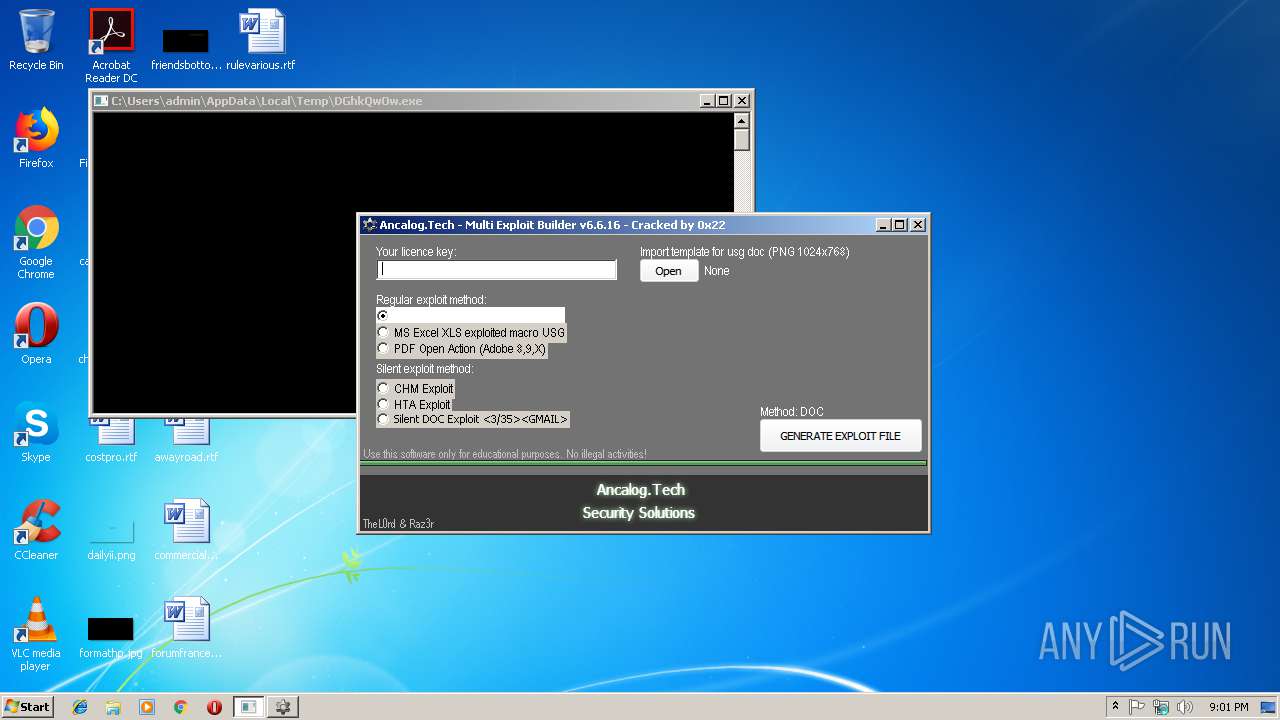
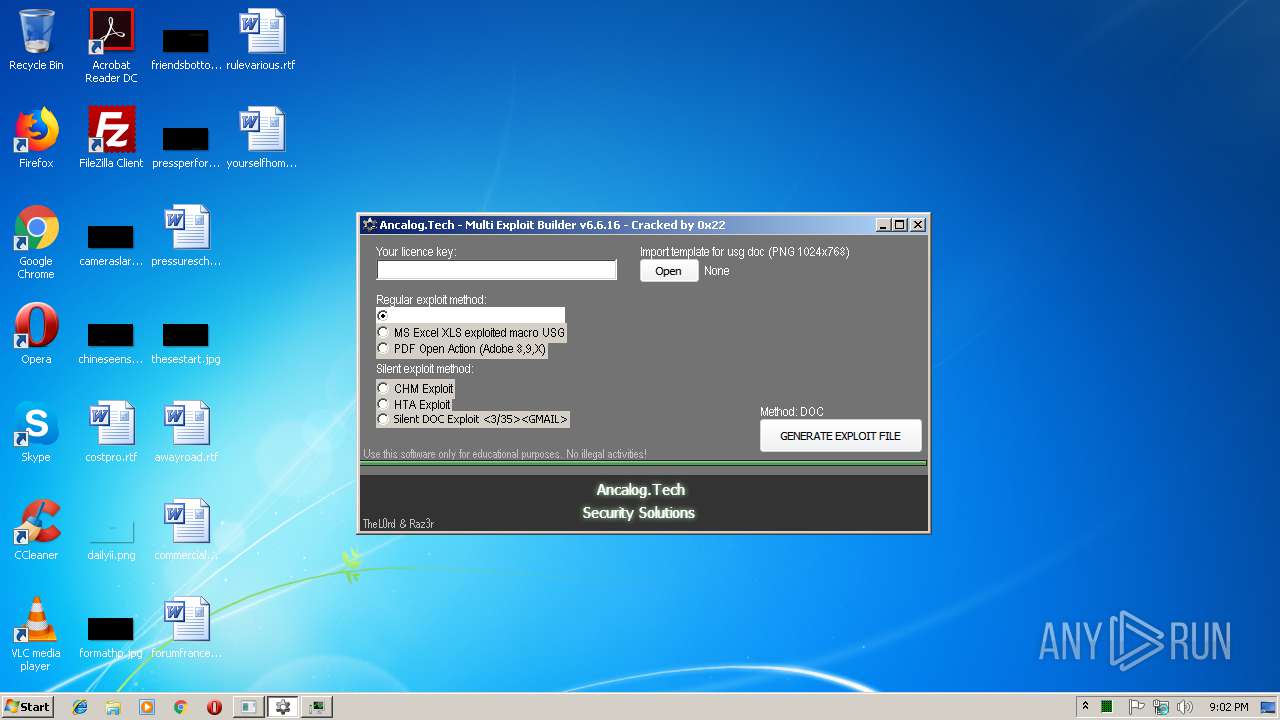
| File name: | Ancalog Exploit Builder.exe |
| Full analysis: | https://app.any.run/tasks/3e436f93-39e0-4ab5-b0ed-3b22fe3e131f |
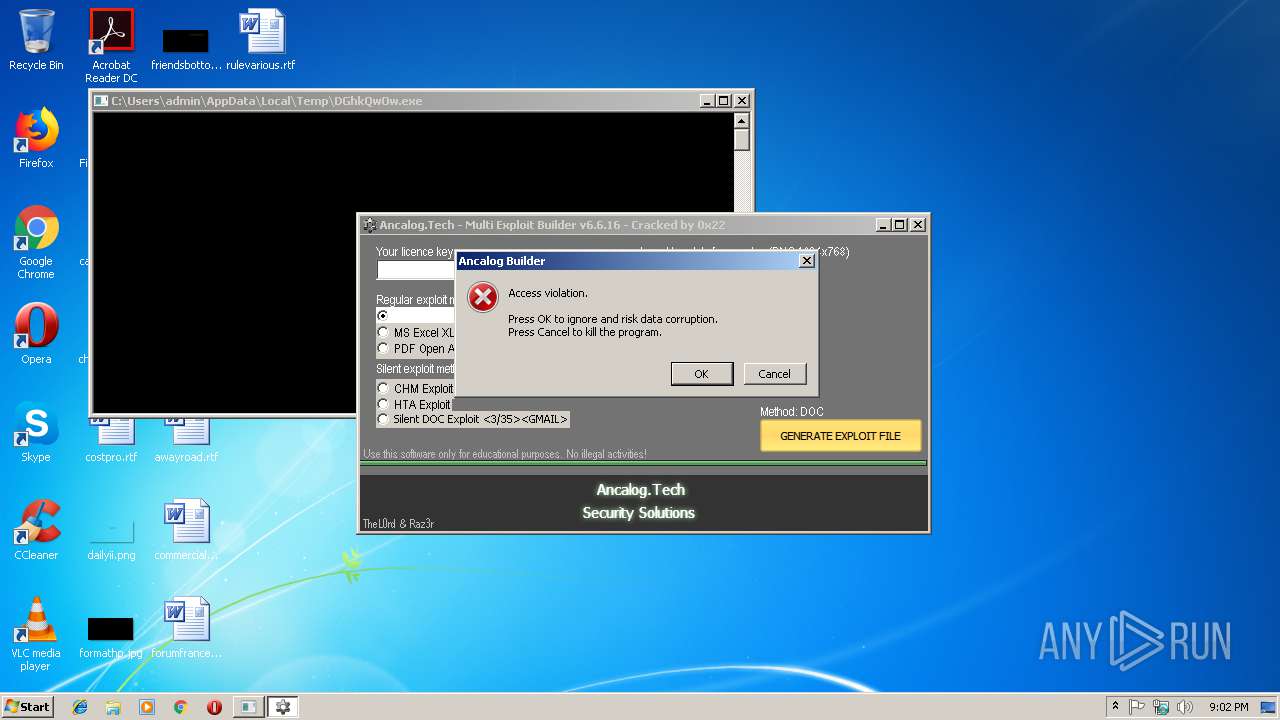
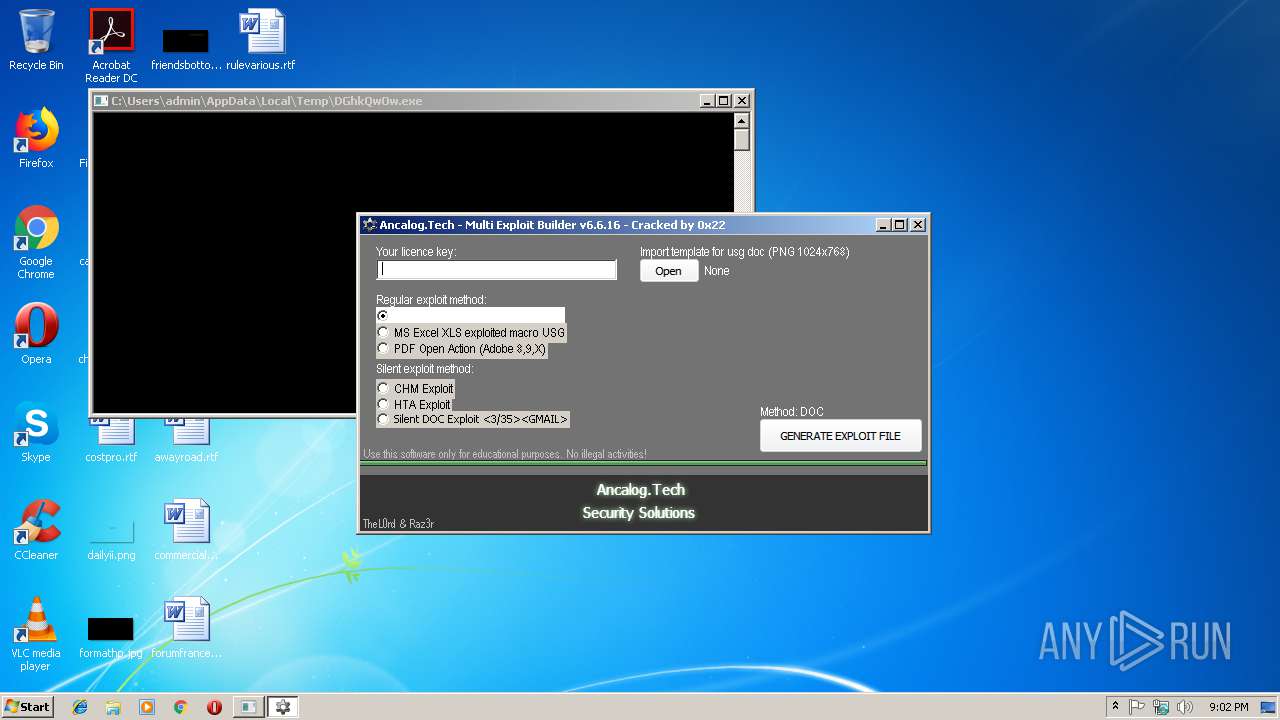
| Verdict: | Malicious activity |
| Analysis date: | January 05, 2019, 21:01:29 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 4E72B56F8B671CBE489B9F2262D03069 |
| SHA1: | 67A2902D1235B4A9F16420A7BBF440FAA49D08EE |
| SHA256: | 7C78B139580EF9493C165E5A236295ABF3B9A8AC0E0708E75C9BCB0EF7541441 |
| SSDEEP: | 24576:Uny/f9u1YRhE5eGHxreVsKoDa/eWRlcmY/hExESkgtEww3VVWsq:VFLhQ5Hxmc+mGcLh5Skdz3VEsq |
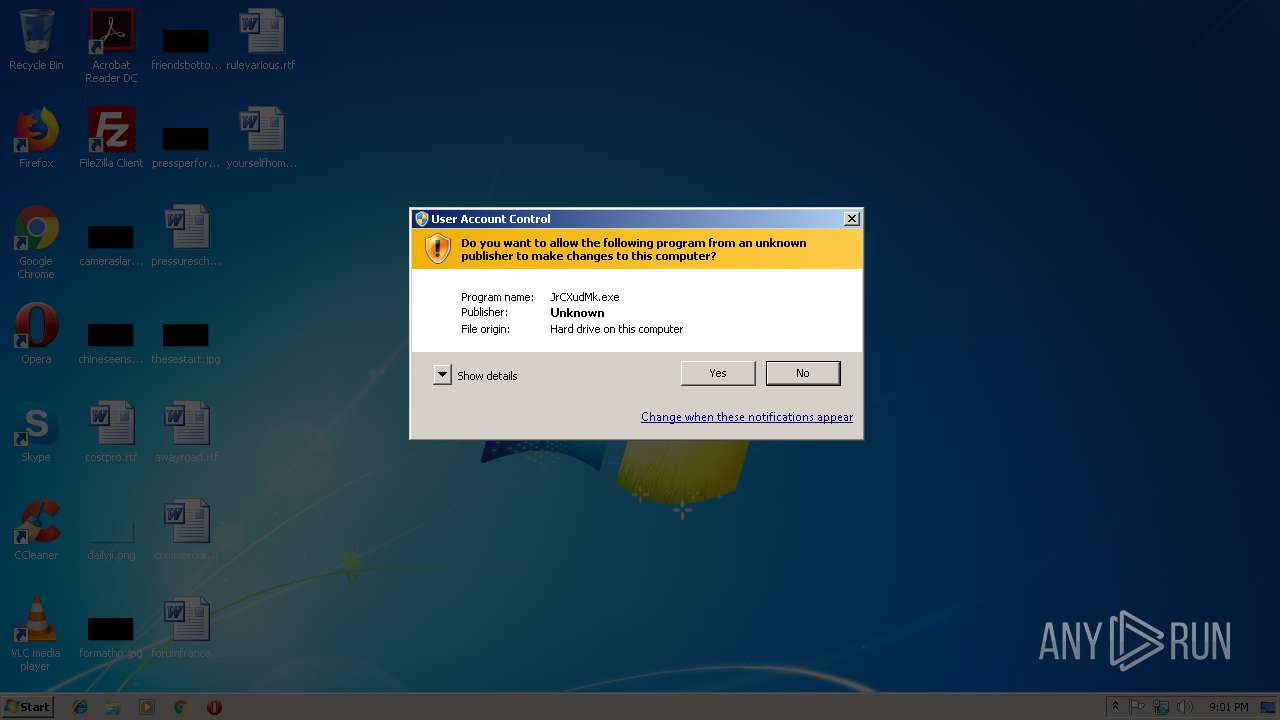
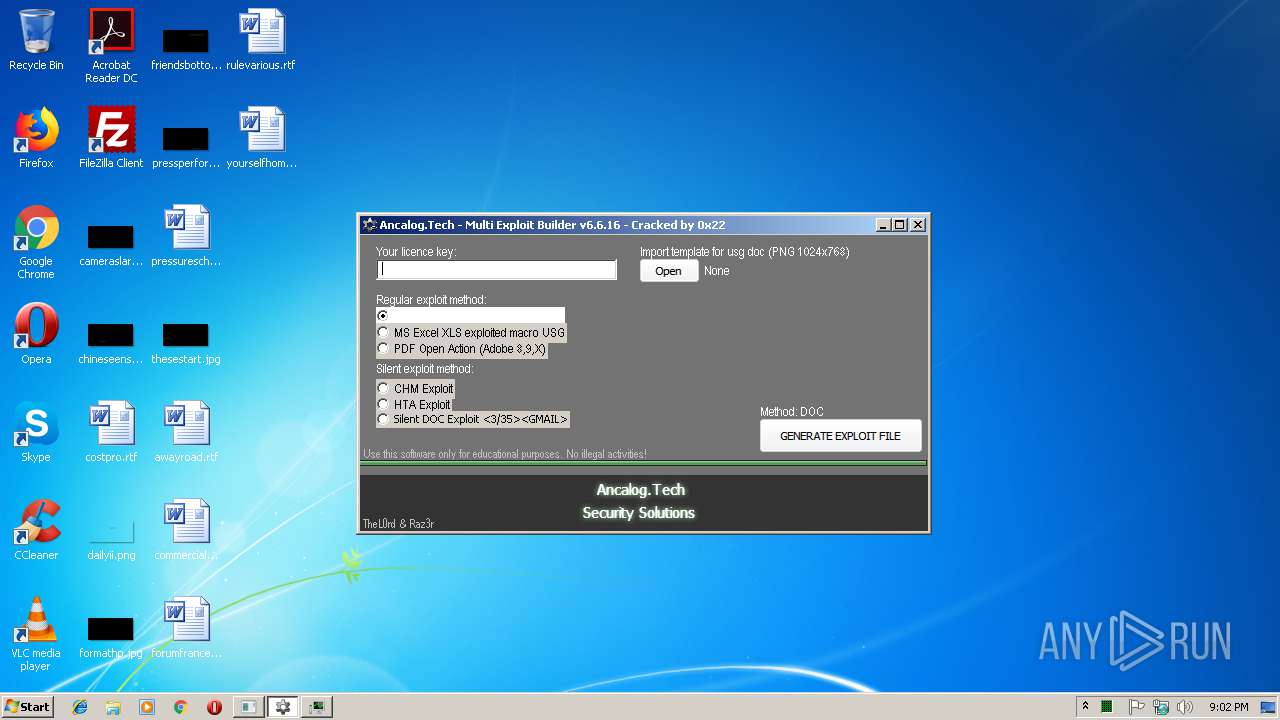
MALICIOUS
Application was dropped or rewritten from another process
- JrCXudMk.exe (PID: 2952)
- DGhkQwOw.exe (PID: 3280)
- JrCXudMk.exe (PID: 2600)
SUSPICIOUS
Creates files in the user directory
- DGhkQwOw.exe (PID: 3280)
Executable content was dropped or overwritten
- Ancalog Exploit Builder.exe (PID: 3144)
INFO
Creates files in the user directory
- WINWORD.EXE (PID: 2976)
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 2976)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (67.4) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (14.2) |
| .exe | | | Win32 Executable (generic) (9.7) |
| .exe | | | Generic Win/DOS Executable (4.3) |
| .exe | | | DOS Executable Generic (4.3) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2015:02:15 09:00:31+01:00 |
| PEType: | PE32 |
| LinkerVersion: | 9 |
| CodeSize: | 165888 |
| InitializedDataSize: | 540672 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x1d7cb |
| OSVersion: | 5 |
| ImageVersion: | - |
| SubsystemVersion: | 5 |
| Subsystem: | Windows GUI |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 15-Feb-2015 08:00:31 |
| Detected languages: |
|
| Debug artifacts: |
|
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x000000E8 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 4 |
| Time date stamp: | 15-Feb-2015 08:00:31 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x0002878A | 0x00028800 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.71935 |
.rdata | 0x0002A000 | 0x00004FD3 | 0x00005000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.38998 |
.data | 0x0002F000 | 0x00021428 | 0x00001600 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 3.46555 |
.rsrc | 0x00051000 | 0x0005D83E | 0x0005DA00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 3.14285 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.24822 | 1738 | UNKNOWN | English - United States | RT_MANIFEST |
7 | 3.1586 | 482 | UNKNOWN | English - United States | RT_STRING |
8 | 3.11685 | 460 | UNKNOWN | English - United States | RT_STRING |
9 | 3.15447 | 494 | UNKNOWN | English - United States | RT_STRING |
10 | 2.99727 | 326 | UNKNOWN | English - United States | RT_STRING |
11 | 3.2036 | 1094 | UNKNOWN | English - United States | RT_STRING |
12 | 3.12889 | 358 | UNKNOWN | English - United States | RT_STRING |
13 | 2.95673 | 288 | UNKNOWN | English - United States | RT_STRING |
14 | 2.77928 | 186 | UNKNOWN | English - United States | RT_STRING |
15 | 2.66523 | 162 | UNKNOWN | English - United States | RT_STRING |
Imports
ADVAPI32.dll |
COMCTL32.dll |
COMDLG32.dll |
GDI32.dll |
KERNEL32.dll |
OLEAUT32.dll |
SHELL32.dll |
SHLWAPI.dll |
USER32.dll |
ole32.dll |
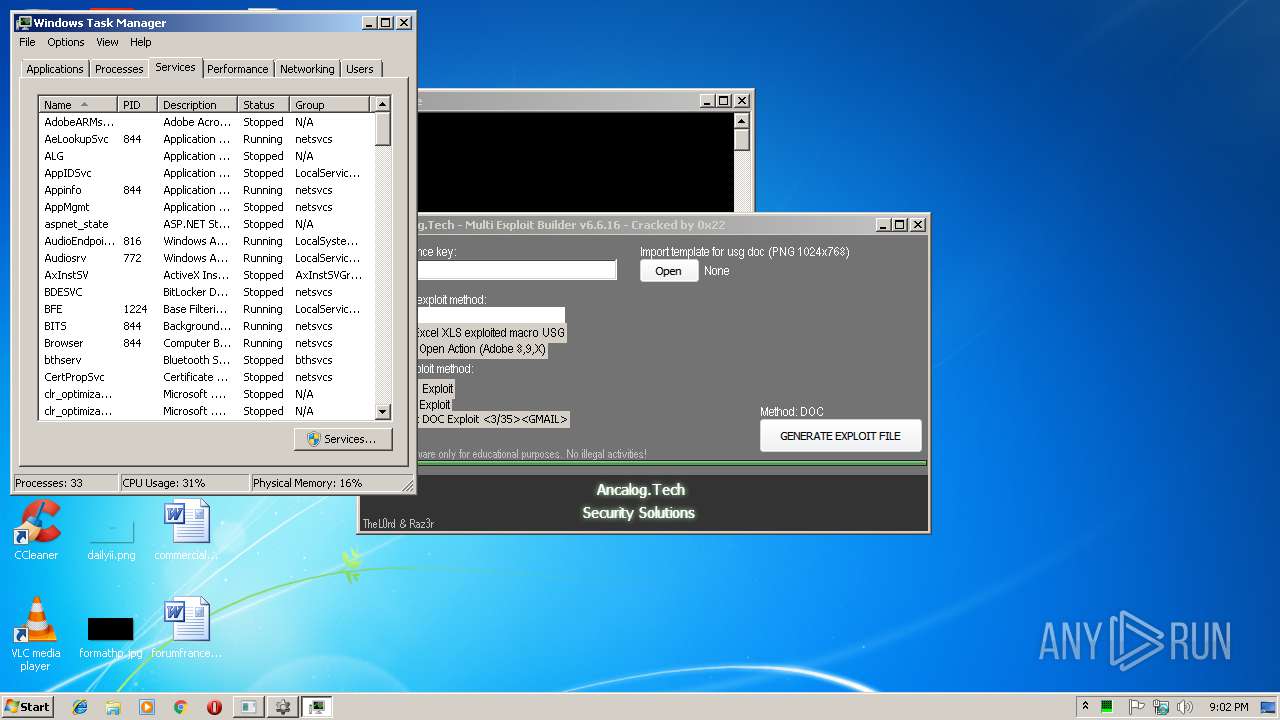
Total processes
42
Monitored processes
6
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
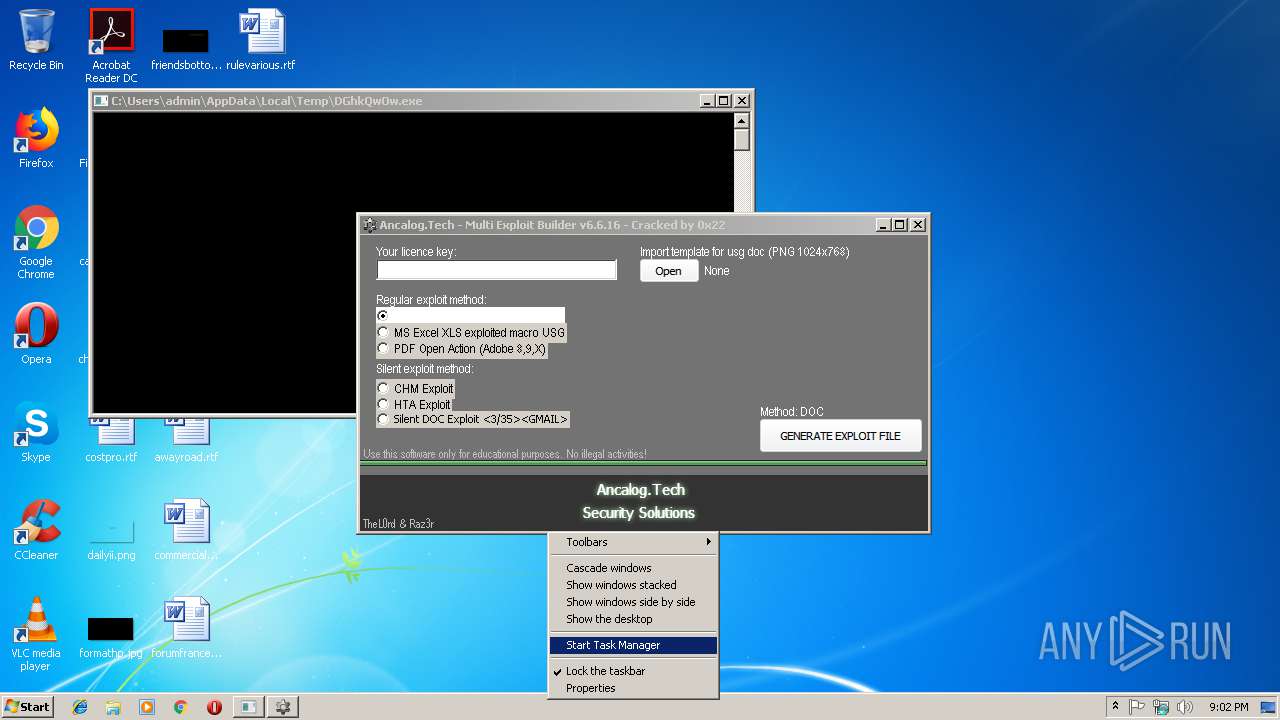
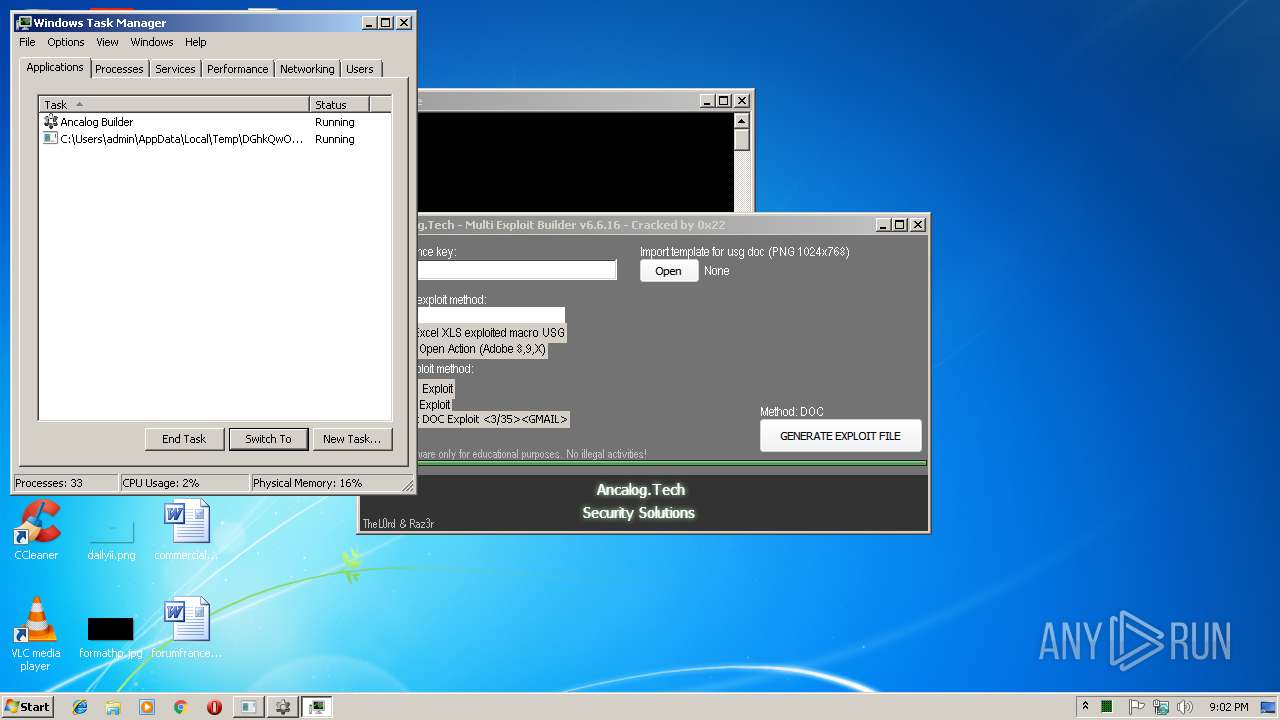
| 2356 | "C:\Windows\system32\taskmgr.exe" /4 | C:\Windows\system32\taskmgr.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Task Manager Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2600 | "C:\Users\admin\AppData\Local\Temp\JrCXudMk.exe" | C:\Users\admin\AppData\Local\Temp\JrCXudMk.exe | — | Ancalog Exploit Builder.exe | |||||||||||
User: admin Company: ancalog.tech Integrity Level: MEDIUM Description: Ancalog Multi Exploit Builder Exit code: 3221226540 Version: 1.0.0.0 Modules
| |||||||||||||||
| 2952 | "C:\Users\admin\AppData\Local\Temp\JrCXudMk.exe" | C:\Users\admin\AppData\Local\Temp\JrCXudMk.exe | Ancalog Exploit Builder.exe | ||||||||||||
User: admin Company: ancalog.tech Integrity Level: HIGH Description: Ancalog Multi Exploit Builder Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
| 2976 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\Desktop\yourselfhomepage.rtf" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 3144 | "C:\Users\admin\AppData\Local\Temp\Ancalog Exploit Builder.exe" | C:\Users\admin\AppData\Local\Temp\Ancalog Exploit Builder.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 3280 | "C:\Users\admin\AppData\Local\Temp\DGhkQwOw.exe" | C:\Users\admin\AppData\Local\Temp\DGhkQwOw.exe | Ancalog Exploit Builder.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Description: Downloader Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
Total events
1 078
Read events
1 006
Write events
61
Delete events
11
Modification events
| (PID) Process: | (3144) Ancalog Exploit Builder.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (3144) Ancalog Exploit Builder.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (3280) DGhkQwOw.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\DGhkQwOw_RASAPI32 |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (3280) DGhkQwOw.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\DGhkQwOw_RASAPI32 |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
| (PID) Process: | (3280) DGhkQwOw.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\DGhkQwOw_RASAPI32 |
| Operation: | write | Name: | FileTracingMask |
Value: 4294901760 | |||
| (PID) Process: | (3280) DGhkQwOw.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\DGhkQwOw_RASAPI32 |
| Operation: | write | Name: | ConsoleTracingMask |
Value: 4294901760 | |||
| (PID) Process: | (3280) DGhkQwOw.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\DGhkQwOw_RASAPI32 |
| Operation: | write | Name: | MaxFileSize |
Value: 1048576 | |||
| (PID) Process: | (3280) DGhkQwOw.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\DGhkQwOw_RASAPI32 |
| Operation: | write | Name: | FileDirectory |
Value: %windir%\tracing | |||
| (PID) Process: | (3280) DGhkQwOw.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\DGhkQwOw_RASMANCS |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (3280) DGhkQwOw.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\DGhkQwOw_RASMANCS |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
Executable files
2
Suspicious files
0
Text files
2
Unknown types
3
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2976 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVR7EE3.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 2976 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.Word\~WRS{B4DCE167-4827-4D26-8F7B-3F09437EEF07}.tmp | — | |
MD5:— | SHA256:— | |||
| 2976 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.Word\~WRS{600BA490-AB07-4559-9C50-8F93A3F0E79D}.tmp | — | |
MD5:— | SHA256:— | |||
| 3144 | Ancalog Exploit Builder.exe | C:\Users\admin\AppData\Local\Temp\DGhkQwOw.exe | executable | |
MD5:— | SHA256:— | |||
| 3144 | Ancalog Exploit Builder.exe | C:\Users\admin\AppData\Local\Temp\JrCXudMk.exe | executable | |
MD5:— | SHA256:— | |||
| 2976 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Office\Recent\yourselfhomepage.rtf.LNK | lnk | |
MD5:— | SHA256:— | |||
| 2976 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Office\Recent\index.dat | text | |
MD5:— | SHA256:— | |||
| 2976 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Templates\~$Normal.dotm | pgc | |
MD5:— | SHA256:— | |||
| 2976 | WINWORD.EXE | C:\Users\admin\Desktop\~$urselfhomepage.rtf | pgc | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
1
DNS requests
1
Threats
1
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3280 | DGhkQwOw.exe | 66.55.90.17:443 | a.pomf.cat | GigeNET | US | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
a.pomf.cat |
| unknown |
Threats
1 ETPRO signatures available at the full report