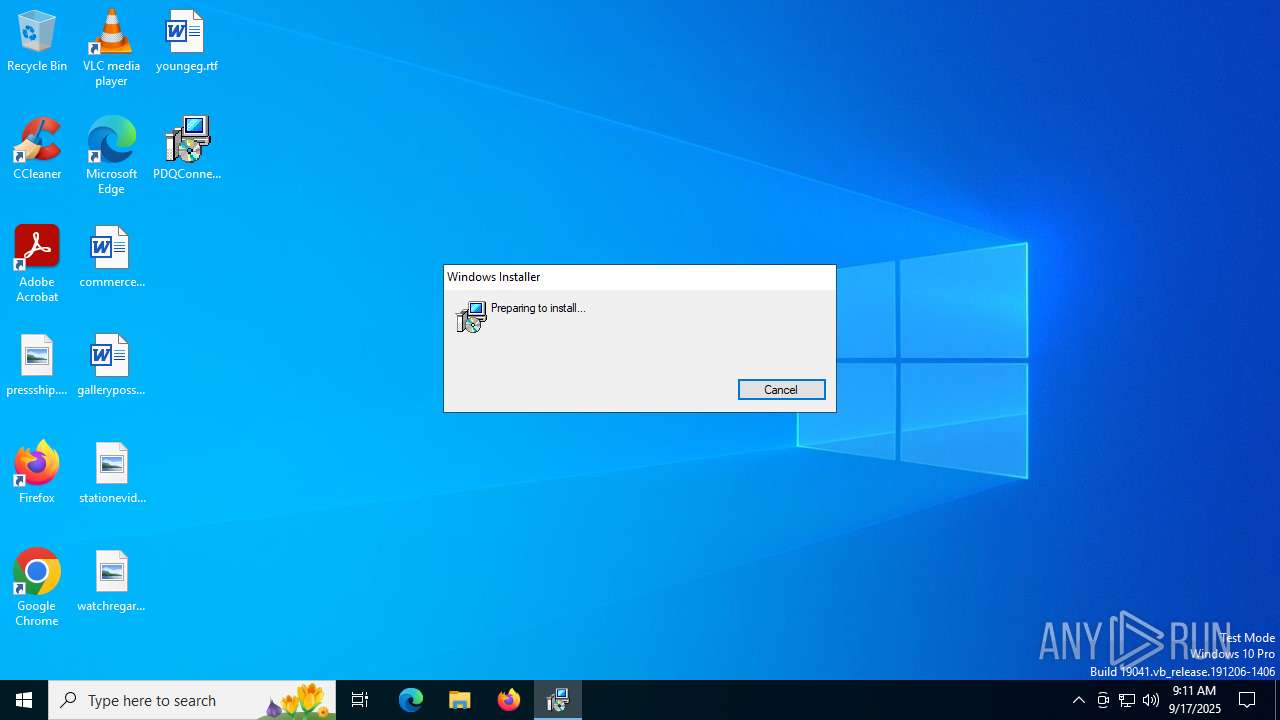
| File name: | PDQConnectAgent-5.8.18.msi |
| Full analysis: | https://app.any.run/tasks/85fcd89c-4a08-4074-86cf-a4012e1e150a |
| Verdict: | Malicious activity |
| Threats: | A loader is malicious software that infiltrates devices to deliver malicious payloads. This malware is capable of infecting victims’ computers, analyzing their system information, and installing other types of threats, such as trojans or stealers. Criminals usually deliver loaders through phishing emails and links by relying on social engineering to trick users into downloading and running their executables. Loaders employ advanced evasion and persistence tactics to avoid detection. |
| Analysis date: | September 17, 2025, 09:11:36 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-msi |
| File info: | Composite Document File V2 Document, Little Endian, Os: Windows, Version 6.2, MSI Installer, Code page: 1252, Title: Installation Database, Subject: PDQConnectAgent, Author: PDQ.com, Keywords: Installer, Comments: This installer database contains the logic and data required to install PDQConnectAgent., Template: x64;1033, Revision Number: {D0DE72FA-0CA1-4048-A672-61BD58D7BDD7}, Create Time/Date: Wed Jul 30 22:25:34 2025, Last Saved Time/Date: Wed Jul 30 22:25:34 2025, Number of Pages: 200, Number of Words: 2, Name of Creating Application: WiX Toolset (5.0.0.0), Security: 2 |
| MD5: | CBCF58588E8CC9F3EDAAC9493E6C3660 |
| SHA1: | 04DE6D0D817FB915BB47E27055EEBB3410741668 |
| SHA256: | 7C977B5C37CC80F59F8B96B860A83BA9D7B7FE5A07450500EB074A71C32185A7 |
| SSDEEP: | 98304:ALb75ziLEYLrv3Y++iJvRwVicWtkQbrg45D2CV7sxO13H5MzlgUYa7yOZfobvLZ7:EAO7tNW |
MALICIOUS
Changes powershell execution policy (Bypass)
- pdq-connect-agent.exe (PID: 6240)
Bypass execution policy to execute commands
- powershell.exe (PID: 4676)
- powershell.exe (PID: 1712)
- powershell.exe (PID: 188)
- powershell.exe (PID: 6664)
- powershell.exe (PID: 4724)
- powershell.exe (PID: 6980)
- powershell.exe (PID: 4512)
- powershell.exe (PID: 304)
- powershell.exe (PID: 2032)
- powershell.exe (PID: 5504)
- powershell.exe (PID: 4724)
- powershell.exe (PID: 6980)
- powershell.exe (PID: 5528)
- powershell.exe (PID: 1568)
- powershell.exe (PID: 6940)
- powershell.exe (PID: 6524)
- powershell.exe (PID: 6656)
- powershell.exe (PID: 6140)
- powershell.exe (PID: 4048)
- powershell.exe (PID: 6808)
- powershell.exe (PID: 4400)
- powershell.exe (PID: 3392)
- powershell.exe (PID: 5988)
- powershell.exe (PID: 2460)
- powershell.exe (PID: 4916)
- powershell.exe (PID: 4688)
- powershell.exe (PID: 4156)
- powershell.exe (PID: 6128)
- powershell.exe (PID: 4892)
- powershell.exe (PID: 5532)
Collects BIOS Properties (Win32_BIOS) (SCRIPT)
- powershell.exe (PID: 6664)
- powershell.exe (PID: 5504)
- powershell.exe (PID: 6524)
- powershell.exe (PID: 3392)
- powershell.exe (PID: 6128)
SUSPICIOUS
Executes as Windows Service
- VSSVC.exe (PID: 3504)
- pdq-connect-agent.exe (PID: 4944)
- pdq-connect-updater.exe (PID: 3628)
- pdq-connect-agent.exe (PID: 6240)
Uses RUNDLL32.EXE to load library
- msiexec.exe (PID: 5808)
- msiexec.exe (PID: 2148)
- msiexec.exe (PID: 2312)
- msiexec.exe (PID: 1652)
Executable content was dropped or overwritten
- rundll32.exe (PID: 2632)
- rundll32.exe (PID: 3768)
- rundll32.exe (PID: 2032)
- rundll32.exe (PID: 4788)
- rundll32.exe (PID: 6648)
- pdq-connect-agent.exe (PID: 4944)
- rundll32.exe (PID: 1568)
- rundll32.exe (PID: 4768)
- rundll32.exe (PID: 5172)
- rundll32.exe (PID: 4684)
- rundll32.exe (PID: 2064)
- rundll32.exe (PID: 4936)
- rundll32.exe (PID: 4844)
- rundll32.exe (PID: 2972)
- rundll32.exe (PID: 7164)
Reads the Windows owner or organization settings
- msiexec.exe (PID: 684)
Application launched itself
- msiexec.exe (PID: 684)
Windows service management via SC.EXE
- sc.exe (PID: 5764)
- sc.exe (PID: 6648)
Starts SC.EXE for service management
- rundll32.exe (PID: 6648)
- rundll32.exe (PID: 7164)
PDQConnect is probably used for system patching and software deployment
- sc.exe (PID: 5764)
- sc.exe (PID: 6648)
The process hide an interactive prompt from the user
- pdq-connect-agent.exe (PID: 6240)
The process hides Powershell's copyright startup banner
- pdq-connect-agent.exe (PID: 6240)
Creates new GUID (POWERSHELL)
- powershell.exe (PID: 4676)
- powershell.exe (PID: 4512)
- powershell.exe (PID: 5528)
- powershell.exe (PID: 6808)
- powershell.exe (PID: 4916)
The process bypasses the loading of PowerShell profile settings
- pdq-connect-agent.exe (PID: 6240)
Starts POWERSHELL.EXE for commands execution
- pdq-connect-agent.exe (PID: 6240)
Enumerates operating system information (Win32_OperatingSystem) (SCRIPT)
- powershell.exe (PID: 188)
- powershell.exe (PID: 2032)
- powershell.exe (PID: 6940)
- powershell.exe (PID: 4048)
- powershell.exe (PID: 4156)
INFO
Reads security settings of Internet Explorer
- msiexec.exe (PID: 7140)
Reads the software policy settings
- msiexec.exe (PID: 7140)
- msiexec.exe (PID: 684)
- pdq-connect-agent.exe (PID: 4944)
- pdq-connect-updater.exe (PID: 3628)
- pdq-connect-agent.exe (PID: 6240)
- slui.exe (PID: 6352)
Creates files or folders in the user directory
- msiexec.exe (PID: 7140)
An automatically generated document
- msiexec.exe (PID: 7140)
Checks proxy server information
- msiexec.exe (PID: 7140)
- slui.exe (PID: 6352)
Checks supported languages
- msiexec.exe (PID: 684)
- msiexec.exe (PID: 5808)
- pdq-connect-agent.exe (PID: 4944)
- msiexec.exe (PID: 2148)
- msiexec.exe (PID: 1652)
- pdq-connect-updater.exe (PID: 3628)
- msiexec.exe (PID: 2312)
- pdq-connect-agent.exe (PID: 6240)
Reads the machine GUID from the registry
- msiexec.exe (PID: 684)
- pdq-connect-agent.exe (PID: 4944)
- pdq-connect-updater.exe (PID: 3628)
- pdq-connect-agent.exe (PID: 6240)
Manages system restore points
- SrTasks.exe (PID: 2116)
Executable content was dropped or overwritten
- msiexec.exe (PID: 684)
Create files in a temporary directory
- rundll32.exe (PID: 2632)
- rundll32.exe (PID: 3768)
The sample compiled with english language support
- msiexec.exe (PID: 684)
PDQCONNECT has been detected
- msiexec.exe (PID: 2148)
- rundll32.exe (PID: 6648)
- pdq-connect-agent.exe (PID: 4944)
- msiexec.exe (PID: 1652)
- rundll32.exe (PID: 7164)
Creates files in the program directory
- rundll32.exe (PID: 4788)
- pdq-connect-agent.exe (PID: 4944)
- msiexec.exe (PID: 1148)
- msiexec.exe (PID: 3964)
Creates a software uninstall entry
- msiexec.exe (PID: 684)
Application based on Rust
- pdq-connect-updater.exe (PID: 3628)
Uses string replace method (POWERSHELL)
- powershell.exe (PID: 4676)
- powershell.exe (PID: 4512)
- powershell.exe (PID: 5528)
- powershell.exe (PID: 6808)
- powershell.exe (PID: 4916)
Process checks computer location settings
- pdq-connect-agent.exe (PID: 6240)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .msi | | | Microsoft Windows Installer (98.5) |
|---|---|---|
| .msi | | | Microsoft Installer (100) |
EXIF
FlashPix
| CodePage: | Windows Latin 1 (Western European) |
|---|---|
| Title: | Installation Database |
| Subject: | PDQConnectAgent |
| Author: | PDQ.com |
| Keywords: | Installer |
| Comments: | This installer database contains the logic and data required to install PDQConnectAgent. |
| Template: | x64;1033 |
| RevisionNumber: | {D0DE72FA-0CA1-4048-A672-61BD58D7BDD7} |
| CreateDate: | 2025:07:30 22:25:34 |
| ModifyDate: | 2025:07:30 22:25:34 |
| Pages: | 200 |
| Words: | 2 |
| Software: | WiX Toolset (5.0.0.0) |
| Security: | Read-only recommended |
Total processes
223
Monitored processes
93
Malicious processes
3
Suspicious processes
16
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 188 | "powershell.exe" -NoLogo -NonInteractive -NoProfile -ExecutionPolicy Bypass -Command - | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | pdq-connect-agent.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows PowerShell Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 304 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | powershell.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 304 | "powershell.exe" -NoLogo -NonInteractive -NoProfile -ExecutionPolicy Bypass -Command - | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | pdq-connect-agent.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows PowerShell Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 684 | C:\WINDOWS\system32\msiexec.exe /V | C:\Windows\System32\msiexec.exe | services.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows® installer Version: 5.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1096 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | powershell.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1148 | "msiexec" /i C:\ProgramData\PDQ\PDQConnectAgent\Updates\PDQConnectUpdater-5.6.16.msi /quiet /qn /norestart /L*V C:\ProgramData\PDQ\PDQConnectAgent\Updates\updater_install.log | C:\Windows\System32\msiexec.exe | — | pdq-connect-agent.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows® installer Exit code: 0 Version: 5.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1180 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | powershell.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1568 | rundll32.exe "C:\WINDOWS\Installer\MSI452B.tmp",zzzzInvokeManagedCustomActionOutOfProc SfxCA_1656109 77 pdqconnectupdater-setup!pdqconnectupdater_setup.CustomActions.CreateEventSource | C:\Windows\System32\rundll32.exe | msiexec.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows host process (Rundll32) Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1568 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | powershell.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1568 | "powershell.exe" -NoLogo -NonInteractive -NoProfile -ExecutionPolicy Bypass -Command - | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | pdq-connect-agent.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows PowerShell Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
159 893
Read events
159 272
Write events
462
Delete events
159
Modification events
| (PID) Process: | (684) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\SPP |
| Operation: | write | Name: | LastIndex |
Value: 11 | |||
| (PID) Process: | (684) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SPP |
| Operation: | write | Name: | SppGatherWriterMetadata (Enter) |
Value: 4800000000000000773CF61AB327DC01AC020000D8010000D30700000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (3504) VSSVC.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\Registry Writer |
| Operation: | write | Name: | IDENTIFY (Enter) |
Value: 480000000000000051C1FF1AB327DC01B00D0000440A0000E80300000100000001000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (3504) VSSVC.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\Shadow Copy Optimization Writer |
| Operation: | write | Name: | IDENTIFY (Enter) |
Value: 48000000000000009A24021BB327DC01B00D000084140000E80300000100000001000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (3504) VSSVC.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\COM+ REGDB Writer |
| Operation: | write | Name: | IDENTIFY (Enter) |
Value: 48000000000000009A24021BB327DC01B00D0000240A0000E80300000100000001000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (3504) VSSVC.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\ASR Writer |
| Operation: | write | Name: | IDENTIFY (Enter) |
Value: 48000000000000009A24021BB327DC01B00D0000681A0000E80300000100000001000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (3504) VSSVC.exe | Key: | HKEY_LOCAL_MACHINE\BCD00000000\Objects\{9dea862c-5cdd-4e70-acc1-f32b344d4795}\Elements\11000001 |
| Operation: | delete key | Name: | (default) |
Value: | |||
| (PID) Process: | (3504) VSSVC.exe | Key: | HKEY_LOCAL_MACHINE\BCD00000000\Objects\{9dea862c-5cdd-4e70-acc1-f32b344d4795}\Elements\11000001 |
| Operation: | write | Name: | Element |
Value: 0000000000000000000000000000000006000000000000004800000000000000715E5C2FA985EB1190A89A9B763584210000000000000000745E5C2FA985EB1190A89A9B7635842100000000000000000000000000000000 | |||
| (PID) Process: | (3504) VSSVC.exe | Key: | HKEY_LOCAL_MACHINE\BCD00000000\Objects\{9dea862c-5cdd-4e70-acc1-f32b344d4795}\Elements\12000002 |
| Operation: | delete key | Name: | (default) |
Value: | |||
| (PID) Process: | (3504) VSSVC.exe | Key: | HKEY_LOCAL_MACHINE\BCD00000000\Objects\{9dea862c-5cdd-4e70-acc1-f32b344d4795}\Elements\12000002 |
| Operation: | write | Name: | Element |
Value: \EFI\Microsoft\Boot\bootmgfw.efi | |||
Executable files
75
Suspicious files
77
Text files
142
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 684 | msiexec.exe | C:\System Volume Information\SPP\metadata-2 | — | |
MD5:— | SHA256:— | |||
| 684 | msiexec.exe | C:\Windows\Installer\191b00.msi | — | |
MD5:— | SHA256:— | |||
| 7140 | msiexec.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\C8E534EE129F27D55460CE17FD628216_8DBAD5A433D1F9275321E076E8B744D4 | binary | |
MD5:52FA5F432DFF312EC1C164CAFB3F5D33 | SHA256:C0DD1FBFF3AEAD98E52BAFC4959BB68C23B43170B65336A9BC495F9FC0C2E1F3 | |||
| 7140 | msiexec.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\D9CB7DFFEEA63BAB482BD2705E7E24AB_D64C5BFAB2C28B4652E4AC7169A0D3DB | binary | |
MD5:89E0F529C42CB96E07F73A89758B4C56 | SHA256:8A89ABC34868F0379AC43F7EF2BDF626AD3304794626CF942A48EA08801ED079 | |||
| 7140 | msiexec.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\C8E534EE129F27D55460CE17FD628216_8DBAD5A433D1F9275321E076E8B744D4 | binary | |
MD5:707F88D38E717B0D28EED320C1028B41 | SHA256:1A339989E22D0DFAED8EA6749C5A28BBDF9634AF90C0AC78D6C7253769588140 | |||
| 7140 | msiexec.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\698460A0B6E60F2F602361424D832905_8BB23D43DE574E82F2BEE0DF0EC47EEB | binary | |
MD5:F868FB69004B1537B095C863594DB633 | SHA256:0D8EB61D93A133EF8A33BF7AB3BEAA132B4941C1AD231BBFF23B45A8C5153DCA | |||
| 7140 | msiexec.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\698460A0B6E60F2F602361424D832905_8BB23D43DE574E82F2BEE0DF0EC47EEB | binary | |
MD5:3447A97AA4A374F73AEA845580294AE1 | SHA256:E856B99739228003F5CD3E5B0B60376E9E5F8C5B7912A51D9A7194380ADB307A | |||
| 2632 | rundll32.exe | C:\Users\admin\AppData\Local\Temp\SFXCA5EB697F933491CD8CEDBF4321384837C\CustomAction.config | xml | |
MD5:C9C40AF1656F8531EAA647CACEB1E436 | SHA256:1A67F60962CA1CBF19873B62A8518EFE8C701A09CD609AF4C50ECC7F0B468BB8 | |||
| 684 | msiexec.exe | C:\System Volume Information\SPP\OnlineMetadataCache\{a2578b7b-65c9-4cd4-a821-1a6ddfe234cf}_OnDiskSnapshotProp | binary | |
MD5:55CF6591545A349805BD0B91F75E1B35 | SHA256:89140DAFFE024A1DAAC19B3771C104CB746AB6E43106B15B90DE502C42E3EEA1 | |||
| 684 | msiexec.exe | C:\Windows\Installer\MSI1E1D.tmp | executable | |
MD5:65E86867B503485775864C25B8889A88 | SHA256:CA23C29ACB6FA1D793C2E562EE424AD96771873EEFC763AE6D75784C15DDC749 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
51
TCP/UDP connections
61
DNS requests
23
Threats
23
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1268 | svchost.exe | GET | 200 | 2.16.164.49:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
5944 | MoUsoCoreWorker.exe | GET | 200 | 2.16.164.49:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 2.16.164.49:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
1268 | svchost.exe | GET | 200 | 23.52.120.96:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
5944 | MoUsoCoreWorker.exe | GET | 200 | 23.52.120.96:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
— | — | POST | 200 | 40.126.31.67:443 | https://login.live.com/RST2.srf | unknown | xml | 1.24 Kb | unknown |
— | — | GET | 200 | 23.52.120.96:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
7140 | msiexec.exe | GET | 200 | 184.30.131.245:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBT3xL4LQLXDRDM9P665TW442vrsUQQUReuir%2FSSy4IxLVGLp6chnfNtyA8CEA6bGI750C3n79tQ4ghAGFo%3D | unknown | — | — | whitelisted |
7140 | msiexec.exe | GET | 200 | 184.30.131.245:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTfIs%2BLjDtGwQ09XEB1Yeq%2BtX%2BBgQQU7NfjgtJxXWRM3y5nP%2Be6mK4cD08CEA5NZ%2FZDFskqO3oXzEaXao8%3D | unknown | — | — | whitelisted |
7140 | msiexec.exe | GET | 200 | 184.30.131.245:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBRhtVltVOu8OqBzmsd%2B%2FeFfks3xTQQUvGsiZZ2MaObmHgXx2HIl1LjgSMACEAvcoEuhCK%2FAlHGPdKmo6gs%3D | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
1268 | svchost.exe | 2.16.164.49:80 | crl.microsoft.com | Akamai International B.V. | NL | whitelisted |
5944 | MoUsoCoreWorker.exe | 2.16.164.49:80 | crl.microsoft.com | Akamai International B.V. | NL | whitelisted |
— | — | 2.16.164.49:80 | crl.microsoft.com | Akamai International B.V. | NL | whitelisted |
1268 | svchost.exe | 23.52.120.96:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
5944 | MoUsoCoreWorker.exe | 23.52.120.96:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
— | — | 23.52.120.96:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
— | — | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
go.microsoft.com |
| whitelisted |
app.pdq.com |
| unknown |
client.wns.windows.com |
| whitelisted |
pdqinstallers.e9d69694c3d8f7465fd531512c22bd0f.r2.cloudflarestorage.com |
| unknown |
Threats
PID | Process | Class | Message |
|---|---|---|---|
— | — | A Network Trojan was detected | ET INFO PDQ Remote Management HTTP Header Observed (x-pdq-key-ids) |
— | — | A Network Trojan was detected | ET INFO PDQ Remote Management HTTP Header Observed (x-pdq-key-ids) |
2200 | svchost.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare R2 Storage (r2 .cloudflarestorage .com) |
— | — | A Network Trojan was detected | ET INFO PDQ Remote Management User-Agent Observed (PDQ rover) |
— | — | A Network Trojan was detected | ET INFO PDQ Remote Management Agent Checkin |
— | — | A Network Trojan was detected | ET INFO PDQ Remote Management HTTP Header Observed (x-pdq-key-ids) |
— | — | A Network Trojan was detected | ET INFO PDQ Remote Management User-Agent Observed (PDQ rover) |
— | — | A Network Trojan was detected | ET INFO PDQ Remote Management Agent Checkin |
— | — | A Network Trojan was detected | ET INFO PDQ Remote Management HTTP Header Observed (x-pdq-key-ids) |
— | — | A Network Trojan was detected | ET INFO PDQ Remote Management User-Agent Observed (PDQ rover) |