| File name: | MEM_Service.zip |
| Full analysis: | https://app.any.run/tasks/d2aa12b3-4865-4632-9908-cd4be8472c93 |
| Verdict: | Malicious activity |
| Analysis date: | July 13, 2020, 06:30:57 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v2.0 to extract |
| MD5: | B1EC6AE412930EDA1F176589DAAB01BF |
| SHA1: | DF543EE4AB6743146FF62D4F7115F8562A84A74F |
| SHA256: | 7C83978224F42374F19D62060527A54825EF63F4D2AE3236E2EE7576FE3FC489 |
| SSDEEP: | 3072:fmQnmEyfhsoX/iq/PorPeh5hWj9A2M+mUOqcM8xHobb4Egvlnu1X8dkaDyI:oEyfhsUiq/PoTynWhvfmE6obb4vvRRl |
MALICIOUS
Unusual execution from Microsoft Office
- WINWORD.EXE (PID: 3116)
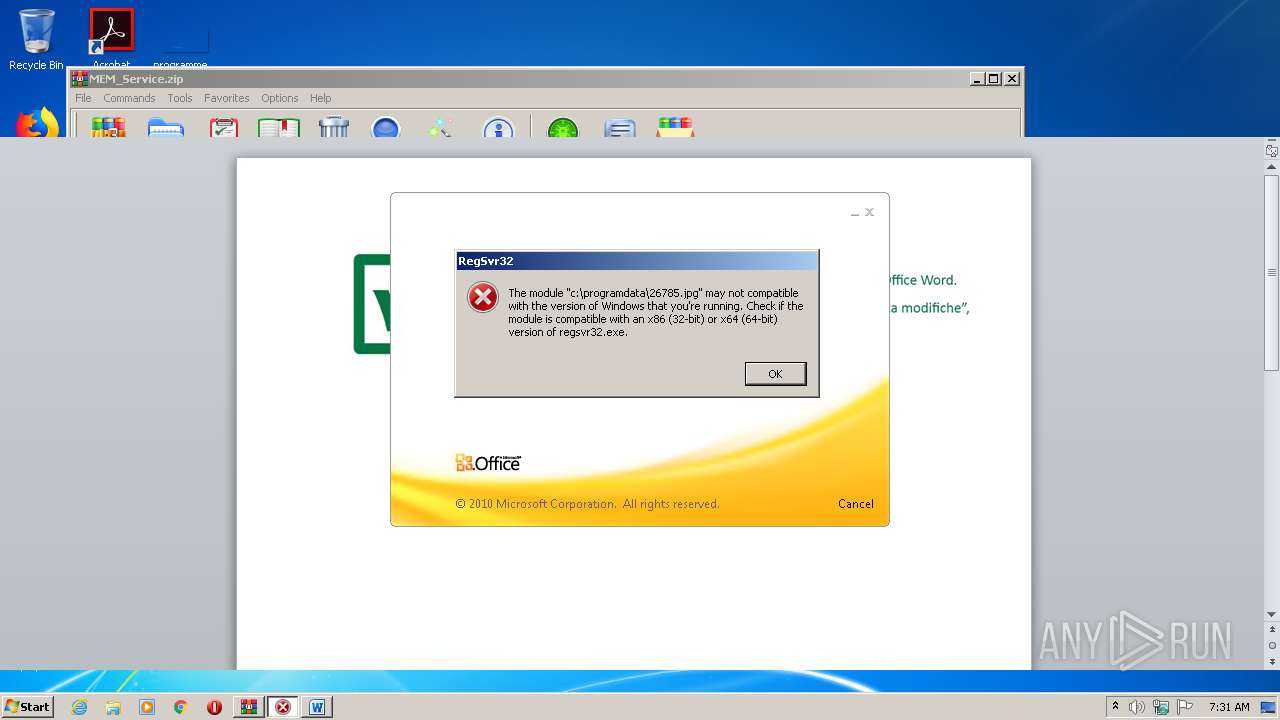
Registers / Runs the DLL via REGSVR32.EXE
- WINWORD.EXE (PID: 3116)
SUSPICIOUS
Creates files in the program directory
- WINWORD.EXE (PID: 3116)
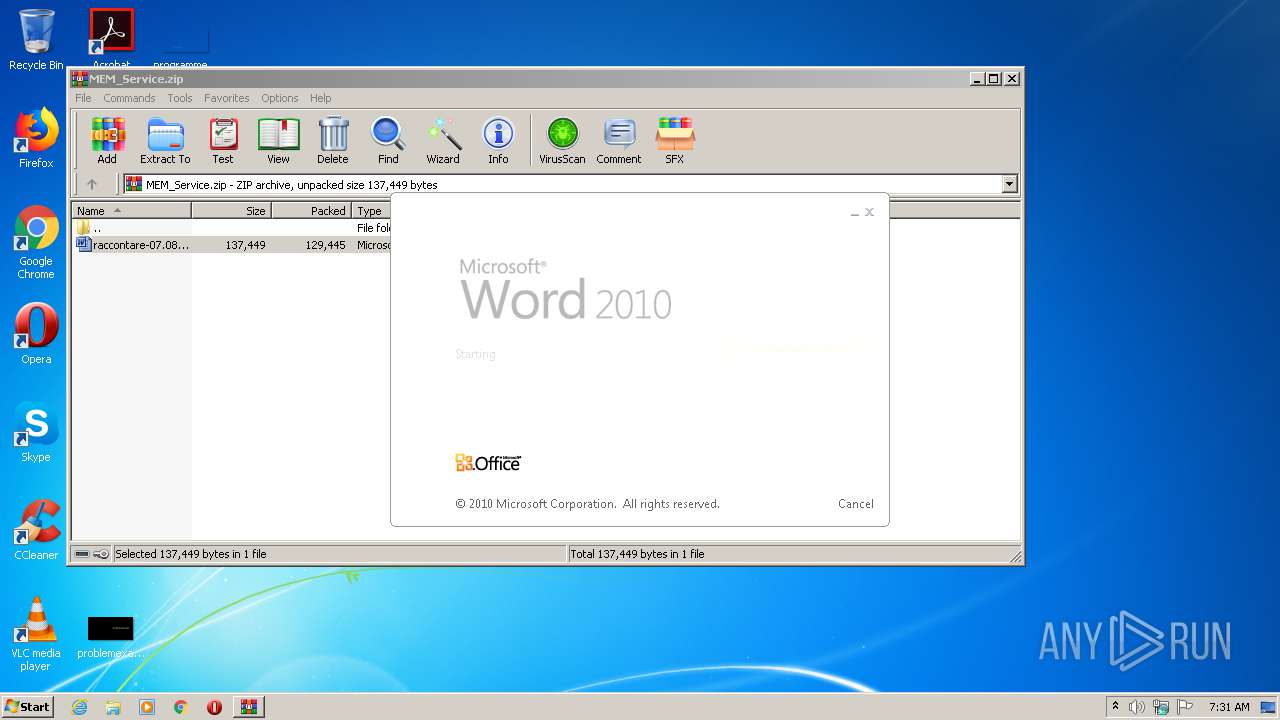
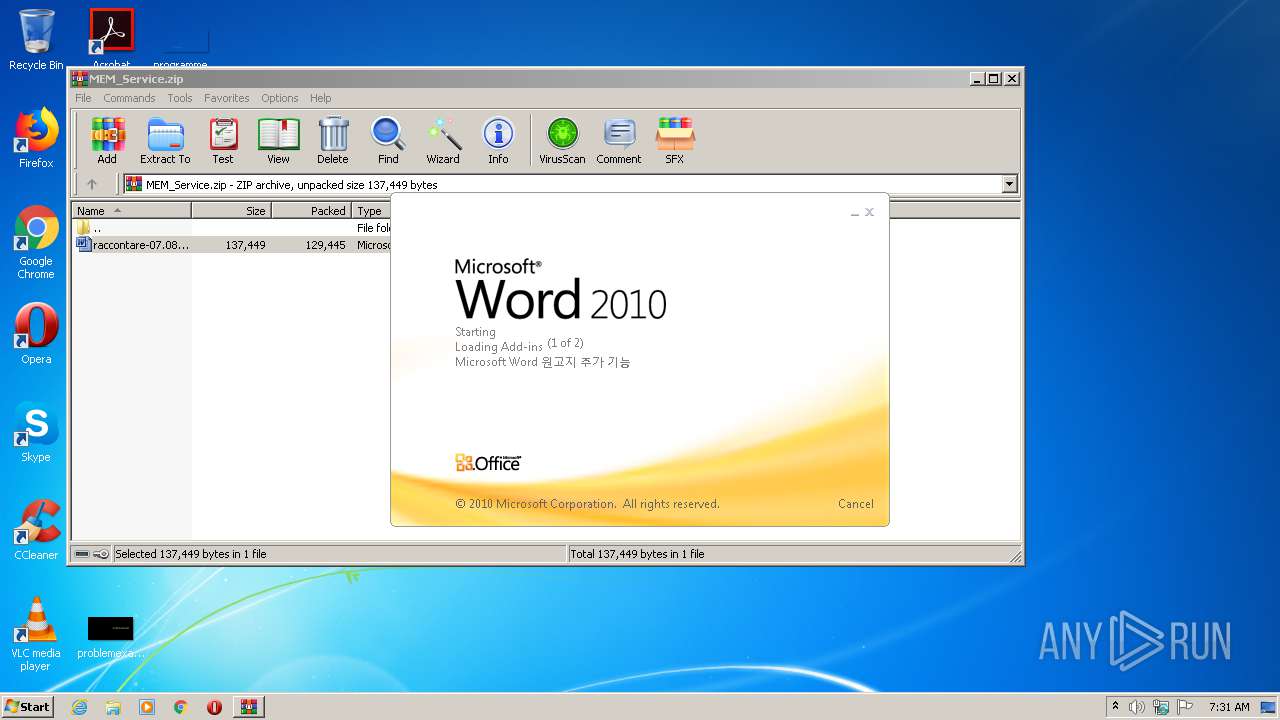
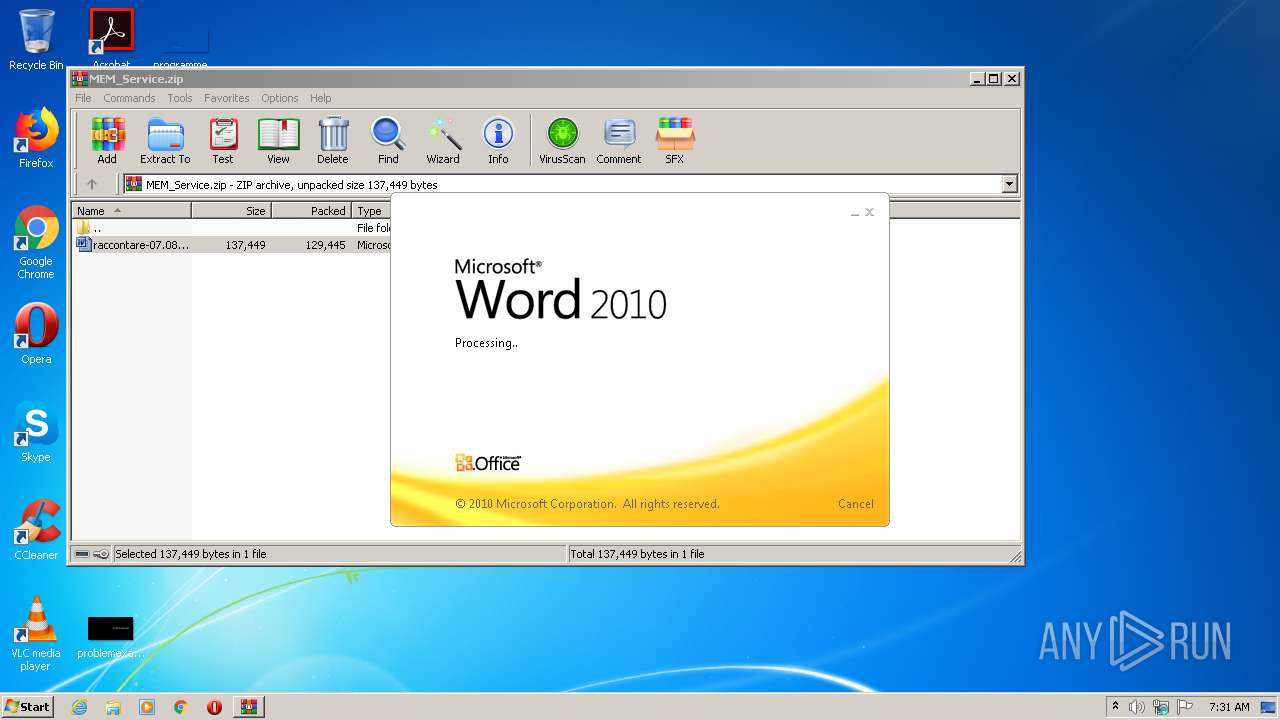
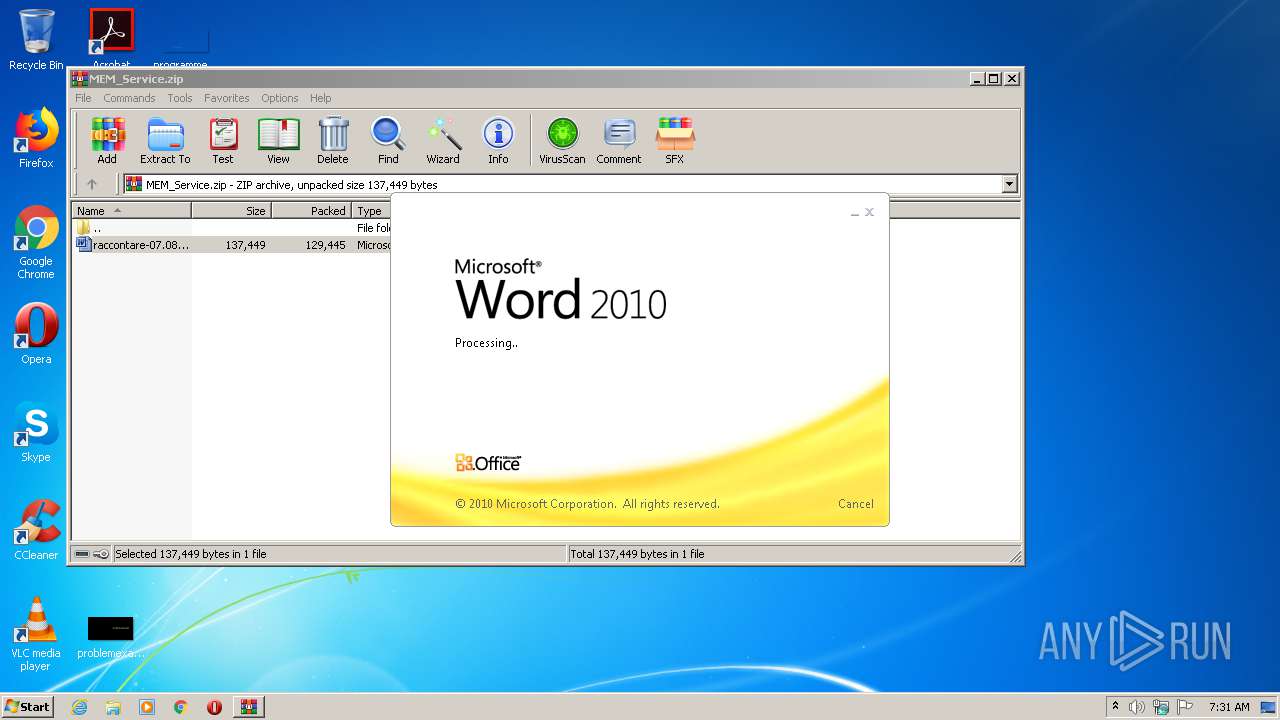
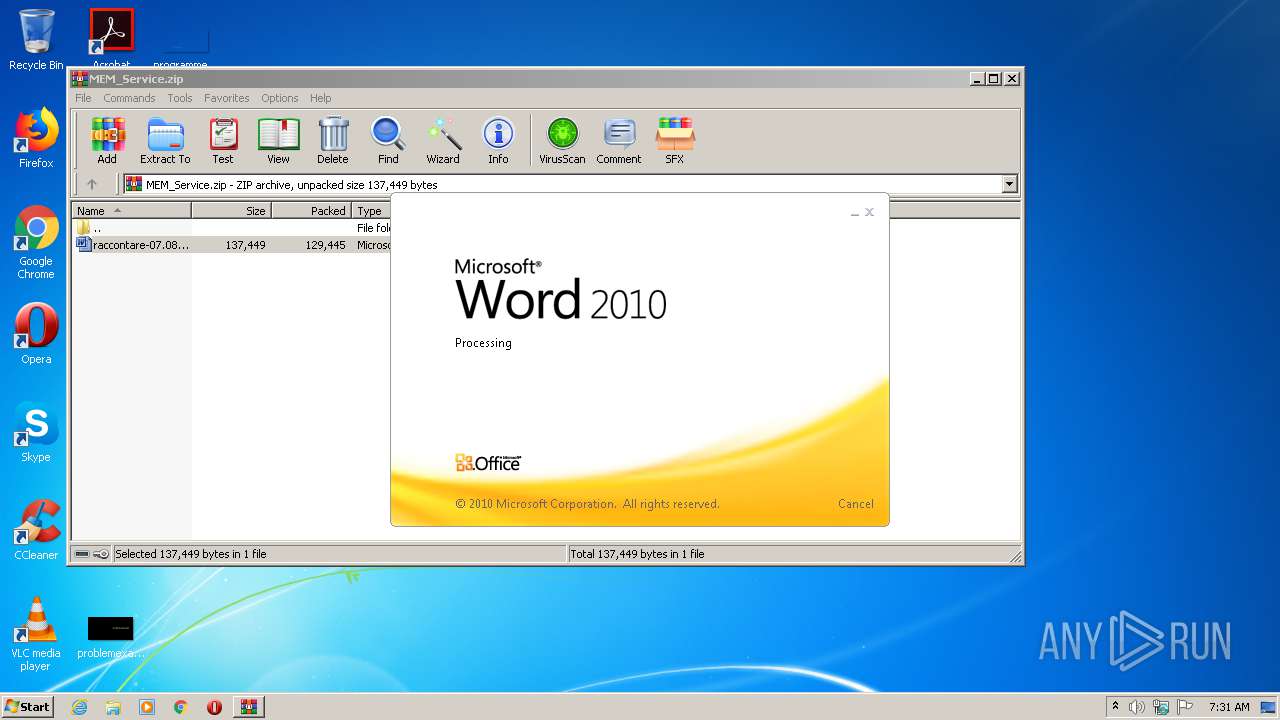
Starts Microsoft Office Application
- WinRAR.exe (PID: 1680)
INFO
Reads Internet Cache Settings
- WINWORD.EXE (PID: 3116)
Creates files in the user directory
- WINWORD.EXE (PID: 3116)
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 3116)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
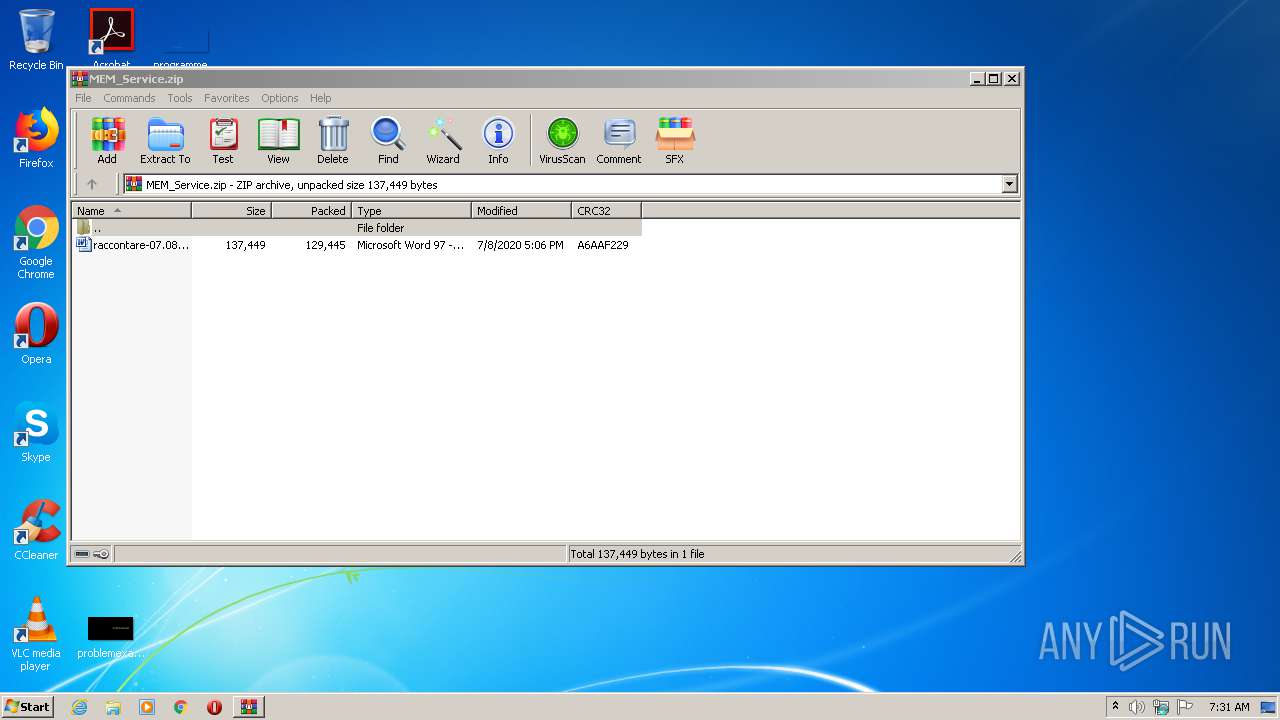
ZIP
| ZipRequiredVersion: | 20 |
|---|---|
| ZipBitFlag: | 0x0009 |
| ZipCompression: | Deflated |
| ZipModifyDate: | 2020:07:08 17:06:08 |
| ZipCRC: | 0xa6aaf229 |
| ZipCompressedSize: | 129445 |
| ZipUncompressedSize: | 137449 |
| ZipFileName: | raccontare-07.08.2020.doc |
Total processes
36
Monitored processes
3
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1284 | regsvr32 c:\programdata\26785.jpg | C:\Windows\system32\regsvr32.exe | — | WINWORD.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft(C) Register Server Exit code: 3 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1680 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Temp\MEM_Service.zip" | C:\Program Files\WinRAR\WinRAR.exe | — | explorer.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
| 3116 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\AppData\Local\Temp\Rar$DIb1680.20960\raccontare-07.08.2020.doc" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | WinRAR.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
Total events
2 456
Read events
1 408
Write events
924
Delete events
124
Modification events
| (PID) Process: | (1680) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (1680) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (1680) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\12F\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (1680) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\12F\52C64B7E |
| Operation: | write | Name: | @C:\Windows\system32\NetworkExplorer.dll,-1 |
Value: Network | |||
| (PID) Process: | (1680) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\MEM_Service.zip | |||
| (PID) Process: | (1680) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (1680) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (1680) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (1680) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
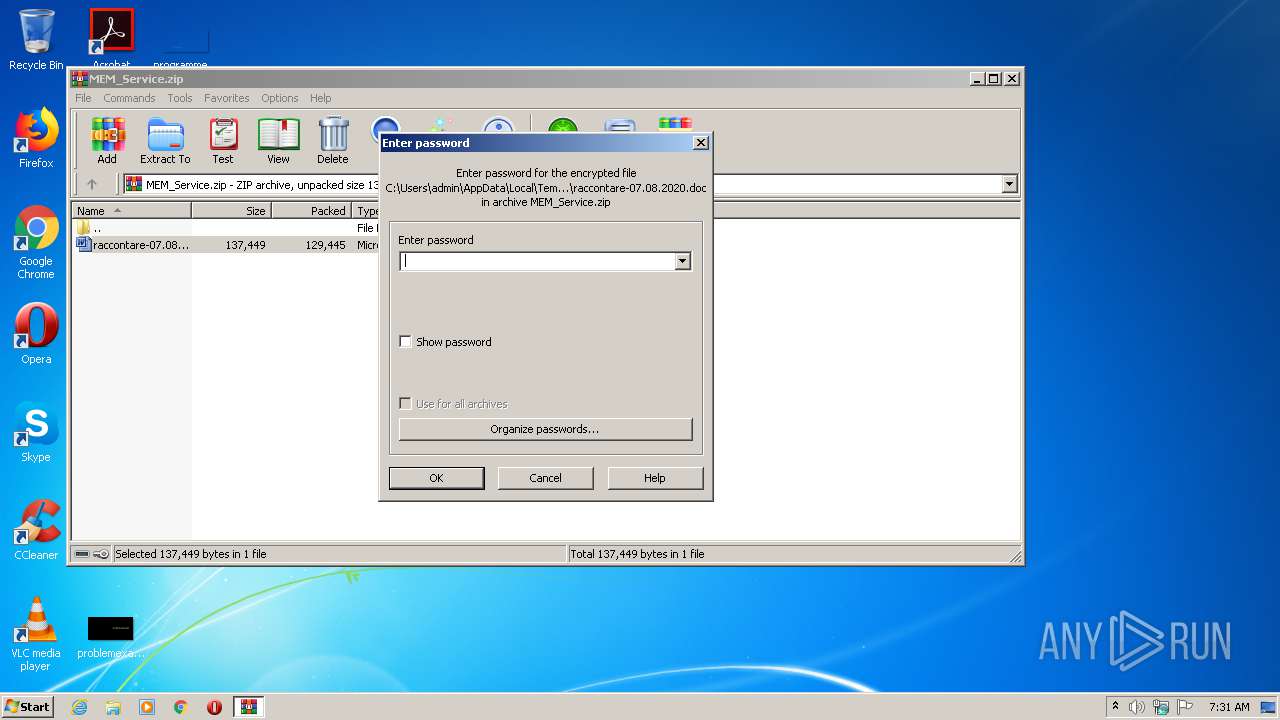
| (PID) Process: | (1680) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface |
| Operation: | write | Name: | ShowPassword |
Value: 0 | |||
Executable files
0
Suspicious files
1
Text files
1
Unknown types
2
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3116 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVRA3E.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 3116 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Templates\~$Normal.dotm | pgc | |
MD5:— | SHA256:— | |||
| 3116 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\Rar$DIb1680.20960\~$ccontare-07.08.2020.doc | pgc | |
MD5:— | SHA256:— | |||
| 1680 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DIb1680.20960\raccontare-07.08.2020.doc | document | |
MD5:— | SHA256:— | |||
| 3116 | WINWORD.EXE | C:\programdata\26785.jpg | text | |
MD5:81051BCC2CF1BEDF378224B0A93E2877 | SHA256:7EB70257593DA06F682A3DDDA54A9D260D4FC514F645237F5CA74B08F8DA61A6 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
1
DNS requests
1
Threats
1
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3116 | WINWORD.EXE | 93.189.41.227:80 | r0rfk.com | Limited Liability Company NTCOM | RU | suspicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
r0rfk.com |
| suspicious |
Threats
1 ETPRO signatures available at the full report