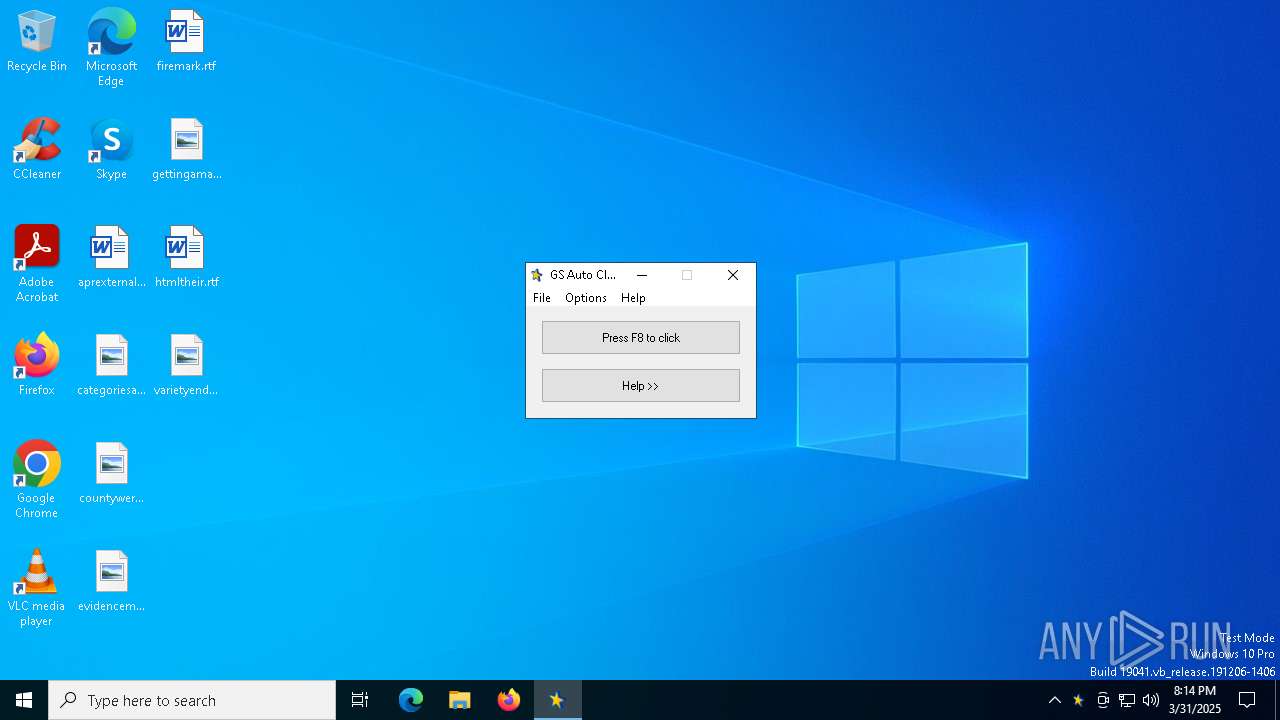
| File name: | gs-auto-clicker.exe |
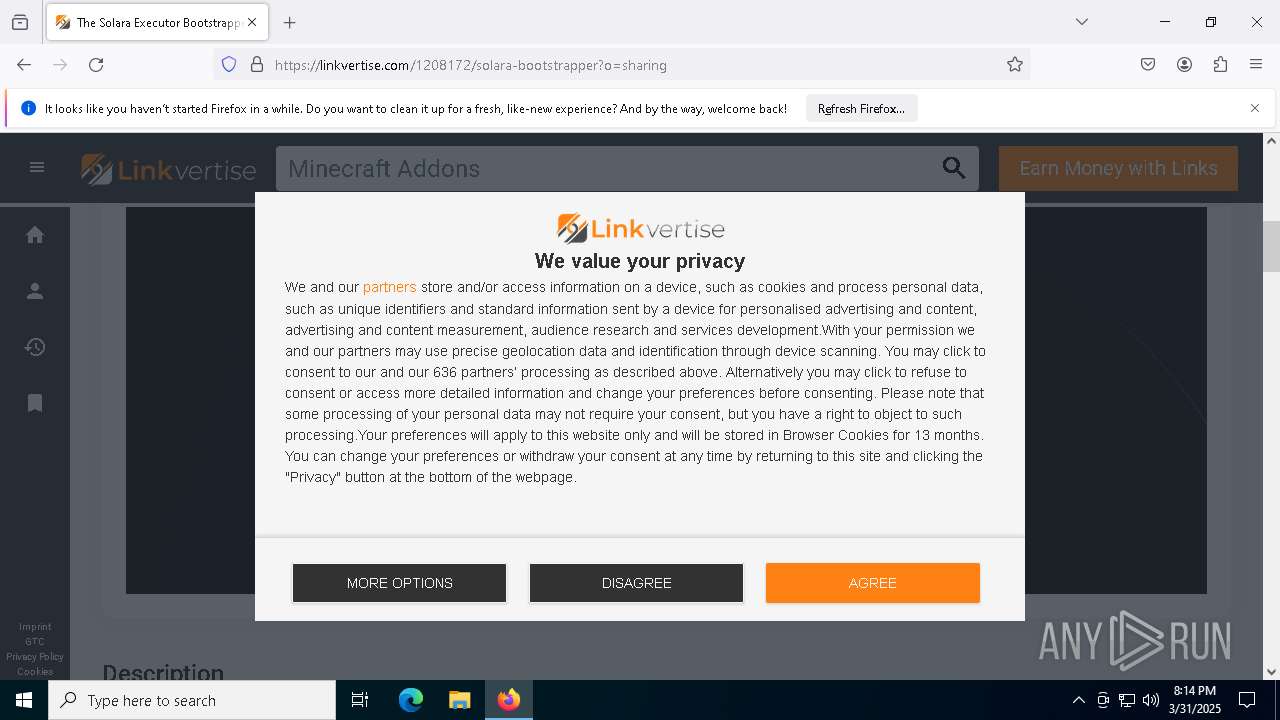
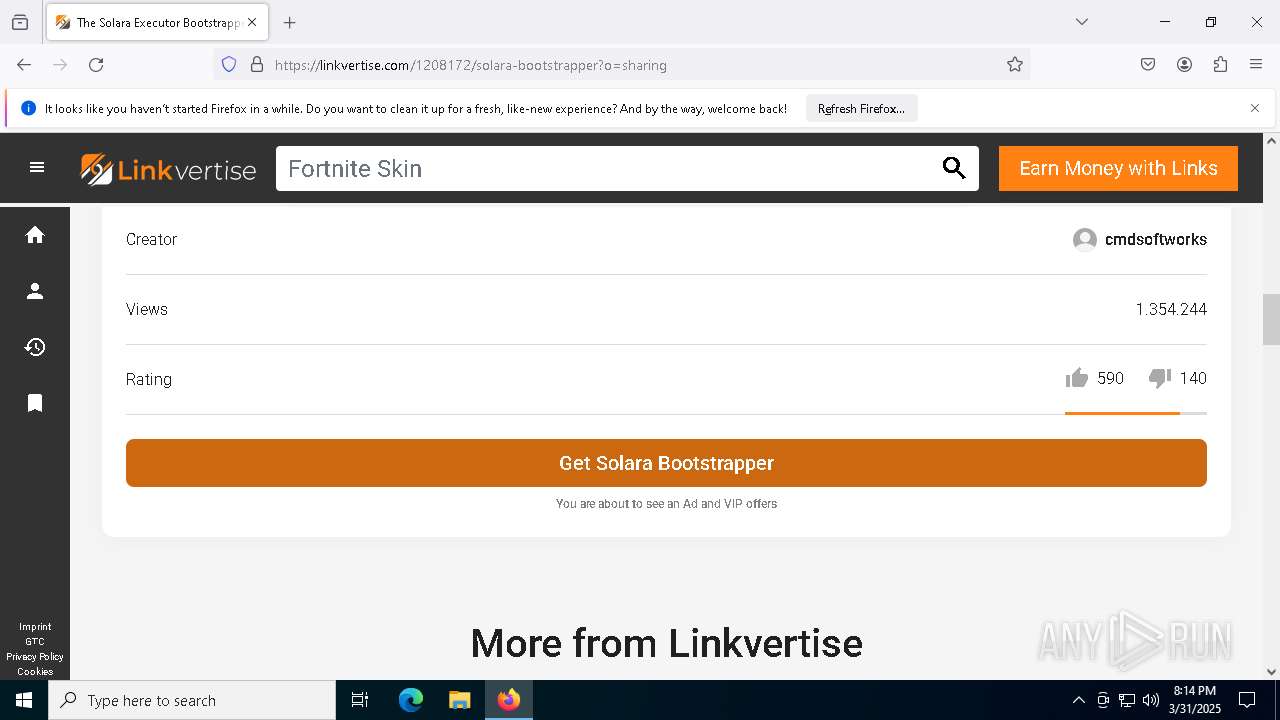
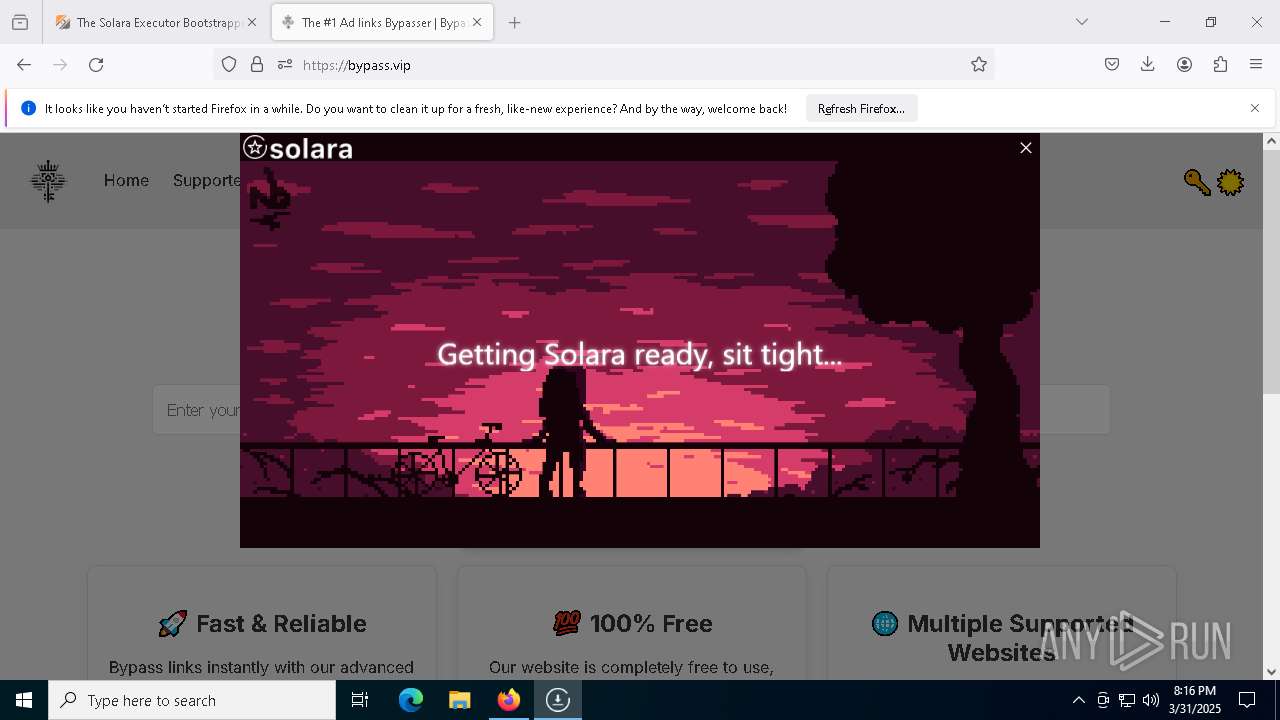
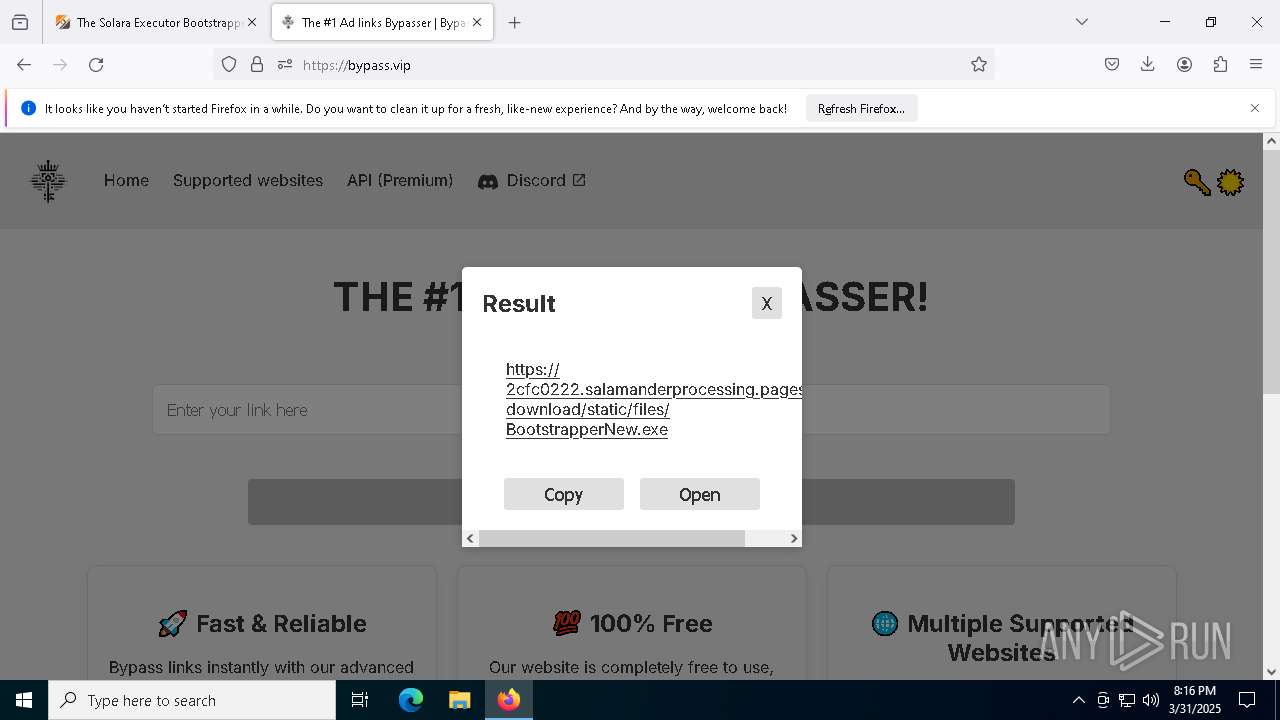
| Full analysis: | https://app.any.run/tasks/92782daf-41f8-4b16-9eb8-cd33a33ff648 |
| Verdict: | Malicious activity |
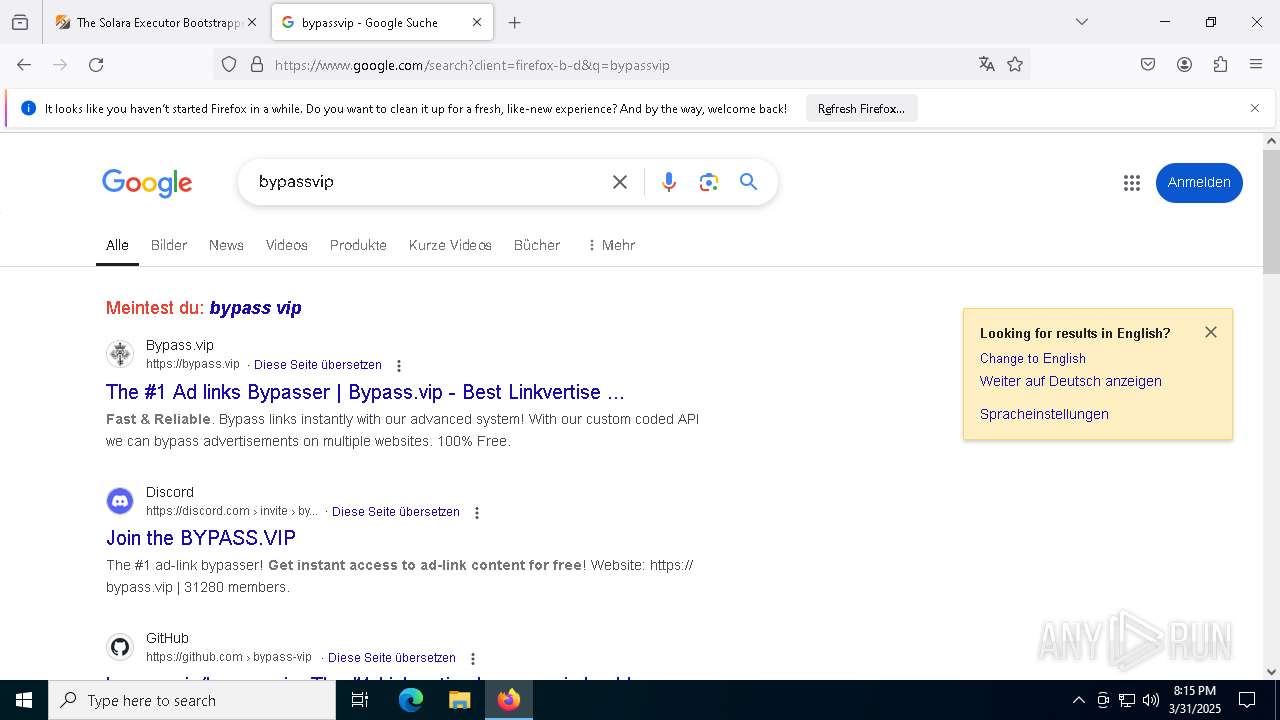
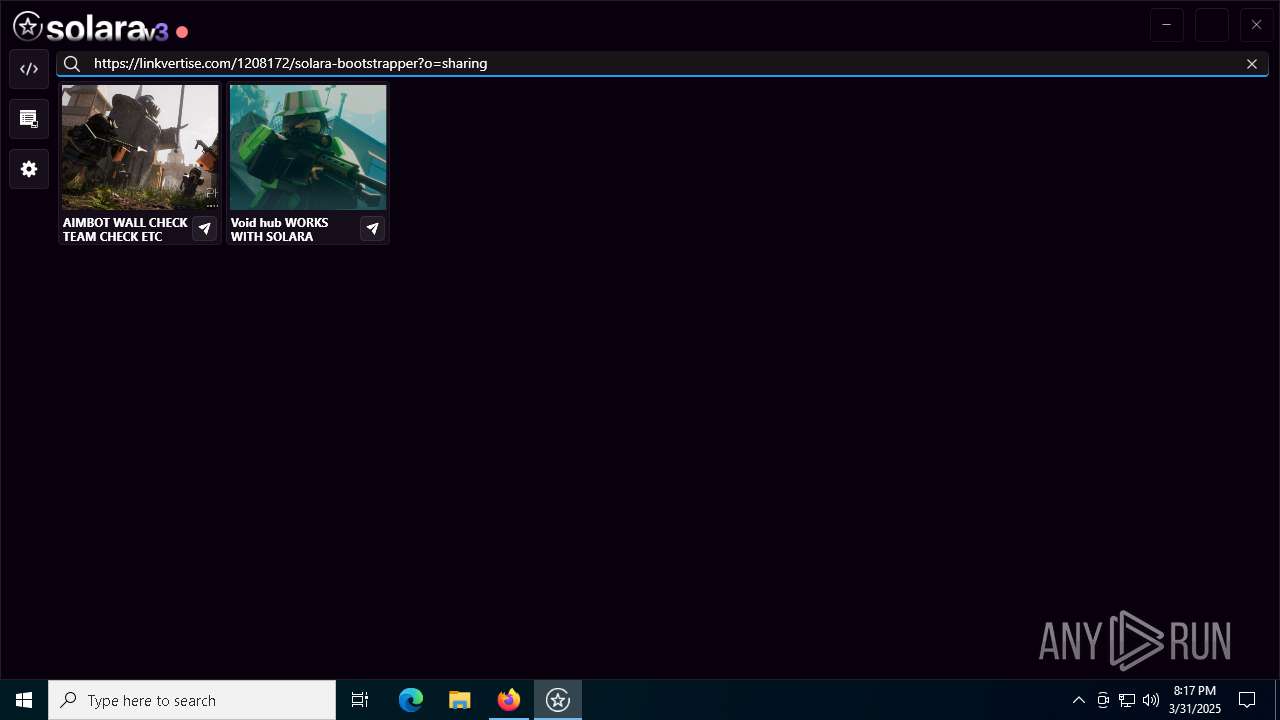
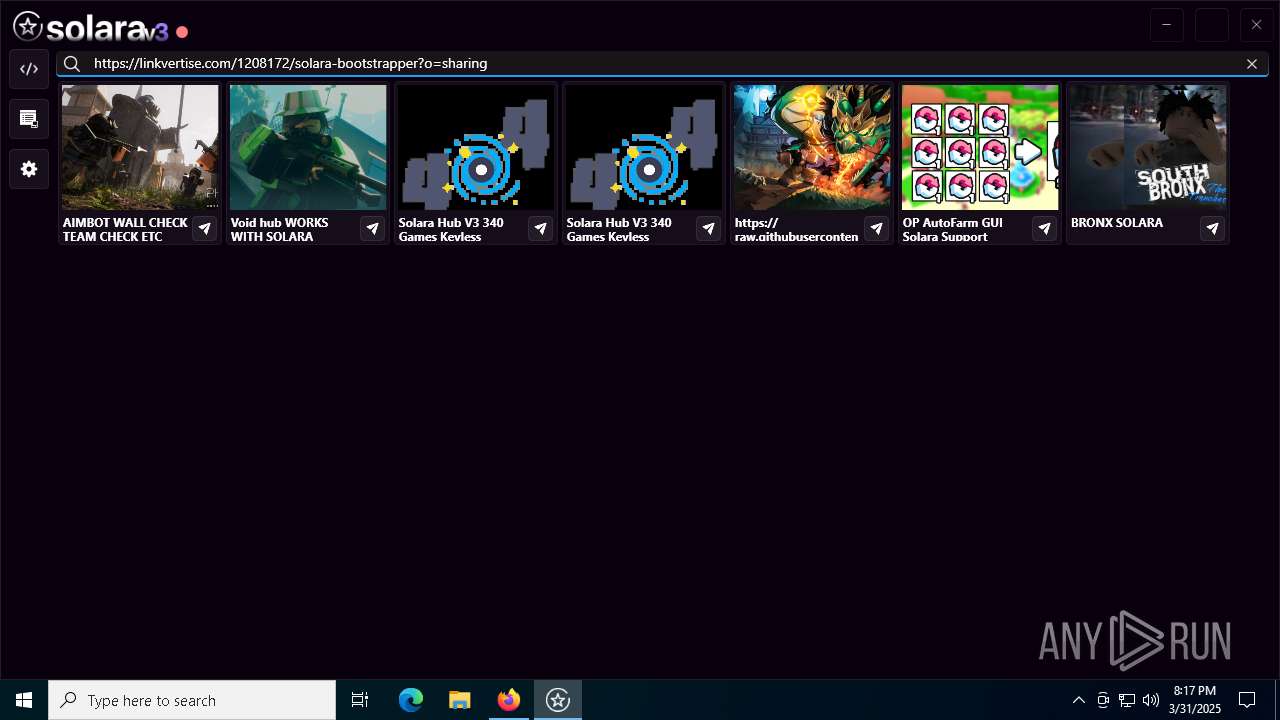
| Threats: | A loader is malicious software that infiltrates devices to deliver malicious payloads. This malware is capable of infecting victims’ computers, analyzing their system information, and installing other types of threats, such as trojans or stealers. Criminals usually deliver loaders through phishing emails and links by relying on social engineering to trick users into downloading and running their executables. Loaders employ advanced evasion and persistence tactics to avoid detection. |
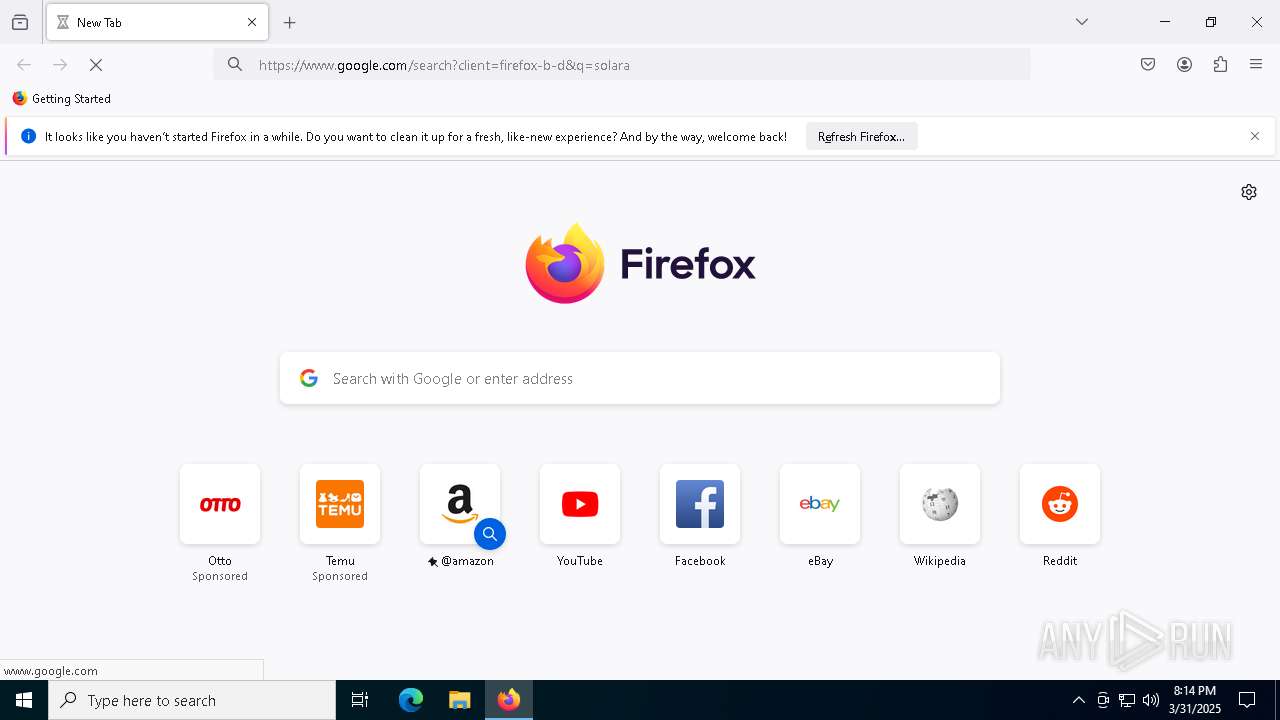
| Analysis date: | March 31, 2025, 20:14:08 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, 4 sections |
| MD5: | 6862F65BE14FD3CE88086EC79777DB6E |
| SHA1: | 7F0EB7535B59A926446A400FF93F48165B58AC95 |
| SHA256: | 7C90795C9B28FAC978386626F5A54033DC9CBA46EF6A3F742FC7D52B394590F2 |
| SSDEEP: | 12288:saWzgMg7v3qnCibErQohh0F4zCJ8lnywQ8S8Xe74050MOm:TaHMv6Cbrj/nywQ8Sfs+7 |
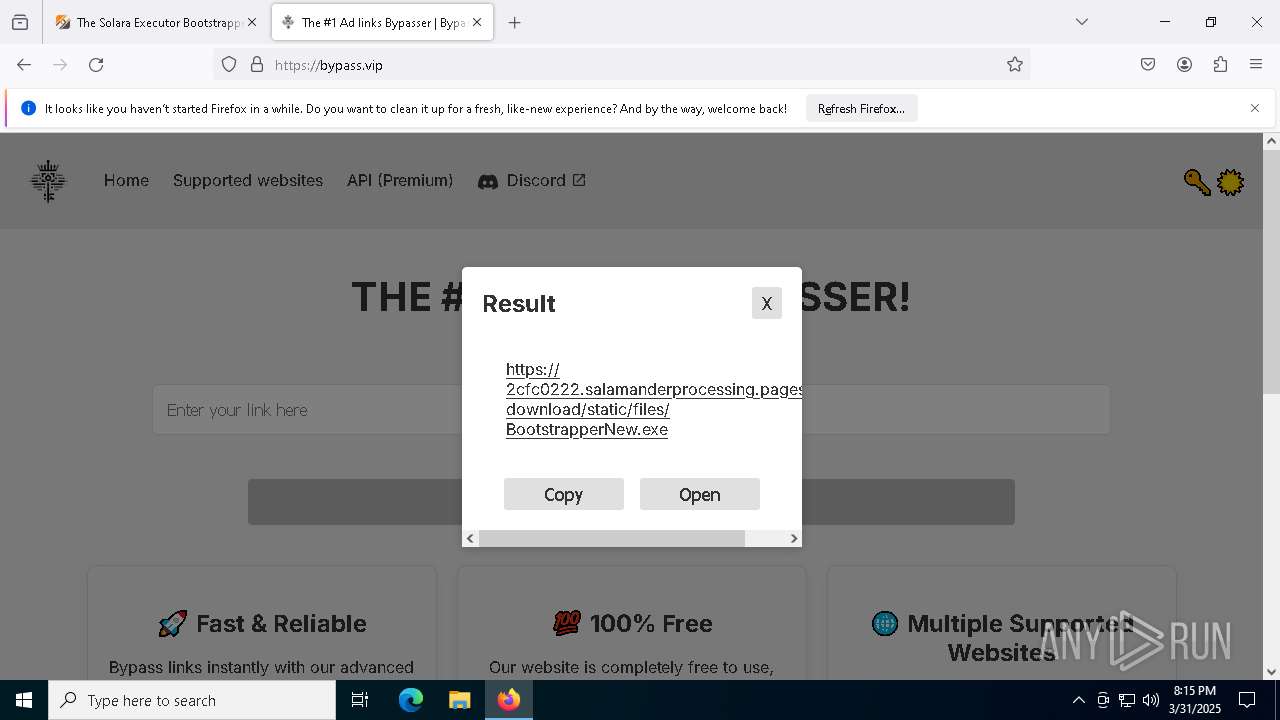
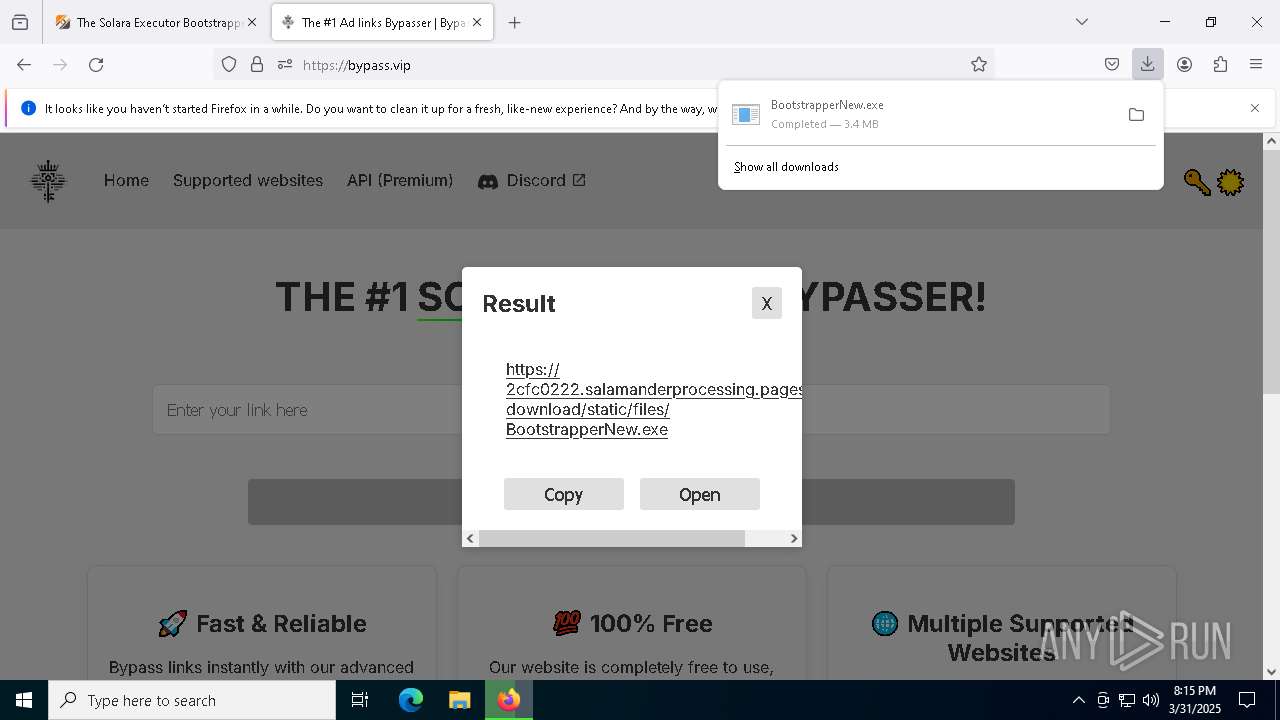
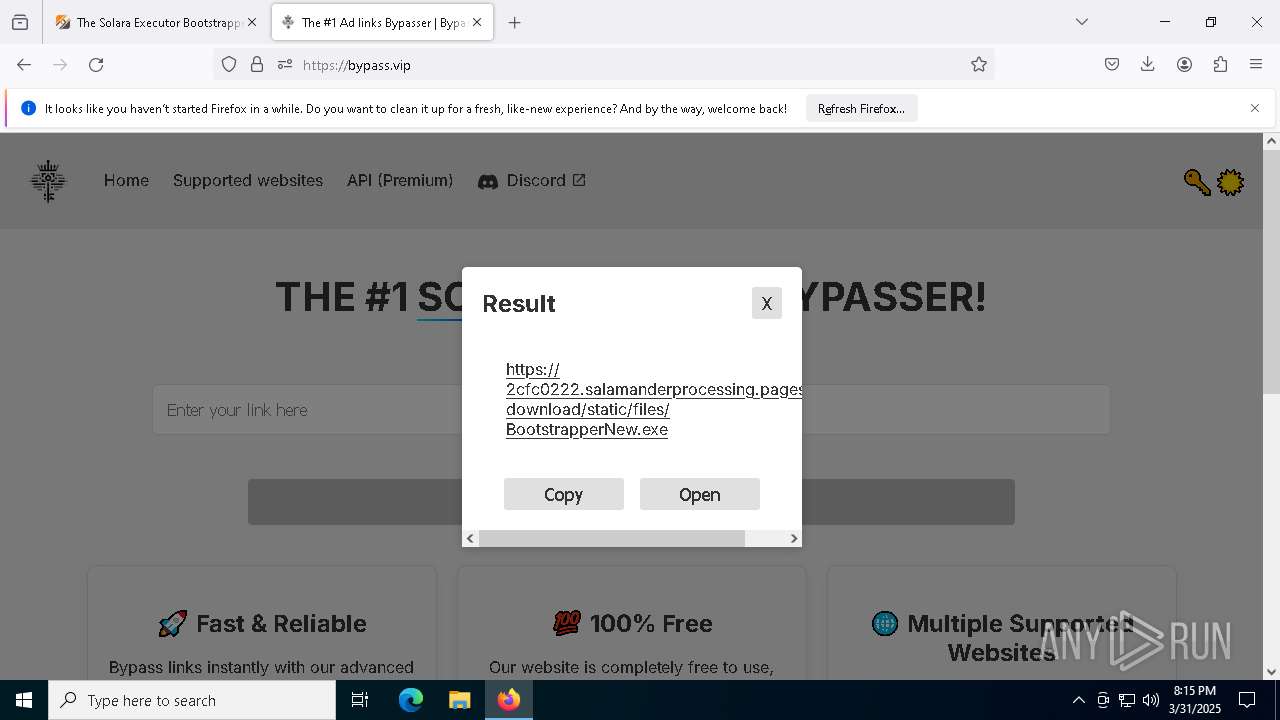
MALICIOUS
Adds path to the Windows Defender exclusion list
- BootstrapperNew.exe (PID: 8488)
Changes Windows Defender settings
- BootstrapperNew.exe (PID: 8488)
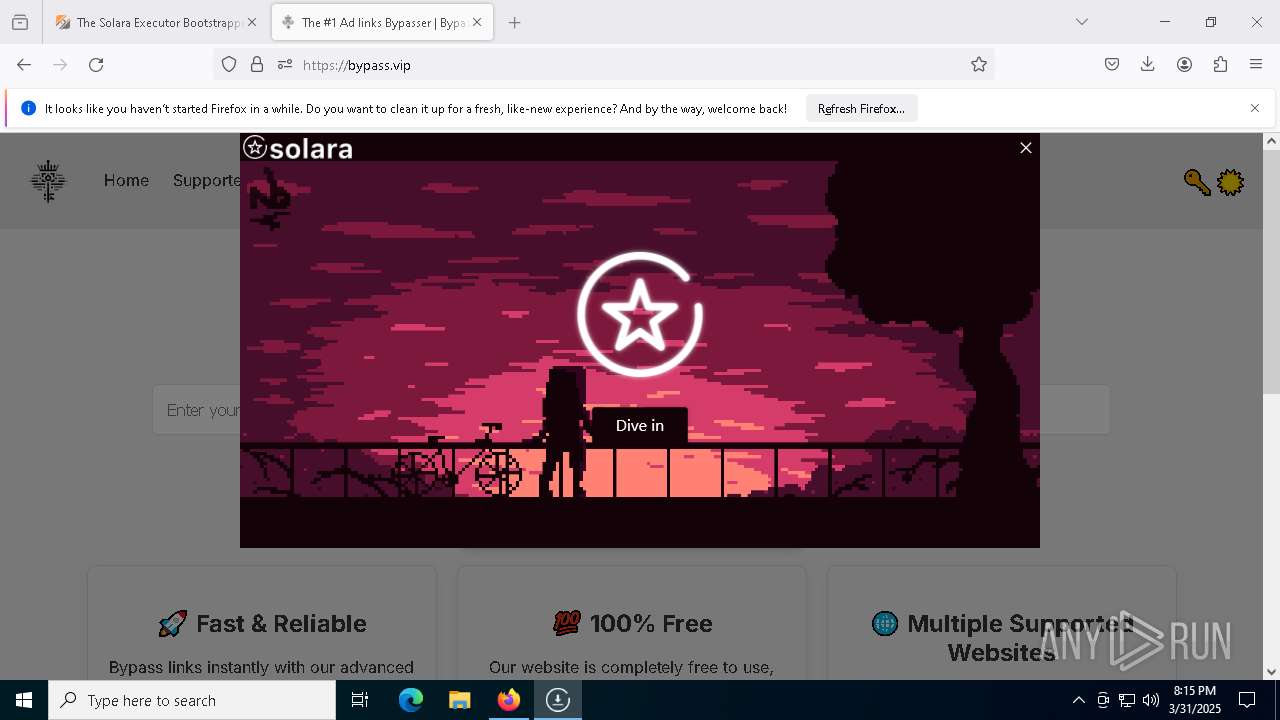
SUSPICIOUS
Reads security settings of Internet Explorer
- BootstrapperNew.exe (PID: 8488)
- MicrosoftEdgeUpdate.exe (PID: 8900)
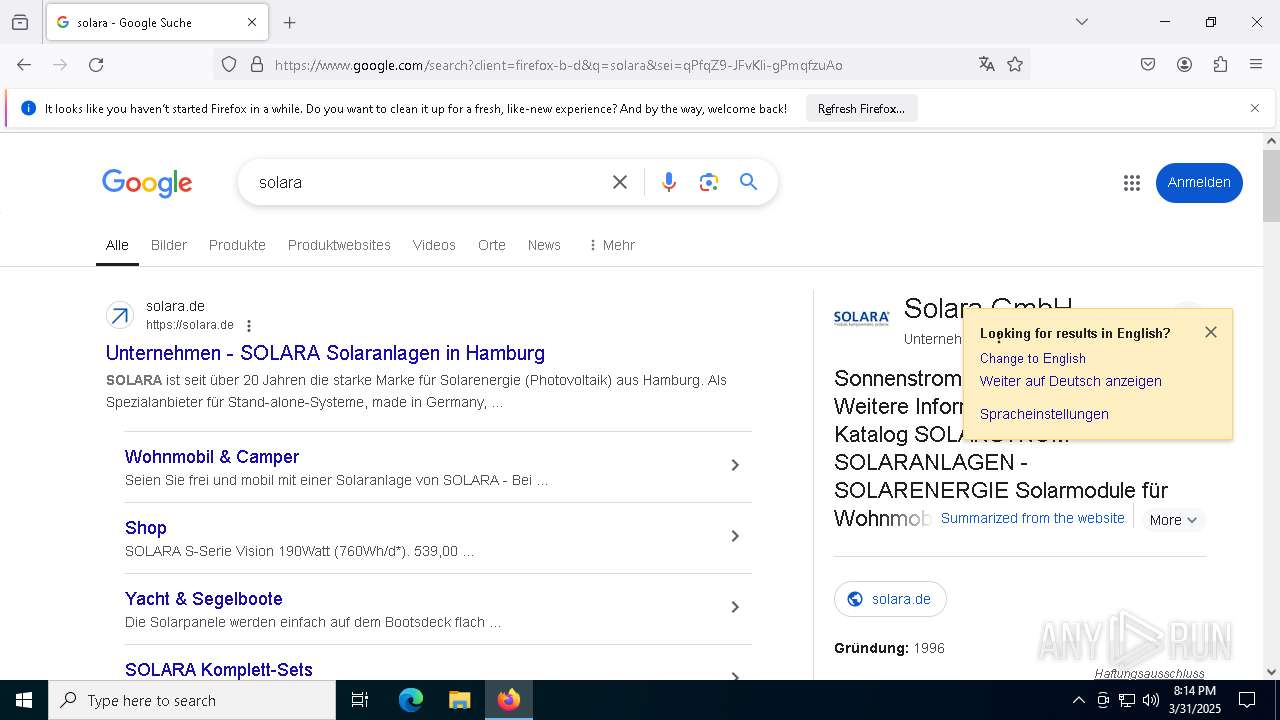
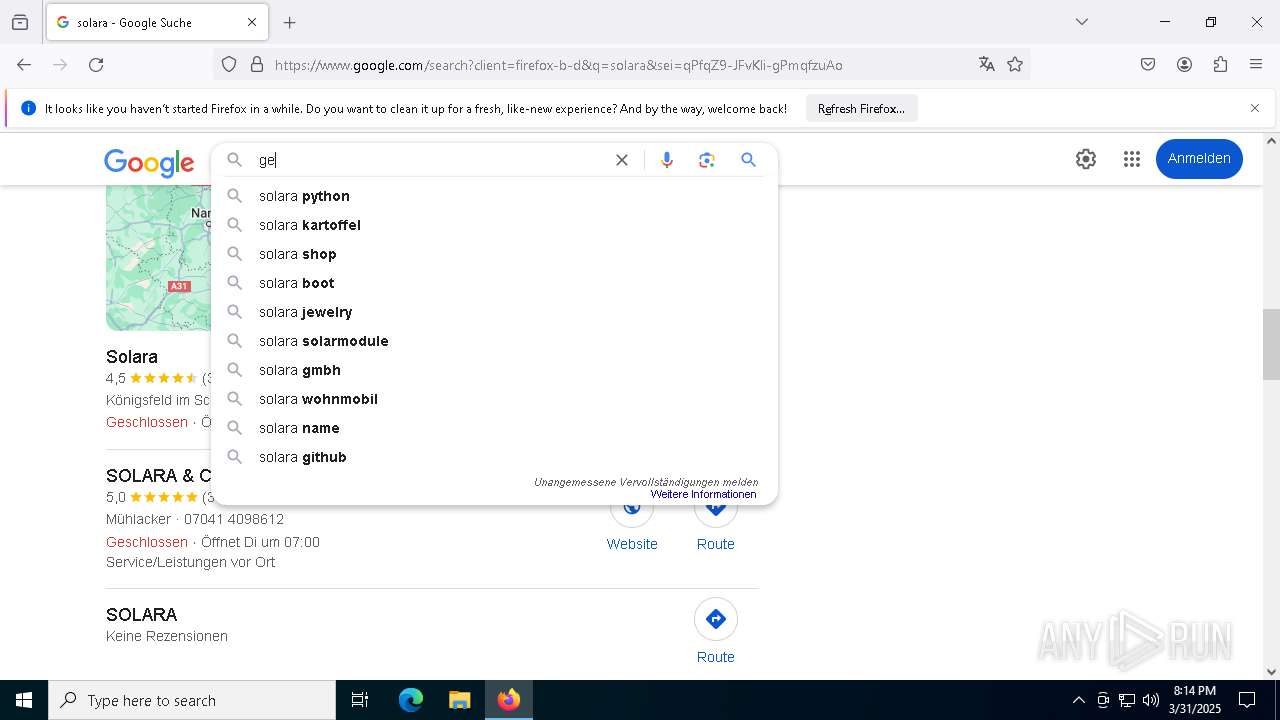
- Solara.exe (PID: 6980)
Query Microsoft Defender preferences
- BootstrapperNew.exe (PID: 8488)
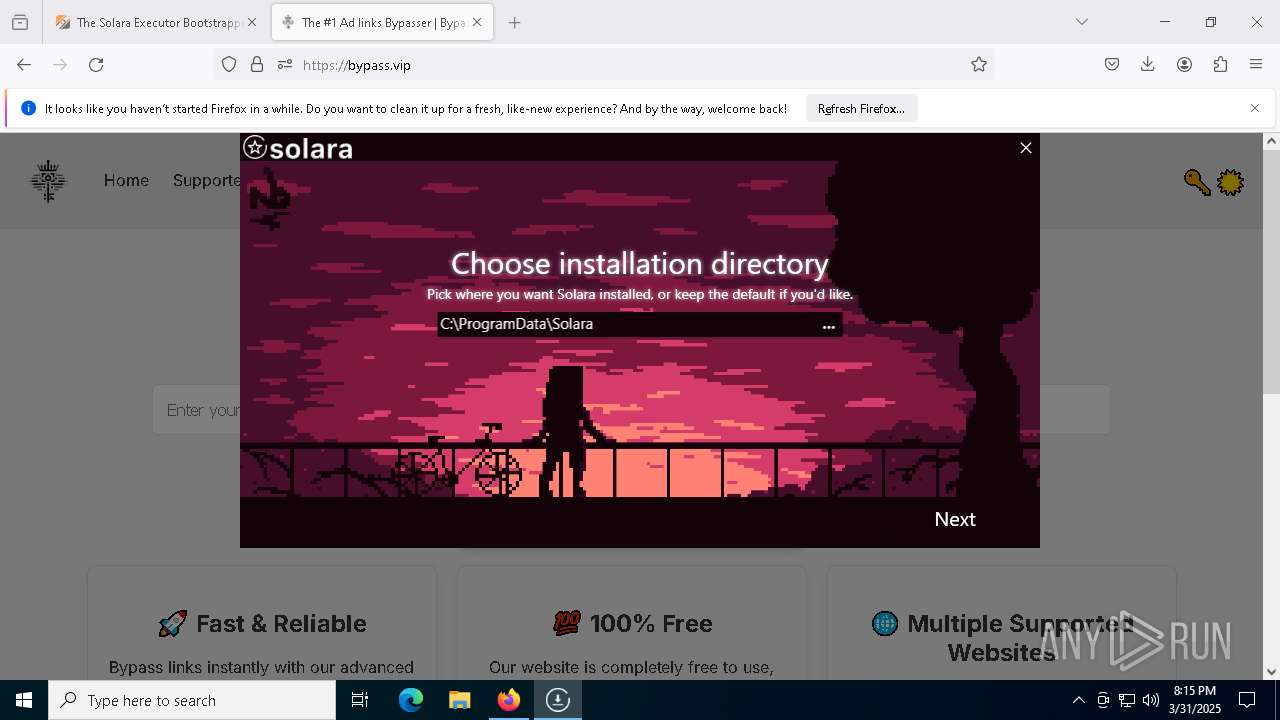
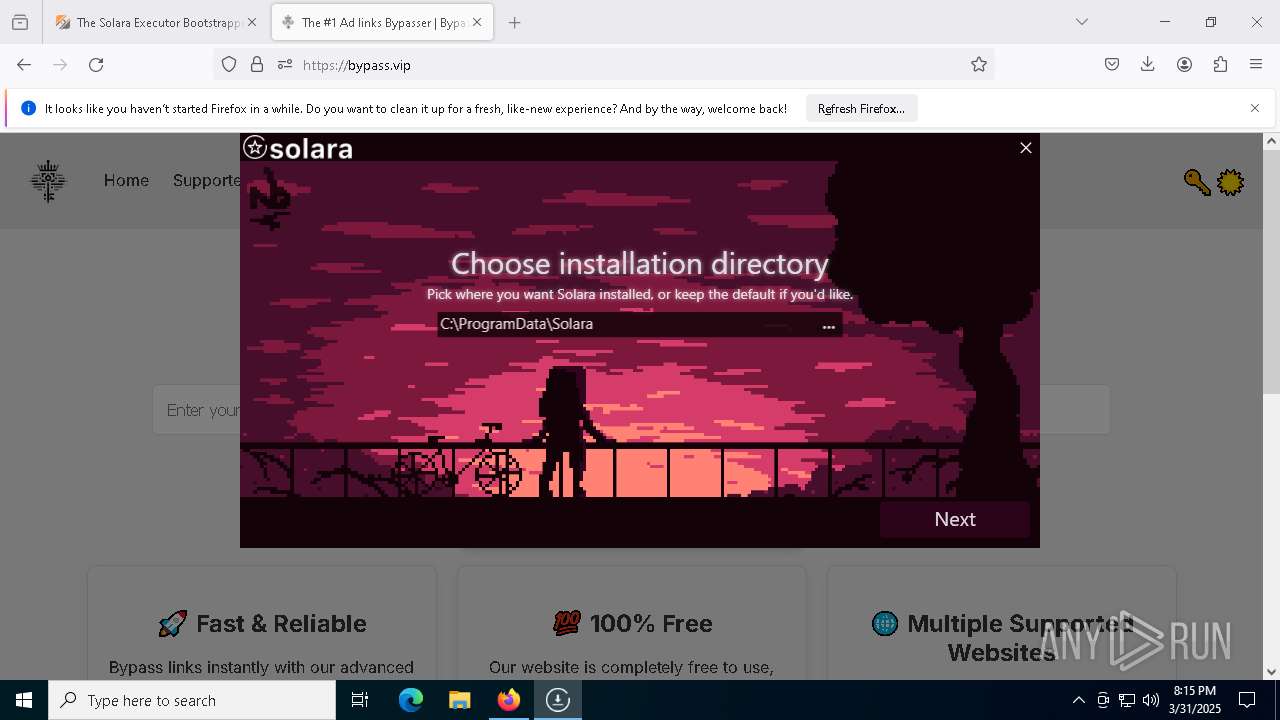
Starts POWERSHELL.EXE for commands execution
- BootstrapperNew.exe (PID: 8488)
Script adds exclusion path to Windows Defender
- BootstrapperNew.exe (PID: 8488)
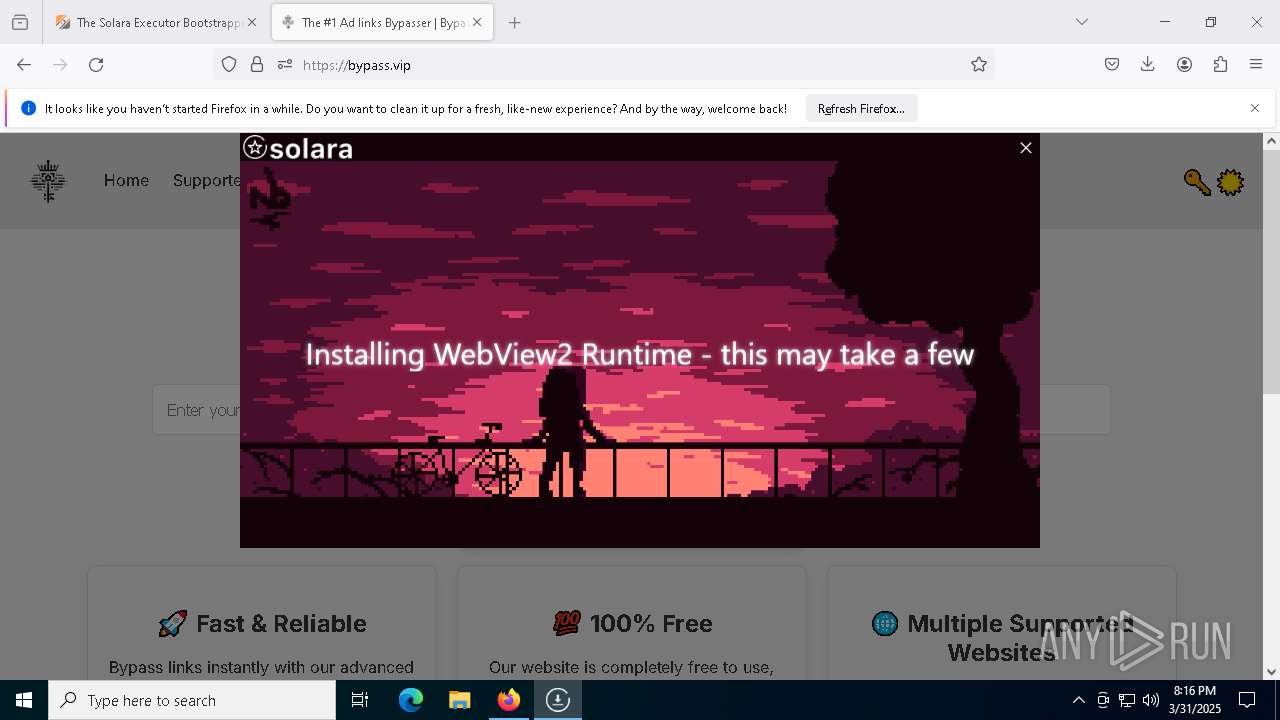
Executable content was dropped or overwritten
- BootstrapperNew.exe (PID: 8488)
- MicrosoftEdgeWebview2Setup.exe (PID: 7904)
Process drops legitimate windows executable
- BootstrapperNew.exe (PID: 8488)
- MicrosoftEdgeWebview2Setup.exe (PID: 7904)
- MicrosoftEdgeUpdate.exe (PID: 8900)
Starts a Microsoft application from unusual location
- MicrosoftEdgeWebview2Setup.exe (PID: 7904)
- MicrosoftEdgeUpdate.exe (PID: 8900)
Process requests binary or script from the Internet
- BootstrapperNew.exe (PID: 8488)
The process drops C-runtime libraries
- BootstrapperNew.exe (PID: 8488)
Reads the date of Windows installation
- BootstrapperNew.exe (PID: 8488)
Disables SEHOP
- MicrosoftEdgeUpdate.exe (PID: 8900)
Reads the BIOS version
- Solara.exe (PID: 6980)
INFO
The sample compiled with english language support
- gs-auto-clicker.exe (PID: 7320)
- MicrosoftEdgeWebview2Setup.exe (PID: 7904)
- BootstrapperNew.exe (PID: 8488)
- MicrosoftEdgeUpdate.exe (PID: 8900)
Reads mouse settings
- gs-auto-clicker.exe (PID: 7320)
Reads the computer name
- gs-auto-clicker.exe (PID: 7320)
- BootstrapperNew.exe (PID: 8488)
- MicrosoftEdgeUpdate.exe (PID: 8900)
- Solara.exe (PID: 6980)
Create files in a temporary directory
- gs-auto-clicker.exe (PID: 7320)
- BootstrapperNew.exe (PID: 8488)
Application launched itself
- firefox.exe (PID: 7688)
- firefox.exe (PID: 7712)
Checks supported languages
- gs-auto-clicker.exe (PID: 7320)
- BootstrapperNew.exe (PID: 8488)
- MicrosoftEdgeWebview2Setup.exe (PID: 7904)
- MicrosoftEdgeUpdate.exe (PID: 8900)
- Solara.exe (PID: 6980)
Manual execution by a user
- firefox.exe (PID: 7688)
Reads the software policy settings
- slui.exe (PID: 7388)
- BootstrapperNew.exe (PID: 8488)
- MicrosoftEdgeUpdate.exe (PID: 8900)
- slui.exe (PID: 8616)
- wermgr.exe (PID: 1052)
- Solara.exe (PID: 6980)
Reads the machine GUID from the registry
- BootstrapperNew.exe (PID: 8488)
- Solara.exe (PID: 6980)
Autorun file from Downloads
- firefox.exe (PID: 7712)
Executable content was dropped or overwritten
- firefox.exe (PID: 7712)
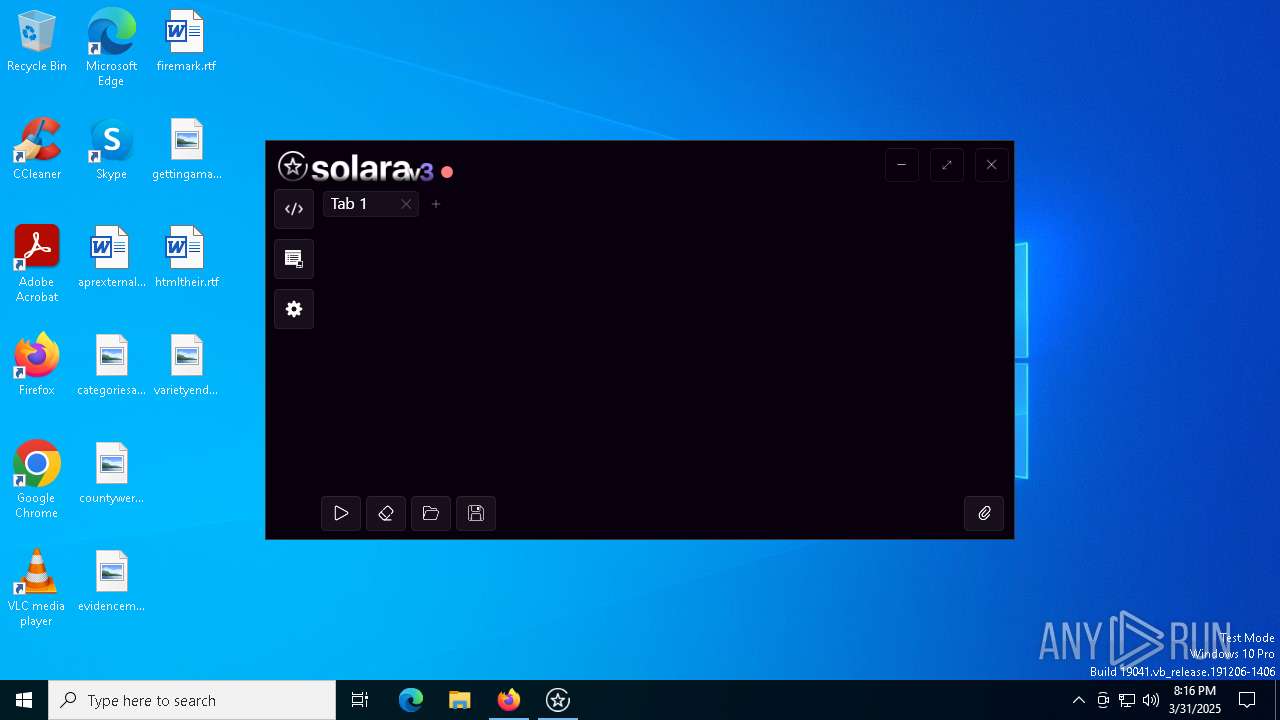
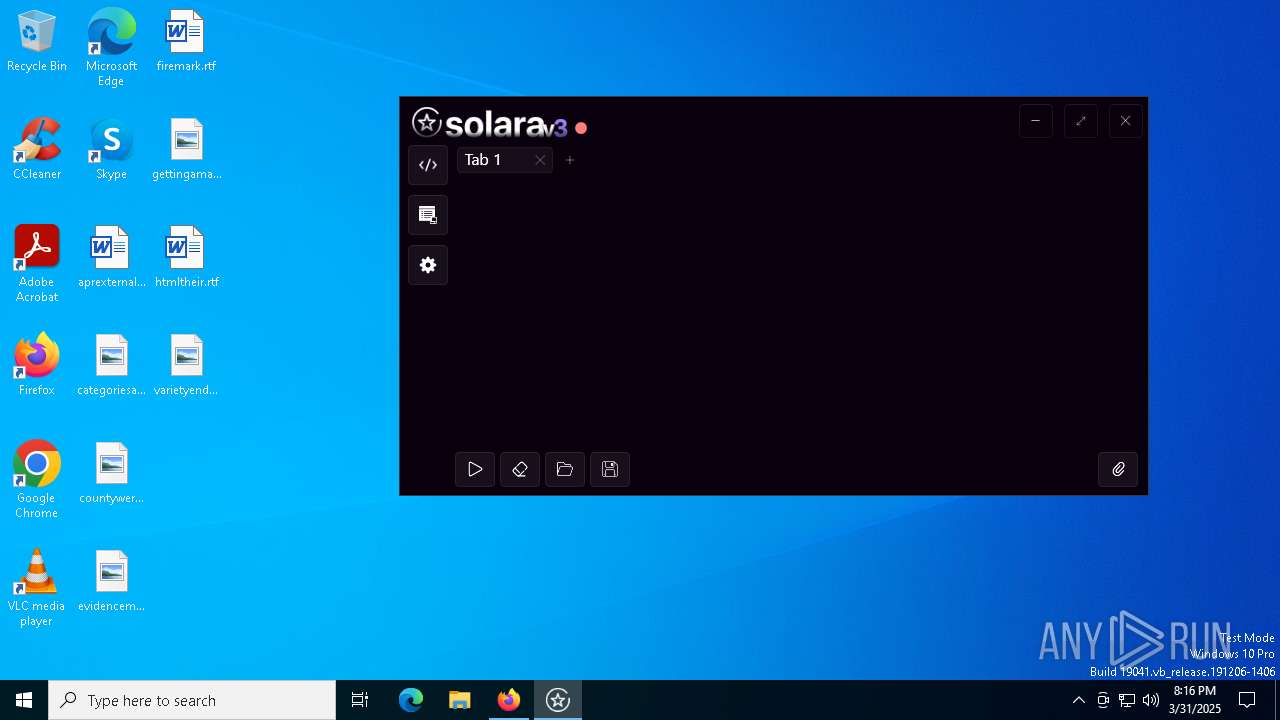
Creates files in the program directory
- BootstrapperNew.exe (PID: 8488)
- MicrosoftEdgeWebview2Setup.exe (PID: 7904)
- Solara.exe (PID: 6980)
Checks if a key exists in the options dictionary (POWERSHELL)
- powershell.exe (PID: 6652)
- powershell.exe (PID: 5360)
Disables trace logs
- BootstrapperNew.exe (PID: 8488)
- Solara.exe (PID: 6980)
Script raised an exception (POWERSHELL)
- powershell.exe (PID: 5360)
Checks proxy server information
- BootstrapperNew.exe (PID: 8488)
- MicrosoftEdgeUpdate.exe (PID: 8900)
- wermgr.exe (PID: 1052)
- slui.exe (PID: 8616)
- Solara.exe (PID: 6980)
Reads Environment values
- BootstrapperNew.exe (PID: 8488)
- MicrosoftEdgeUpdate.exe (PID: 8900)
- Solara.exe (PID: 6980)
Process checks computer location settings
- MicrosoftEdgeUpdate.exe (PID: 8900)
- BootstrapperNew.exe (PID: 8488)
Creates files or folders in the user directory
- wermgr.exe (PID: 1052)
Process checks whether UAC notifications are on
- Solara.exe (PID: 6980)
Themida protector has been detected
- Solara.exe (PID: 6980)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win64 Executable (generic) (64.6) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (15.4) |
| .exe | | | Win32 Executable (generic) (10.5) |
| .exe | | | Generic Win/DOS Executable (4.6) |
| .exe | | | DOS Executable Generic (4.6) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2016:05:30 16:33:32+00:00 |
| ImageFileCharacteristics: | No relocs, Executable, Large address aware, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 9 |
| CodeSize: | 524800 |
| InitializedDataSize: | 122368 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x16310 |
| OSVersion: | 5 |
| ImageVersion: | - |
| SubsystemVersion: | 5 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 3.1.4.0 |
| ProductVersionNumber: | 3.1.4.0 |
| FileFlagsMask: | 0x0000 |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Unknown |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Unicode |
| Comments: | www.goldensoft.org |
| FileDescription: | GS Auto Clicker |
| FileVersion: | 3.1.4 |
| LegalCopyright: | goldensoft.org |
| ProductName: | GS Auto Clicker |
| ProductVersion: | 3.1.4 |
Total processes
172
Monitored processes
36
Malicious processes
5
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 720 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc --channel=6248 -childID 9 -isForBrowser -prefsHandle 6240 -prefMapHandle 6236 -prefsLen 31374 -prefMapSize 244583 -jsInitHandle 1528 -jsInitLen 235124 -parentBuildID 20240213221259 -win32kLockedDown -appDir "C:\Program Files\Mozilla Firefox\browser" - {d0fc42bc-9385-43af-8bb4-bdd64070e510} 7712 "\\.\pipe\gecko-crash-server-pipe.7712" 243f451a4d0 tab | C:\Program Files\Mozilla Firefox\firefox.exe | — | firefox.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: MEDIUM Description: Firefox Exit code: 0 Version: 123.0 Modules
| |||||||||||||||
| 1052 | "C:\WINDOWS\system32\wermgr.exe" "-outproc" "0" "8900" "2064" "1980" "2068" "0" "0" "0" "0" "0" "0" "0" "0" | C:\Windows\SysWOW64\wermgr.exe | MicrosoftEdgeUpdate.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Problem Reporting Exit code: 0 Version: 10.0.19041.3996 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1300 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc --channel=4312 -childID 8 -isForBrowser -prefsHandle 5168 -prefMapHandle 5088 -prefsLen 31374 -prefMapSize 244583 -jsInitHandle 1528 -jsInitLen 235124 -parentBuildID 20240213221259 -win32kLockedDown -appDir "C:\Program Files\Mozilla Firefox\browser" - {452c0e9d-b921-44e5-9e92-e2dac8805e12} 7712 "\\.\pipe\gecko-crash-server-pipe.7712" 243f9a44a10 tab | C:\Program Files\Mozilla Firefox\firefox.exe | — | firefox.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: MEDIUM Description: Firefox Exit code: 0 Version: 123.0 Modules
| |||||||||||||||
| 2772 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc --channel=6548 -childID 10 -isForBrowser -prefsHandle 6700 -prefMapHandle 6684 -prefsLen 31424 -prefMapSize 244583 -jsInitHandle 1528 -jsInitLen 235124 -parentBuildID 20240213221259 -win32kLockedDown -appDir "C:\Program Files\Mozilla Firefox\browser" - {86daf6be-9a33-4630-91c2-995cebb629f6} 7712 "\\.\pipe\gecko-crash-server-pipe.7712" 243f9e2c850 tab | C:\Program Files\Mozilla Firefox\firefox.exe | — | firefox.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: MEDIUM Description: Firefox Version: 123.0 Modules
| |||||||||||||||
| 4428 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc --channel=6876 -childID 12 -isForBrowser -prefsHandle 6860 -prefMapHandle 6856 -prefsLen 31577 -prefMapSize 244583 -jsInitHandle 1528 -jsInitLen 235124 -parentBuildID 20240213221259 -win32kLockedDown -appDir "C:\Program Files\Mozilla Firefox\browser" - {f0b0402b-ba38-47b0-8b36-c5c1c29a4686} 7712 "\\.\pipe\gecko-crash-server-pipe.7712" 243f451abd0 tab | C:\Program Files\Mozilla Firefox\firefox.exe | — | firefox.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: MEDIUM Description: Firefox Version: 123.0 Modules
| |||||||||||||||
| 5008 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc --channel=4572 -childID 4 -isForBrowser -prefsHandle 4780 -prefMapHandle 4776 -prefsLen 31144 -prefMapSize 244583 -jsInitHandle 1528 -jsInitLen 235124 -parentBuildID 20240213221259 -win32kLockedDown -appDir "C:\Program Files\Mozilla Firefox\browser" - {24aff98c-9537-48b5-b65f-c5fd511fd256} 7712 "\\.\pipe\gecko-crash-server-pipe.7712" 243f82b2d90 tab | C:\Program Files\Mozilla Firefox\firefox.exe | — | firefox.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: MEDIUM Description: Firefox Version: 123.0 Modules
| |||||||||||||||
| 5112 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc --channel=4676 -childID 3 -isForBrowser -prefsHandle 4768 -prefMapHandle 4764 -prefsLen 31144 -prefMapSize 244583 -jsInitHandle 1528 -jsInitLen 235124 -parentBuildID 20240213221259 -win32kLockedDown -appDir "C:\Program Files\Mozilla Firefox\browser" - {2969cdf1-39c4-4a84-b1ac-9831db16bd09} 7712 "\\.\pipe\gecko-crash-server-pipe.7712" 243f82b2bd0 tab | C:\Program Files\Mozilla Firefox\firefox.exe | — | firefox.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: MEDIUM Description: Firefox Version: 123.0 Modules
| |||||||||||||||
| 5360 | "powershell" -Command "Add-MpPreference -ExclusionPath 'C:\ProgramData\Solara'" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | BootstrapperNew.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows PowerShell Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5404 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc --channel=5864 -childID 6 -isForBrowser -prefsHandle 5884 -prefMapHandle 5904 -prefsLen 31293 -prefMapSize 244583 -jsInitHandle 1528 -jsInitLen 235124 -parentBuildID 20240213221259 -win32kLockedDown -appDir "C:\Program Files\Mozilla Firefox\browser" - {83821b88-074a-4742-85c9-2b5ed317c43b} 7712 "\\.\pipe\gecko-crash-server-pipe.7712" 243fb78d150 tab | C:\Program Files\Mozilla Firefox\firefox.exe | — | firefox.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: MEDIUM Description: Firefox Version: 123.0 Modules
| |||||||||||||||
| 5756 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc --channel=6692 -childID 11 -isForBrowser -prefsHandle 6588 -prefMapHandle 5720 -prefsLen 31424 -prefMapSize 244583 -jsInitHandle 1528 -jsInitLen 235124 -parentBuildID 20240213221259 -win32kLockedDown -appDir "C:\Program Files\Mozilla Firefox\browser" - {e295f8f0-ba10-4344-9380-797ed805c67c} 7712 "\\.\pipe\gecko-crash-server-pipe.7712" 243f9e2ca10 tab | C:\Program Files\Mozilla Firefox\firefox.exe | — | firefox.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: MEDIUM Description: Firefox Version: 123.0 Modules
| |||||||||||||||
Total events
44 863
Read events
44 797
Write events
64
Delete events
2
Modification events
| (PID) Process: | (7712) firefox.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Mozilla\Firefox\DllPrefetchExperiment |
| Operation: | write | Name: | C:\Program Files\Mozilla Firefox\firefox.exe |
Value: 0 | |||
| (PID) Process: | (7712) firefox.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer |
| Operation: | write | Name: | SlowContextMenuEntries |
Value: 6024B221EA3A6910A2DC08002B30309D0A010000BD0E0C47735D584D9CEDE91E22E23282770100000114020000000000C0000000000000468D0000006078A409B011A54DAFA526D86198A780390100009AD298B2EDA6DE11BA8CA68E55D895936E000000 | |||
| (PID) Process: | (8488) BootstrapperNew.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\BootstrapperNew_RASAPI32 |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (8488) BootstrapperNew.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\BootstrapperNew_RASAPI32 |
| Operation: | write | Name: | EnableAutoFileTracing |
Value: 0 | |||
| (PID) Process: | (8488) BootstrapperNew.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\BootstrapperNew_RASAPI32 |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
| (PID) Process: | (8488) BootstrapperNew.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\BootstrapperNew_RASAPI32 |
| Operation: | write | Name: | FileTracingMask |
Value: | |||
| (PID) Process: | (8488) BootstrapperNew.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\BootstrapperNew_RASAPI32 |
| Operation: | write | Name: | ConsoleTracingMask |
Value: | |||
| (PID) Process: | (8488) BootstrapperNew.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\BootstrapperNew_RASAPI32 |
| Operation: | write | Name: | MaxFileSize |
Value: 1048576 | |||
| (PID) Process: | (8488) BootstrapperNew.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\BootstrapperNew_RASAPI32 |
| Operation: | write | Name: | FileDirectory |
Value: %windir%\tracing | |||
| (PID) Process: | (8488) BootstrapperNew.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\BootstrapperNew_RASMANCS |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
Executable files
213
Suspicious files
216
Text files
41
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 7712 | firefox.exe | C:\Users\admin\AppData\Local\Mozilla\Firefox\Profiles\9kie7cg6.default-release\startupCache\scriptCache-current.bin | — | |
MD5:— | SHA256:— | |||
| 7712 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\sessionCheckpoints.json.tmp | binary | |
MD5:EA8B62857DFDBD3D0BE7D7E4A954EC9A | SHA256:792955295AE9C382986222C6731C5870BD0E921E7F7E34CC4615F5CD67F225DA | |||
| 7712 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\prefs.js | text | |
MD5:0F2A4575A82E92C1D2CDFEDF3C2B5CD3 | SHA256:— | |||
| 7712 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\storage\permanent\chrome\idb\3870112724rsegmnoittet-es.sqlite | — | |
MD5:— | SHA256:— | |||
| 7712 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\cookies.sqlite-shm | binary | |
MD5:B7C14EC6110FA820CA6B65F5AEC85911 | SHA256:FD4C9FDA9CD3F9AE7C962B0DDF37232294D55580E1AA165AA06129B8549389EB | |||
| 7712 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\datareporting\glean\db\data.safe.bin | binary | |
MD5:EF90022DF0735160DD056C0E6670E915 | SHA256:2B663C0B462A437C8DE3D9B95EE157AE181249B78BDD6F7BD73F7EB6D9E03F87 | |||
| 7712 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\storage\permanent\chrome\idb\1657114595AmcateirvtiSty.sqlite-shm | binary | |
MD5:B7C14EC6110FA820CA6B65F5AEC85911 | SHA256:FD4C9FDA9CD3F9AE7C962B0DDF37232294D55580E1AA165AA06129B8549389EB | |||
| 7712 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\prefs-1.js | text | |
MD5:0F2A4575A82E92C1D2CDFEDF3C2B5CD3 | SHA256:— | |||
| 7712 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\storage\permanent\chrome\idb\2823318777ntouromlalnodry--naod.sqlite-shm | binary | |
MD5:B7C14EC6110FA820CA6B65F5AEC85911 | SHA256:FD4C9FDA9CD3F9AE7C962B0DDF37232294D55580E1AA165AA06129B8549389EB | |||
| 7712 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\SiteSecurityServiceState.bin | binary | |
MD5:8B4AF8126E4B16222F212FBE636958DD | SHA256:AA07E227121171B851F7202696A0C00ACB3390A7B8FC222EC81D44FAAD5B9F2C | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
79
TCP/UDP connections
390
DNS requests
378
Threats
26
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
7712 | firefox.exe | POST | 200 | 142.250.186.99:80 | http://o.pki.goog/we2 | unknown | — | — | whitelisted |
7712 | firefox.exe | POST | 200 | 142.250.186.99:80 | http://o.pki.goog/s/wr3/UTA | unknown | — | — | whitelisted |
6544 | svchost.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
7712 | firefox.exe | GET | 200 | 34.107.221.82:80 | http://detectportal.firefox.com/canonical.html | unknown | — | — | whitelisted |
5496 | MoUsoCoreWorker.exe | GET | 200 | 23.48.23.141:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
7712 | firefox.exe | GET | 200 | 34.107.221.82:80 | http://detectportal.firefox.com/success.txt?ipv4 | unknown | — | — | whitelisted |
7712 | firefox.exe | POST | 200 | 142.250.186.99:80 | http://o.pki.goog/s/wr3/cgo | unknown | — | — | whitelisted |
7712 | firefox.exe | POST | 200 | 184.24.77.48:80 | http://r10.o.lencr.org/ | unknown | — | — | whitelisted |
7712 | firefox.exe | POST | 200 | 184.24.77.47:80 | http://r11.o.lencr.org/ | unknown | — | — | whitelisted |
7712 | firefox.exe | POST | 200 | 184.24.77.47:80 | http://r11.o.lencr.org/ | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
5216 | RUXIMICS.exe | 51.104.136.2:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 51.104.136.2:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
2104 | svchost.exe | 51.104.136.2:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
5496 | MoUsoCoreWorker.exe | 23.48.23.141:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
2112 | svchost.exe | 51.104.136.2:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
3216 | svchost.exe | 20.10.31.115:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
7712 | firefox.exe | 34.107.221.82:80 | detectportal.firefox.com | GOOGLE | US | whitelisted |
7712 | firefox.exe | 34.117.188.166:443 | contile.services.mozilla.com | GOOGLE-CLOUD-PLATFORM | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
detectportal.firefox.com |
| whitelisted |
prod.detectportal.prod.cloudops.mozgcp.net |
| whitelisted |
example.org |
| whitelisted |
ipv4only.arpa |
| whitelisted |
contile.services.mozilla.com |
| whitelisted |
spocs.getpocket.com |
| whitelisted |
content-signature-2.cdn.mozilla.net |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2196 | svchost.exe | Not Suspicious Traffic | INFO [ANY.RUN] BootstrapCDN (stackpath .bootstrapcdn .com) |
2196 | svchost.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare content delivery network (cdnjs .cloudflare .com) |
2196 | svchost.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare content delivery network (cdnjs .cloudflare .com) |
2196 | svchost.exe | Not Suspicious Traffic | INFO [ANY.RUN] BootstrapCDN (stackpath .bootstrapcdn .com) |
2196 | svchost.exe | Not Suspicious Traffic | INFO [ANY.RUN] BootstrapCDN (stackpath .bootstrapcdn .com) |
2196 | svchost.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare content delivery network (cdnjs .cloudflare .com) |
2196 | svchost.exe | Misc activity | ET INFO External IP Lookup Domain (ipify .org) in DNS Lookup |
2196 | svchost.exe | Misc activity | ET INFO External IP Lookup Domain (ipify .org) in DNS Lookup |
2196 | svchost.exe | Misc activity | ET INFO External IP Lookup Domain (ipify .org) in DNS Lookup |
7712 | firefox.exe | Misc activity | ET INFO External IP Address Lookup Domain (ipify .org) in TLS SNI |