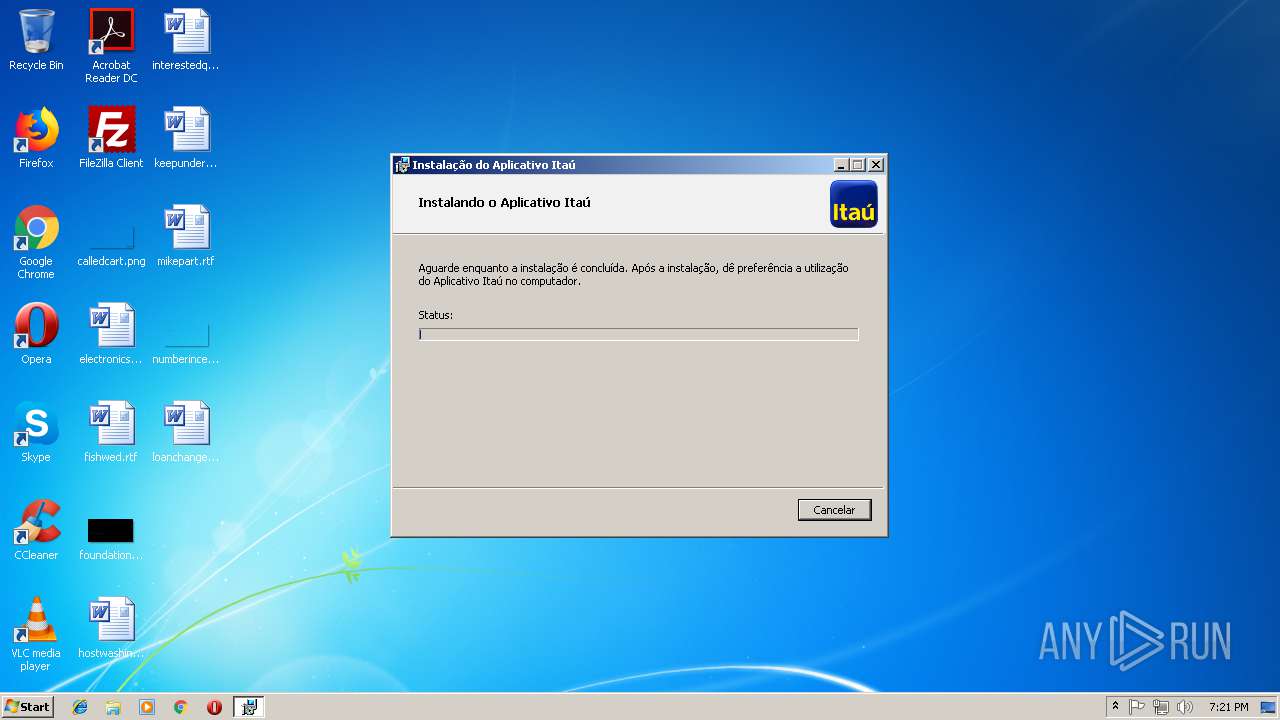
Executable content was dropped or overwritten
- msiexec.exe (PID: 3996)
Creates files in the user directory
- msiexec.exe (PID: 3996)
INFO
Reads settings of System Certificates
- chrome.exe (PID: 3228)
Low-level read access rights to disk partition
- vssvc.exe (PID: 3224)
Reads Internet Cache Settings
- chrome.exe (PID: 3228)
Creates files in the user directory
- chrome.exe (PID: 3228)
- chrome.exe (PID: 1308)
Creates or modifies windows services
- msiexec.exe (PID: 3996)
- vssvc.exe (PID: 3224)
Application launched itself
- chrome.exe (PID: 3228)
- chrome.exe (PID: 1308)
Searches for installed software
- msiexec.exe (PID: 3996)
Creates a software uninstall entry
- msiexec.exe (PID: 3996)
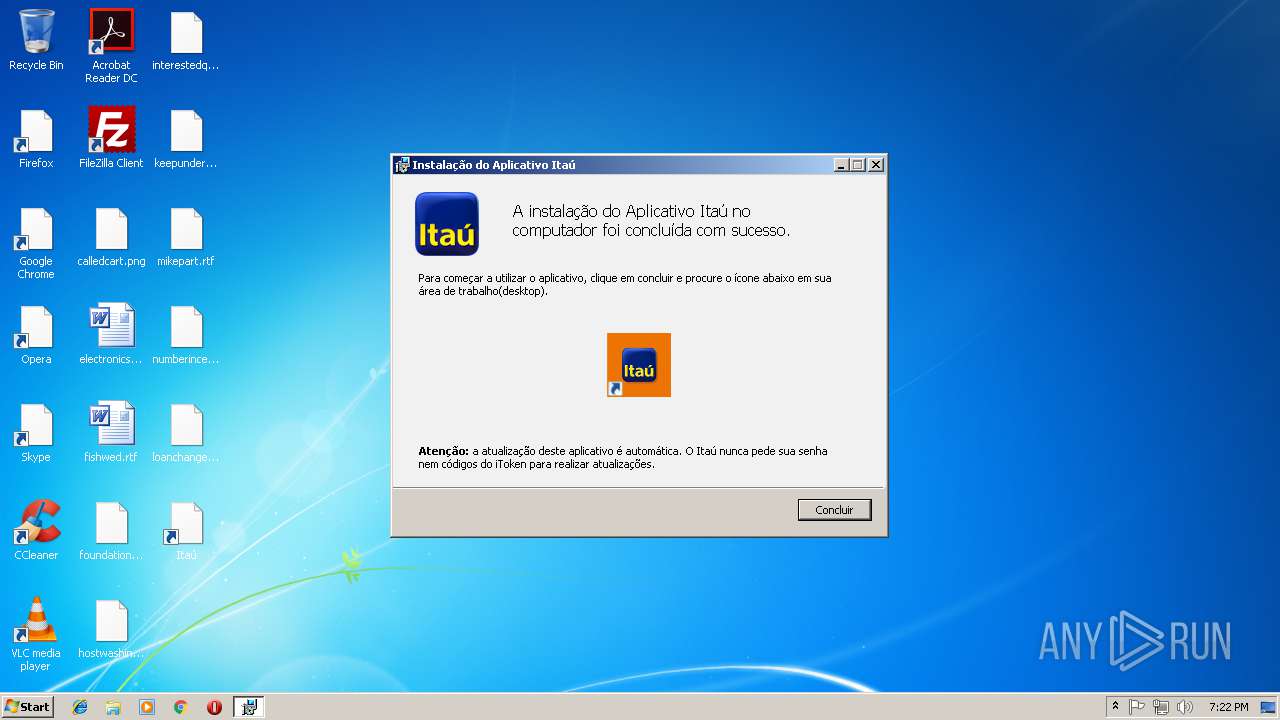
Dropped object may contain Bitcoin addresses
- msiexec.exe (PID: 3996)
- chrome.exe (PID: 1308)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (42.2) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (37.3) |
| .dll | | | Win32 Dynamic Link Library (generic) (8.8) |
| .exe | | | Win32 Executable (generic) (6) |
| .exe | | | Generic Win/DOS Executable (2.7) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2018:08:06 17:00:14+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 9 |
| CodeSize: | 151040 |
| InitializedDataSize: | 605696 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x12325 |
| OSVersion: | 5 |
| ImageVersion: | - |
| SubsystemVersion: | 5 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 1.9.7.964 |
| ProductVersionNumber: | 1.9.7.964 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Windows NT 32-bit |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Unicode |
| Comments: | Identically Bkmarks Delete Networkinterface |
| InternalName: | Attached |
| ProductName: | Attached |
| FileDescription: | Identically Bkmarks Delete Networkinterface |
| LegalCopyright: | Copyright 2015 |
| CompanyName: | Bitdefender LLC |
| ProductVersion: | 1.9.7.964 |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 06-Aug-2018 15:00:14 |
| Detected languages: |
|
| Debug artifacts: |
|
| Comments: | Identically Bkmarks Delete Networkinterface |
| InternalName: | Attached |
| ProductName: | Attached |
| FileDescription: | Identically Bkmarks Delete Networkinterface |
| LegalCopyright: | Copyright 2015 |
| CompanyName: | Bitdefender LLC |
| ProductVersion: | 1.9.7.964 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x000000F8 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 4 |
| Time date stamp: | 06-Aug-2018 15:00:14 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x00024D73 | 0x00024E00 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.68747 |
.rdata | 0x00026000 | 0x00009608 | 0x00009800 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 6.09198 |
.data | 0x00030000 | 0x00005084 | 0x00003400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 6.04737 |
.rsrc | 0x00036000 | 0x000871BC | 0x00087200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 7.78787 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 4.93343 | 657 | Latin 1 / Western European | English - United States | RT_MANIFEST |
2 | 3.69318 | 21640 | Latin 1 / Western European | English - United States | RT_ICON |
3 | 3.05225 | 16936 | Latin 1 / Western European | English - United States | RT_ICON |
4 | 4.00809 | 9640 | Latin 1 / Western European | English - United States | RT_ICON |
5 | 3.33953 | 4264 | Latin 1 / Western European | English - United States | RT_ICON |
6 | 4.27232 | 2440 | Latin 1 / Western European | English - United States | RT_ICON |
101 | 3.03869 | 90 | Latin 1 / Western European | English - United States | RT_GROUP_ICON |
310 | 3.86979 | 490 | Latin 1 / Western European | English - United States | RT_STRING |
311 | 1.28243 | 40 | Latin 1 / Western European | English - United States | RT_STRING |
363 | 3.33609 | 308 | Latin 1 / Western European | English - United States | RT_CURSOR |
Imports
ADVAPI32.dll |
AUTHZ.dll |
COMCTL32.dll |
GDI32.dll |
IMM32.dll |
KERNEL32.dll |
MSACM32.dll |
NETAPI32.dll |
ODBC32.dll |
OLEAUT32.dll |
Total processes
86
Monitored processes
52
Malicious processes
4
Suspicious processes
4
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 184 | "C:\Users\admin\AppData\Local\Temp\7c9f3607e7ded8209a0d73274834dc35cc0b0300ffb882f0dd4d4114959e9ece.bin.exe" | C:\Users\admin\AppData\Local\Temp\7c9f3607e7ded8209a0d73274834dc35cc0b0300ffb882f0dd4d4114959e9ece.bin.exe | — | explorer.exe | |||||||||||
User: admin Company: Bitdefender LLC Integrity Level: MEDIUM Description: Identically Bkmarks Delete Networkinterface Exit code: 0 Modules
| |||||||||||||||
| 584 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=856,11287558885759409268,13831361049620686929,131072 --enable-features=PasswordImport --disable-gpu-compositing --service-pipe-token=082EECF97BAD4E3DD8AE66A4E299C3D8 --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=082EECF97BAD4E3DD8AE66A4E299C3D8 --renderer-client-id=11 --mojo-platform-channel-handle=3900 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 676 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=856,11287558885759409268,13831361049620686929,131072 --enable-features=PasswordImport --disable-gpu-sandbox --gpu-preferences=KAAAAAAAAACAAwBAAQAAAAAAAAAAAGAAEAAAAAAAAAAAAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAKAAAAEAAAAAAAAAAAAAAACwAAABAAAAAAAAAAAQAAAAoAAAAQAAAAAAAAAAEAAAALAAAA --service-request-channel-token=D379A6B8459043B898481879B55A1EB3 --mojo-platform-channel-handle=3884 /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 776 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=872,12173081635556541403,18026357139765734803,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=DED1564CC3E9B370E74839373D1CB10A --mojo-platform-channel-handle=4140 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
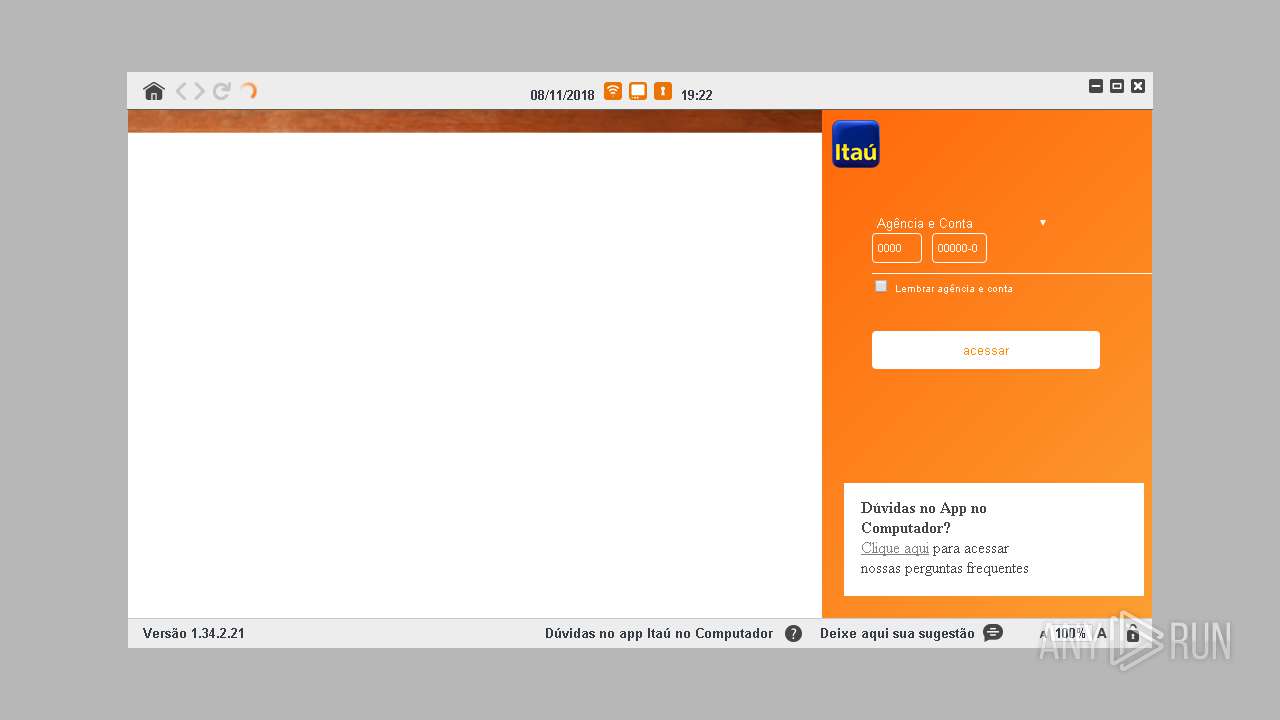
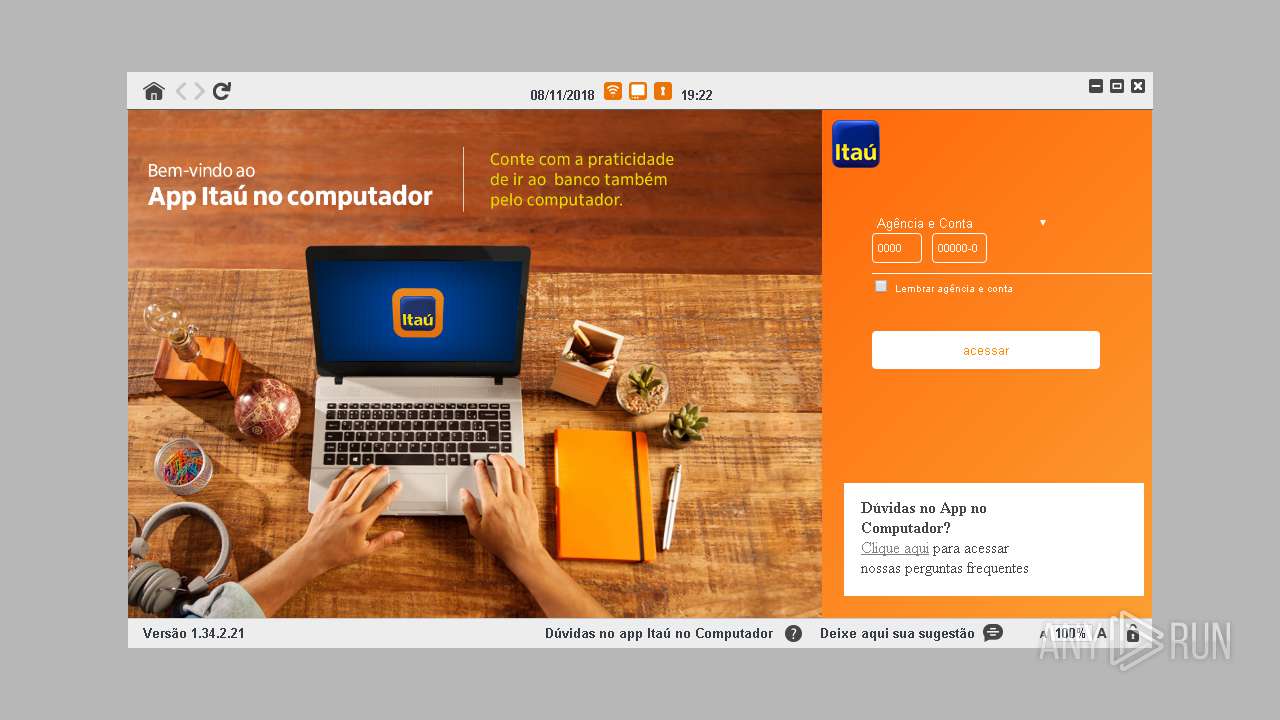
| 800 | "C:\Users\admin\AppData\Local\Aplicativo Itau\itauaplicativo.exe" | C:\Users\admin\AppData\Local\Aplicativo Itau\itauaplicativo.exe | explorer.exe | ||||||||||||
User: admin Company: Banco Itaú Integrity Level: MEDIUM Description: Aplicativo Itaú Exit code: 0 Version: 1.34.2.21 Modules
| |||||||||||||||
| 944 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=872,12173081635556541403,18026357139765734803,131072 --enable-features=PasswordImport --disable-gpu-compositing --service-pipe-token=1C2046EE20E49861363329B49B3A7D6A --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=1C2046EE20E49861363329B49B3A7D6A --renderer-client-id=18 --mojo-platform-channel-handle=2660 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 968 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=872,12173081635556541403,18026357139765734803,131072 --enable-features=PasswordImport --lang=en-US --no-sandbox --service-request-channel-token=08CC9872413864F2DFD2AC144AE43A8D --mojo-platform-channel-handle=5668 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 1000 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=856,11287558885759409268,13831361049620686929,131072 --enable-features=PasswordImport --disable-gpu-compositing --service-pipe-token=FEF686F62C5CC4BB337605553AB6FC02 --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=FEF686F62C5CC4BB337605553AB6FC02 --renderer-client-id=14 --mojo-platform-channel-handle=524 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 1112 | "C:\Users\admin\AppData\Local\Aplicativo Itau\itauaplicativo.exe" --type=renderer --no-sandbox --disable-databases --primordial-pipe-token=AFF4E84EEDD279AA1747D1E4C2C04862 --lang=en-US --lang=pt-BR --log-file="C:\Users\admin\AppData\Local\Aplicativo Itau\debug.log" --log-severity=disable --enable-pinch --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --content-image-texture-target=0,0,3553;0,1,3553;0,2,3553;0,3,3553;0,4,3553;0,5,3553;0,6,3553;0,7,3553;0,8,3553;0,9,3553;0,10,3553;0,11,3553;0,12,3553;0,13,3553;0,14,3553;0,15,3553;0,16,3553;1,0,3553;1,1,3553;1,2,3553;1,3,3553;1,4,3553;1,5,3553;1,6,3553;1,7,3553;1,8,3553;1,9,3553;1,10,3553;1,11,3553;1,12,3553;1,13,3553;1,14,3553;1,15,3553;1,16,3553;2,0,3553;2,1,3553;2,2,3553;2,3,3553;2,4,3553;2,5,3553;2,6,3553;2,7,3553;2,8,3553;2,9,3553;2,10,3553;2,11,3553;2,12,3553;2,13,3553;2,14,3553;2,15,3553;2,16,3553;3,0,3553;3,1,3553;3,2,3553;3,3,3553;3,4,3553;3,5,3553;3,6,3553;3,7,3553;3,8,3553;3,9,3553;3,10,3553;3,11,3553;3,12,3553;3,13,3553;3,14,3553;3,15,3553;3,16,3553;4,0,3553;4,1,3553;4,2,3553;4,3,3553;4,4,3553;4,5,3553;4,6,3553;4,7,3553;4,8,3553;4,9,3553;4,10,3553;4,11,3553;4,12,3553;4,13,3553;4,14,3553;4,15,3553;4,16,3553 --disable-accelerated-video-decode --disable-webrtc-hw-vp8-encoding --disable-gpu-compositing --service-request-channel-token=AFF4E84EEDD279AA1747D1E4C2C04862 --renderer-client-id=2 --mojo-platform-channel-handle=1708 /prefetch:1 | C:\Users\admin\AppData\Local\Aplicativo Itau\itauaplicativo.exe | — | itauaplicativo.exe | |||||||||||
User: admin Company: Banco Itaú Integrity Level: MEDIUM Description: Aplicativo Itaú Exit code: 0 Version: 1.34.2.21 Modules
| |||||||||||||||
| 1152 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=872,12173081635556541403,18026357139765734803,131072 --enable-features=PasswordImport --disable-gpu-compositing --service-pipe-token=27757A5BECA2CB3C166961A6AD6378E7 --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=27757A5BECA2CB3C166961A6AD6378E7 --renderer-client-id=9 --mojo-platform-channel-handle=2532 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
Total events
2 362
Read events
1 770
Write events
572
Delete events
20
Modification events
| (PID) Process: | (3228) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (3228) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (2064) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 3228-13186178424063125 |
Value: 259 | |||
| (PID) Process: | (3228) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (3228) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (3228) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (3228) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 3516-13180984670829101 |
Value: 0 | |||
| (PID) Process: | (3228) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 3228-13186178424063125 |
Value: 259 | |||
| (PID) Process: | (3228) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
| (PID) Process: | (3228) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | metricsid |
Value: | |||
Executable files
19
Suspicious files
340
Text files
376
Unknown types
32
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3228 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\db4af204-5d71-45c0-8f0a-eece7128a145.tmp | — | |
MD5:— | SHA256:— | |||
| 3228 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Download Service\EntryDB\000016.dbtmp | — | |
MD5:— | SHA256:— | |||
| 3228 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000016.dbtmp | — | |
MD5:— | SHA256:— | |||
| 3228 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\c56c6ff2-d57a-49aa-8ba8-f8cbf09f55e7.tmp | — | |
MD5:— | SHA256:— | |||
| 3228 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Last Version | text | |
MD5:— | SHA256:— | |||
| 3228 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Service Worker\Database\LOG.old | text | |
MD5:— | SHA256:— | |||
| 3228 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Service Worker\CacheStorage\e6622492fa163609ddd4212f54512baa07929ed3\caecb3bd-7969-4305-84d6-3a376453ec73\index-dir\temp-index | — | |
MD5:— | SHA256:— | |||
| 3228 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old | text | |
MD5:— | SHA256:— | |||
| 3228 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old~RF5dbe1b.TMP | text | |
MD5:— | SHA256:— | |||
| 3228 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old | text | |
MD5:— | SHA256:— | |||
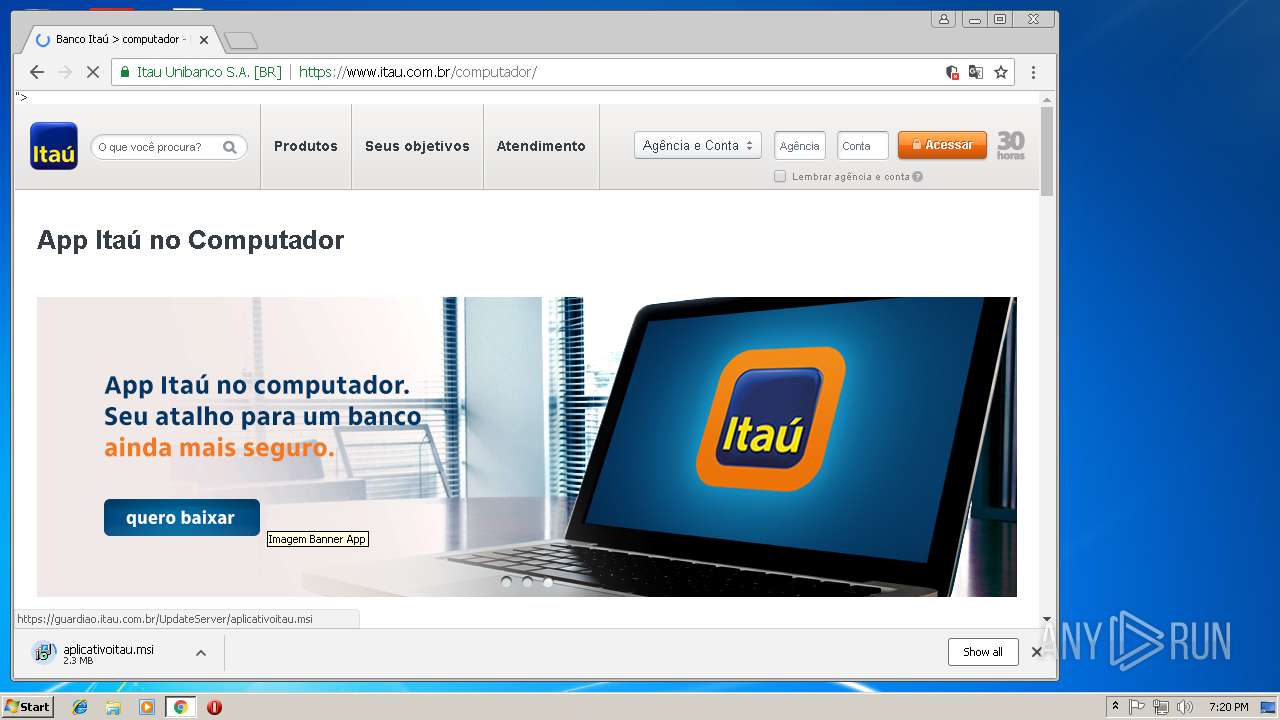
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
22
TCP/UDP connections
178
DNS requests
89
Threats
9
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
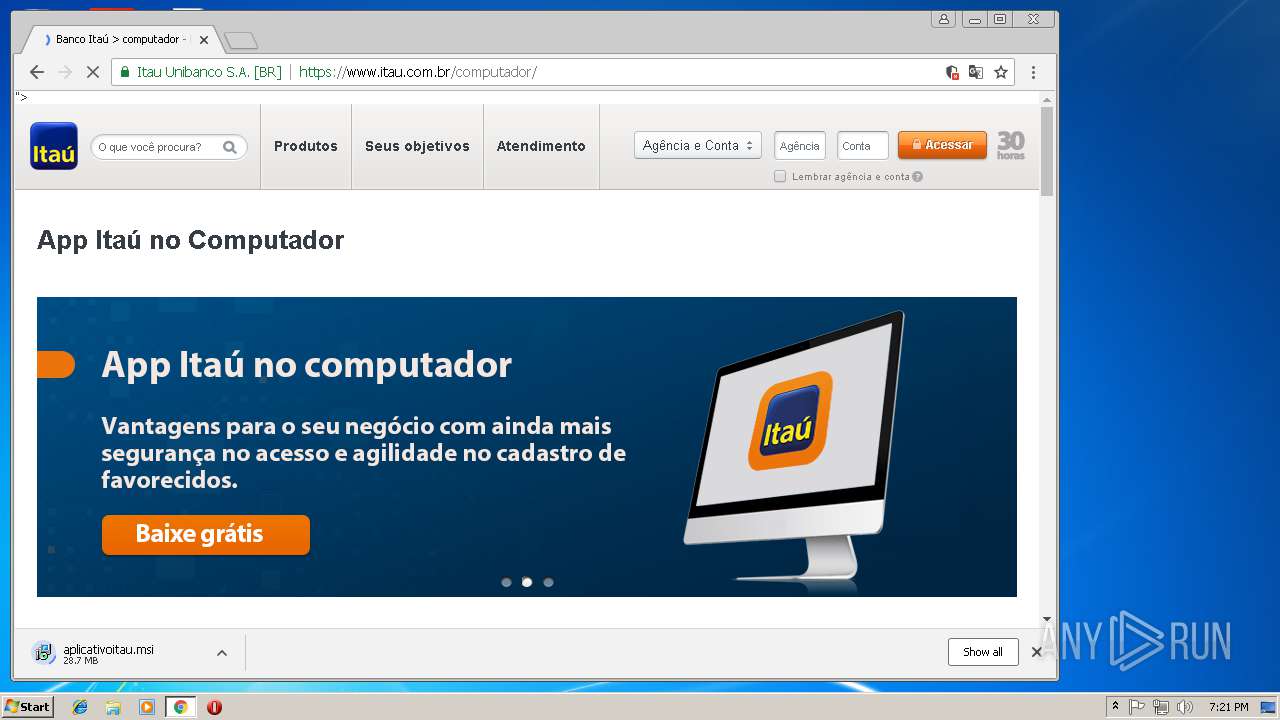
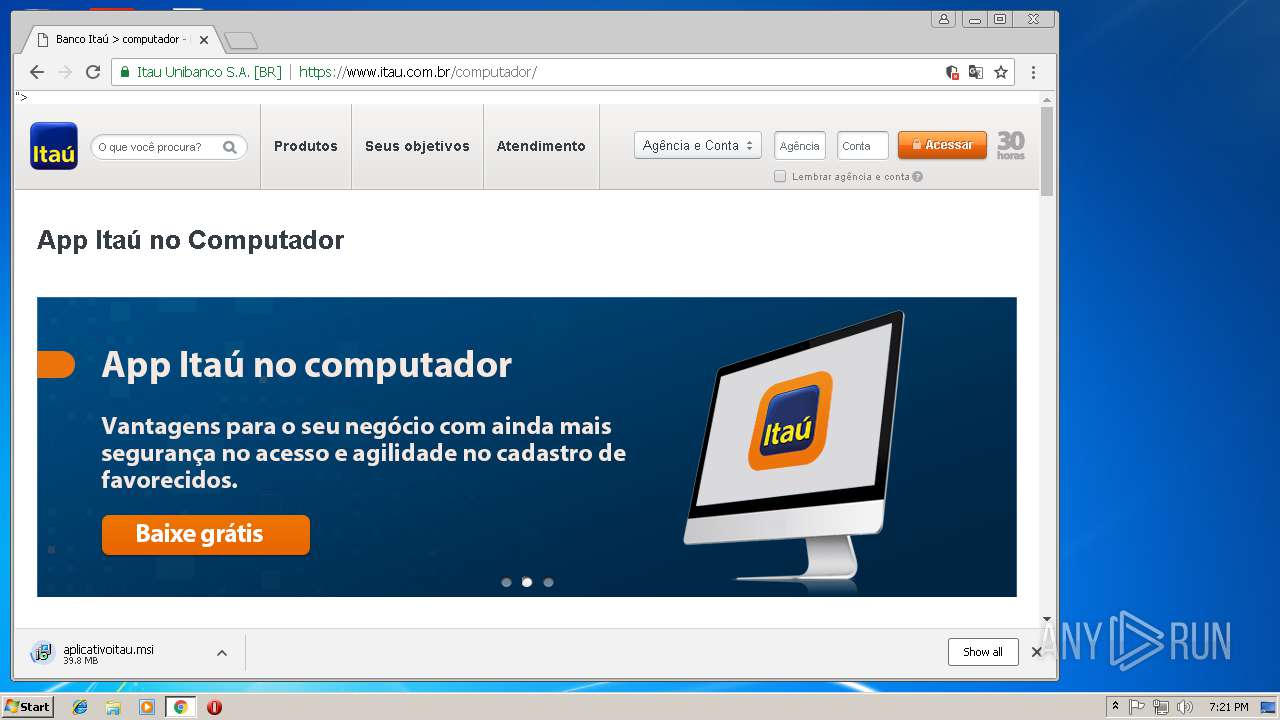
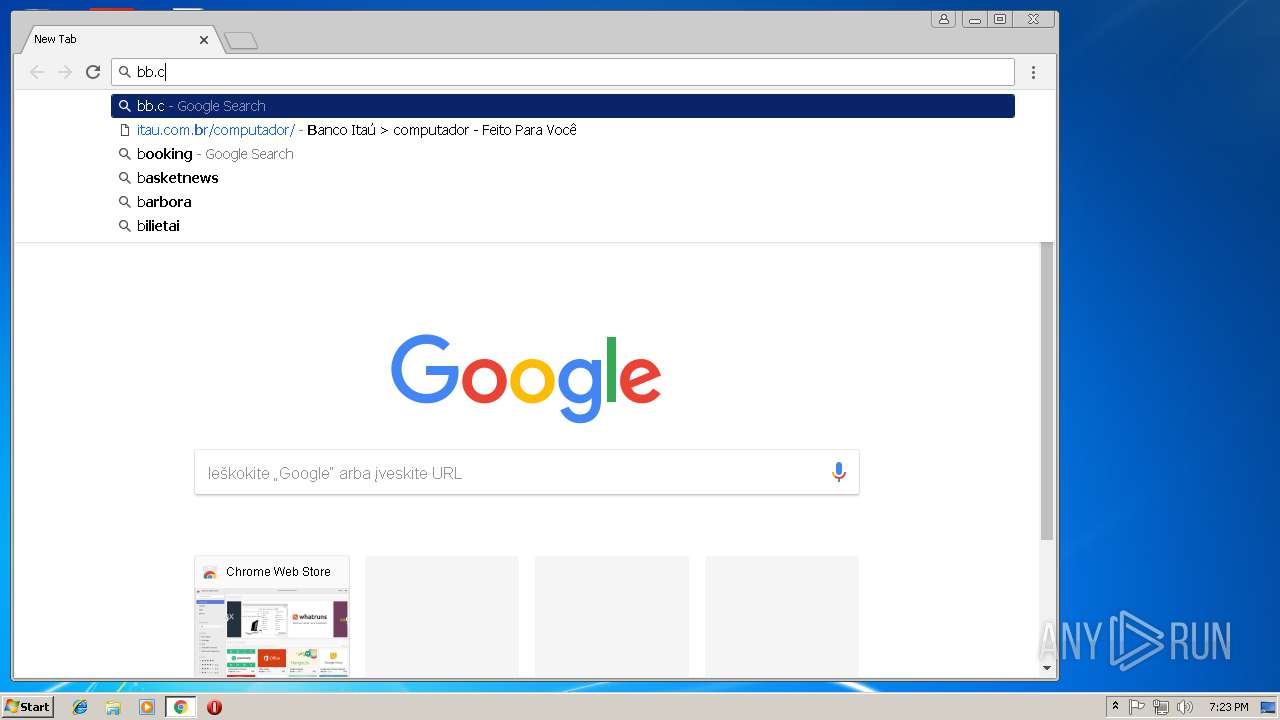
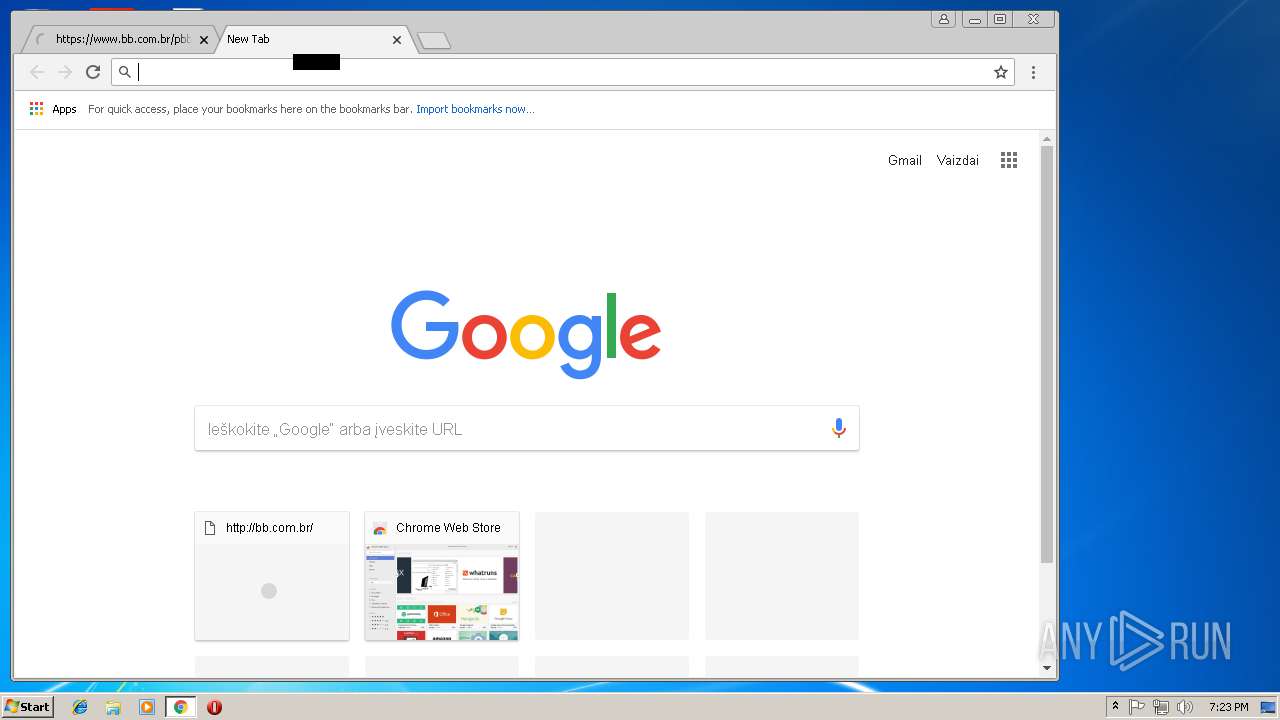
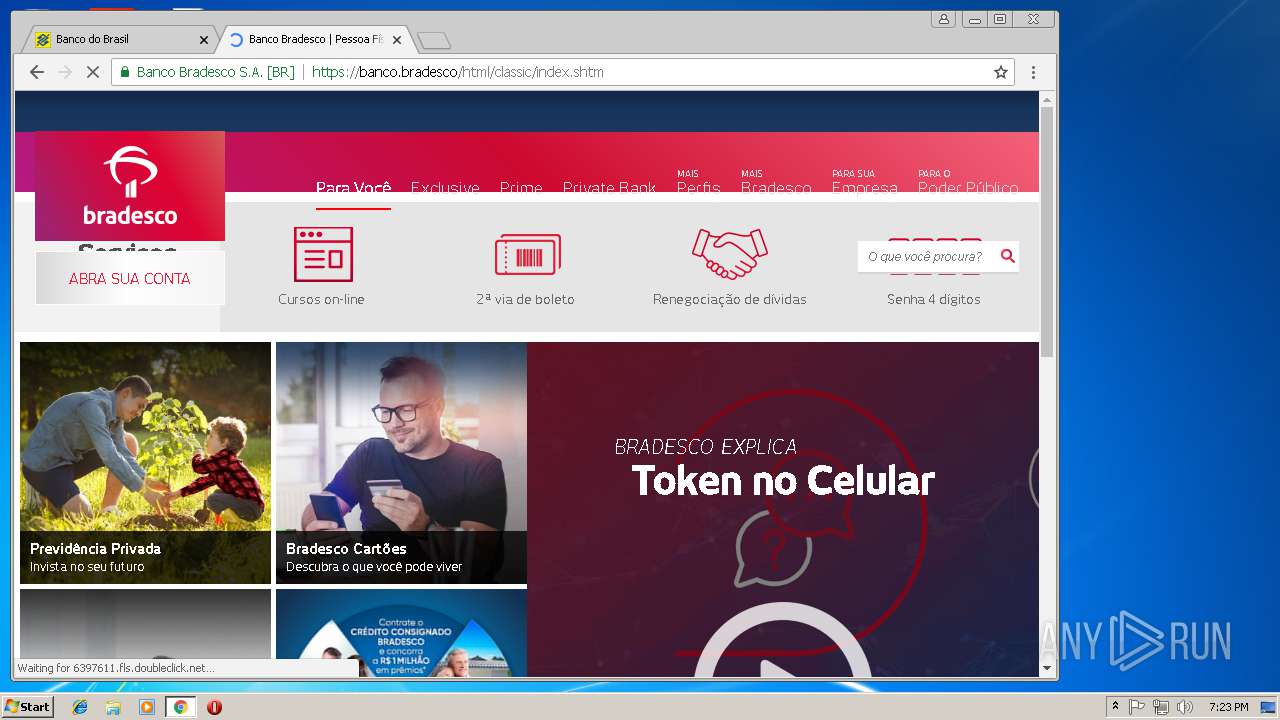
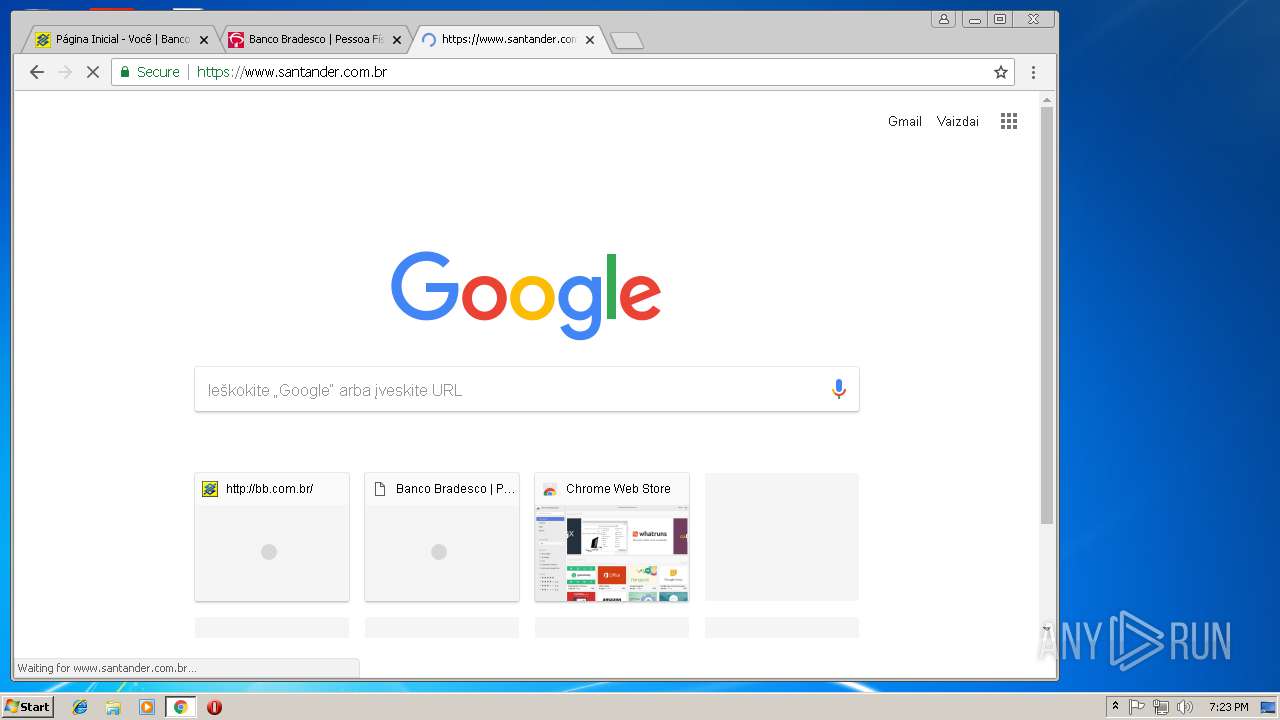
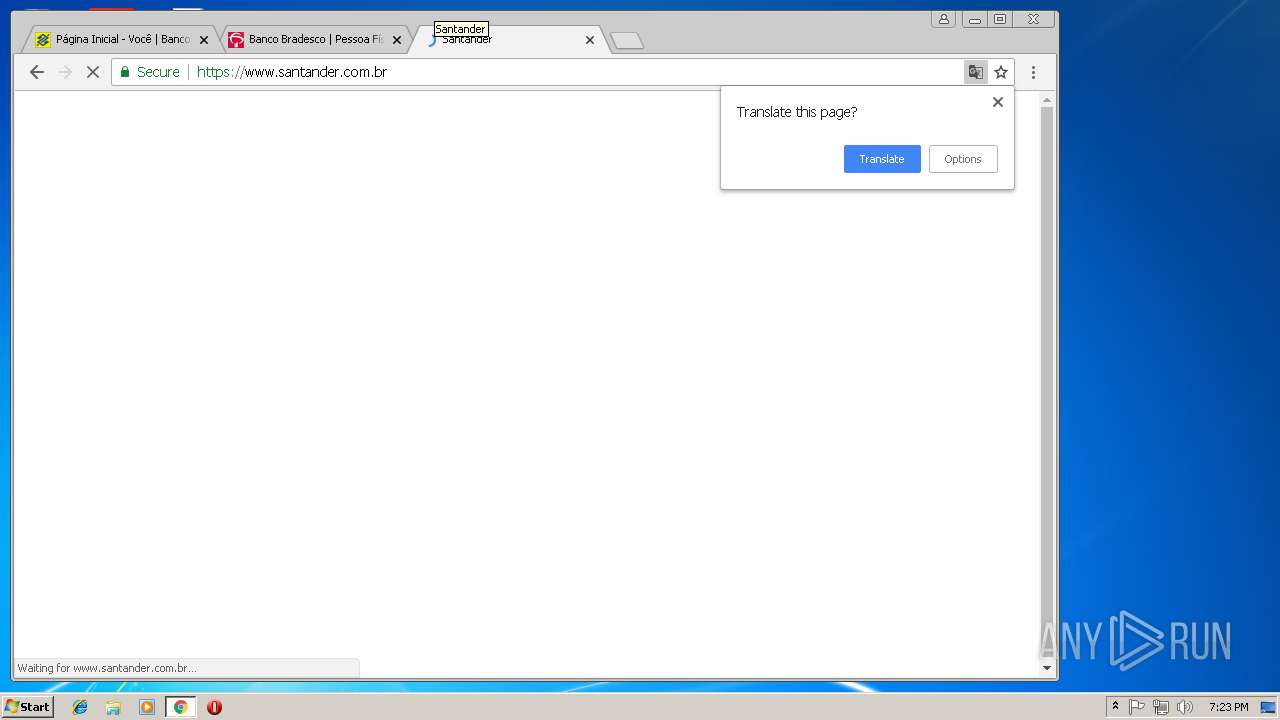
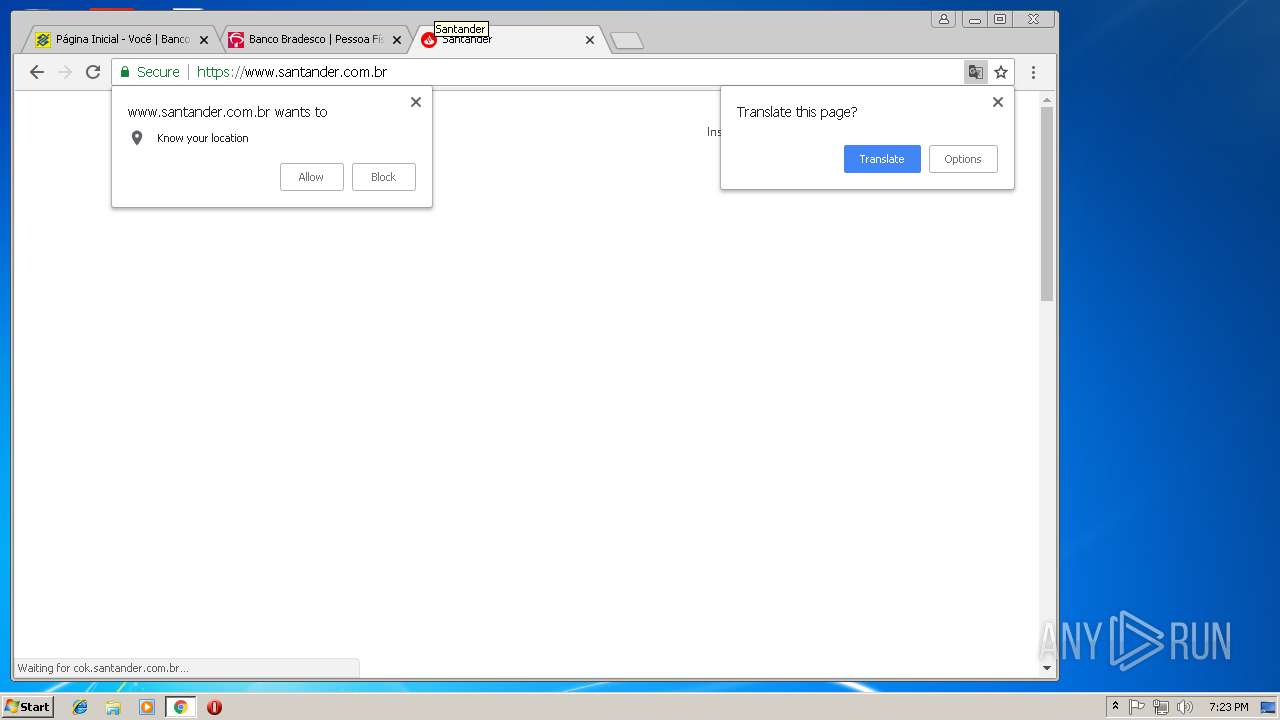
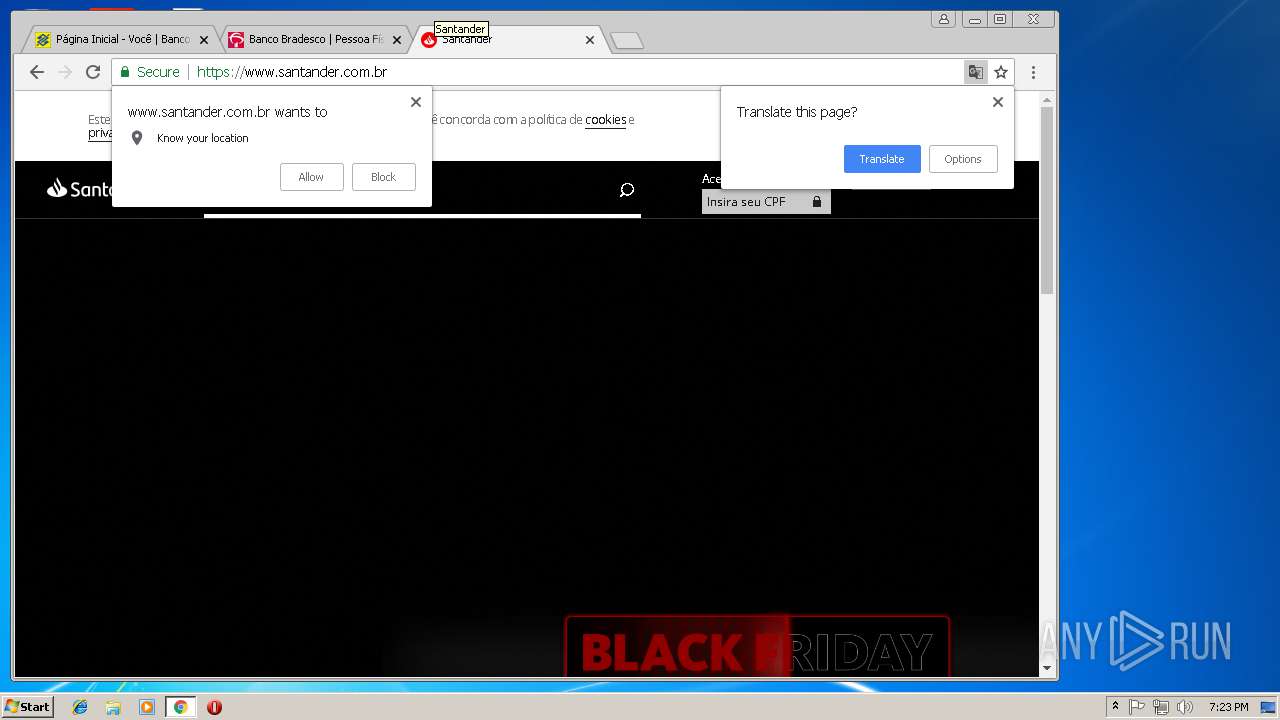
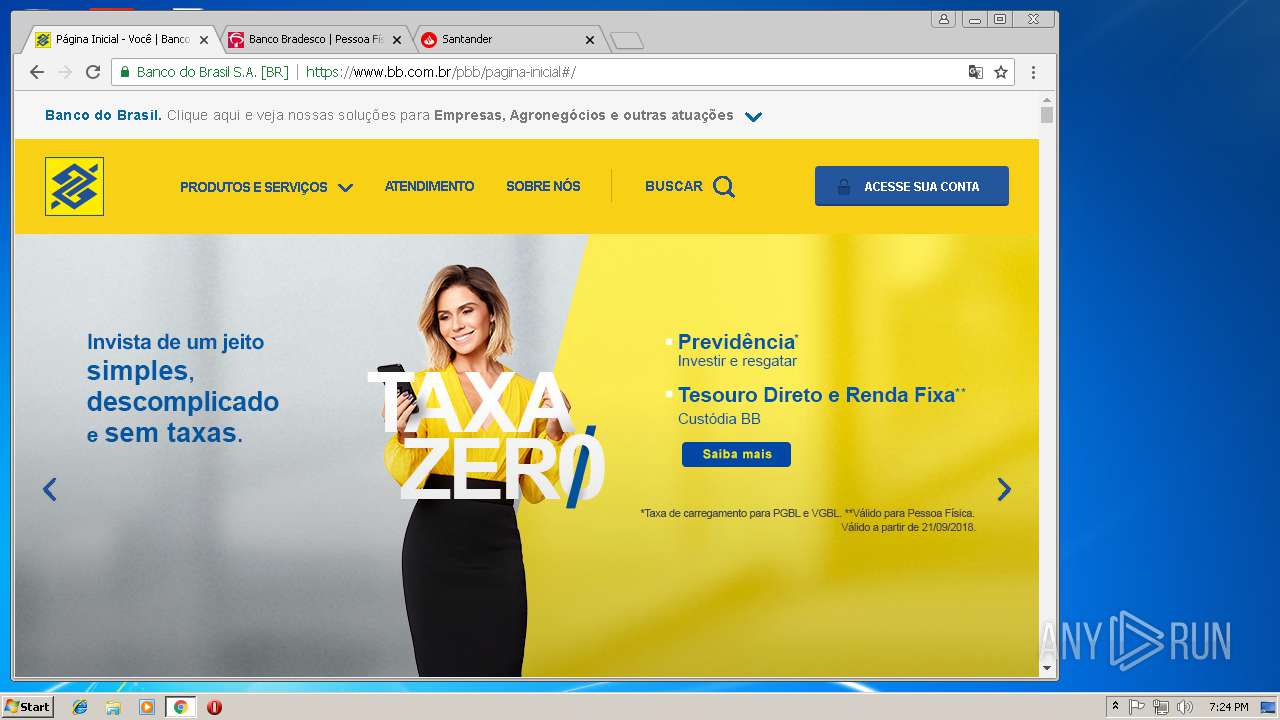
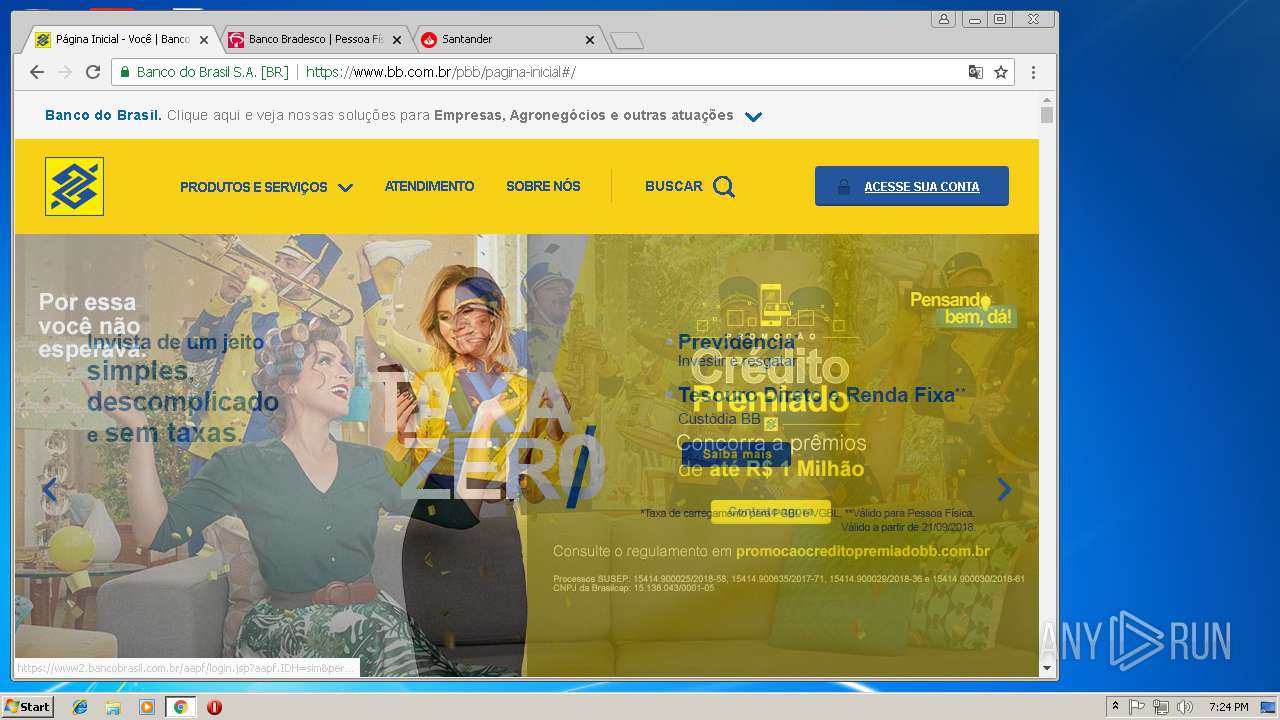
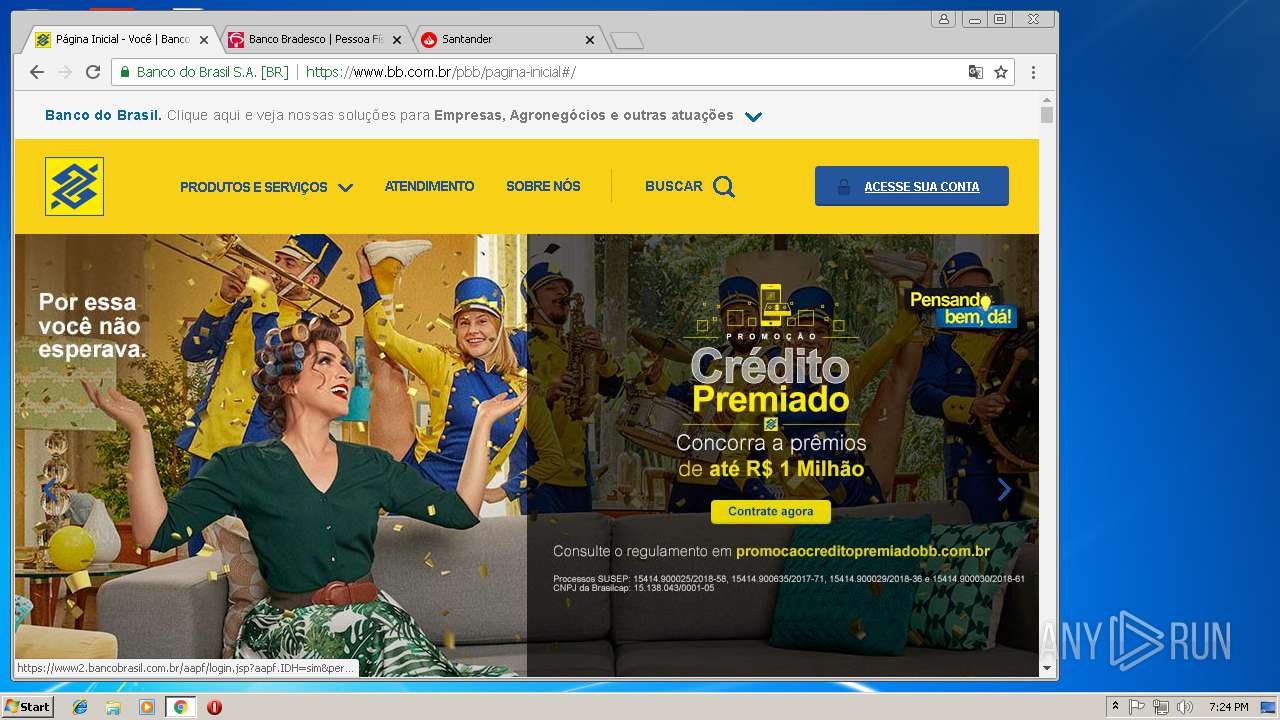
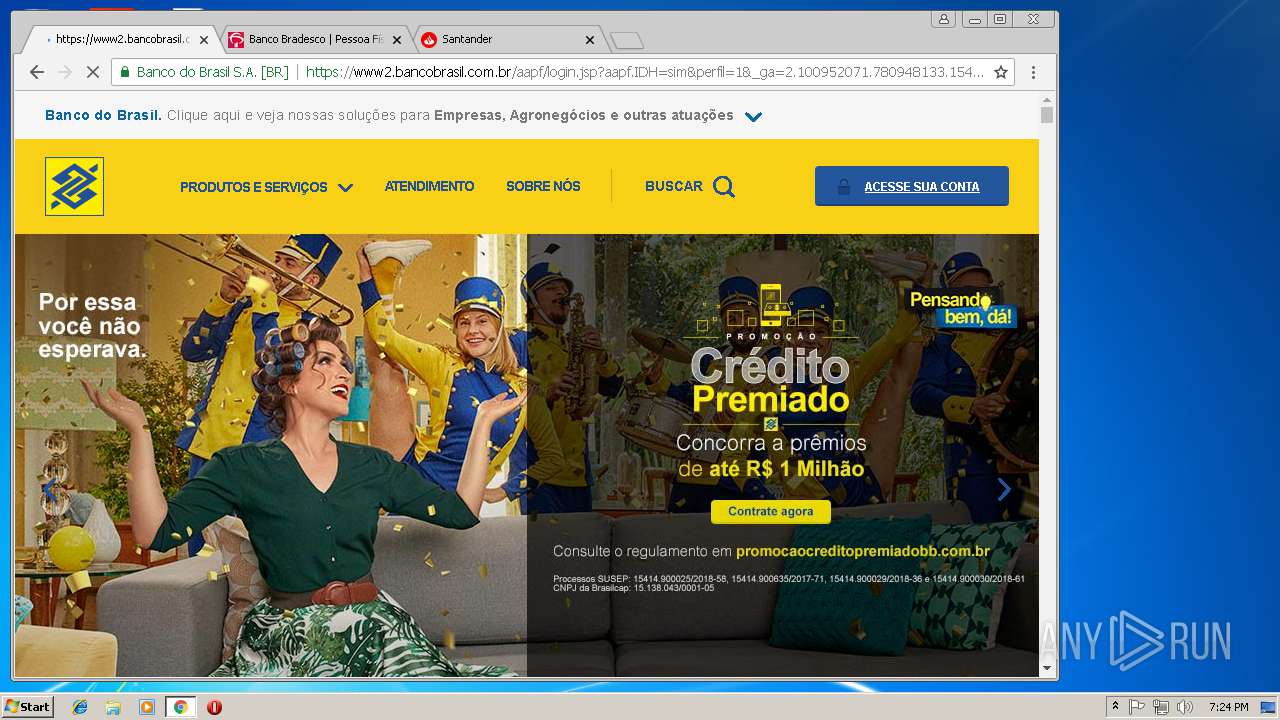
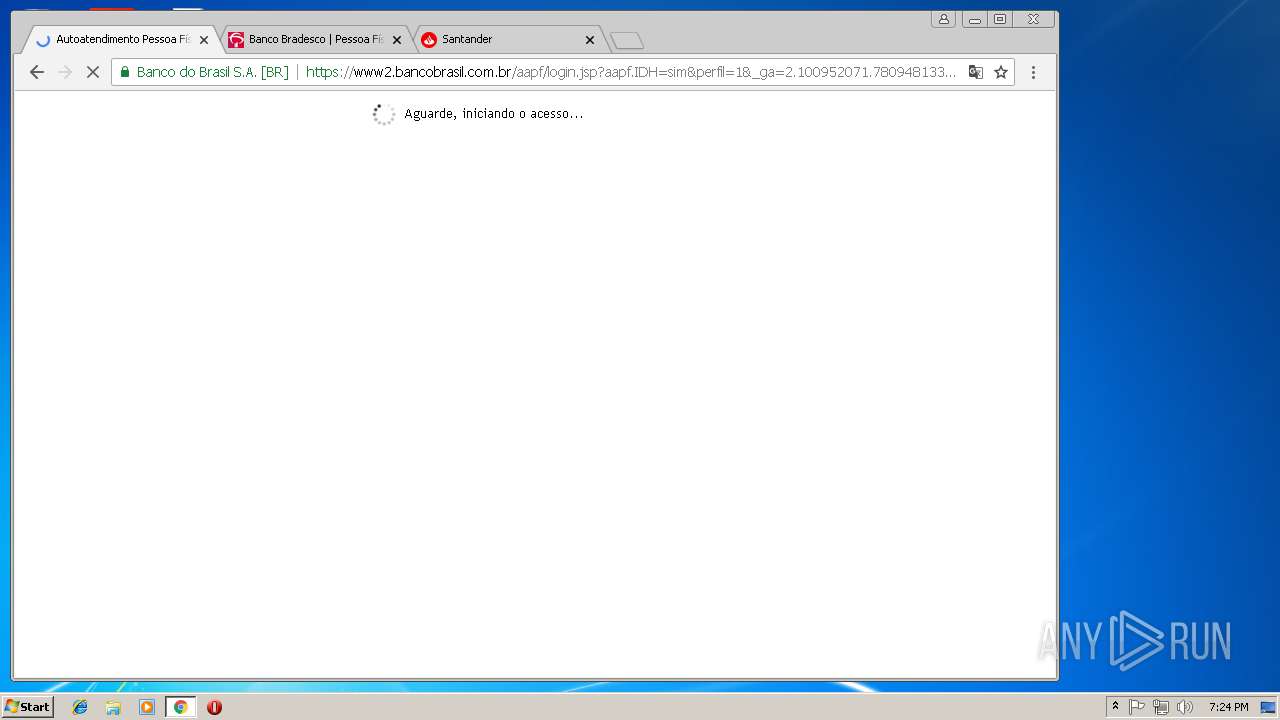
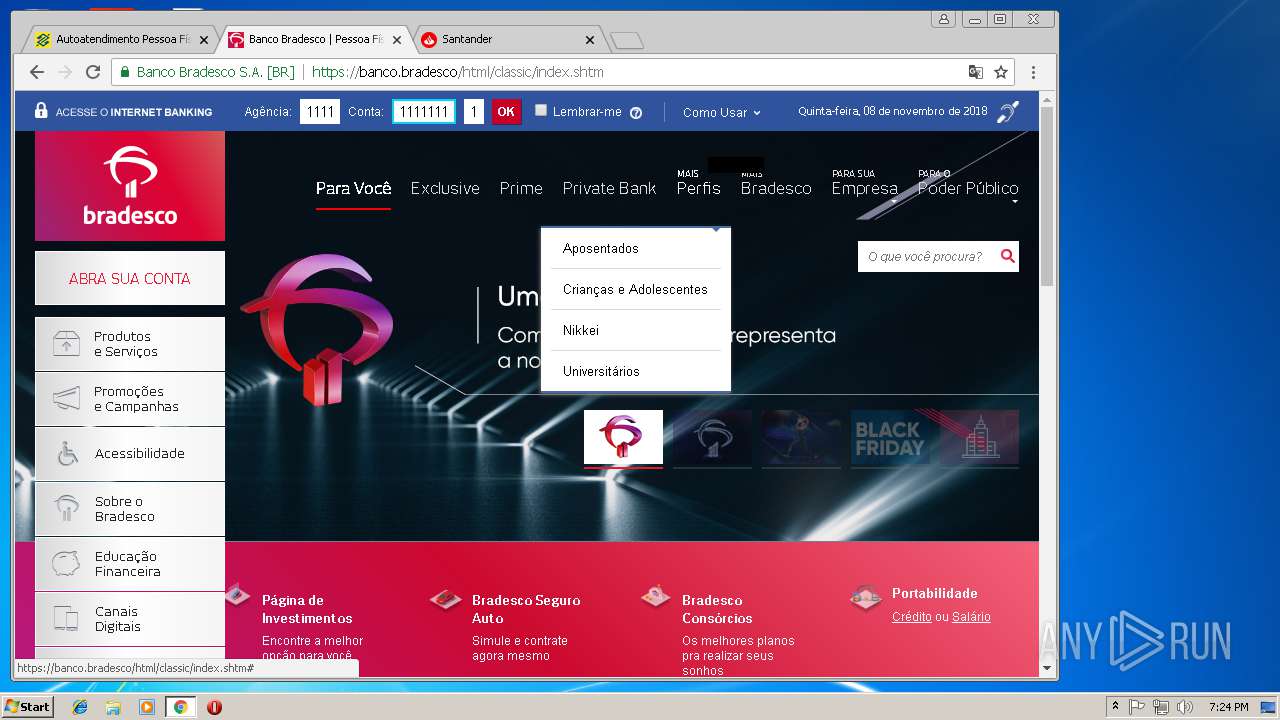
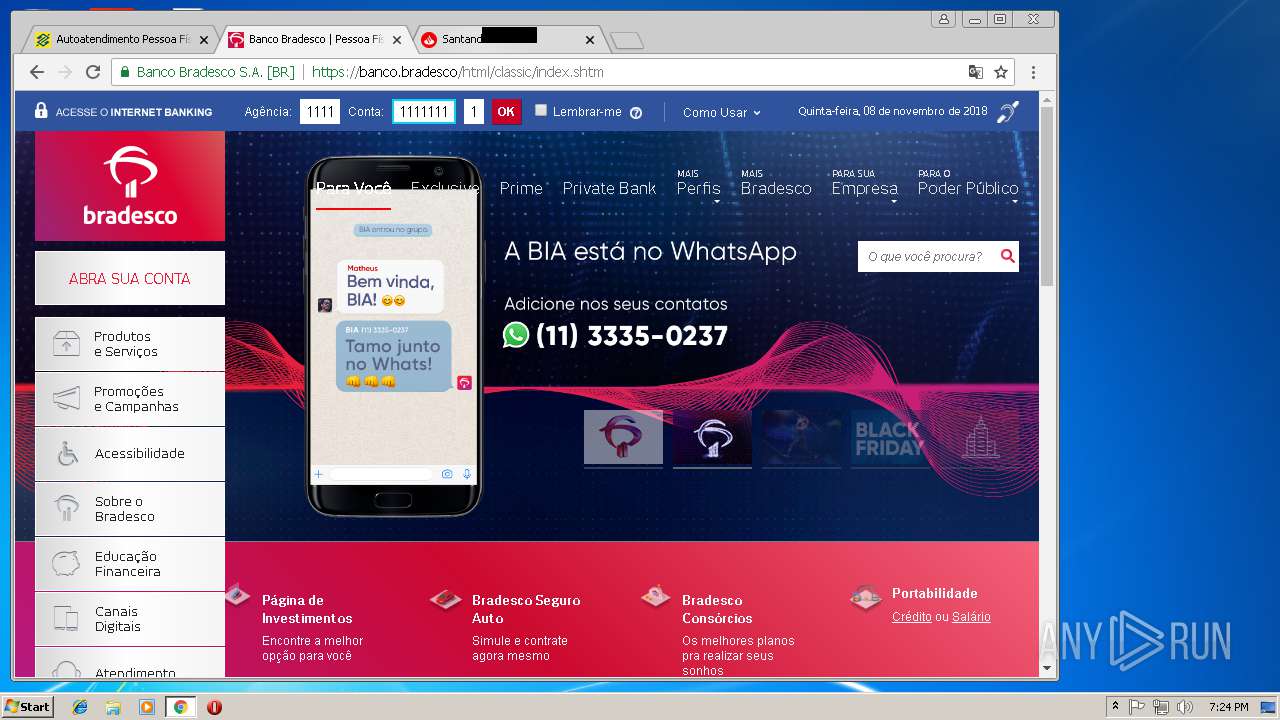
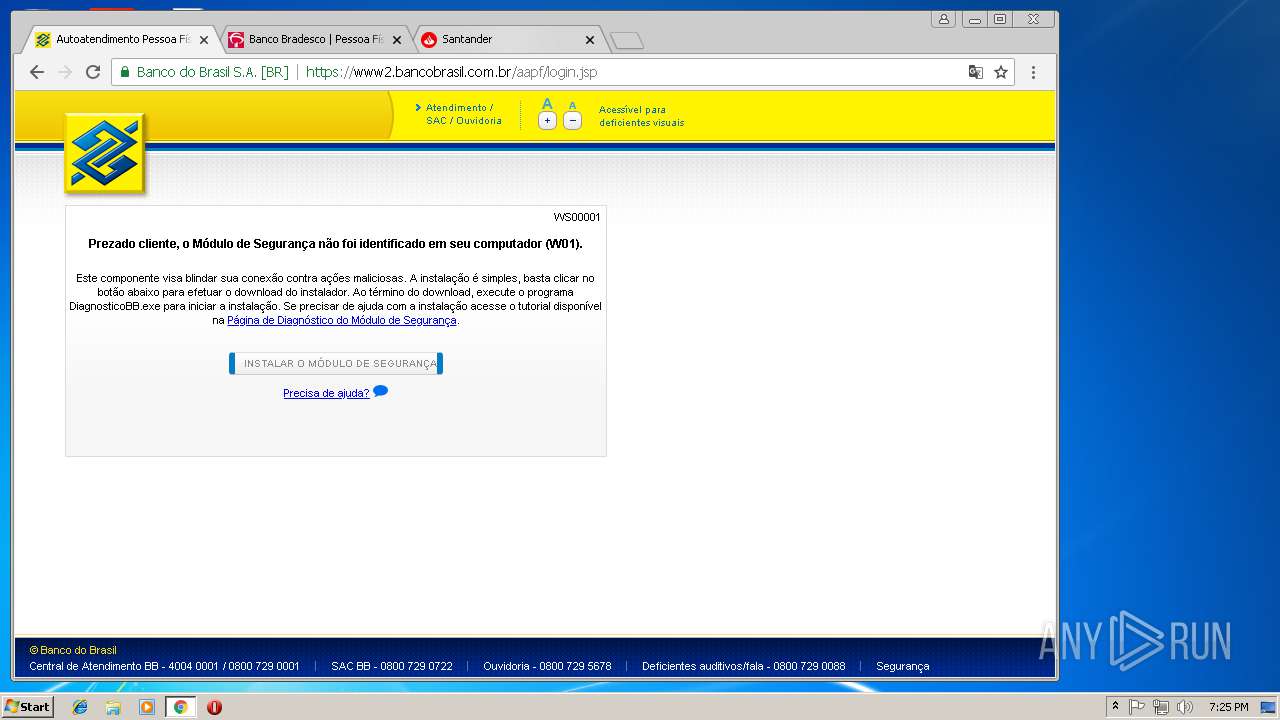
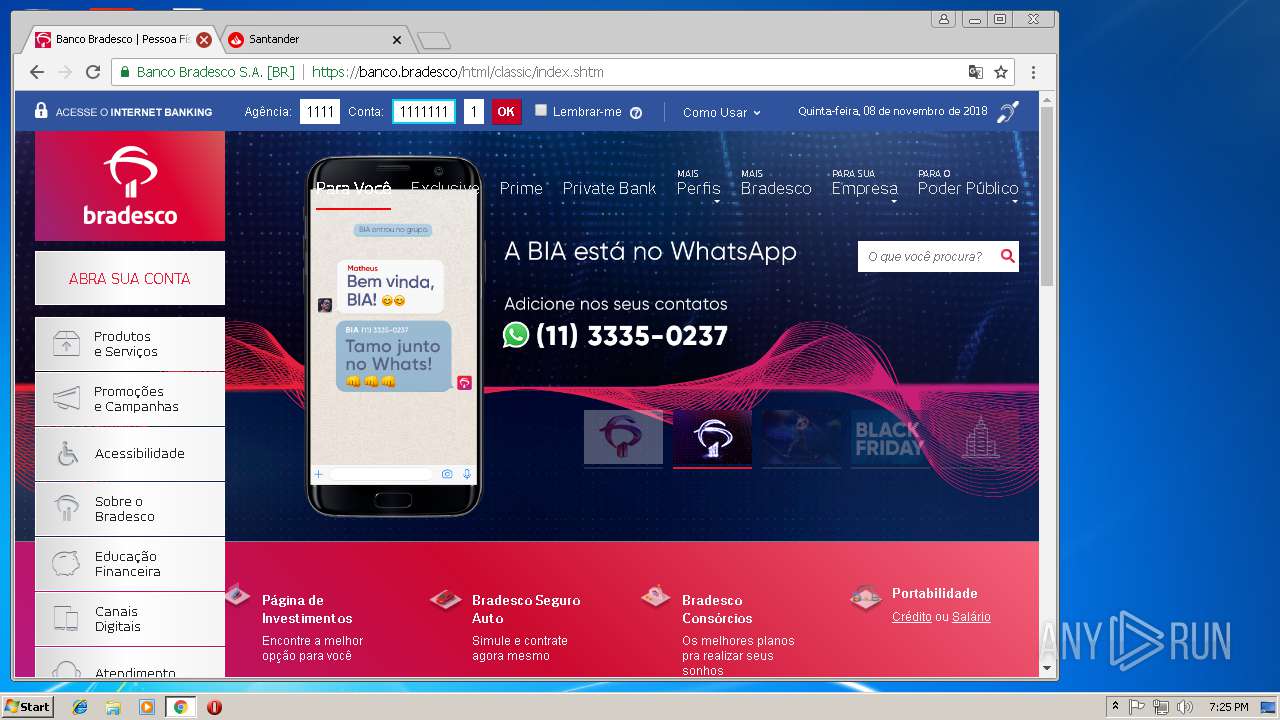
1308 | chrome.exe | GET | — | 170.66.11.10:80 | http://bb.com.br/ | BR | — | — | whitelisted |
3228 | chrome.exe | GET | 301 | 2.18.233.32:80 | http://www.itau.com.br/ | unknown | — | — | whitelisted |
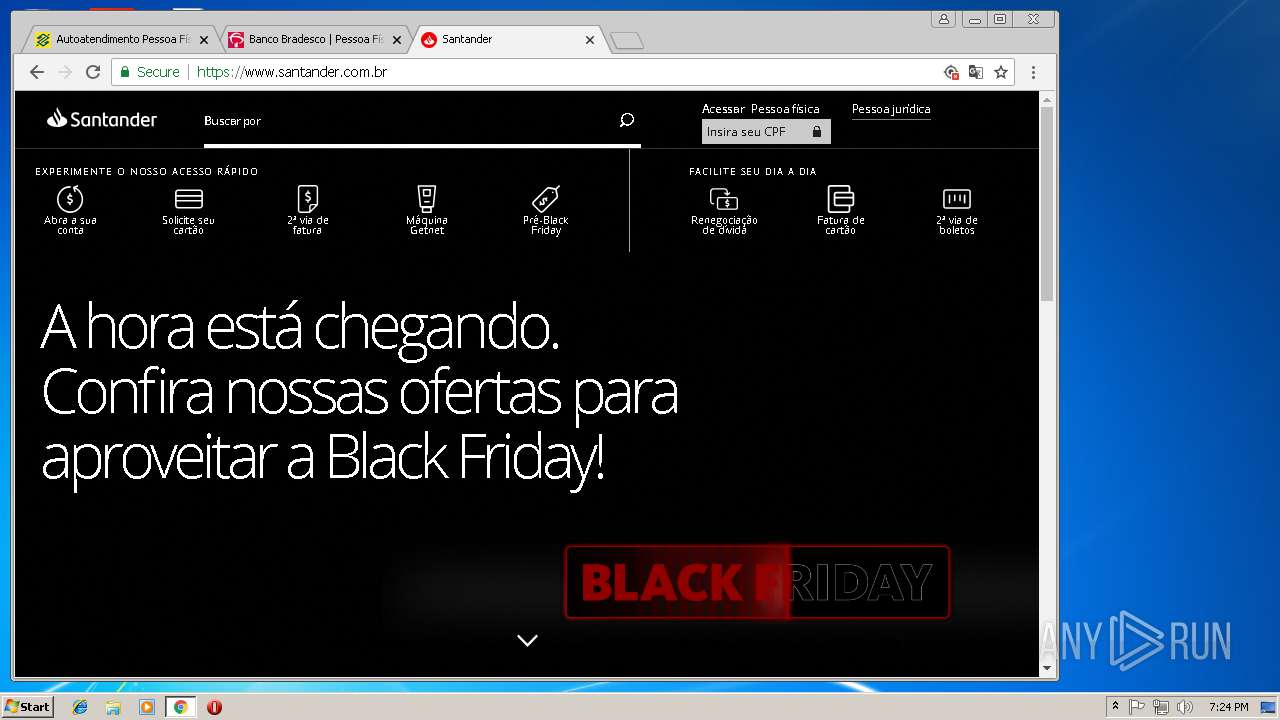
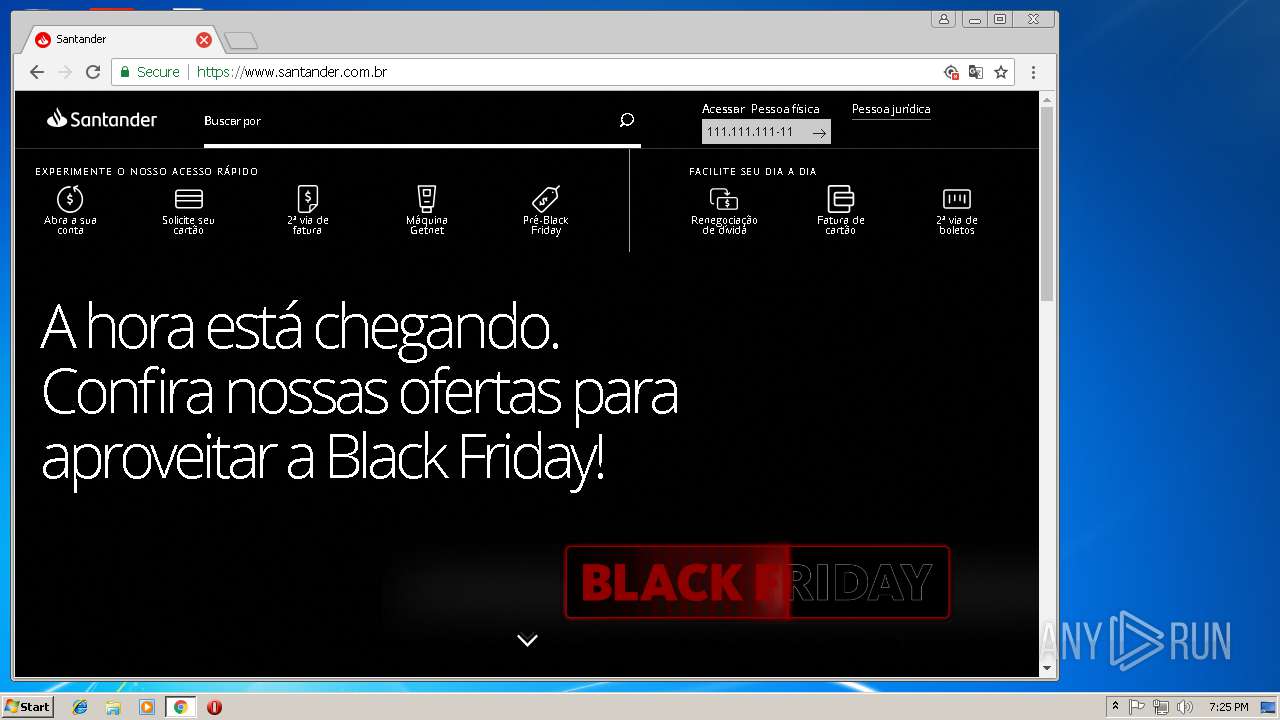
1308 | chrome.exe | GET | 301 | 2.19.62.24:80 | http://santander.com.br/ | unknown | — | — | whitelisted |
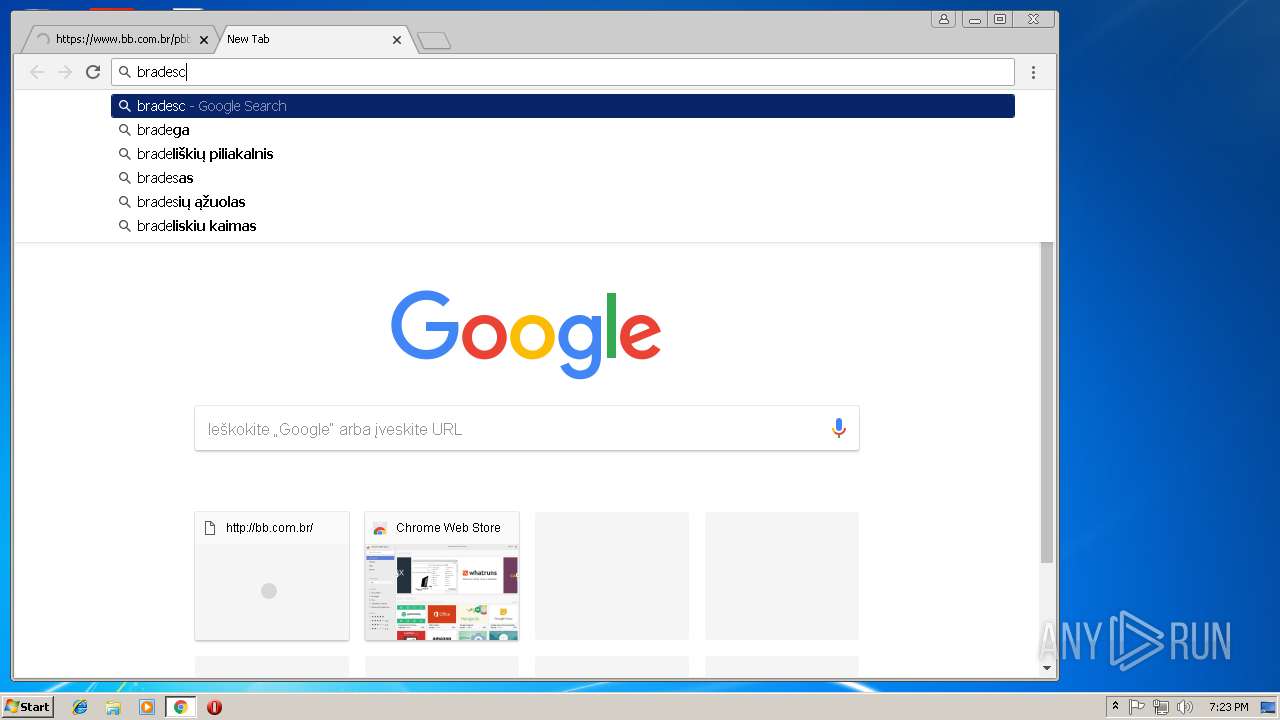
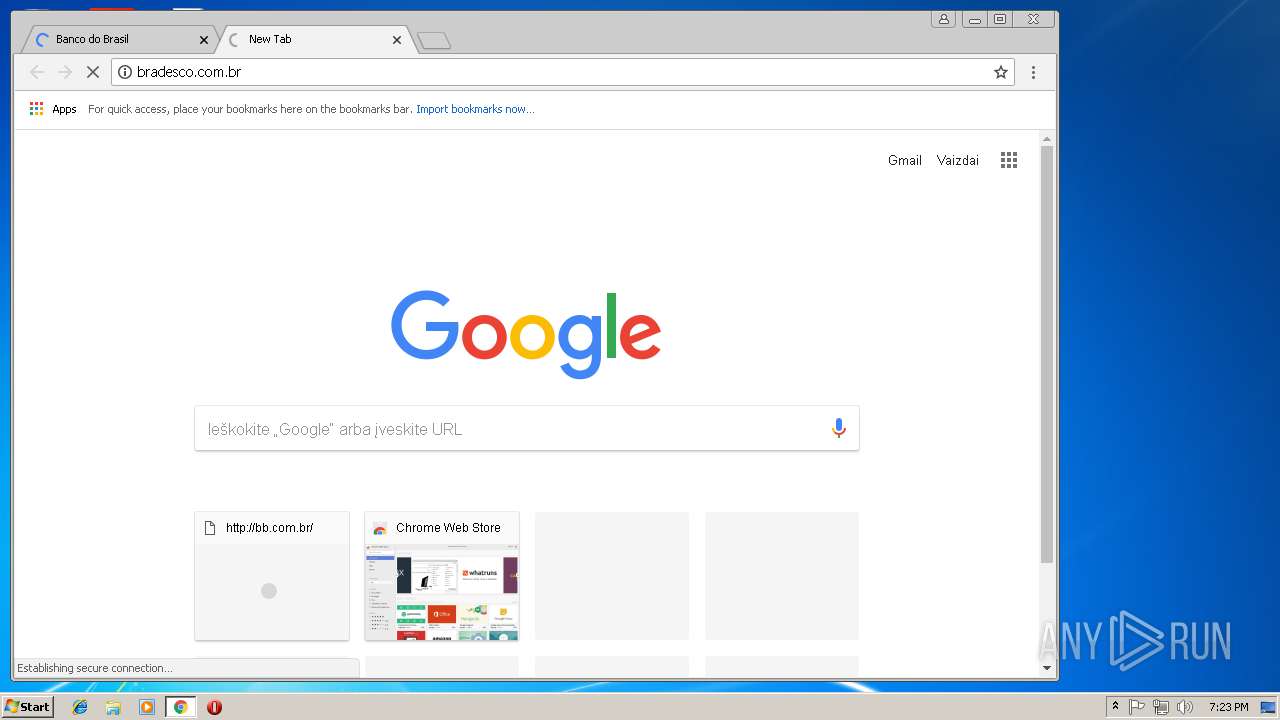
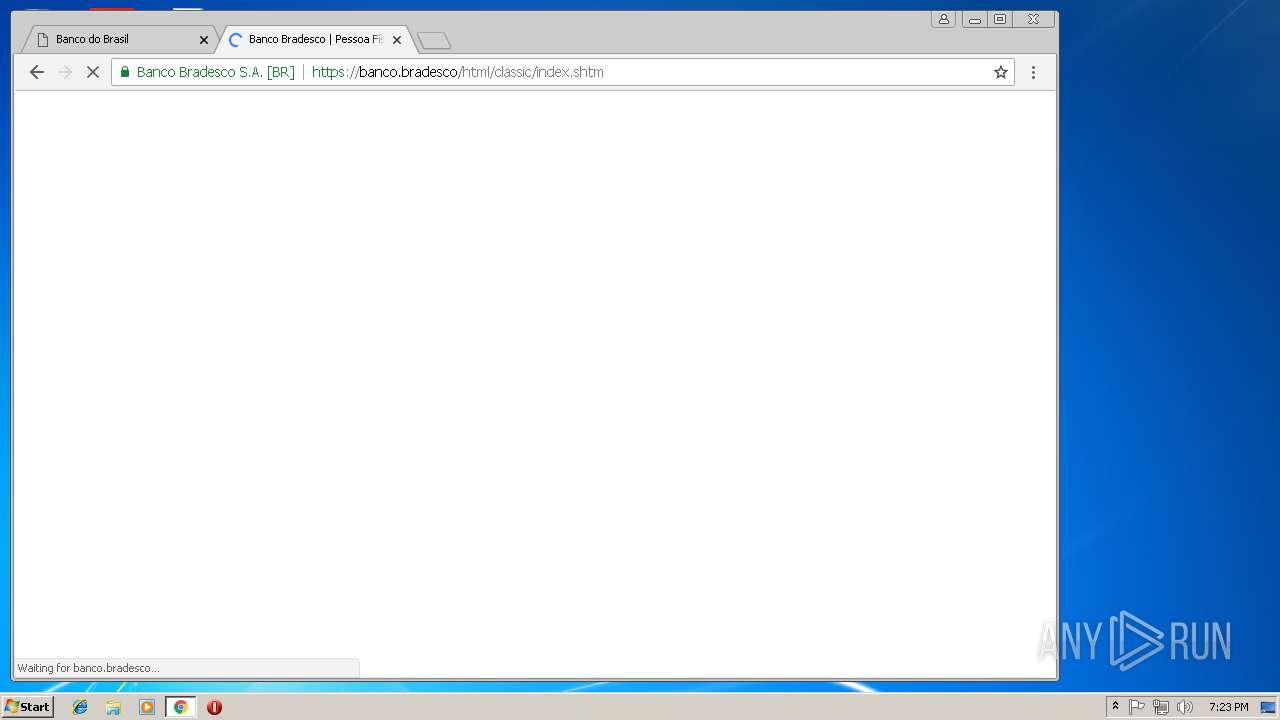
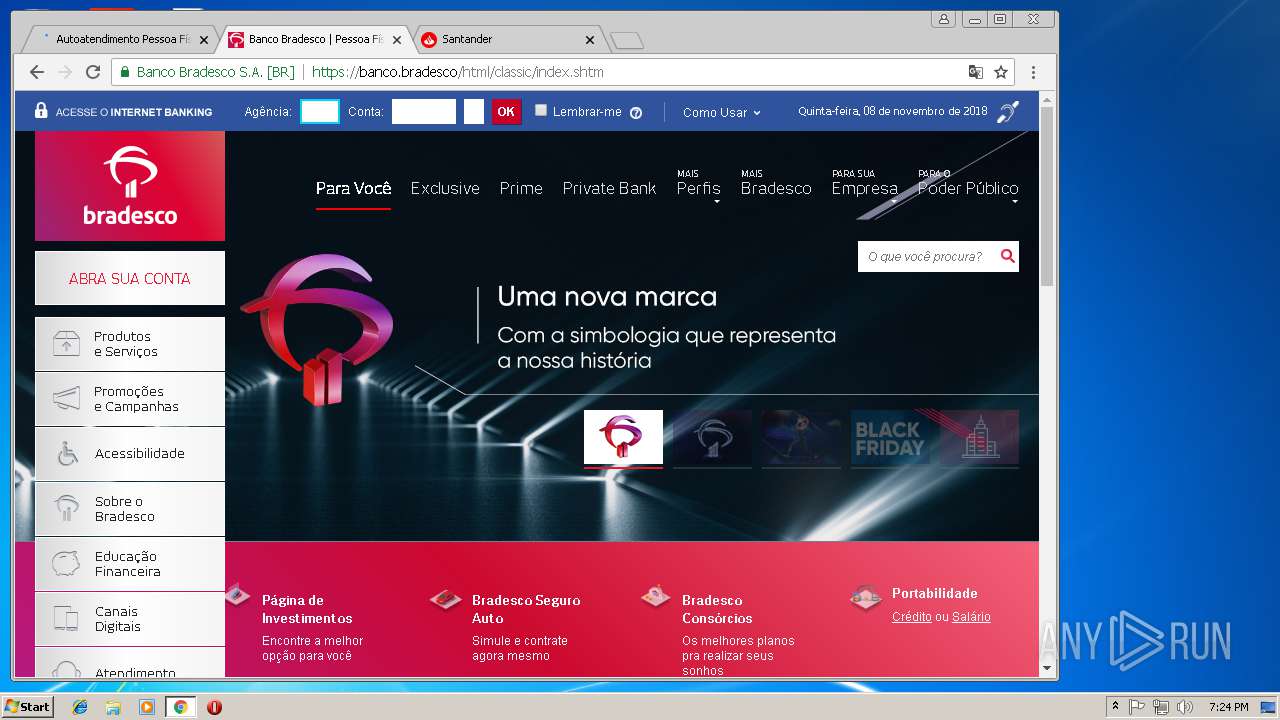
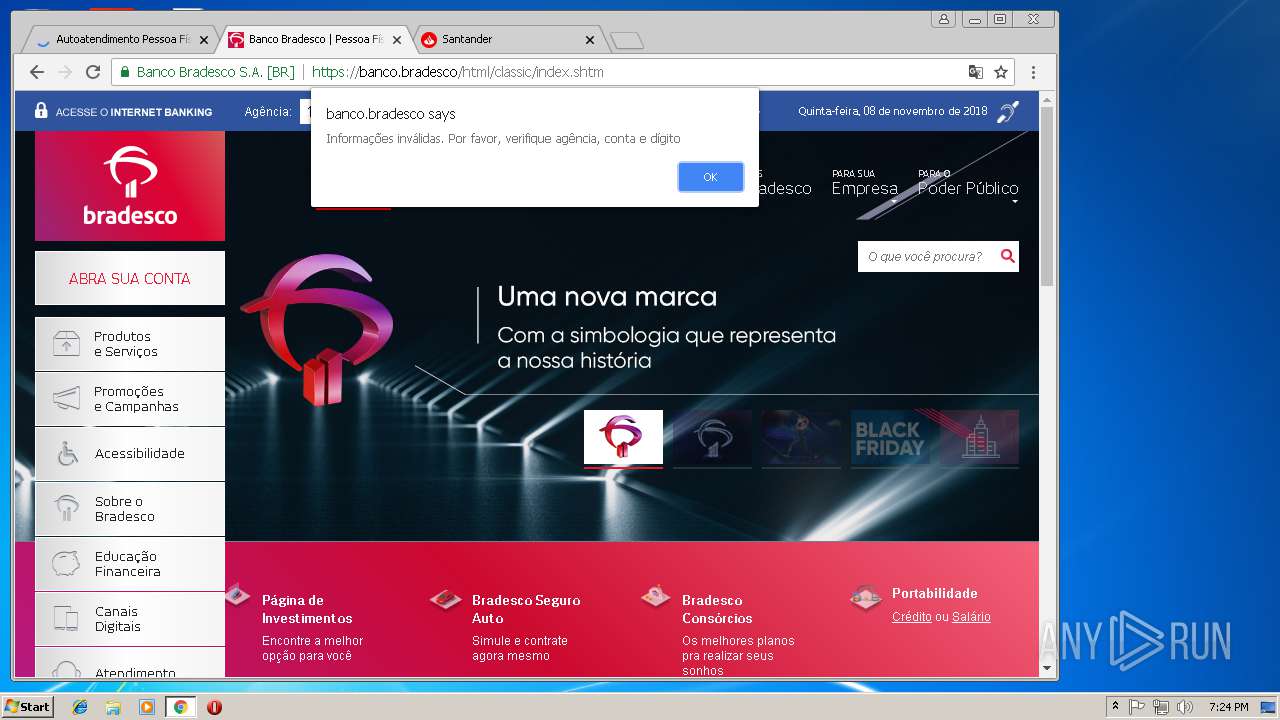
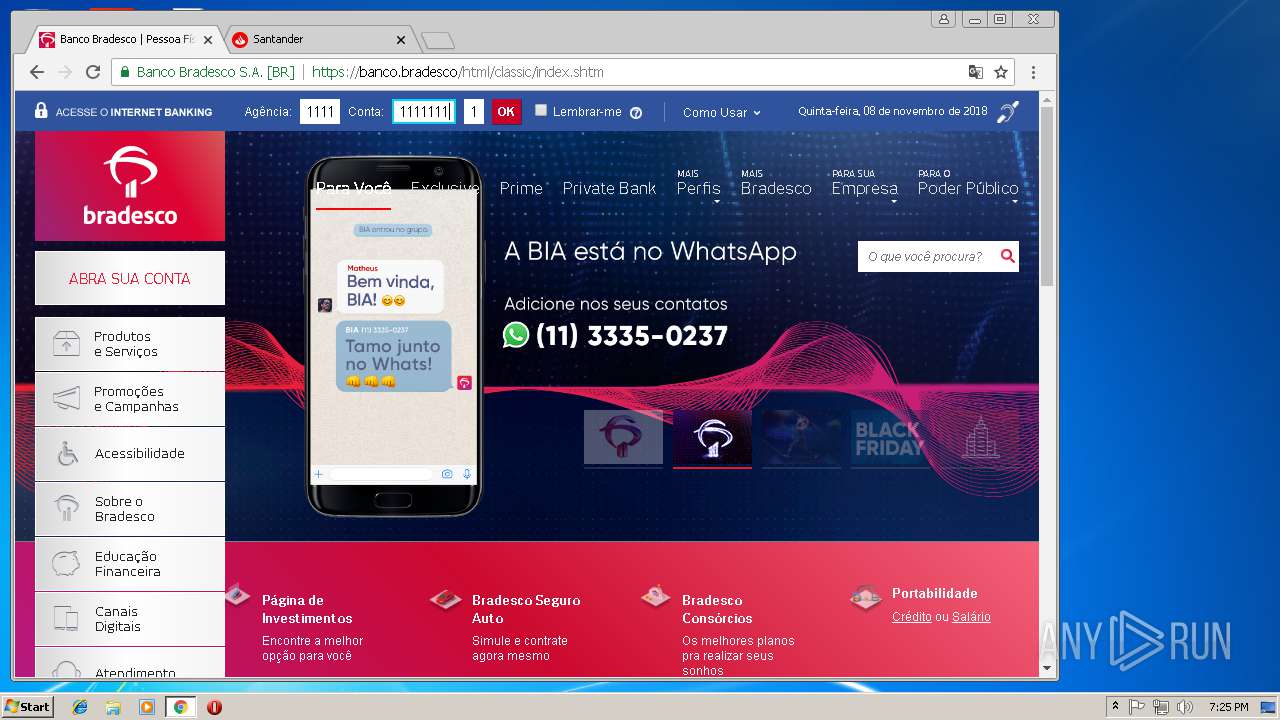
1308 | chrome.exe | GET | 301 | 2.18.232.58:80 | http://bradesco.com.br/ | unknown | — | — | whitelisted |
1308 | chrome.exe | GET | 301 | 2.18.232.151:80 | http://www.santander.com.br/ | unknown | — | — | whitelisted |
3228 | chrome.exe | GET | 301 | 2.18.233.32:80 | http://www.itau.com.br/computador/ | unknown | — | — | whitelisted |
3228 | chrome.exe | GET | 200 | 66.225.197.197:80 | http://crl4.digicert.com/DigiCertHighAssuranceEVRootCA.crl | US | der | 543 b | whitelisted |
1408 | itauaplicativo.exe | GET | 200 | 92.122.192.209:80 | http://crl.microsoft.com/pki/crl/products/microsoftrootcert.crl | DE | der | 781 b | whitelisted |
1308 | chrome.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBRJ9L2KGL92BpjF3kAtaDtxauTmhgQUPdNQpdagre7zSmAKZdMh1Pj41g8CEALnzTnH9dBbw2kNuKbE6tQ%3D | US | der | 471 b | whitelisted |
1308 | chrome.exe | GET | 200 | 13.107.4.50:80 | http://www.download.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab | US | compressed | 54.4 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3228 | chrome.exe | 172.217.168.13:443 | accounts.google.com | Google Inc. | US | whitelisted |
3228 | chrome.exe | 216.58.215.238:443 | apis.google.com | Google Inc. | US | whitelisted |
3228 | chrome.exe | 172.217.168.67:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
3228 | chrome.exe | 172.217.168.3:443 | www.google.de | Google Inc. | US | whitelisted |
3228 | chrome.exe | 172.217.168.4:443 | www.google.com | Google Inc. | US | whitelisted |
3228 | chrome.exe | 2.18.233.32:80 | www.itau.com.br | Akamai International B.V. | — | whitelisted |
1416 | svchost.exe | 74.118.139.159:443 | — | TeraSwitch Networks Inc. | US | malicious |
3228 | chrome.exe | 216.58.215.234:443 | safebrowsing.googleapis.com | Google Inc. | US | whitelisted |
3228 | chrome.exe | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
3228 | chrome.exe | 172.217.168.34:443 | www.googleadservices.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.google.de |
| whitelisted |
clientservices.googleapis.com |
| whitelisted |
www.gstatic.com |
| whitelisted |
safebrowsing.googleapis.com |
| whitelisted |
accounts.google.com |
| shared |
ssl.gstatic.com |
| whitelisted |
apis.google.com |
| whitelisted |
www.google.com |
| malicious |
www.google.lt |
| whitelisted |
www.itau.com.br |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1416 | svchost.exe | A Network Trojan was detected | MALWARE [PTsecurity] Trojan.Win32.Agent.qwgtfu (bkdr Zegost) connection |
1416 | svchost.exe | A Network Trojan was detected | MALWARE [PTsecurity] Trojan.Win32.Agent.qwgtfu (bkdr Zegost) connection |
1416 | svchost.exe | A Network Trojan was detected | MALWARE [PTsecurity] Trojan.Win32.Agent.qwgtfu (bkdr Zegost) connection |
1416 | svchost.exe | A Network Trojan was detected | MALWARE [PTsecurity] Trojan.Win32.Agent.qwgtfu (bkdr Zegost) connection |
1416 | svchost.exe | A Network Trojan was detected | MALWARE [PTsecurity] Trojan.Win32.Agent.qwgtfu (bkdr Zegost) connection |
1416 | svchost.exe | A Network Trojan was detected | MALWARE [PTsecurity] Trojan.Win32.Agent.qwgtfu (bkdr Zegost) connection |
1416 | svchost.exe | A Network Trojan was detected | MALWARE [PTsecurity] Trojan.Win32.Agent.qwgtfu (bkdr Zegost) connection |
1416 | svchost.exe | A Network Trojan was detected | MALWARE [PTsecurity] Trojan.Win32.Agent.qwgtfu (bkdr Zegost) connection |
1416 | svchost.exe | A Network Trojan was detected | MALWARE [PTsecurity] Trojan.Win32.Agent.qwgtfu (bkdr Zegost) connection |
Process | Message |
|---|---|
itauaplicativo.exe | %s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s |