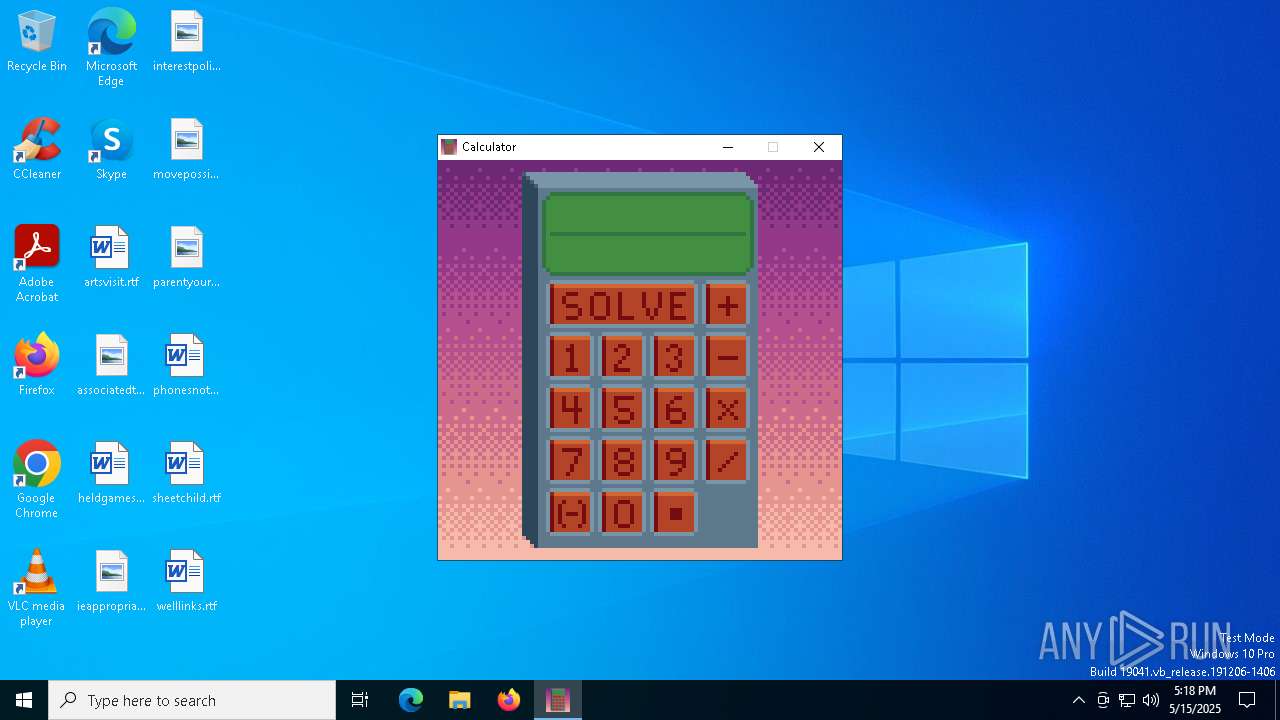
| File name: | Calculator.exe |
| Full analysis: | https://app.any.run/tasks/81e4edd5-7704-4a50-99f0-1ed3f5efe39d |
| Verdict: | Malicious activity |
| Analysis date: | May 15, 2025, 17:18:12 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32+ executable (GUI) x86-64, for MS Windows, 6 sections |
| MD5: | B3AC8B8E872D88237E8C00AE0F7F7381 |
| SHA1: | 479D28D9AC4EDE141BFFC65DB174D5690CAFB00D |
| SHA256: | 7C8AA797B1B0254728483B5F98975D17AD2563538514B6C700B684CA7A9550B2 |
| SSDEEP: | 393216:M3h+MnB7ebU0ybDPEHBoM6CIVTOGZC9v:2JnBmJfH6CIVTOG49 |
MALICIOUS
No malicious indicators.SUSPICIOUS
The process drops C-runtime libraries
- Calculator.exe (PID: 300)
Process drops legitimate windows executable
- Calculator.exe (PID: 300)
Process drops python dynamic module
- Calculator.exe (PID: 300)
Executable content was dropped or overwritten
- Calculator.exe (PID: 300)
Application launched itself
- Calculator.exe (PID: 300)
Loads Python modules
- Calculator.exe (PID: 4736)
There is functionality for taking screenshot (YARA)
- Calculator.exe (PID: 300)
- Calculator.exe (PID: 4736)
INFO
Reads the computer name
- Calculator.exe (PID: 300)
- Calculator.exe (PID: 4736)
Checks supported languages
- Calculator.exe (PID: 300)
- Calculator.exe (PID: 4736)
The sample compiled with english language support
- Calculator.exe (PID: 300)
Create files in a temporary directory
- Calculator.exe (PID: 300)
Reads the machine GUID from the registry
- Calculator.exe (PID: 4736)
Reads mouse settings
- Calculator.exe (PID: 4736)
PyInstaller has been detected (YARA)
- Calculator.exe (PID: 300)
- Calculator.exe (PID: 4736)
Reads the software policy settings
- slui.exe (PID: 4756)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win64 Executable (generic) (87.3) |
|---|---|---|
| .exe | | | Generic Win/DOS Executable (6.3) |
| .exe | | | DOS Executable Generic (6.3) |
EXIF
EXE
| MachineType: | AMD AMD64 |
|---|---|
| TimeStamp: | 2025:05:14 20:00:10+00:00 |
| ImageFileCharacteristics: | Executable, Large address aware |
| PEType: | PE32+ |
| LinkerVersion: | 14.4 |
| CodeSize: | 167936 |
| InitializedDataSize: | 306688 |
| UninitializedDataSize: | - |
| EntryPoint: | 0xbe20 |
| OSVersion: | 5.2 |
| ImageVersion: | - |
| SubsystemVersion: | 5.2 |
| Subsystem: | Windows GUI |
Total processes
131
Monitored processes
5
Malicious processes
1
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 300 | "C:\Users\admin\AppData\Local\Temp\Calculator.exe" | C:\Users\admin\AppData\Local\Temp\Calculator.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Modules
| |||||||||||||||
| 1164 | C:\WINDOWS\System32\slui.exe -Embedding | C:\Windows\System32\slui.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Activation Client Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4380 | C:\WINDOWS\system32\SppExtComObj.exe -Embedding | C:\Windows\System32\SppExtComObj.Exe | — | svchost.exe | |||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: KMS Connection Broker Version: 10.0.19041.3996 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4736 | "C:\Users\admin\AppData\Local\Temp\Calculator.exe" | C:\Users\admin\AppData\Local\Temp\Calculator.exe | — | Calculator.exe | |||||||||||
User: admin Integrity Level: MEDIUM Modules
| |||||||||||||||
| 4756 | "C:\WINDOWS\System32\SLUI.exe" RuleId=3482d82e-ca2c-4e1f-8864-da0267b484b2;Action=AutoActivate;AppId=55c92734-d682-4d71-983e-d6ec3f16059f;SkuId=4de7cb65-cdf1-4de9-8ae8-e3cce27b9f2c;NotificationInterval=1440;Trigger=TimerEvent | C:\Windows\System32\slui.exe | SppExtComObj.Exe | ||||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows Activation Client Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
886
Read events
885
Write events
1
Delete events
0
Modification events
| (PID) Process: | (4736) Calculator.exe | Key: | HKEY_CURRENT_USER\System\CurrentControlSet\Control\MediaProperties\PrivateProperties\DirectInput\VID_0627&PID_0001\Calibration\0 |
| Operation: | write | Name: | GUID |
Value: F01341A0B031F0118001444553540000 | |||
Executable files
95
Suspicious files
7
Text files
1
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 300 | Calculator.exe | C:\Users\admin\AppData\Local\Temp\_MEI3002\SDL2_image.dll | executable | |
MD5:B8D249A5E394B4E6A954C557AF1B80E6 | SHA256:1E364AF75FEE0C83506FBDFD4D5B0E386C4E9C6A33DDBDDAC61DDB131E360194 | |||
| 300 | Calculator.exe | C:\Users\admin\AppData\Local\Temp\_MEI3002\Pythonwin\win32ui.pyd | executable | |
MD5:79FF2A54A88364617450A95224BAAFFD | SHA256:18D37C6FEE55515F9242D31A627671EC4413A428B08A14EA329D8D9B2A54D57F | |||
| 300 | Calculator.exe | C:\Users\admin\AppData\Local\Temp\_MEI3002\SDL2_mixer.dll | executable | |
MD5:201AA86DC9349396B83EED4C15ABE764 | SHA256:2A0FC5E9F72C2EAEC3240CB82B7594A58CCDA609485981F256B94D0A4DD8D6F8 | |||
| 300 | Calculator.exe | C:\Users\admin\AppData\Local\Temp\_MEI3002\SDL2_ttf.dll | executable | |
MD5:F187DFDCCC102436E27704DC572A2C16 | SHA256:FCDFABDFCE868EB33F7514025FF59C1BB6C418F1BCD6ACE2300A9CD4053E1D63 | |||
| 300 | Calculator.exe | C:\Users\admin\AppData\Local\Temp\_MEI3002\VCRUNTIME140_1.dll | executable | |
MD5:135359D350F72AD4BF716B764D39E749 | SHA256:34048ABAA070ECC13B318CEA31425F4CA3EDD133D350318AC65259E6058C8B32 | |||
| 300 | Calculator.exe | C:\Users\admin\AppData\Local\Temp\_MEI3002\Pythonwin\mfc140u.dll | executable | |
MD5:CD1D99DF975EE5395174DF834E82B256 | SHA256:D8CA1DEA862085F0204680230D29BFF4D168FFF675AB4700EEAF63704D995CB3 | |||
| 300 | Calculator.exe | C:\Users\admin\AppData\Local\Temp\_MEI3002\SDL2.dll | executable | |
MD5:83C5FF24EAE3B9038D74AD91DC884E32 | SHA256:520D0459B91EFA32FBCCF9027A9CA1FC5AAE657E679CE8E90F179F9CF5AFD279 | |||
| 300 | Calculator.exe | C:\Users\admin\AppData\Local\Temp\_MEI3002\_lzma.pyd | executable | |
MD5:7447EFD8D71E8A1929BE0FAC722B42DC | SHA256:60793C8592193CFBD00FD3E5263BE4315D650BA4F9E4FDA9C45A10642FD998BE | |||
| 300 | Calculator.exe | C:\Users\admin\AppData\Local\Temp\_MEI3002\_multiprocessing.pyd | executable | |
MD5:A9A0588711147E01EED59BE23C7944A9 | SHA256:7581EDEA33C1DB0A49B8361E51E6291688601640E57D75909FB2007B2104FA4C | |||
| 300 | Calculator.exe | C:\Users\admin\AppData\Local\Temp\_MEI3002\_decimal.pyd | executable | |
MD5:20C77203DDF9FF2FF96D6D11DEA2EDCF | SHA256:9AAC010A424C757C434C460C3C0A6515D7720966AB64BAD667539282A17B4133 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
7
TCP/UDP connections
22
DNS requests
14
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
5496 | MoUsoCoreWorker.exe | GET | 200 | 23.48.23.177:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
5496 | MoUsoCoreWorker.exe | GET | 200 | 69.192.161.161:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 69.192.161.161:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
2104 | svchost.exe | GET | 200 | 69.192.161.161:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
6544 | svchost.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
1568 | SIHClient.exe | GET | 200 | 2.23.246.101:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
1568 | SIHClient.exe | GET | 200 | 2.23.246.101:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
— | — | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
5496 | MoUsoCoreWorker.exe | 23.48.23.177:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
5496 | MoUsoCoreWorker.exe | 69.192.161.161:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
— | — | 69.192.161.161:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
2104 | svchost.exe | 69.192.161.161:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
3216 | svchost.exe | 172.211.123.248:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | FR | whitelisted |
6544 | svchost.exe | 20.190.159.68:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
6544 | svchost.exe | 2.17.190.73:80 | ocsp.digicert.com | AKAMAI-AS | DE | whitelisted |
2104 | svchost.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
google.com |
| whitelisted |
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
fe3cr.delivery.mp.microsoft.com |
| whitelisted |
nexusrules.officeapps.live.com |
| whitelisted |